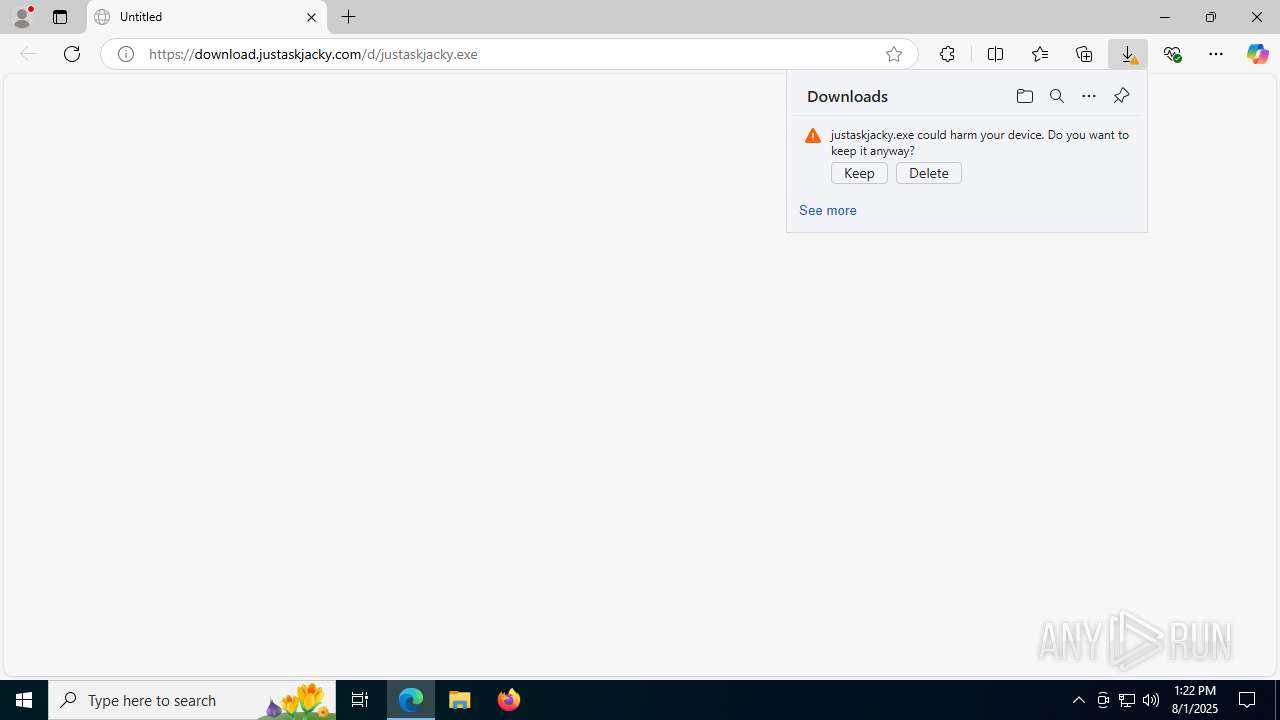
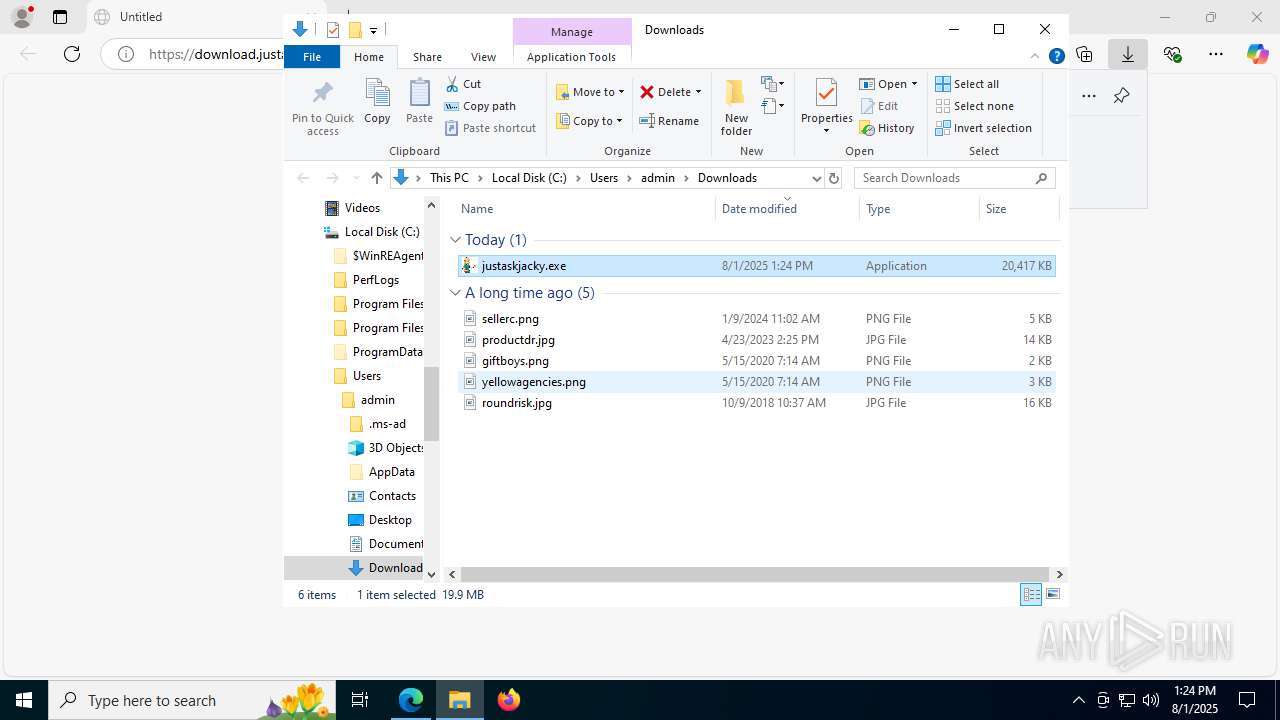
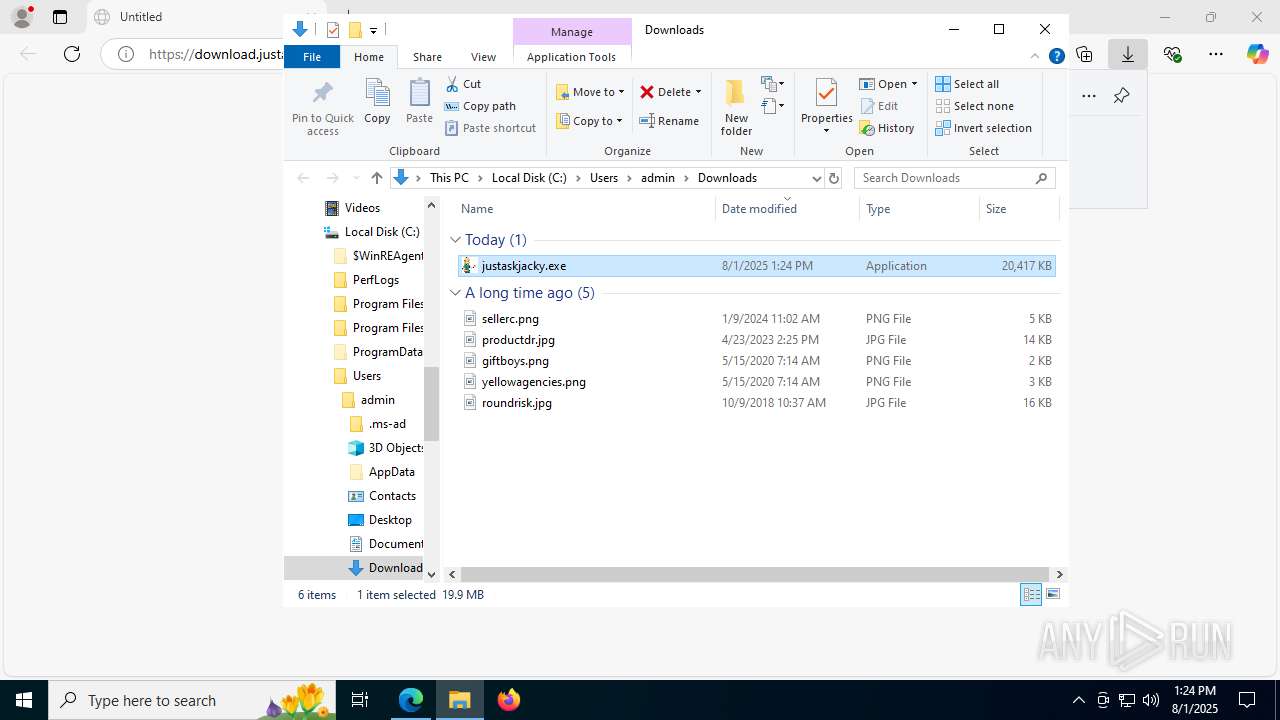
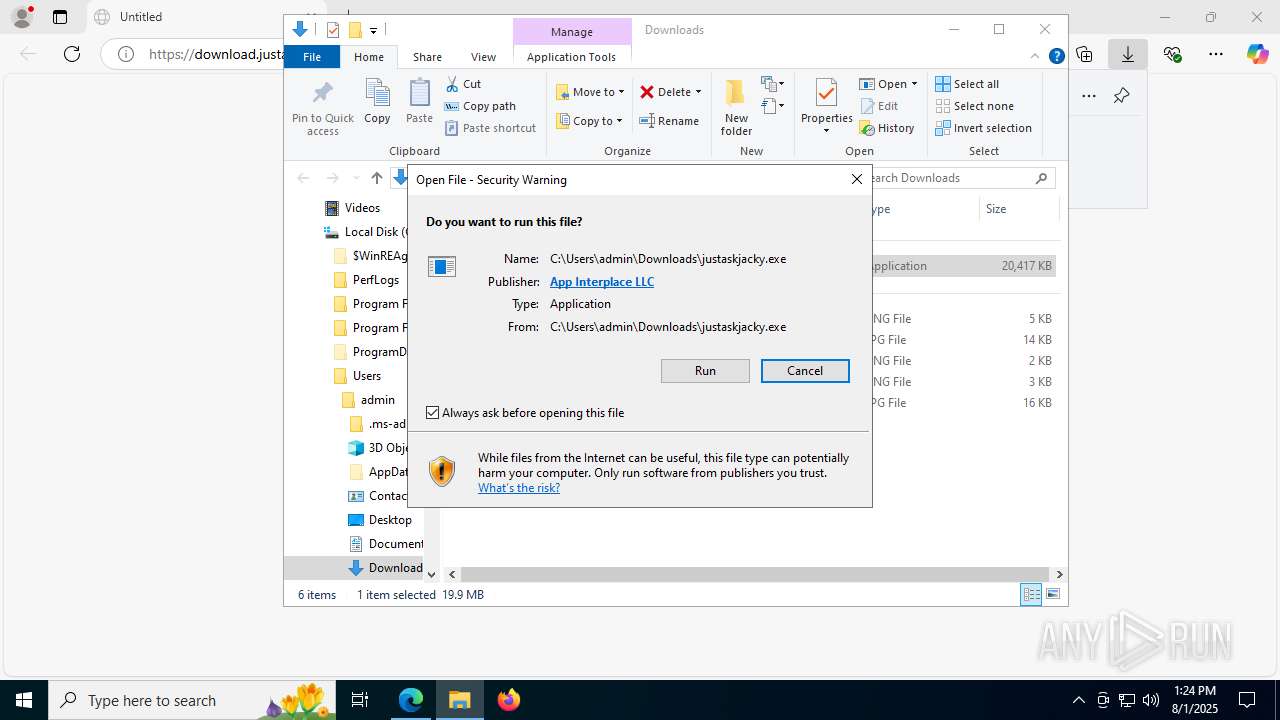
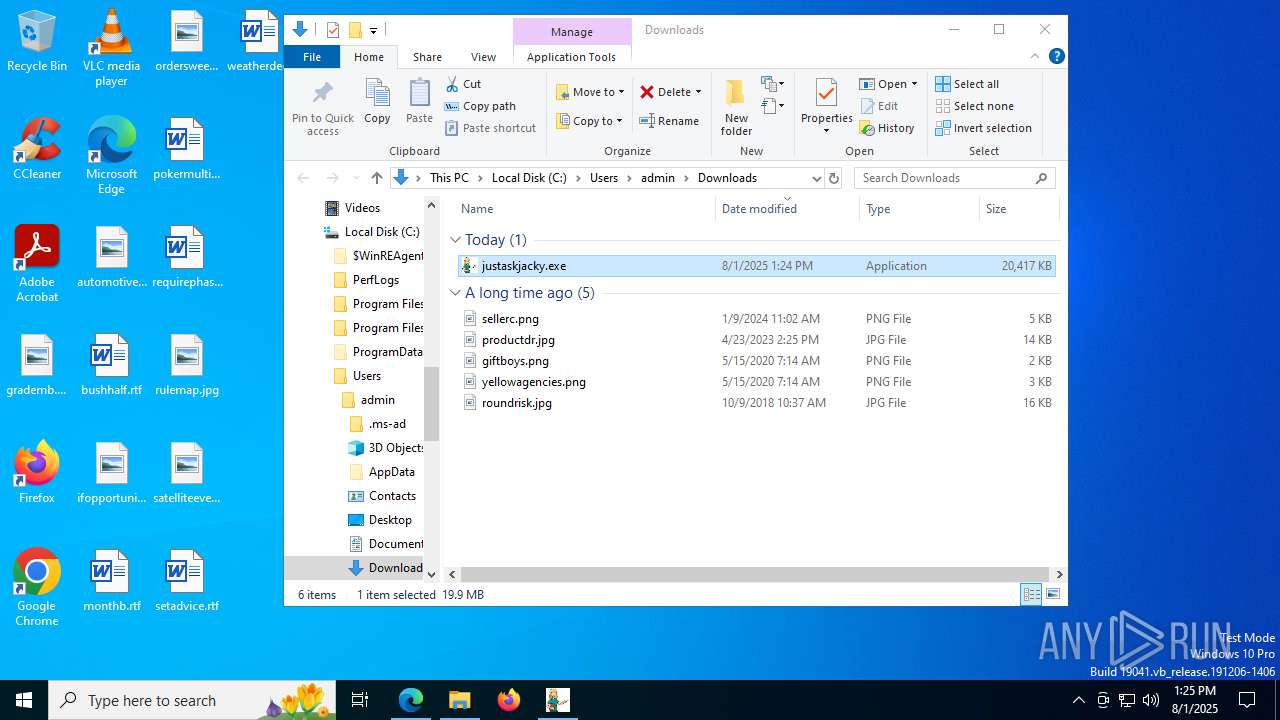
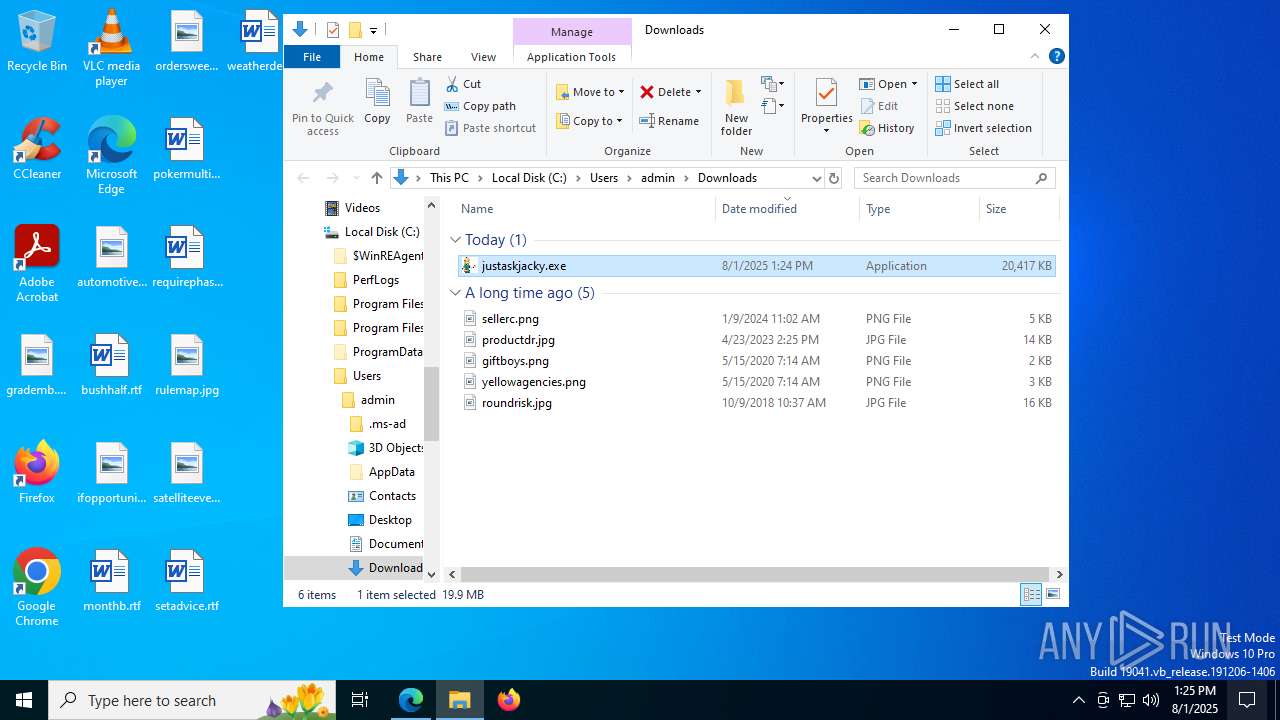
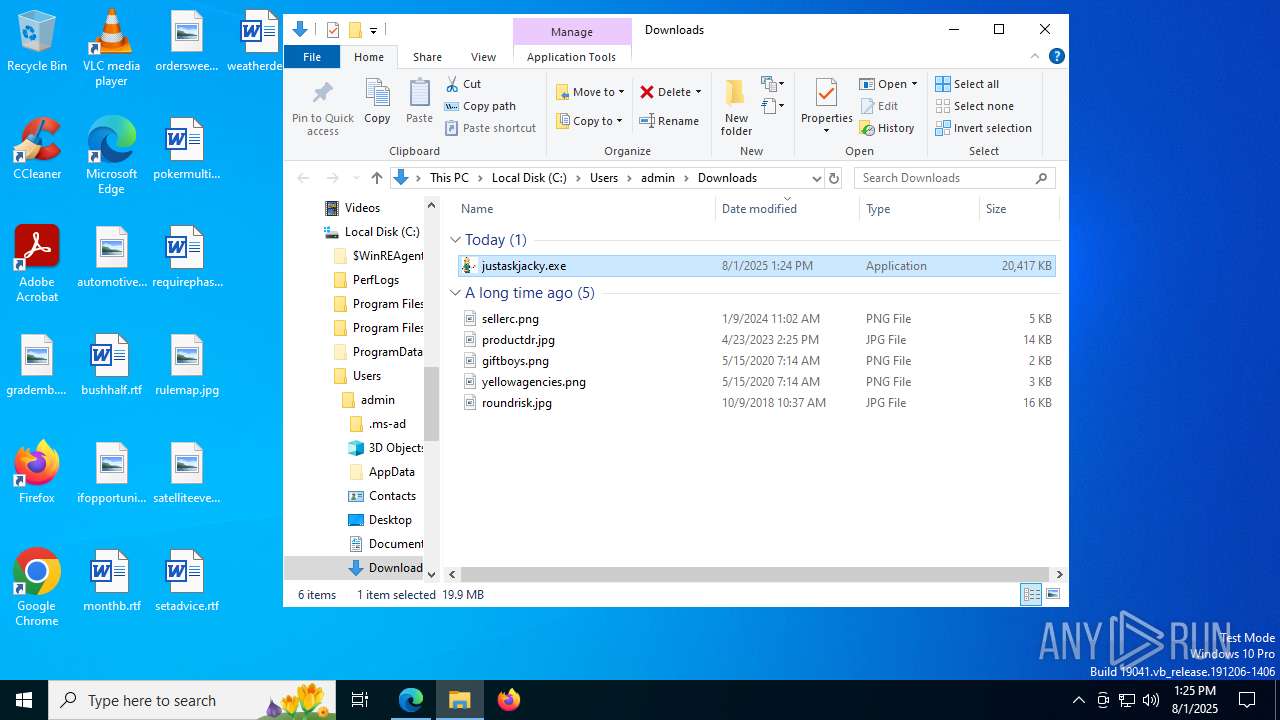
| URL: | https://download.justaskjacky.com:443/d/justaskjacky.exe |
| Full analysis: | https://app.any.run/tasks/f5125bd8-6160-439d-b3d4-827f58e2191a |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 13:22:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 52D1C8783F528A21BDF1145BDBA41373 |
| SHA1: | 231519B5E0C2696F41A1AFF3F1F0E260B67D7E6F |
| SHA256: | 6E108E288899F21FE74DE939B3719EF7DCE3E65ACA38F7670643EA7AFC41B1BA |
| SSDEEP: | 3:N8SEloVXO6dim5DEXO6N:2SKAeljeO |
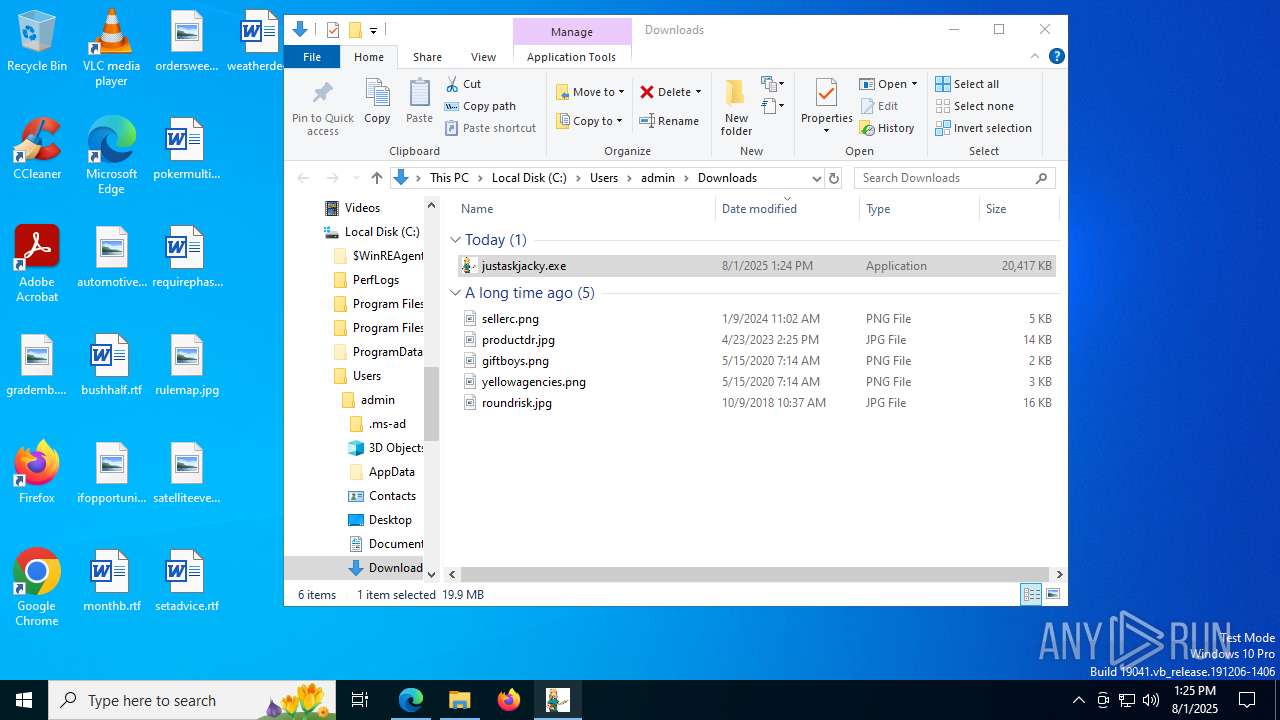
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1036)
SUSPICIOUS
Creates file in the systems drive root
- explorer.exe (PID: 4772)
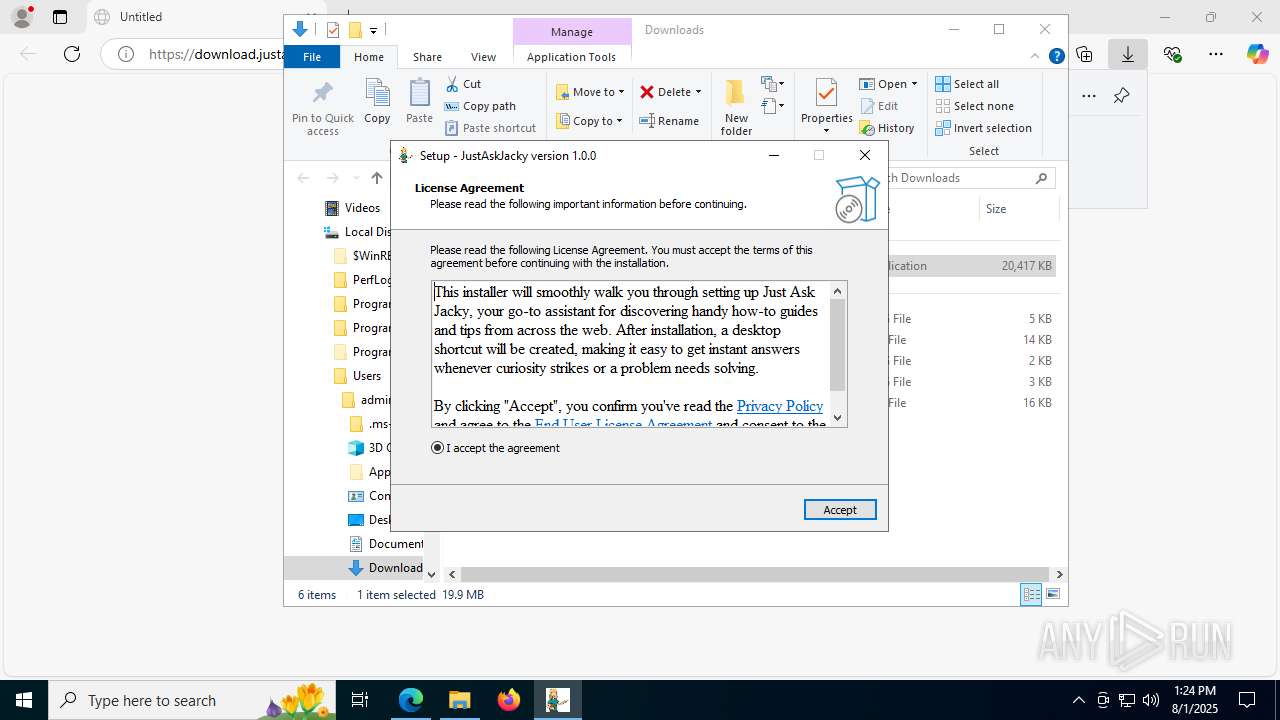
Reads the Windows owner or organization settings
- justaskjacky.tmp (PID: 7688)
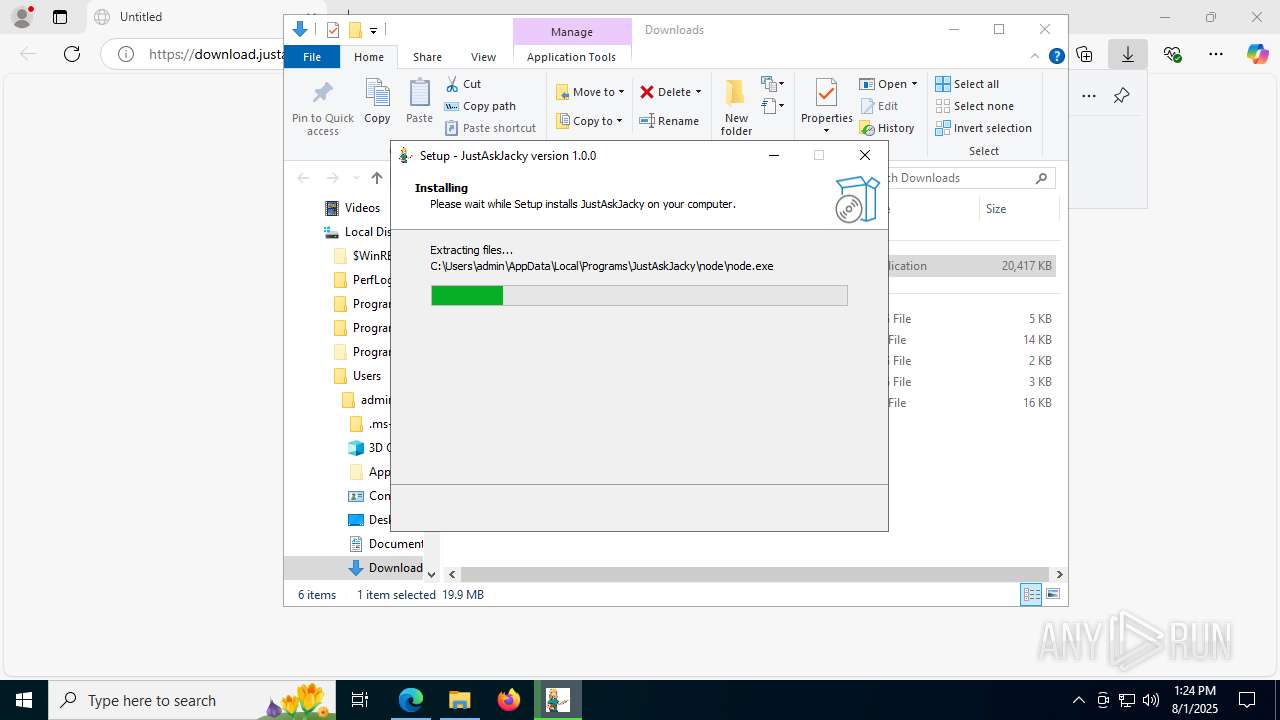
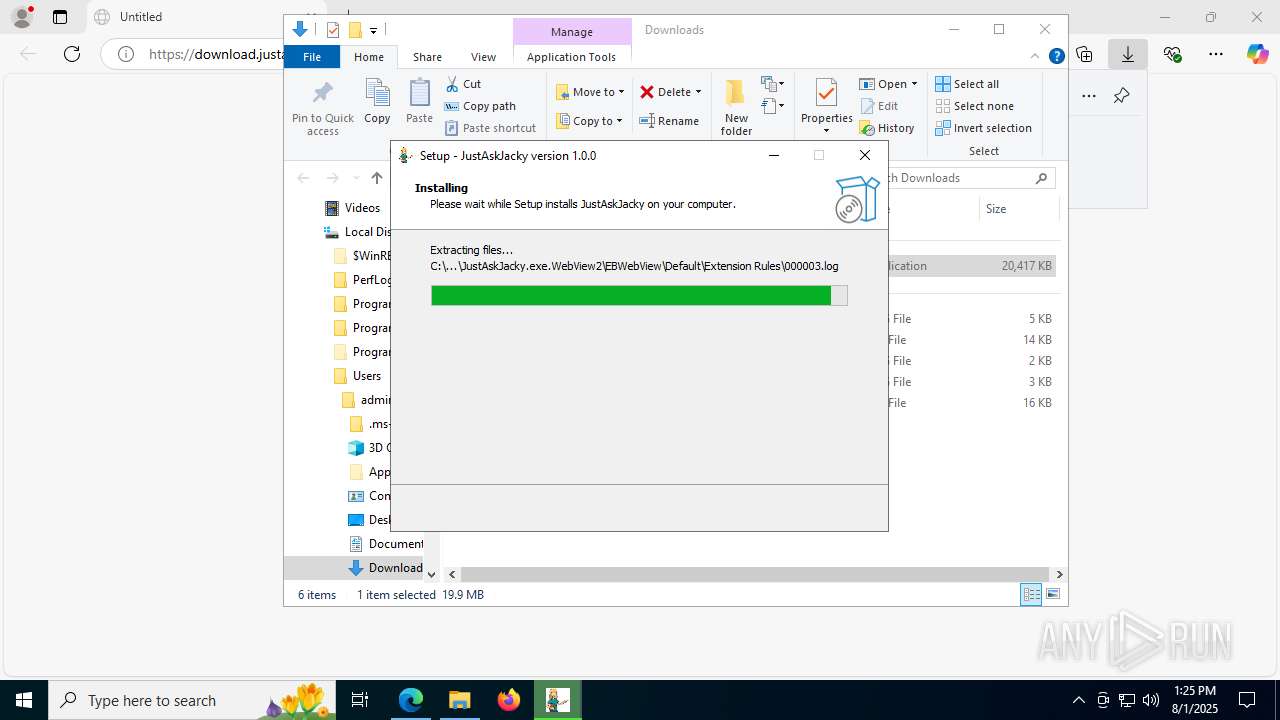
Executable content was dropped or overwritten
- justaskjacky.exe (PID: 7544)
- justaskjacky.tmp (PID: 7688)
Process drops legitimate windows executable
- justaskjacky.tmp (PID: 7688)
Executes script using NodeJS
- node.exe (PID: 5284)
The process executes via Task Scheduler
- cmd.exe (PID: 8036)
- updater.exe (PID: 3052)
Reads security settings of Internet Explorer
- justaskjacky.tmp (PID: 7688)
- ShellExperienceHost.exe (PID: 5600)
Starts CMD.EXE for commands execution
- node.exe (PID: 5284)
- justaskjacky.tmp (PID: 7688)
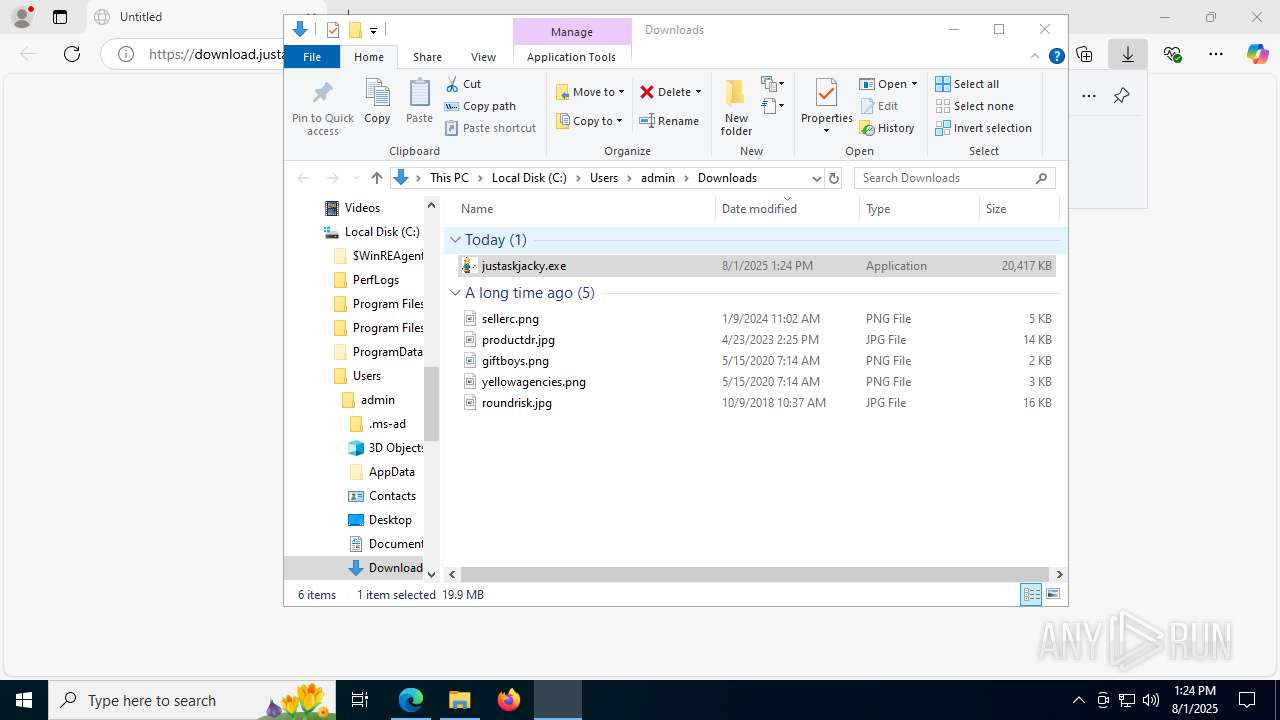
Application launched itself
- updater.exe (PID: 3052)
Executes application which crashes
- JustAskJacky.exe (PID: 1332)
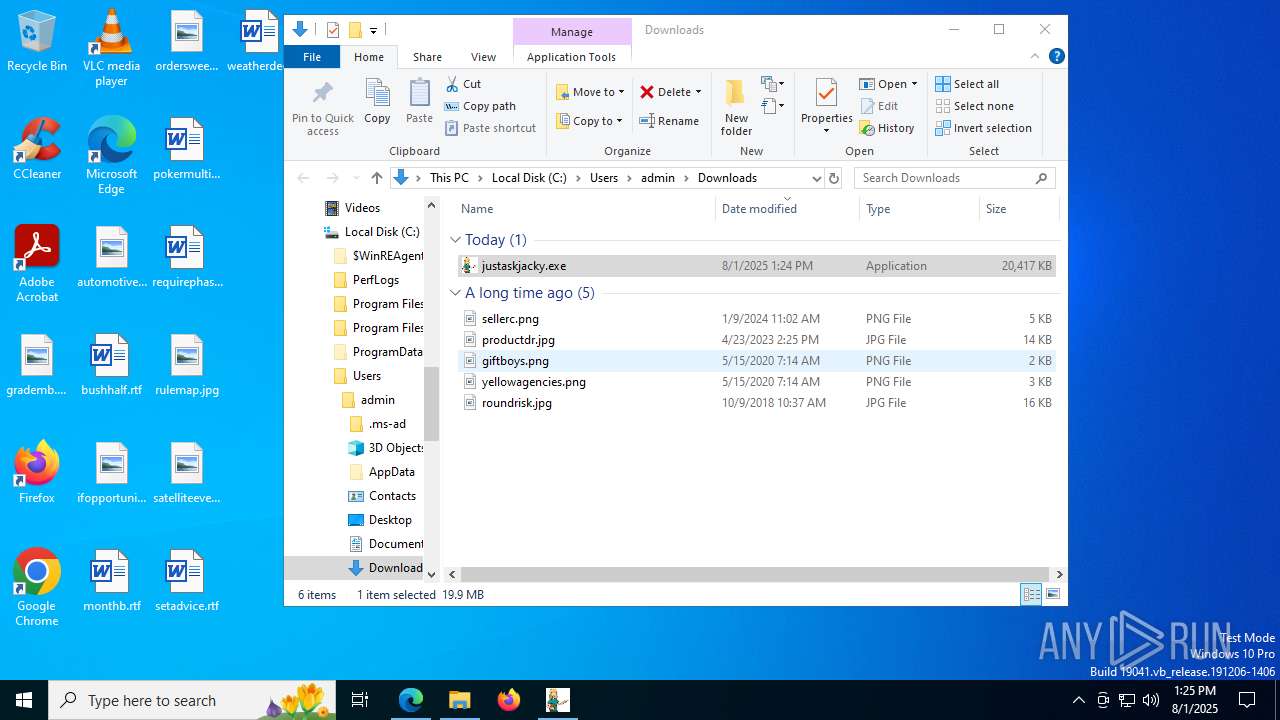
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 1056)
Application launched itself
- msedge.exe (PID: 1056)
- msedge.exe (PID: 5928)
- firefox.exe (PID: 7096)
- firefox.exe (PID: 3460)
Reads Environment values
- identity_helper.exe (PID: 7676)
- node.exe (PID: 5284)
- identity_helper.exe (PID: 8492)
Reads the software policy settings
- slui.exe (PID: 7900)
- explorer.exe (PID: 4772)
- justaskjacky.tmp (PID: 7688)
- WerFault.exe (PID: 3628)
Checks supported languages
- identity_helper.exe (PID: 7676)
- justaskjacky.exe (PID: 7544)
- justaskjacky.tmp (PID: 7688)
- JustAskJacky.exe (PID: 1332)
- node.exe (PID: 5284)
- ShellExperienceHost.exe (PID: 5600)
- updater.exe (PID: 3052)
- updater.exe (PID: 7628)
- identity_helper.exe (PID: 8492)
Reads the computer name
- identity_helper.exe (PID: 7676)
- JustAskJacky.exe (PID: 1332)
- justaskjacky.tmp (PID: 7688)
- ShellExperienceHost.exe (PID: 5600)
- node.exe (PID: 5284)
- updater.exe (PID: 3052)
- identity_helper.exe (PID: 8492)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4772)
Checks proxy server information
- slui.exe (PID: 7900)
- explorer.exe (PID: 4772)
- WerFault.exe (PID: 3628)
Creates files or folders in the user directory
- explorer.exe (PID: 4772)
- justaskjacky.tmp (PID: 7688)
- node.exe (PID: 5284)
- WerFault.exe (PID: 3628)
Create files in a temporary directory
- justaskjacky.tmp (PID: 7688)
- justaskjacky.exe (PID: 7544)
Compiled with Borland Delphi (YARA)
- justaskjacky.exe (PID: 7544)
- justaskjacky.tmp (PID: 7688)
Creates a software uninstall entry
- justaskjacky.tmp (PID: 7688)
