| File name: | 3.exe |
| Full analysis: | https://app.any.run/tasks/f702aeb5-16f8-429f-8bca-c444d6b8e852 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 11:23:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 36EDED983E5654B69BF7D9825469582D |
| SHA1: | 810E7F9D19460F94E01B843AC7126450A4CFA2DD |
| SHA256: | 6E00D48F5FBA56C4B80E0363DC5741F4E4D044818B81FD7686695433A56C5A69 |
| SSDEEP: | 98304:znUSpO3+rr8FkZvMXLZ+tDfzm8dZmRhXl8ReQJe10QJe1zUoQJe1Rp0m1yybMweA:jvnrrIkvMQt7+RhXlkJeJJeRgJenp1bd |
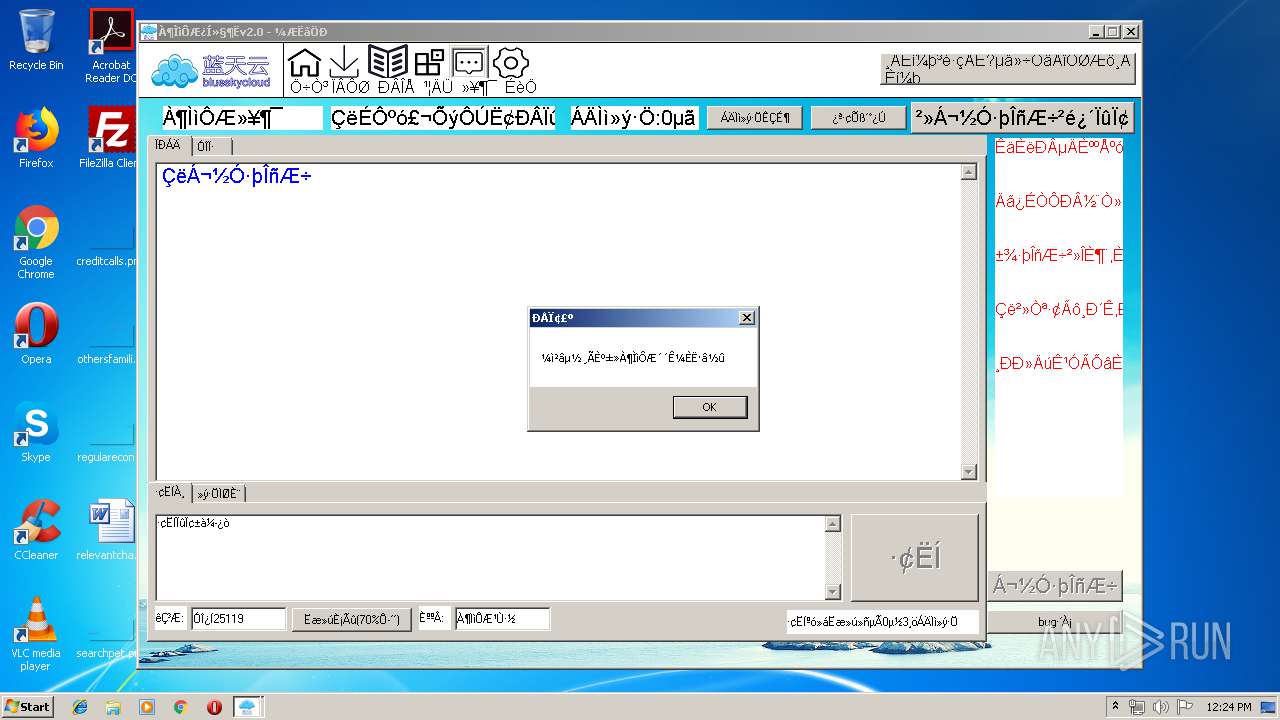
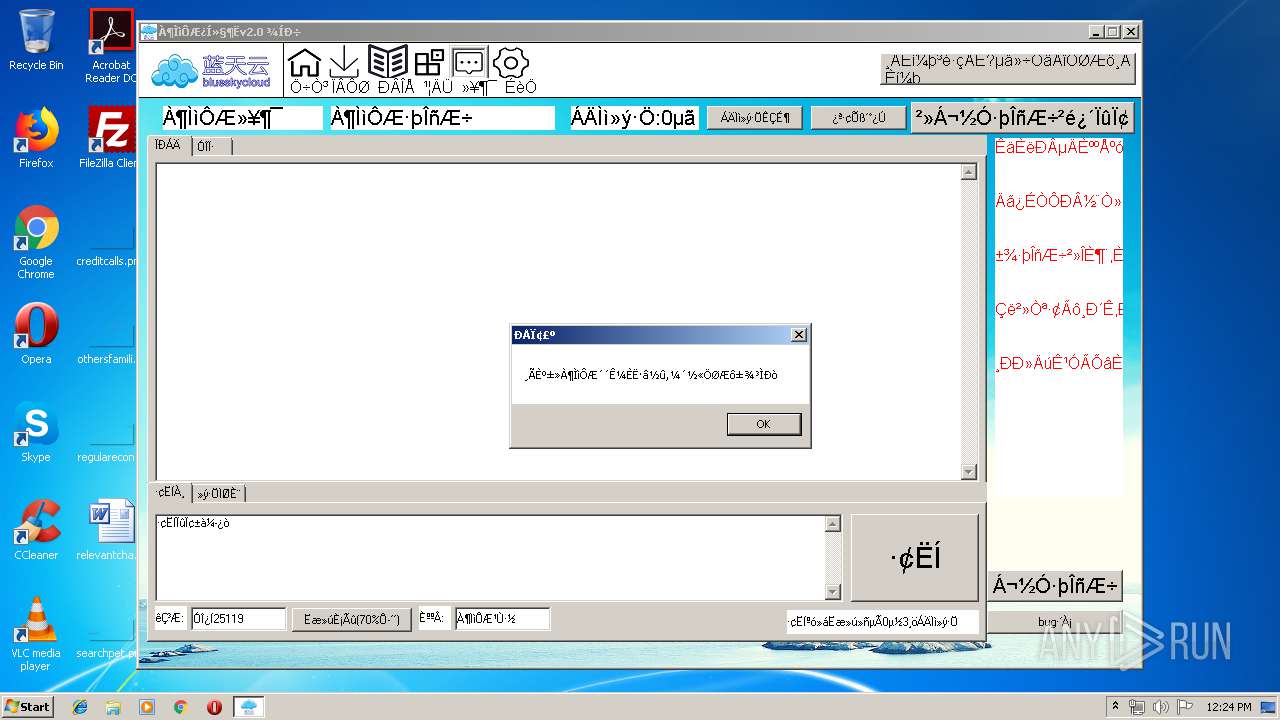
MALICIOUS
Loads dropped or rewritten executable
- 3.exe (PID: 3808)
- 3.exe (PID: 1224)
- 3.exe (PID: 3756)
SUSPICIOUS
Application launched itself
- 3.exe (PID: 3808)
- 3.exe (PID: 3756)
Executable content was dropped or overwritten
- 3.exe (PID: 1224)
- 3.exe (PID: 3808)
- 3.exe (PID: 3756)
INFO
Dropped object may contain Bitcoin addresses
- 3.exe (PID: 3756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (52.5) |
|---|---|---|
| .scr | | | Windows screen saver (22) |
| .dll | | | Win32 Dynamic Link Library (generic) (11) |
| .exe | | | Win32 Executable (generic) (7.5) |
| .exe | | | Generic Win/DOS Executable (3.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1972:12:25 06:33:23+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5.6 |
| CodeSize: | 20480 |
| InitializedDataSize: | 4182016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3861 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
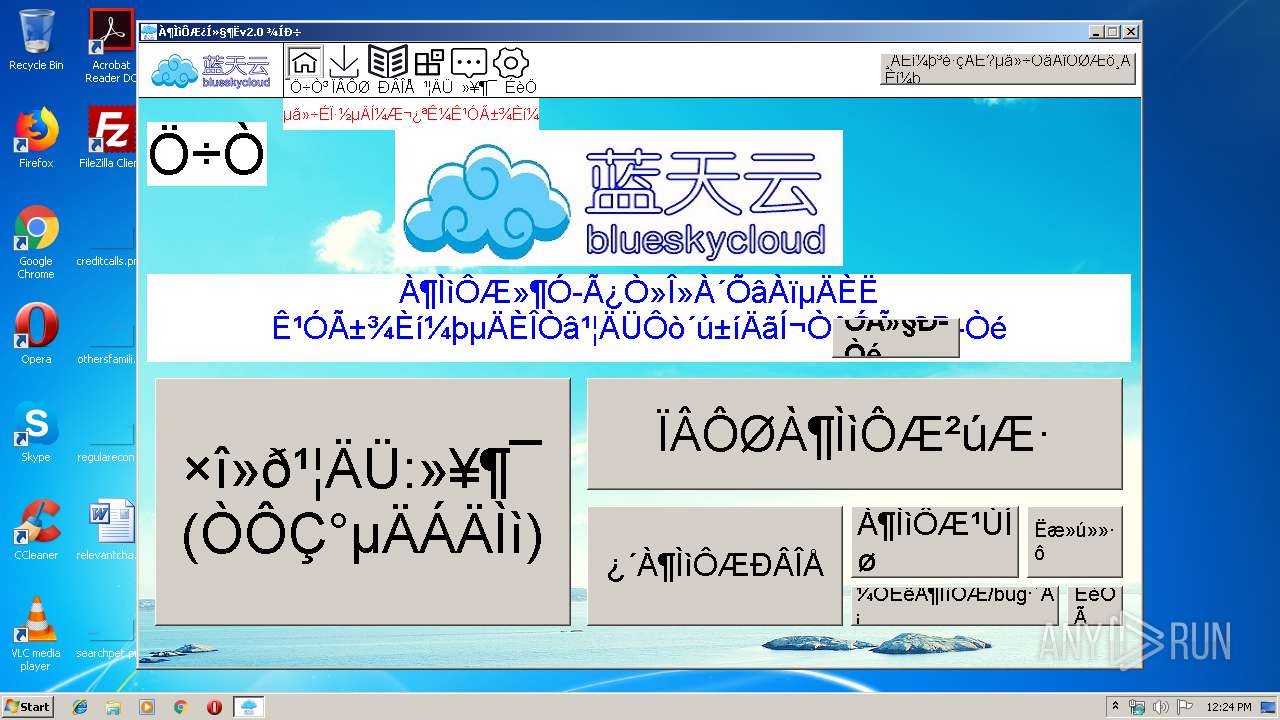
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| FileDescription: | 易语言程序 |
| ProductName: | 易语言程序 |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | 作者版权所有 请尊重并使用正版 |
| Comments: | 本程序使用易语言编写(http://www.eyuyan.com) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-1972 05:33:23 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| FileDescription: | 易语言程序 |
| ProductName: | 易语言程序 |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | 作者版权所有 请尊重并使用正版 |
| Comments: | 本程序使用易语言编写(http://www.eyuyan.com) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Dec-1972 05:33:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00004DCC | 0x00005000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52193 |
.rdata | 0x00006000 | 0x00000A4A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.55983 |
.data | 0x00009000 | 0x003F7000 | 0x003F7000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.94 |
.rsrc | 0x00400000 | 0x00002AFC | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.40772 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
129 | 1.91924 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1224 | C:\Users\admin\AppData\Local\Temp\3.exe | C:\Users\admin\AppData\Local\Temp\3.exe | 3.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3756 | "C:\Users\admin\AppData\Local\Temp\3.exe" | C:\Users\admin\AppData\Local\Temp\3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3808 | C:\Users\admin\AppData\Local\Temp\3.exe | C:\Users\admin\AppData\Local\Temp\3.exe | 3.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
90
Read events
60
Write events
30
Delete events
0
Modification events
| (PID) Process: | (3756) 3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\3_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3756) 3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\3_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3756) 3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\3_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) 3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\3_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) 3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\3_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3756) 3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\3_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3756) 3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\3_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3756) 3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\3_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3756) 3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\3_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) 3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\3_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
21
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
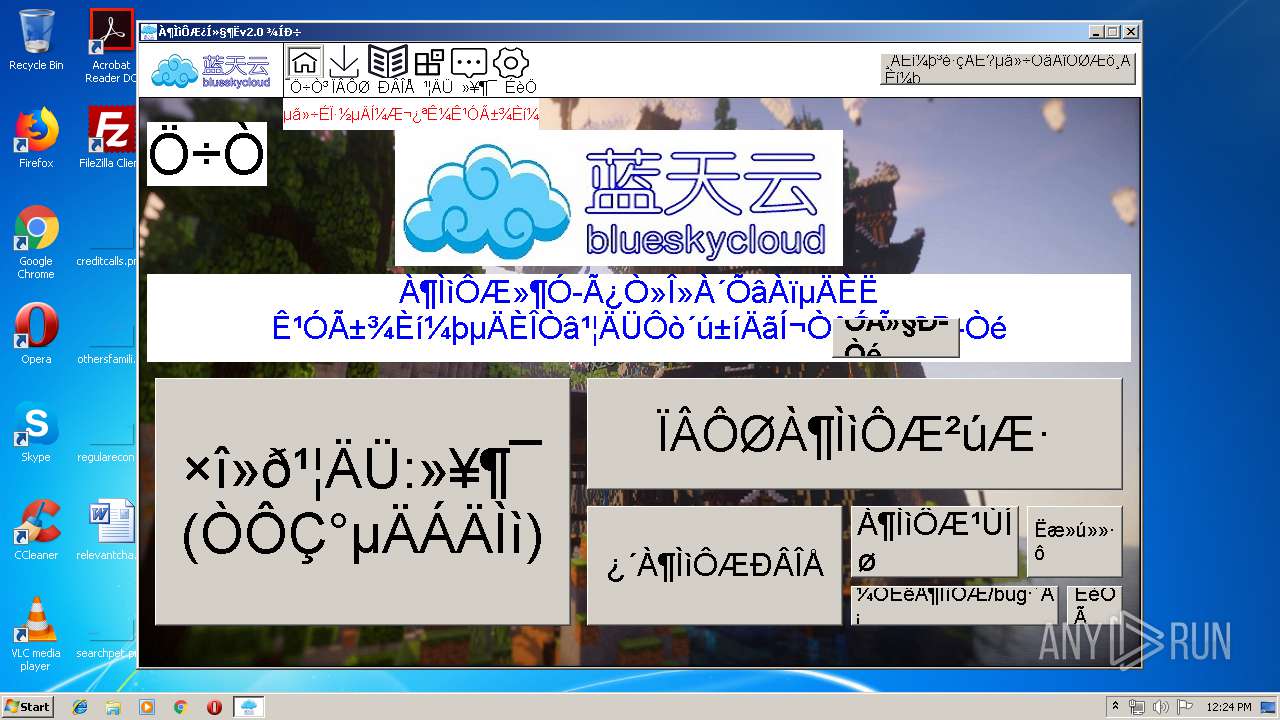
| 3756 | 3.exe | C:\Users\admin\AppData\Local\Temp\À¶ÌìÔƹٷ½.x | — | |
MD5:— | SHA256:— | |||
| 3808 | 3.exe | C:\Users\admin\AppData\Local\Temp\À¶ÌìÔƹٷ½.x | — | |
MD5:— | SHA256:— | |||
| 3756 | 3.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\GDI+Ö§³Ö¿â.fne | executable | |
MD5:77EA76FF8B4BCE61C5955BC31BB33518 | SHA256:316E6B6BF5DB2EEDCFFBC3204423A17583B4EADA920A3BB86605EE762C591687 | |||
| 3756 | 3.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\dp1.fne | executable | |
MD5:07201B1FD5F8925DD49A4556AC3B5BAB | SHA256:ABEBBB0981D3D51EB63ABCFA68BE98DA0CAE4E6E3B143DD431FC845D1457DBD2 | |||
| 3756 | 3.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\eAPI.fne | executable | |
MD5:7C1FF88991F5EAFAB82B1BEAEFC33A42 | SHA256:53483523C316AD8C022C2B07A5CABFFF3339BC5CB5E4AC24C3260EEA4F4D9731 | |||
| 3808 | 3.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\À¶ÌìÔƹٷ½[1].htm | text | |
MD5:— | SHA256:— | |||
| 3756 | 3.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\À¶ÌìÔƹٷ½[1].htm | text | |
MD5:— | SHA256:— | |||
| 3756 | 3.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\spec.fne | executable | |
MD5:BD6EEF5EA9A52A412A8F57490D8BD8E4 | SHA256:0C9E6EB8648F4BF5C585D5344035E91C3249BB9686A302503B4681B7BA828DC0 | |||
| 3808 | 3.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\iext2.fne | executable | |
MD5:DBA5FDBE7EC94463B3F6FDF2162C9F95 | SHA256:A8B14F31098A191631696DB5DDC77E029B48999542E0EC15B63DF02220C66D37 | |||
| 3756 | 3.exe | C:\Users\admin\AppData\Local\Temp\E_N60005\internet.fne | executable | |
MD5:7B129C5916896C845752F93B9635FC4C | SHA256:ADC45970F4A0EAFD2F372302F64836802380C253096A99CA964677A70A7128F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
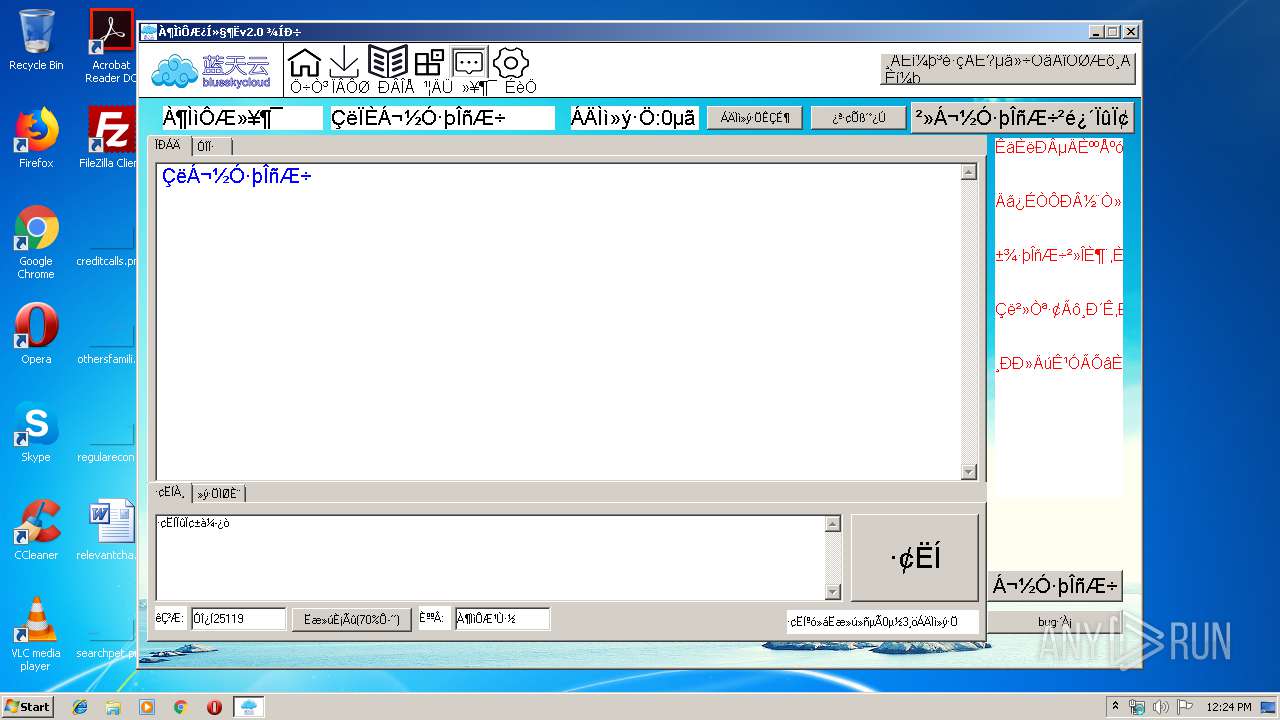
HTTP(S) requests
8
TCP/UDP connections
9
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3756 | 3.exe | GET | 200 | 173.82.115.72:80 | http://maorenjie147.web3v.vip/app.html | US | text | 1.91 Kb | suspicious |
3756 | 3.exe | GET | 200 | 173.82.115.72:80 | http://maorenjie147.web3v.vip/@6LlTF9Y7=.html | US | text | 709 b | suspicious |
3756 | 3.exe | GET | 200 | 173.82.115.72:80 | http://maorenjie147.web3v.vip/news.html | US | text | 209 b | suspicious |
3808 | 3.exe | GET | 200 | 173.82.115.72:80 | http://maorenjie147.web3v.vip/news.html | US | text | 209 b | suspicious |
3808 | 3.exe | GET | 200 | 173.82.115.72:80 | http://maorenjie147.web3v.vip/app.html | US | text | 1.91 Kb | suspicious |
3808 | 3.exe | GET | 200 | 173.82.115.72:80 | http://maorenjie147.web3v.vip/@6LlTF9Y7=.html | US | text | 709 b | suspicious |
1224 | 3.exe | GET | 200 | 173.82.115.72:80 | http://maorenjie147.web3v.vip/news.html | US | text | 209 b | suspicious |
1224 | 3.exe | GET | 200 | 173.82.115.72:80 | http://maorenjie147.web3v.vip/app.html | US | text | 1.91 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3756 | 3.exe | 173.82.115.72:80 | maorenjie147.web3v.vip | MULTACOM CORPORATION | US | suspicious |
3756 | 3.exe | 52.128.243.181:21 | 007.3vftp.com | — | US | unknown |
3756 | 3.exe | 52.128.243.181:4902 | 007.3vftp.com | — | US | unknown |
3756 | 3.exe | 52.128.243.181:4916 | 007.3vftp.com | — | US | unknown |
3808 | 3.exe | 173.82.115.72:80 | maorenjie147.web3v.vip | MULTACOM CORPORATION | US | suspicious |
3808 | 3.exe | 52.128.243.181:21 | 007.3vftp.com | — | US | unknown |
3808 | 3.exe | 52.128.243.181:4990 | 007.3vftp.com | — | US | unknown |
1224 | 3.exe | 173.82.115.72:80 | maorenjie147.web3v.vip | MULTACOM CORPORATION | US | suspicious |
3808 | 3.exe | 52.128.243.181:4994 | 007.3vftp.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
maorenjie147.web3v.vip |
| suspicious |
007.3vftp.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3756 | 3.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3756 | 3.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3756 | 3.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3808 | 3.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
1224 | 3.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
1224 | 3.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |