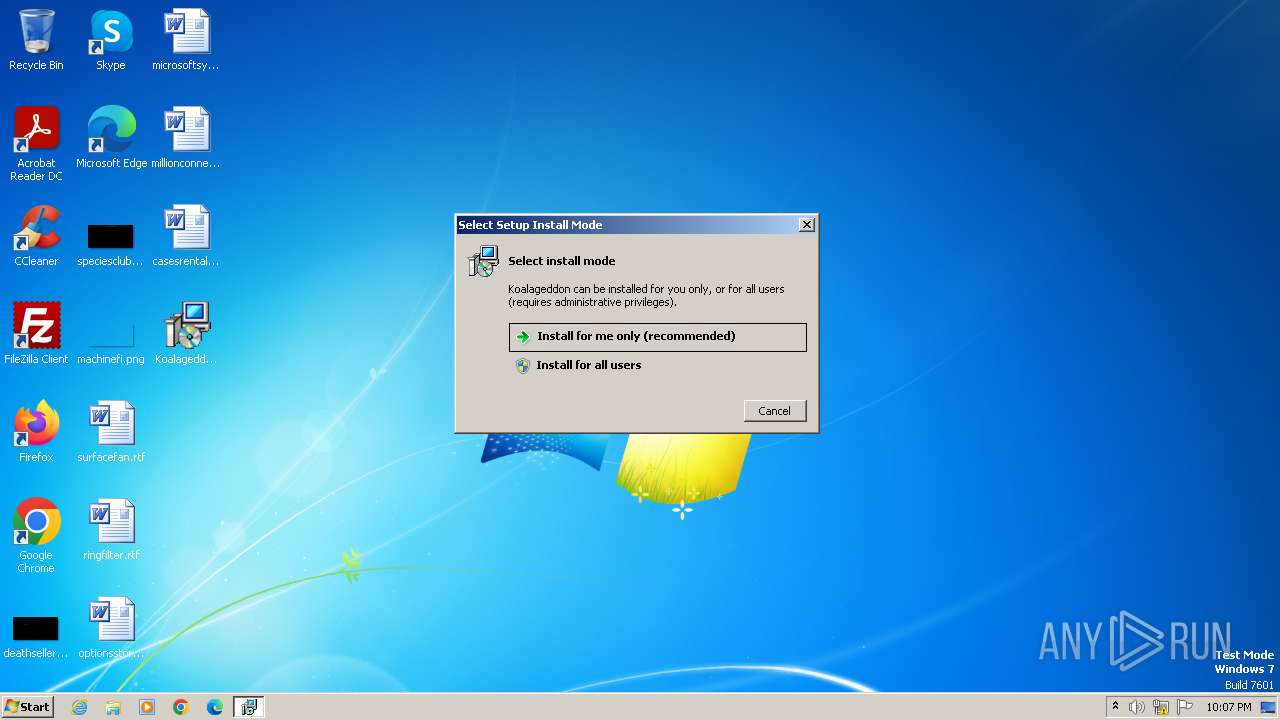
| File name: | KoalageddonInstaller.exe |
| Full analysis: | https://app.any.run/tasks/465bdb85-2a8b-4092-9967-f1e9e55cc526 |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2023, 22:06:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 238691250A5960BEB04574BBB4BA069C |
| SHA1: | F4F3B5FA7E0EDD6AA99587AEDFE9DD89A3B582F0 |
| SHA256: | 6E027B8D745EA9EF349493F65D12347D090B2A6AE7B0162B4F8C9C801A82B7F9 |
| SSDEEP: | 49152:Nqe3f6lOhceD/FPTOVZjVaopG+HzPiicUf+DidXvh6dS/04OOR5Qv2U:cSilkJ/FKZvpG+H++f+DidXvh6d204Ot |
MALICIOUS
Drops the executable file immediately after the start
- KoalageddonInstaller.exe (PID: 3428)
- KoalageddonInstaller.tmp (PID: 3460)
SUSPICIOUS
Reads the Windows owner or organization settings
- KoalageddonInstaller.tmp (PID: 3460)
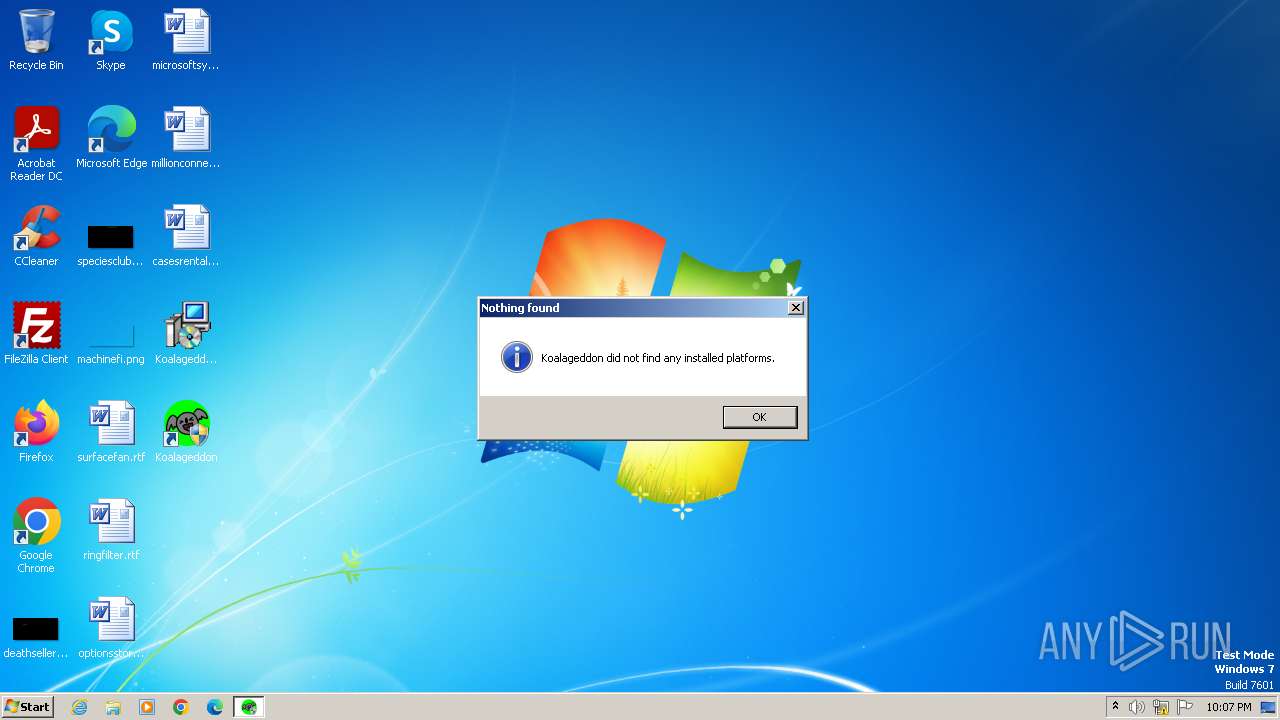
INFO
Checks supported languages
- KoalageddonInstaller.exe (PID: 3428)
- KoalageddonInstaller.tmp (PID: 3460)
- IntegrationWizard32.exe (PID: 3688)
- IntegrationWizard32.exe (PID: 3828)
Reads the computer name
- KoalageddonInstaller.tmp (PID: 3460)
- IntegrationWizard32.exe (PID: 3688)
- IntegrationWizard32.exe (PID: 3828)
Create files in a temporary directory
- KoalageddonInstaller.exe (PID: 3428)
Creates files or folders in the user directory
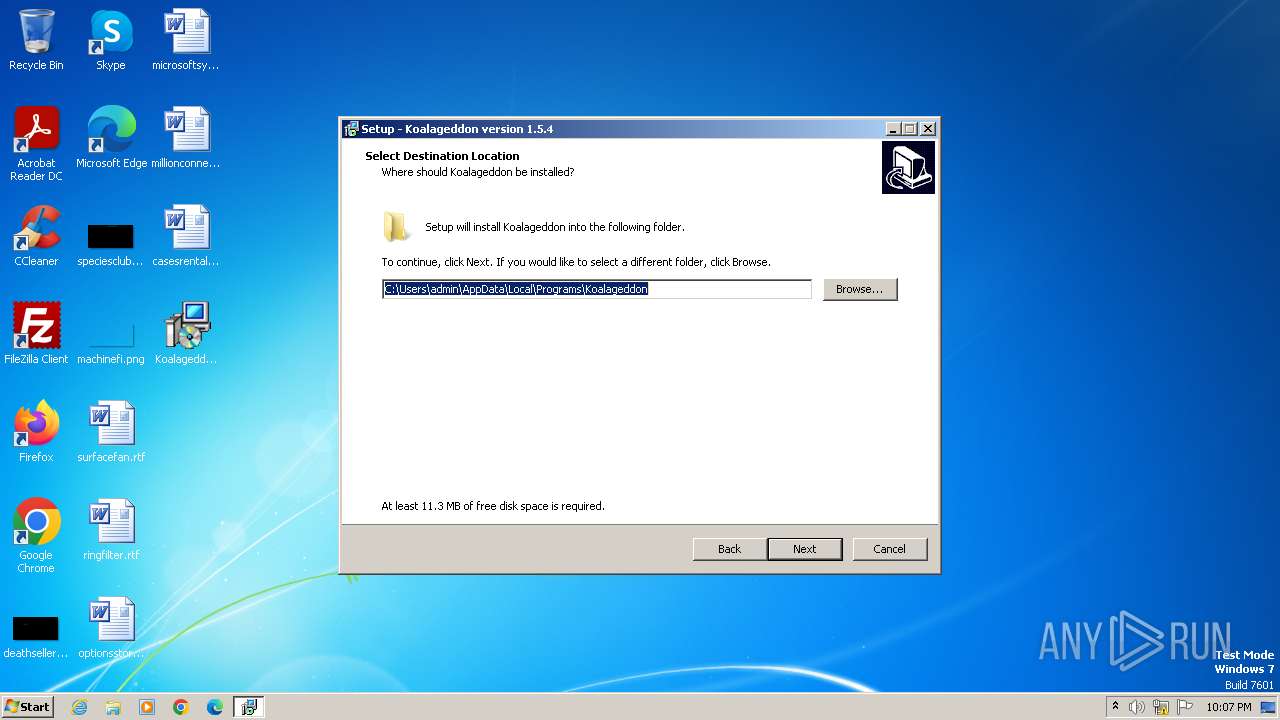
- KoalageddonInstaller.tmp (PID: 3460)
Manual execution by a user
- IntegrationWizard32.exe (PID: 3500)
- IntegrationWizard32.exe (PID: 3688)
- IntegrationWizard32.exe (PID: 3844)
- IntegrationWizard32.exe (PID: 3828)
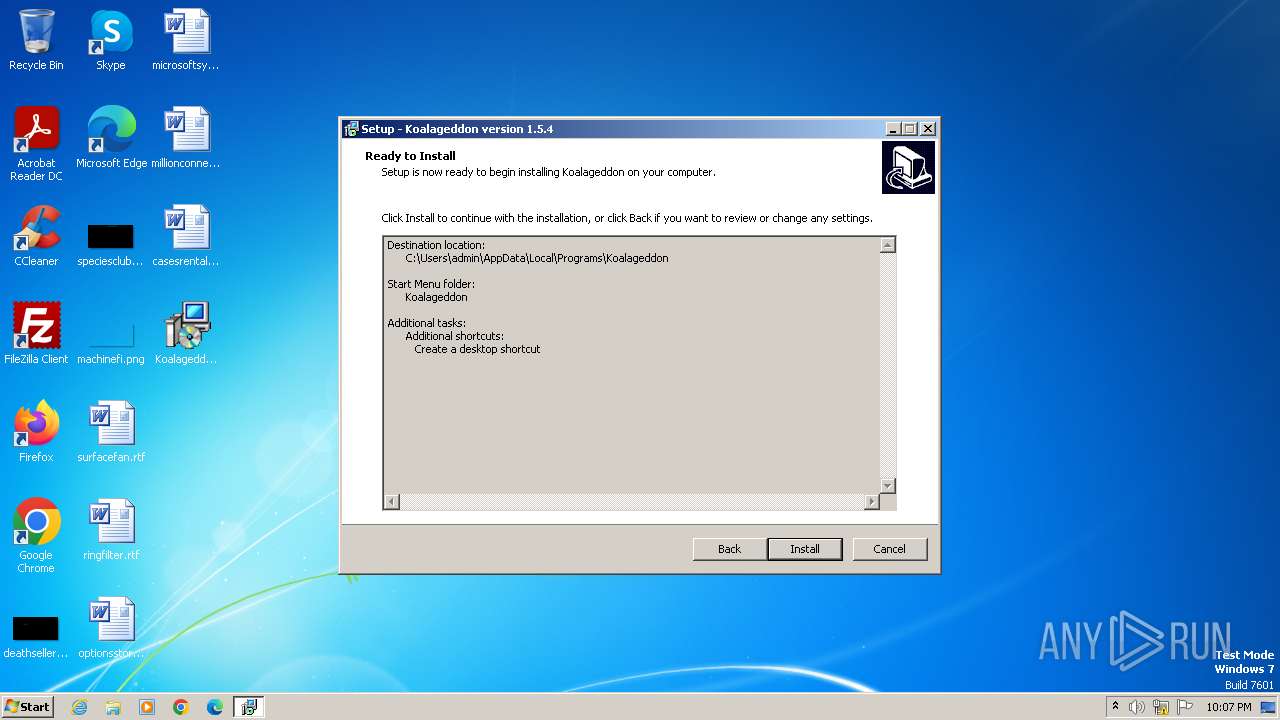
Creates files in the program directory
- IntegrationWizard32.exe (PID: 3688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:15 10:48:30+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
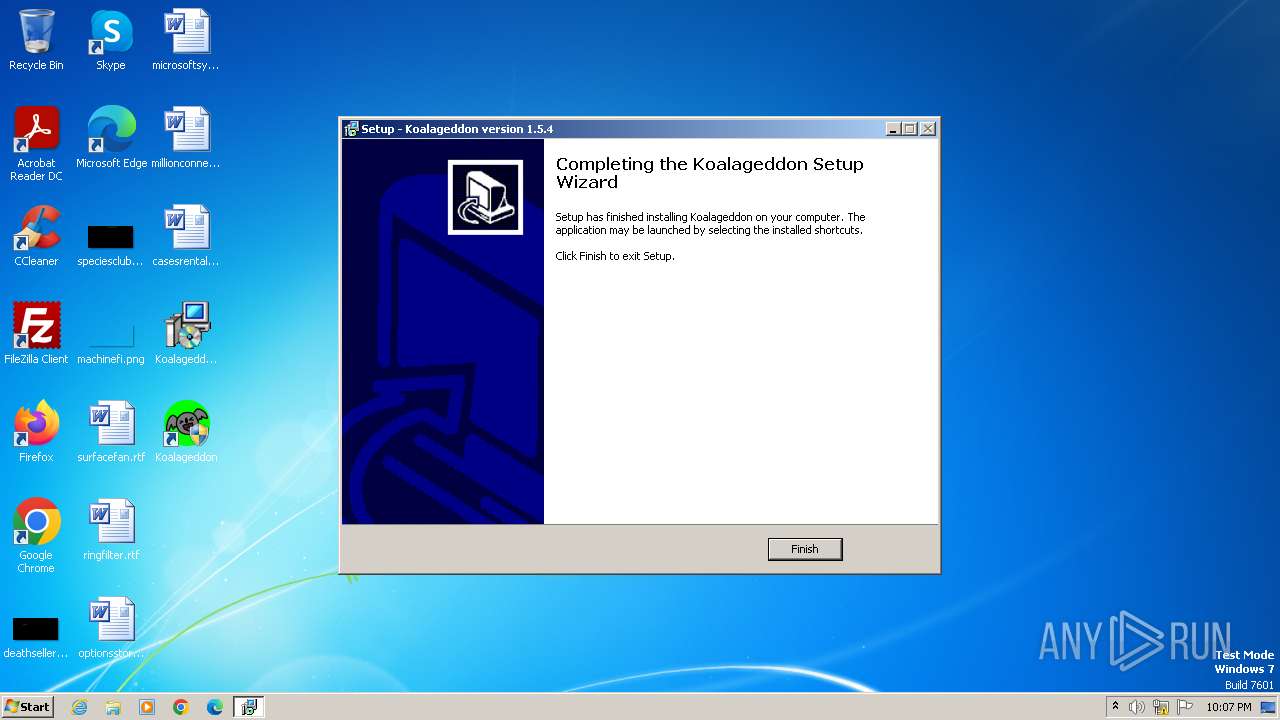
| FileVersionNumber: | 1.5.4.0 |
| ProductVersionNumber: | 1.5.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
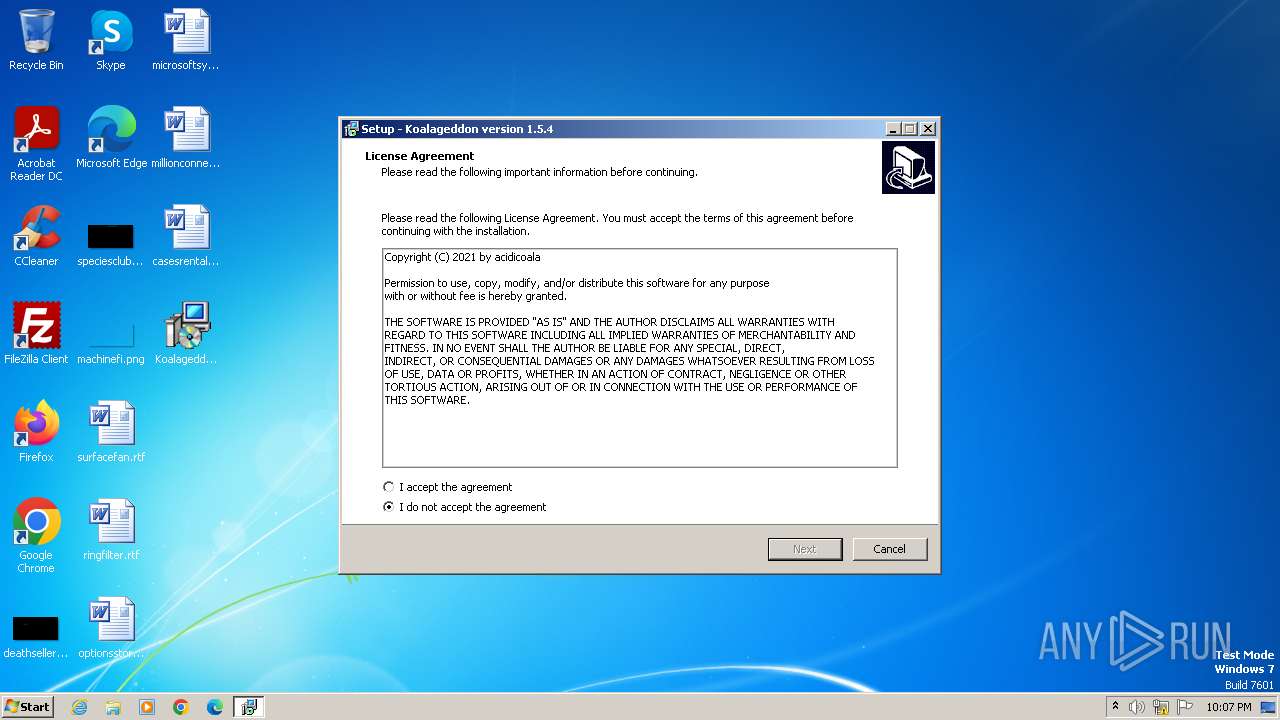
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | acidicoala |
| FileDescription: | Koalageddon Setup |
| FileVersion: | 1.5.4 |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Koalageddon |
| ProductVersion: | 1.5.4 |
Total processes
45
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3428 | "C:\Users\admin\Desktop\KoalageddonInstaller.exe" | C:\Users\admin\Desktop\KoalageddonInstaller.exe | — | explorer.exe | |||||||||||
User: admin Company: acidicoala Integrity Level: MEDIUM Description: Koalageddon Setup Exit code: 0 Version: 1.5.4 Modules
| |||||||||||||||
| 3460 | "C:\Users\admin\AppData\Local\Temp\is-3K30M.tmp\KoalageddonInstaller.tmp" /SL5="$60134,2244670,780800,C:\Users\admin\Desktop\KoalageddonInstaller.exe" | C:\Users\admin\AppData\Local\Temp\is-3K30M.tmp\KoalageddonInstaller.tmp | — | KoalageddonInstaller.exe | |||||||||||
