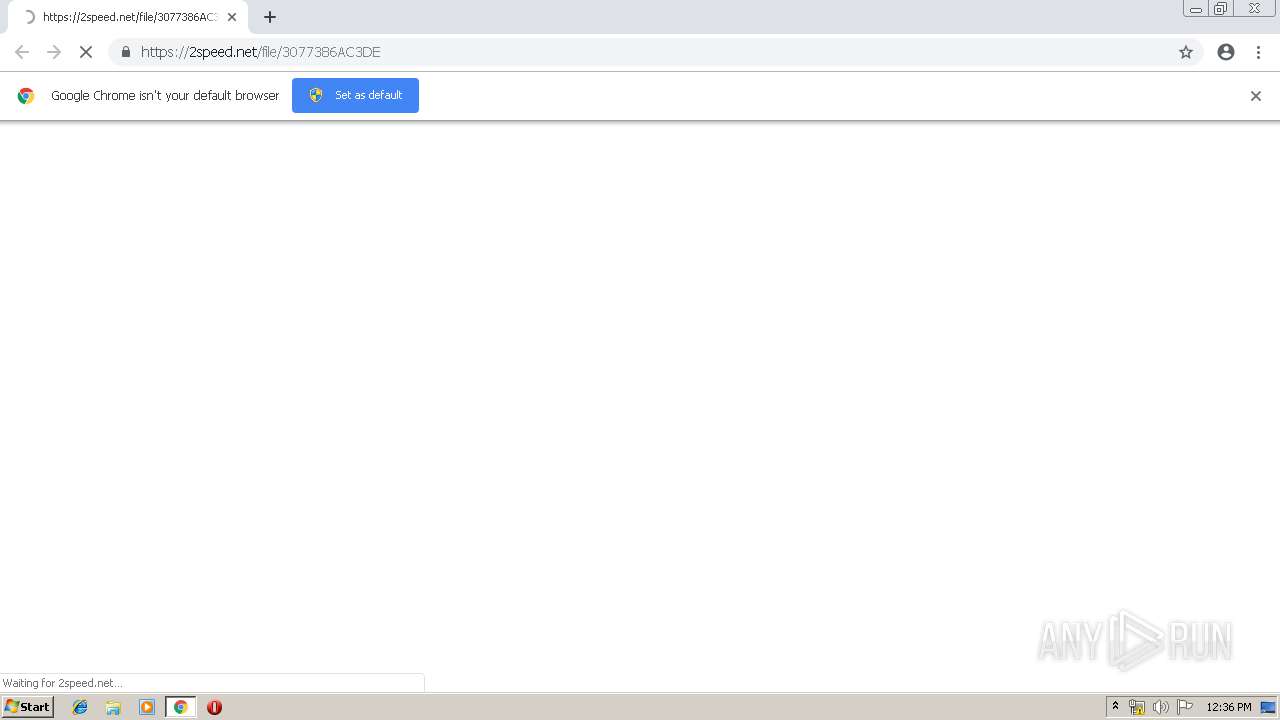
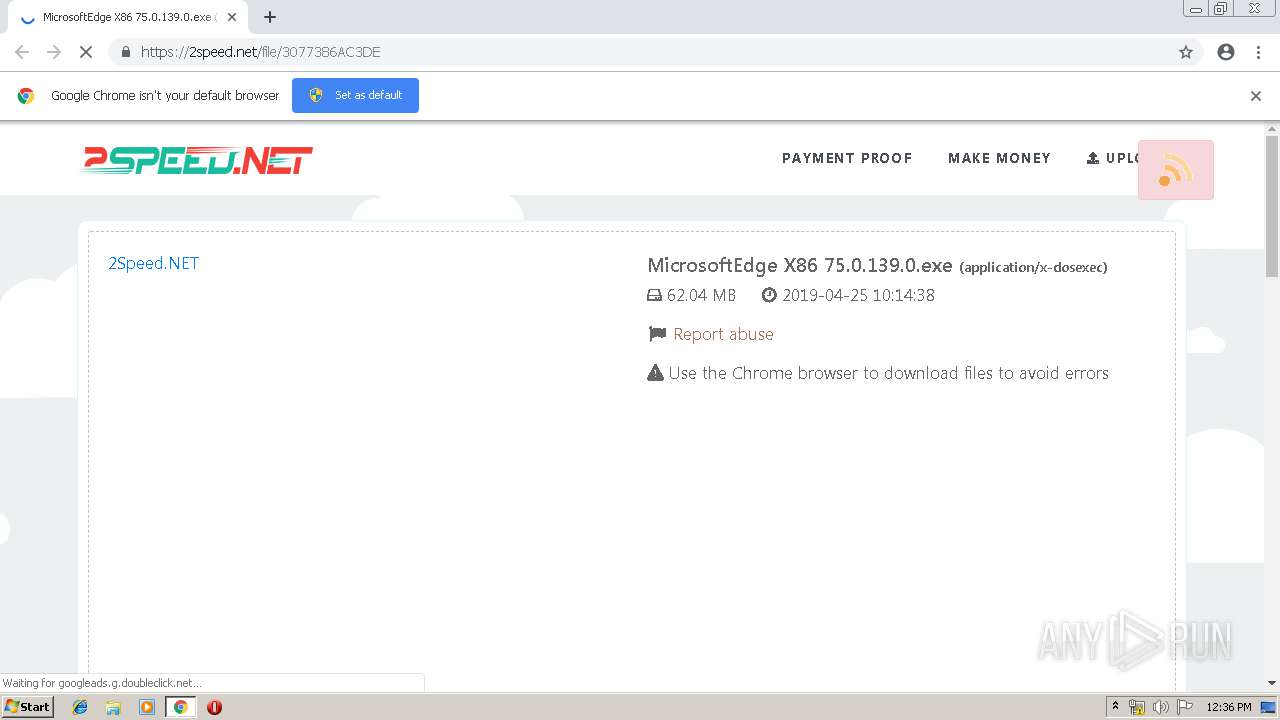
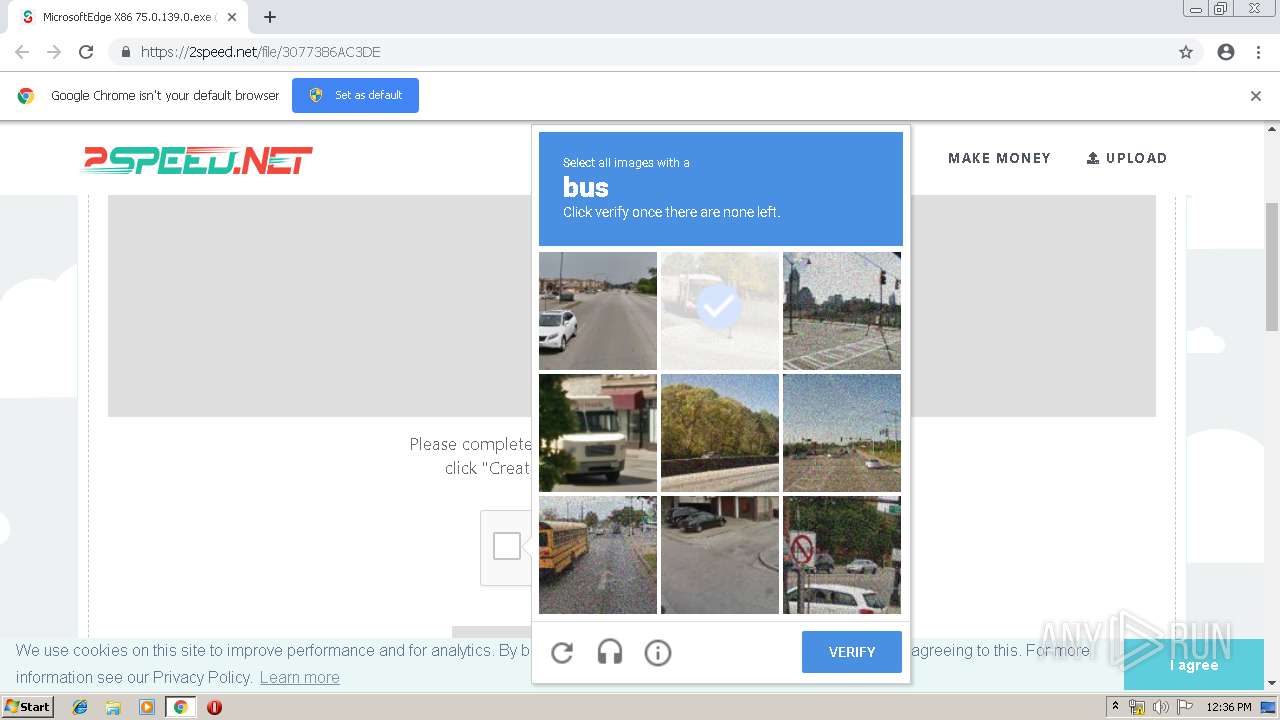
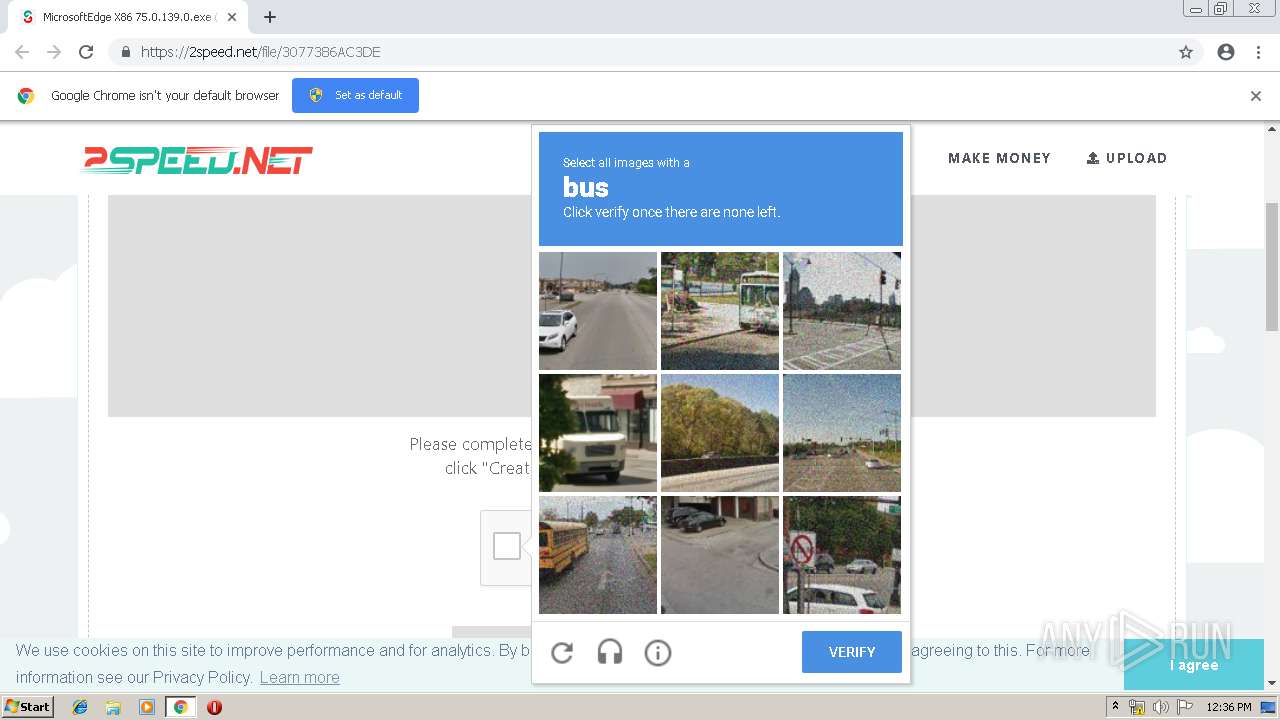
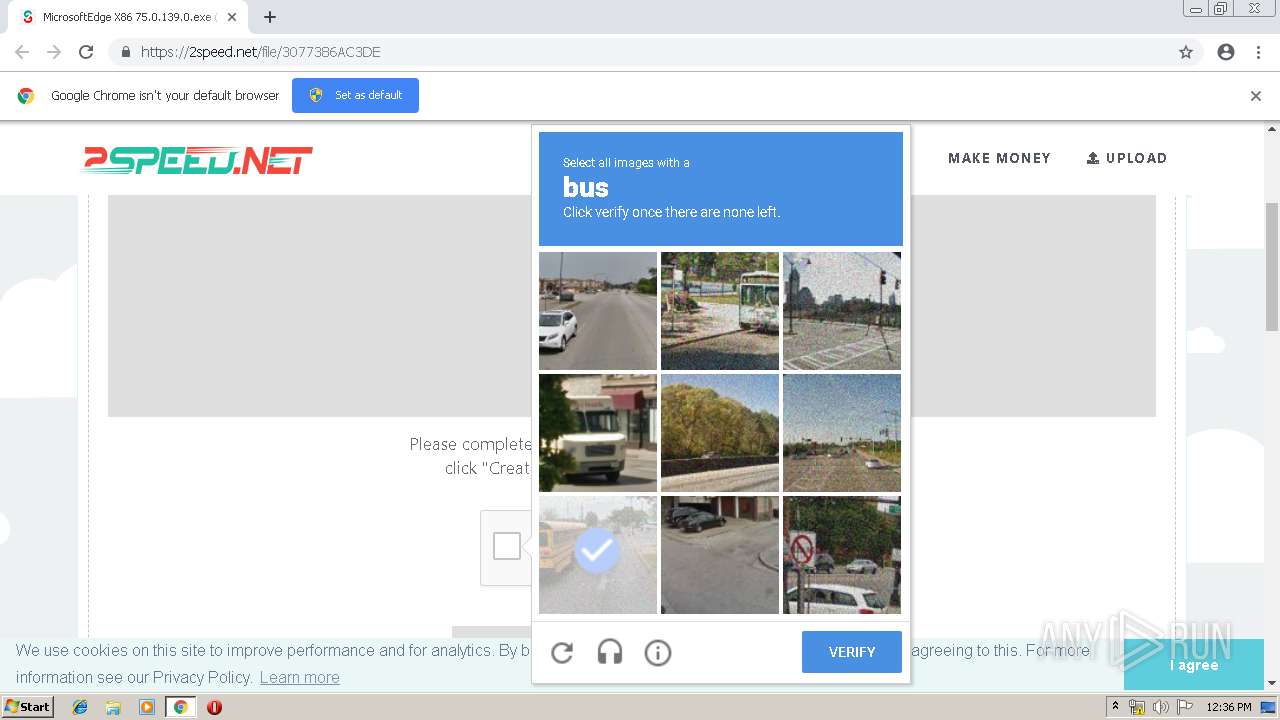
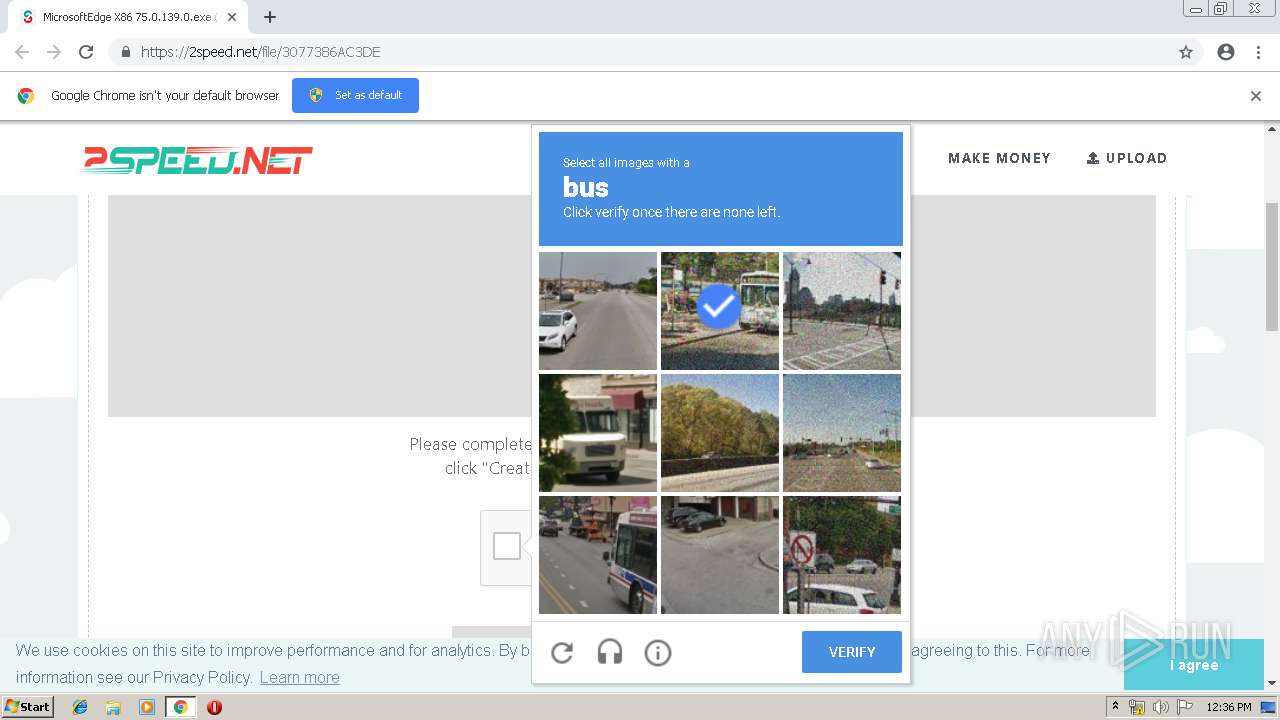
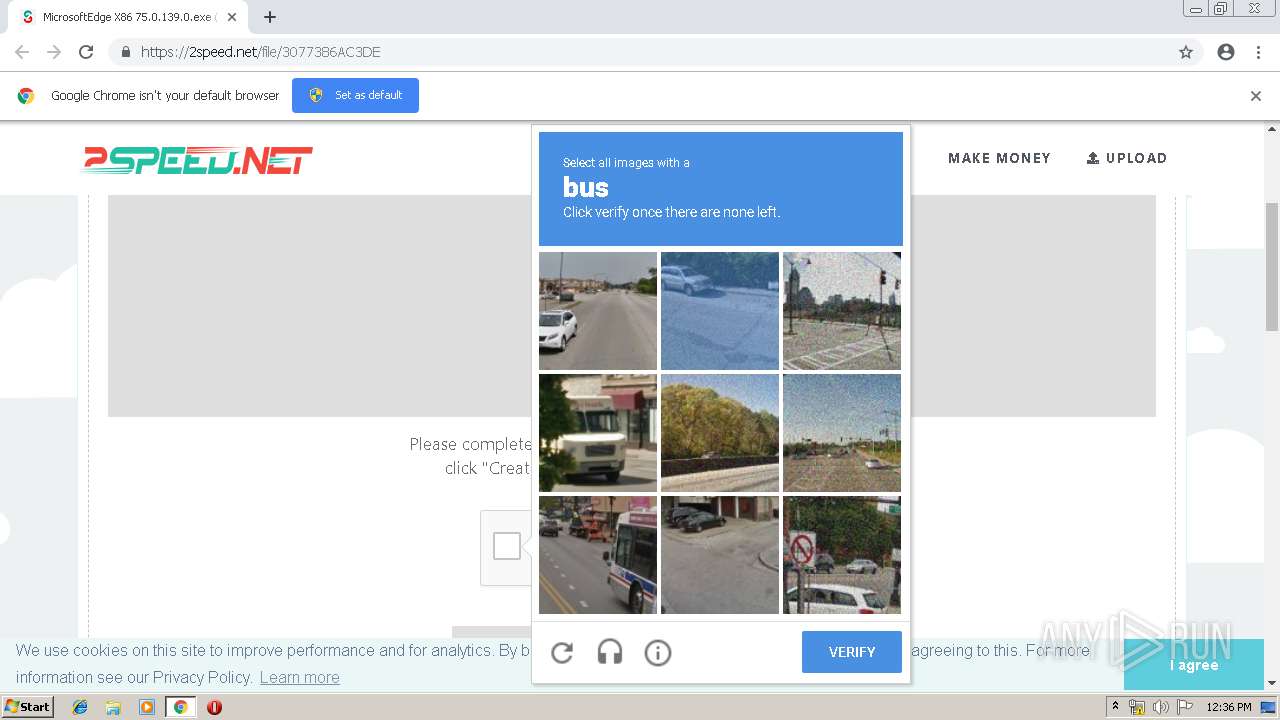
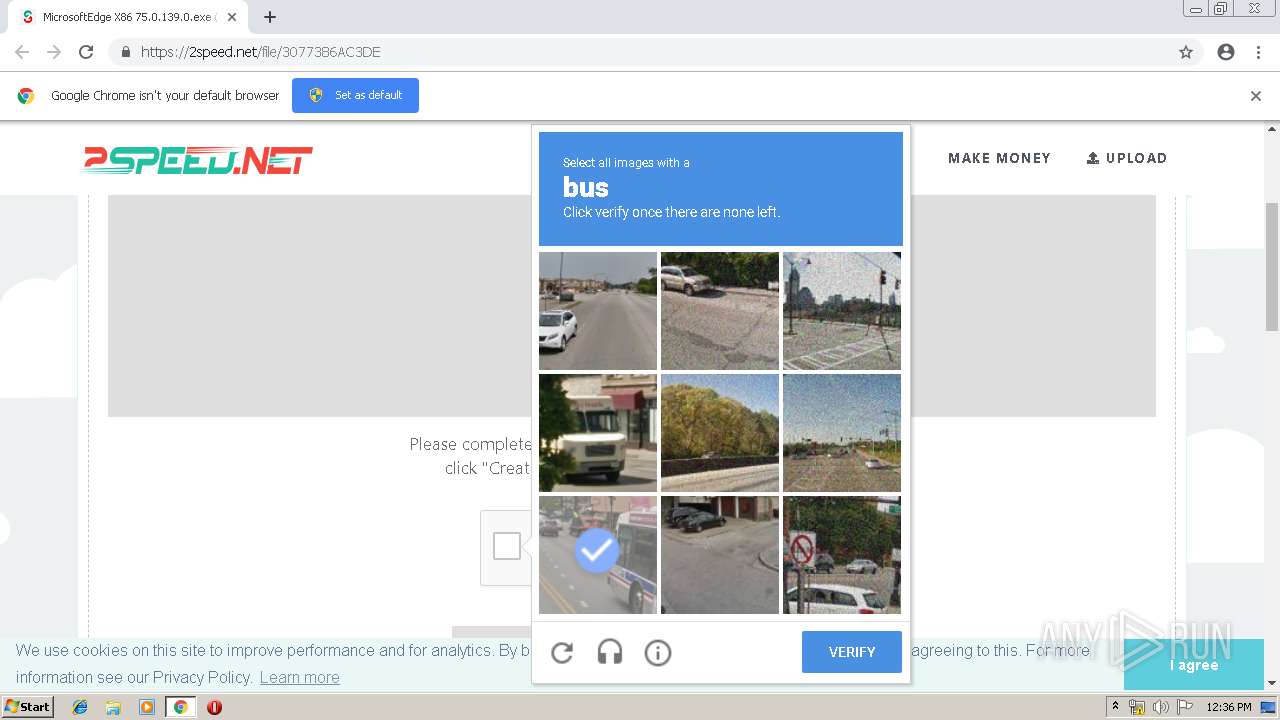
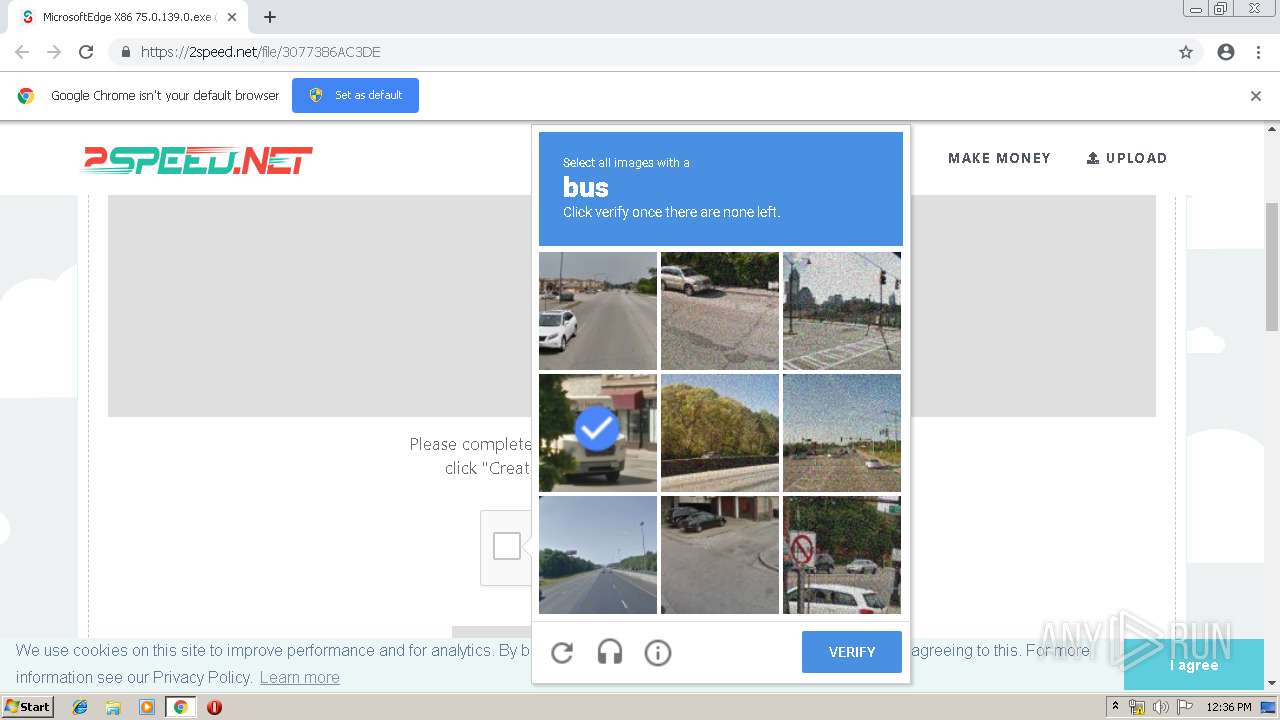
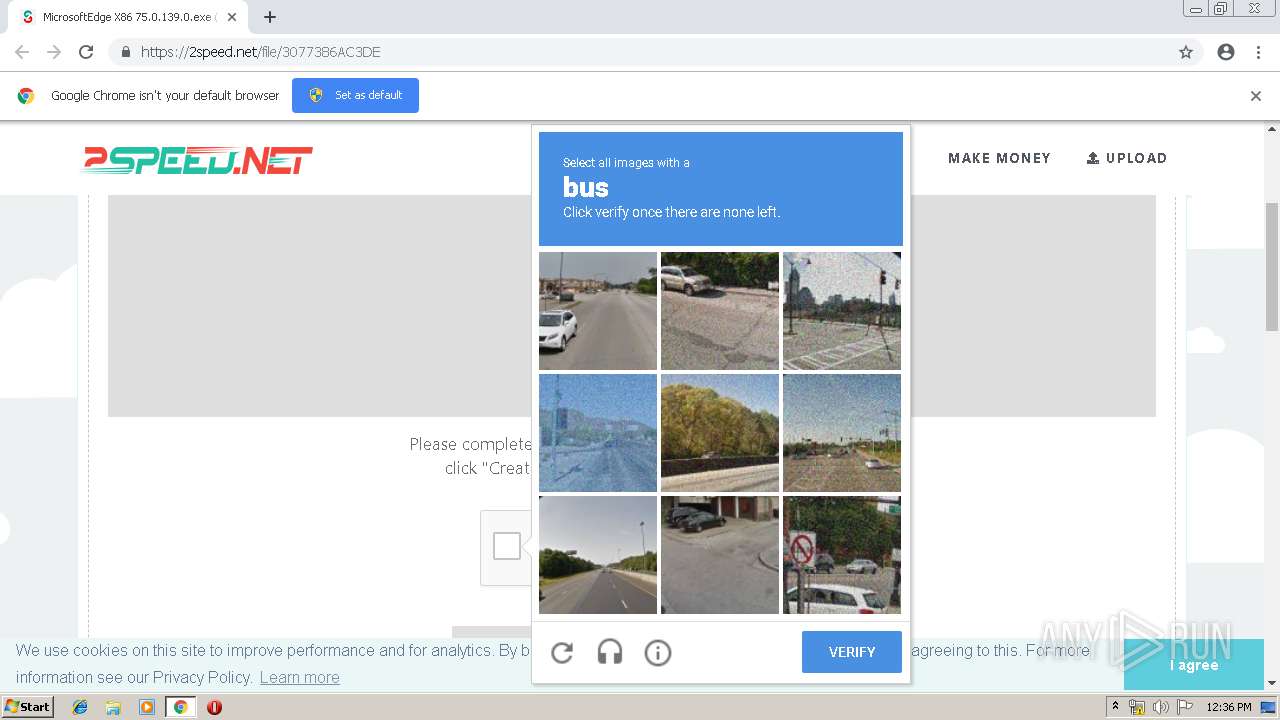
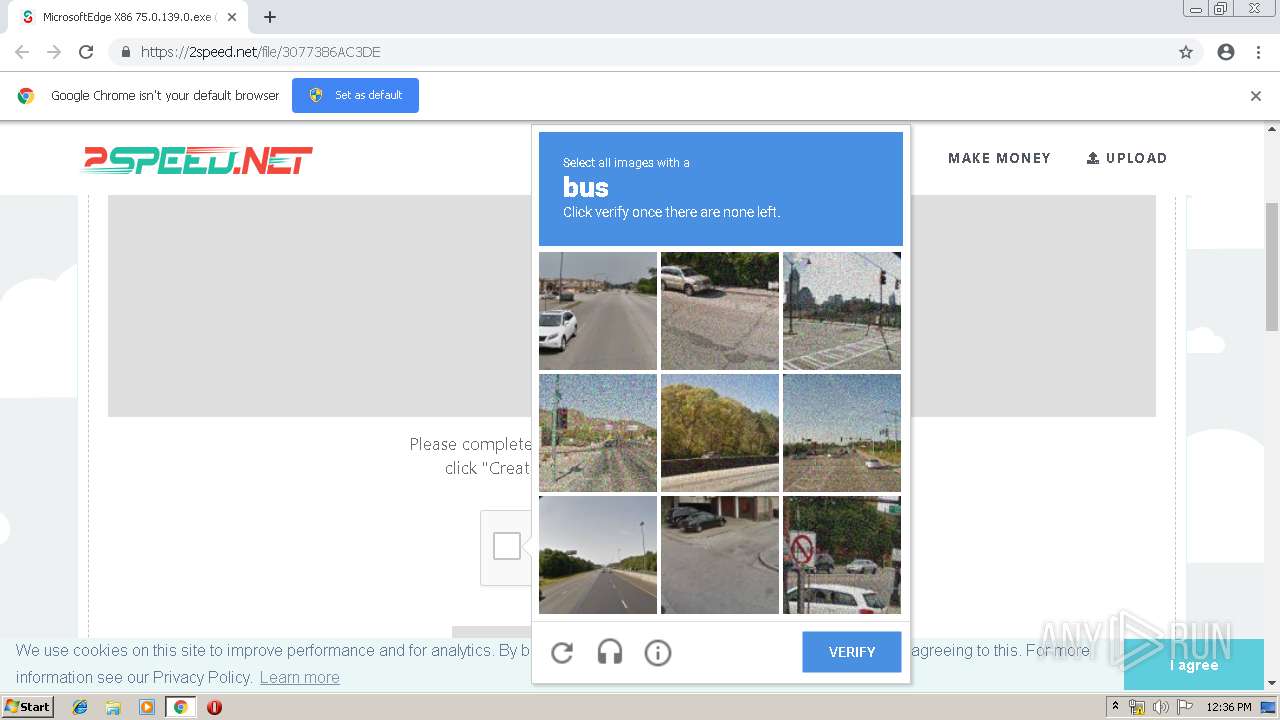
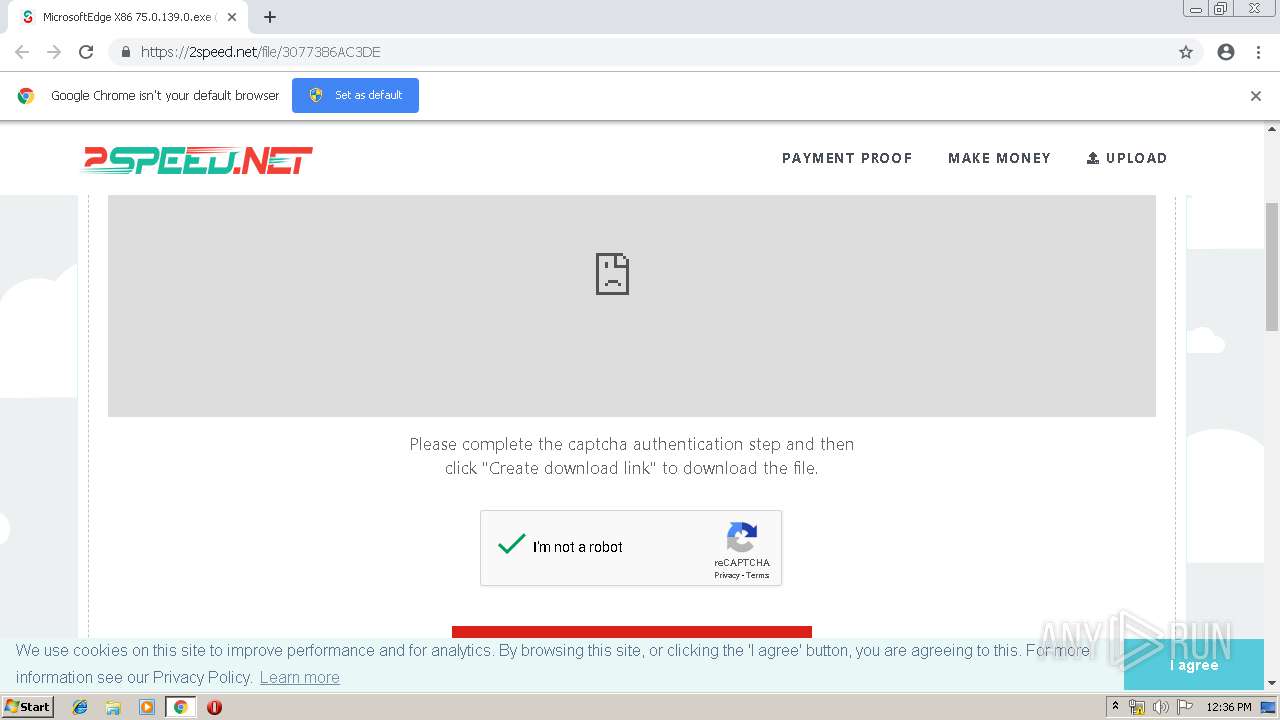
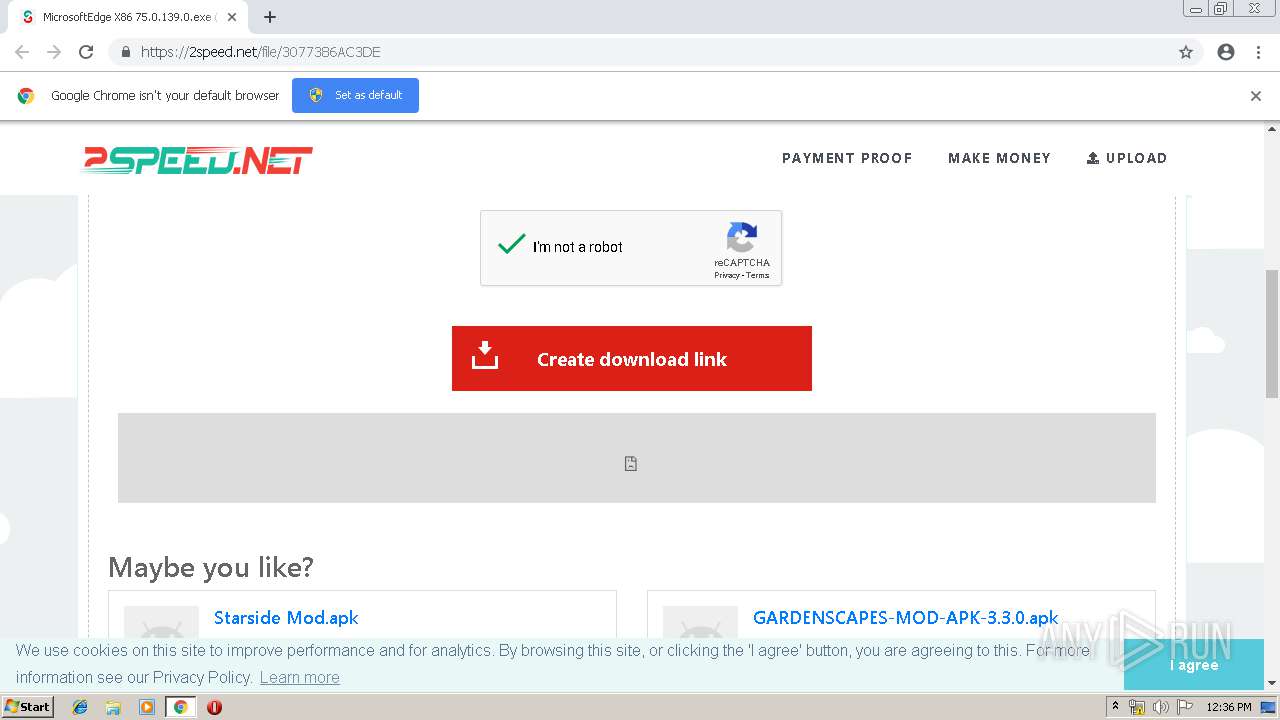
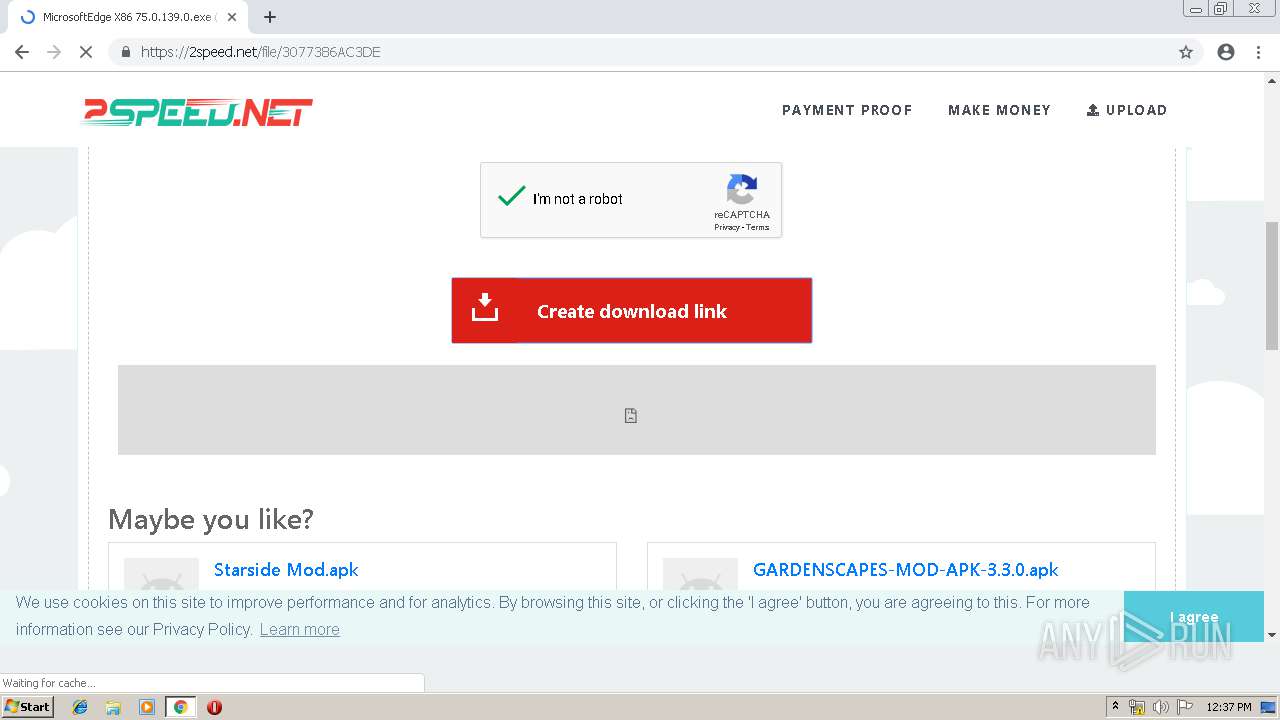
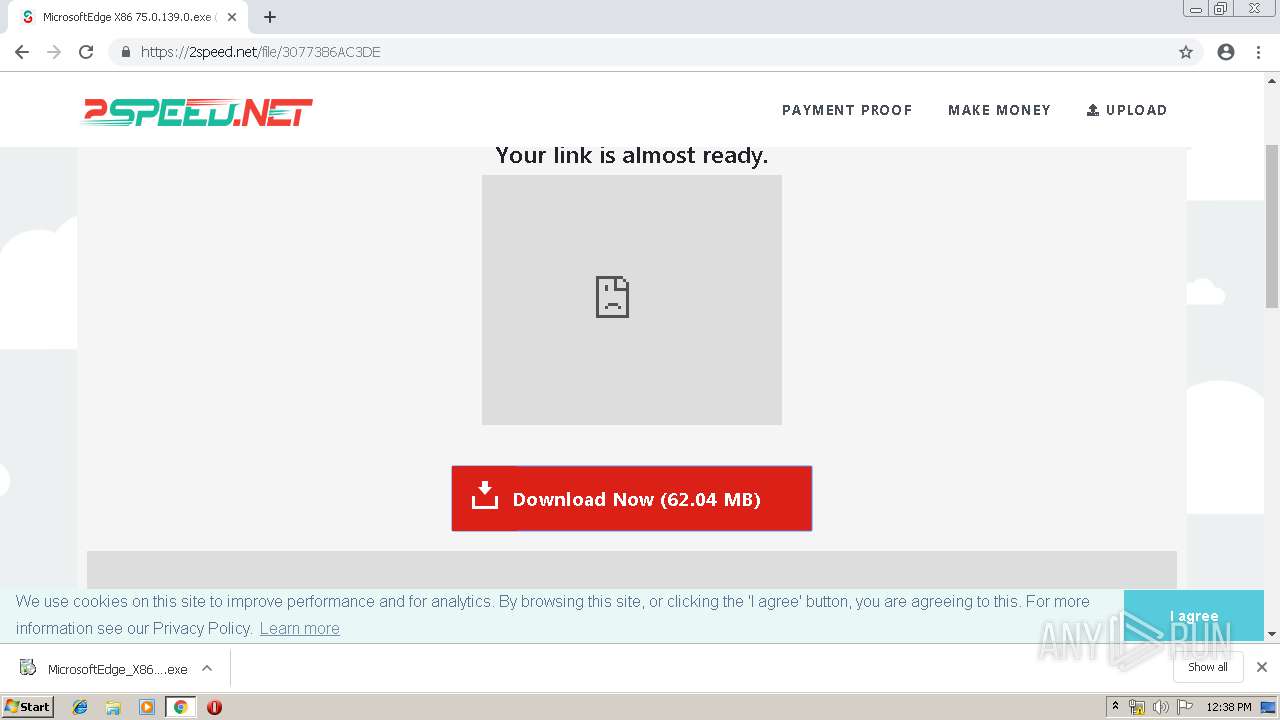
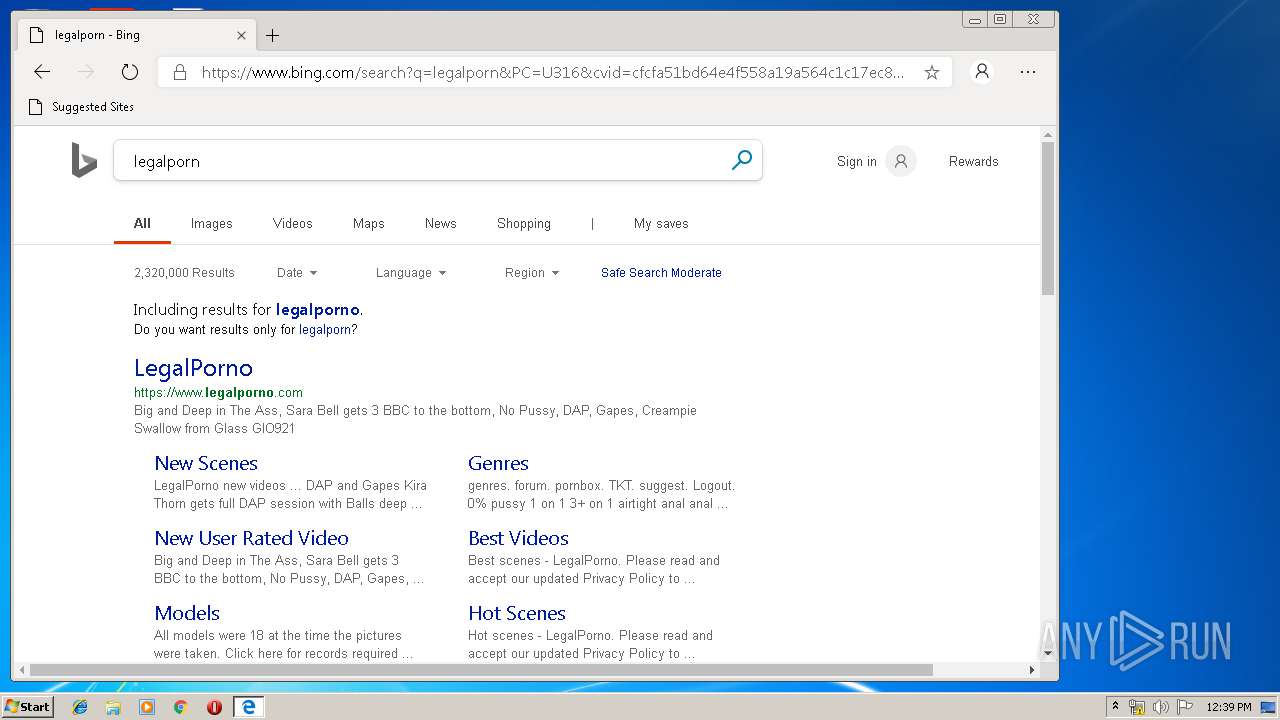
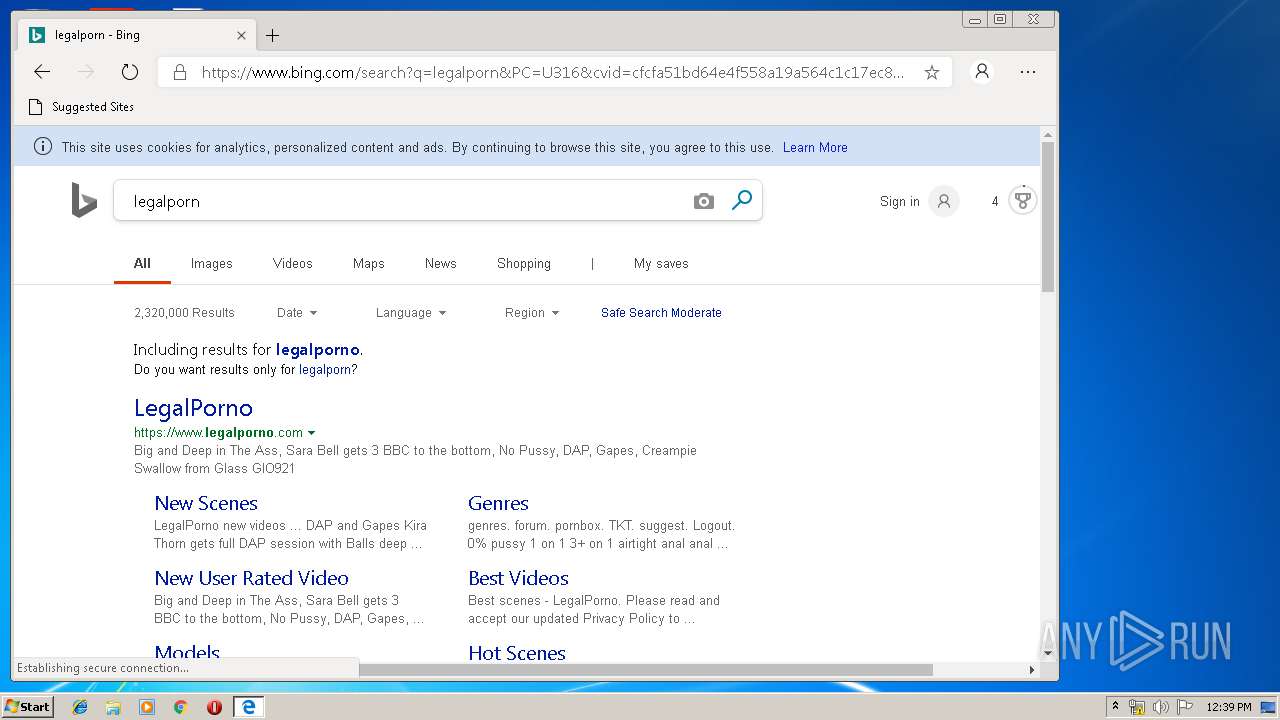
| URL: | https://2speed.net/file/3077386AC3DE |
| Full analysis: | https://app.any.run/tasks/3b3ebab7-696a-4194-a383-0343f0c34195 |
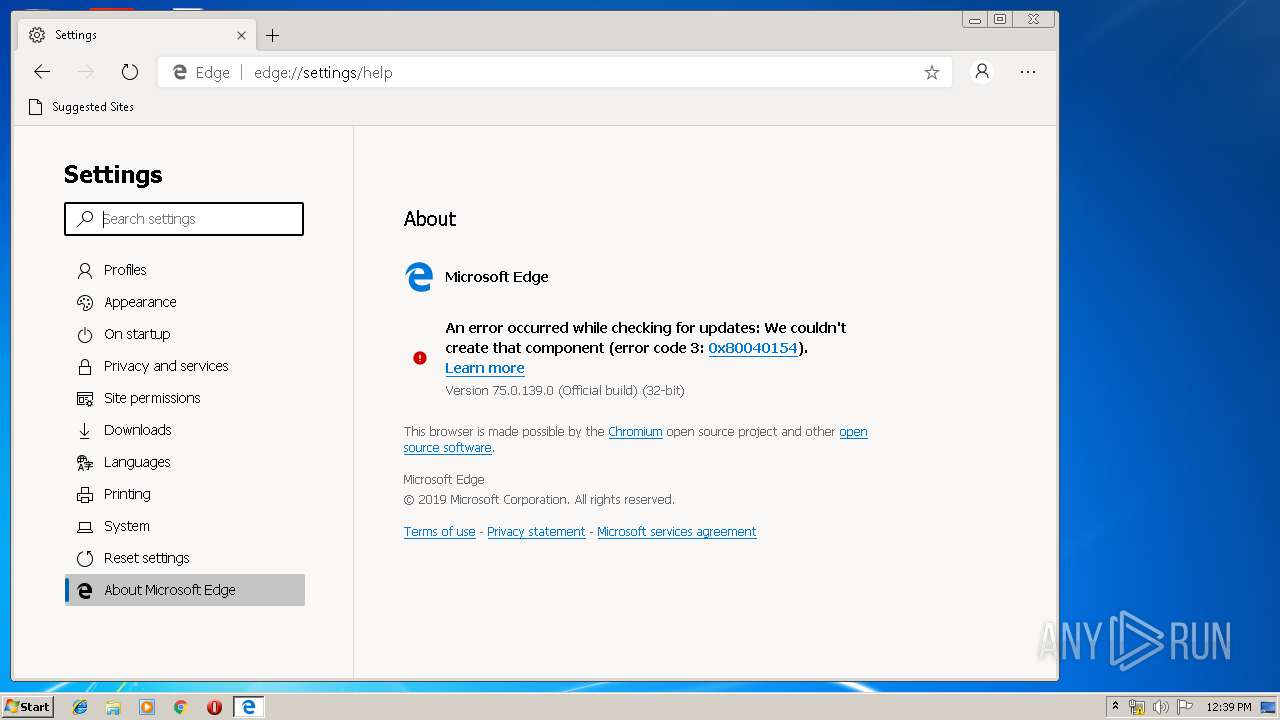
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 11:35:47 |
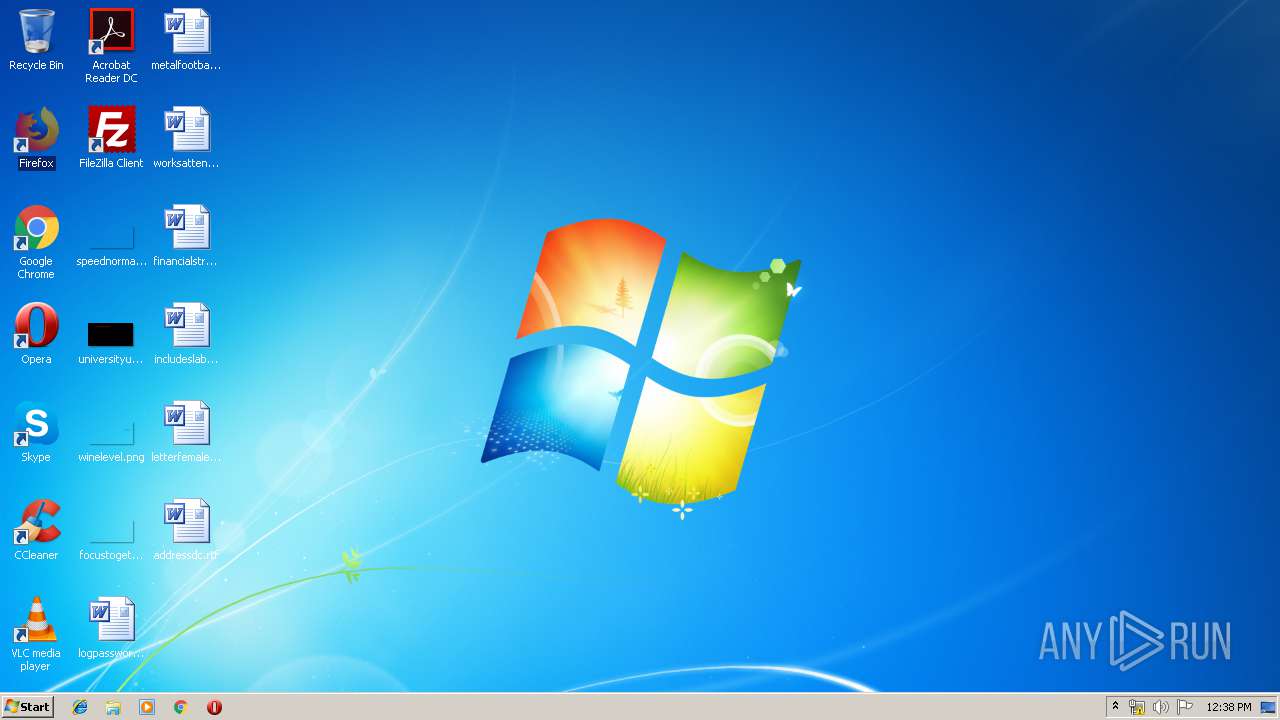
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A2085BA0BEB18F26E4C95681A7AFAEB6 |
| SHA1: | DD94413D8BEFB495C2B2CDFC8964F40A7635820A |
| SHA256: | 6E0E20F5DECA5F2EF59E6745B36BCFB9FCEC99E1A08B88C390F060E0907046AA |
| SSDEEP: | 3:N8ioW+dTO2n:2pdTO2 |
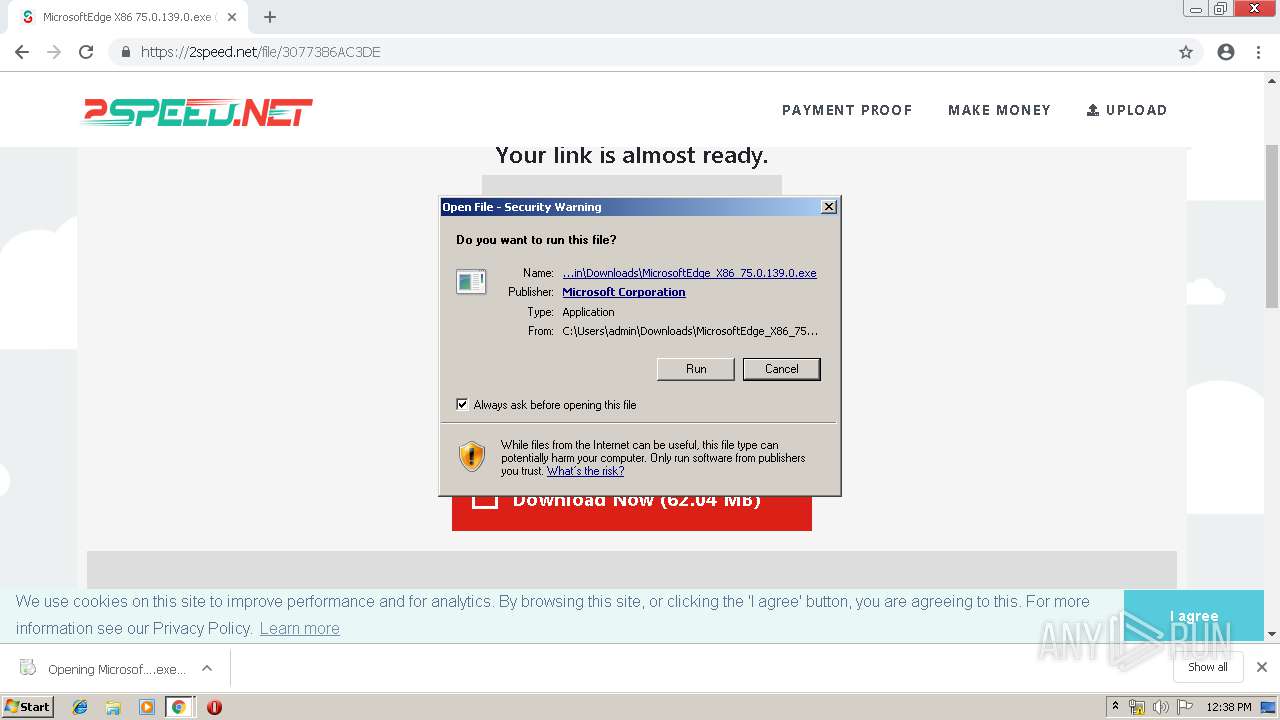
MALICIOUS
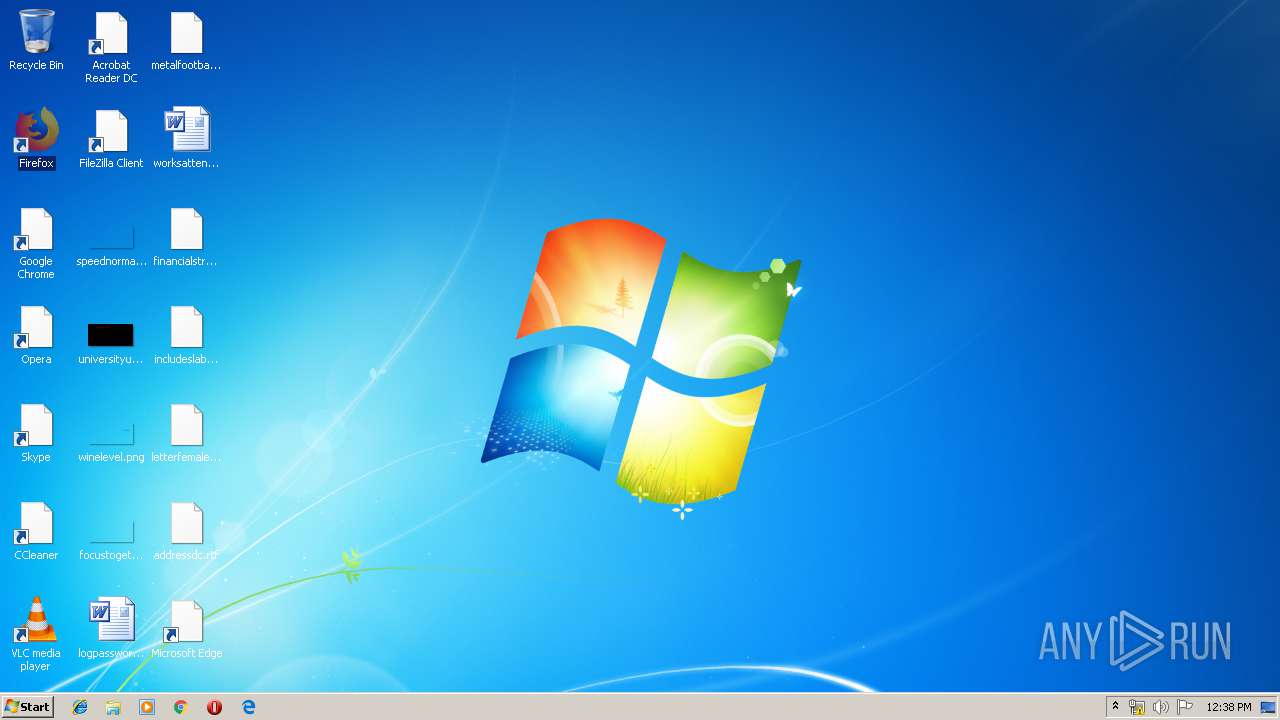
