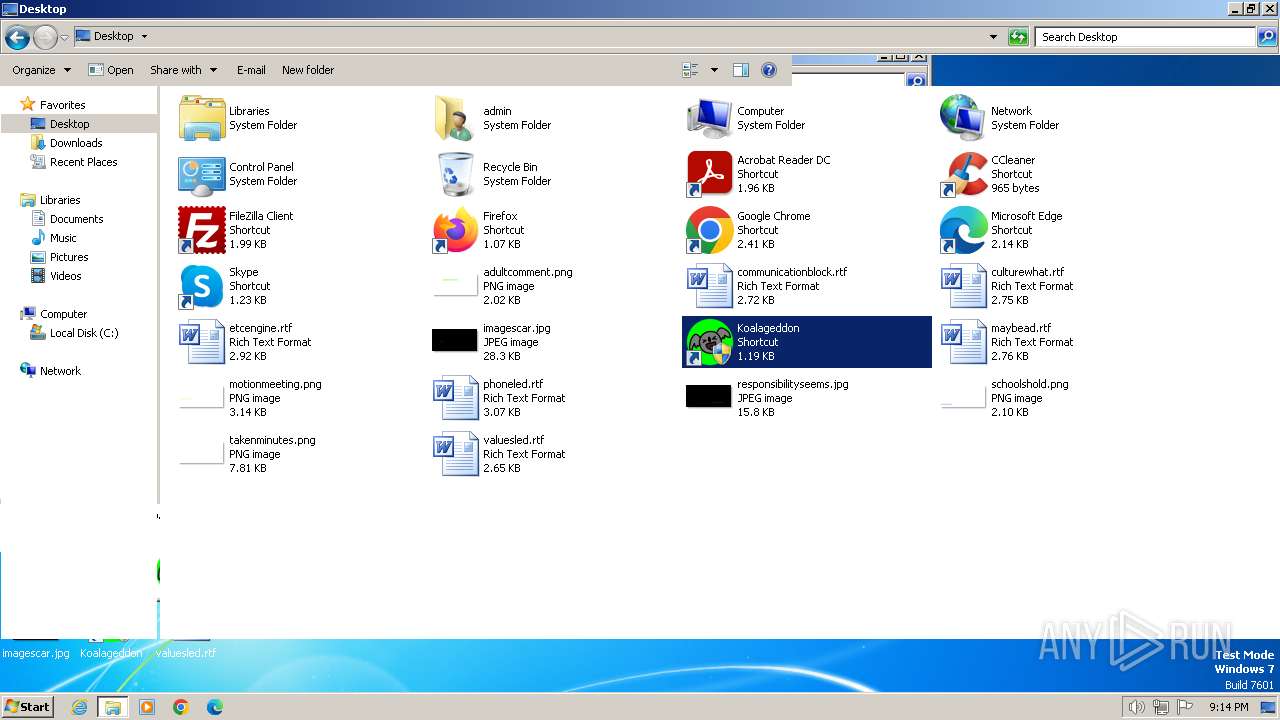
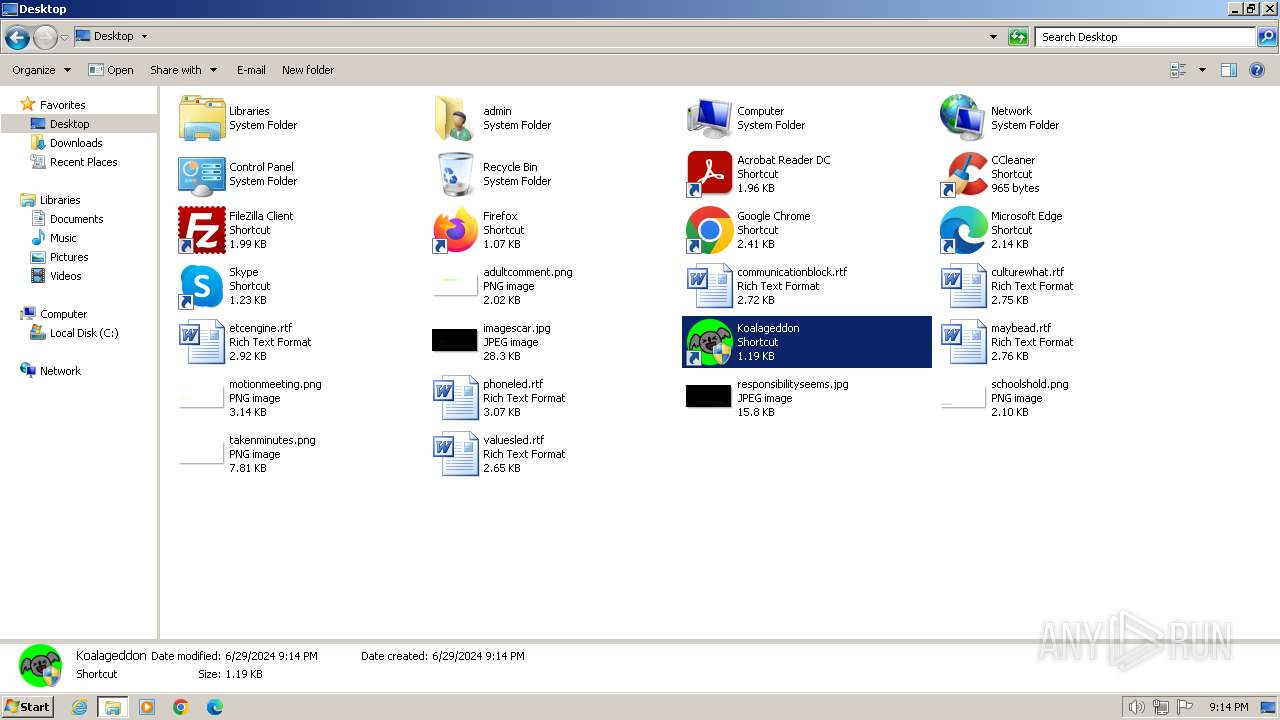
| File name: | KoalageddonInstaller(1).exe |
| Full analysis: | https://app.any.run/tasks/950b64a3-b00e-4caa-8fac-20daf756f4c0 |
| Verdict: | Malicious activity |
| Analysis date: | June 29, 2024, 20:14:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 238691250A5960BEB04574BBB4BA069C |
| SHA1: | F4F3B5FA7E0EDD6AA99587AEDFE9DD89A3B582F0 |
| SHA256: | 6E027B8D745EA9EF349493F65D12347D090B2A6AE7B0162B4F8C9C801A82B7F9 |
| SSDEEP: | 49152:Nqe3f6lOhceD/FPTOVZjVaopG+HzPiicUf+DidXvh6dS/04OOR5Qv2U:cSilkJ/FKZvpG+H++f+DidXvh6d204Ot |
MALICIOUS
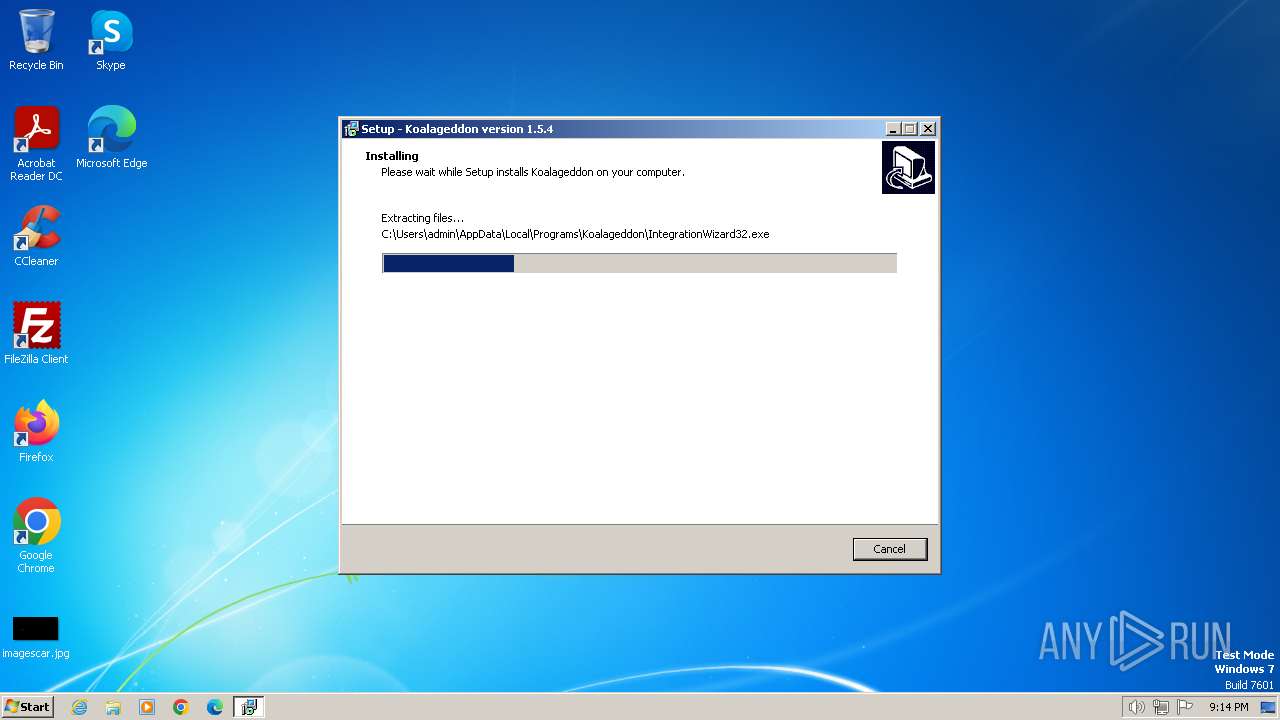
Drops the executable file immediately after the start
- KoalageddonInstaller(1).exe (PID: 3332)
- KoalageddonInstaller(1).tmp (PID: 3568)
SUSPICIOUS
Executable content was dropped or overwritten
- KoalageddonInstaller(1).exe (PID: 3332)
- KoalageddonInstaller(1).tmp (PID: 3568)
Reads the Windows owner or organization settings
- KoalageddonInstaller(1).tmp (PID: 3568)
INFO
Checks supported languages
- KoalageddonInstaller(1).tmp (PID: 3568)
- KoalageddonInstaller(1).exe (PID: 3332)