User: admin Company: acidicoala Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
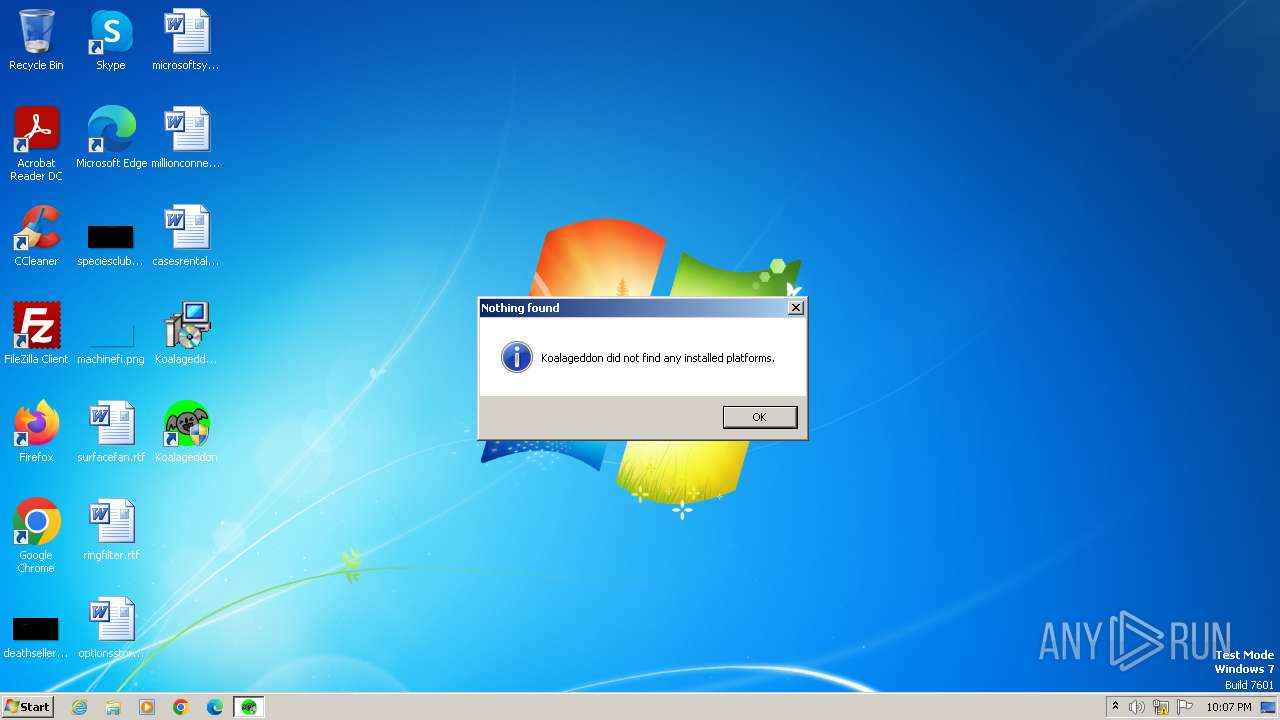
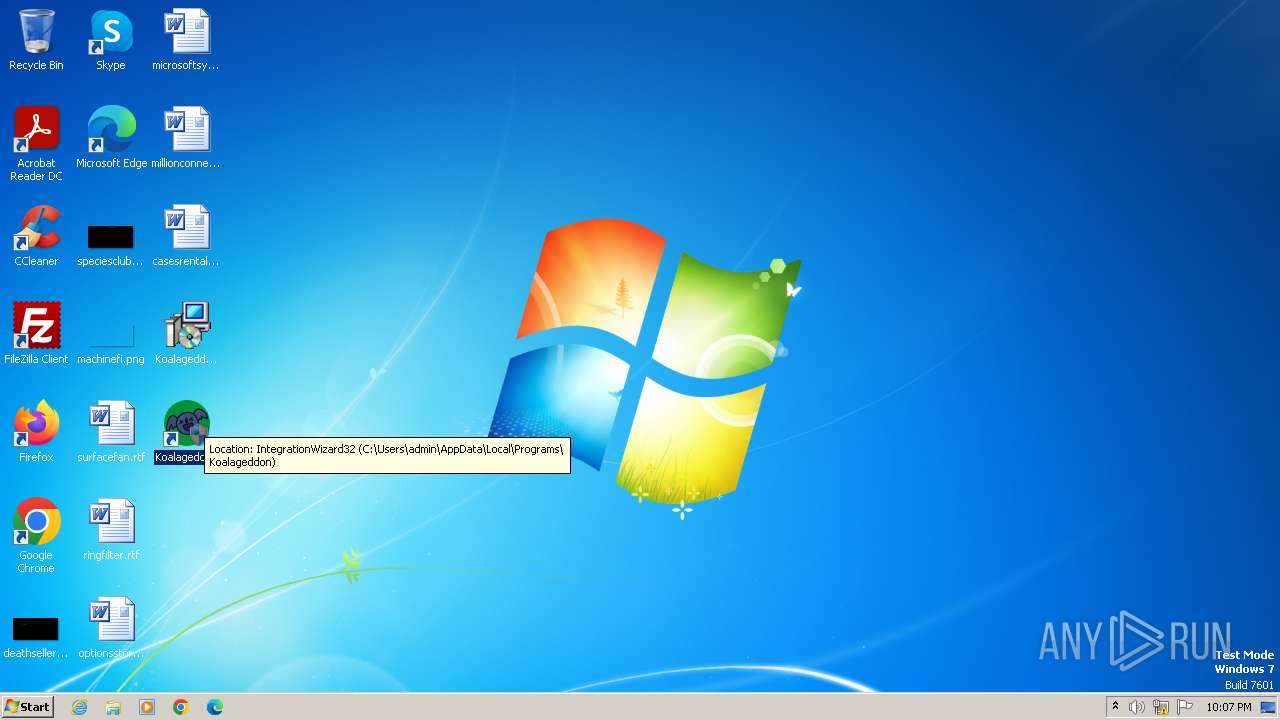
| 3500 | "C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe" | C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3688 | "C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe" | C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3828 | "C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe" | C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3844 | "C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe" | C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
909
Read events
901
Write events
2
Delete events
6
Modification events
| (PID) Process: | (3460) KoalageddonInstaller.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: 089137CA26A8EFD46ED427020848D62C3F67A13F45C00839D9E807B85FAE6AB2 | |||
| (PID) Process: | (3460) KoalageddonInstaller.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | |||
| (PID) Process: | (3460) KoalageddonInstaller.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3460) KoalageddonInstaller.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: 79B4394AED25E635F571F8ED78255972190B90976F01B17B7FB38B9CD122E999 | |||
| (PID) Process: | (3460) KoalageddonInstaller.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 840D0000685A8C67591EDA01 | |||
| (PID) Process: | (3460) KoalageddonInstaller.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3828) IntegrationWizard32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\acidicoala\Koalageddon |
| Operation: | write | Name: | INSTALL_DIR |
Value: C:\Users\admin\AppData\Local\Programs\Koalageddon | |||
| (PID) Process: | (3828) IntegrationWizard32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\acidicoala\Koalageddon |
| Operation: | write | Name: | WORKING_DIR |
Value: C:\ProgramData\acidicoala\Koalageddon | |||
Executable files
17
Suspicious files
4
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3460 | KoalageddonInstaller.tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\is-OAJ1S.tmp | executable | |
MD5:8D188050B9E4C0A5F0F24FCEA65B1133 | SHA256:6C2E59B3ECC0E453A141E7229E25CAFEB286EBE27C0C68096C18BFB3CE97B50A | |||
| 3460 | KoalageddonInstaller.tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\is-A1L7H.tmp | executable | |
MD5:1ECD0299C555A220ECBC07C981B7E57B | SHA256:10C42F378FBB106472A22A50C36E830427A2883C1E09CD1403FD3E41E23CCEBB | |||
| 3428 | KoalageddonInstaller.exe | C:\Users\admin\AppData\Local\Temp\is-3K30M.tmp\KoalageddonInstaller.tmp | executable | |
MD5:094DEB38AB94632C639192A61A62E820 | SHA256:47FEEC7D162557B5B989280D6F57BBD44C976D24063D5FE01A68BB4C230CC610 | |||
| 3460 | KoalageddonInstaller.tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\unins000.exe | executable | |
MD5:1ECD0299C555A220ECBC07C981B7E57B | SHA256:10C42F378FBB106472A22A50C36E830427A2883C1E09CD1403FD3E41E23CCEBB | |||
| 3460 | KoalageddonInstaller.tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\Injector64.exe | executable | |
MD5:B1C63C12DE6131DABD104707485758F3 | SHA256:BC9250F57748ACCE502A30D2488BB0EFAD7F0EEE1D10D2D839D4F56D8B86BEAB | |||
| 3460 | KoalageddonInstaller.tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\Injector32.exe | executable | |
MD5:A8066E5387A21092926451AA1538A709 | SHA256:F3E5EC14A045D9B2E75AE26AC0A2BBD58A41CF445F0528ABA2F028C063A291B3 | |||
| 3460 | KoalageddonInstaller.tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\is-24NUO.tmp | executable | |
MD5:A8066E5387A21092926451AA1538A709 | SHA256:F3E5EC14A045D9B2E75AE26AC0A2BBD58A41CF445F0528ABA2F028C063A291B3 | |||
| 3460 | KoalageddonInstaller.tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\is-SC7DG.tmp | executable | |
MD5:B1C63C12DE6131DABD104707485758F3 | SHA256:BC9250F57748ACCE502A30D2488BB0EFAD7F0EEE1D10D2D839D4F56D8B86BEAB | |||
| 3460 | KoalageddonInstaller.tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\IntegrationWizard32.exe | executable | |
MD5:8D188050B9E4C0A5F0F24FCEA65B1133 | SHA256:6C2E59B3ECC0E453A141E7229E25CAFEB286EBE27C0C68096C18BFB3CE97B50A | |||
| 3460 | KoalageddonInstaller.tmp | C:\Users\admin\AppData\Local\Programs\Koalageddon\Integration32.dll | executable | |
MD5:C5B9B71E86000D255CA57D9BFDE85B75 | SHA256:C91D5A5F269CA62CAE863695A9AB3C25D5E16B171E0789FBC73AB379BA958E9B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |