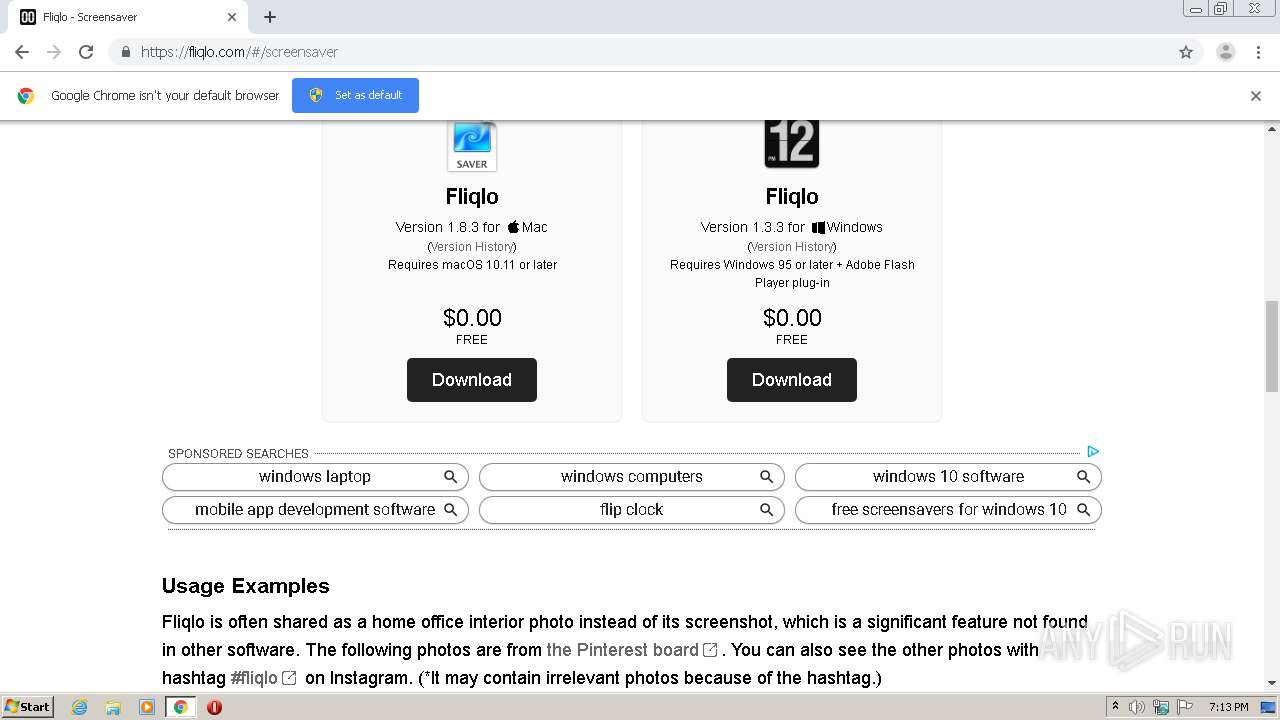
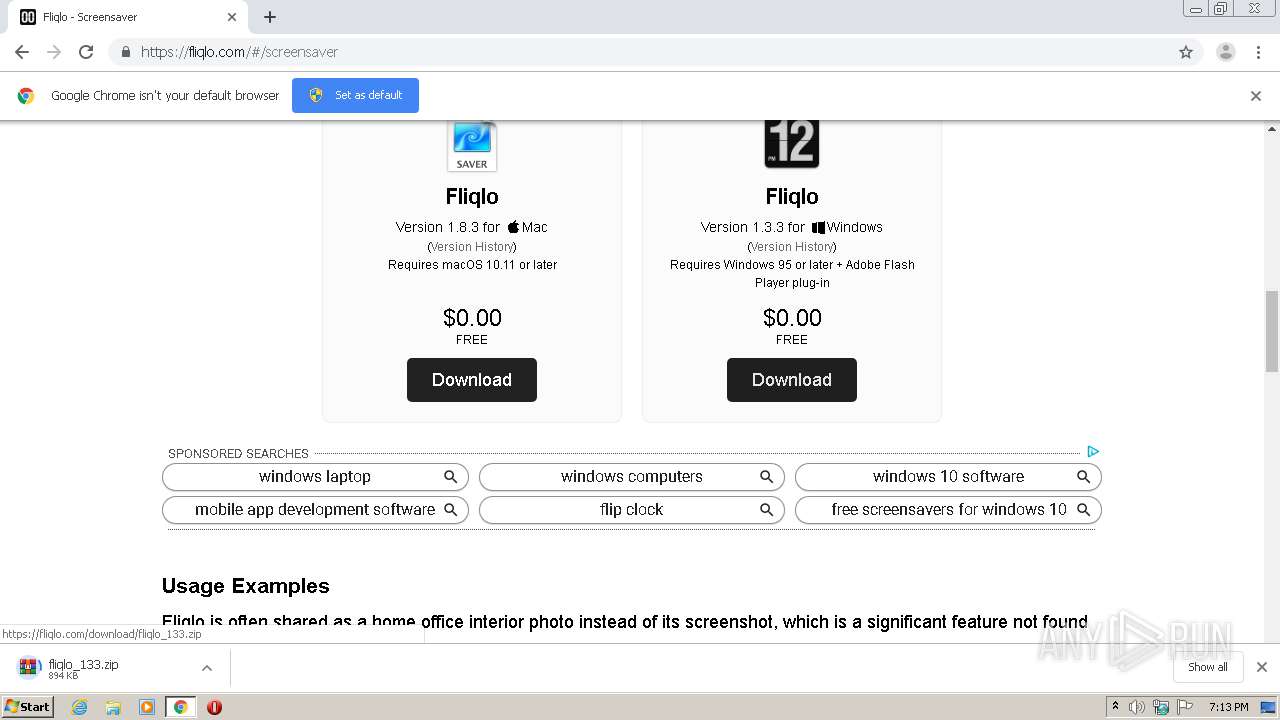
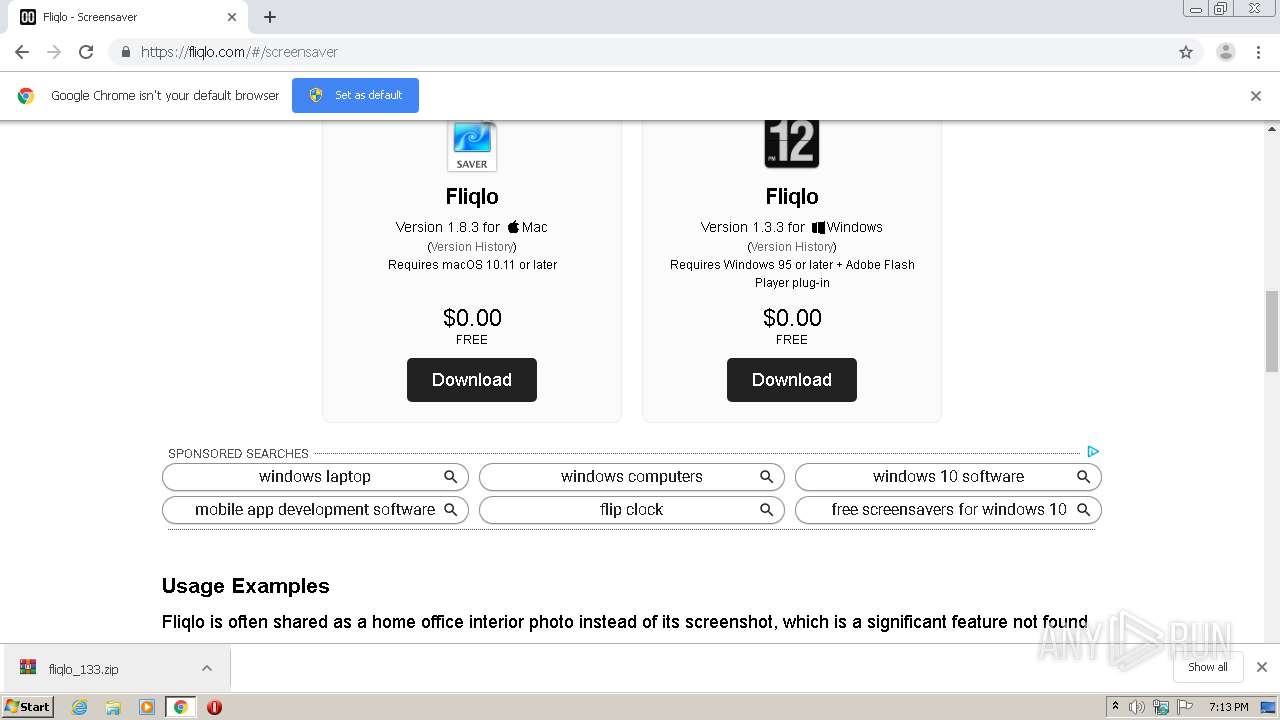
| URL: | https://fliqlo.com |
| Full analysis: | https://app.any.run/tasks/25bef759-b197-43b8-aa79-8d2ea11a97ea |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2020, 18:13:06 |
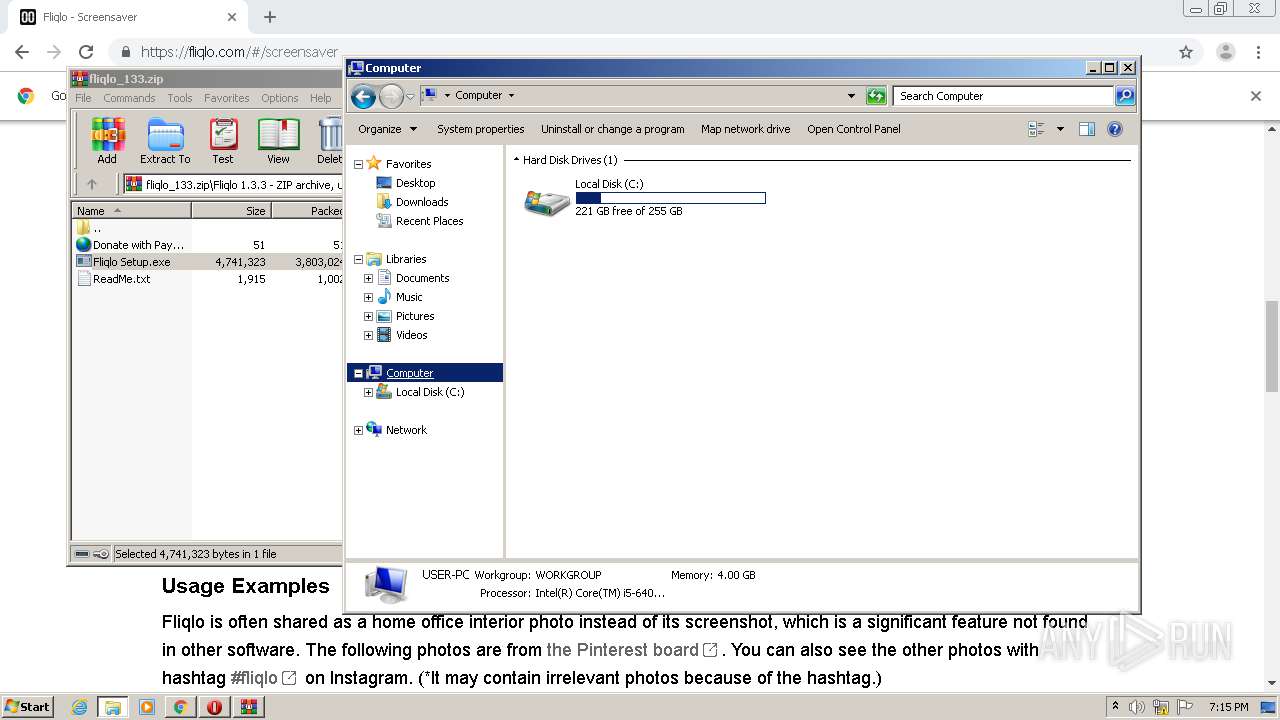
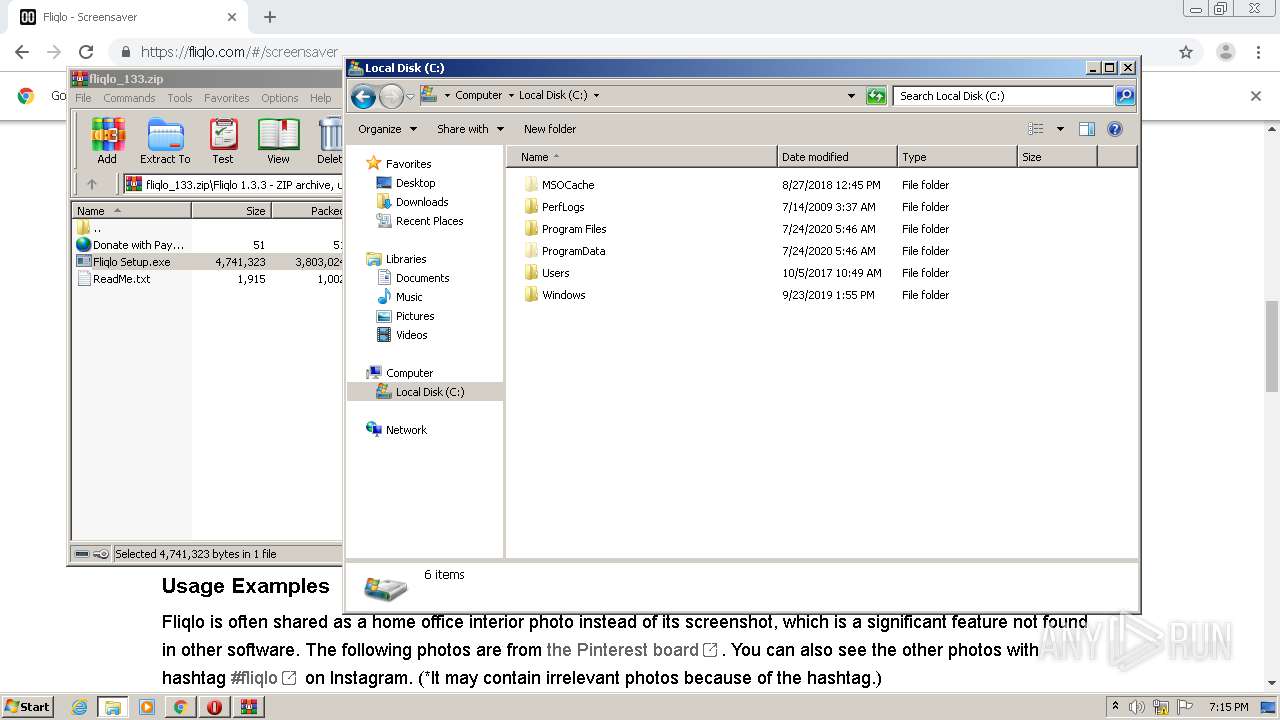