- wmpnscfg.exe (PID: 3308)
- IntegrationWizard32.exe (PID: 1044)
- IntegrationWizard32.exe (PID: 3852)
- IntegrationWizard32.exe (PID: 4032)
Create files in a temporary directory
- KoalageddonInstaller(1).exe (PID: 3332)
Reads the computer name
- KoalageddonInstaller(1).tmp (PID: 3568)
- IntegrationWizard32.exe (PID: 1044)
- IntegrationWizard32.exe (PID: 3852)
- IntegrationWizard32.exe (PID: 4032)
- wmpnscfg.exe (PID: 3308)
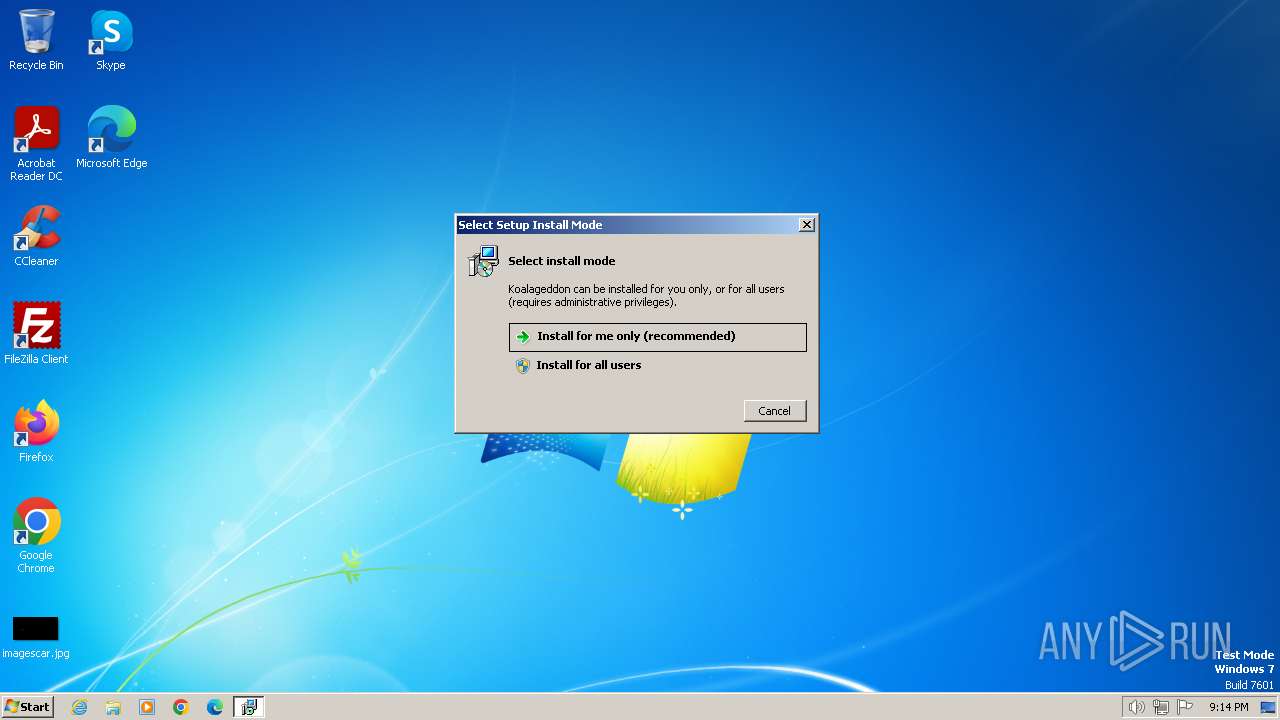
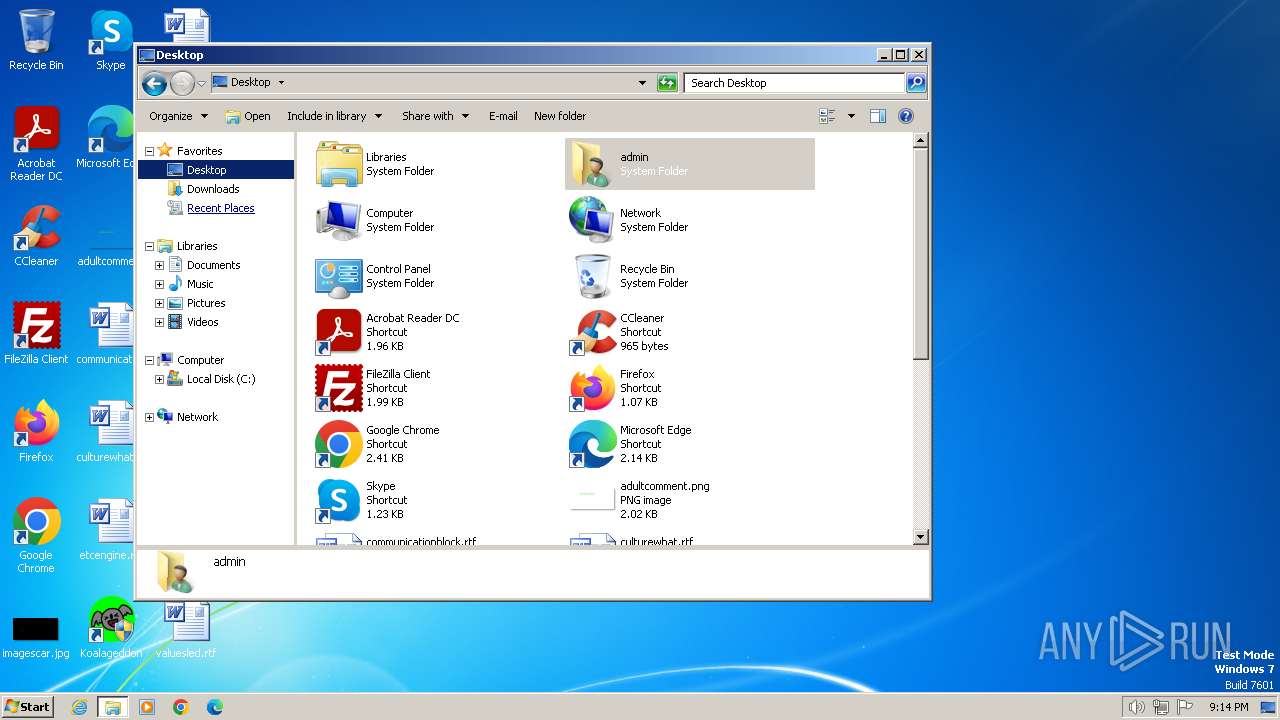
Manual execution by a user
- wmpnscfg.exe (PID: 3308)
- IntegrationWizard32.exe (PID: 3852)
- IntegrationWizard32.exe (PID: 1044)
- explorer.exe (PID: 3936)
- IntegrationWizard32.exe (PID: 2416)
- IntegrationWizard32.exe (PID: 4032)
- IntegrationWizard32.exe (PID: 324)
- IntegrationWizard32.exe (PID: 2936)
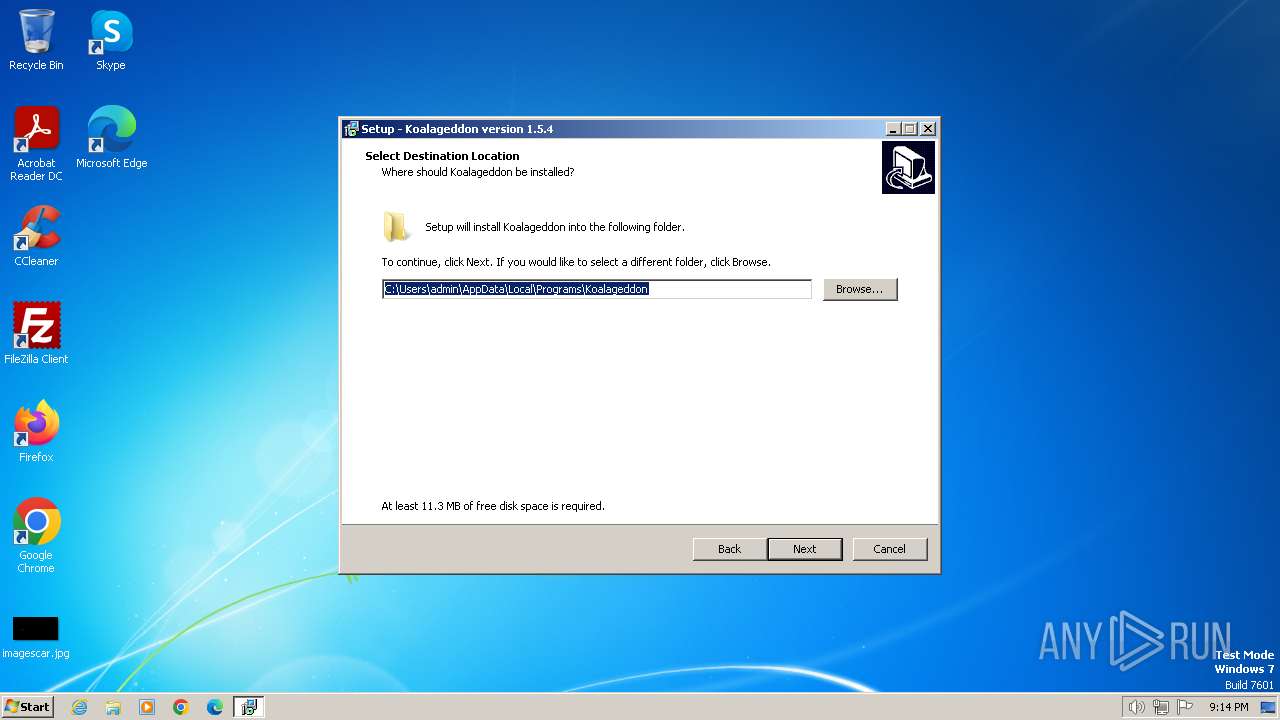
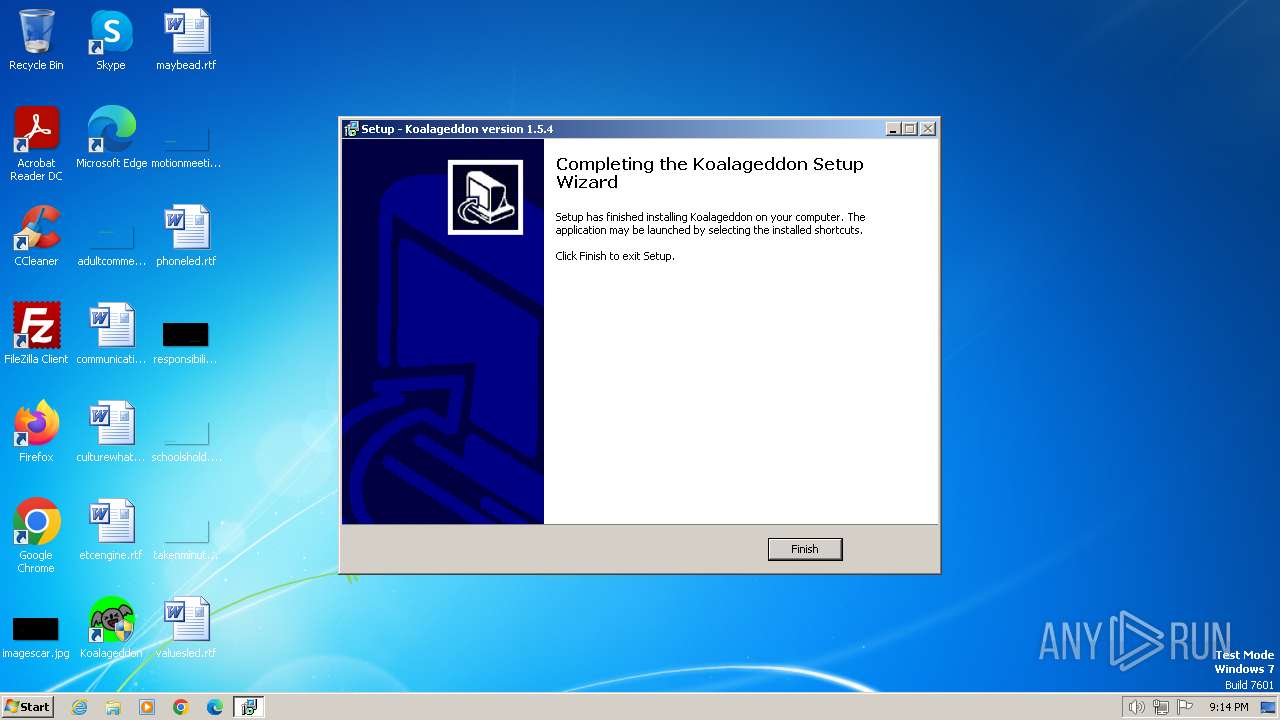
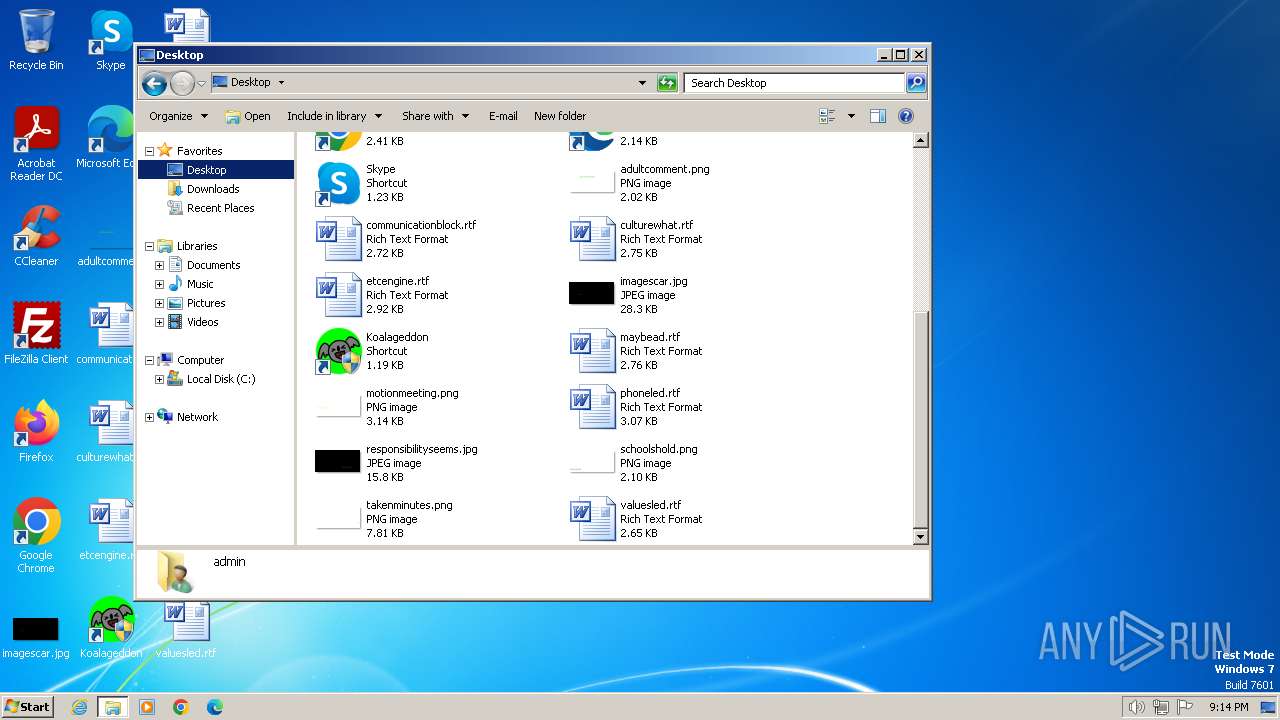
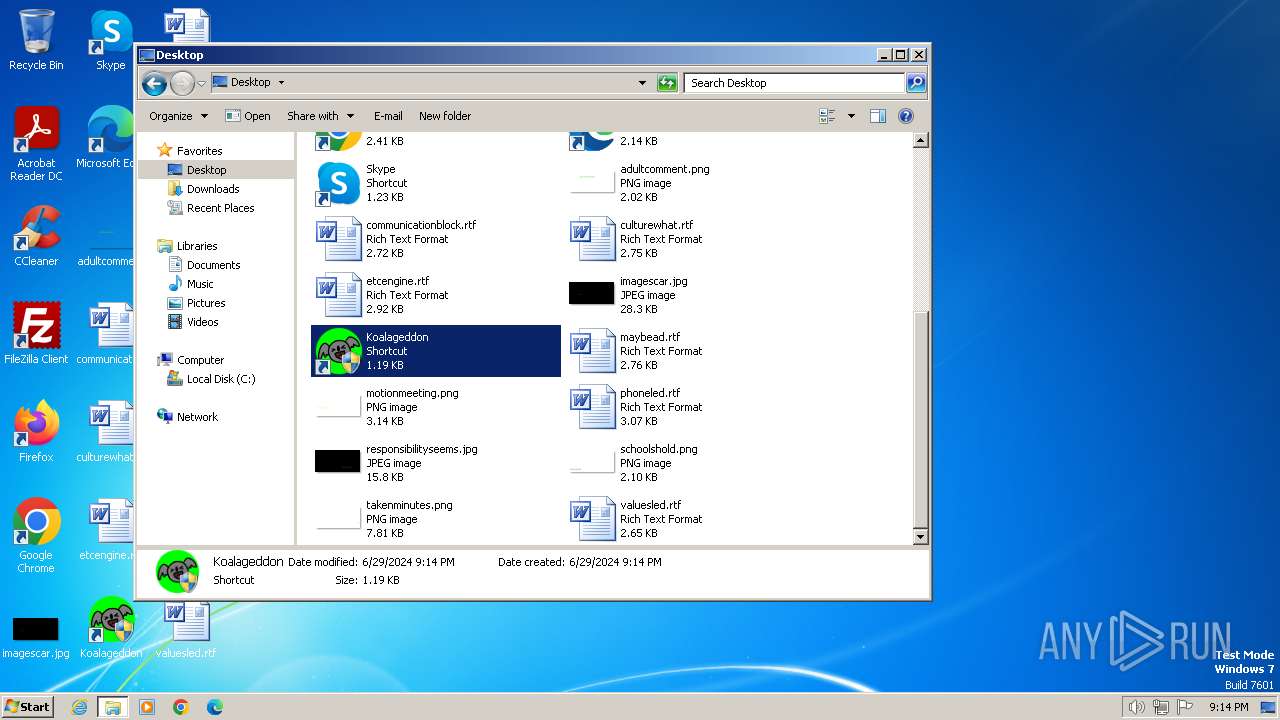
Creates files or folders in the user directory
- KoalageddonInstaller(1).tmp (PID: 3568)
Creates files in the program directory