Reads the machine GUID from the registry
- justaskjacky.tmp (PID: 7688)
- JustAskJacky.exe (PID: 1332)
Detects InnoSetup installer (YARA)
- justaskjacky.exe (PID: 7544)
- justaskjacky.tmp (PID: 7688)
The sample compiled with english language support
- justaskjacky.tmp (PID: 7688)
Reads product name
- node.exe (PID: 5284)
Process checks whether UAC notifications are on
- updater.exe (PID: 3052)
Reads Microsoft Office registry keys
- firefox.exe (PID: 7096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
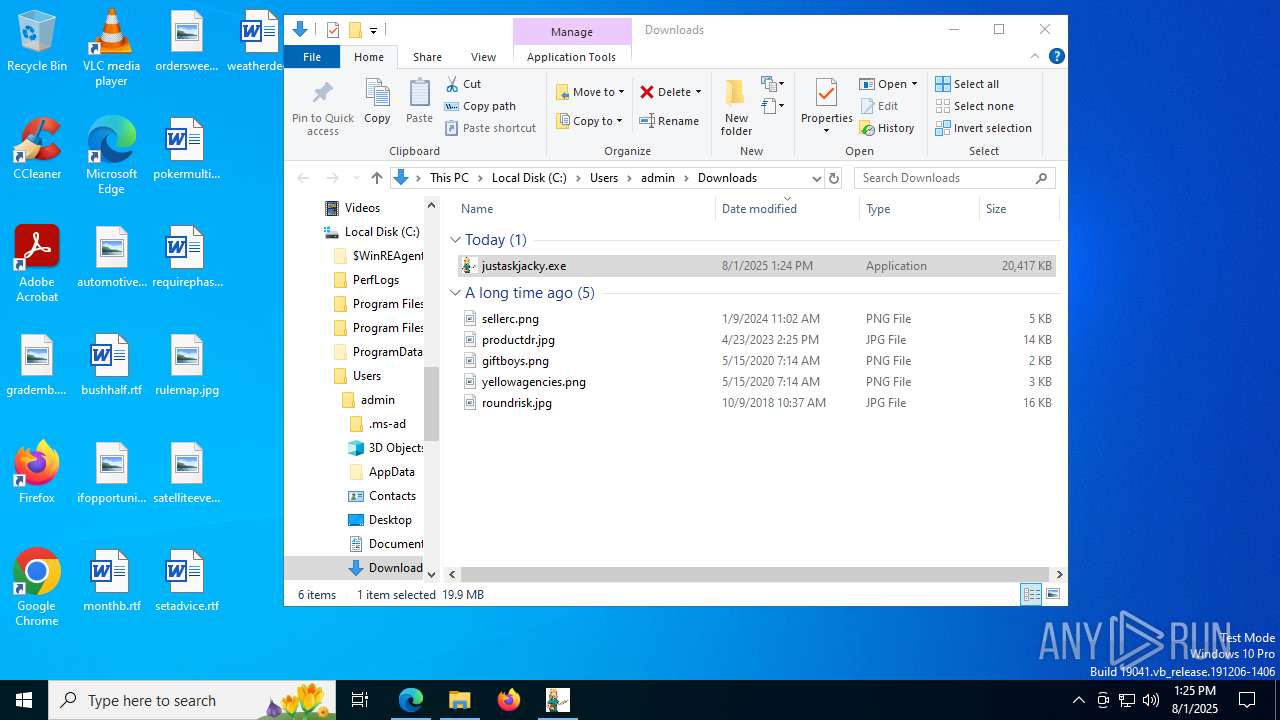
Total processes
235
Monitored processes
81
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3604,i,505508588807169003,184926490401684740,262144 --variations-seed-version --mojo-platform-channel-handle=3664 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7644,i,505508588807169003,184926490401684740,262144 --variations-seed-version --mojo-platform-channel-handle=5736 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4908 -prefsLen 39068 -prefMapHandle 5116 -prefMapSize 272997 -jsInitHandle 5112 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3884 -initialChannelId {65db6775-4ffa-4ac6-b164-b96e160cba7e} -parentPid 7096 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7096" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 9 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1036 | "C:\WINDOWS\system32\cmd.exe" /C schtasks /Create /tn "fb2a691d-bf5c-4660-abd3-bca584c85782" /xml "C:\Users\admin\AppData\Local\Temp\is-MIMQC.tmp\task.xml" | C:\Windows\SysWOW64\cmd.exe | — | justaskjacky.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
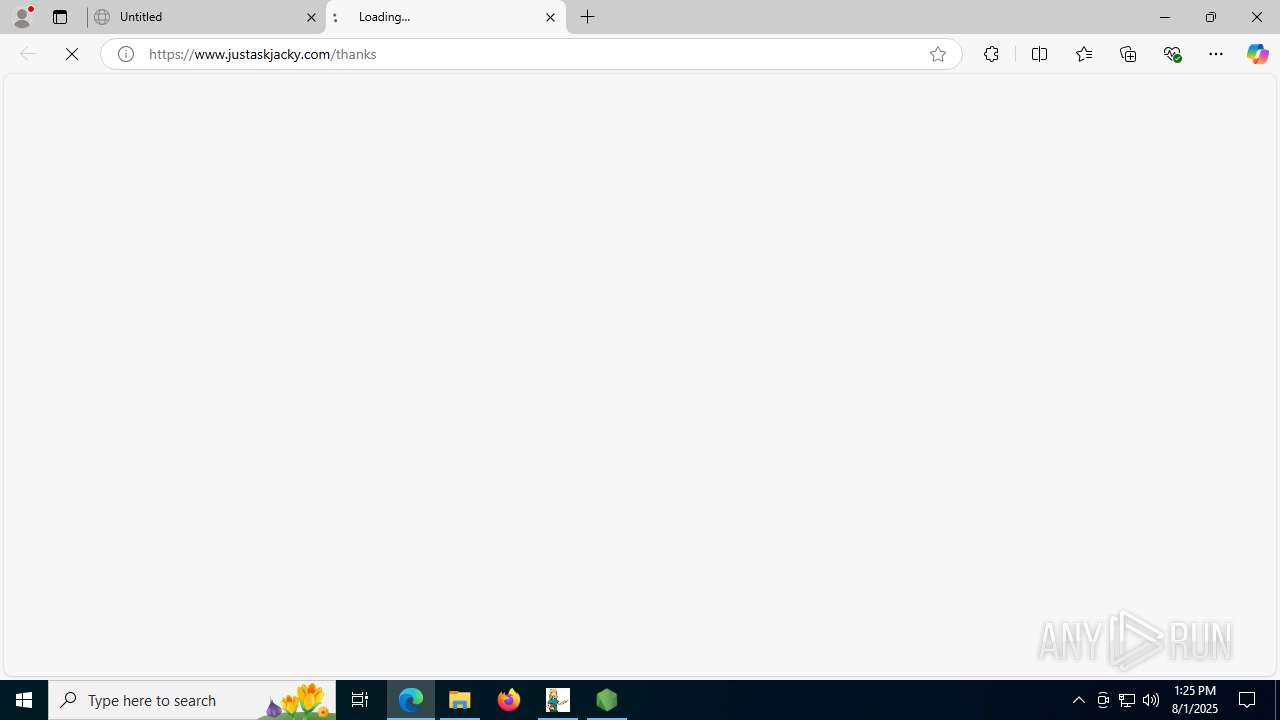
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --edge-skip-compat-layer-relaunch --single-argument https://www.justaskjacky.com/thanks | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://download.justaskjacky.com:443/d/justaskjacky.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4320,i,505508588807169003,184926490401684740,262144 --variations-seed-version --mojo-platform-channel-handle=4336 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | "C:\Users\admin\AppData\Local\Programs\JustAskJacky\JustAskJacky.exe" | C:\Users\admin\AppData\Local\Programs\JustAskJacky\JustAskJacky.exe | justaskjacky.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Description: JustAskJacky Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2752,i,505508588807169003,184926490401684740,262144 --variations-seed-version --mojo-platform-channel-handle=2356 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
37 101
Read events
36 971
Write events
124
Delete events
6
Modification events
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 49C26EEEE3992F00 | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1835042 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AE11BCFE-F471-41C6-A4C4-EE7637067B37} | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (1056) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\1835042 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {94752024-C76B-45B2-BAA0-C2A46001E28D} | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000001C0022 |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000A030A |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
Executable files
23
Suspicious files
474
Text files
225
Unknown types
357
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d28d.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18d29d.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d29d.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d2ac.TMP | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1056 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d2bc.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
145
DNS requests
208
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3836 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:CHyszwCMAYga32X3xY-x-G7QcLQP_yRUBz8ib_Dv-aM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
6176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7344 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7344 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4196 | svchost.exe | HEAD | 200 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754482852&P2=404&P3=2&P4=KAQ6aOyJ%2bGMP4LLe0Luzlx7ubV8JIGIFLOC0RxEXzgfhBsAXXUhjORCb4gymjpSuzHGWj2UiZfiBbTsItWu5VQ%3d%3d | unknown | — | — | whitelisted |
4196 | svchost.exe | GET | 200 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1754479254&P2=404&P3=2&P4=Cm3poE8PHjTBU%2btk%2b47042NQgFE7jq%2fbZOq3Oqii7ZI%2bHW6eFwSWuh0DBmOKBtQs2q1NjaL456l7K6OGij6KUQ%3d%3d | unknown | — | — | whitelisted |
4196 | svchost.exe | GET | 206 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754482852&P2=404&P3=2&P4=KAQ6aOyJ%2bGMP4LLe0Luzlx7ubV8JIGIFLOC0RxEXzgfhBsAXXUhjORCb4gymjpSuzHGWj2UiZfiBbTsItWu5VQ%3d%3d | unknown | — | — | whitelisted |
4196 | svchost.exe | GET | 206 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754482852&P2=404&P3=2&P4=KAQ6aOyJ%2bGMP4LLe0Luzlx7ubV8JIGIFLOC0RxEXzgfhBsAXXUhjORCb4gymjpSuzHGWj2UiZfiBbTsItWu5VQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6312 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3836 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3836 | msedge.exe | 142.250.185.225:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
3836 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3836 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3836 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
download.justaskjacky.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3836 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
JustAskJacky.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|