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8C8D23DA84B7D5F1578B1765CC378DD9 |
| SHA1: | 2149F8D1599DEC3E35D0660C4653DBFCEA66B206 |
| SHA256: | 6DDA393A04DBABEC1906A8058070D4CDD94618A71DDB5942FBFB1B5DABF5B882 |
| SSDEEP: | 3:N8IUJQK:2pd |
MALICIOUS
Application was dropped or rewritten from another process
- Fliqlo Setup.exe (PID: 1700)
- Fliqlo Setup.exe (PID: 3256)
- Fliqlo Setup.exe (PID: 2192)
- Fliqlo Setup.exe (PID: 3092)
- Fliqlo Setup.exe (PID: 2360)
- Fliqlo.scr (PID: 608)
- Fliqlo.scr (PID: 560)
- Fliqlo.scr (PID: 2704)
- Fliqlo.scr (PID: 3272)
Loads dropped or rewritten executable
- Fliqlo Setup.exe (PID: 3256)
- Fliqlo Setup.exe (PID: 2360)
SUSPICIOUS
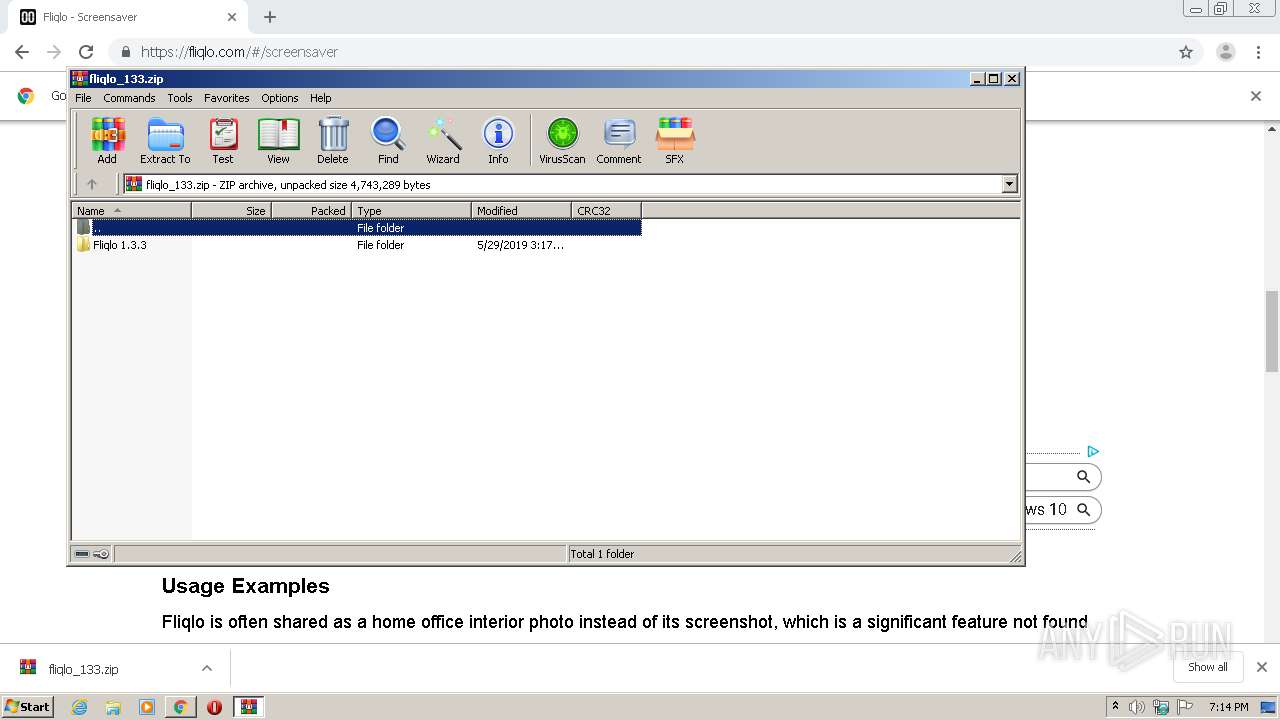
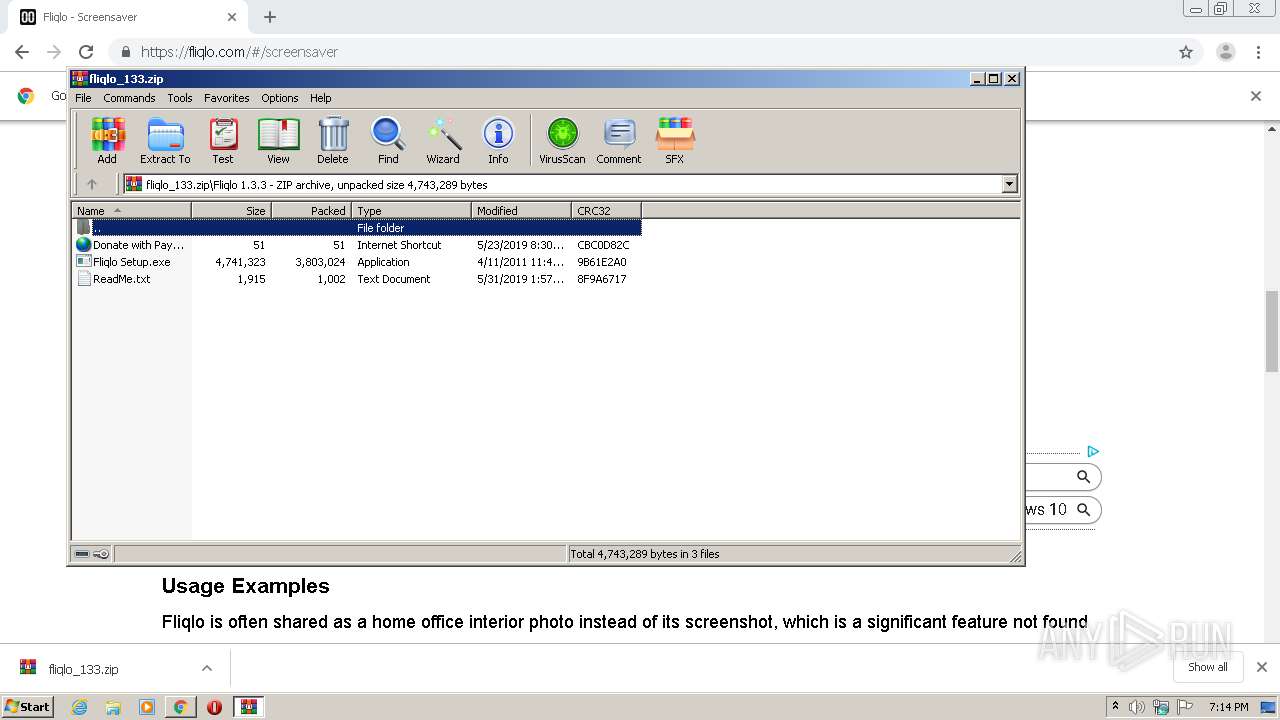