- IntegrationWizard32.exe (PID: 1044)
Creates a software uninstall entry
- KoalageddonInstaller(1).tmp (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:15 09:48:30+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.4.0 |
| ProductVersionNumber: | 1.5.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
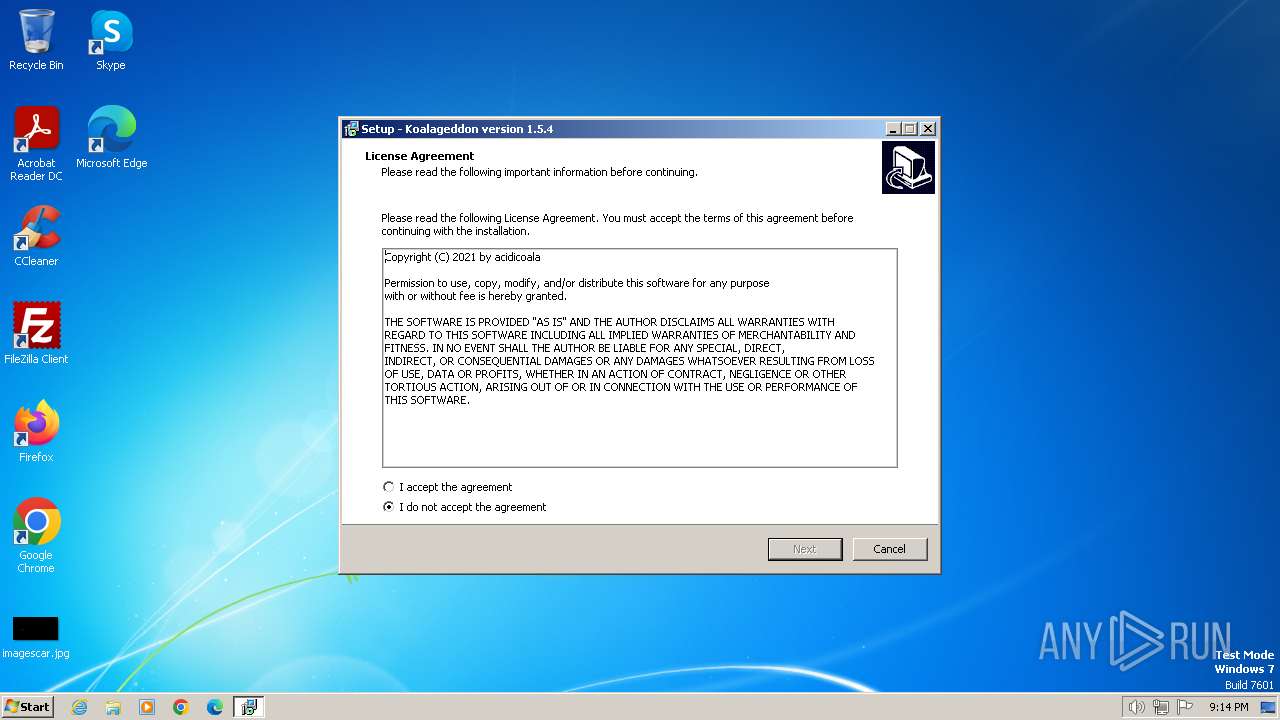
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | acidicoala |
| FileDescription: | Koalageddon Setup |
| FileVersion: | 1.5.4 |
| LegalCopyright: | |
| OriginalFileName: | |
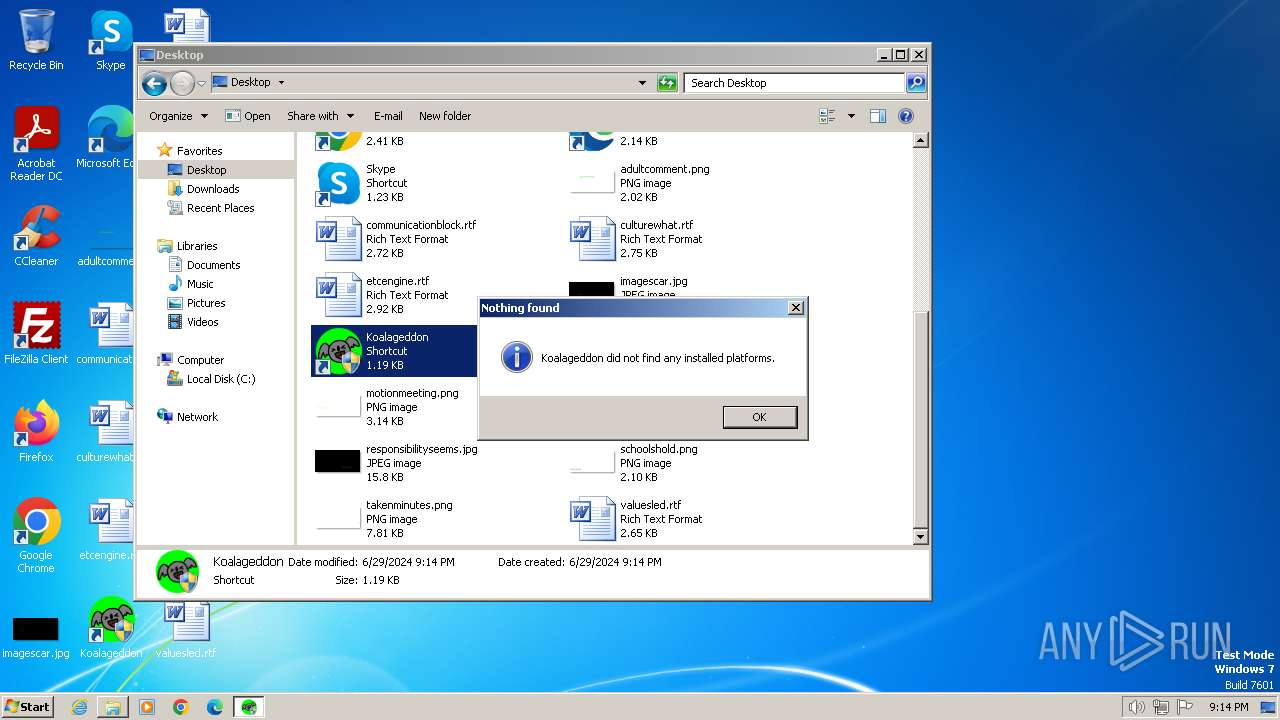
| ProductName: | Koalageddon |
| ProductVersion: | 1.5.4 |
Total processes
58
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
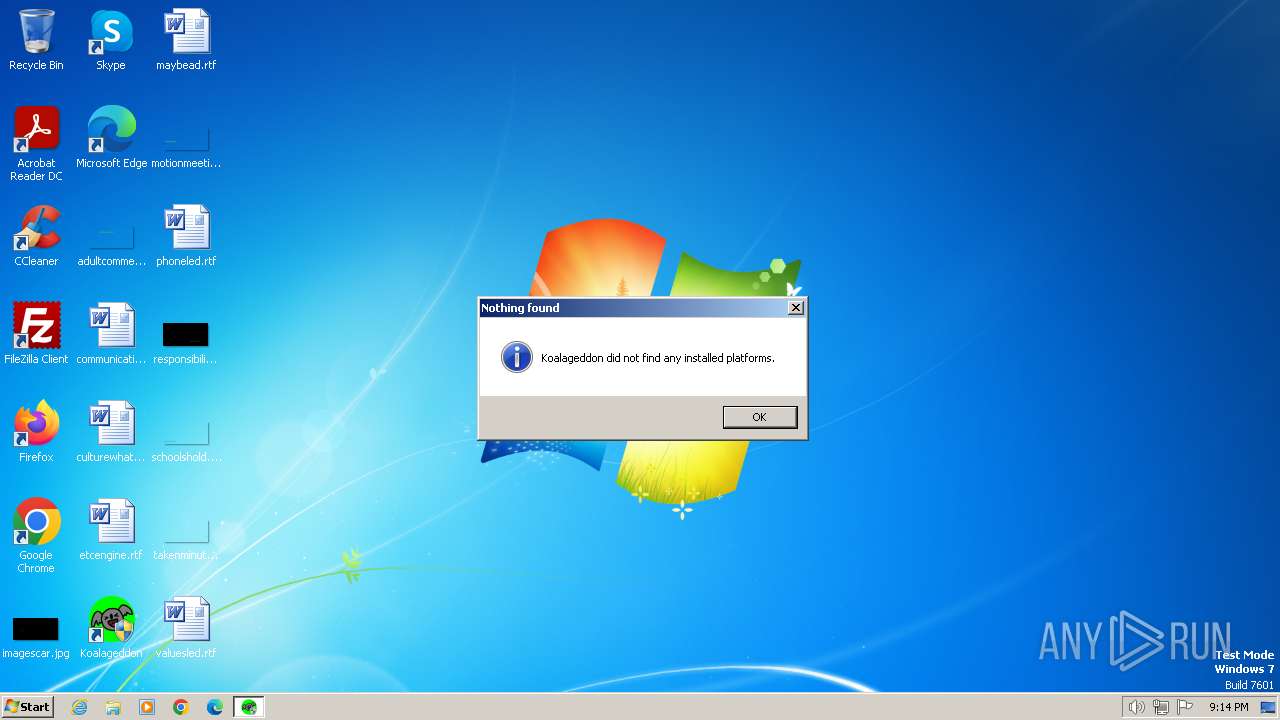
| 324 | "C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe" | C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1044 | "C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe" | C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe" | C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2936 | "C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe" | C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3308 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3332 | "C:\Users\admin\AppData\Local\Temp\KoalageddonInstaller(1).exe" | C:\Users\admin\AppData\Local\Temp\KoalageddonInstaller(1).exe | explorer.exe | ||||||||||||
User: admin Company: acidicoala Integrity Level: MEDIUM Description: Koalageddon Setup Exit code: 0 Version: 1.5.4 Modules
| |||||||||||||||
| 3568 | "C:\Users\admin\AppData\Local\Temp\is-POVHQ.tmp\KoalageddonInstaller(1).tmp" /SL5="$B016A,2244670,780800,C:\Users\admin\AppData\Local\Temp\KoalageddonInstaller(1).exe" | C:\Users\admin\AppData\Local\Temp\is-POVHQ.tmp\KoalageddonInstaller(1).tmp | KoalageddonInstaller(1).exe | ||||||||||||
User: admin Company: acidicoala Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3852 | "C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe" | C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3936 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4032 | "C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe" | C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
3 049
Read events
3 008
Write events
35
Delete events
6
Modification events
| (PID) Process: | (3568) KoalageddonInstaller(1).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: F00D0000F6A8D0E760CADA01 | |||
| (PID) Process: | (3568) KoalageddonInstaller(1).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 8DCCF1A515E1F380555EC34AF5259223BF3D13F603D92E8349CC1B01CE40CCDE | |||
| (PID) Process: | (3568) KoalageddonInstaller(1).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3568) KoalageddonInstaller(1).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | |||
| (PID) Process: | (3568) KoalageddonInstaller(1).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 8F82BA7A7C05A655BE69AFCFCB96DBA4617CCC42BDDC0938326A70824EC31714 | |||
| (PID) Process: | (3568) KoalageddonInstaller(1).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{42B0E81F-EF53-474B-B4A3-262EDC67D93A}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.1.2 | |||
| (PID) Process: | (3568) KoalageddonInstaller(1).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{42B0E81F-EF53-474B-B4A3-262EDC67D93A}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Users\admin\AppData\Local\Programs\Koalageddon | |||
| (PID) Process: | (3568) KoalageddonInstaller(1).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{42B0E81F-EF53-474B-B4A3-262EDC67D93A}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\Koalageddon\ | |||
| (PID) Process: | (3568) KoalageddonInstaller(1).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{42B0E81F-EF53-474B-B4A3-262EDC67D93A}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Koalageddon | |||
| (PID) Process: | (3568) KoalageddonInstaller(1).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{42B0E81F-EF53-474B-B4A3-262EDC67D93A}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
17
Suspicious files
4
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | KoalageddonInstaller(1).tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\is-JBUAI.tmp | executable | |
MD5:A8066E5387A21092926451AA1538A709 | SHA256:F3E5EC14A045D9B2E75AE26AC0A2BBD58A41CF445F0528ABA2F028C063A291B3 | |||
| 3568 | KoalageddonInstaller(1).tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\unins000.exe | executable | |
MD5:1ECD0299C555A220ECBC07C981B7E57B | SHA256:10C42F378FBB106472A22A50C36E830427A2883C1E09CD1403FD3E41E23CCEBB | |||
| 3568 | KoalageddonInstaller(1).tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\is-DUNVC.tmp | executable | |
MD5:C5B9B71E86000D255CA57D9BFDE85B75 | SHA256:C91D5A5F269CA62CAE863695A9AB3C25D5E16B171E0789FBC73AB379BA958E9B | |||
| 3568 | KoalageddonInstaller(1).tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\Injector32.exe | executable | |
MD5:A8066E5387A21092926451AA1538A709 | SHA256:F3E5EC14A045D9B2E75AE26AC0A2BBD58A41CF445F0528ABA2F028C063A291B3 | |||
| 3568 | KoalageddonInstaller(1).tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\is-JK750.tmp | executable | |
MD5:16209CB374C2AD72684EB216A2730E44 | SHA256:99AFF3E11438478E2036B3AE35BCC5714AAA5C6AF851B4F3C76042CD0F5F2EA7 | |||
| 3568 | KoalageddonInstaller(1).tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\Integration64.dll | executable | |
MD5:16209CB374C2AD72684EB216A2730E44 | SHA256:99AFF3E11438478E2036B3AE35BCC5714AAA5C6AF851B4F3C76042CD0F5F2EA7 | |||
| 3568 | KoalageddonInstaller(1).tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\is-3PSAC.tmp | executable | |
MD5:6F7F5C5B53F0FBF7820F5468E12440AD | SHA256:F023340A9AF2AD520178D731CF4BD1686093CF3BDCCC8BBC3B0434F9BA3635A4 | |||
| 3568 | KoalageddonInstaller(1).tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\Injector64.exe | executable | |
MD5:B1C63C12DE6131DABD104707485758F3 | SHA256:BC9250F57748ACCE502A30D2488BB0EFAD7F0EEE1D10D2D839D4F56D8B86BEAB | |||
| 3568 | KoalageddonInstaller(1).tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\is-UASJH.tmp | executable | |
MD5:F7EE86F25EDE0BE856599F07D67C0C61 | SHA256:A2A49F356E5CF628287071C0547542283966CBBBC97A08962086445FFD0371F0 | |||
| 3568 | KoalageddonInstaller(1).tmp | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Koalageddon\Koalageddon.lnk | binary | |
MD5:E64C89ACF5E8E4F608CF17699687A36D | SHA256:3B95FE4DD42BFB26D2548DC232510BFA0A87582FD9CCFCE29FE494B1665A3345 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
12
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1372 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1372 | svchost.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
1372 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1060 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |