| File name: | u1806 (2).exe |
| Full analysis: | https://app.any.run/tasks/55a17939-575d-4f89-8137-9376bd41ee3b |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2018, 16:36:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 621550F1287A6C72DE1321553F34847E |
| SHA1: | 2DAACFCC5E5A0EF16C8D9EA5ED97A1132B727522 |
| SHA256: | 6DF55C9E31F958DA74249DA9007FD672D08D4411CD5D54DB05E55B4C01B121FE |
| SSDEEP: | 98304:VElRxPh4LqXGer2lpNdXvaU4EXLNbfcJJ227Q1oMLjLtQpX7fcQBsozPo/Bhepq:C1JnGKypNVd3XRbEJJofj5AXoQBsGwfT |
MALICIOUS
Changes internet zones settings
- u1806 (2).exe (PID: 3124)
Application was dropped or rewritten from another process
- u.exe (PID: 3872)
- u.exe (PID: 4076)
SUSPICIOUS
Reads Internet Cache Settings
- rundll32.exe (PID: 3704)
- rundll32.exe (PID: 3560)
- rundll32.exe (PID: 3588)
- rundll32.exe (PID: 2808)
- rundll32.exe (PID: 3976)
- rundll32.exe (PID: 2912)
Uses RUNDLL32.EXE to load library
- u1806 (2).exe (PID: 3124)
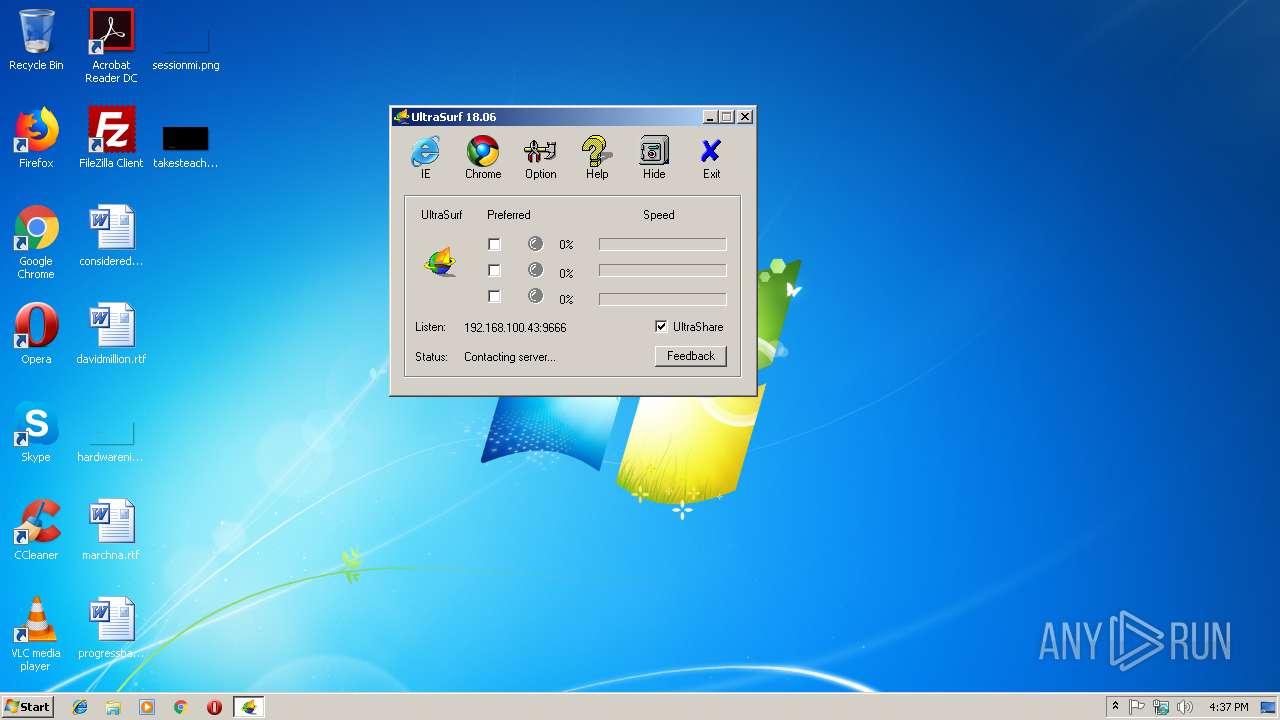
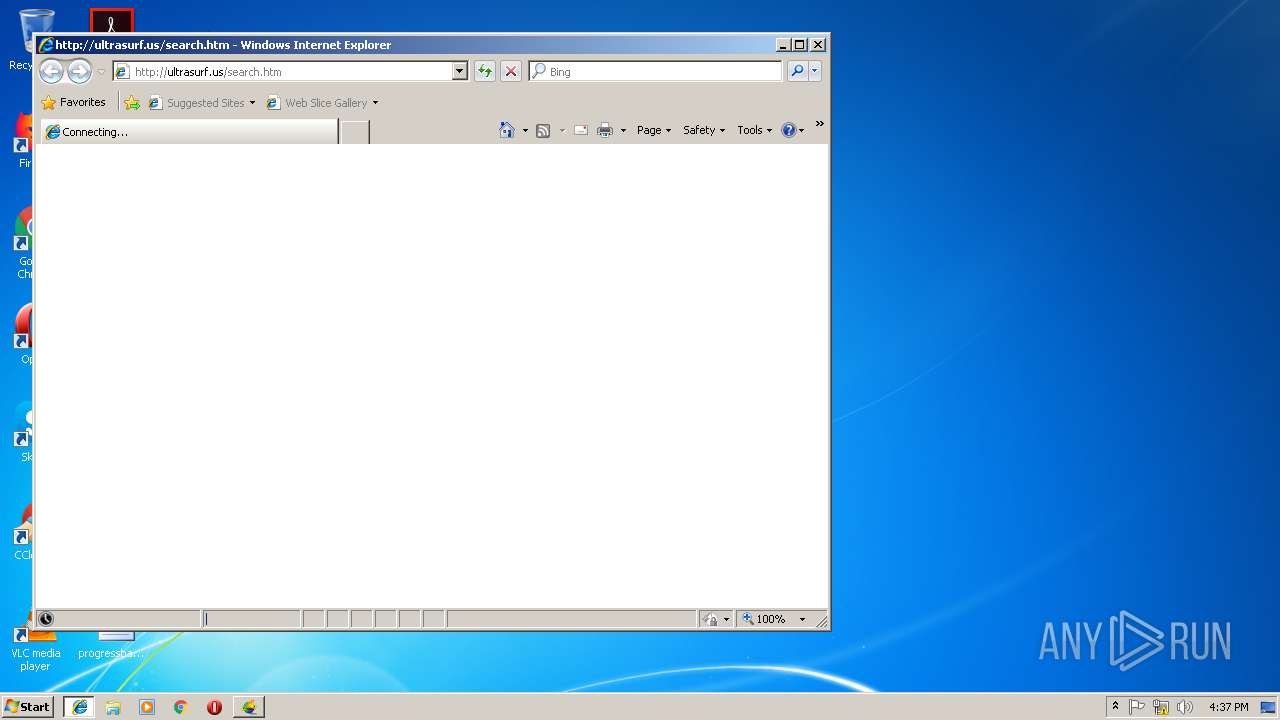
Starts Internet Explorer
- u1806 (2).exe (PID: 3124)
Executable content was dropped or overwritten
- u1806 (2).exe (PID: 3124)
INFO
Application launched itself
- iexplore.exe (PID: 3148)
Creates files in the user directory
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3524)
Reads Internet Cache Settings
- iexplore.exe (PID: 3524)
Changes internet zones settings
- iexplore.exe (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (33) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (32.4) |
| .scr | | | Windows screen saver (16) |
| .dll | | | Win32 Dynamic Link Library (generic) (8) |
| .exe | | | Win32 Executable (generic) (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:23 08:33:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 3653632 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | 1306624 |
| EntryPoint: | 0x4bb6b0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Nov-2018 07:33:14 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 23-Nov-2018 07:33:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0013F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00140000 | 0x0037C000 | 0x0037BA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.8231 |
.rsrc | 0x004BC000 | 0x00003000 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.67175 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
NETAPI32.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
WINMM.dll |
WINSPOOL.DRV |
Total processes
40
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2808 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | u1806 (2).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2912 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | u1806 (2).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3124 | "C:\Users\admin\AppData\Local\Temp\u1806 (2).exe" | C:\Users\admin\AppData\Local\Temp\u1806 (2).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Internet Explorer\iexplore.exe" http://ultrasurf.us/search.htm | C:\Program Files\Internet Explorer\iexplore.exe | u1806 (2).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3524 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3148 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3560 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | u1806 (2).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3588 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | u1806 (2).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3704 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | u1806 (2).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3872 | C:\Users\admin\AppData\Local\Temp\utmp\u.exe -L="127.0.0.1:9666" -CID="40e0c2f6", -ProgPath="C:\Users\admin\AppData\Local\Temp\\" -TmpPath="C:\Users\admin\AppData\Local\Temp\utmp\\" -ConnMode=0 -version="1806100" | C:\Users\admin\AppData\Local\Temp\utmp\u.exe | u1806 (2).exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3976 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | u1806 (2).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
504
Read events
354
Write events
150
Delete events
0
Modification events
| (PID) Process: | (3124) u1806 (2).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1806 (2)_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3124) u1806 (2).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1806 (2)_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3124) u1806 (2).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1806 (2)_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3124) u1806 (2).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1806 (2)_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3124) u1806 (2).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1806 (2)_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3124) u1806 (2).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1806 (2)_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3124) u1806 (2).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1806 (2)_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3124) u1806 (2).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1806 (2)_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3124) u1806 (2).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1806 (2)_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3124) u1806 (2).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\u1806 (2)_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
5
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3124 | u1806 (2).exe | C:\Users\admin\AppData\Local\Temp\utmp\~mofwomjks2i4v3v | binary | |
MD5:— | SHA256:— | |||
| 3124 | u1806 (2).exe | C:\Users\admin\AppData\Local\Temp\utmp\~nafkltwgd4x3w6t | binary | |
MD5:— | SHA256:— | |||
| 3124 | u1806 (2).exe | C:\Users\admin\AppData\Local\Temp\u.ini | text | |
MD5:— | SHA256:— | |||
| 3124 | u1806 (2).exe | C:\Users\admin\AppData\Local\Temp\utmp\~lguqrmxmj9q2w3k | binary | |
MD5:— | SHA256:— | |||
| 3124 | u1806 (2).exe | C:\Users\admin\PUTTY.RND | binary | |
MD5:— | SHA256:— | |||
| 3124 | u1806 (2).exe | C:\Users\admin\AppData\Local\Temp\utmp\~cpvjabtrq1i8g5s | text | |
MD5:— | SHA256:— | |||
| 3124 | u1806 (2).exe | C:\Users\admin\AppData\Local\Temp\utmp\u.exe | executable | |
MD5:2F0ACA833F2FD867FB32B640503C3973 | SHA256:98D421FE57E56E498E804EF7476CB4039D98AE9896BA663B04AA5070185C3AFD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
47
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3872 | u.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3872 | u.exe | 172.217.168.37:443 | mail.google.com | Google Inc. | US | whitelisted |
3872 | u.exe | 66.160.201.39:443 | — | Hurricane Electric, Inc. | US | unknown |
3872 | u.exe | 72.52.112.87:443 | — | Hurricane Electric, Inc. | US | unknown |
4076 | u.exe | 172.217.168.5:443 | www.gmail.com | Google Inc. | US | whitelisted |
4076 | u.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4076 | u.exe | 74.82.60.86:443 | — | Hurricane Electric, Inc. | US | unknown |
4076 | u.exe | 74.82.17.63:443 | — | Hurricane Electric, Inc. | US | unknown |
4076 | u.exe | 64.62.232.56:443 | — | Hurricane Electric, Inc. | US | unknown |
4076 | u.exe | 66.160.188.40:443 | — | Hurricane Electric, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iecvlist.microsoft.com |
| whitelisted |
mail.google.com |
| shared |
do.skype.com |
| whitelisted |
www.gmail.com |
| shared |
dq33tynpwunh.cloudfront.net |
| suspicious |