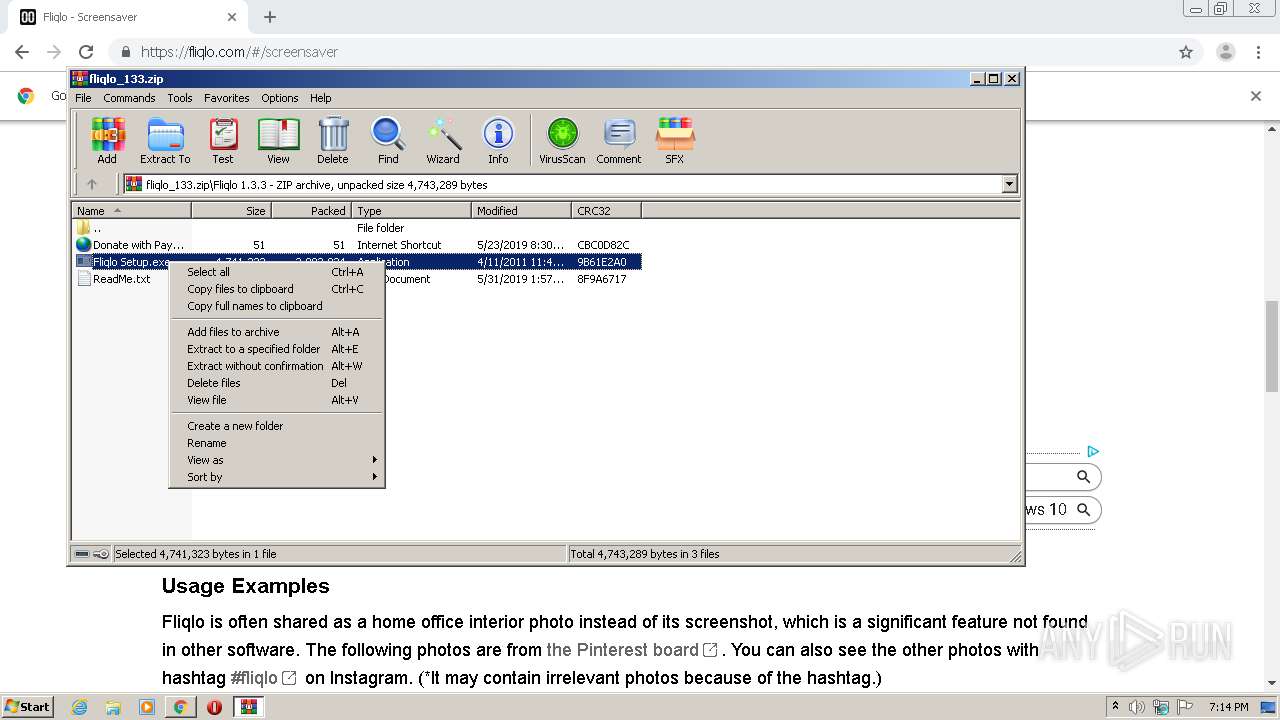
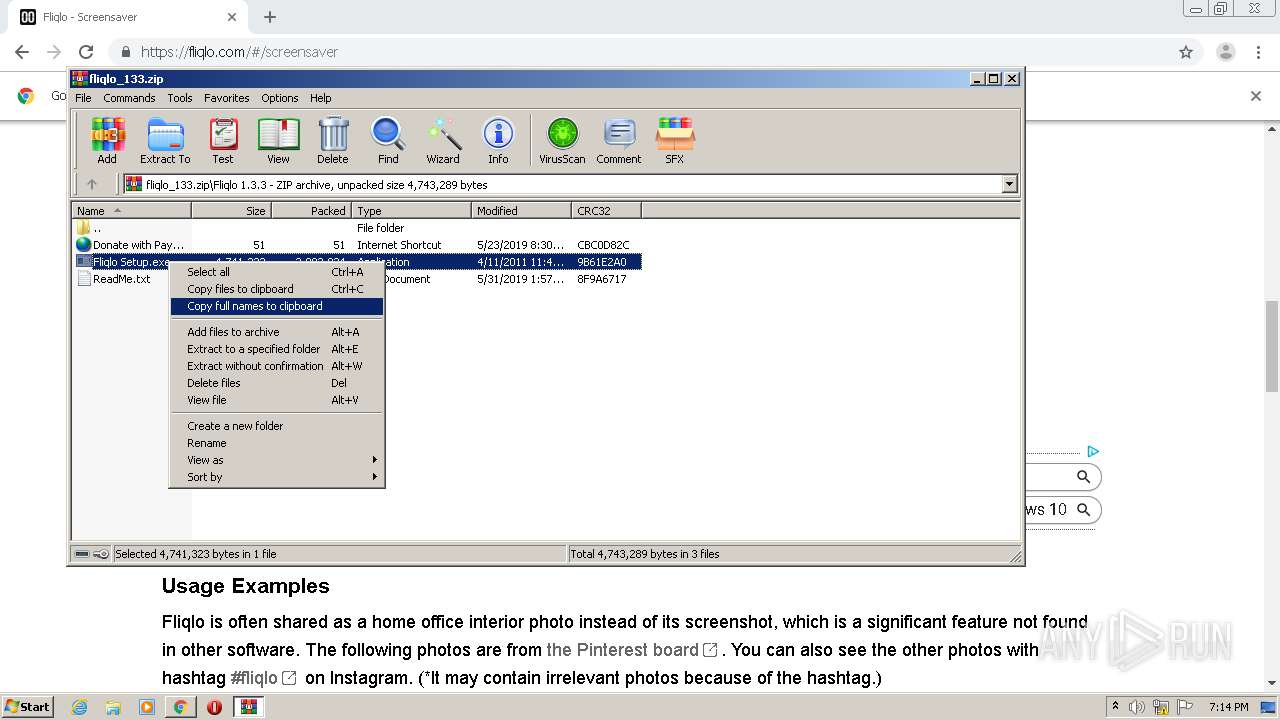
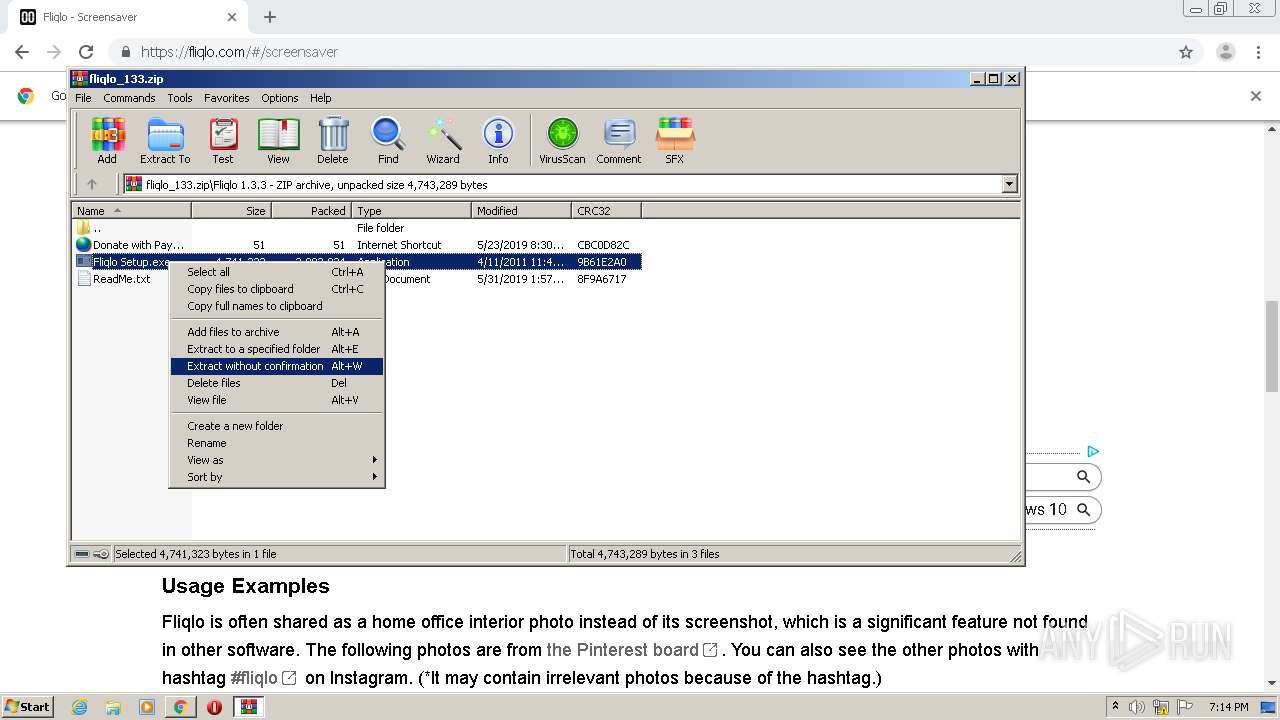
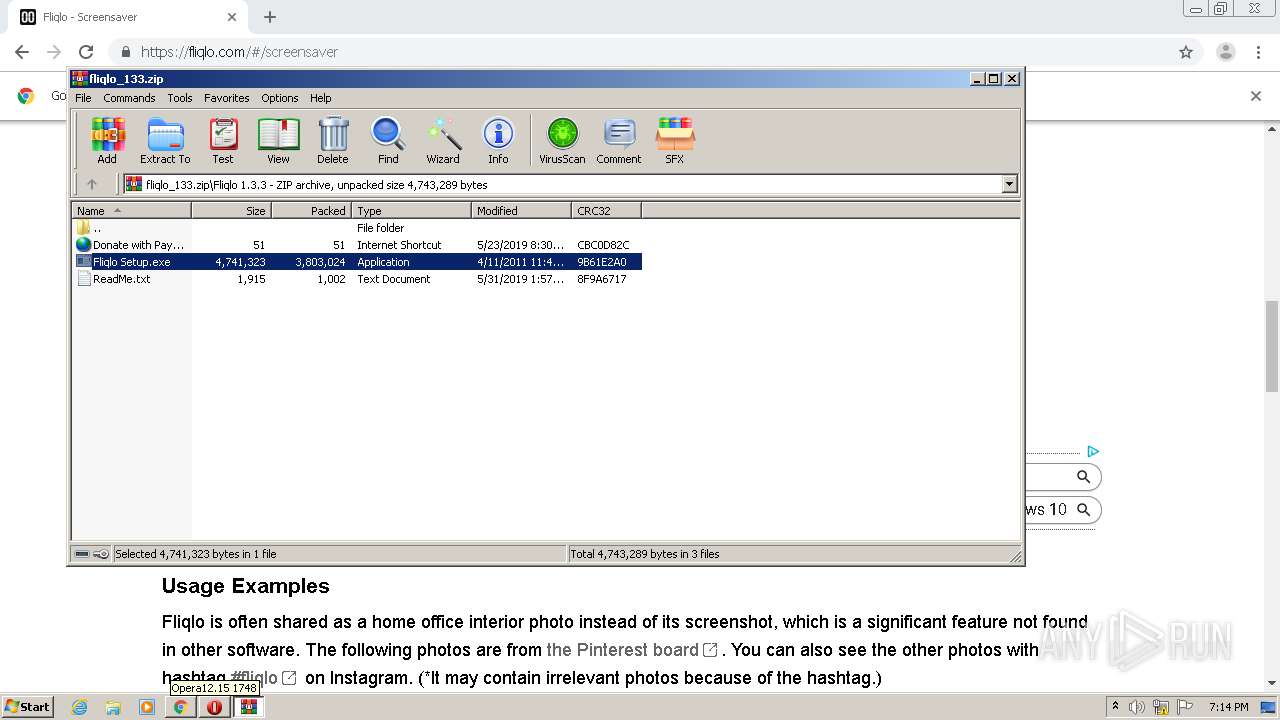
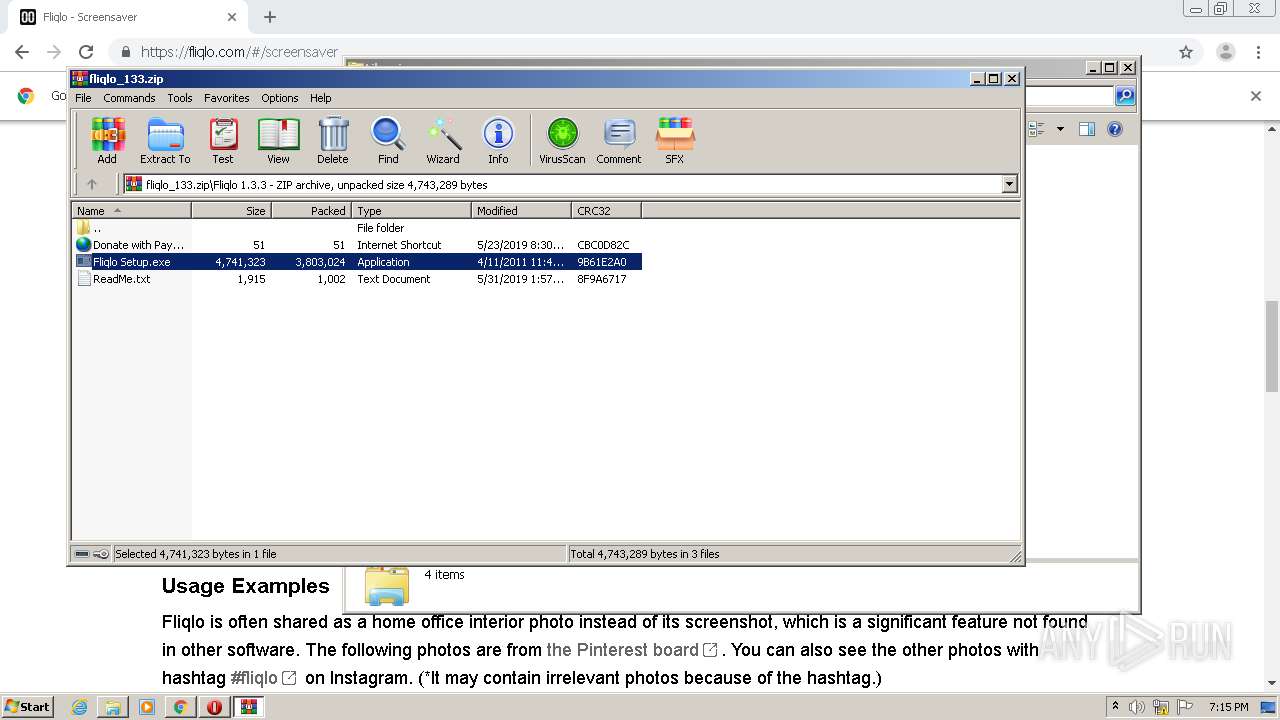
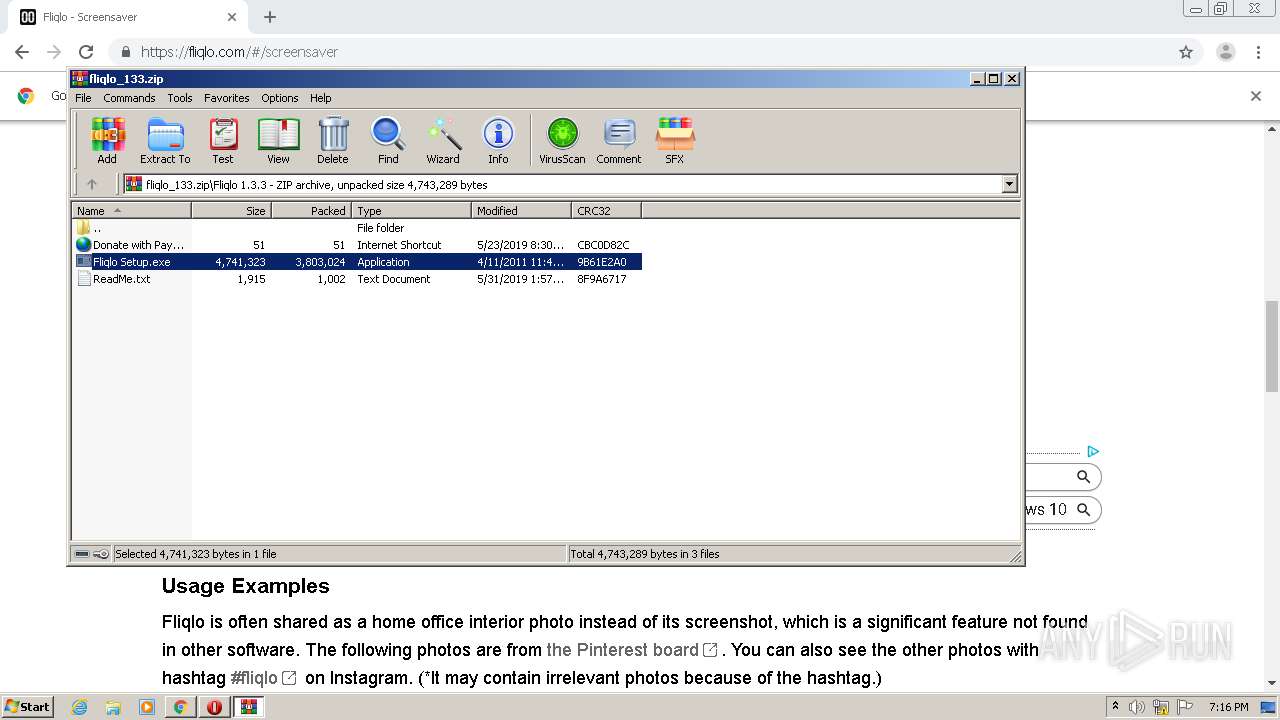
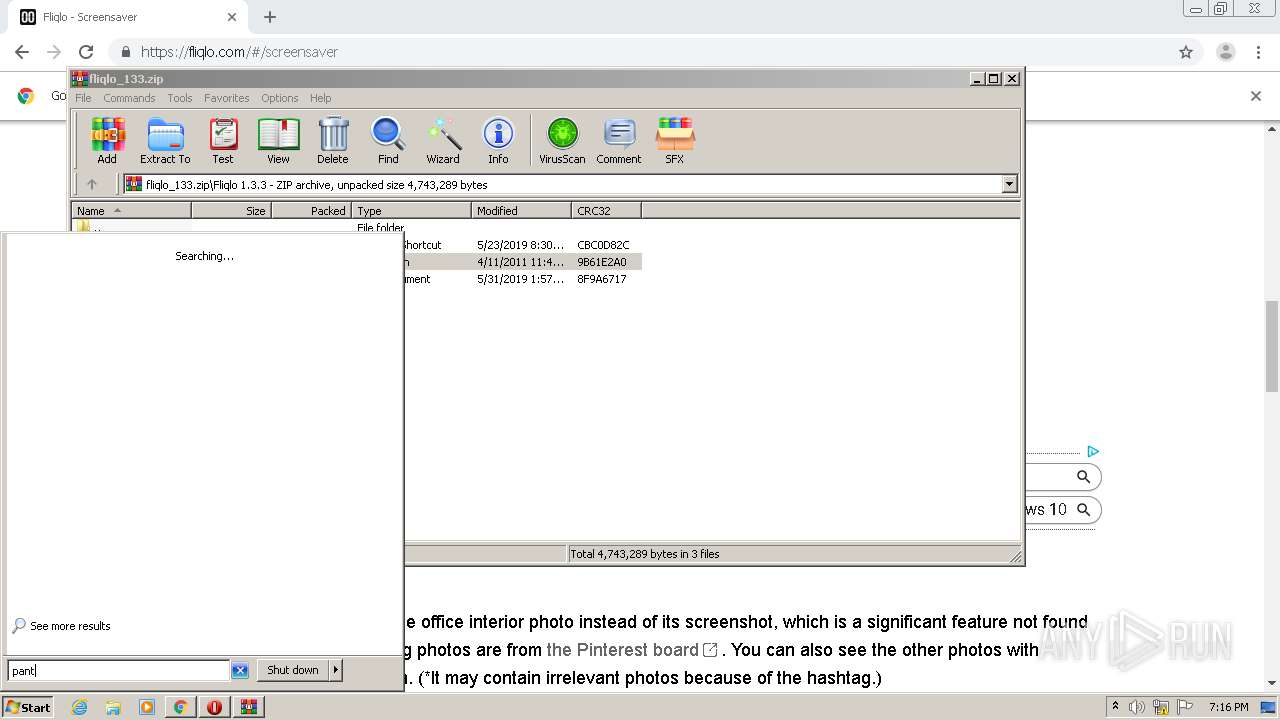
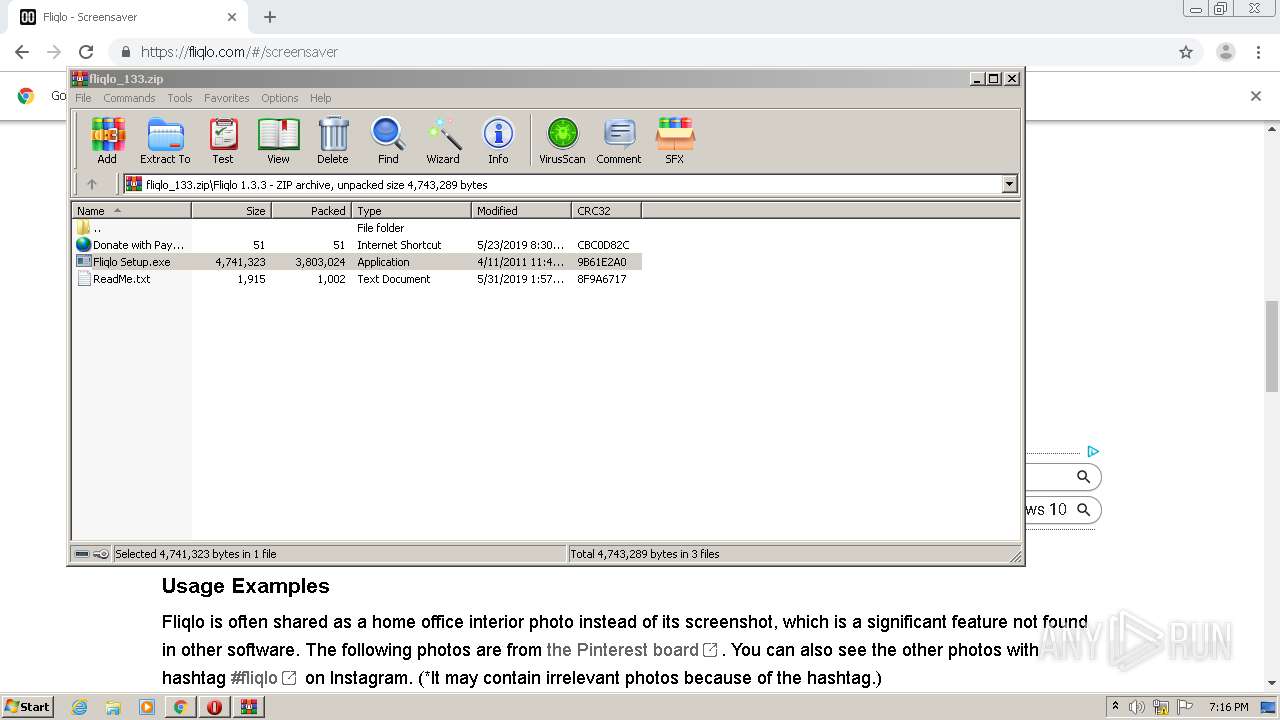
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3056)
- Fliqlo Setup.exe (PID: 3256)
- Fliqlo Setup.exe (PID: 3092)
- Fliqlo Setup.exe (PID: 2360)
- Fliqlo Setup.exe (PID: 2192)
Creates files in the program directory
- Fliqlo Setup.exe (PID: 3256)
- Fliqlo.scr (PID: 608)
- Fliqlo Setup.exe (PID: 2360)
- Fliqlo.scr (PID: 2704)
- Fliqlo.scr (PID: 560)
Creates files in the Windows directory
- Fliqlo Setup.exe (PID: 3256)
- Fliqlo Setup.exe (PID: 2360)
Creates a software uninstall entry
- Fliqlo Setup.exe (PID: 3256)
- Fliqlo Setup.exe (PID: 2360)
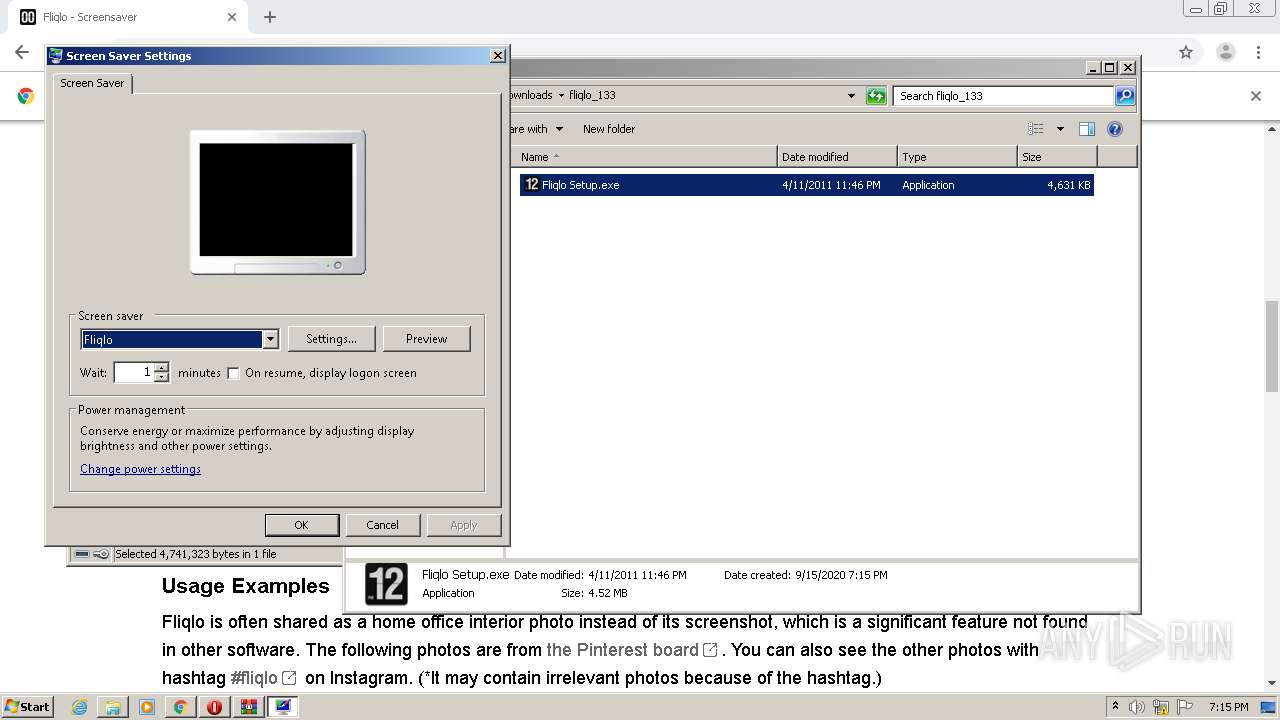
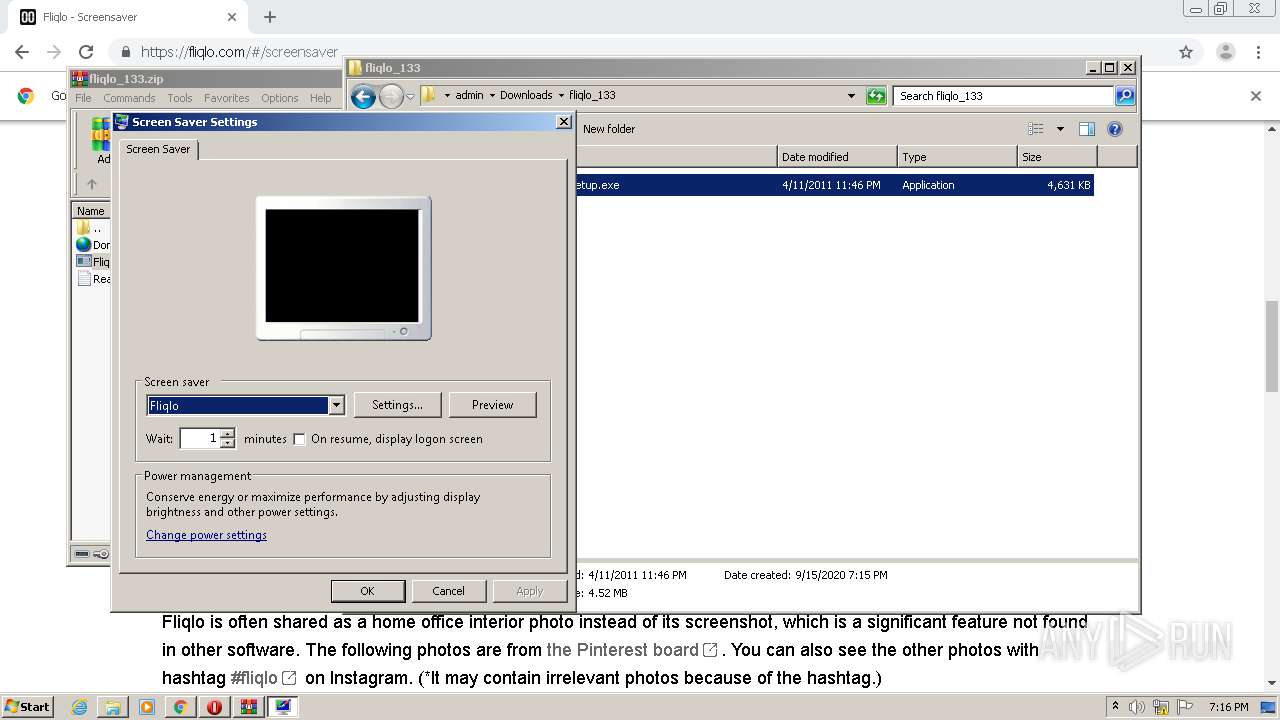
Starts application with an unusual extension
- rundll32.exe (PID: 1932)
- rundll32.exe (PID: 1820)
Creates files in the user directory
- Fliqlo.scr (PID: 608)
Uses RUNDLL32.EXE to load library
