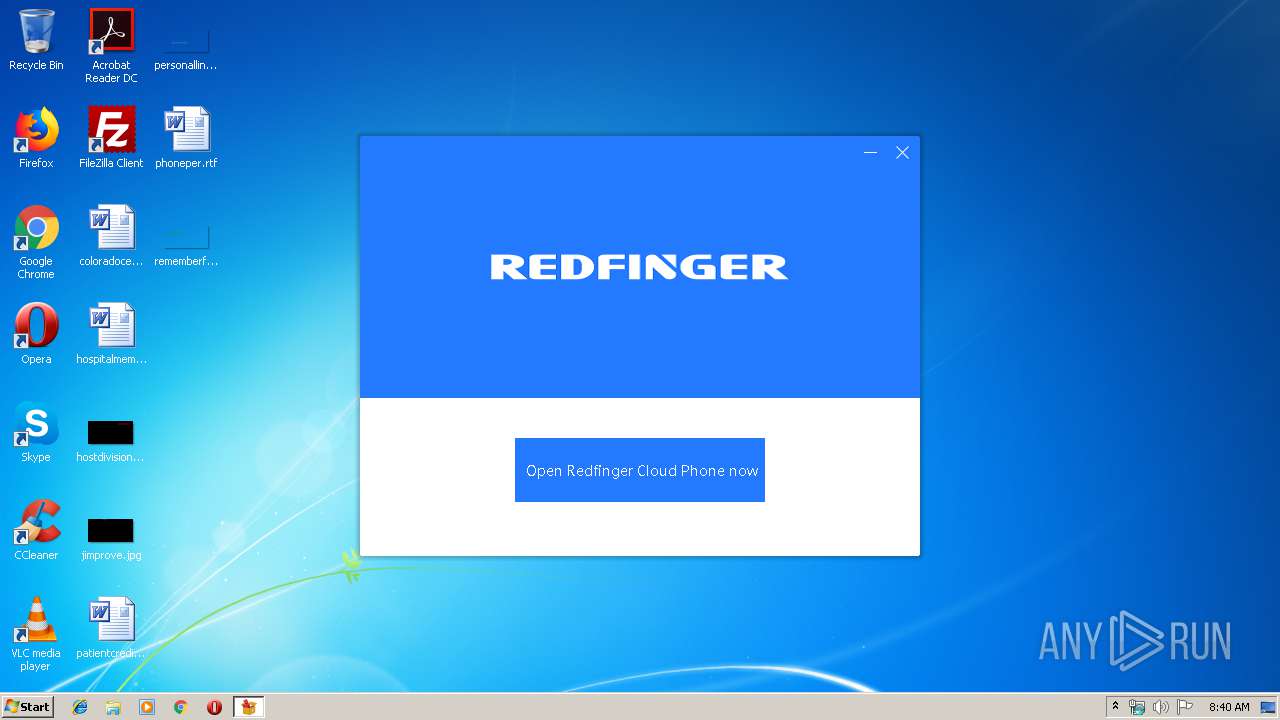
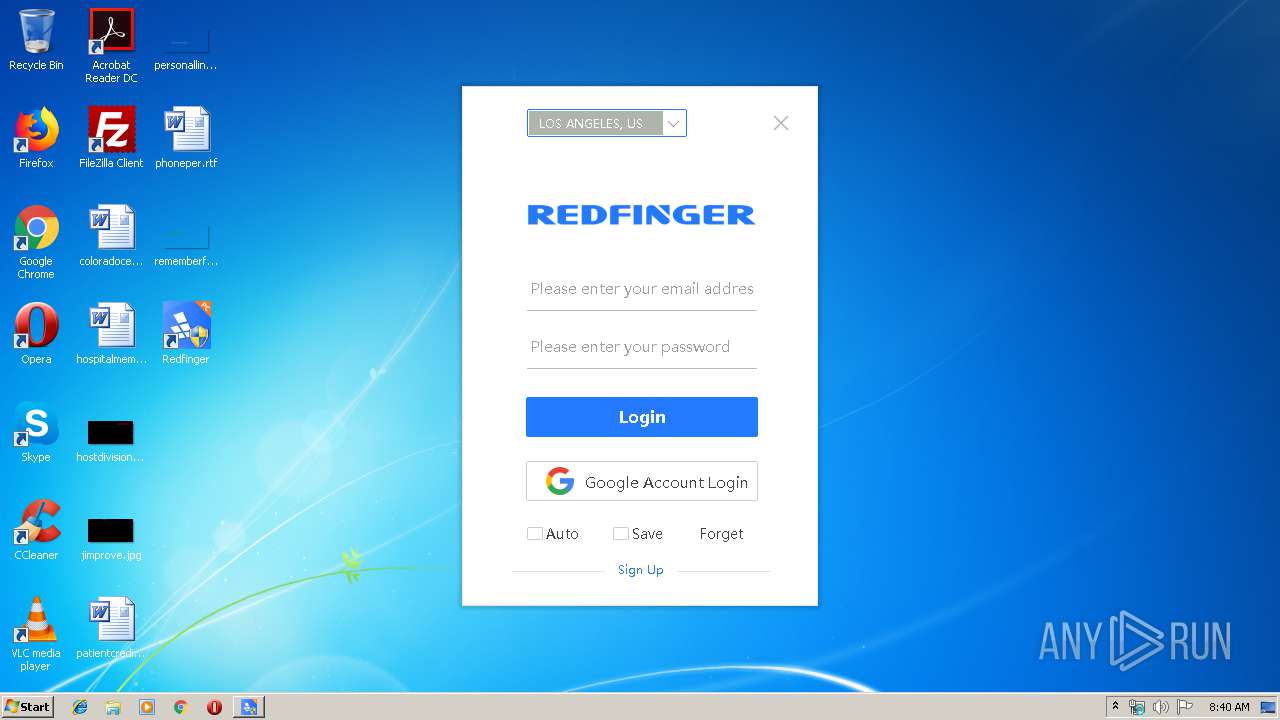
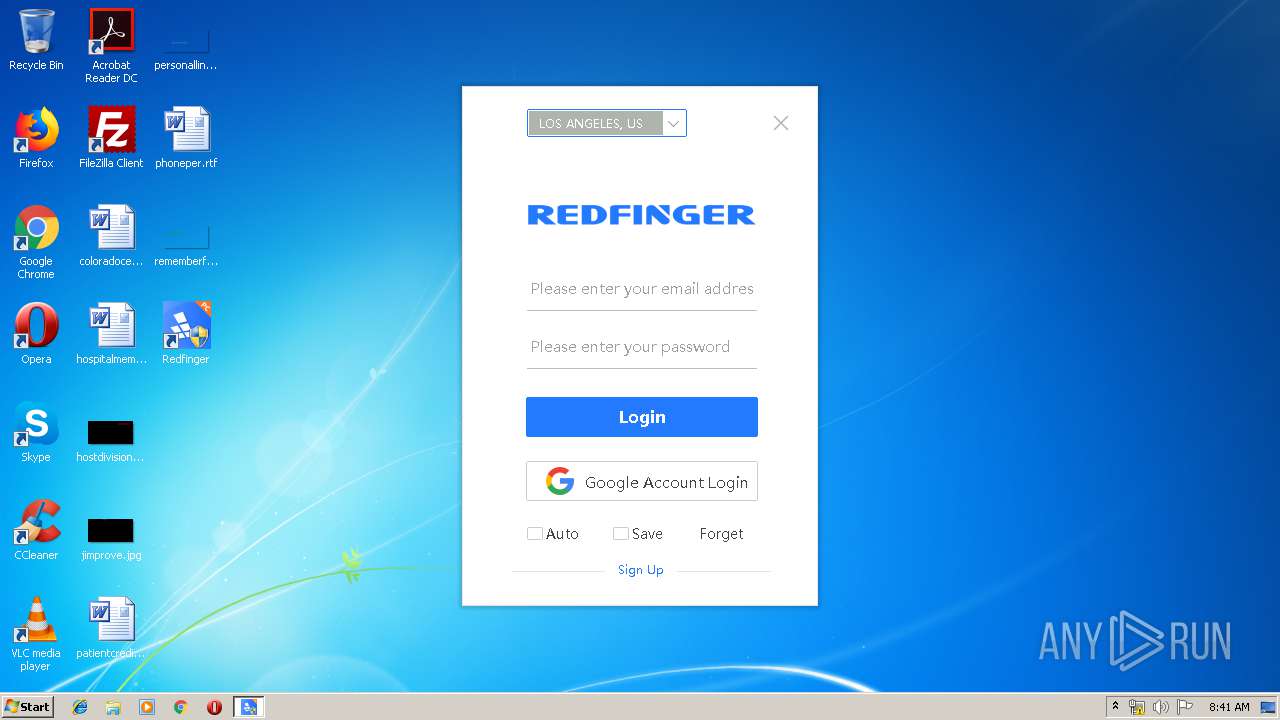
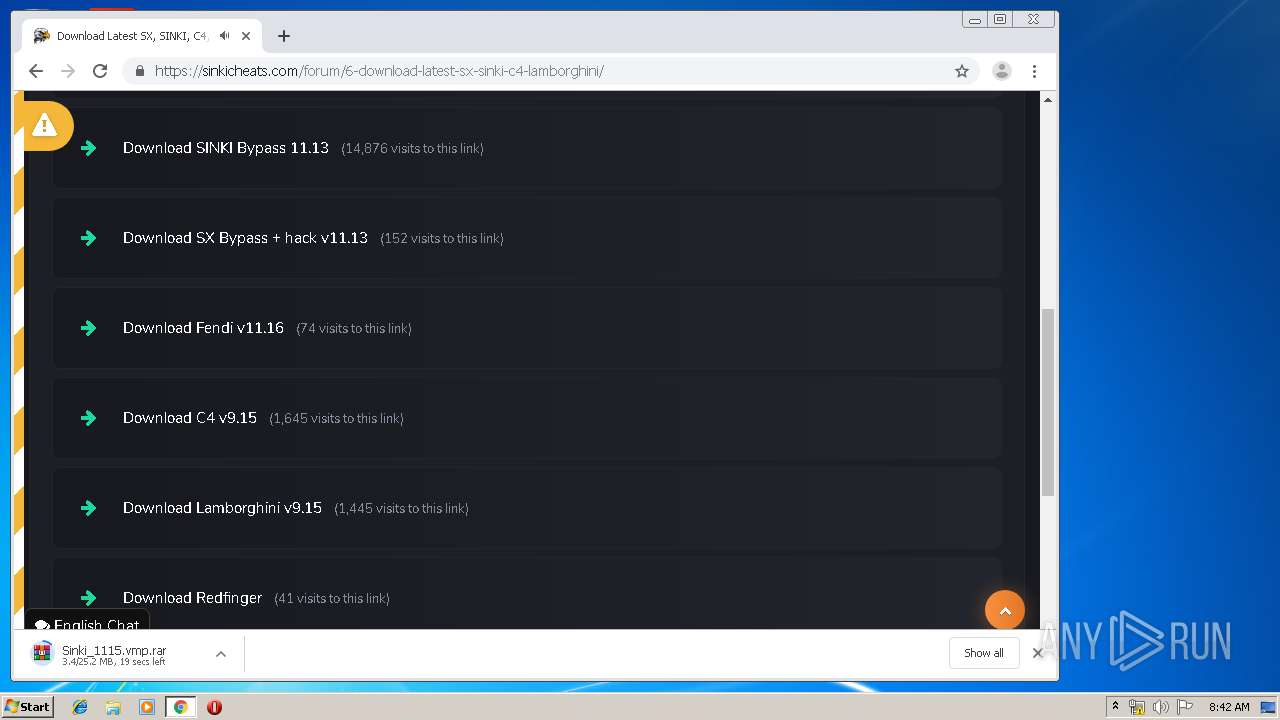
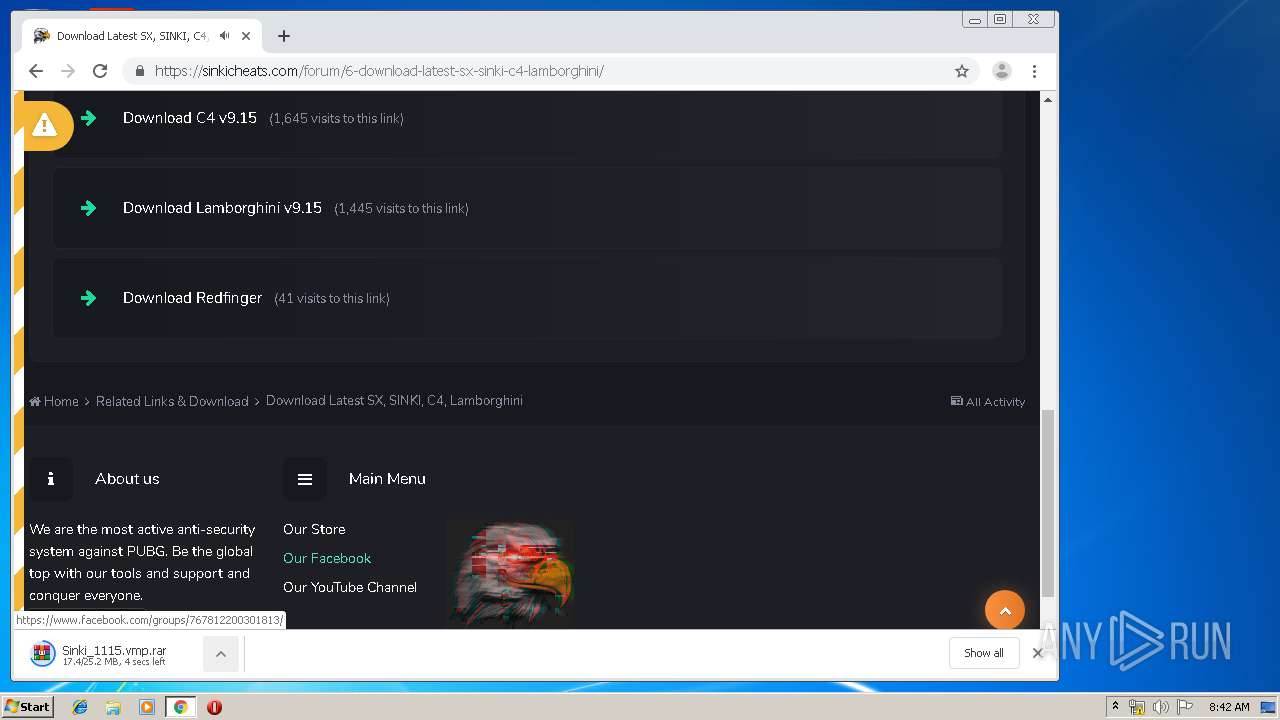
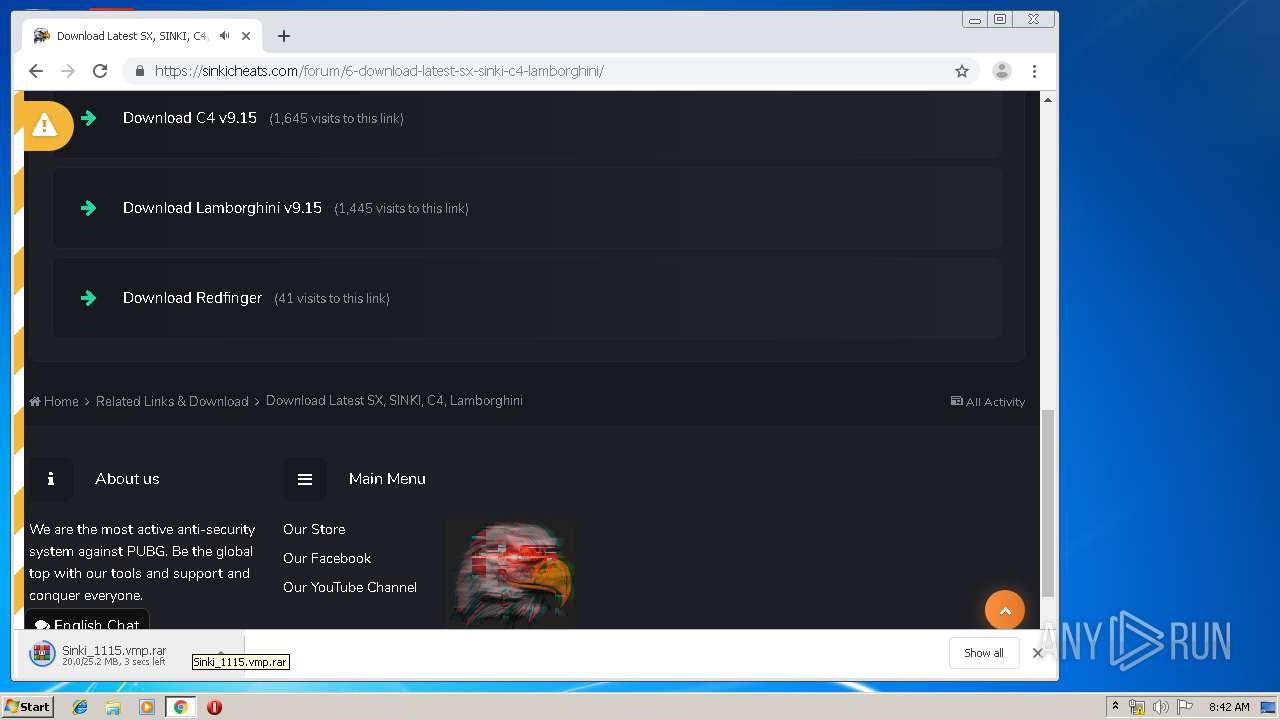
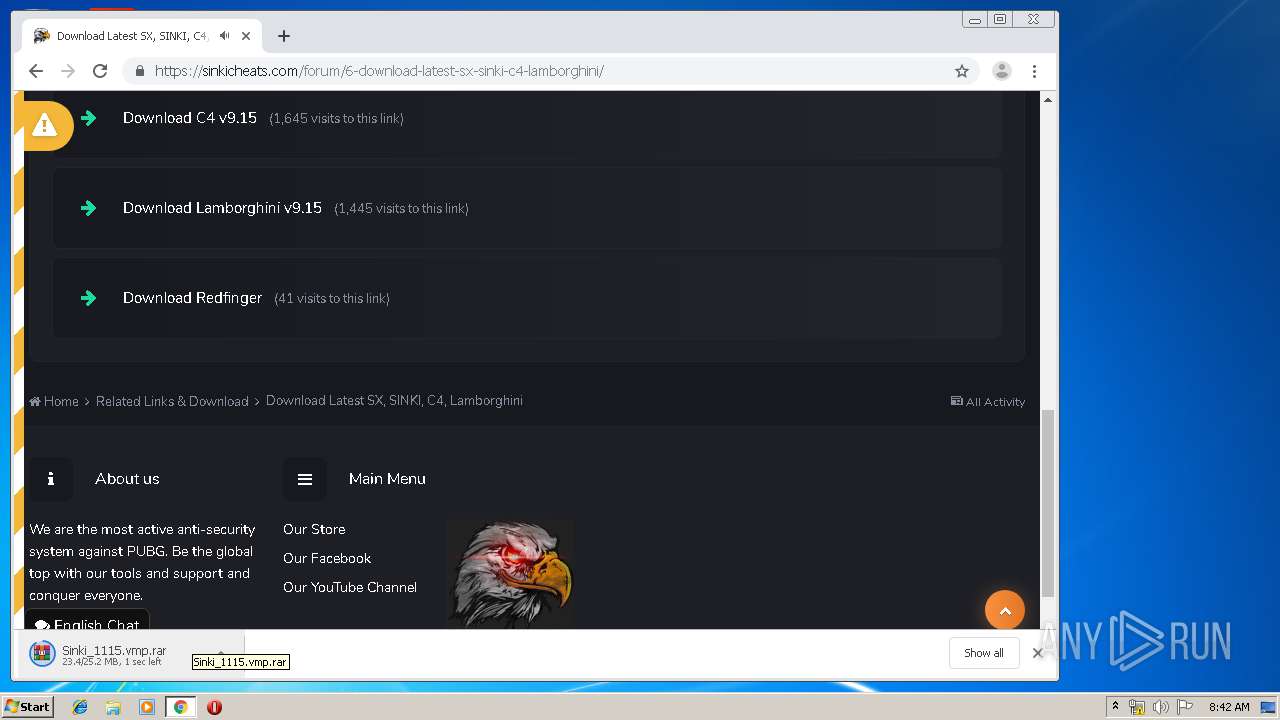
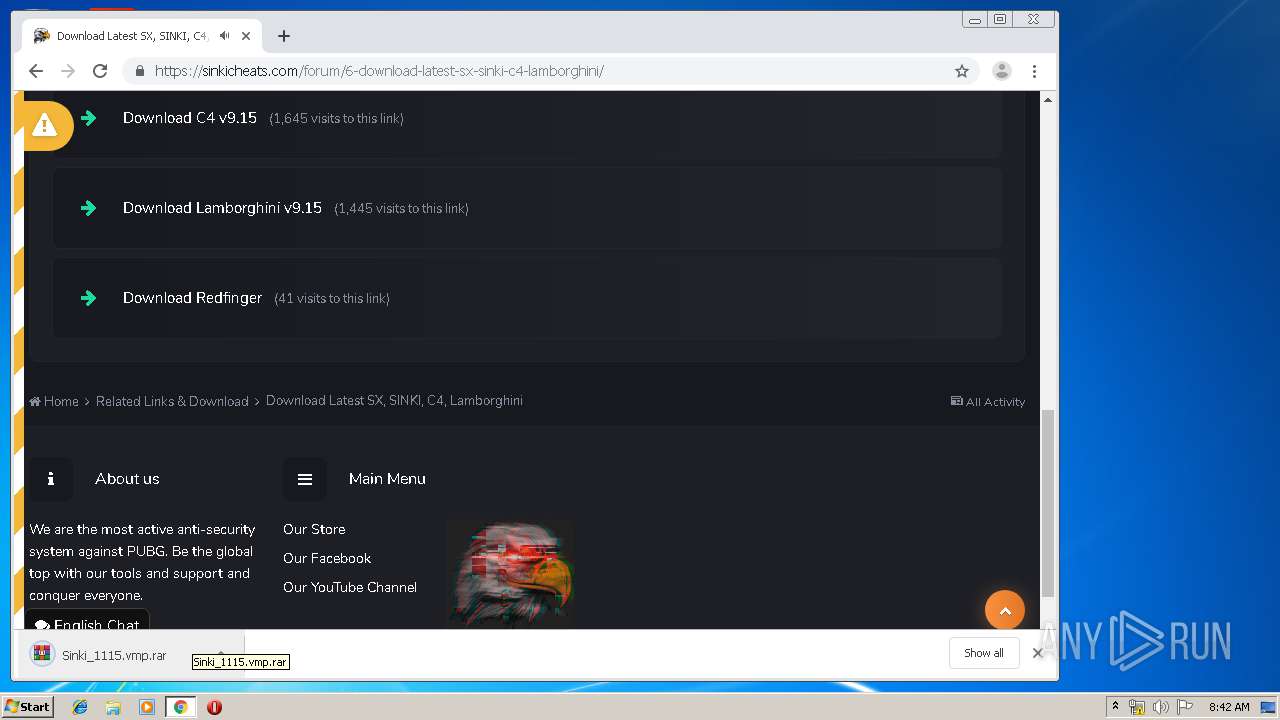
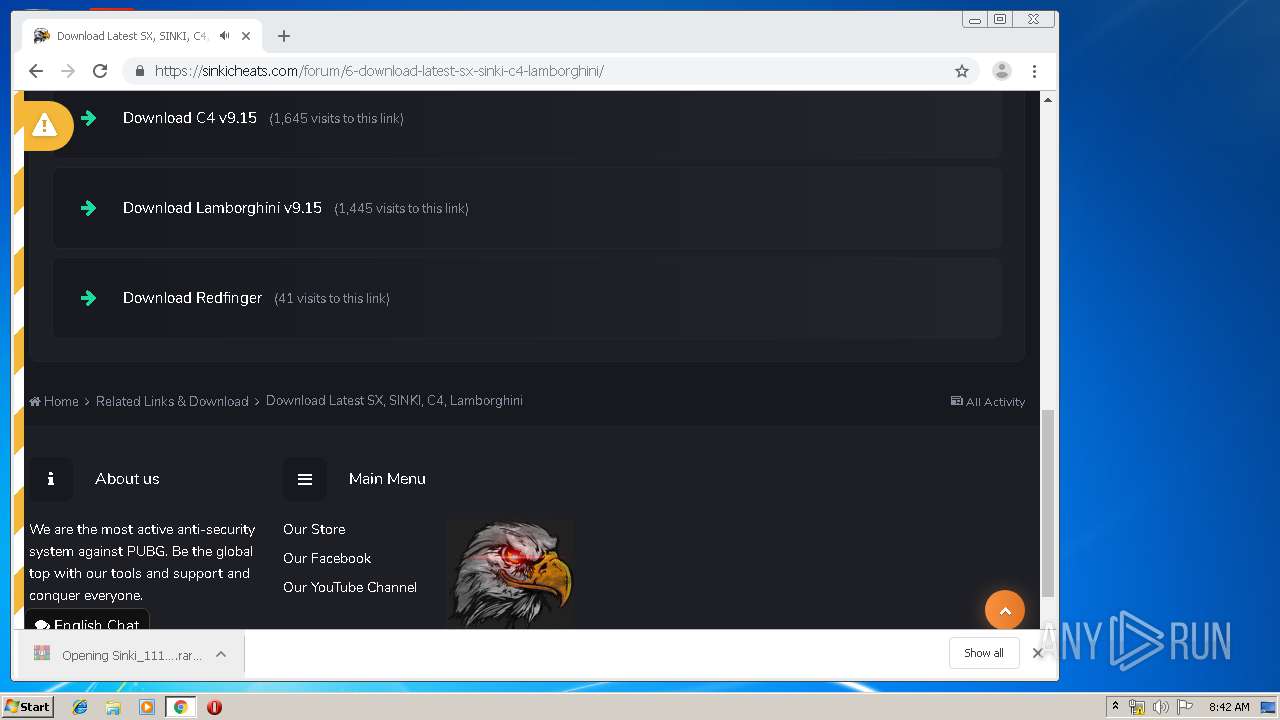
| download: | redfinger.exe |
| Full analysis: | https://app.any.run/tasks/674bc1c1-a7f5-459d-851d-6fd35f38b4ef |
| Verdict: | Malicious activity |
| Analysis date: | November 20, 2019, 08:39:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5B4518B0C0E20BC78BBBDE061CDC36BA |
| SHA1: | D2BD4E2CE435B5671C6A552951F399CADF01639A |
| SHA256: | 6E0127762E1F15CF87A1942B86FE1501E94891DA483E12AD6A38FFF5692F746F |
| SSDEEP: | 196608:cSYXc/uA0x60MjLKllTX92bNBw+YQgm6cmpy5:wceMjLsNX92vP3b5 |
MALICIOUS
Loads dropped or rewritten executable
- RedFingerPlayerGlobal.exe (PID: 292)
Application was dropped or rewritten from another process
- RedFingerPlayerGlobal.exe (PID: 292)
SUSPICIOUS
Executable content was dropped or overwritten
- redfinger.exe (PID: 688)
- WinRAR.exe (PID: 444)
Starts Internet Explorer
- RedFingerPlayerGlobal.exe (PID: 292)
Creates files in the program directory
- RedFingerPlayerGlobal.exe (PID: 292)
Creates a software uninstall entry
- redfinger.exe (PID: 688)
Creates files in the user directory
- redfinger.exe (PID: 688)
Uses WMIC.EXE to obtain a system information
- RedFingerPlayerGlobal.exe (PID: 292)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2080)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2952)
Manual execution by user
- chrome.exe (PID: 2080)
Dropped object may contain Bitcoin addresses
- redfinger.exe (PID: 688)
- chrome.exe (PID: 2080)
Reads the hosts file
- chrome.exe (PID: 2080)
- chrome.exe (PID: 3928)
Reads Internet Cache Settings
- chrome.exe (PID: 2080)
Application launched itself
- chrome.exe (PID: 2080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:28 08:44:10+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 660992 |
| InitializedDataSize: | 7825408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6ced0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Oct-2019 07:44:10 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 28-Oct-2019 07:44:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000A1597 | 0x000A1600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60429 |
.rdata | 0x000A3000 | 0x0002D5AA | 0x0002D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.25009 |
.data | 0x000D1000 | 0x00008F68 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.69555 |
.rsrc | 0x000DA000 | 0x00735D40 | 0x00735E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99561 |
.reloc | 0x00810000 | 0x0000A2E0 | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.50237 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06216 | 651 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.09278 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 3.37232 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 4.71168 | 3752 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 5.11819 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 3.13741 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 4.1257 | 67624 | UNKNOWN | Chinese - PRC | RT_ICON |
8 | 4.97344 | 9640 | UNKNOWN | Chinese - PRC | RT_ICON |
9 | 5.2319 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
10 | 5.7157 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WS2_32.dll |
Total processes
85
Monitored processes
42
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\RedFingerPlayerGlobal\RedFingerPlayerGlobal.exe" | C:\Program Files\RedFingerPlayerGlobal\RedFingerPlayerGlobal.exe | redfinger.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
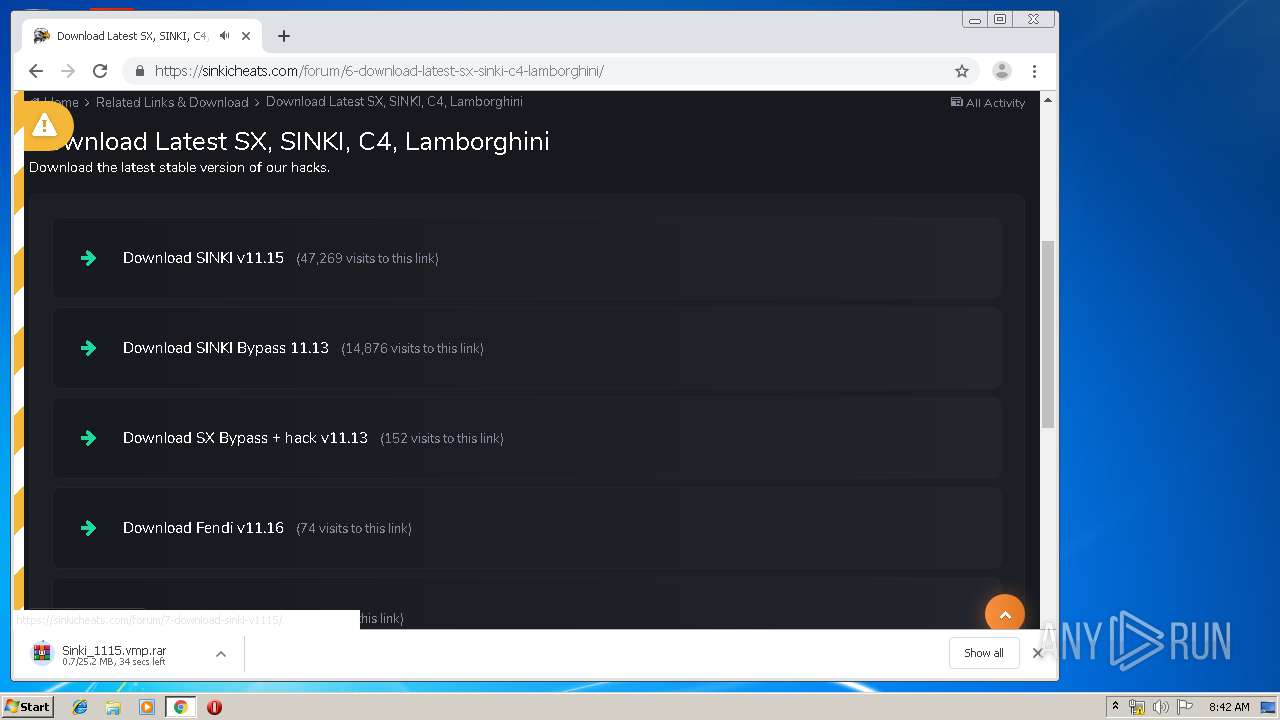
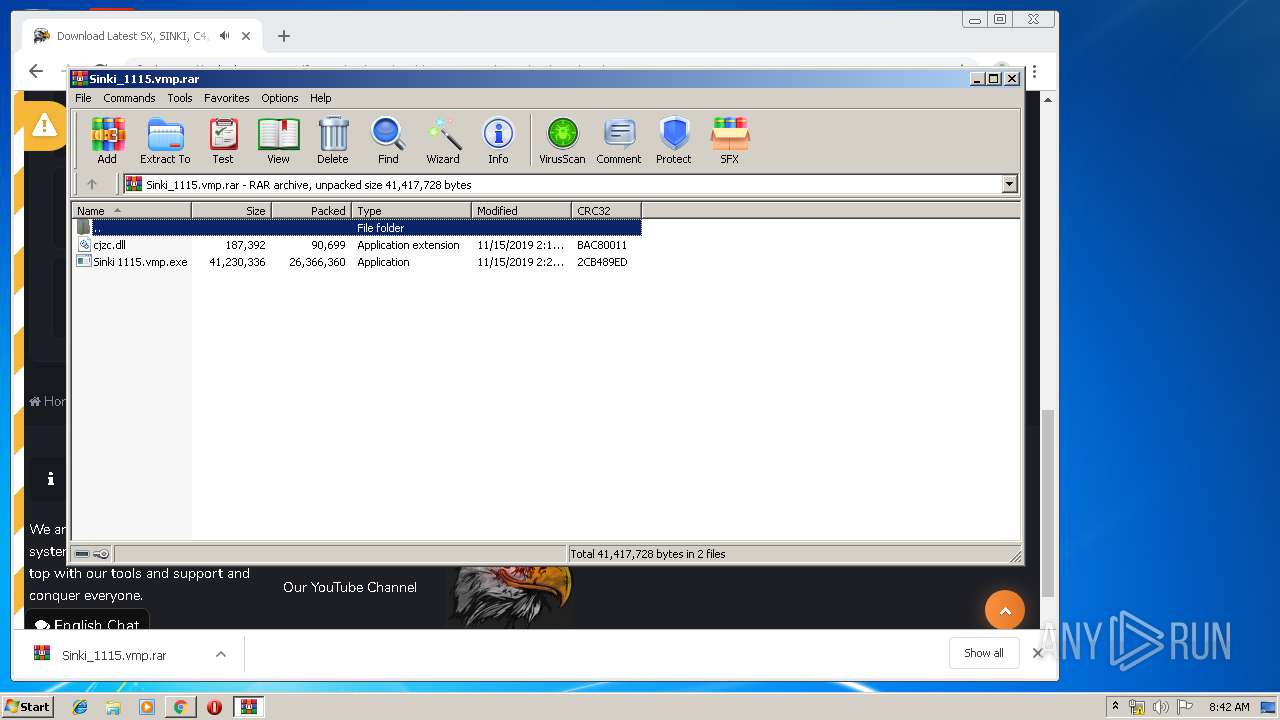
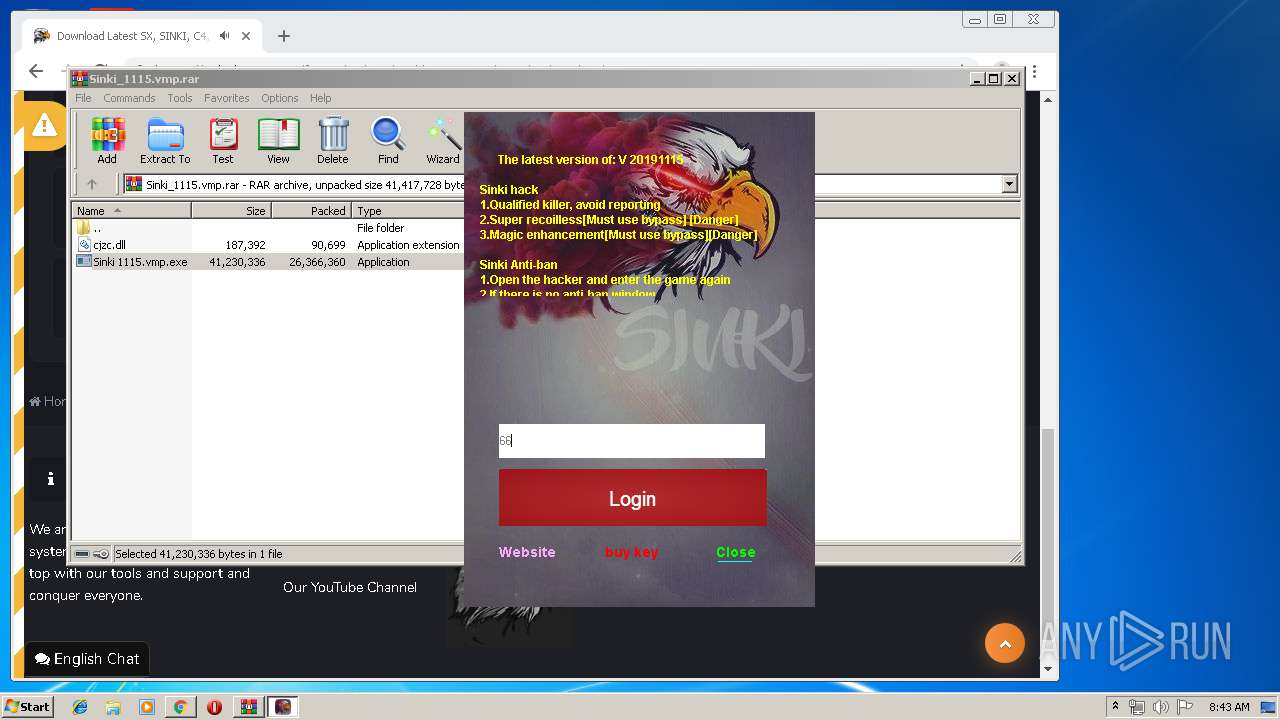
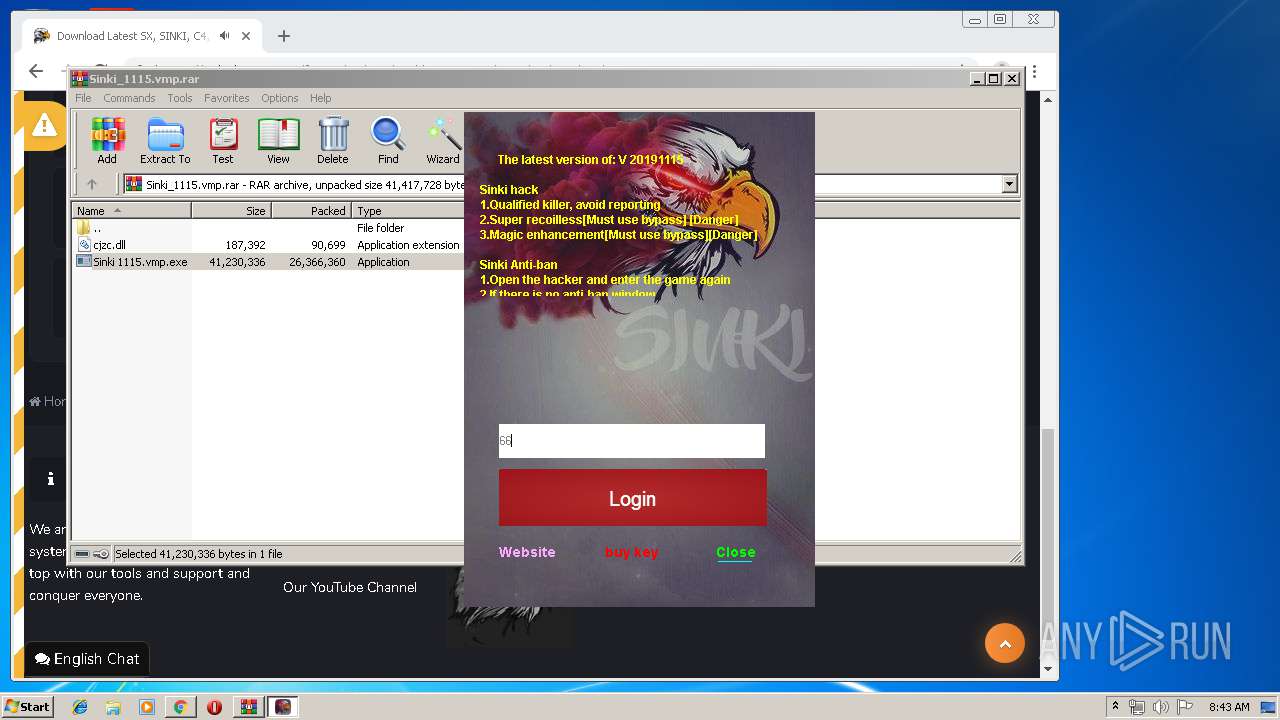
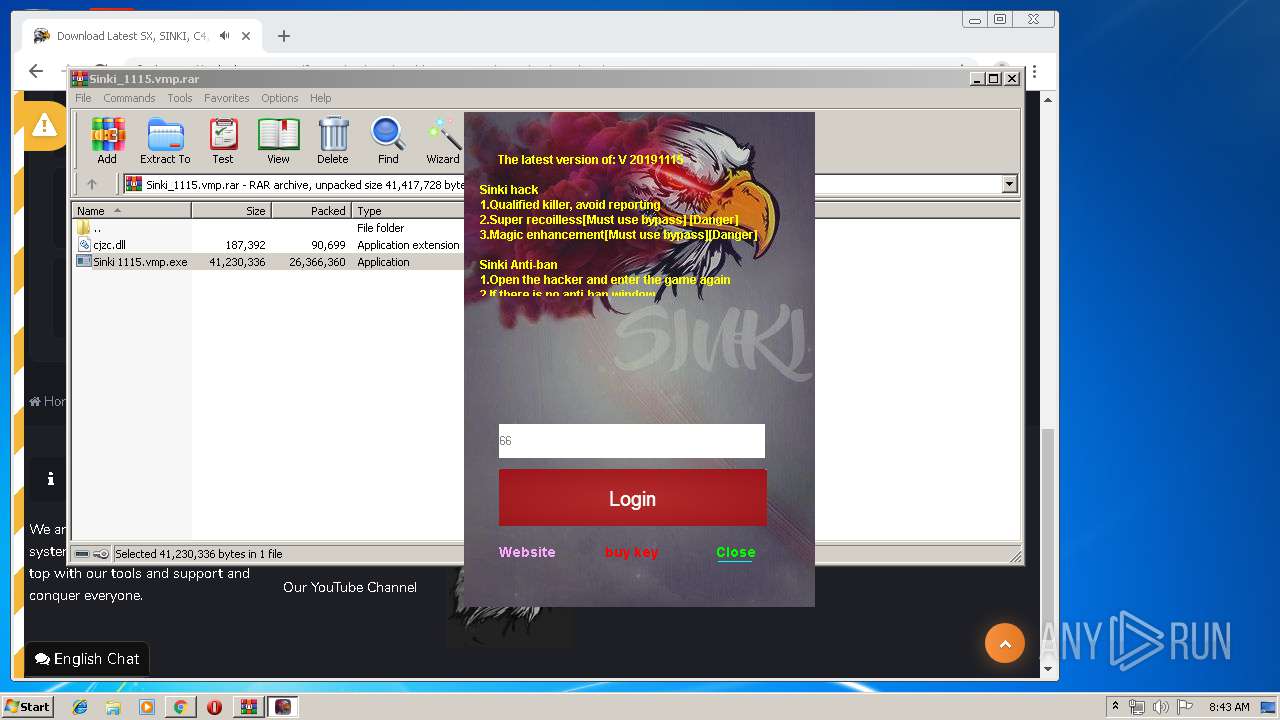
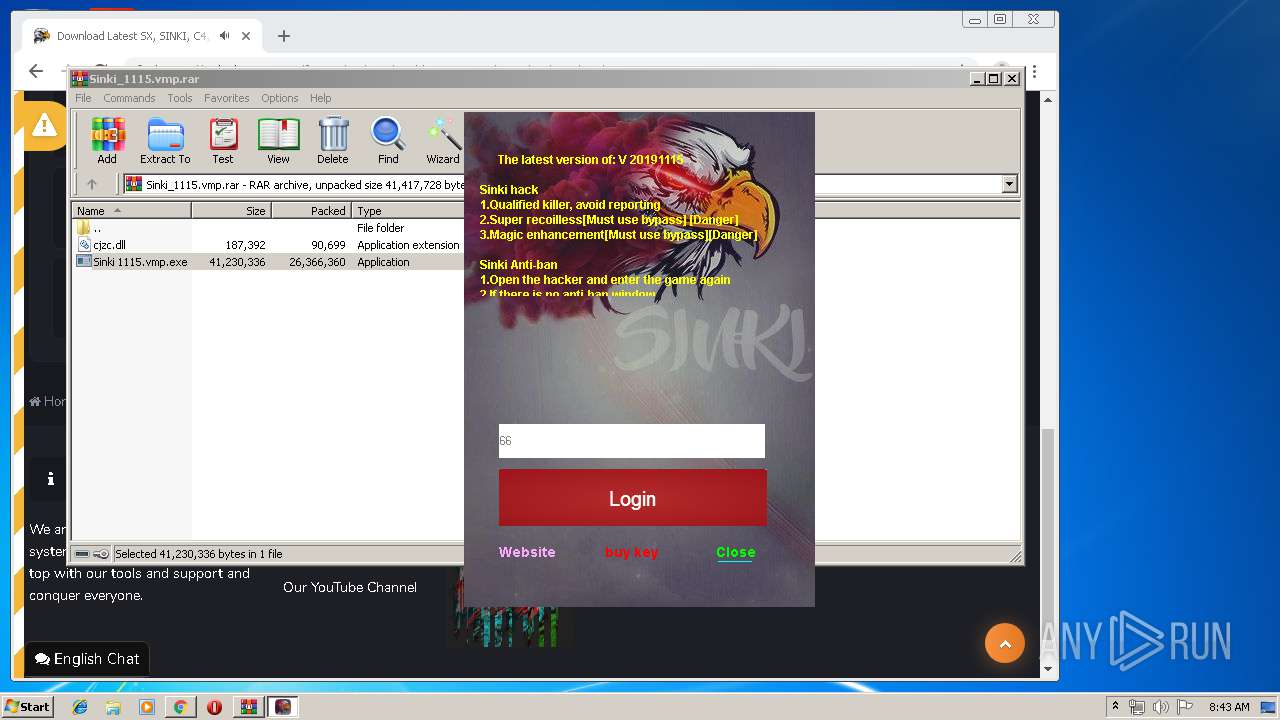
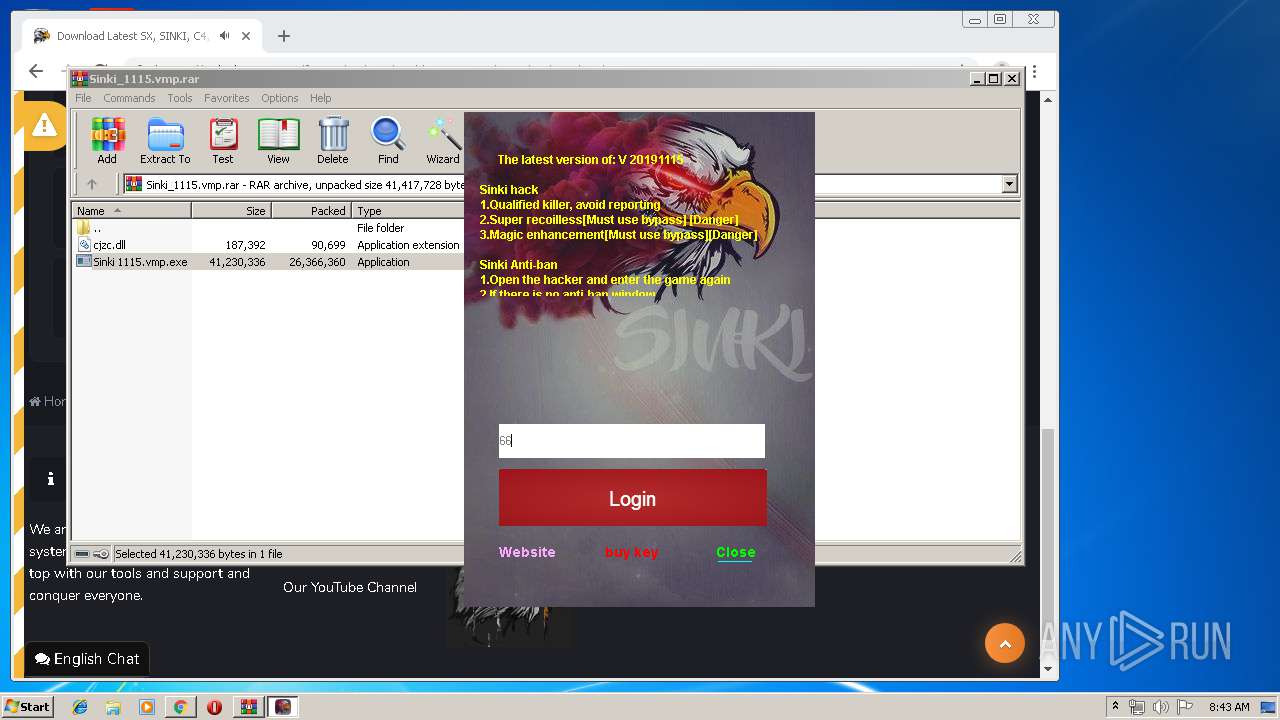
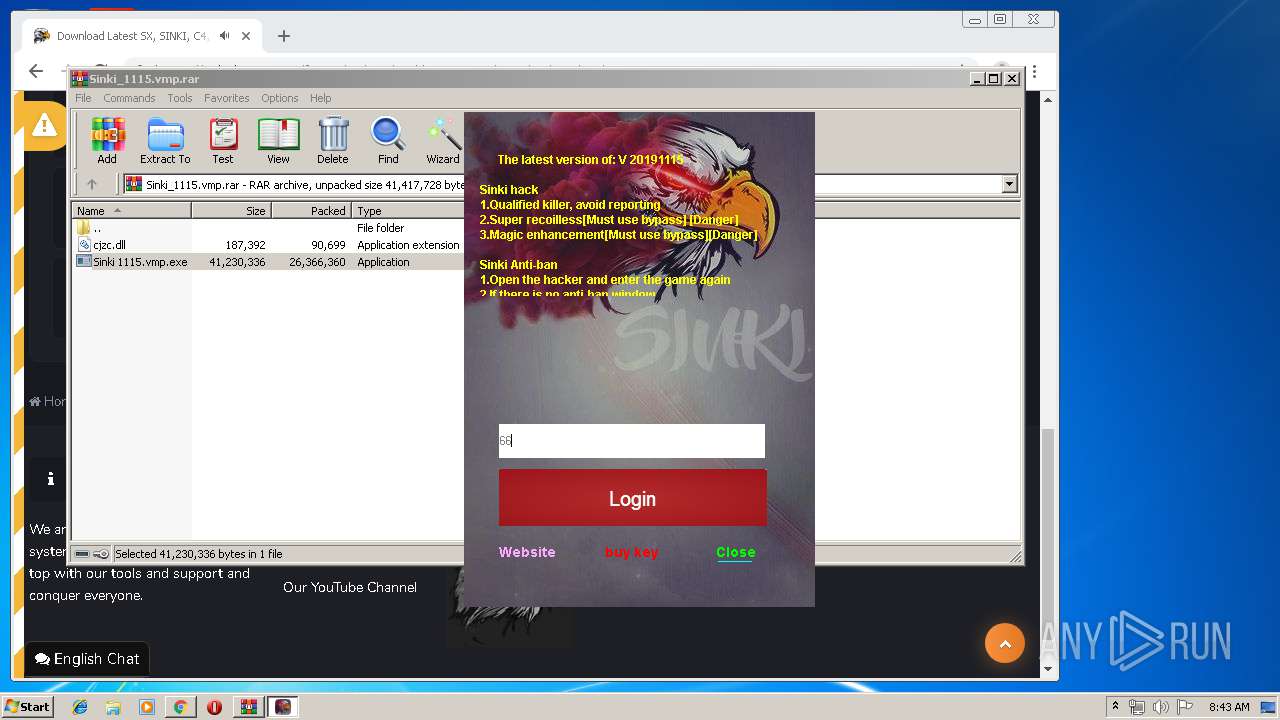
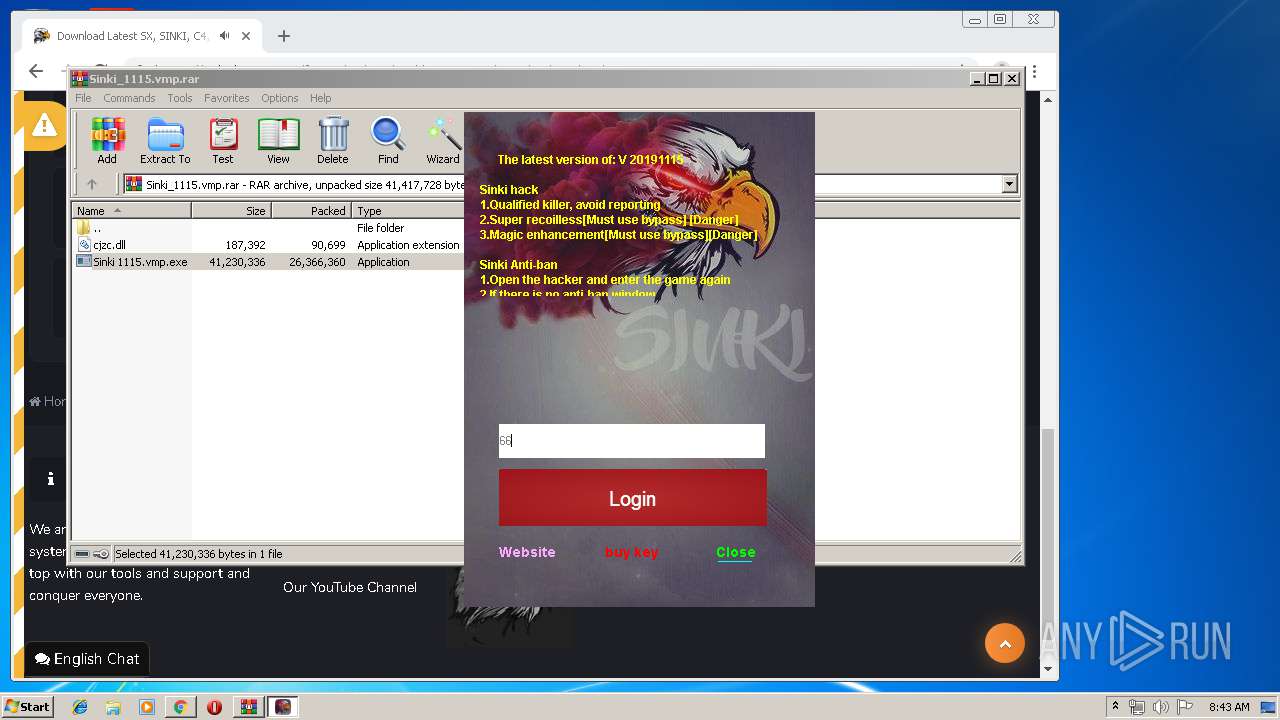
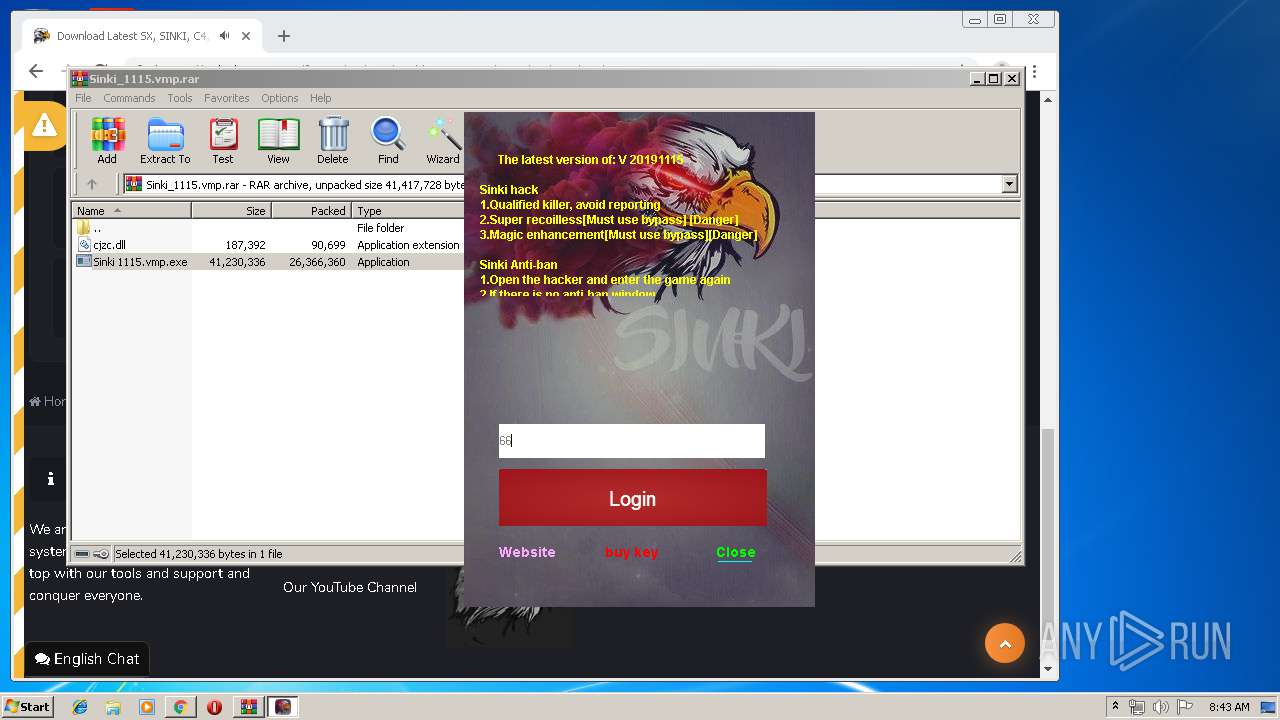
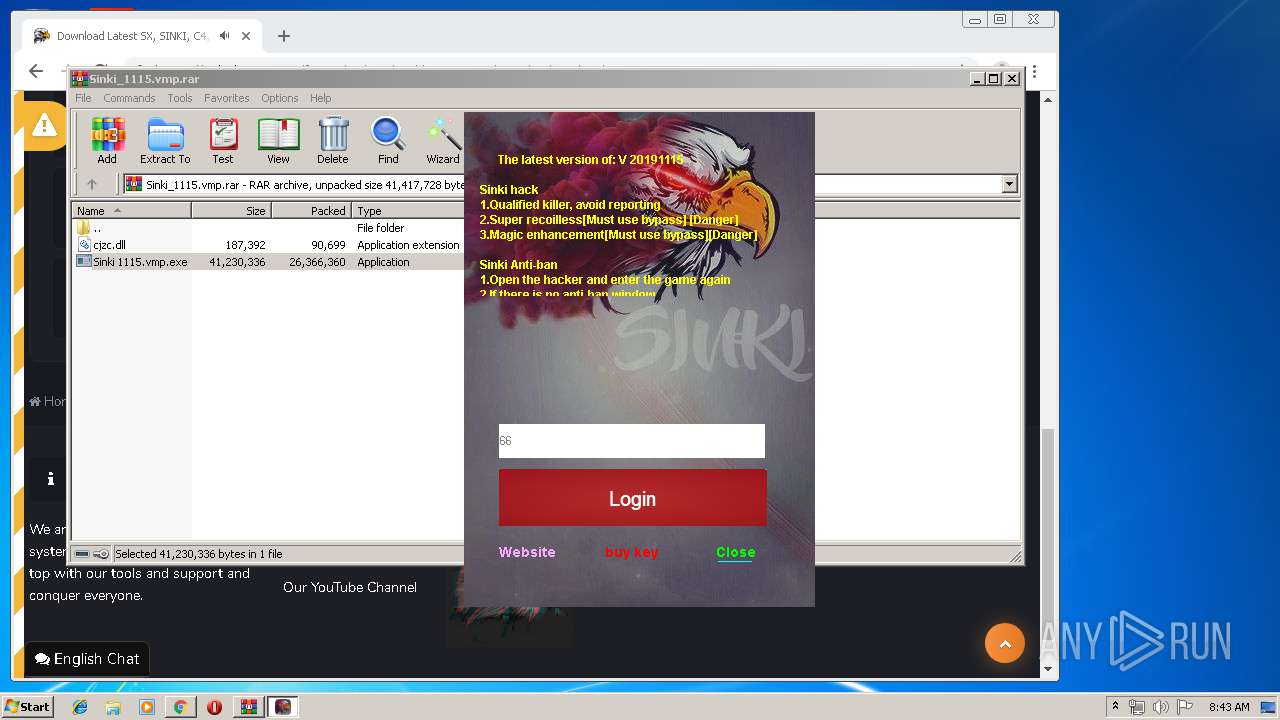
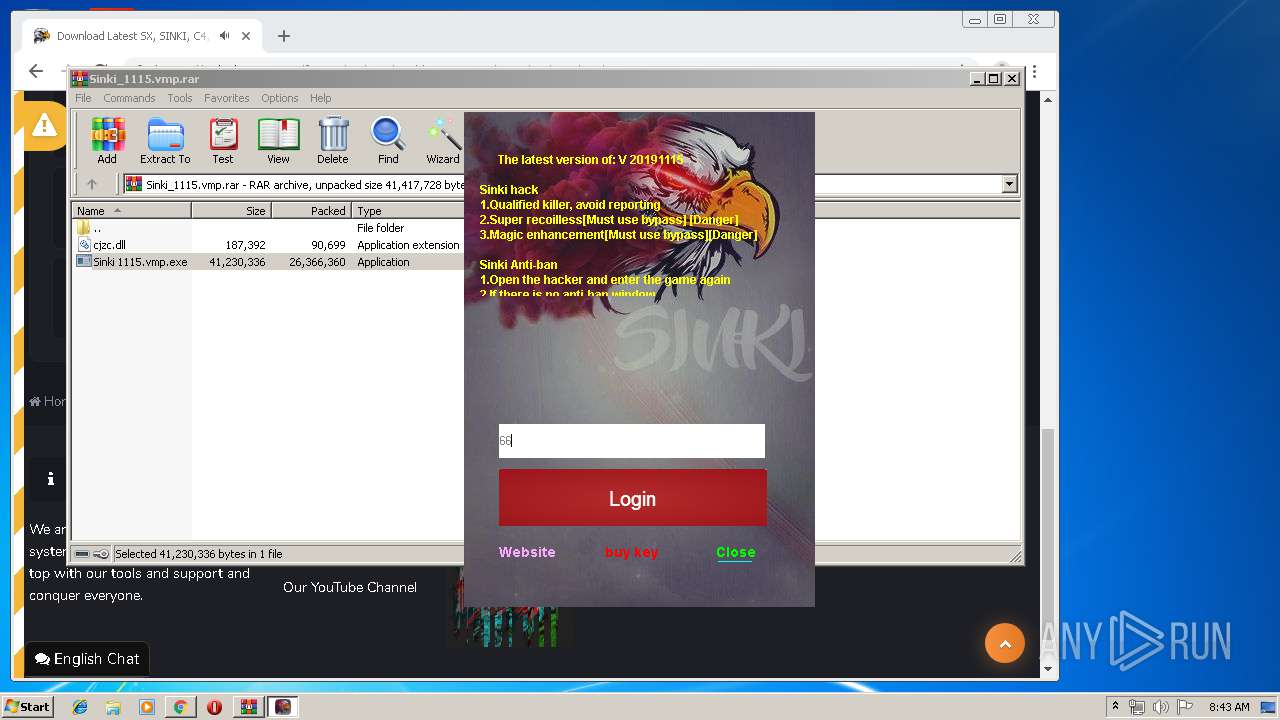
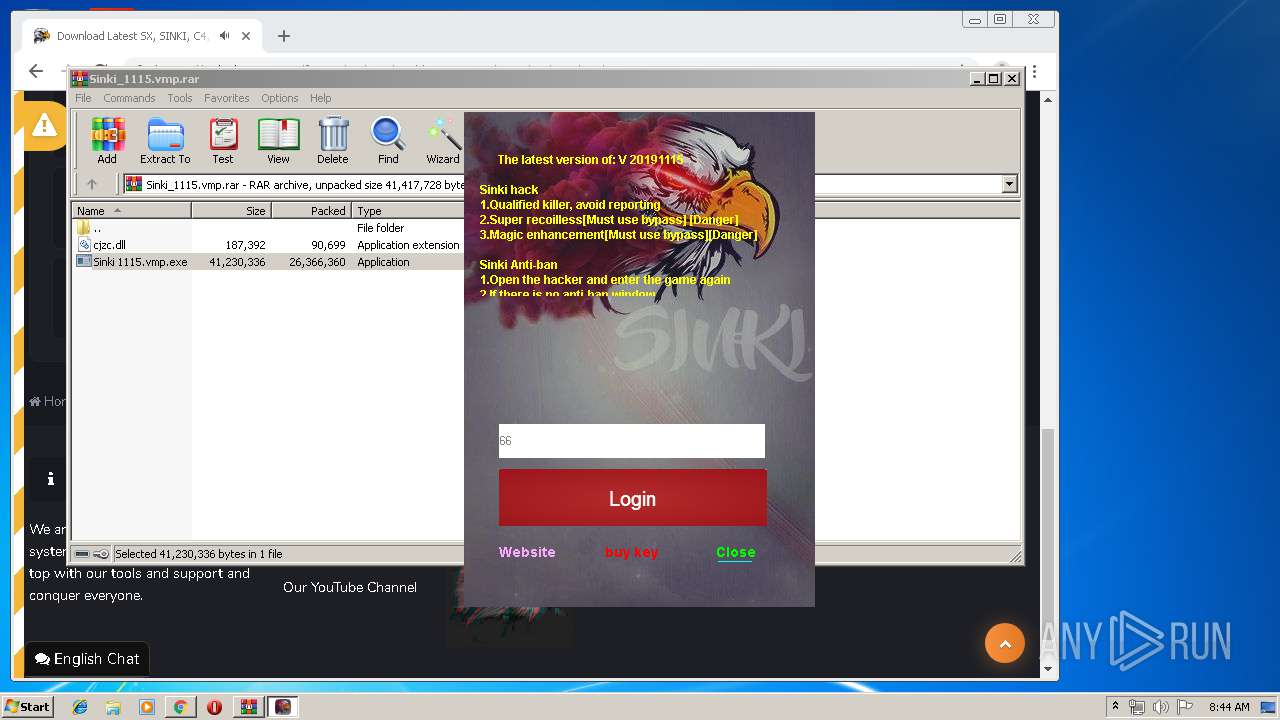
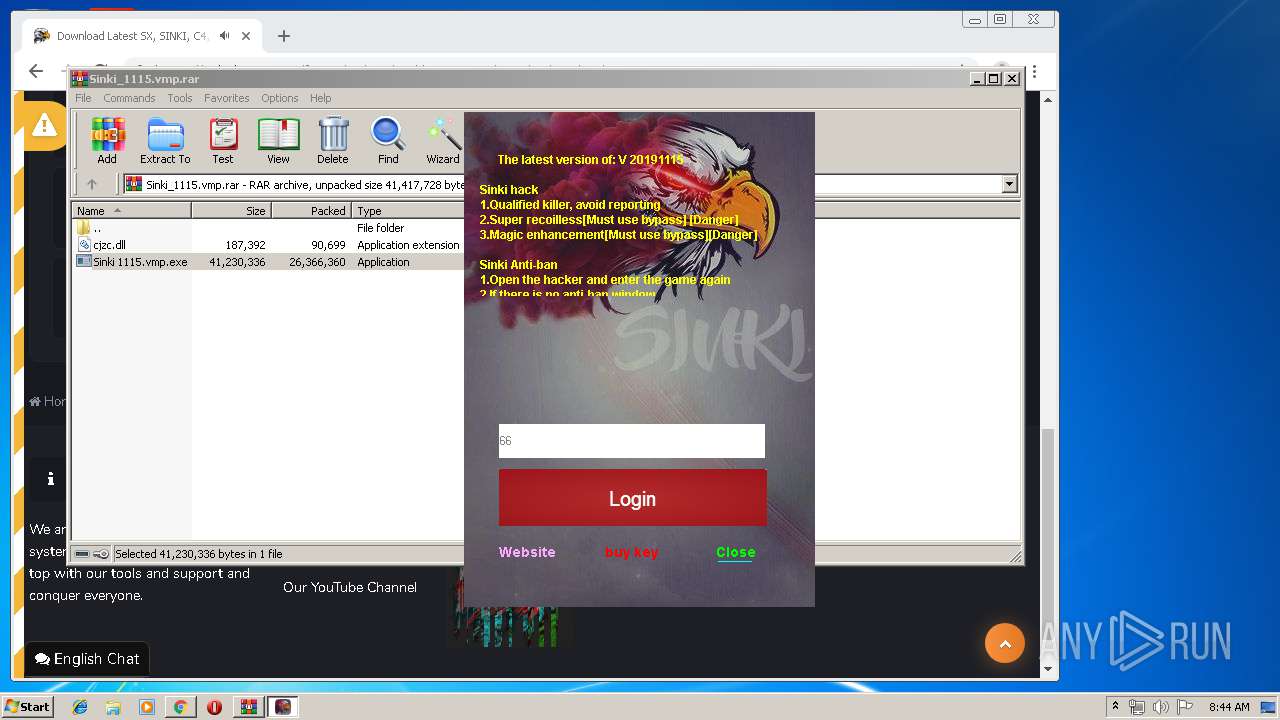
| 444 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Sinki_1115.vmp.rar" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,17318886728488951923,16469663510028672941,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9142048893066630851 --mojo-platform-channel-handle=3752 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,17318886728488951923,16469663510028672941,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9344683638161955760 --mojo-platform-channel-handle=3864 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 688 | "C:\Users\admin\AppData\Local\Temp\redfinger.exe" | C:\Users\admin\AppData\Local\Temp\redfinger.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,17318886728488951923,16469663510028672941,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12022087271655181923 --mojo-platform-channel-handle=3424 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,17318886728488951923,16469663510028672941,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1571617943260040797 --mojo-platform-channel-handle=3340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3288 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,17318886728488951923,16469663510028672941,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2387739492877092471 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,17318886728488951923,16469663510028672941,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9833253331506049336 --mojo-platform-channel-handle=3364 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 000
Read events
1 797
Write events
197
Delete events
6
Modification events
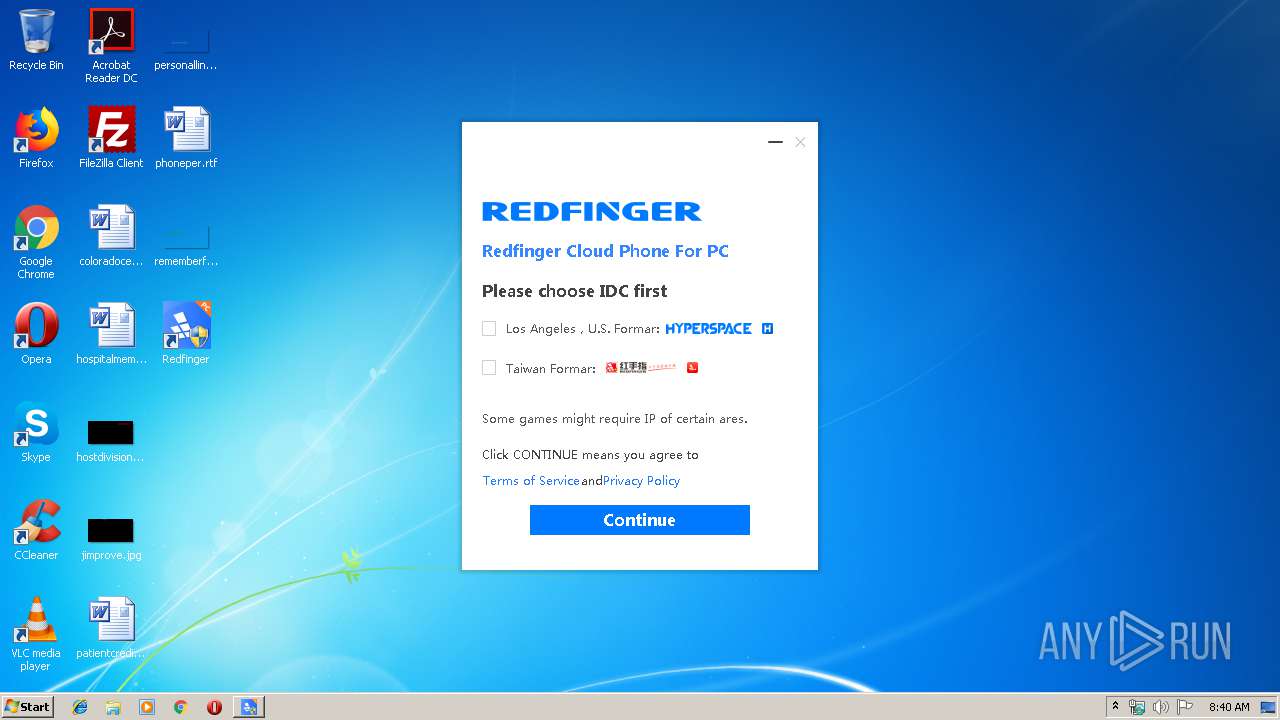
| (PID) Process: | (688) redfinger.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Redfinger |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\RedFingerPlayerGlobal\uninst.exe | |||
| (PID) Process: | (688) redfinger.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Redfinger |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\RedFingerPlayerGlobal\RedFingerPlayerGlobal.exe | |||
| (PID) Process: | (688) redfinger.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Redfinger |
| Operation: | write | Name: | DisplayName |
Value: Redfinger | |||
| (PID) Process: | (688) redfinger.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Redfinger |
| Operation: | write | Name: | Publisher |
Value: REDFINGER CLOUD PHONE | |||
| (PID) Process: | (688) redfinger.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Redfinger |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\RedFingerPlayerGlobal\ | |||
| (PID) Process: | (688) redfinger.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Redfinger |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.5 | |||
| (PID) Process: | (688) redfinger.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Redfinger |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.gc.com.cn | |||
| (PID) Process: | (688) redfinger.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Redfinger |
| Operation: | write | Name: | HelpLink |
Value: http://www.gc.com.cn | |||
| (PID) Process: | (688) redfinger.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Redfinger |
| Operation: | write | Name: | EstimatedSize |
Value: 13507 | |||
| (PID) Process: | (688) redfinger.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Redfinger |
| Operation: | write | Name: | _PROCESS_CHANNEL_ |
Value: com.redfinger.app | |||
Executable files
19
Suspicious files
127
Text files
302
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 688 | redfinger.exe | C:\Users\admin\AppData\Local\Temp\redTmp\avcodec-56.dll | — | |
MD5:— | SHA256:— | |||
| 688 | redfinger.exe | C:\Users\admin\AppData\Local\Temp\redTmp\avutil-54.dll | — | |
MD5:— | SHA256:— | |||
| 688 | redfinger.exe | C:\Users\admin\AppData\Local\Temp\redTmp\config.txt | — | |
MD5:— | SHA256:— | |||
| 688 | redfinger.exe | C:\Users\admin\AppData\Local\Temp\redTmp\def_language.ini | — | |
MD5:— | SHA256:— | |||
| 688 | redfinger.exe | C:\Users\admin\AppData\Local\Temp\redTmp\FAQ.txt | — | |
MD5:— | SHA256:— | |||
| 688 | redfinger.exe | C:\Users\admin\AppData\Local\Temp\redTmp\libeay32.dll | — | |
MD5:— | SHA256:— | |||
| 688 | redfinger.exe | C:\Users\admin\AppData\Local\Temp\redTmp\libredfinger.dll | — | |
MD5:— | SHA256:— | |||
| 688 | redfinger.exe | C:\Users\admin\AppData\Local\Temp\2019112083935708 | text | |
MD5:550D8F336FC1E2BCF251504D942DC914 | SHA256:57EE3EB7932E4B4634B6E9329B9F7128F034F8FE7FD7A3E61CC927D64B02C226 | |||
| 688 | redfinger.exe | C:\Users\admin\AppData\Local\Temp\redTmp\libredfinger_csproto.dll | executable | |
MD5:932597E1FBD5ED0F344F6A9358F12A37 | SHA256:F69BD5F6E286EBF9E6F7050958E91FD6F6EAC167399D346DFBF46F8459E13BA9 | |||
| 688 | redfinger.exe | C:\Users\admin\AppData\Local\Temp\redtmp.zip | compressed | |
MD5:D006EFA097FB8C0BE7A77E20AA3B80D1 | SHA256:587E67C466C1AE84FB5900B9A19A9539EF745F3F6ECB6D7134322166A10C43CE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
43
DNS requests
32
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
292 | RedFingerPlayerGlobal.exe | POST | 200 | 69.28.52.100:80 | http://play.redfinger.com/osfingerauth/version/checkAppVersion.html?client=win&channelVersionCode=100000005&uuid=1F8BFBFF000506E352-54-00-4A-04-AF&languageType=en_US&versionCode=100000005&channelCode=com.redfinger.app×tamp=1574210416000 | US | text | 392 b | unknown |
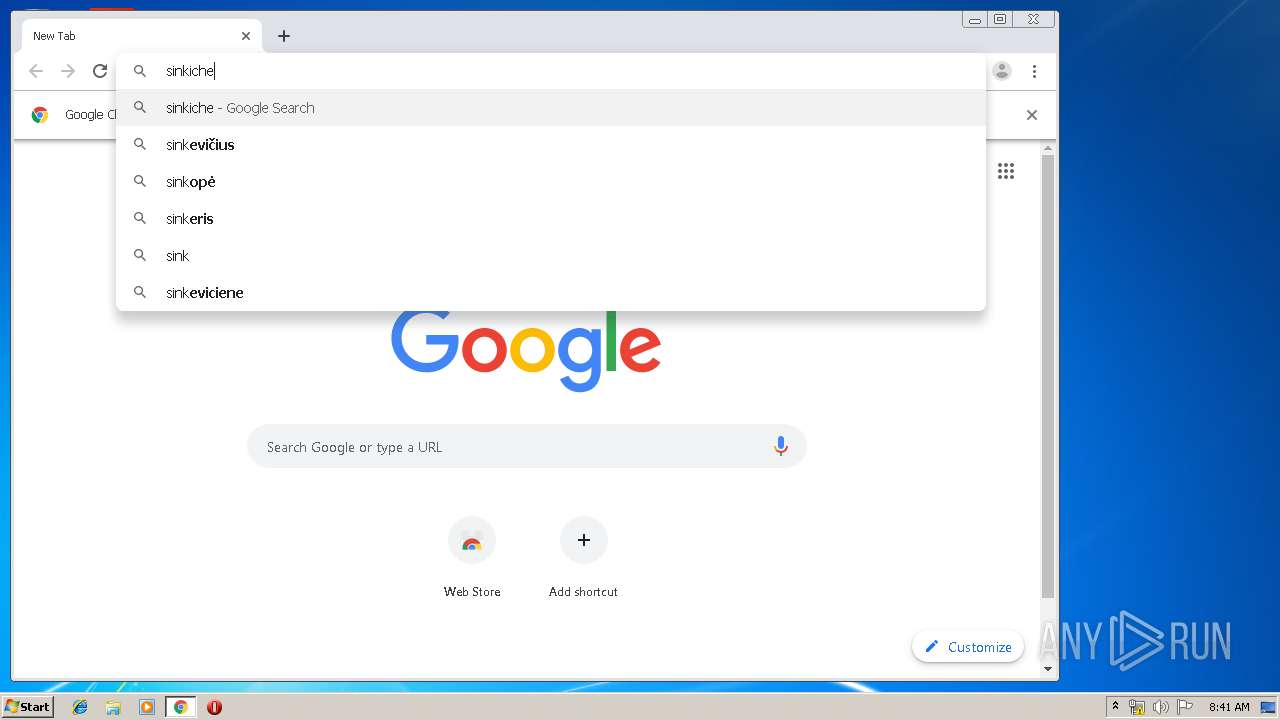
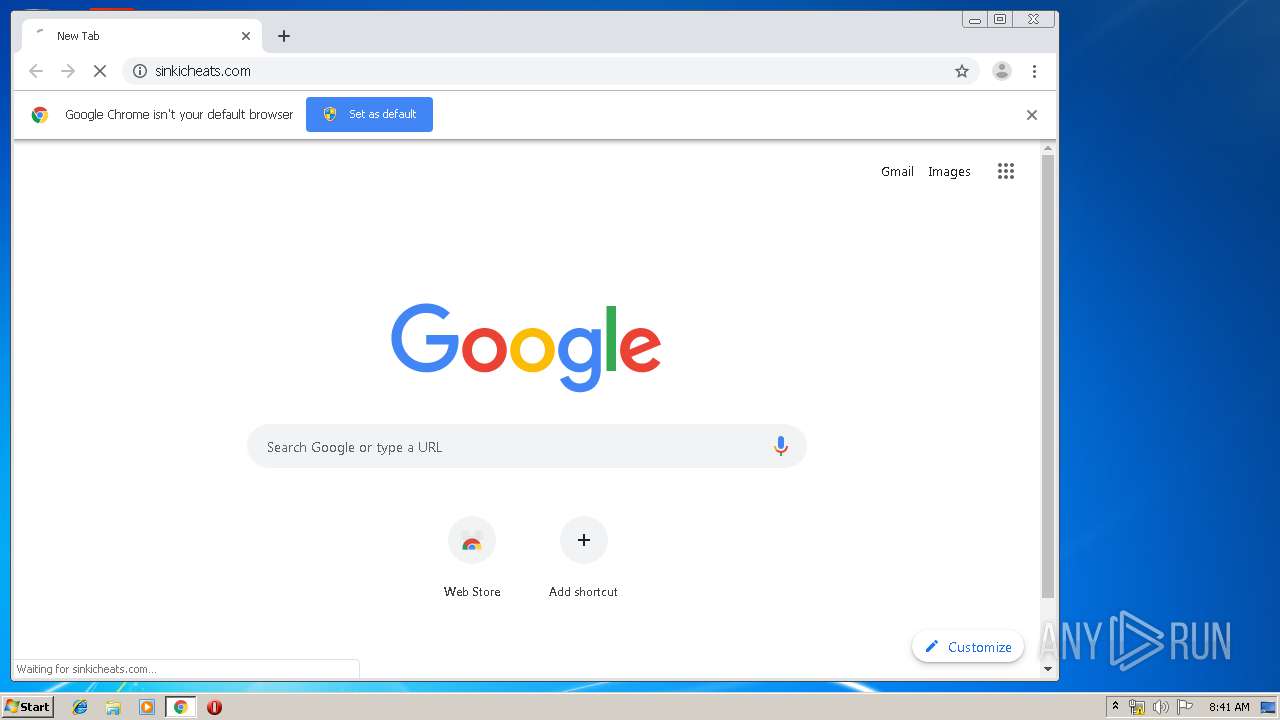
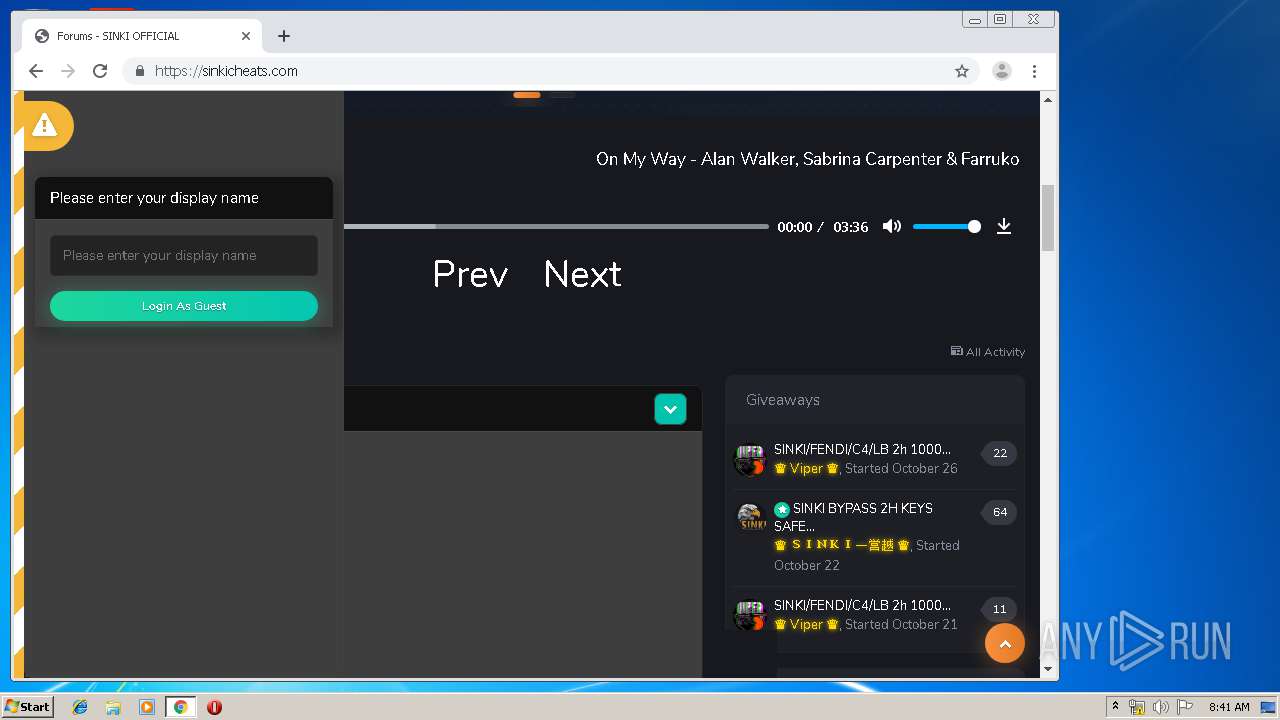
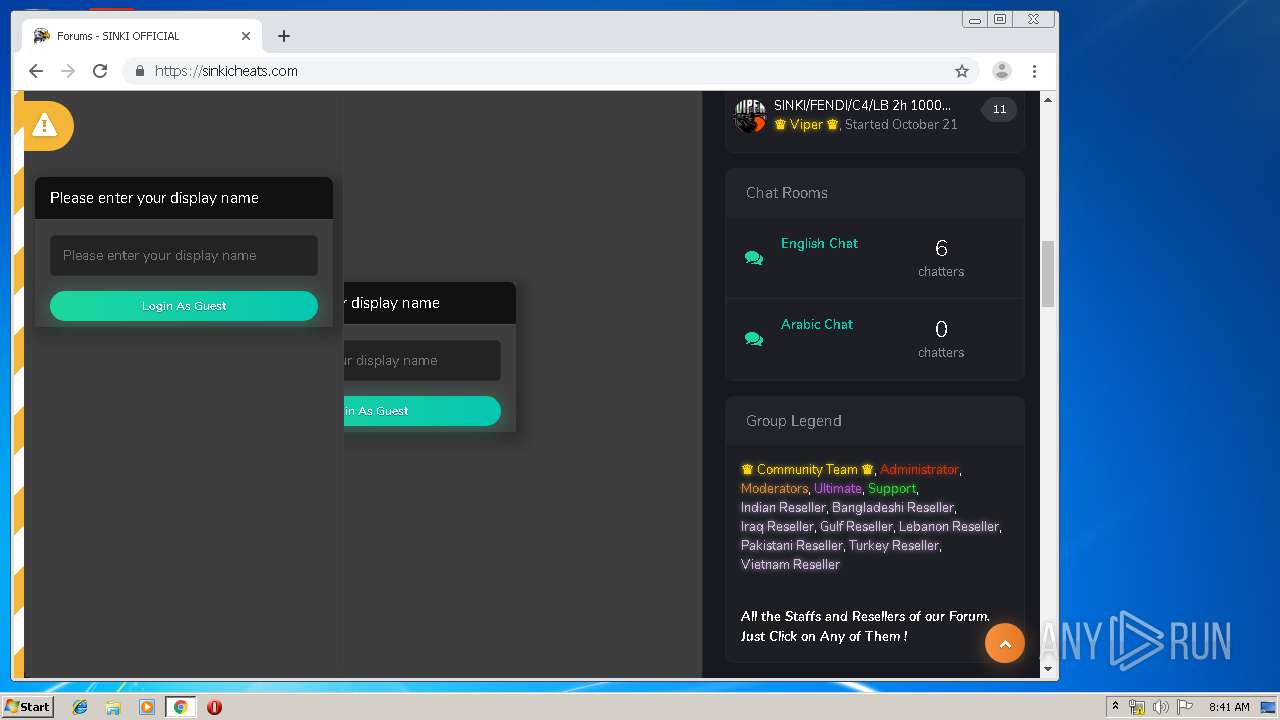
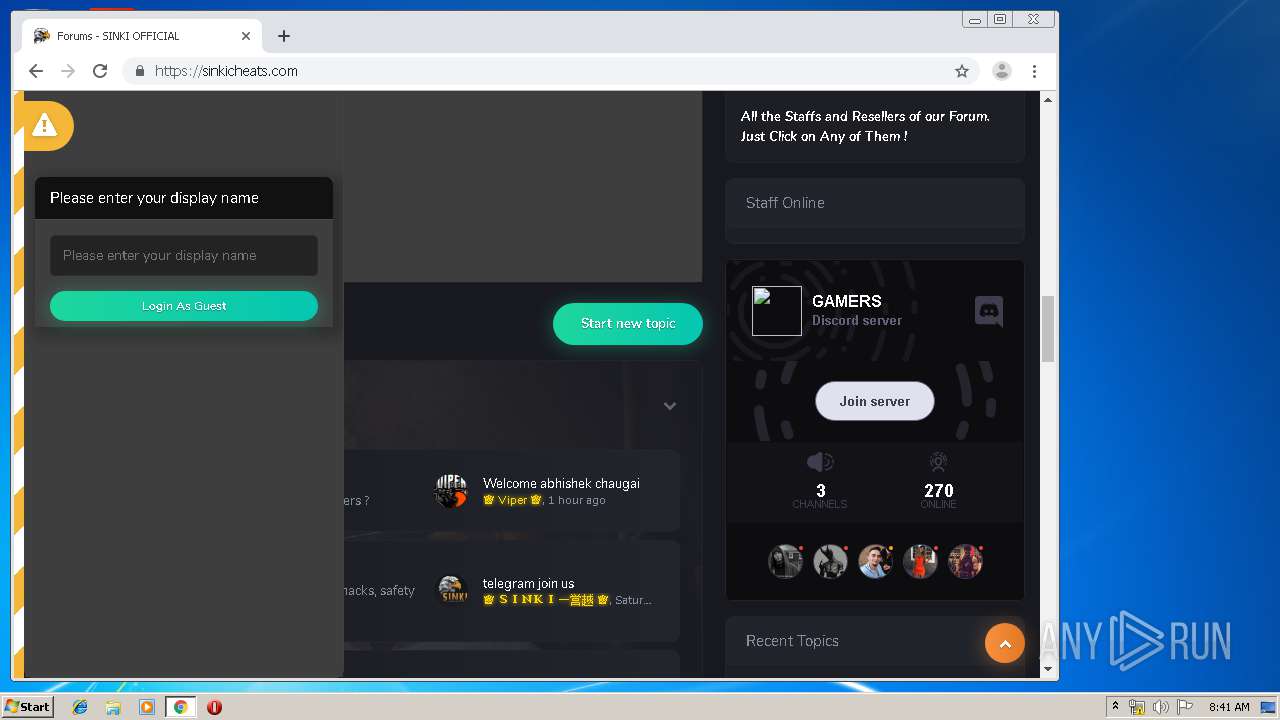
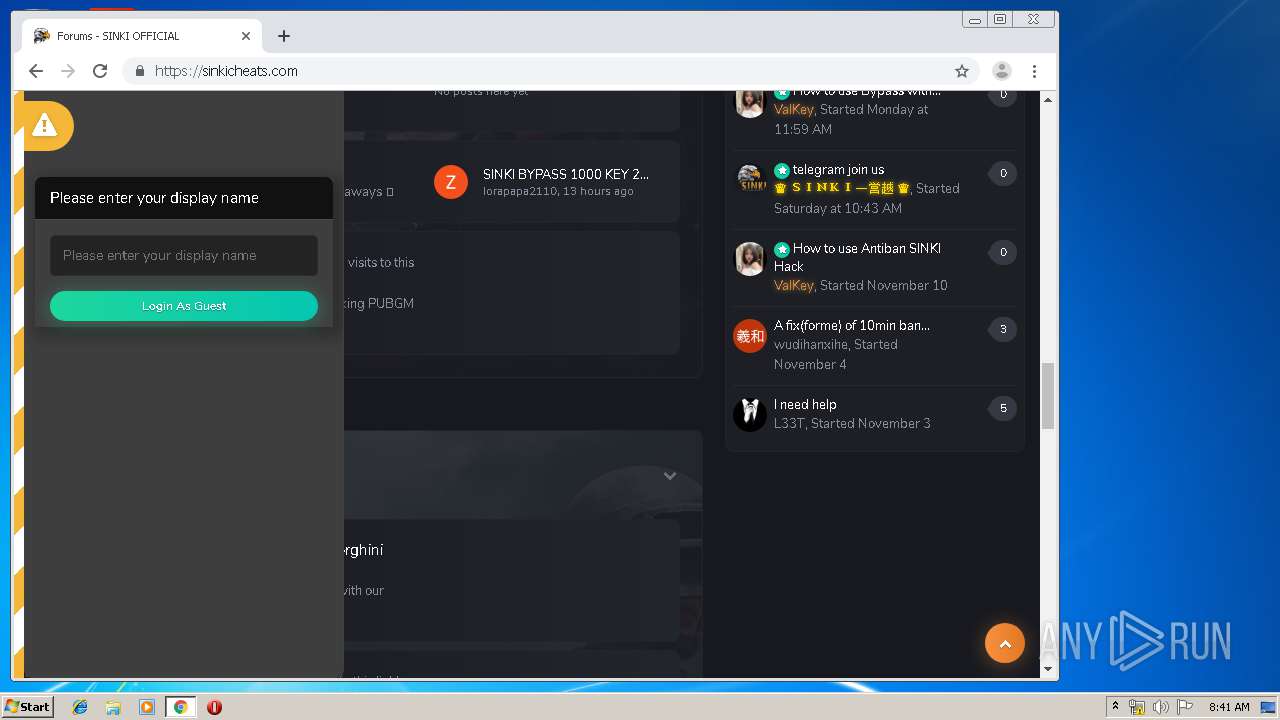
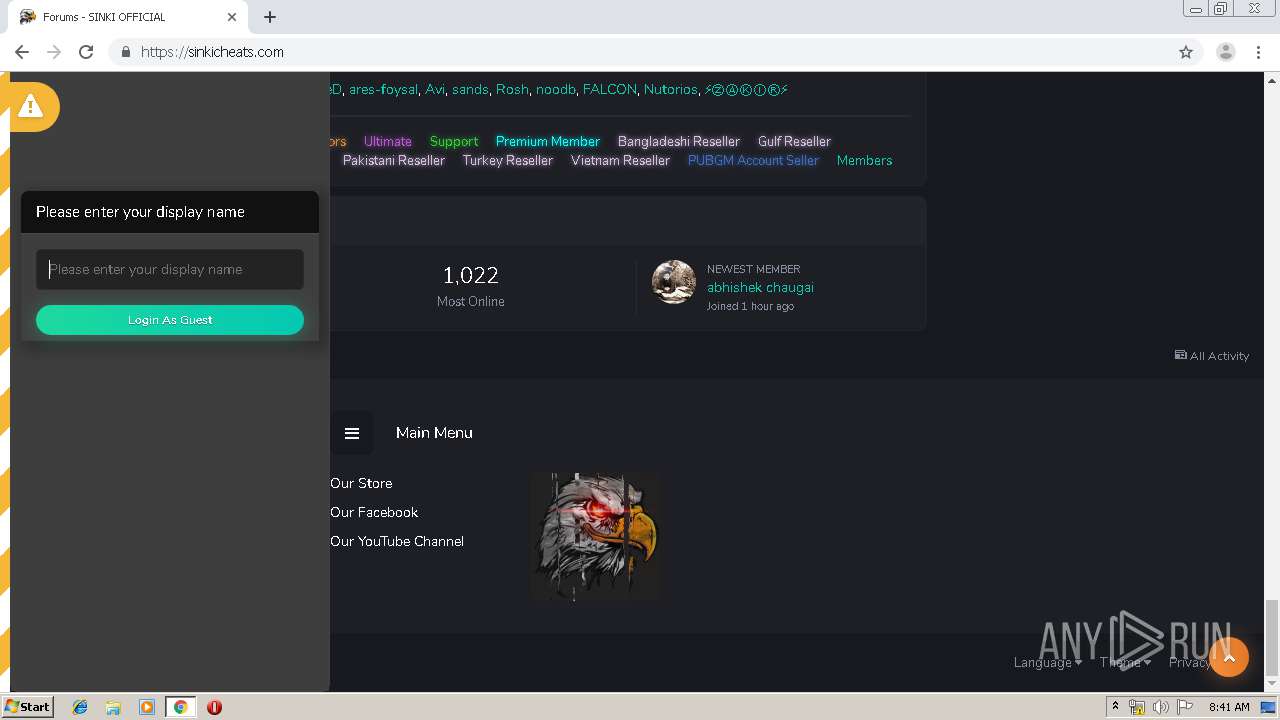
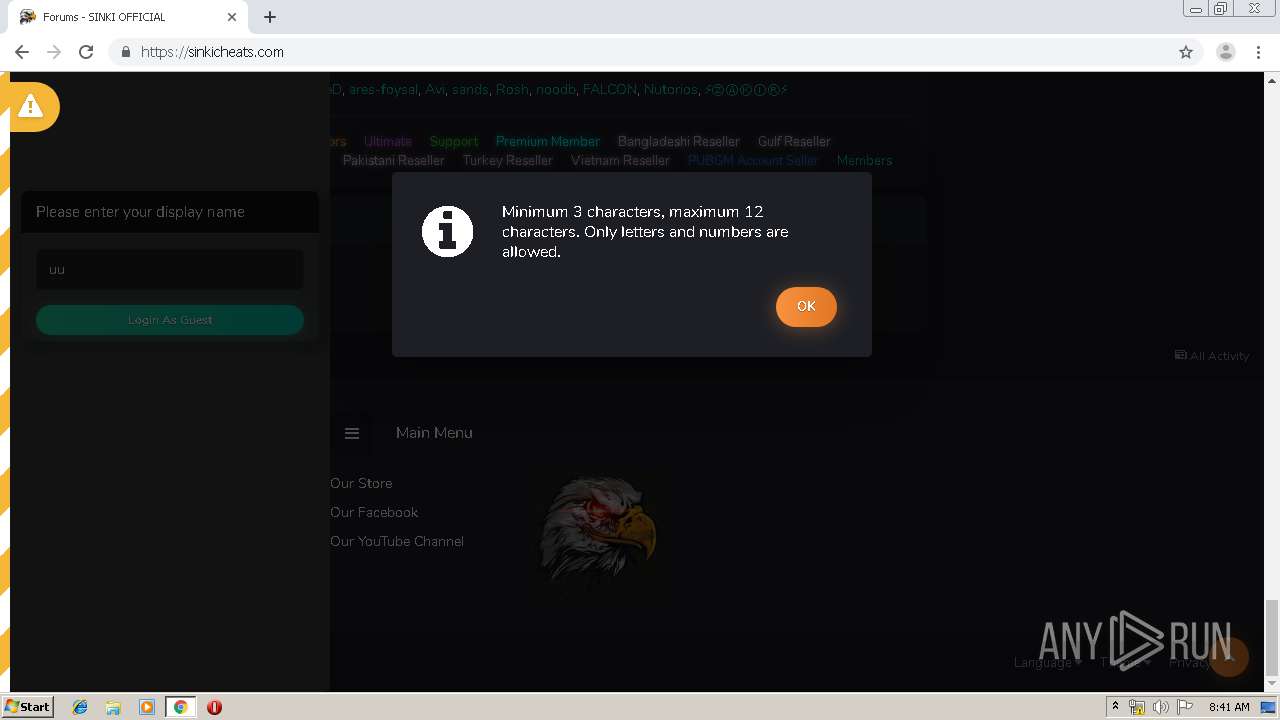
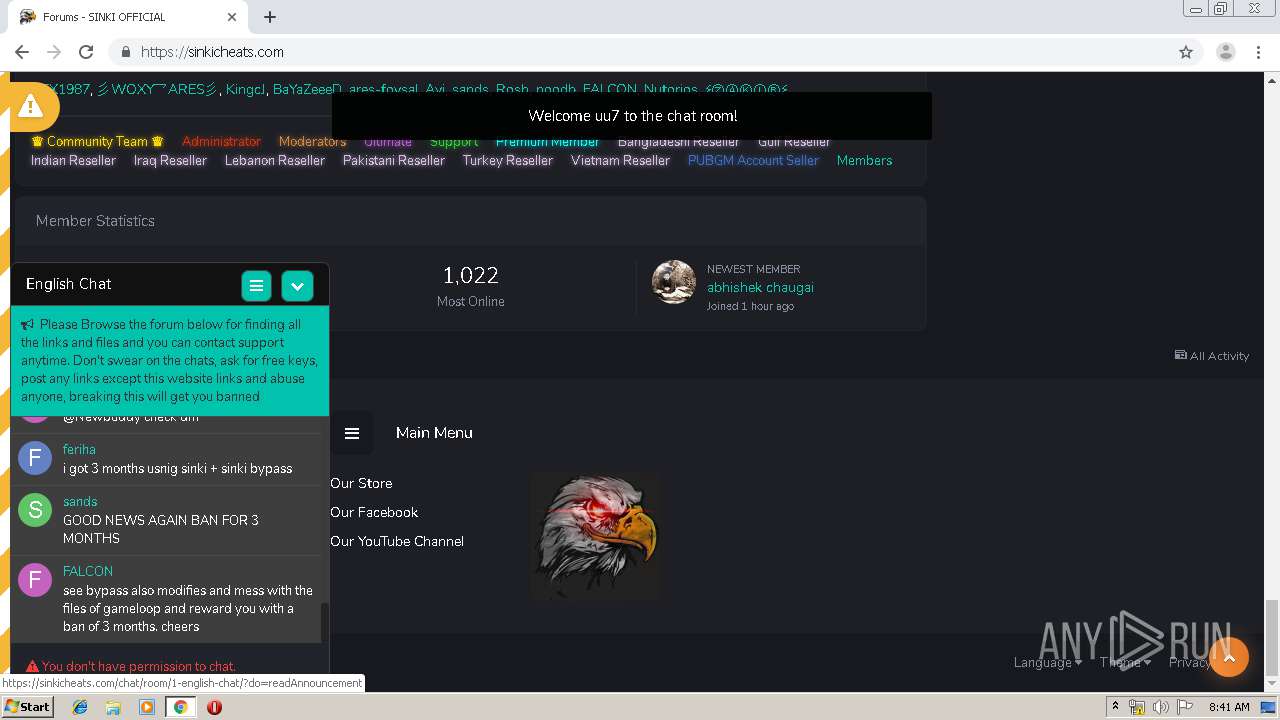
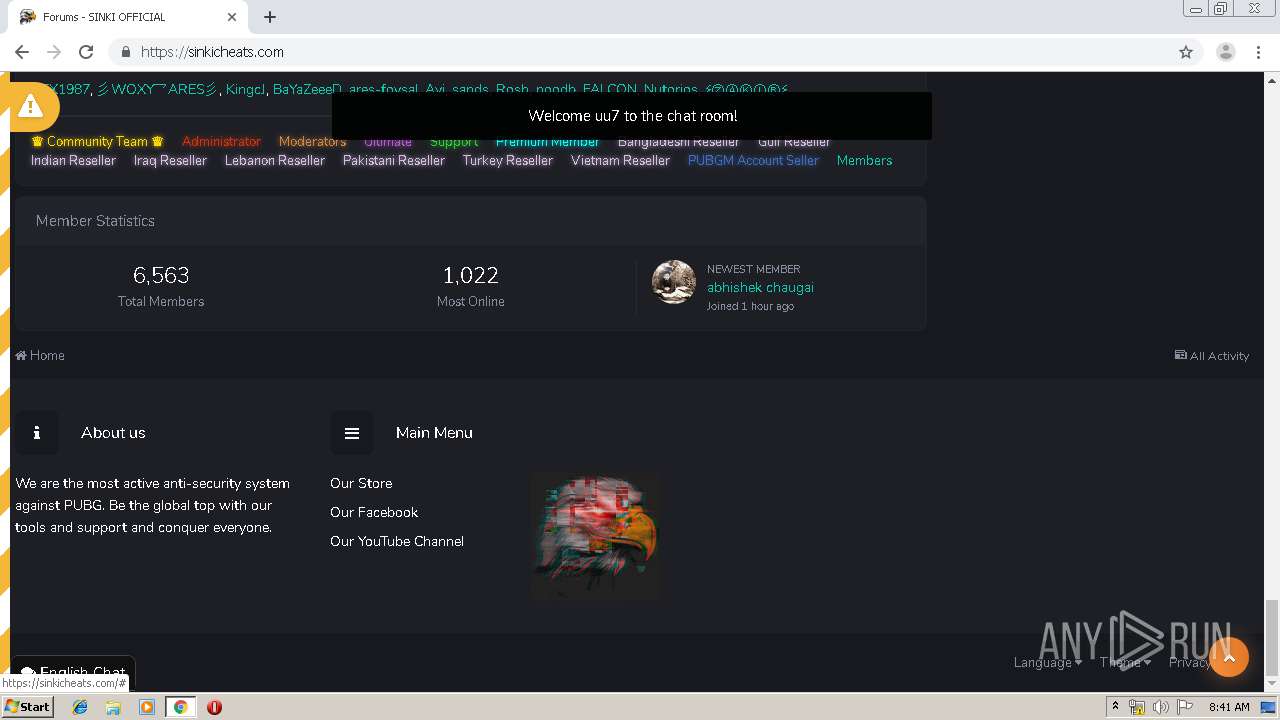
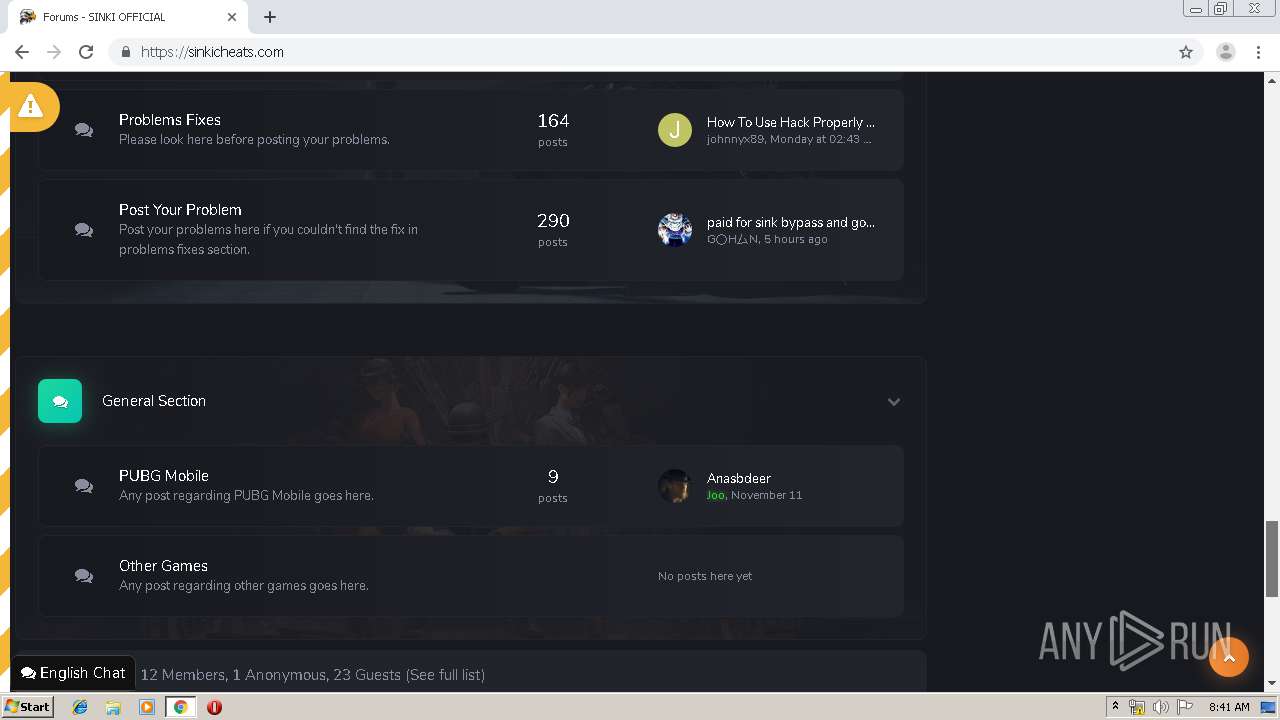
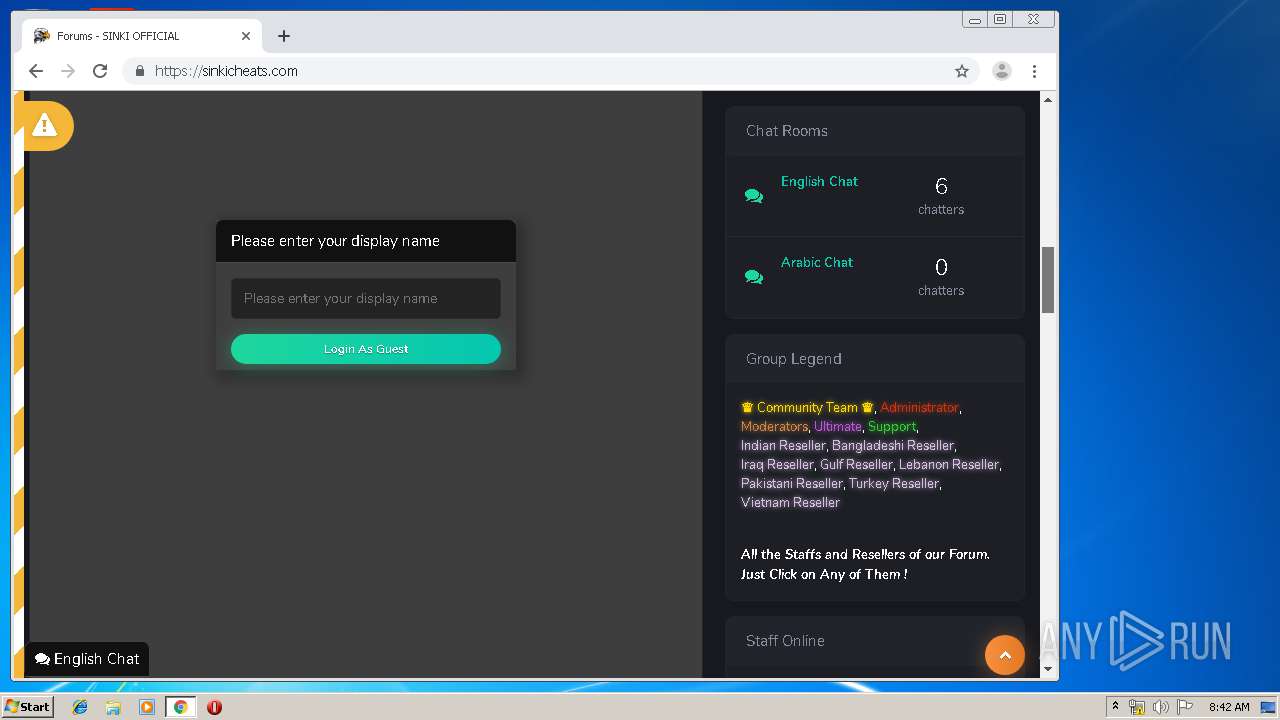
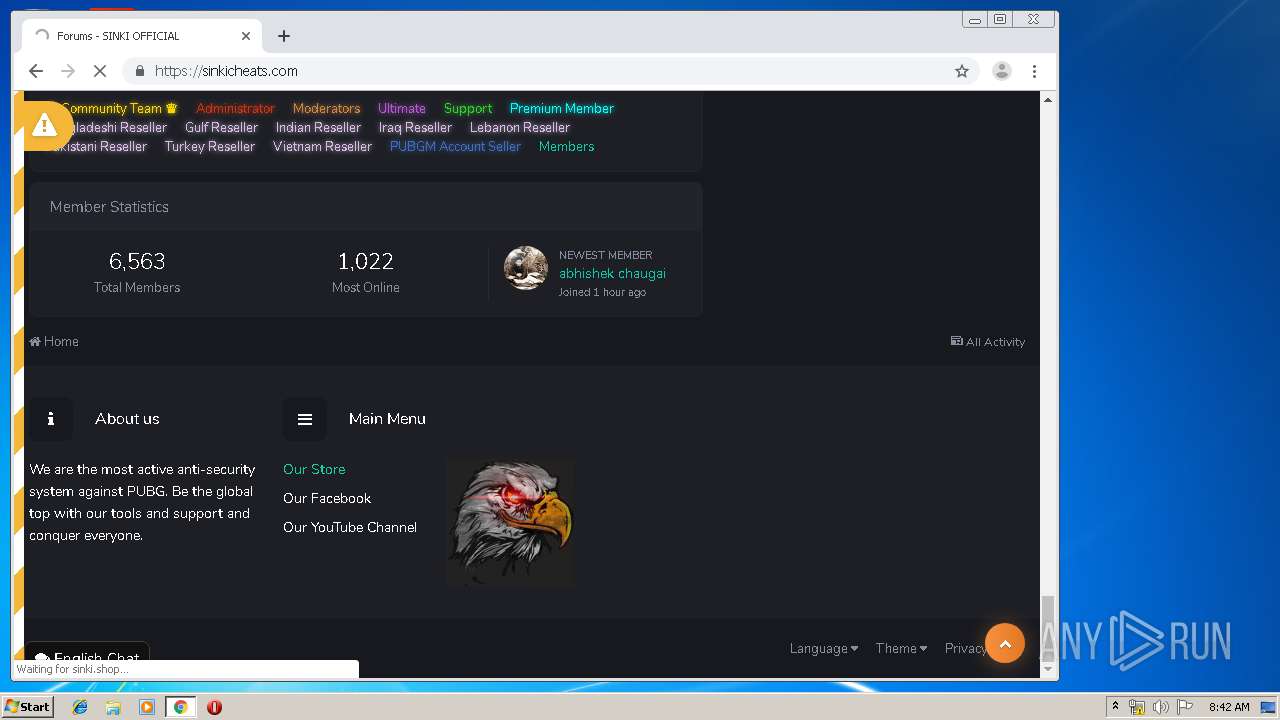
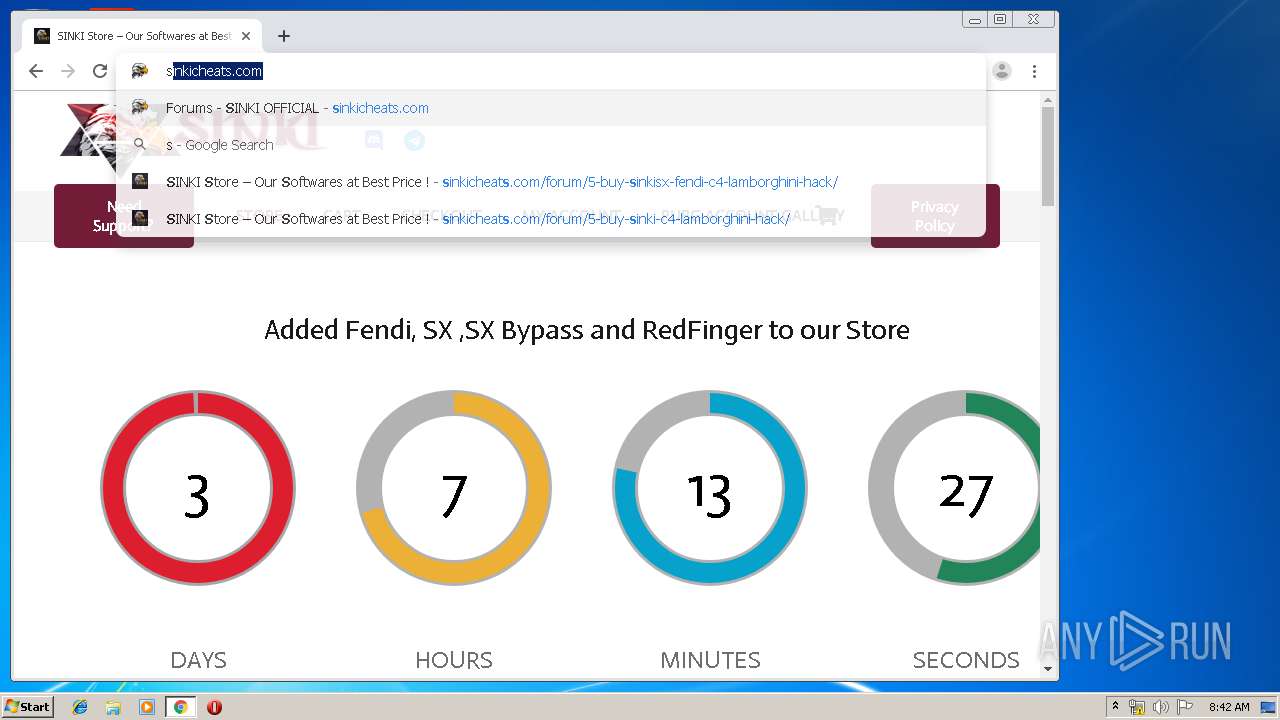
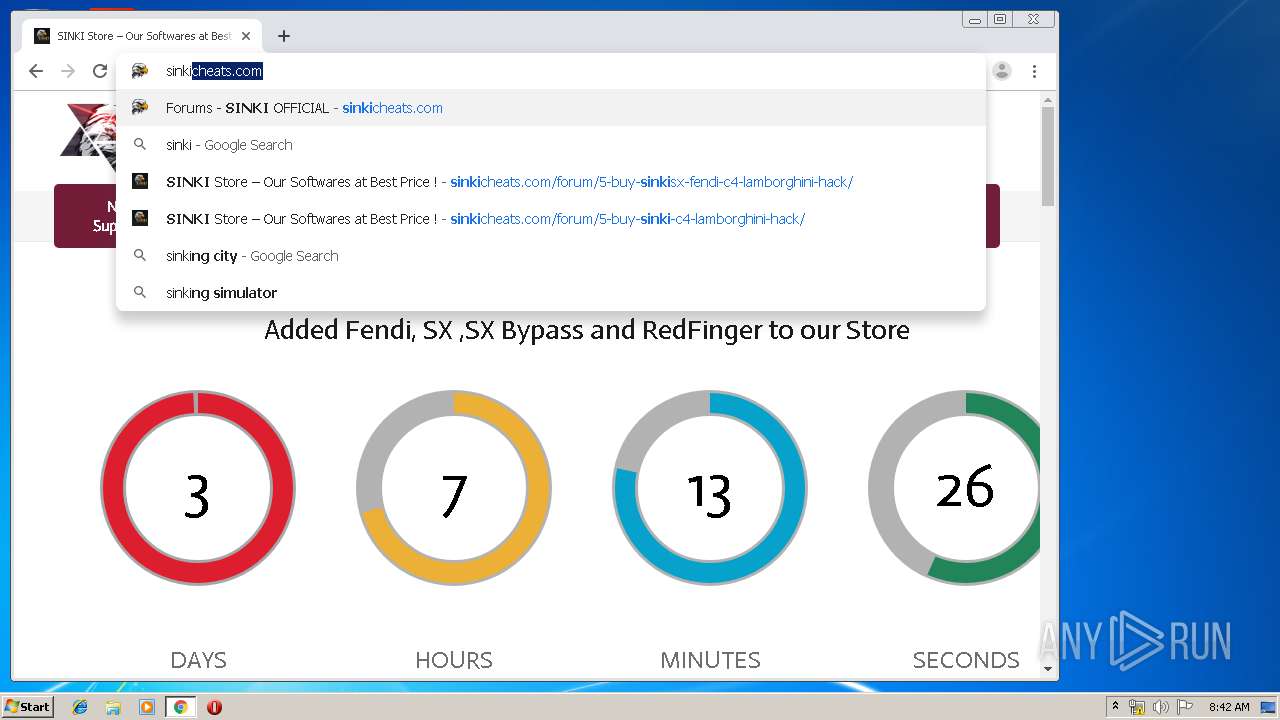
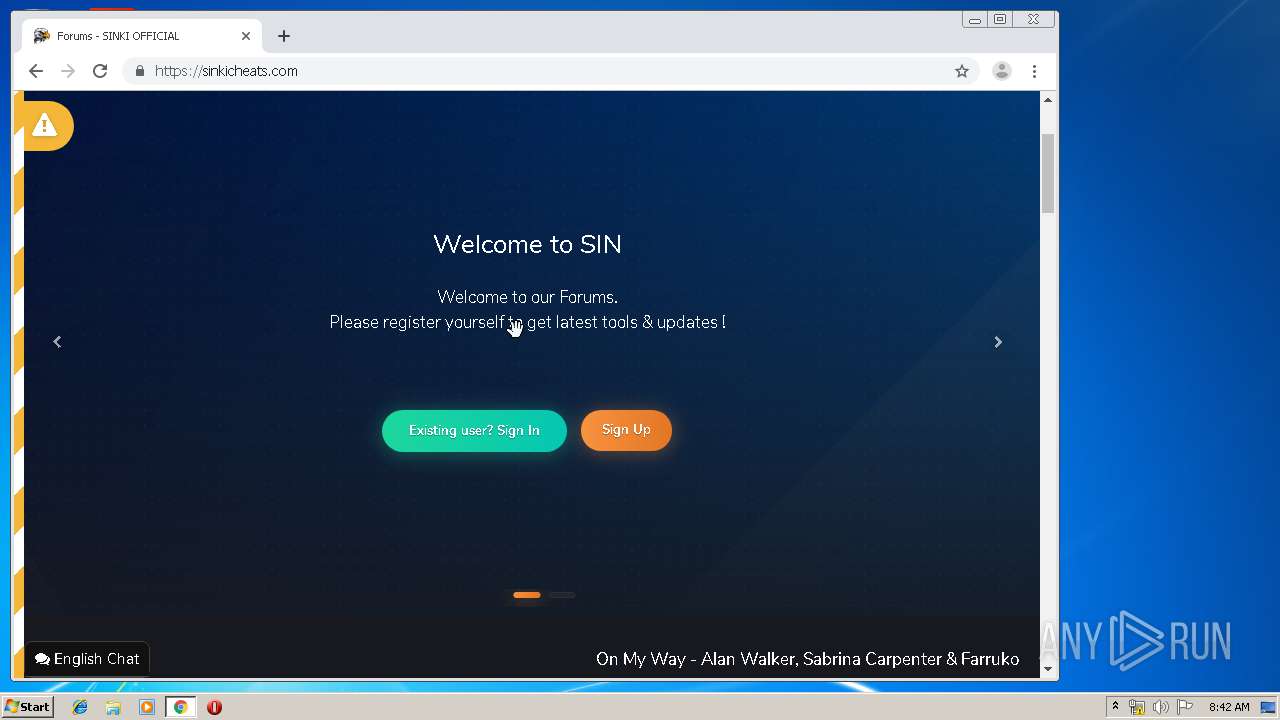
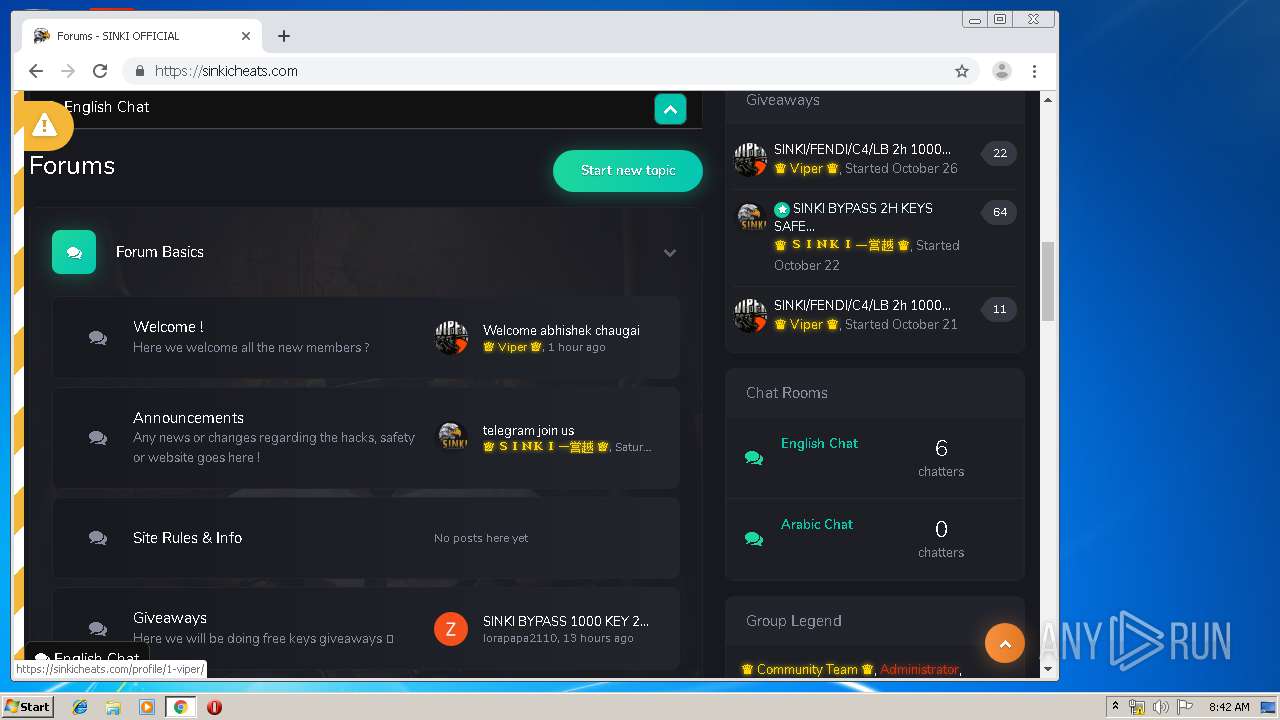
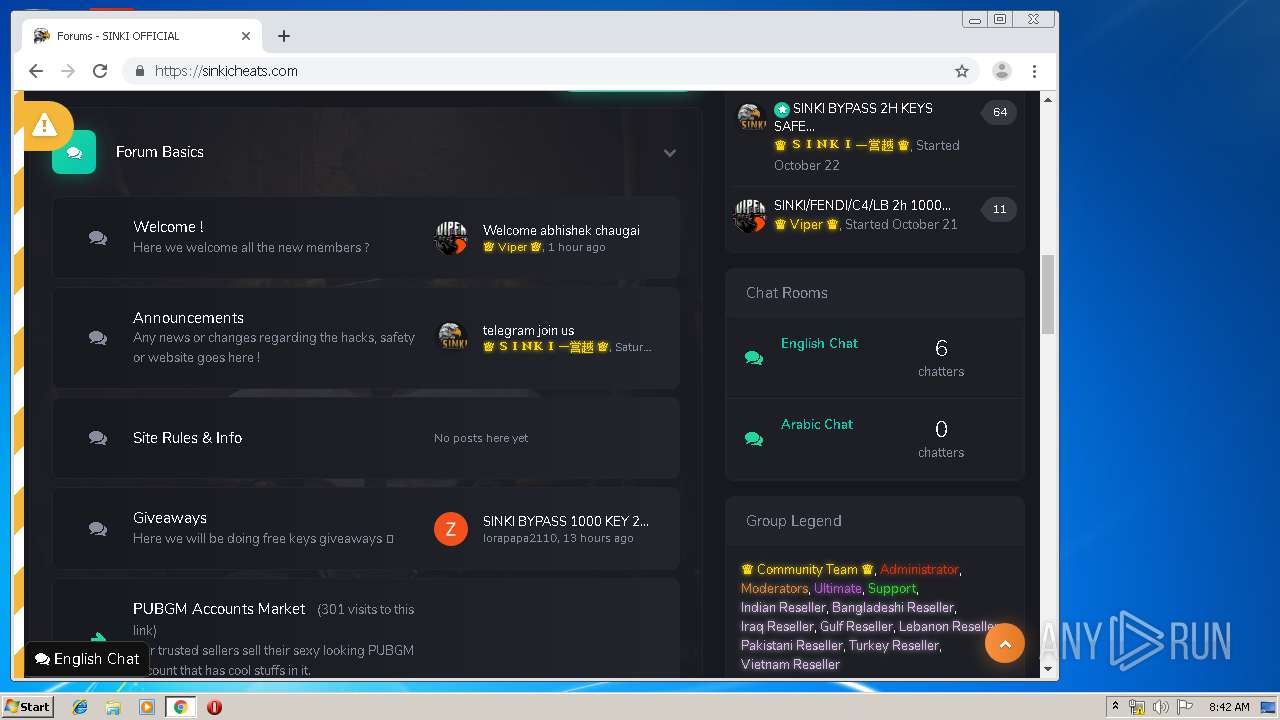
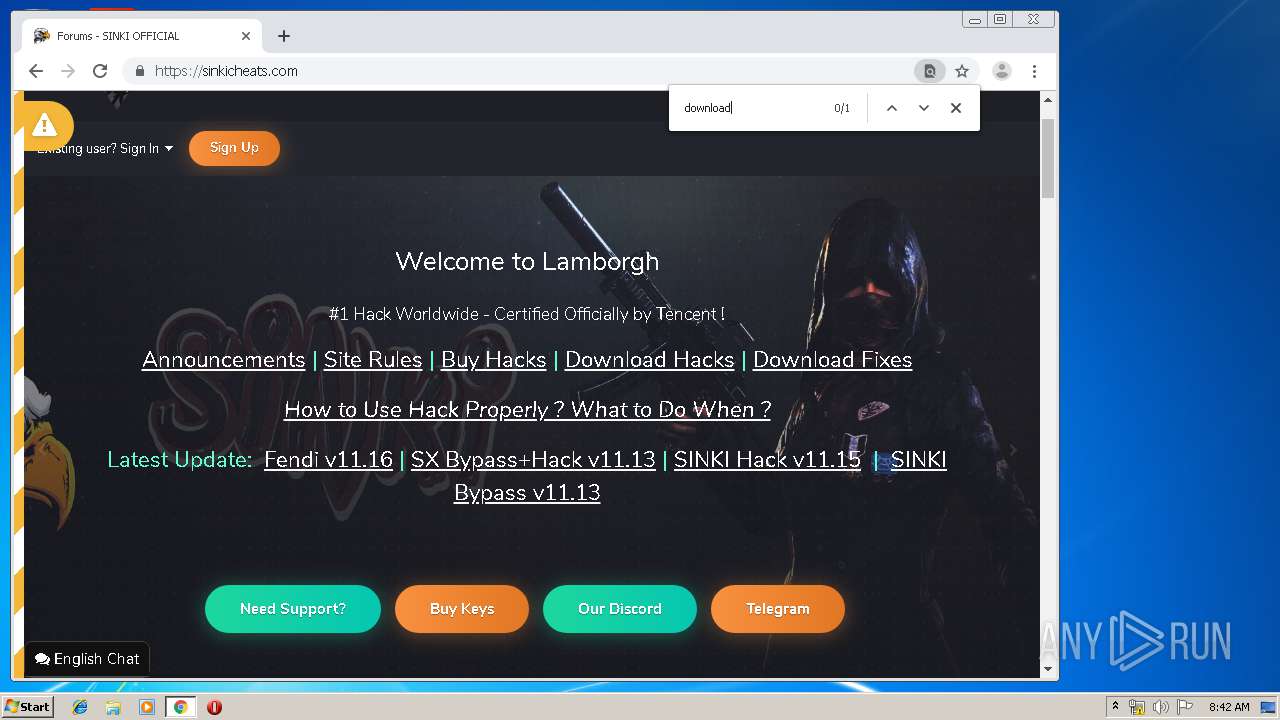
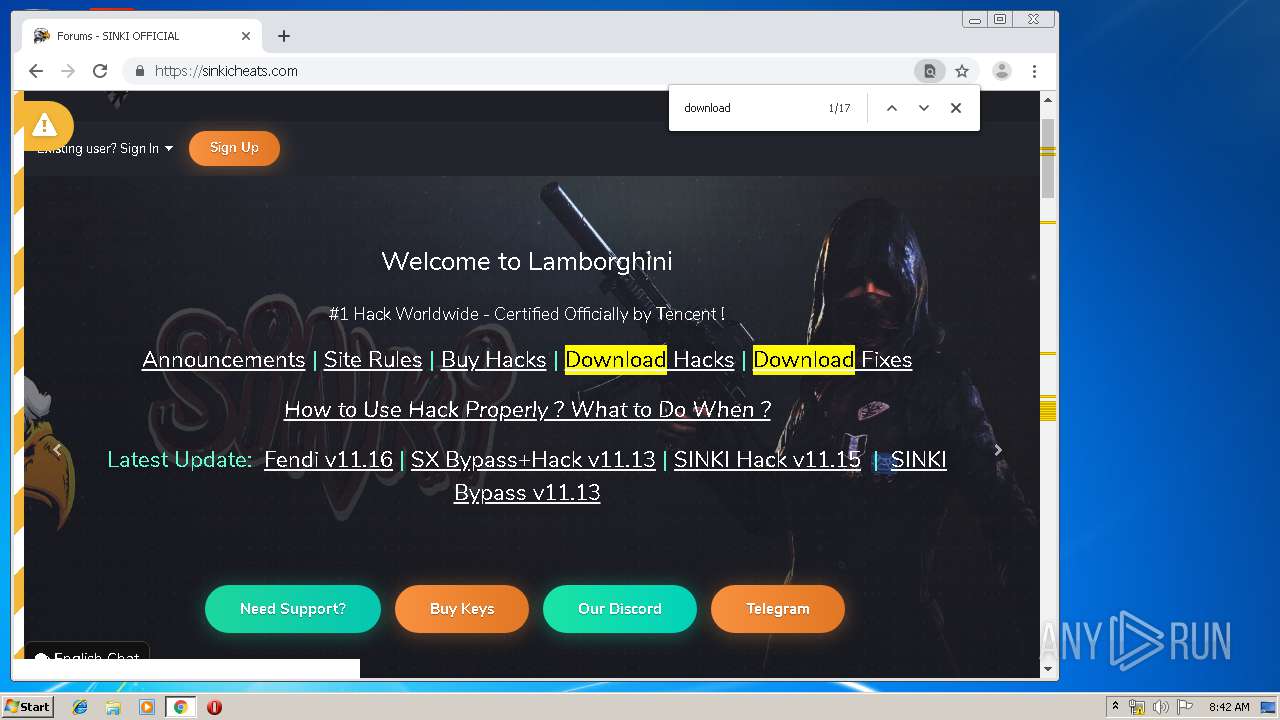
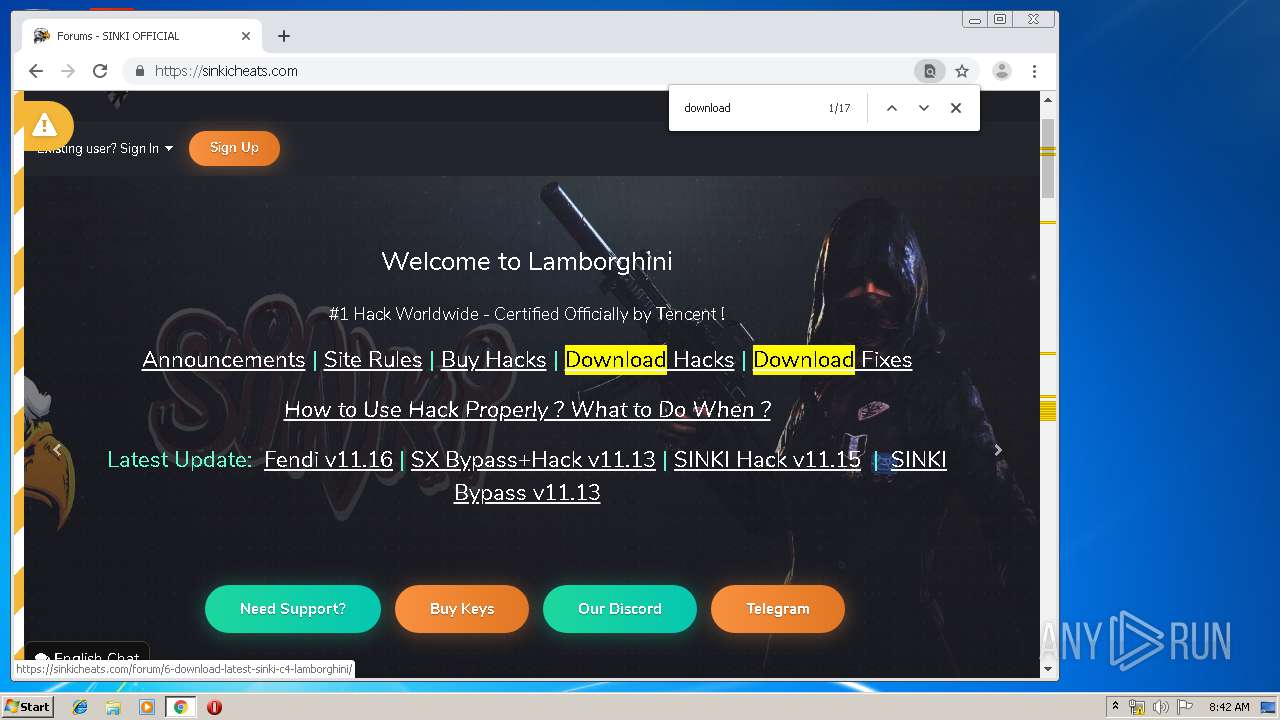
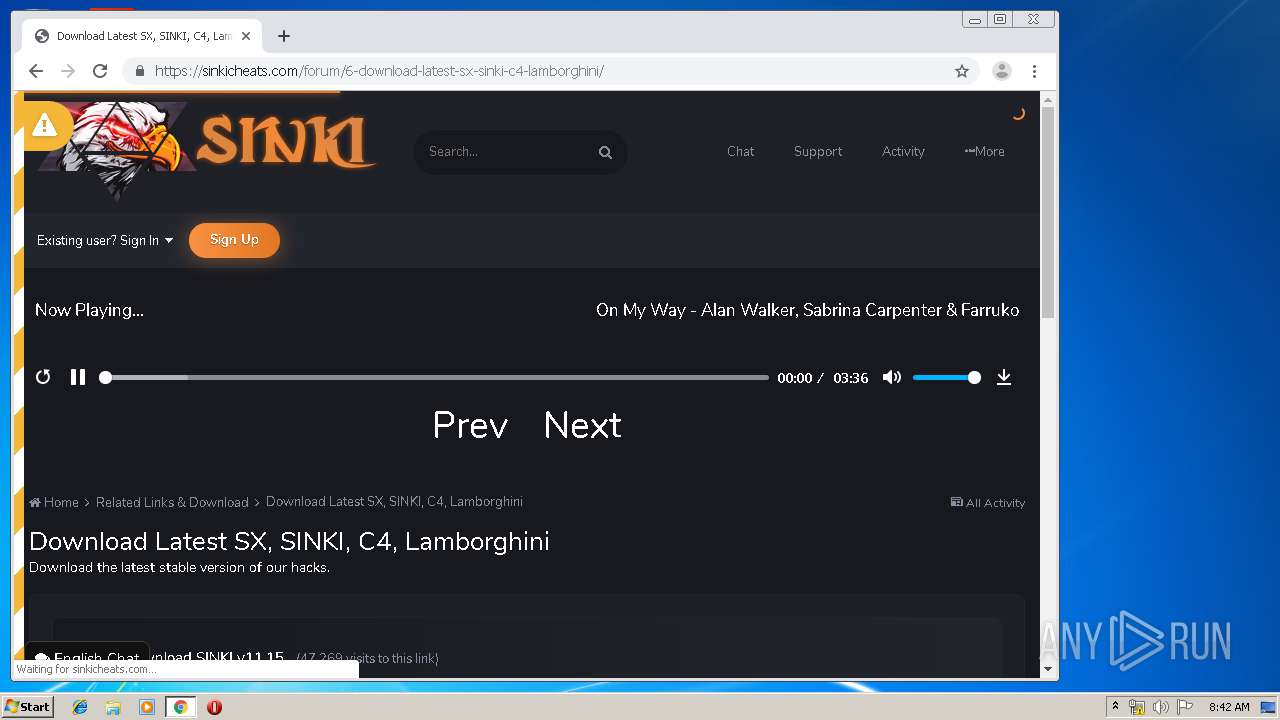
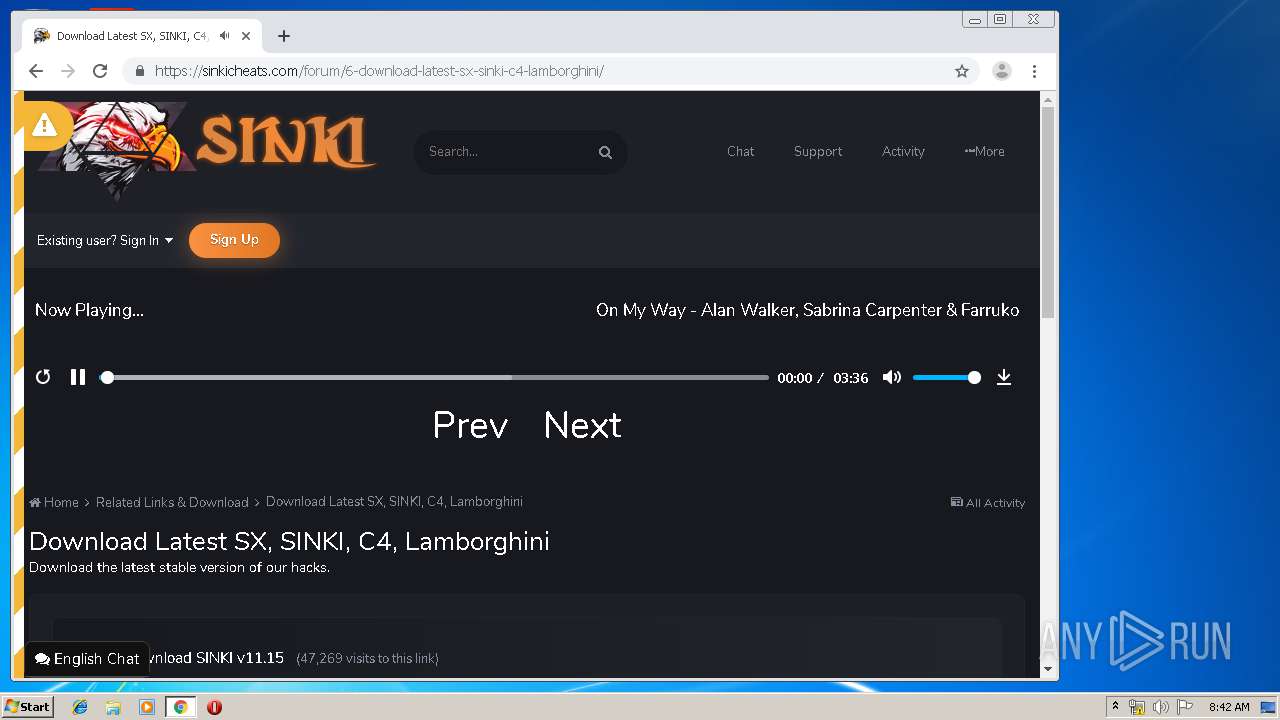
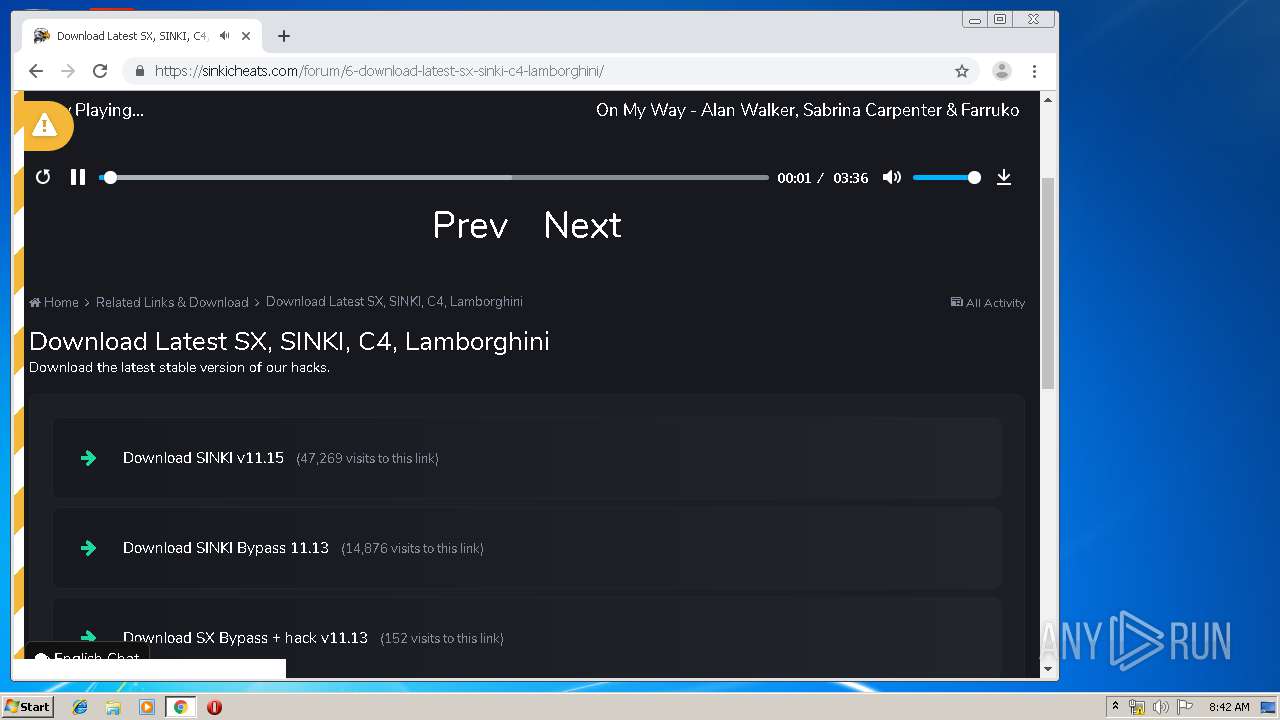
3928 | chrome.exe | GET | — | 104.24.106.106:80 | http://sinkicheats.com/ | US | — | — | suspicious |
3928 | chrome.exe | GET | 301 | 104.24.106.106:80 | http://sinkicheats.com/favicon.ico | US | — | — | suspicious |
3928 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 527 b | whitelisted |
3928 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
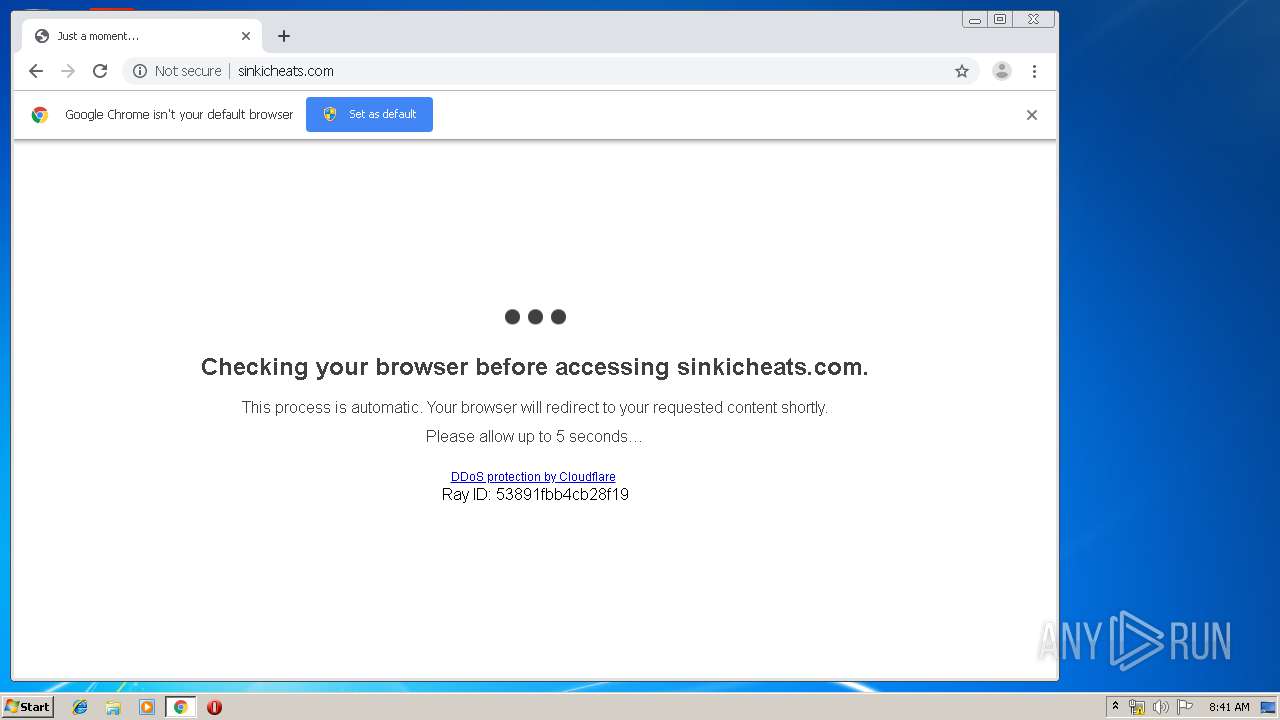
3928 | chrome.exe | GET | 302 | 104.24.106.106:80 | http://sinkicheats.com/cdn-cgi/l/chk_jschl?s=32ea5844fa3799cde59e2bddde11faf417e734b7-1574239277-0-AcmWgtv5Rzl3lgkyen6bZzBGEGECx5gy181IjiJD3%2BrXK0gejKGbozo8%2BixSKYGmo3cy5sHJbHx1tJkB09fBVhdU5bMo2I7ksf%2FROL2ur35F0RW7UZ2yHat7fNtDEjkWUUpYcPpH3m6Jl7ZP71Kyr0Y%3D&jschl_vc=2b631f28f865ab91a8d62164d02cb10c&pass=1574239281.334-kPeL8qDm6y&jschl_answer=-6.4800988724 | US | html | 143 b | suspicious |
3928 | chrome.exe | GET | 200 | 84.15.64.140:80 | http://r1---sn-cpux-8ov6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.206.166.82&mm=28&mn=sn-cpux-8ov6&ms=nvh&mt=1574238453&mv=u&mvi=0&pcm2cms=yes&pl=23&shardbypass=yes | LT | crx | 293 Kb | whitelisted |
3928 | chrome.exe | GET | 200 | 84.15.64.141:80 | http://r2---sn-cpux-8ov6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.206.166.82&mm=28&mn=sn-cpux-8ov6&ms=nvh&mt=1574238453&mv=u&mvi=1&pl=23&shardbypass=yes | LT | crx | 862 Kb | whitelisted |
3928 | chrome.exe | GET | 301 | 104.24.106.106:80 | http://store.sinkicheats.com/ | US | — | — | suspicious |
2952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
292 | RedFingerPlayerGlobal.exe | 69.28.52.100:80 | play.redfinger.com | Zenlayer Inc | US | unknown |
3760 | iexplore.exe | 104.31.78.18:443 | www.cloudemulator.net | Cloudflare Inc | US | malicious |
2952 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3928 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 216.58.207.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 172.217.22.46:443 | ogs.google.com | Google Inc. | US | whitelisted |
3928 | chrome.exe | 172.217.18.110:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
play.redfinger.com |
| unknown |
www.cloudemulator.net |
| malicious |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
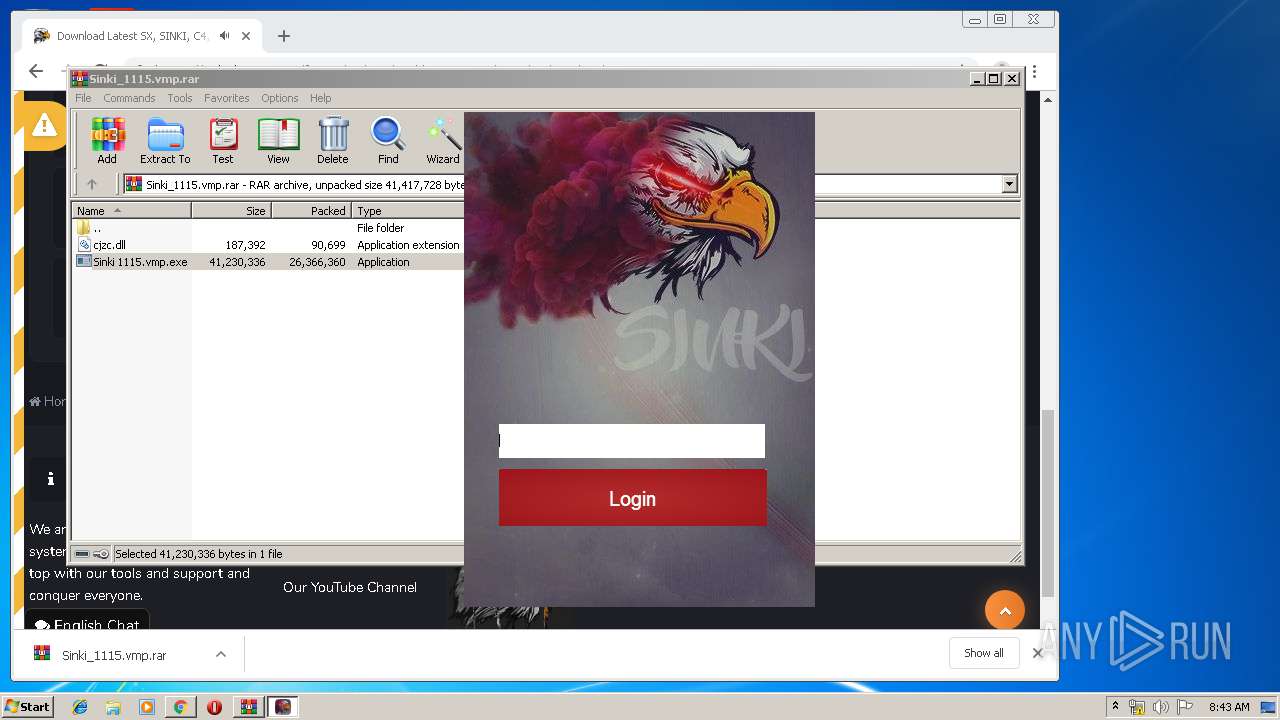
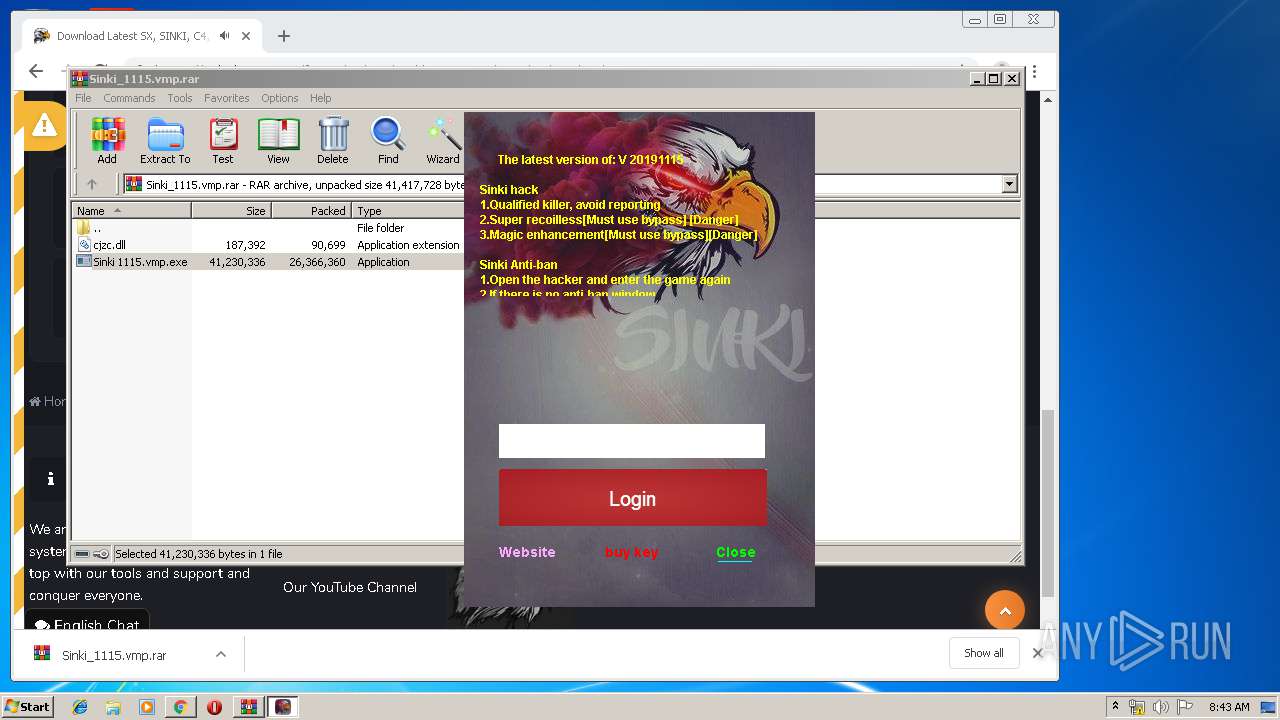
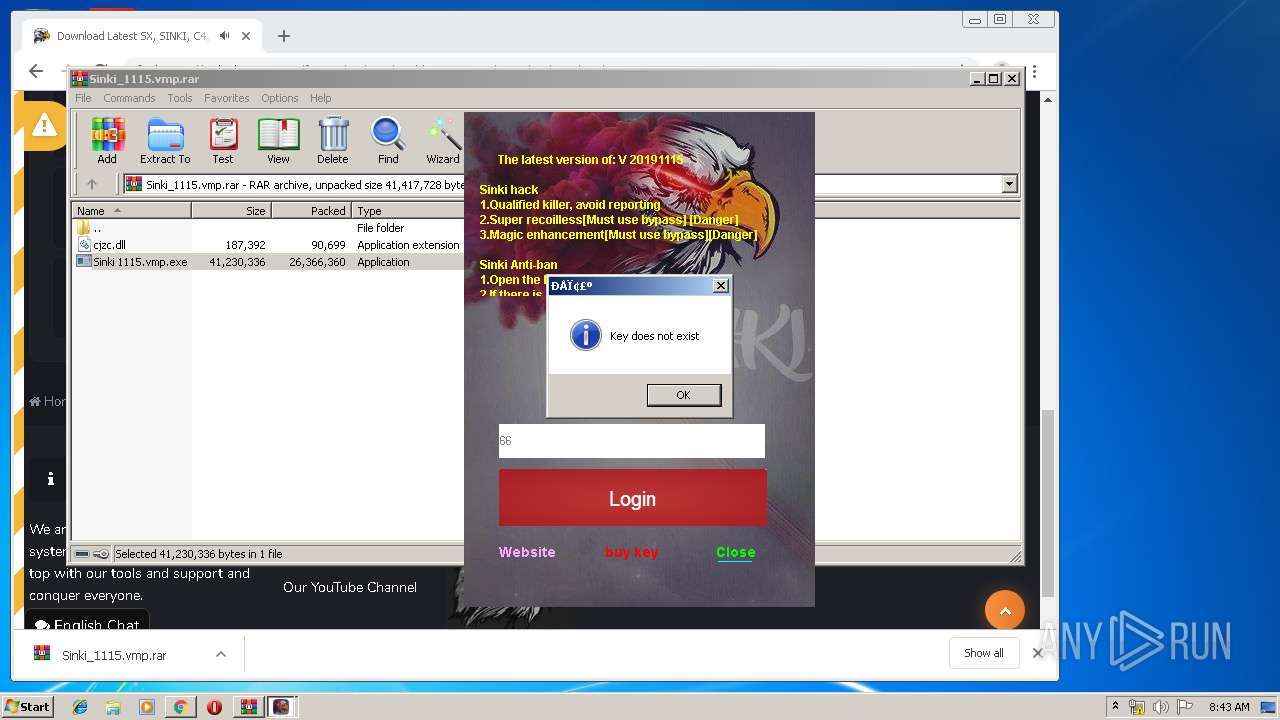
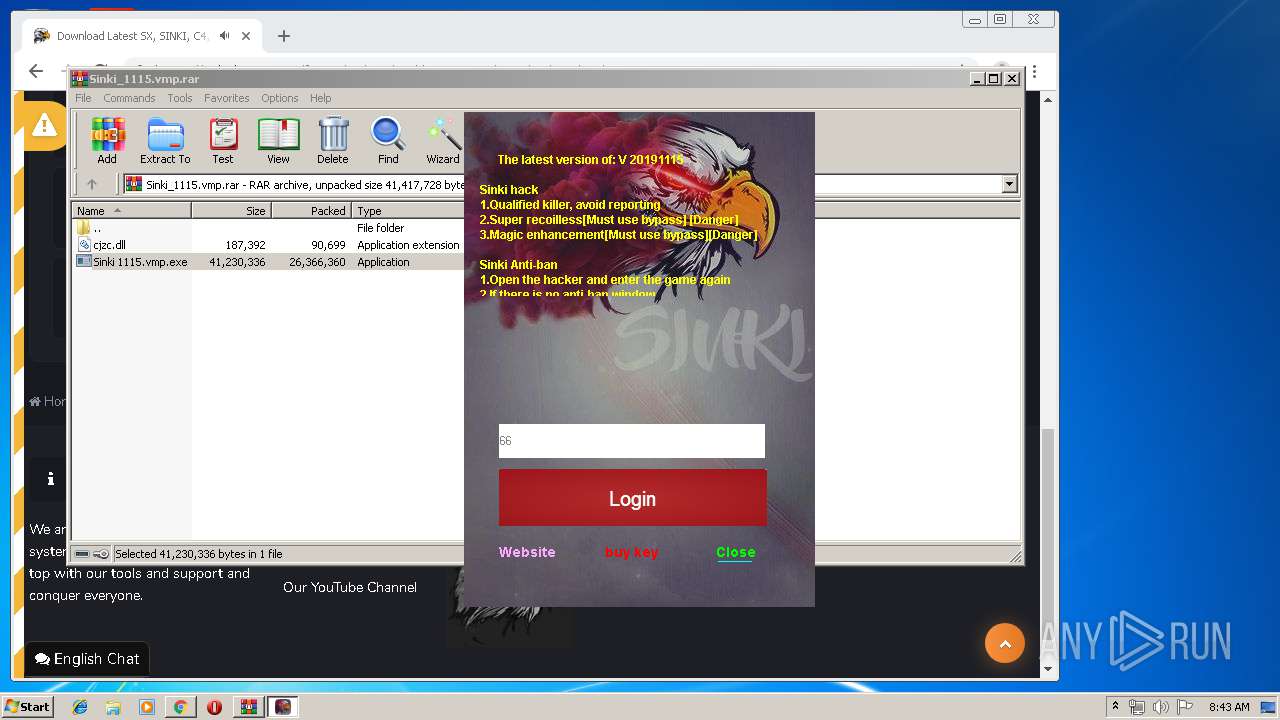
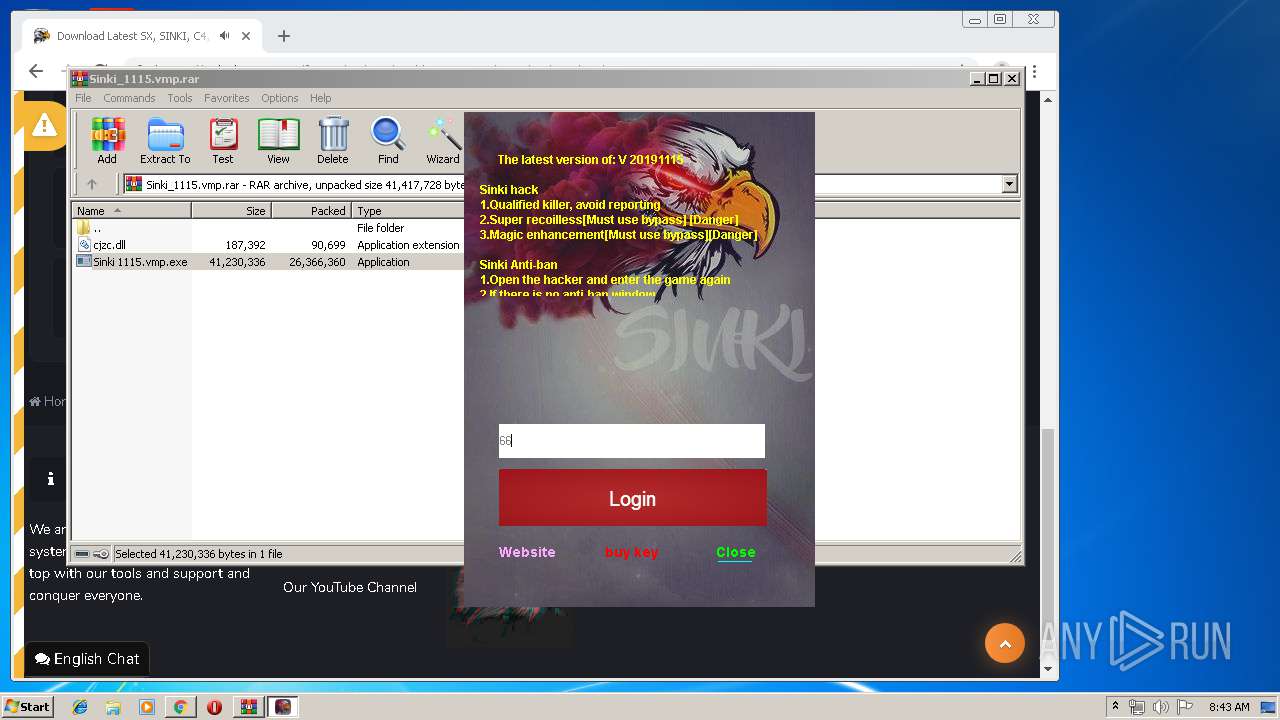
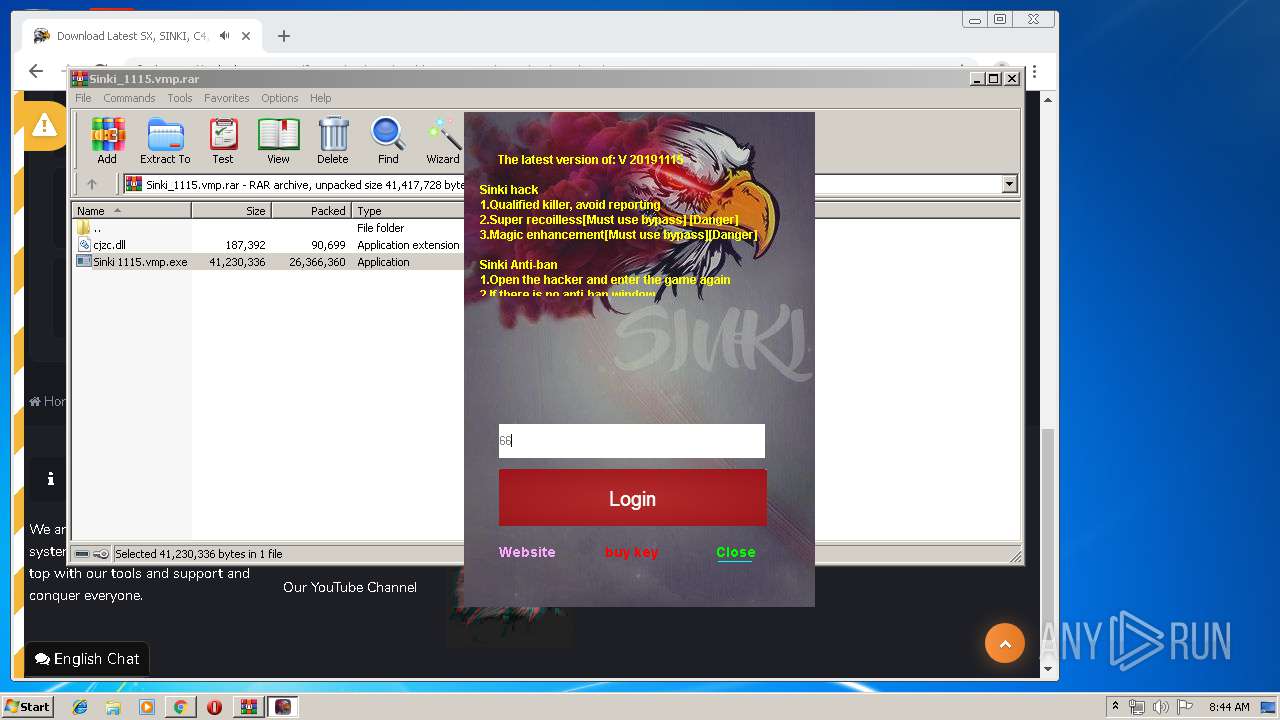
2456 | Sinki 1115.vmp.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan:Win32/Wacatac.B!ml |
2456 | Sinki 1115.vmp.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan:Win32/Wacatac.B!ml |
Process | Message |
|---|---|
redfinger.exe | Size = 21
|
RedFingerPlayerGlobal.exe | Size = 581
|