Application was dropped or rewritten from another process
- MicrosoftEdge_X86_75.0.139.0.exe (PID: 2476)
- setup.exe (PID: 3540)
- setup.exe (PID: 2756)
- msedge.exe (PID: 2120)
- msedge.exe (PID: 3572)
- msedge.exe (PID: 3256)
- msedge.exe (PID: 2236)
- msedge.exe (PID: 964)
- msedge.exe (PID: 1796)
- msedge.exe (PID: 3580)
- msedge.exe (PID: 2200)
- msedge.exe (PID: 3968)
- msedge.exe (PID: 3824)
- msedge.exe (PID: 868)
- msedge.exe (PID: 392)
- msedge.exe (PID: 3860)
- msedge.exe (PID: 3220)
- msedge.exe (PID: 3400)
- msedge.exe (PID: 2884)
- msedge.exe (PID: 3644)
- msedge.exe (PID: 2412)
- msedge.exe (PID: 3096)
- msedge.exe (PID: 3884)
- msedge.exe (PID: 4016)
- msedge.exe (PID: 3060)
- msedge.exe (PID: 3804)
- msedge.exe (PID: 1204)
- msedge.exe (PID: 2144)
- msedge.exe (PID: 3648)
- msedge.exe (PID: 1248)
- msedge.exe (PID: 3280)
- msedge.exe (PID: 2136)
- msedge.exe (PID: 3308)
- msedge.exe (PID: 124)
- msedge.exe (PID: 1904)
- msedge.exe (PID: 2348)
- msedge.exe (PID: 1132)
- msedge.exe (PID: 320)
- msedge.exe (PID: 3536)
- msedge.exe (PID: 2908)
- msedge.exe (PID: 2840)
Loads dropped or rewritten executable
- msedge.exe (PID: 1796)
- msedge.exe (PID: 2120)
- msedge.exe (PID: 3572)
- msedge.exe (PID: 3256)
- msedge.exe (PID: 3580)
- msedge.exe (PID: 964)
- msedge.exe (PID: 868)
- msedge.exe (PID: 2236)
- msedge.exe (PID: 2200)
- msedge.exe (PID: 3968)
- msedge.exe (PID: 392)
- msedge.exe (PID: 3824)
- msedge.exe (PID: 3400)
- msedge.exe (PID: 2884)
- msedge.exe (PID: 2412)
- msedge.exe (PID: 3860)
- msedge.exe (PID: 3220)
- msedge.exe (PID: 3644)
- msedge.exe (PID: 3884)
- msedge.exe (PID: 3060)
- msedge.exe (PID: 3096)
- msedge.exe (PID: 3280)
- msedge.exe (PID: 4016)
- msedge.exe (PID: 1204)
- msedge.exe (PID: 3804)
- msedge.exe (PID: 3648)
- msedge.exe (PID: 3308)
- msedge.exe (PID: 2136)
- msedge.exe (PID: 2144)
- msedge.exe (PID: 1248)
- msedge.exe (PID: 124)
- msedge.exe (PID: 1904)
- msedge.exe (PID: 2348)
- msedge.exe (PID: 1132)
- msedge.exe (PID: 320)
- msedge.exe (PID: 3536)
- msedge.exe (PID: 2908)
- msedge.exe (PID: 2840)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1524)
Application launched itself
- setup.exe (PID: 2756)
- msedge.exe (PID: 2120)
Executable content was dropped or overwritten
- MicrosoftEdge_X86_75.0.139.0.exe (PID: 2476)
- chrome.exe (PID: 1524)
- setup.exe (PID: 2756)
Creates a software uninstall entry
- setup.exe (PID: 2756)
Creates files in the user directory
- setup.exe (PID: 2756)
Modifies the open verb of a shell class
- setup.exe (PID: 2756)
INFO
Dropped object may contain TOR URL's
- chrome.exe (PID: 1524)
Application launched itself
- chrome.exe (PID: 1524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
105
Monitored processes
68
Malicious processes
18
Suspicious processes
17
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe" --type=renderer --field-trial-handle=904,14912244584490051487,8236614818812930188,131072 --disable-gpu-compositing --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-refresh --enable-offline-auto-refresh-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2386969145176963544 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4700 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 75.0.139.0 Modules
| |||||||||||||||
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,6498408520033864158,1178594876917076201,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17837399921617928941 --mojo-platform-channel-handle=3552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 320 | "C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe" --type=renderer --field-trial-handle=904,14912244584490051487,8236614818812930188,131072 --disable-gpu-compositing --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-refresh --enable-offline-auto-refresh-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=928298067045831993 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3384 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 75.0.139.0 Modules
| |||||||||||||||
| 392 | "C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe" --type=utility --field-trial-handle=904,14912244584490051487,8236614818812930188,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14195771615569550921 --mojo-platform-channel-handle=3808 --ignored=" --type=renderer " /prefetch:8 | C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 75.0.139.0 Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,6498408520033864158,1178594876917076201,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9975178857606040535 --mojo-platform-channel-handle=5612 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 868 | "C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe" --type=renderer --field-trial-handle=904,14912244584490051487,8236614818812930188,131072 --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-refresh --enable-offline-auto-refresh-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13750442119732590285 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2340 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 75.0.139.0 Modules
| |||||||||||||||
| 912 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 964 | "C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe" --type=renderer --field-trial-handle=904,14912244584490051487,8236614818812930188,131072 --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-refresh --enable-offline-auto-refresh-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6111526359405423046 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 75.0.139.0 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,6498408520033864158,1178594876917076201,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17882181889748453485 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17882181889748453485 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,6498408520033864158,1178594876917076201,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11744243404688306301 --mojo-platform-channel-handle=4040 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 362
Read events
2 069
Write events
286
Delete events
7
Modification events
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1524-13200665774177125 |
Value: 259 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
51
Suspicious files
254
Text files
519
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4efa55bf-8867-482c-858c-f3a143332bb7.tmp | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
118
DNS requests
88
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3256 | msedge.exe | GET | — | 74.125.104.76:80 | http://r6---sn-4g5e6nl6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWRiQUFXRzBmNy0xYlVRZ0JEM3hyZ3NxUQ/7519.415.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.119.8&mm=28&mn=sn-4g5e6nl6&ms=nvh&mt=1556192248&mv=m&pl=24&shardbypass=yes | US | — | — | whitelisted |
2120 | msedge.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | — | — | whitelisted |
3256 | msedge.exe | GET | — | 74.125.104.76:80 | http://r6---sn-4g5e6nl6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWRiQUFXRzBmNy0xYlVRZ0JEM3hyZ3NxUQ/7519.415.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.119.8&mm=28&mn=sn-4g5e6nl6&ms=nvh&mt=1556192248&mv=m&pl=24&shardbypass=yes | US | — | — | whitelisted |
3256 | msedge.exe | GET | — | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWRiQUFXRzBmNy0xYlVRZ0JEM3hyZ3NxUQ/7519.415.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | — | — | whitelisted |
2120 | msedge.exe | GET | — | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIGkp0%2Fv9GUvNUu1EP06Tu7%2BChyAQUkZ47RGw9V5xCdyo010%2FRzEqXLNoCEyAAA7VE2alhoJR2mHYAAAADtUQ%3D | US | — | — | whitelisted |
3256 | msedge.exe | GET | — | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYWRiQUFXRzBmNy0xYlVRZ0JEM3hyZ3NxUQ/7519.415.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | — | — | whitelisted |
1524 | chrome.exe | GET | 200 | 74.125.173.138:80 | http://r5---sn-4g5ednsy.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.119.8&mm=28&mn=sn-4g5ednsy&ms=nvh&mt=1556192066&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
1524 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1524 | chrome.exe | 104.25.9.107:443 | 2speed.net | Cloudflare Inc | US | shared |
1524 | chrome.exe | 104.19.197.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
1524 | chrome.exe | 172.217.18.98:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1524 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
1524 | chrome.exe | 172.217.16.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1524 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
1524 | chrome.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1524 | chrome.exe | 172.217.16.130:443 | adservice.google.com | Google Inc. | US | whitelisted |
1524 | chrome.exe | 151.101.120.134:443 | 2speed-net.disqus.com | Fastly | US | unknown |
1524 | chrome.exe | 216.58.206.2:443 | adservice.google.fr | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
2speed.net |
| malicious |
accounts.google.com |
| shared |
apis.google.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
www.google.com |
| malicious |
www.googletagmanager.com |
| whitelisted |