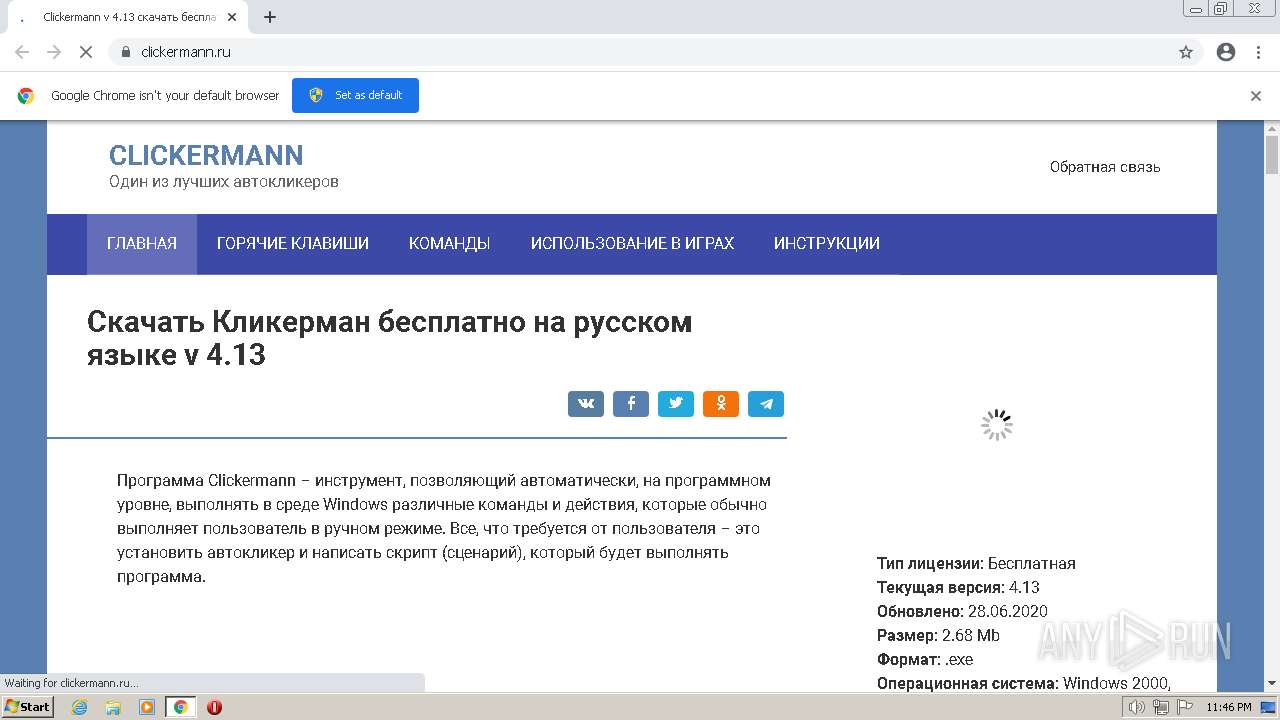
| URL: | https://clickermann.ru/ |
| Full analysis: | https://app.any.run/tasks/e18bcf83-3e12-4b24-9829-cf5b5e99fa80 |
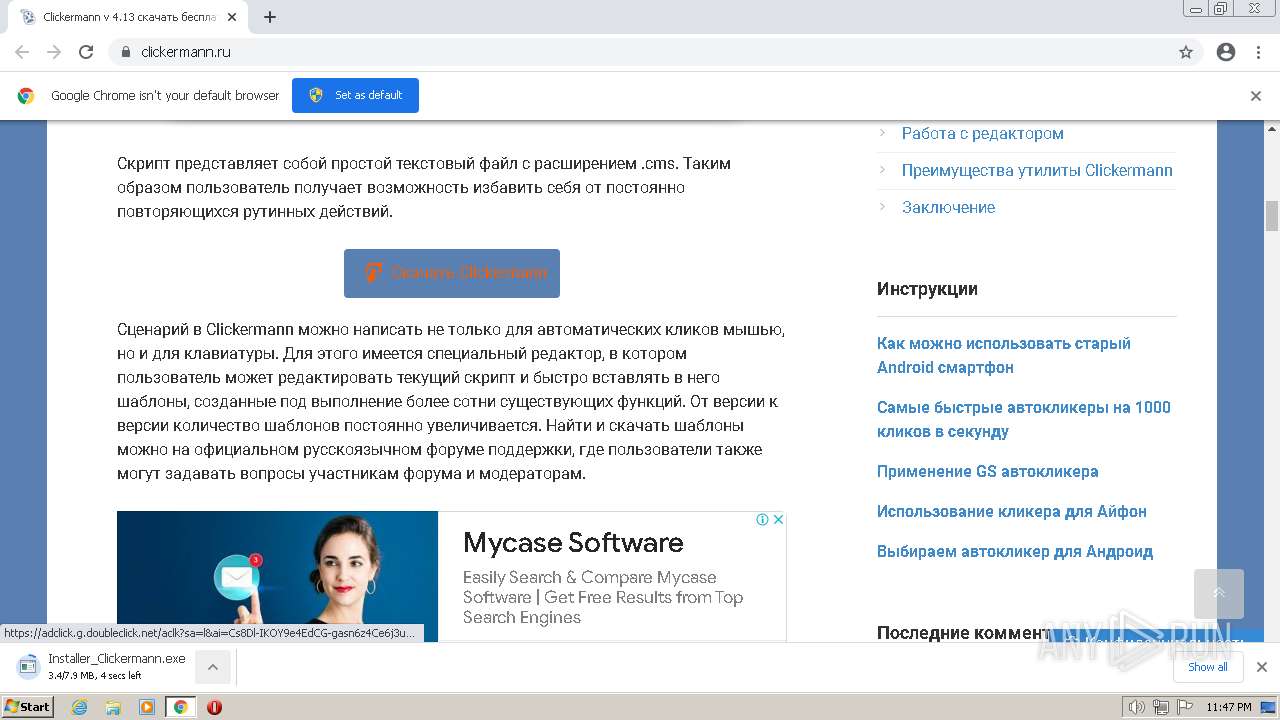
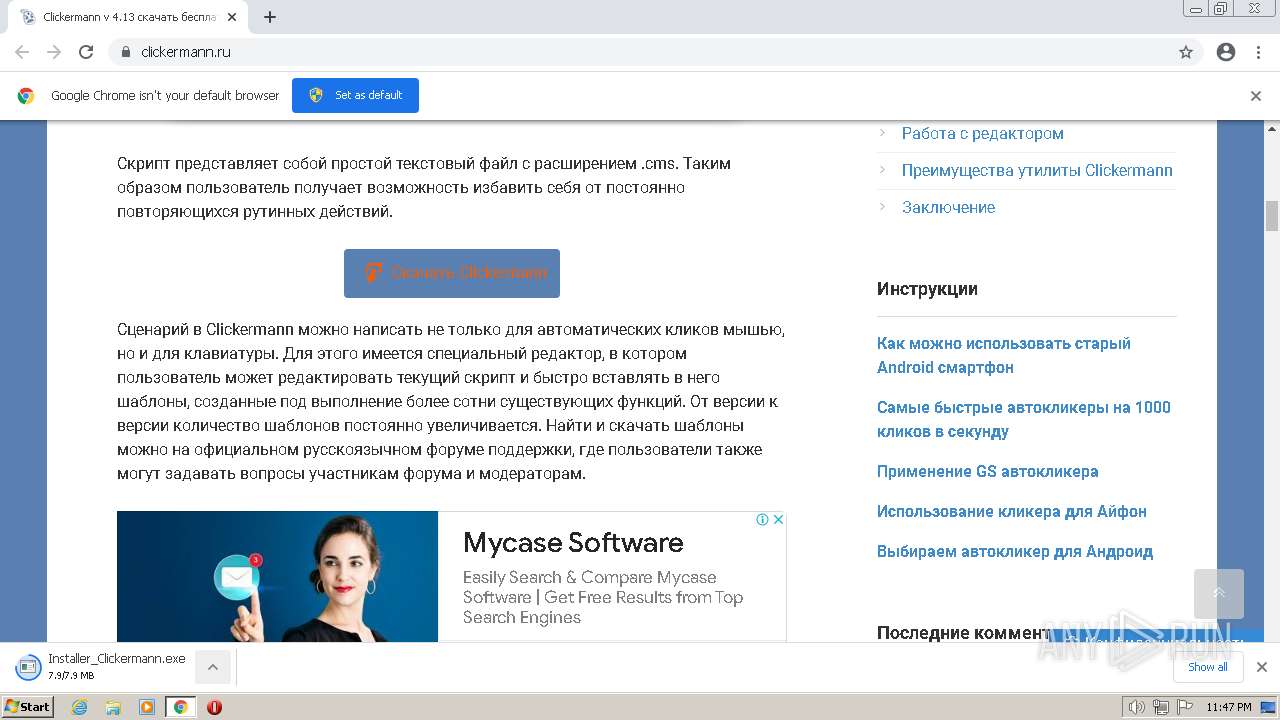
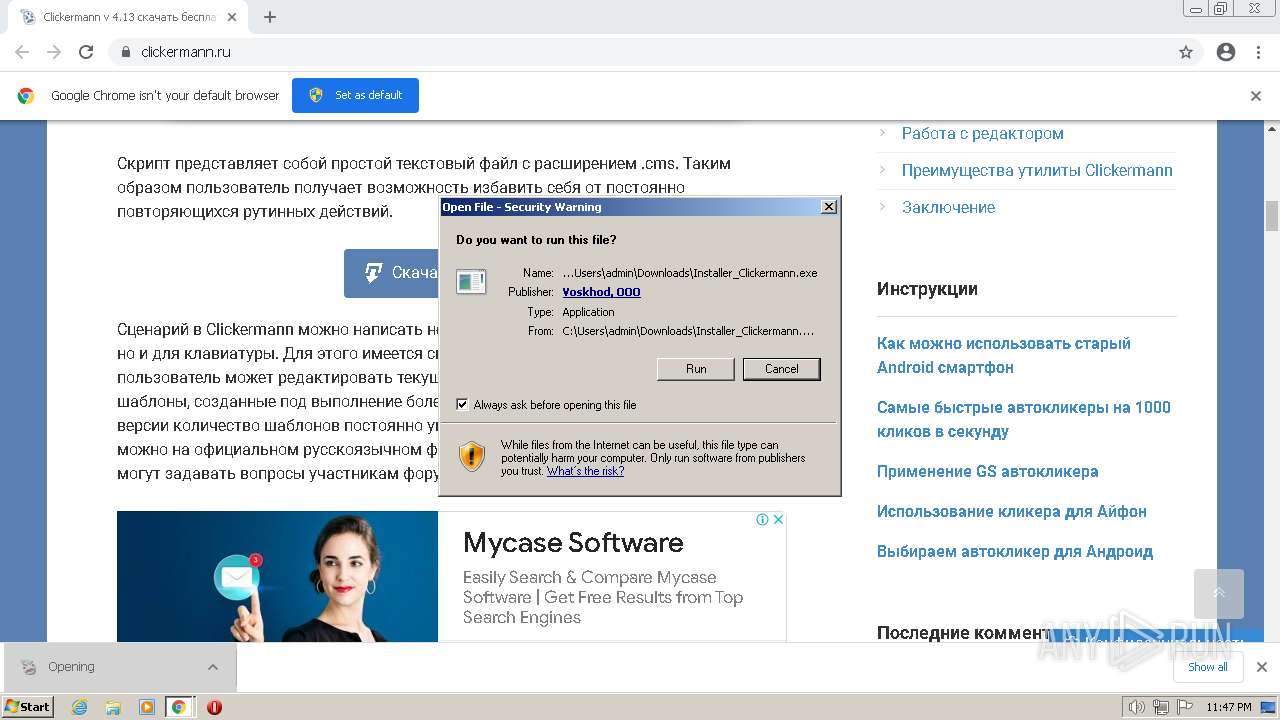
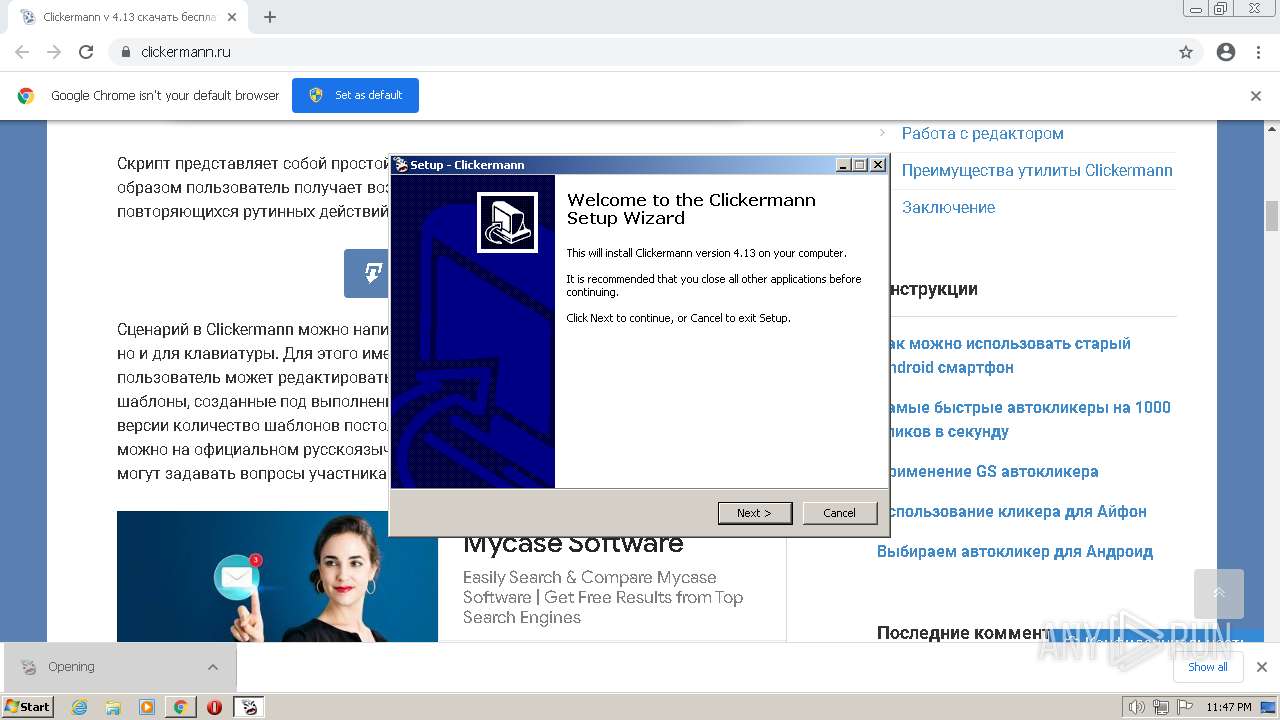
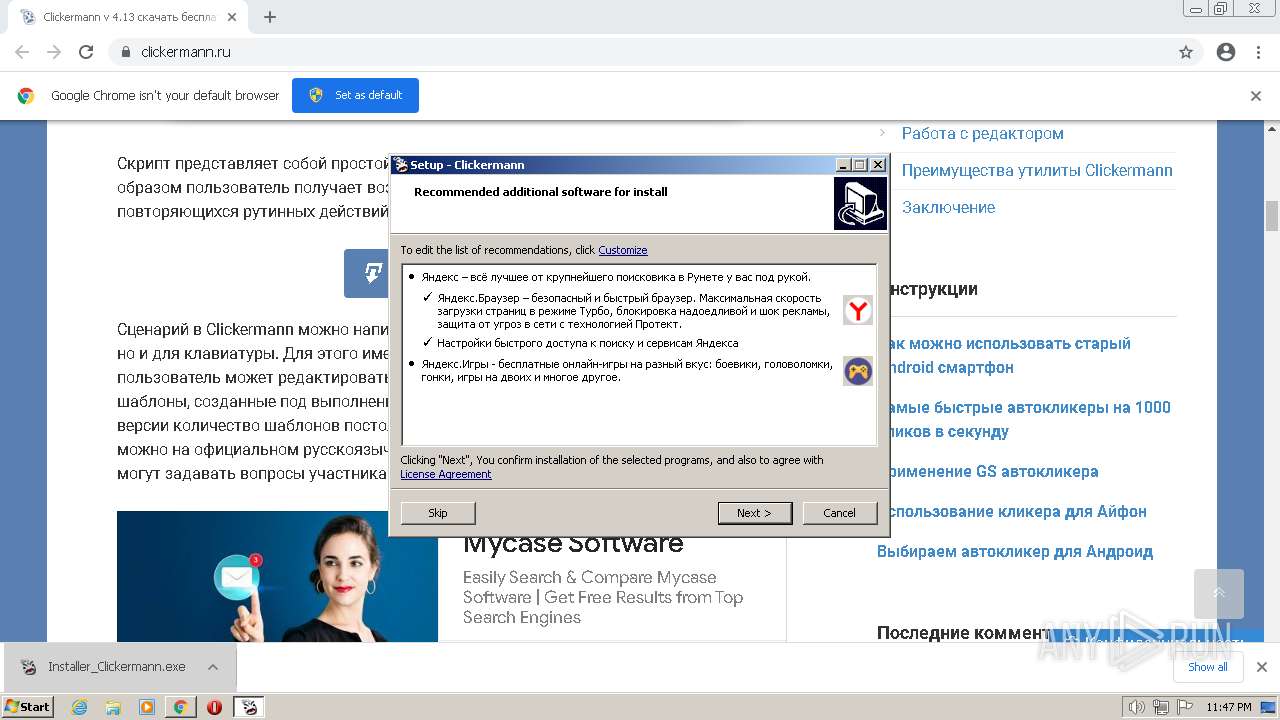
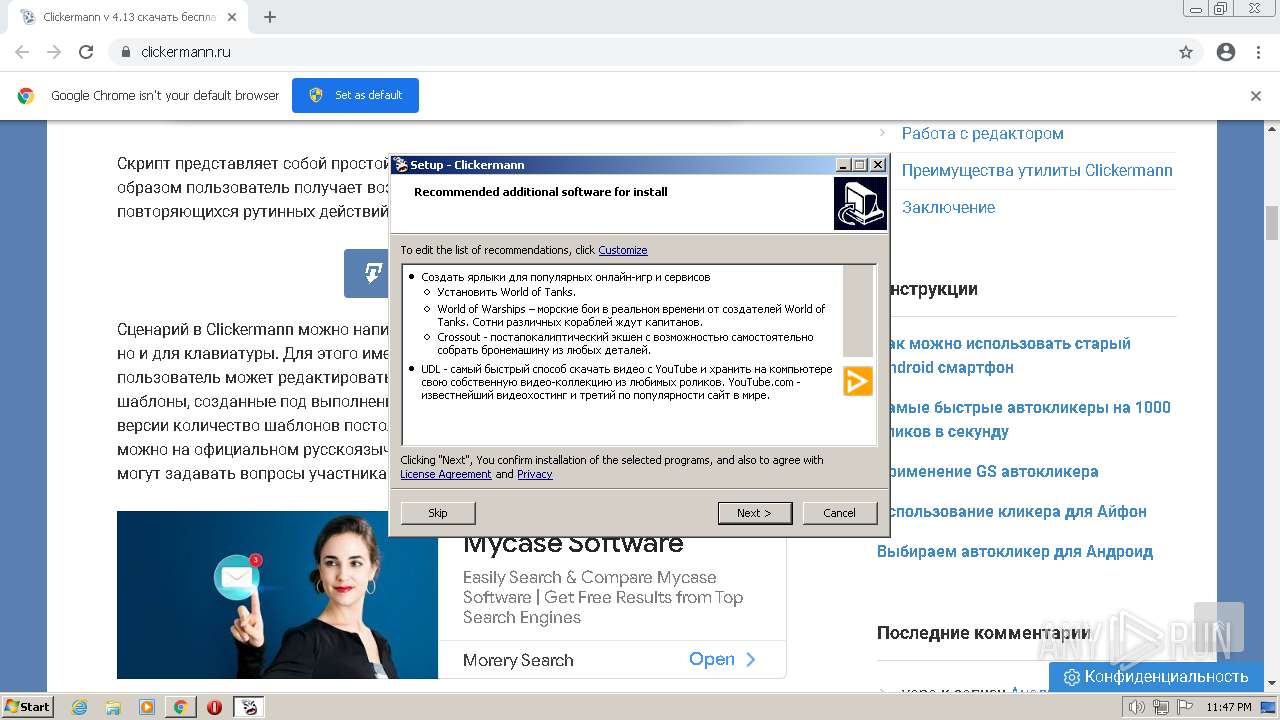
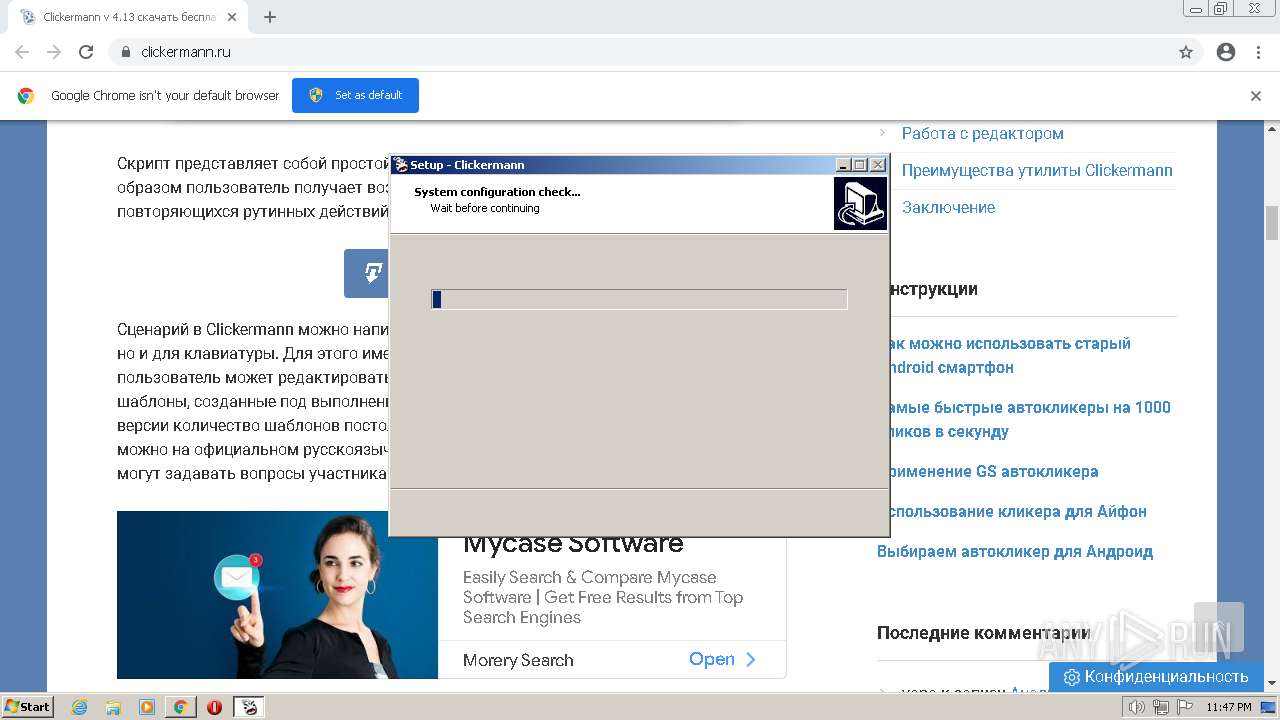
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2022, 23:46:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4CC59EA4F55DA1CAF291ABEE1DBF38C5 |
| SHA1: | 4BDBD94EFC6B47009AA632BBD4A0163169359B12 |
| SHA256: | 6DF0FDB00FCB866629B9F75DECD38B9850DE936D848291A8F56F9B1DC1118E8E |
| SSDEEP: | 3:N8UvIEL/XQK:2UQWXf |
MALICIOUS
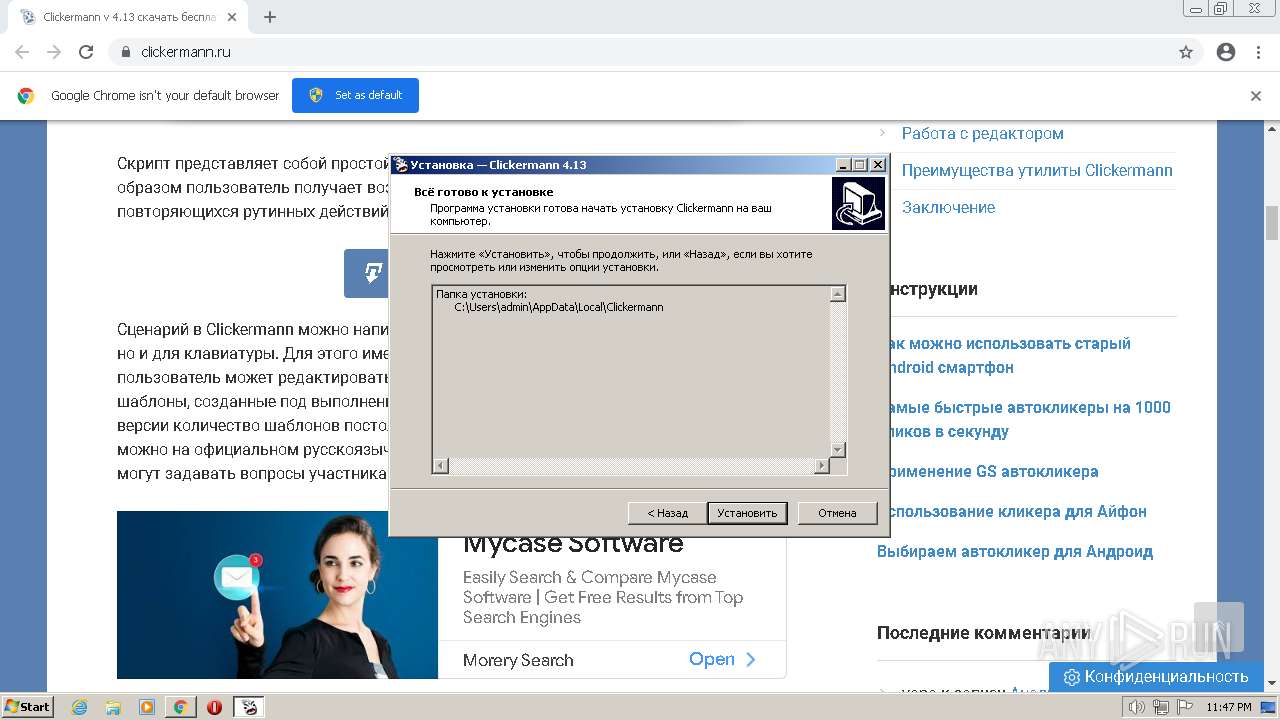
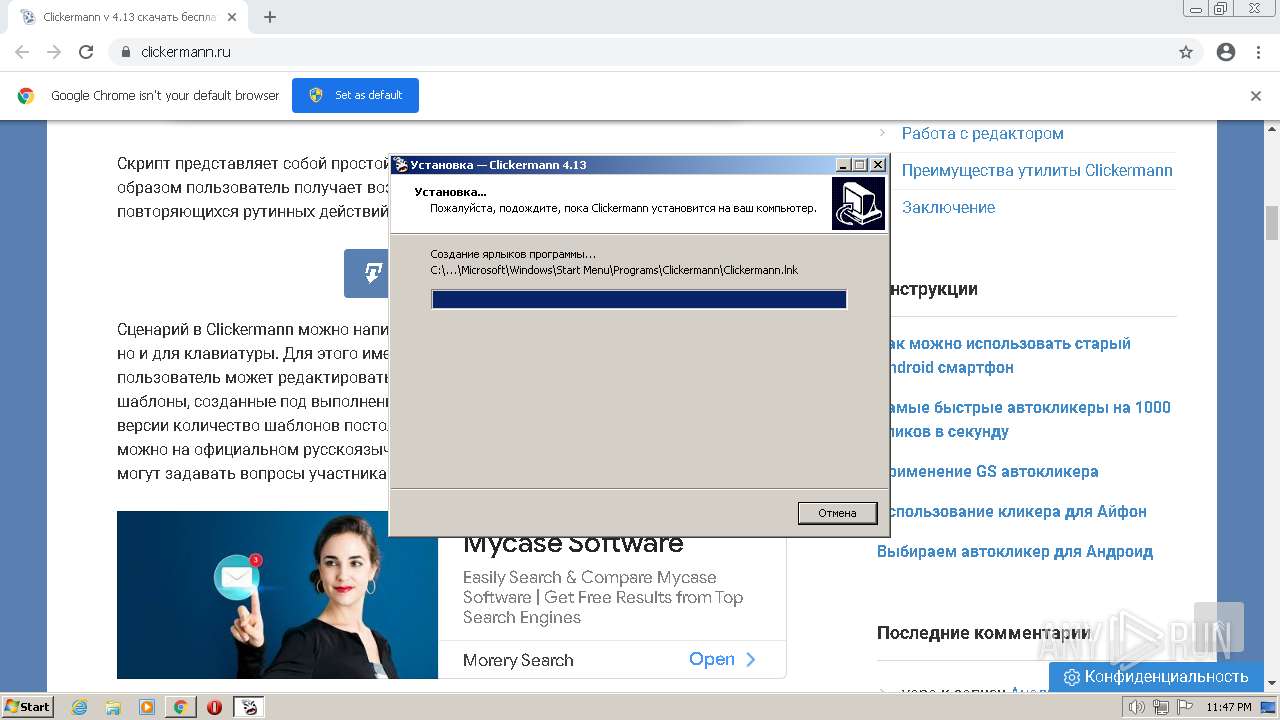
Application was dropped or rewritten from another process
- Installer_Clickermann.exe (PID: 3396)
- Installer_Clickermann.exe (PID: 2496)
- Clickermann.exe (PID: 2784)
- downloader.exe (PID: 2008)
Drops the executable file immediately after the start
- Installer_Clickermann.tmp (PID: 2976)
- Clickermann.tmp (PID: 3240)
SUSPICIOUS
Executable content was dropped or overwritten
- Installer_Clickermann.tmp (PID: 2976)
- Clickermann.tmp (PID: 3240)
INFO
Application was dropped or rewritten from another process
- Installer_Clickermann.tmp (PID: 2976)
- Installer_Clickermann.tmp (PID: 3580)
- Clickermann.tmp (PID: 3240)
Loads dropped or rewritten executable
- Installer_Clickermann.tmp (PID: 2976)
Drops a file that was compiled in debug mode
- Installer_Clickermann.tmp (PID: 2976)
Drops the executable file immediately after the start
- chrome.exe (PID: 2056)
Executable content was dropped or overwritten
- chrome.exe (PID: 2056)
Application launched itself
- chrome.exe (PID: 2056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
27
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1068,9661477012864492885,16410468650033949897,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2688 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1068,9661477012864492885,16410468650033949897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2864 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1068,9661477012864492885,16410468650033949897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4008 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2008 | "C:\Users\admin\AppData\Local\Temp\is-L9T9T.tmp\aGt8VeATSB0o1hW\downloader.exe" --sync --partner 26983 --distr /quiet /msicl "YABROWSER=y YAHOMEPAGE=y YAQSEARCH=y VID=57" | C:\Users\admin\AppData\Local\Temp\is-L9T9T.tmp\aGt8VeATSB0o1hW\downloader.exe | Installer_Clickermann.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Downloader Exit code: 0 Version: 0.1.0.33 Modules
| |||||||||||||||
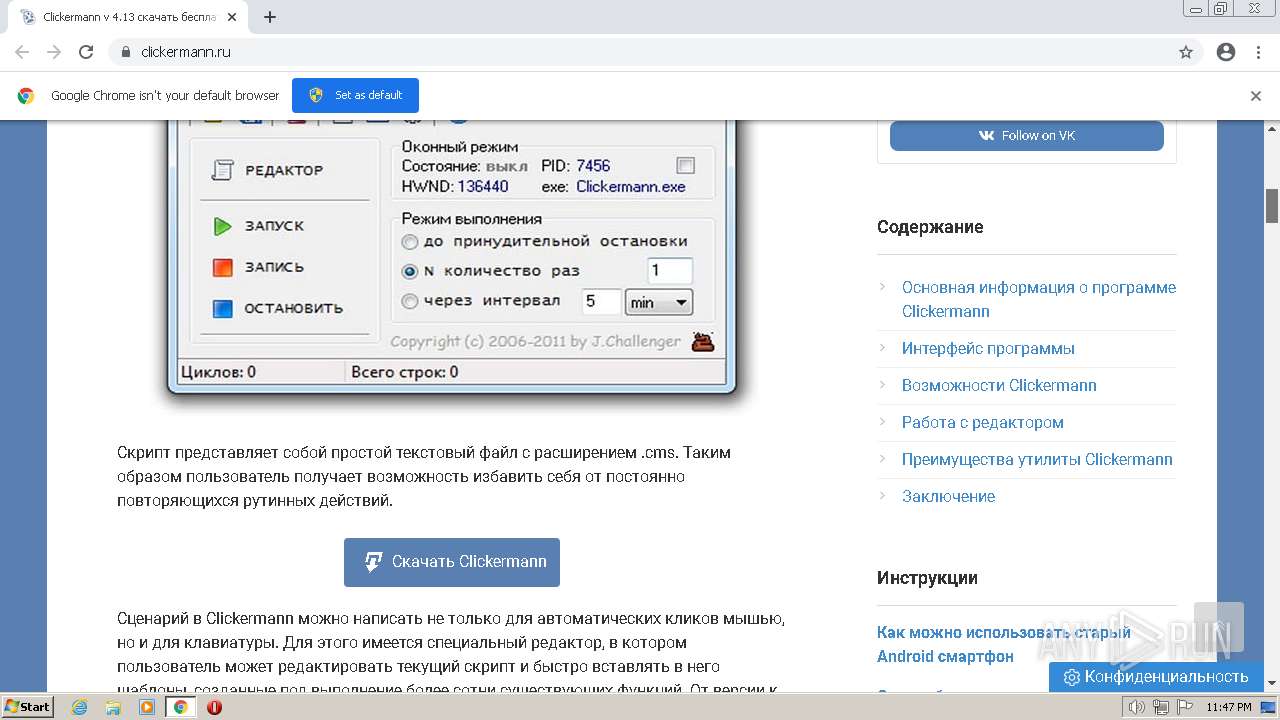
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://clickermann.ru/" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1068,9661477012864492885,16410468650033949897,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1264 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e95d988,0x6e95d998,0x6e95d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
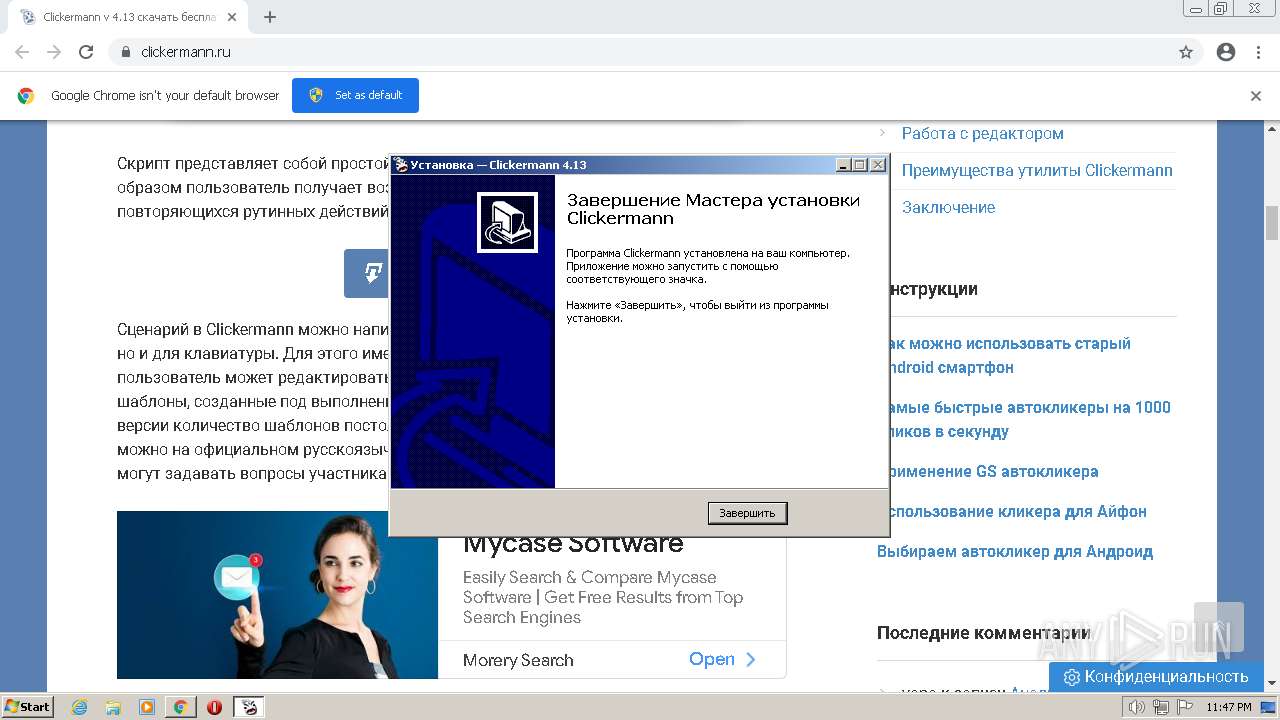
| 2496 | "C:\Users\admin\Downloads\Installer_Clickermann.exe" /SPAWNWND=$40194 /NOTIFYWND=$4015A | C:\Users\admin\Downloads\Installer_Clickermann.exe | Installer_Clickermann.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Clickermann Setup (r2210131054) Exit code: 0 Version: 4.13 Modules
| |||||||||||||||
| 2536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,9661477012864492885,16410468650033949897,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2784 | "C:\Users\admin\AppData\Local\Temp\is-L9T9T.tmp\x3iIPA\Clickermann.exe" | C:\Users\admin\AppData\Local\Temp\is-L9T9T.tmp\x3iIPA\Clickermann.exe | — | Installer_Clickermann.tmp | |||||||||||
User: admin Company: Integrity Level: HIGH Description: Clickermann Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
23 186
Read events
22 992
Write events
187
Delete events
7
Modification events
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
20
Suspicious files
30
Text files
229
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-638E82E3-808.pma | — | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0518b9c4-7725-416f-9d58-a67017982b6e.tmp | text | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF106f87e.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF106f85f.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2056 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\26389ee4-3f7d-4f6b-81ae-b92a4551676f.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
190
DNS requests
81
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
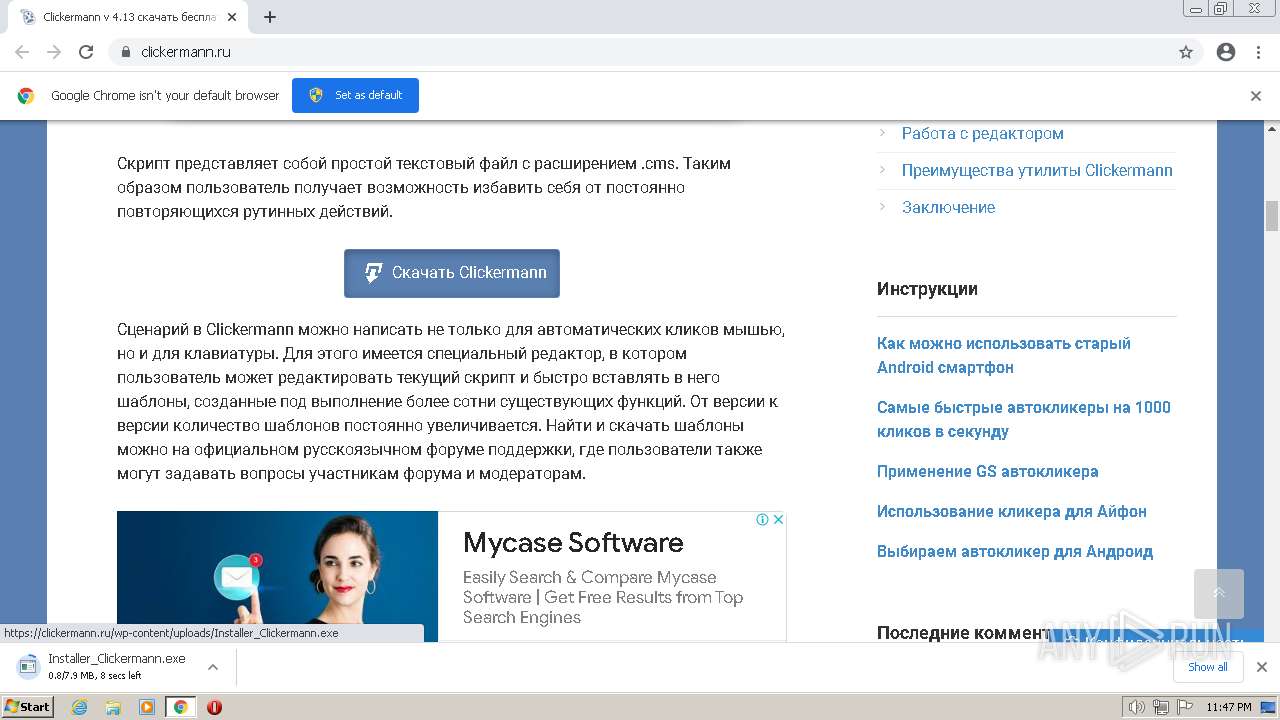
2008 | downloader.exe | GET | 302 | 5.45.205.242:80 | http://download.yandex.ru/yandex-pack/downloader/info.rss | RU | — | — | whitelisted |
2008 | downloader.exe | GET | 302 | 5.45.205.242:80 | http://downloader.yandex.net/yandex-pack/26983/YandexPackSetup.exe | RU | — | — | whitelisted |
2008 | downloader.exe | GET | — | 185.70.202.15:80 | http://ext-cachev2-itt03.cdn.yandex.net/downloader.yandex.net/yandex-pack/26983/YandexPackSetup.exe?lid=1529 | IT | — | — | whitelisted |
2008 | downloader.exe | GET | 200 | 149.5.241.43:80 | http://ext-cachev2-cogent03.cdn.yandex.net/download.yandex.ru/yandex-pack/downloader/info.rss?lid=1503 | US | xml | 267 b | whitelisted |
2140 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c103ef856097fbf4 | US | compressed | 61.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2140 | chrome.exe | 142.250.186.78:443 | clients2.google.com | GOOGLE | US | whitelisted |
2140 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2140 | chrome.exe | 95.216.65.102:443 | rotarb.bid | Hetzner Online GmbH | FI | suspicious |
2140 | chrome.exe | 87.240.129.133:443 | vk.com | VKontakte Ltd | RU | malicious |
2140 | chrome.exe | 142.250.185.194:443 | pagead2.googlesyndication.com | GOOGLE | US | suspicious |
— | — | 87.240.190.70:443 | api.vk.com | VKontakte Ltd | RU | unknown |
2140 | chrome.exe | 65.9.66.56:443 | quantcast.mgr.consensu.org | AMAZON-02 | US | suspicious |
2140 | chrome.exe | 142.250.186.162:443 | googleads.g.doubleclick.net | GOOGLE | US | whitelisted |
2140 | chrome.exe | 93.158.134.90:443 | an.yandex.ru | YANDEX LLC | RU | whitelisted |
2140 | chrome.exe | 93.158.134.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
clickermann.ru |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
rotarb.bid |
| whitelisted |
s.w.org |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2008 | downloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |