| URL: | https://ims-na1.adobelogin.com/ims/authorize?scope=allow_ac_dt_exchange%2Copenid%2CAdobeID%2Ccreative_cloud%2Ccreative_sdk%2Cread_organizations%2Csao.cce_private%2Cadditional_info.account_type&locale=en_US&client_id=CreativeCloudInstallerWeb_v1_0&redirect_uri=https%3A%2F%2Fauth.services.adobe.com%2Fen_US%2Fdeeplink.html%3Fdelegated_request_id%3D78f4fe6b-4bd4-430a-b3fd-ecb1a96638ec%26client_id%3DCreativeCloudInstallerWeb_v1_0%26deeplink%3Ddelegation |
| Full analysis: | https://app.any.run/tasks/6cf4ca8f-3152-4f46-9911-a6804a0b304f |
| Verdict: | No threats detected |
| Analysis date: | April 14, 2020, 06:31:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 803EF1697C5235640C3E826E9D7DF986 |
| SHA1: | E42F59D7070825684266DA15116E05383B6D42EF |
| SHA256: | 6E126369B5209C84A243DC91155DF7588C08C15D9895EC58CA3B53EF66BE9A45 |
| SSDEEP: | 12:2/qcCP7MBMAIElU2oZYLlEgXL1Y5RX7RP8uT38EgXPT:2oPCBIEW2oelESubN8/ESr |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 620)
Reads Internet Cache Settings
- iexplore.exe (PID: 620)
- iexplore.exe (PID: 1348)
Reads internet explorer settings
- iexplore.exe (PID: 1348)
Creates files in the user directory
- iexplore.exe (PID: 1348)
Reads settings of System Certificates
- iexplore.exe (PID: 1348)
- iexplore.exe (PID: 620)
Changes settings of System certificates
- iexplore.exe (PID: 620)
Adds / modifies Windows certificates
- iexplore.exe (PID: 620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files\Internet Explorer\iexplore.exe" https://ims-na1.adobelogin.com/ims/authorize?scope=allow_ac_dt_exchange%2Copenid%2CAdobeID%2Ccreative_cloud%2Ccreative_sdk%2Cread_organizations%2Csao.cce_private%2Cadditional_info.account_type&locale=en_US&client_id=CreativeCloudInstallerWeb_v1_0&redirect_uri=https%3A%2F%2Fauth.services.adobe.com%2Fen_US%2Fdeeplink.html%3Fdelegated_request_id%3D78f4fe6b-4bd4-430a-b3fd-ecb1a96638ec%26client_id%3DCreativeCloudInstallerWeb_v1_0%26deeplink%3Ddelegation | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:620 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
5 956
Read events
765
Write events
3 474
Delete events
1 717
Modification events
| (PID) Process: | (620) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2080143214 | |||
| (PID) Process: | (620) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30806566 | |||
| (PID) Process: | (620) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (620) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (620) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (620) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (620) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (620) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (620) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (620) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
51
Text files
38
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1348 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE547.tmp | — | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE548.tmp | — | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | binary | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1E11E75149C17A93653DA7DC0B8CF53F_1C0B508A0ECF68802270C96D25A23B40 | der | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1E11E75149C17A93653DA7DC0B8CF53F_1C0B508A0ECF68802270C96D25A23B40 | binary | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\deeplink[1].htm | html | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\styles.9812c5ab[1].css | text | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\scripts[1].js | binary | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
| 1348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\messages[1].json | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
52
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1348 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEF24i%2Bskh3%2FwCAAAAAA17OE%3D | US | der | 471 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEF24i%2Bskh3%2FwCAAAAAA17OE%3D | US | der | 471 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEArLKLpGXuU5CHZ0cPPNxhI%3D | US | der | 471 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCRUm2CdHJBtwgAAAAANe1T | US | der | 472 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCRUm2CdHJBtwgAAAAANe1T | US | der | 472 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEGOilOa74PejAgAAAABfmL8%3D | US | der | 471 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAza5nSVYZrPeIlAtSf0Rcs%3D | US | der | 471 b | whitelisted |
1348 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAFT5zSjKfJcBOJBfeXVZHY%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1348 | iexplore.exe | 104.108.57.29:443 | c.evidon.com | Akamai Technologies, Inc. | NL | unknown |
1348 | iexplore.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1348 | iexplore.exe | 3.234.108.176:443 | l.betrad.com | — | US | unknown |
1348 | iexplore.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
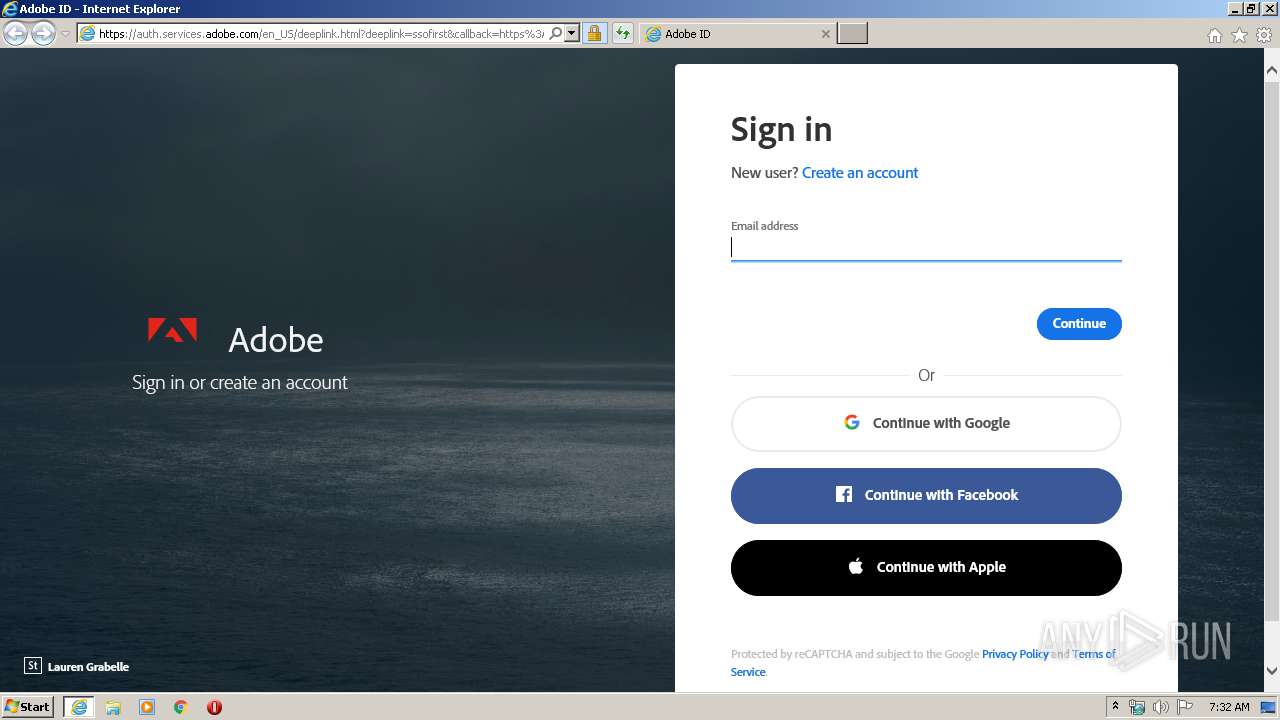
1348 | iexplore.exe | 34.252.48.249:443 | ims-na1.adobelogin.com | Amazon.com, Inc. | IE | unknown |
1348 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1348 | iexplore.exe | 52.222.167.102:443 | auth.services.adobe.com | Amazon.com, Inc. | US | unknown |
1348 | iexplore.exe | 104.111.215.74:443 | use.typekit.net | Akamai International B.V. | NL | unknown |
1348 | iexplore.exe | 15.188.105.205:443 | sstats.adobe.com | Hewlett-Packard Company | US | suspicious |
1348 | iexplore.exe | 23.213.165.28:443 | assets.adobedtm.com | Akamai Technologies, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ims-na1.adobelogin.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
auth.services.adobe.com |
| whitelisted |
use.typekit.net |
| whitelisted |
www.recaptcha.net |
| whitelisted |
www.adobe.com |
| whitelisted |
wwwimages2.adobe.com |
| whitelisted |
p.typekit.net |
| shared |
ocsp.pki.goog |
| whitelisted |
assets.adobedtm.com |
| whitelisted |