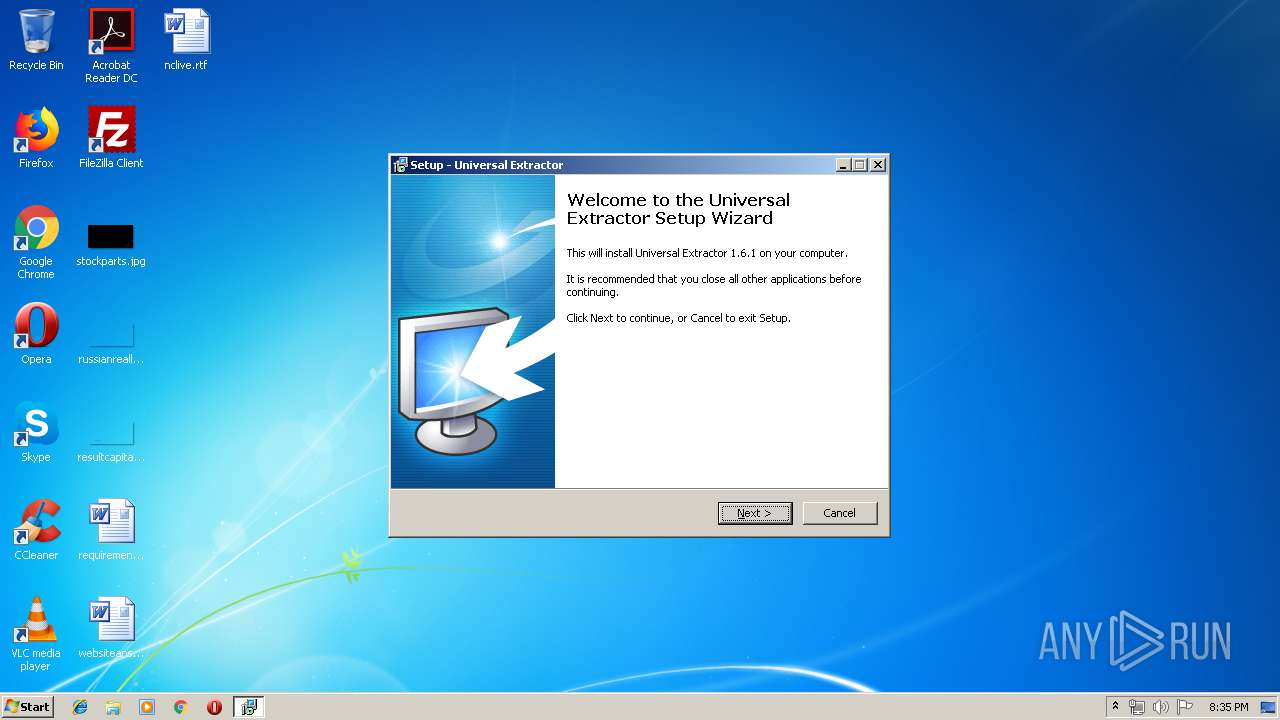
| File name: | uniextract161.exe |
| Full analysis: | https://app.any.run/tasks/752b3657-5026-44ec-a706-96241ca1990c |
| Verdict: | Suspicious activity |
| Analysis date: | June 19, 2019, 19:35:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 551AB65DAA00A24089B40725D9F97BE1 |
| SHA1: | 2E31438E3DA025877B3394344D54D7C31C646863 |
| SHA256: | 6DF6A742C23EEFA480CB37BAD3835C5005801C61168D32610504EEB72C7B7F30 |
| SSDEEP: | 98304:8T5CA7FsoyEuYFV2rNDw7TyIZu16Mxb9bgyP3HVj4jBttyJOA+N:89CAJBuM2rN07uIMxZbBPXVROAa |
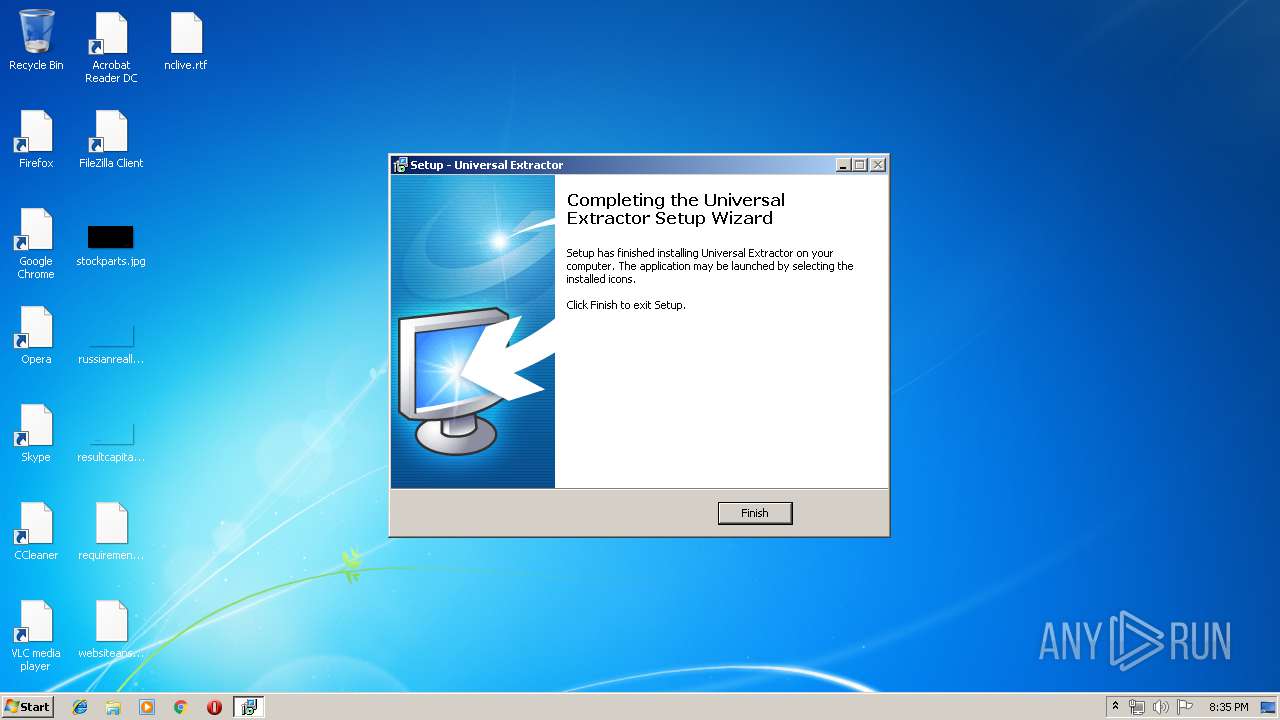
MALICIOUS
Application was dropped or rewritten from another process
- UniExtract.exe (PID: 2160)
SUSPICIOUS
Executable content was dropped or overwritten
- uniextract161.exe (PID: 2720)
- uniextract161.exe (PID: 3456)
- uniextract161.tmp (PID: 3048)
Reads Windows owner or organization settings
- uniextract161.tmp (PID: 3048)
Reads the Windows organization settings
- uniextract161.tmp (PID: 3048)
INFO
Application was dropped or rewritten from another process
- uniextract161.tmp (PID: 1352)
- uniextract161.tmp (PID: 3048)
Loads dropped or rewritten executable
- uniextract161.tmp (PID: 3048)
Creates a software uninstall entry
- uniextract161.tmp (PID: 3048)
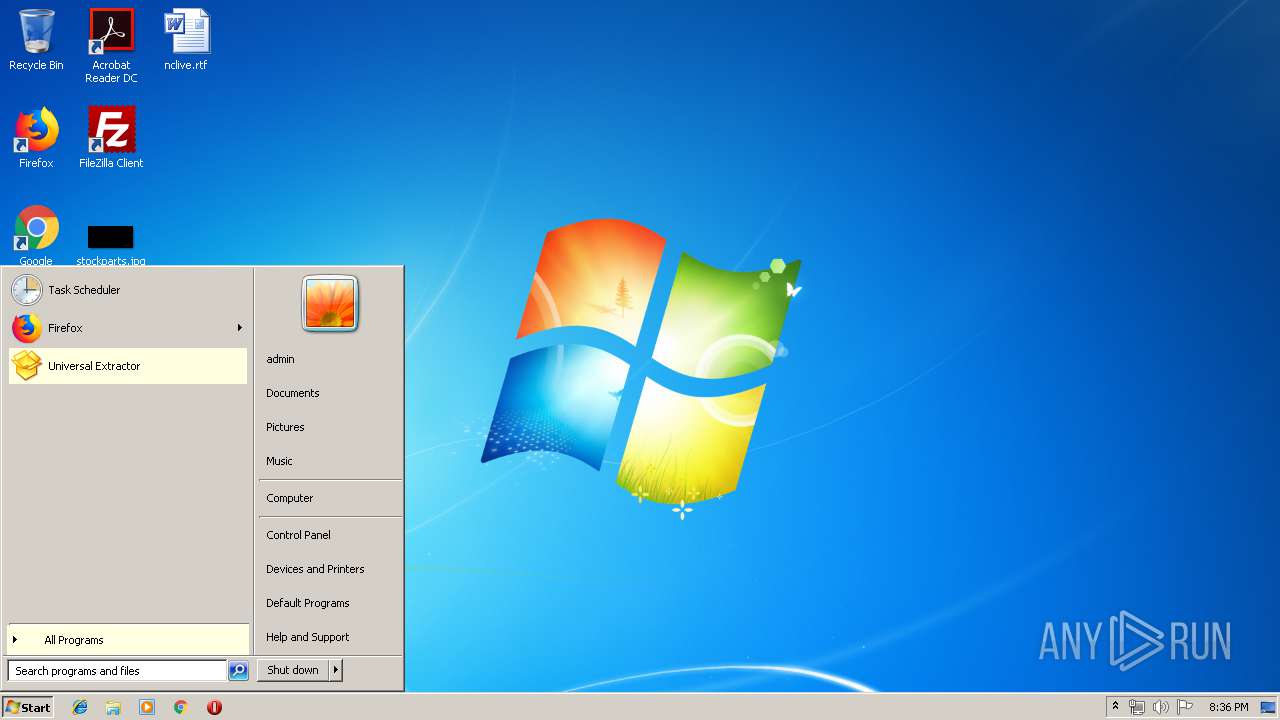
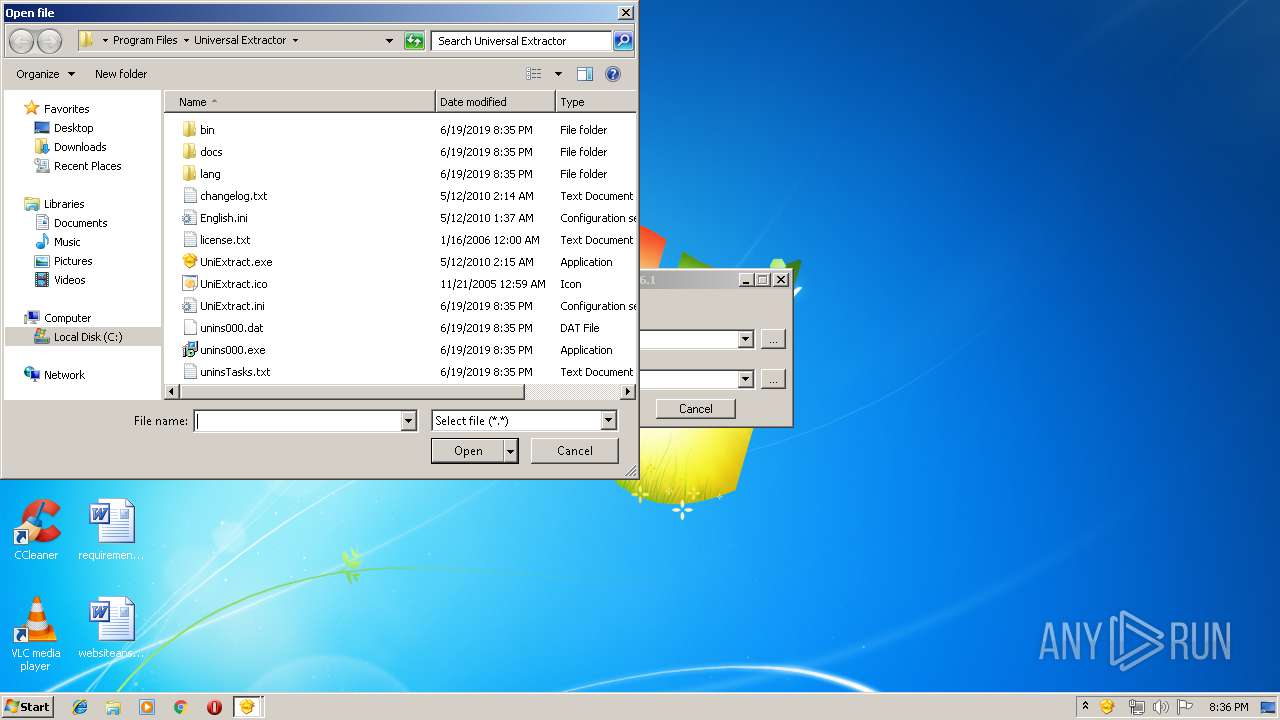
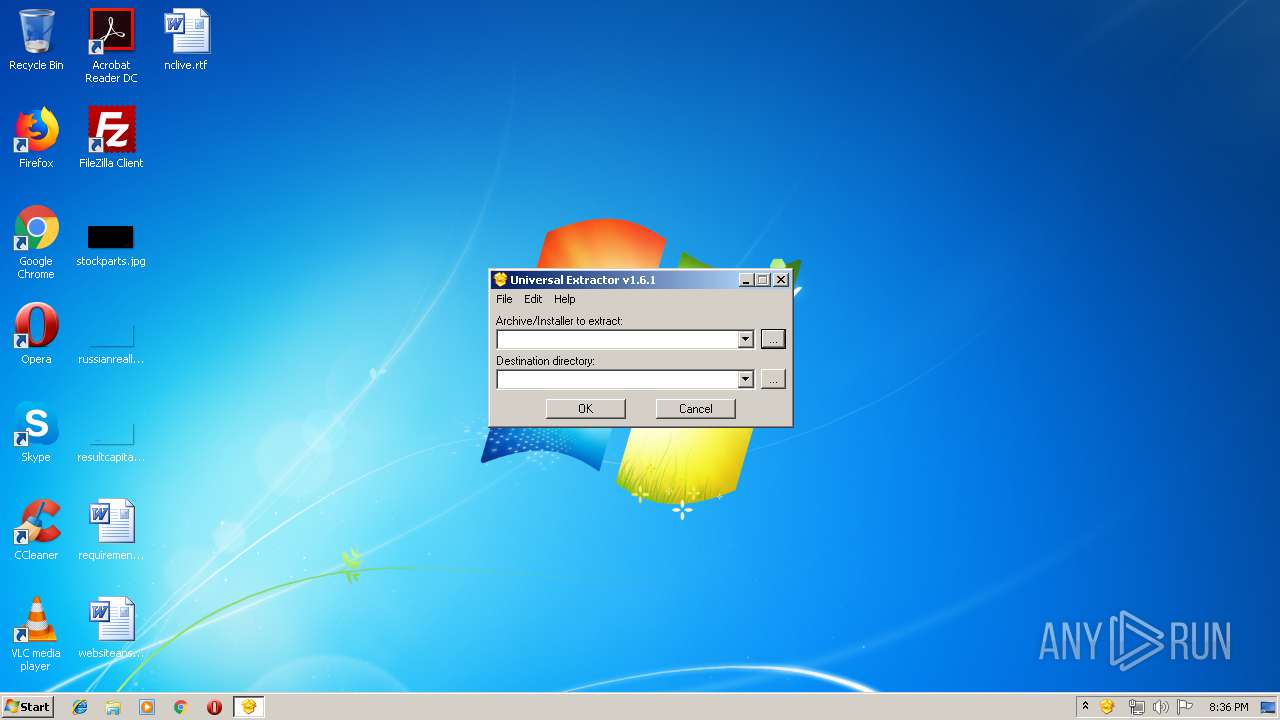
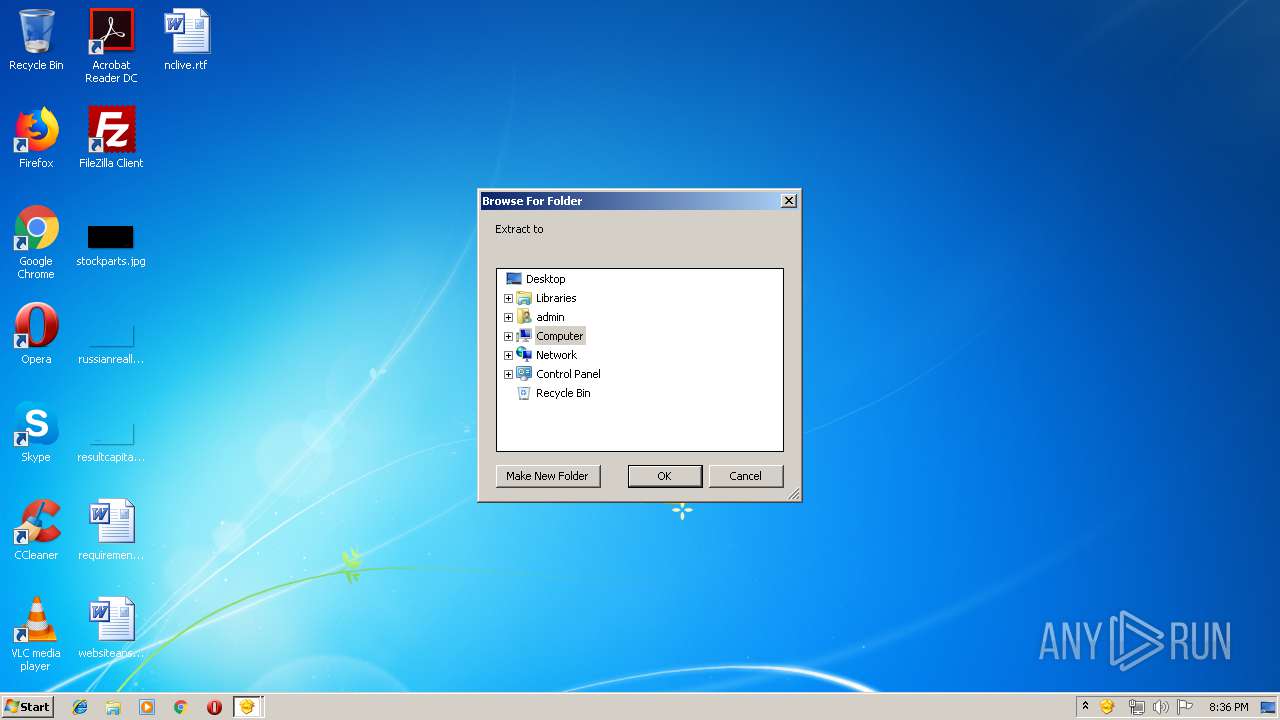
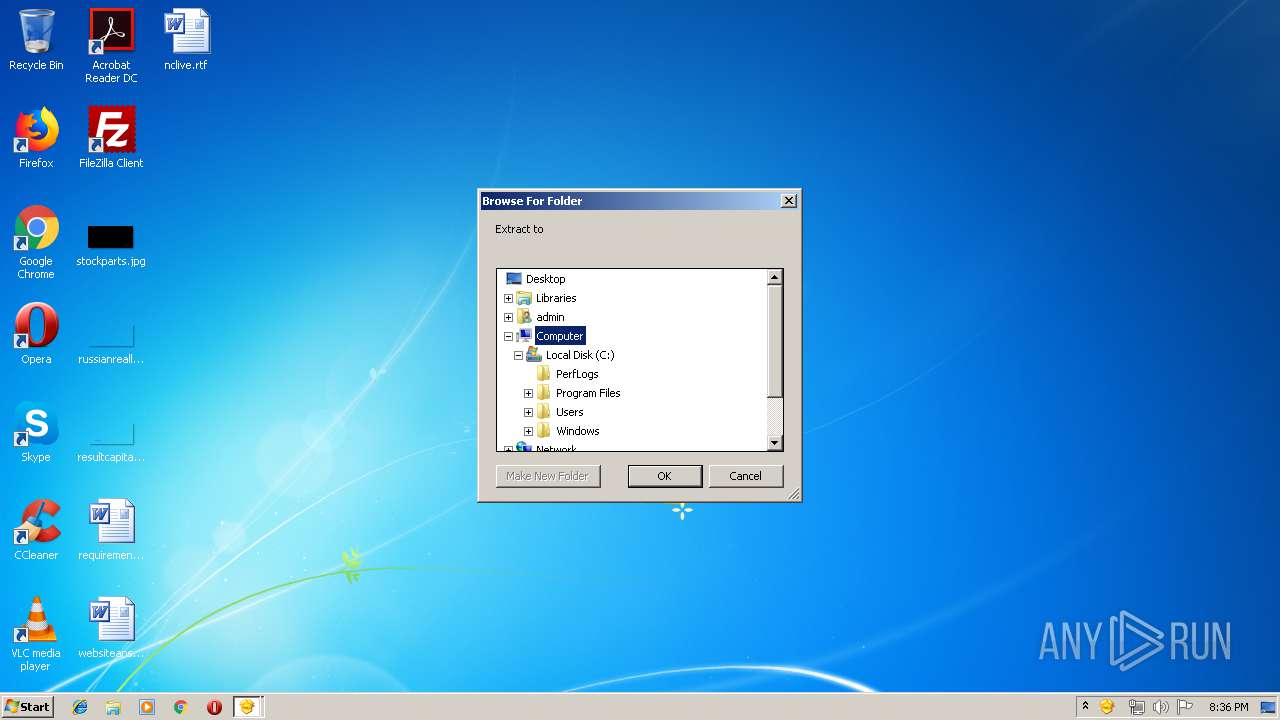
Manual execution by user
- UniExtract.exe (PID: 2160)
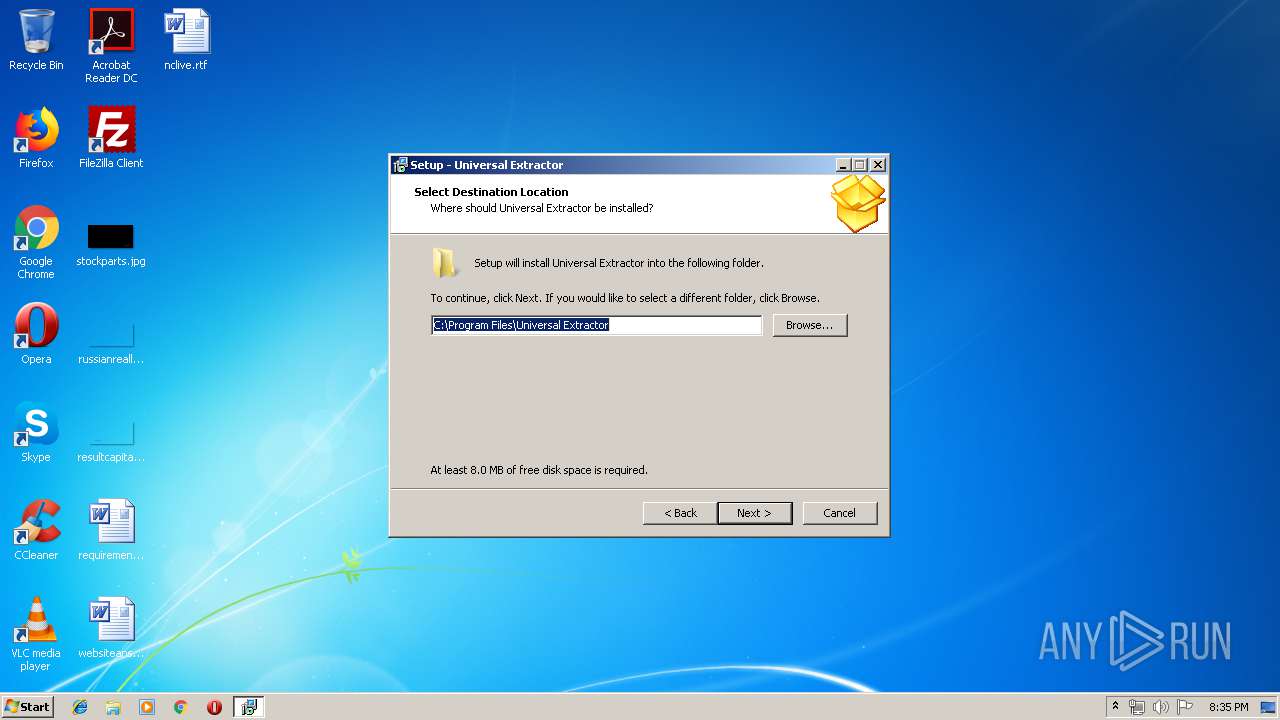
Creates files in the program directory
- uniextract161.tmp (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:10 18:57:59+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 87040 |
| InitializedDataSize: | 60416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x163c4 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
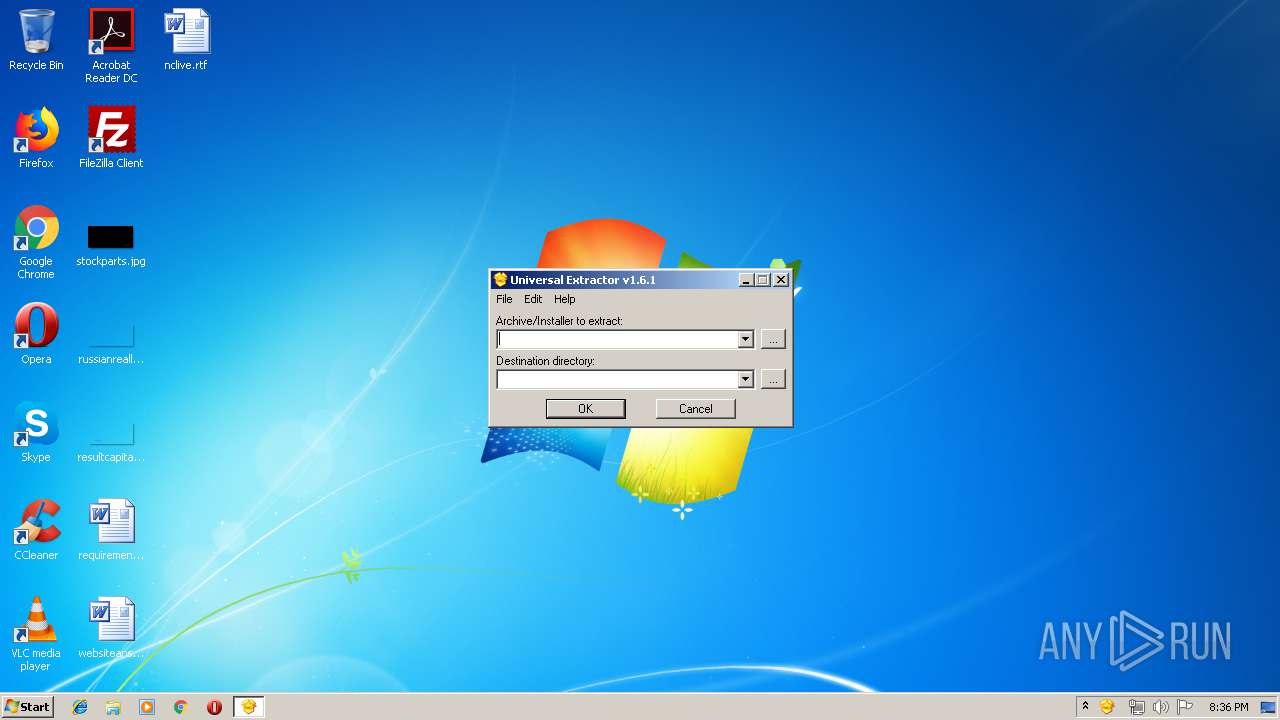
| FileVersionNumber: | 1.6.1.0 |
| ProductVersionNumber: | 1.6.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Jared Breland |
| FileDescription: | Package for Universal Extractor |
| FileVersion: | 1.6.1 |
| LegalCopyright: | GNU General Public License v2 |
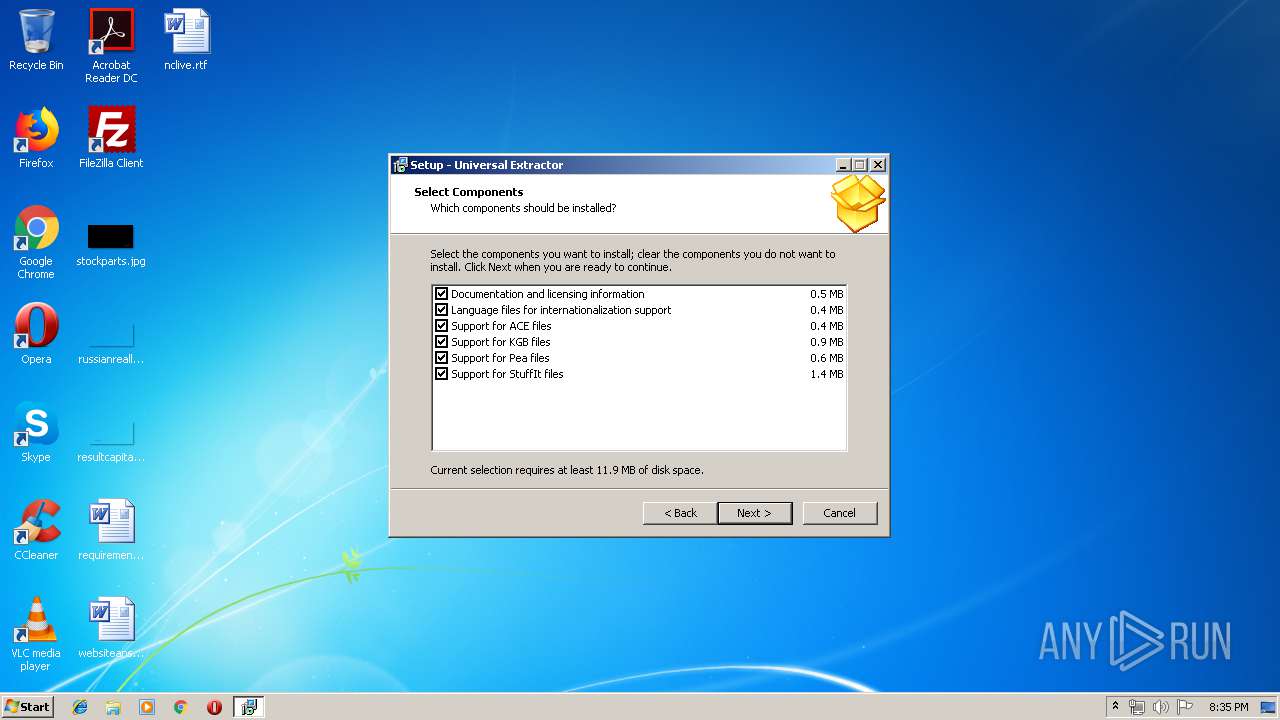
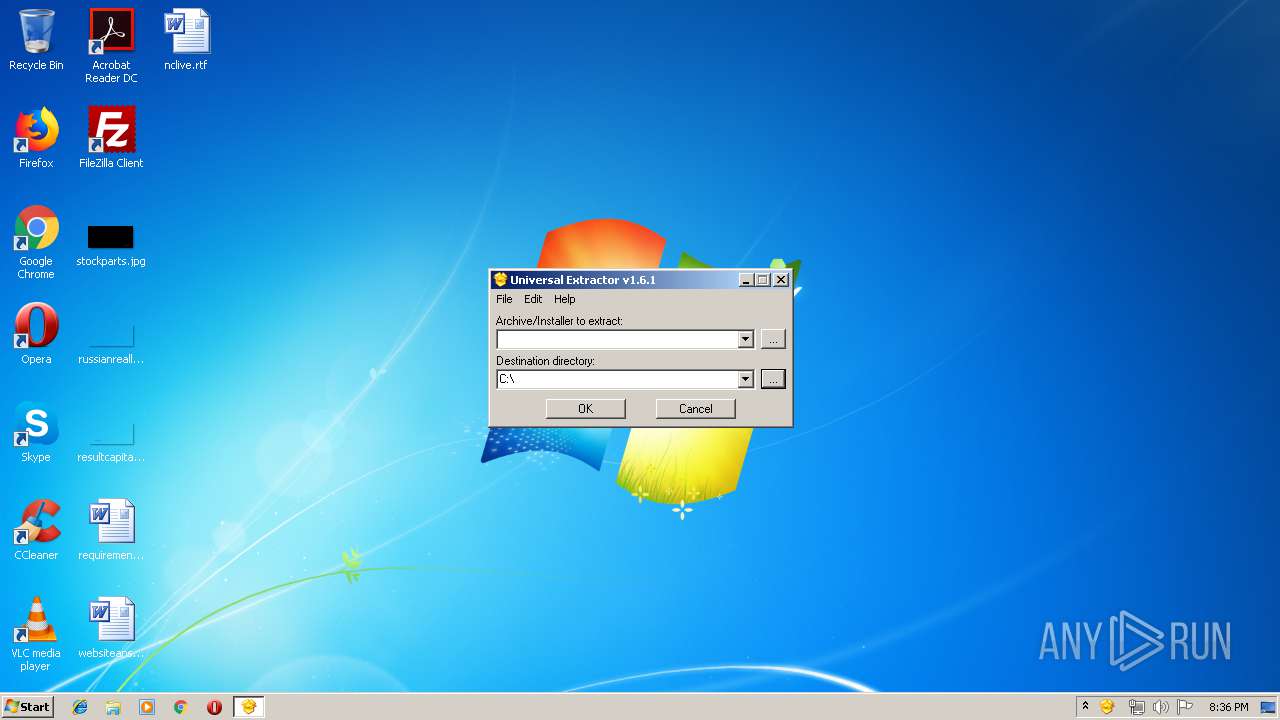
| ProductName: | Universal Extractor |
| ProductVersion: | 1.6.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Apr-2010 16:57:59 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Jared Breland |
| FileDescription: | Package for Universal Extractor |
| FileVersion: | 1.6.1 |
| LegalCopyright: | GNU General Public License v2 |
| ProductName: | Universal Extractor |
| ProductVersion: | 1.6.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 10-Apr-2010 16:57:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001468C | 0x00014800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46621 |
.itext | 0x00016000 | 0x00000B34 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.79471 |
.data | 0x00017000 | 0x00000D9C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.67747 |
.bss | 0x00018000 | 0x00005714 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001E000 | 0x00000F9E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96778 |
.tls | 0x0001F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00020000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.190489 |
.reloc | 0x00021000 | 0x00001944 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0 |
.rsrc | 0x00023000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.15549 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 3.13038 | 196 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.36196 | 204 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.34841 | 372 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.29351 | 924 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
41
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1352 | "C:\Users\admin\AppData\Local\Temp\is-9PLKM.tmp\uniextract161.tmp" /SL5="$70256,5065856,141824,C:\Users\admin\AppData\Local\Temp\uniextract161.exe" | C:\Users\admin\AppData\Local\Temp\is-9PLKM.tmp\uniextract161.tmp | — | uniextract161.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Universal Extractor\UniExtract.exe" | C:\Program Files\Universal Extractor\UniExtract.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Universal Extractor Exit code: 0 Version: 1.6.1 Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Local\Temp\uniextract161.exe" | C:\Users\admin\AppData\Local\Temp\uniextract161.exe | explorer.exe | ||||||||||||
User: admin Company: Jared Breland Integrity Level: MEDIUM Description: Package for Universal Extractor Exit code: 0 Version: 1.6.1 Modules
| |||||||||||||||
| 3048 | "C:\Users\admin\AppData\Local\Temp\is-1QP8G.tmp\uniextract161.tmp" /SL5="$90230,5065856,141824,C:\Users\admin\AppData\Local\Temp\uniextract161.exe" /SPAWNWND=$6023E /NOTIFYWND=$70256 | C:\Users\admin\AppData\Local\Temp\is-1QP8G.tmp\uniextract161.tmp | uniextract161.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3456 | "C:\Users\admin\AppData\Local\Temp\uniextract161.exe" /SPAWNWND=$6023E /NOTIFYWND=$70256 | C:\Users\admin\AppData\Local\Temp\uniextract161.exe | uniextract161.tmp | ||||||||||||
User: admin Company: Jared Breland Integrity Level: HIGH Description: Package for Universal Extractor Exit code: 0 Version: 1.6.1 Modules
| |||||||||||||||
Total events
1 601
Read events
1 319
Write events
281
Delete events
1
Modification events
| (PID) Process: | (3048) uniextract161.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\UniExtract.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\Universal Extractor\UniExtract.exe | |||
| (PID) Process: | (3048) uniextract161.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\UniExtract.exe |
| Operation: | write | Name: | Path |
Value: C:\Program Files\Universal Extractor | |||
| (PID) Process: | (3048) uniextract161.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UniExtract |
| Operation: | write | Name: | |
Value: Universal Extractor Archive | |||
| (PID) Process: | (3048) uniextract161.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UniExtract\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Program Files\Universal Extractor\UniExtract.ico | |||
| (PID) Process: | (3048) uniextract161.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UniExtract\shell\uniextract |
| Operation: | write | Name: | |
Value: UniExtract &Files... | |||
| (PID) Process: | (3048) uniextract161.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UniExtract\shell\uniextract\command |
| Operation: | write | Name: | |
Value: "C:\Program Files\Universal Extractor\uniextract.exe" "%1" | |||
| (PID) Process: | (3048) uniextract161.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UniExtract\shell\uniextract_here |
| Operation: | write | Name: | |
Value: UniExtract &Here | |||
| (PID) Process: | (3048) uniextract161.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UniExtract\shell\uniextract_here\command |
| Operation: | write | Name: | |
Value: "C:\Program Files\Universal Extractor\uniextract.exe" "%1" . | |||
| (PID) Process: | (3048) uniextract161.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UniExtract\shell\uniextract_sub |
| Operation: | write | Name: | |
Value: UniExtract to &Subdir | |||
| (PID) Process: | (3048) uniextract161.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\UniExtract\shell\uniextract_sub\command |
| Operation: | write | Name: | |
Value: "C:\Program Files\Universal Extractor\uniextract.exe" "%1" /sub | |||
Executable files
65
Suspicious files
0
Text files
159
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3048 | uniextract161.tmp | C:\Users\admin\AppData\Local\Temp\is-NT503.tmp\English.ini | text | |
MD5:FACB4039A8FEAE4F73BFB2AD797BCB4B | SHA256:557362374EEC538314FA4A60031EC395F99FF465BB475AB7CDCCE88F2A7D7B77 | |||
| 3048 | uniextract161.tmp | C:\Users\admin\AppData\Local\Temp\is-NT503.tmp\Arabic.ini | text | |
MD5:386B515E053DD4E30938B72891B55BEC | SHA256:E9432780CCF573CA48CF5DA973A2740279F2DCFBAC5CC1038F9218DCCABDDB9A | |||
| 3048 | uniextract161.tmp | C:\Users\admin\AppData\Local\Temp\is-NT503.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 3456 | uniextract161.exe | C:\Users\admin\AppData\Local\Temp\is-1QP8G.tmp\uniextract161.tmp | executable | |
MD5:713BFB93270414F034FA70496D5CFFFC | SHA256:8F7C04C54C61B7F11D3C6016254ABAAB89997CB0D5198E8C7EF0DF2EDBCA16D7 | |||
| 3048 | uniextract161.tmp | C:\Users\admin\AppData\Local\Temp\is-NT503.tmp\German.ini | text | |
MD5:03F84963ABAA842E124AA14D535CC912 | SHA256:753BABAA77BAD4BC54174096B72314F92ADBBB5DF99337BB529C803F9AB25C61 | |||
| 3048 | uniextract161.tmp | C:\Users\admin\AppData\Local\Temp\is-NT503.tmp\Japanese.ini | text | |
MD5:003CDA8197AB7F58988DFF8DFD8DECD8 | SHA256:1FF984CB36D0AA98431AFCD3E26A05D91CBE553FAB19F602C83DE2983A654F37 | |||
| 3048 | uniextract161.tmp | C:\Users\admin\AppData\Local\Temp\is-NT503.tmp\Italian.ini | text | |
MD5:6CAAE9E2C3B310FBAFF65BC80ADC6A25 | SHA256:9ECB01FCF17BD9286FBCB33DA131F354400E85ECDAA135BB2832667ECBC45C1F | |||
| 3048 | uniextract161.tmp | C:\Users\admin\AppData\Local\Temp\is-NT503.tmp\Korean.ini | text | |
MD5:E15337D23C076E96716E5077FB36A22B | SHA256:7ADC907C5F554B1A47E8E8BA3229AB252BECFC5D29712EEAD7A5E019598CFCF9 | |||
| 3048 | uniextract161.tmp | C:\Program Files\Universal Extractor\is-N3U6N.tmp | — | |
MD5:— | SHA256:— | |||
| 3048 | uniextract161.tmp | C:\Users\admin\AppData\Local\Temp\is-NT503.tmp\Portuguese.ini | text | |
MD5:97A3EE2FC9E0031FD2D17B92A0E43816 | SHA256:3FC6D8C6549D6D62FD727546F73539052FBFA828BC27D61D96B789BA494F95BF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report