| File name: | inetlock.exe |
| Full analysis: | https://app.any.run/tasks/4f63455c-d09f-4e7b-a9b1-54a404a67385 |
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2020, 00:03:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | FF6609A96DA1C2B36CC53EB10ADF4314 |
| SHA1: | 706062E7623EA6FBF5B5AF636DF16B157E206B69 |
| SHA256: | 6E0F868378E2C0C113540856F9F55CD6A7AF90AE92604E4CF3CB46B4F08145AF |
| SSDEEP: | 12288:En9fJDaQ/Lm4eKJVp9WkZ+aRJc3Gh2L0NvRMHVFamE1oao0BavdyIZdN3Pzbq:E904Lm4eapQuc3Gh2L0NZMHiUOqLZP7G |
MALICIOUS
Loads dropped or rewritten executable
- inetlock.exe (PID: 4040)
Application was dropped or rewritten from another process
- ILSvc.exe (PID: 864)
- ILSvc.exe (PID: 1508)
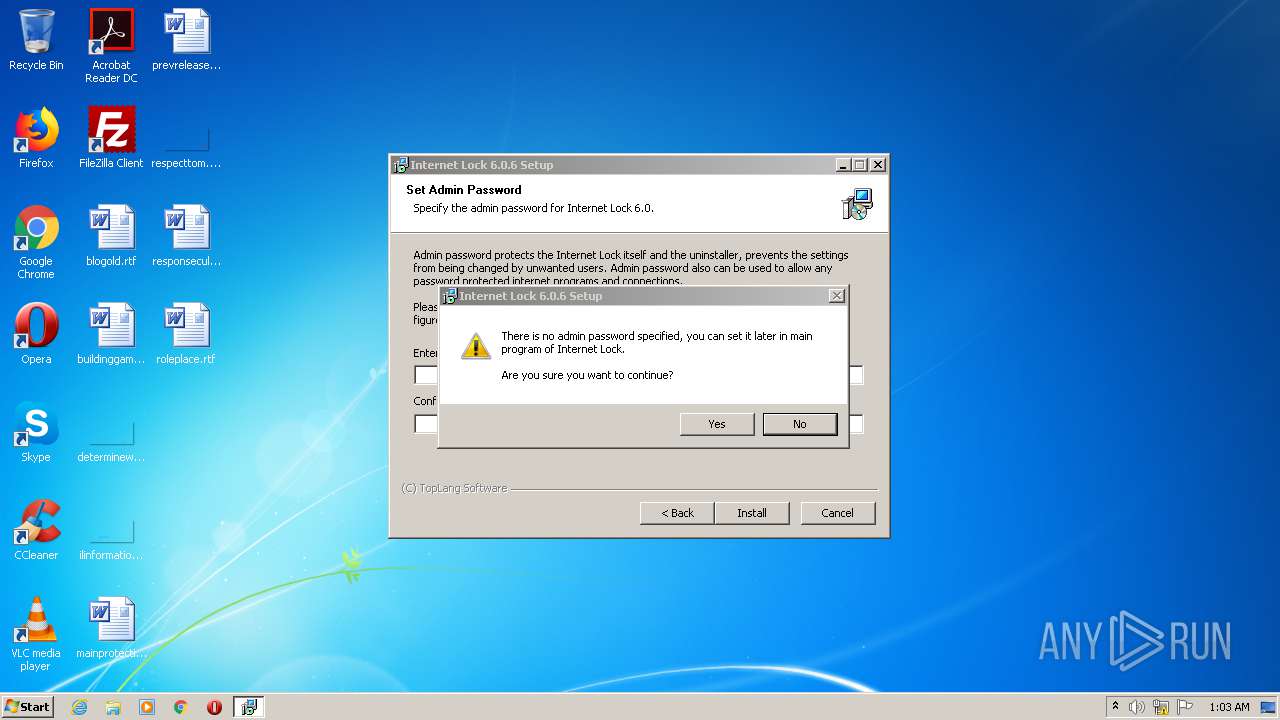
Changes settings of System certificates
- inetlock.exe (PID: 4040)
SUSPICIOUS
Creates files in the Windows directory
- inetlock.exe (PID: 4040)
Executable content was dropped or overwritten
- inetlock.exe (PID: 4040)
Creates a software uninstall entry
- inetlock.exe (PID: 4040)
Creates files in the driver directory
- inetlock.exe (PID: 4040)
Creates files in the program directory
- inetlock.exe (PID: 4040)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.6.1 |
| ProductVersionNumber: | 6.0.6.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | TopLang software |
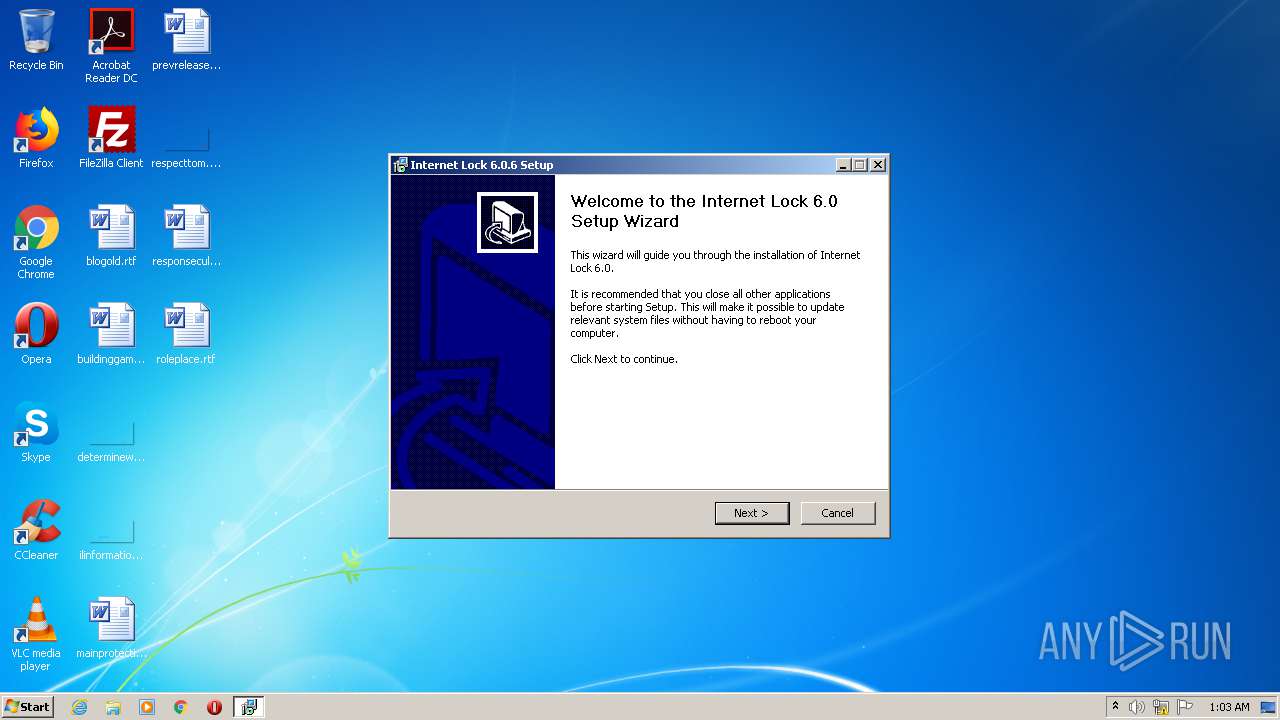
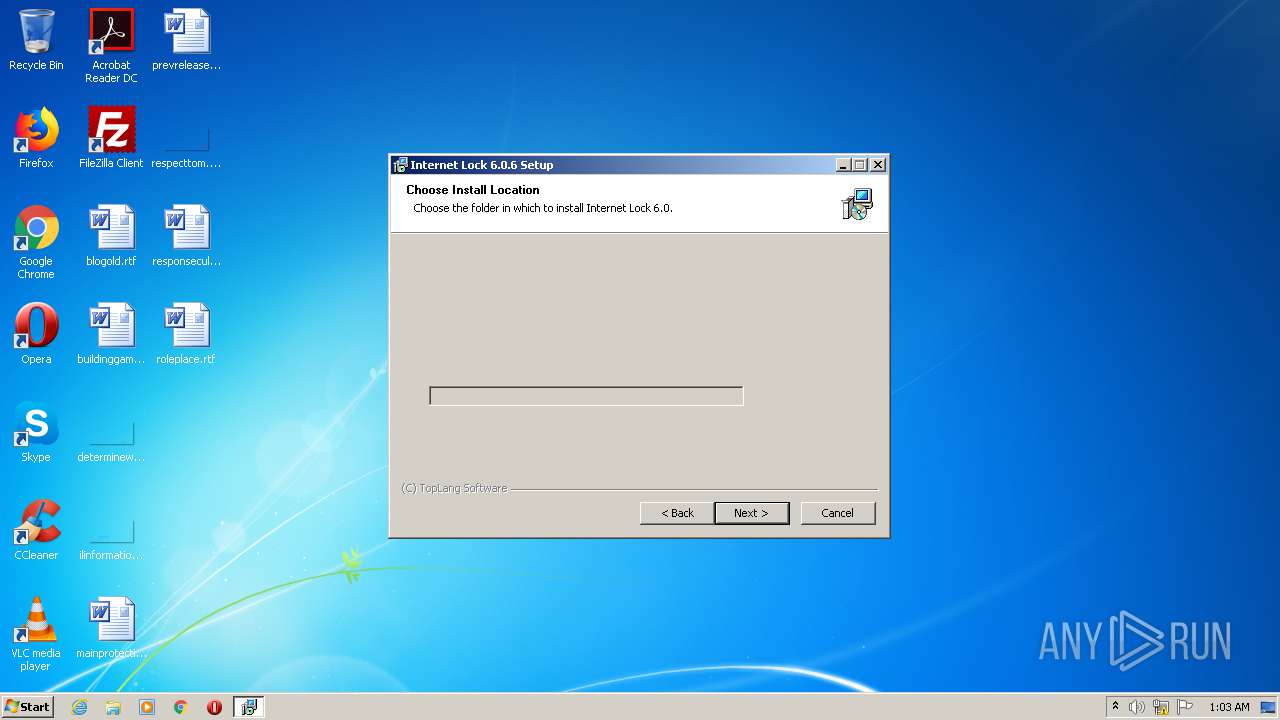
| FileDescription: | Internet Lock 6.0.6 Setup |
| FileVersion: | 6.0.6 |
| LegalCopyright: | Copyright (C) TopLang software |
| ProductName: | Internet Lock |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| CompanyName: | TopLang software |
| FileDescription: | Internet Lock 6.0.6 Setup |
| FileVersion: | 6.0.6 |
| LegalCopyright: | Copyright (C) TopLang software |
| ProductName: | Internet Lock |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00015000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00039000 | 0x00001F38 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.23386 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 3.25755 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.21733 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 3.12946 | 218 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
45
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Users\admin\AppData\Local\Temp\ILSvc.exe" /precheck | C:\Users\admin\AppData\Local\Temp\ILSvc.exe | — | inetlock.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Internet Lock\ILSvc.exe" /inst | C:\Program Files\Internet Lock\ILSvc.exe | — | inetlock.exe | |||||||||||
User: admin Company: TopLang Software Integrity Level: HIGH Description: Internet Lock Service Exit code: 0 Version: 6, 0, 6, 1 Modules
| |||||||||||||||
| 2636 | "C:\Users\admin\AppData\Local\Temp\inetlock.exe" | C:\Users\admin\AppData\Local\Temp\inetlock.exe | — | explorer.exe | |||||||||||
User: admin Company: TopLang software Integrity Level: MEDIUM Description: Internet Lock 6.0.6 Setup Exit code: 3221226540 Version: 6.0.6 Modules
| |||||||||||||||
| 4040 | "C:\Users\admin\AppData\Local\Temp\inetlock.exe" | C:\Users\admin\AppData\Local\Temp\inetlock.exe | explorer.exe | ||||||||||||
User: admin Company: TopLang software Integrity Level: HIGH Description: Internet Lock 6.0.6 Setup Exit code: 0 Version: 6.0.6 Modules
| |||||||||||||||
Total events
360
Read events
349
Write events
11
Delete events
0
Modification events
| (PID) Process: | (4040) inetlock.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\24B87352038431C8D89DB9C73813E6D9ACC17CED |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000024B87352038431C8D89DB9C73813E6D9ACC17CED2000000001000000E6020000308202E23082024BA0030201020210D6A4C22F4A7C89AC4A3C46AC7205A72B300D06092A864886F70D0101040500305A31193017060355040A1310546F704C616E6720536F6674776172653122302006092A864886F70D0109011613737570706F727440746F706C616E672E636F6D3119301706035504031310546F704C616E6720536F667477617265301E170D3131313232343037343232395A170D3339313233313233353935395A305A31193017060355040A1310546F704C616E6720536F6674776172653122302006092A864886F70D0109011613737570706F727440746F706C616E672E636F6D3119301706035504031310546F704C616E6720536F66747761726530819F300D06092A864886F70D010101050003818D0030818902818100906F91477F3831C47984D7412BBE517294722CBB9AA5D157DDD973FB22B21B700E6AFC51D54B550E4D07DCD02E1876B0A70C0D2299682C2C55F051F8AF6F31D1EBD2A213499592654392929A14F78F4C65C9BE5EA52E40293071906F852C380753BADD9DB7E64555F5C57F16CC2BD5D293B369E9250CF84569A15CA1021F7D330203010001A381A83081A530130603551D25040C300A06082B0601050507030330818D0603551D0104818530818280104FE0FB0BB21E437792568FDF2B35A37CA15C305A31193017060355040A1310546F704C616E6720536F6674776172653122302006092A864886F70D0109011613737570706F727440746F706C616E672E636F6D3119301706035504031310546F704C616E6720536F6674776172658210D6A4C22F4A7C89AC4A3C46AC7205A72B300D06092A864886F70D01010405000381810040A10C1C56E3CBF01D22EDB12B45410A5BC6F31BEB6F225B3AD2CC1DF5C4B9E42E0468414217B64C9333593C683509F93EA4ADC8E8A791FD4E5DF13B530B8A3A4201550A32936B2B0CA10038899CC1FCD22EE5ACD26A224EC725D0C60783C886B40881F3A210B791DAE585493DA6CB86C92AF8BE7BD5352E99F2E715DD94F296 | |||
| (PID) Process: | (4040) inetlock.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Internet Lock |
| Operation: | write | Name: | DisplayName |
Value: Internet Lock 6.0 | |||
| (PID) Process: | (4040) inetlock.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Internet Lock |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Internet Lock\uninst.exe | |||
| (PID) Process: | (4040) inetlock.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Internet Lock |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Internet Lock\InetLock.exe | |||
| (PID) Process: | (4040) inetlock.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Internet Lock |
| Operation: | write | Name: | DisplayVersion |
Value: 6.0 | |||
| (PID) Process: | (4040) inetlock.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Internet Lock |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.toplang.com | |||
| (PID) Process: | (4040) inetlock.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Internet Lock |
| Operation: | write | Name: | Publisher |
Value: TopLang software | |||
| (PID) Process: | (4040) inetlock.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\InetLock.exe |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Internet Lock\InetLock.exe | |||
| (PID) Process: | (4040) inetlock.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\TopLang\Internet Lock |
| Operation: | write | Name: | InternalVersion |
Value: 393222 | |||
| (PID) Process: | (1508) ILSvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
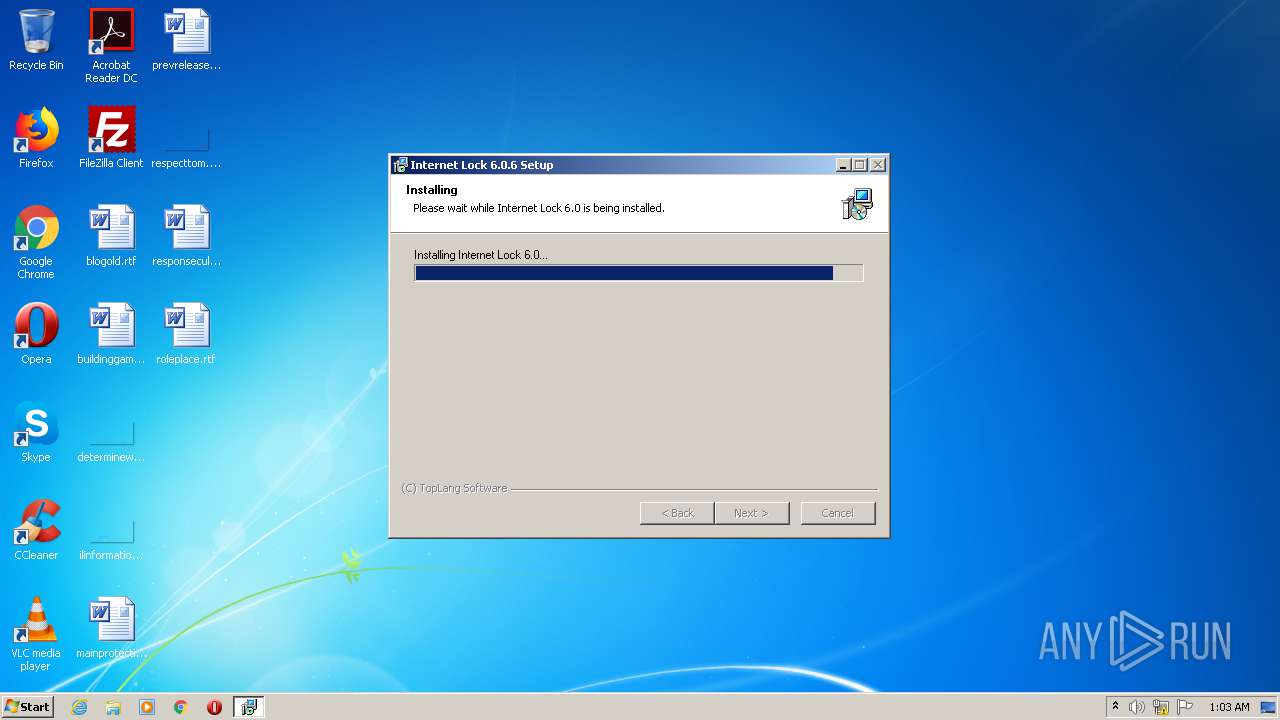
Executable files
7
Suspicious files
1
Text files
10
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | inetlock.exe | C:\Users\admin\AppData\Local\Temp\TLCertTool.dll | — | |
MD5:— | SHA256:— | |||
| 4040 | inetlock.exe | C:\Users\admin\AppData\Local\Temp\ILSvc.exe | executable | |
MD5:8A72D5B647DDB6BE807A0095D58309D9 | SHA256:03D84676CD9CA3D2184093D462D2F9BF42389A6CA817C195738D5240CD9DAD2A | |||
| 4040 | inetlock.exe | C:\Windows\inf\InetLock.inf | binary | |
MD5:A4A46B199F18451A26B4F70982BE33F9 | SHA256:F72C1E5FD4B495120ABDC21A27DACF666D6D003E90C8488F036A92953915B2EF | |||
| 4040 | inetlock.exe | C:\Program Files\Internet Lock\License.txt | text | |
MD5:7A58EB2FBAF2B2C200C013739B30F961 | SHA256:E061852B64F8A1D26DB1BA475DE50F406BADCE80EA19174A19CD78175B6D632A | |||
| 4040 | inetlock.exe | C:\Program Files\Internet Lock\Lang\English.ini | text | |
MD5:4480CDDB9476191884E66756B405AA76 | SHA256:4DDDD58074CF4C0CFC7B4F86F2187871733CD5730854D5321EA5571EF6862D38 | |||
| 4040 | inetlock.exe | C:\Users\admin\AppData\Local\Temp\nsk5E2.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 4040 | inetlock.exe | C:\Users\admin\AppData\Local\Temp\nsk5E2.tmp\nsDialogs.dll | executable | |
MD5:C10E04DD4AD4277D5ADC951BB331C777 | SHA256:E31AD6C6E82E603378CB6B80E67D0E0DCD9CF384E1199AC5A65CB4935680021A | |||
| 4040 | inetlock.exe | C:\Program Files\Internet Lock\ILSvc.exe | executable | |
MD5:8A72D5B647DDB6BE807A0095D58309D9 | SHA256:03D84676CD9CA3D2184093D462D2F9BF42389A6CA817C195738D5240CD9DAD2A | |||
| 4040 | inetlock.exe | C:\Program Files\Internet Lock\uninst.exe | executable | |
MD5:9158A7925472DE876F1357B2540D7726 | SHA256:B71D8257DA280E3734DADB73822993A110D75CF132DC502941D746E7D7832F4E | |||
| 4040 | inetlock.exe | C:\Program Files\Internet Lock\Predefined.ini | text | |
MD5:FE230A68F8966063A0B77D4FDD90A399 | SHA256:EA4DFE27E89238F982ABF96054431F62314C0AC03887715E9870D019A2412804 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report