- Fliqlo Setup.exe (PID: 2192)
- Fliqlo Setup.exe (PID: 3092)
Reads Internet Cache Settings
- Fliqlo.scr (PID: 608)
- Fliqlo.scr (PID: 560)
Removes files from Windows directory
- Fliqlo Setup.exe (PID: 2360)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1144)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3012)
Application launched itself
- chrome.exe (PID: 1144)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 2376)
Reads the hosts file
- chrome.exe (PID: 1144)
- chrome.exe (PID: 3012)
Reads Internet Cache Settings
- chrome.exe (PID: 1144)
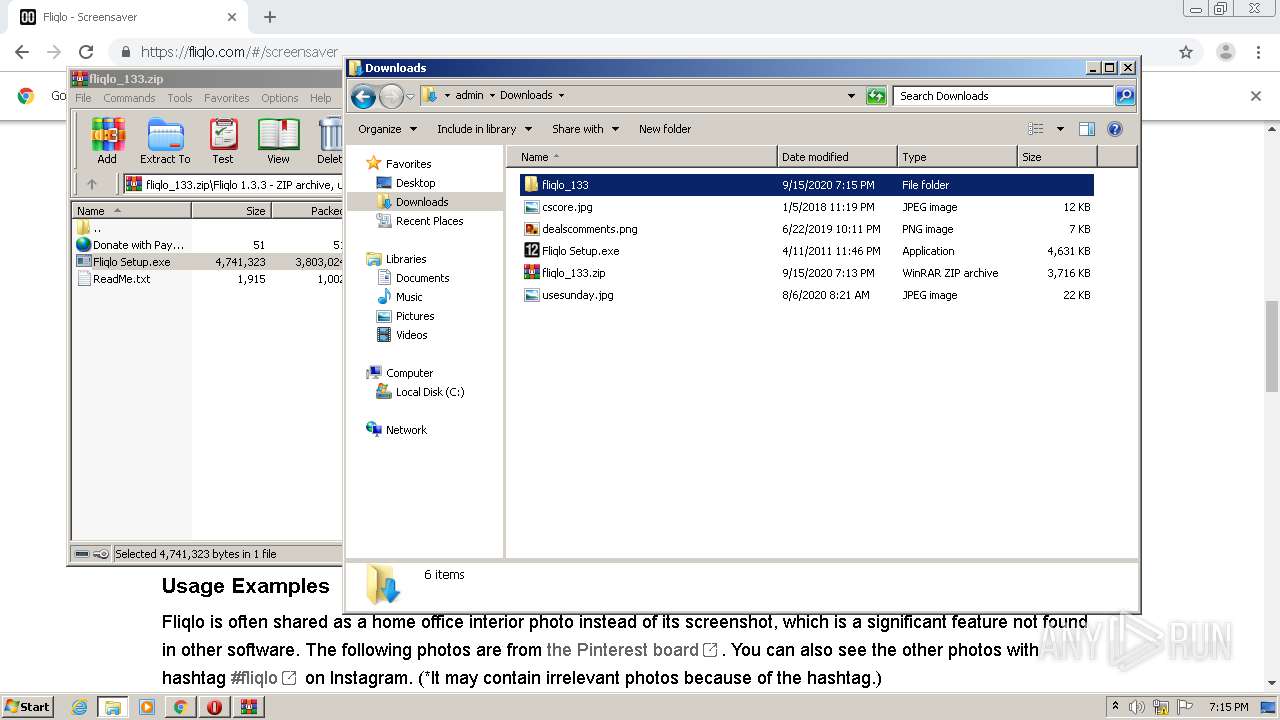
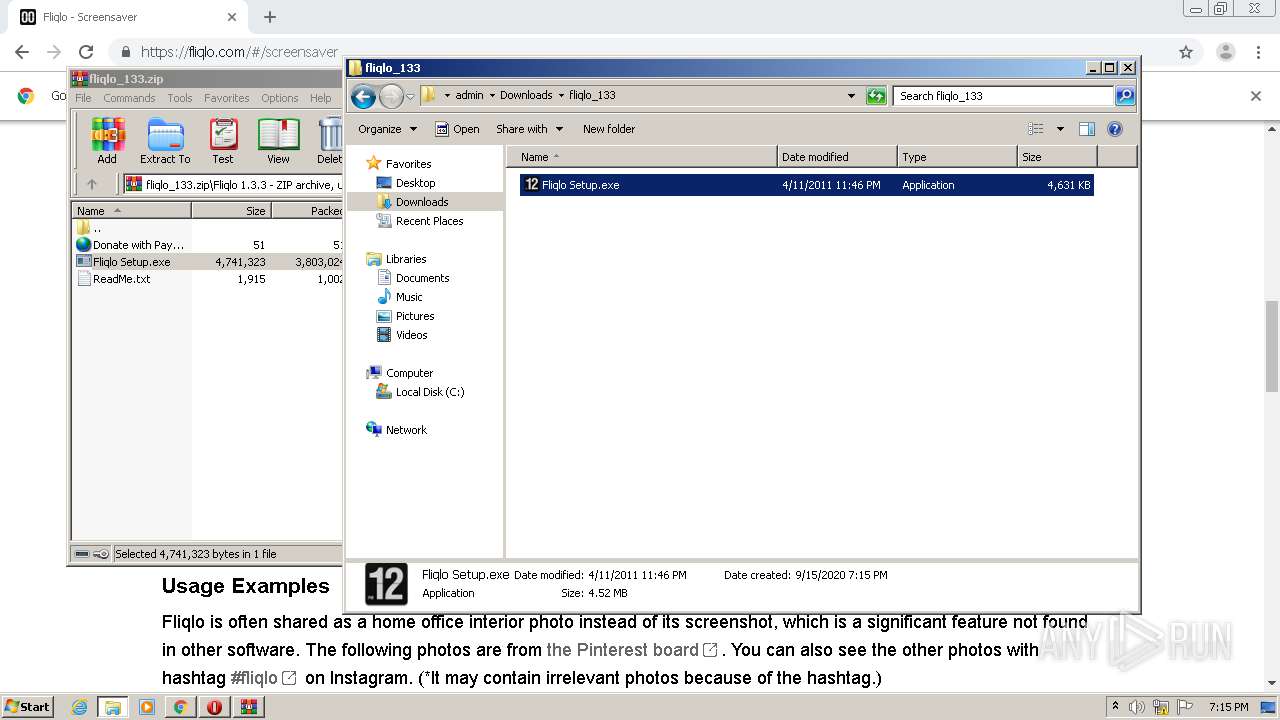
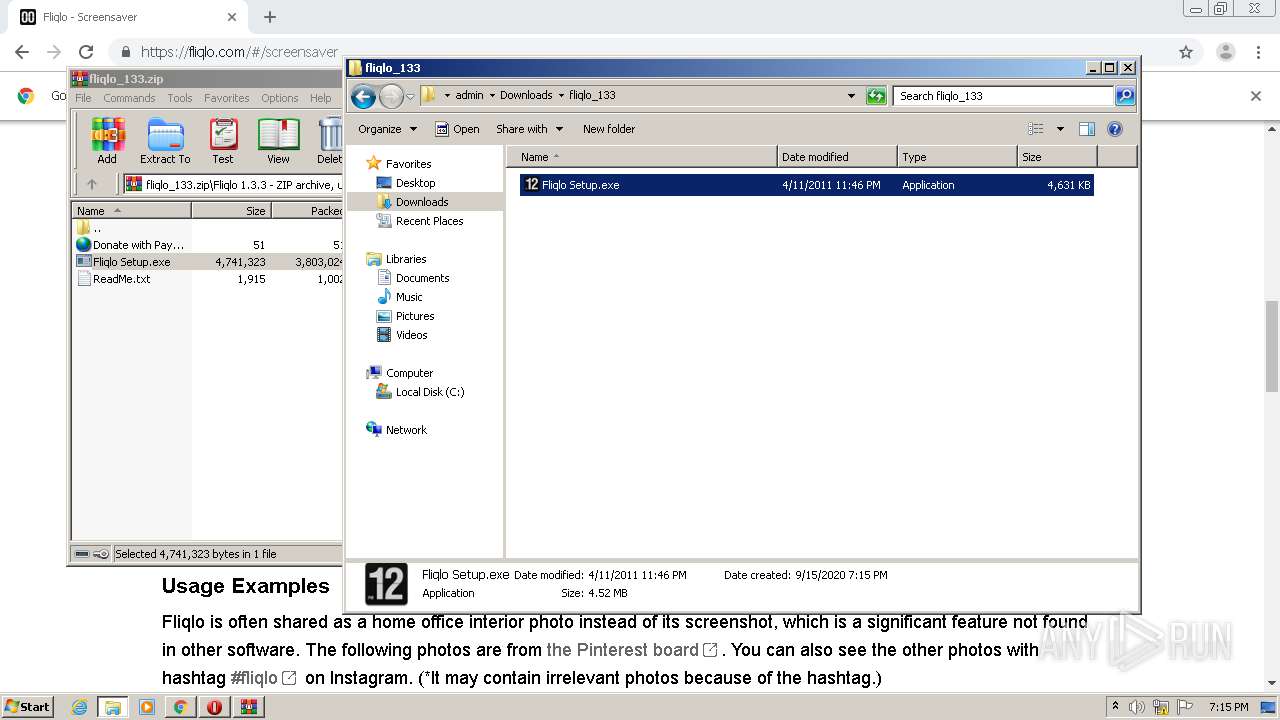
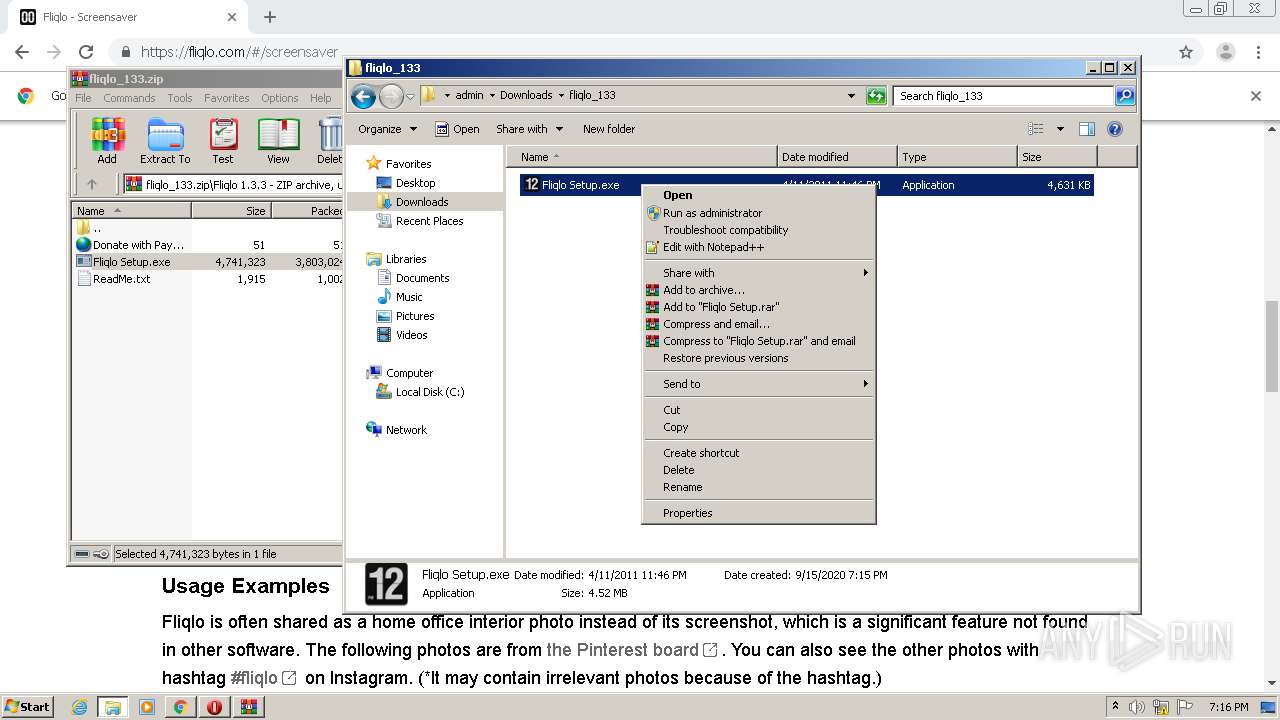
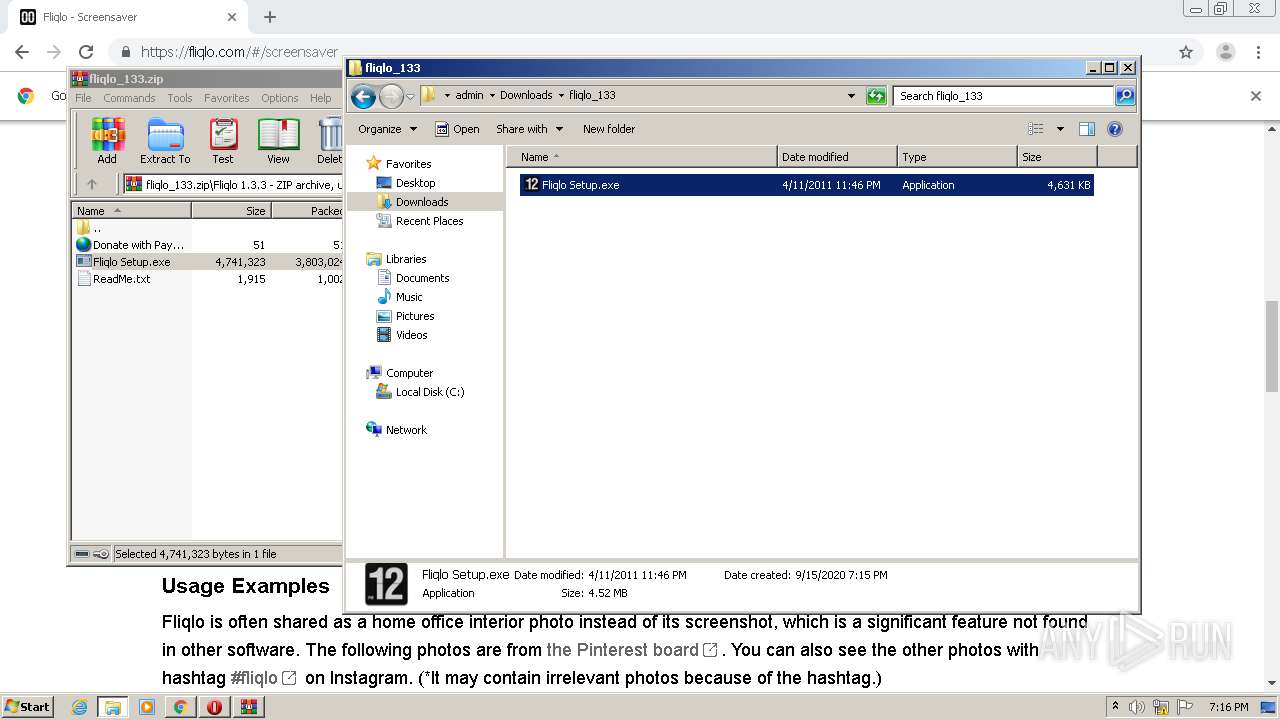
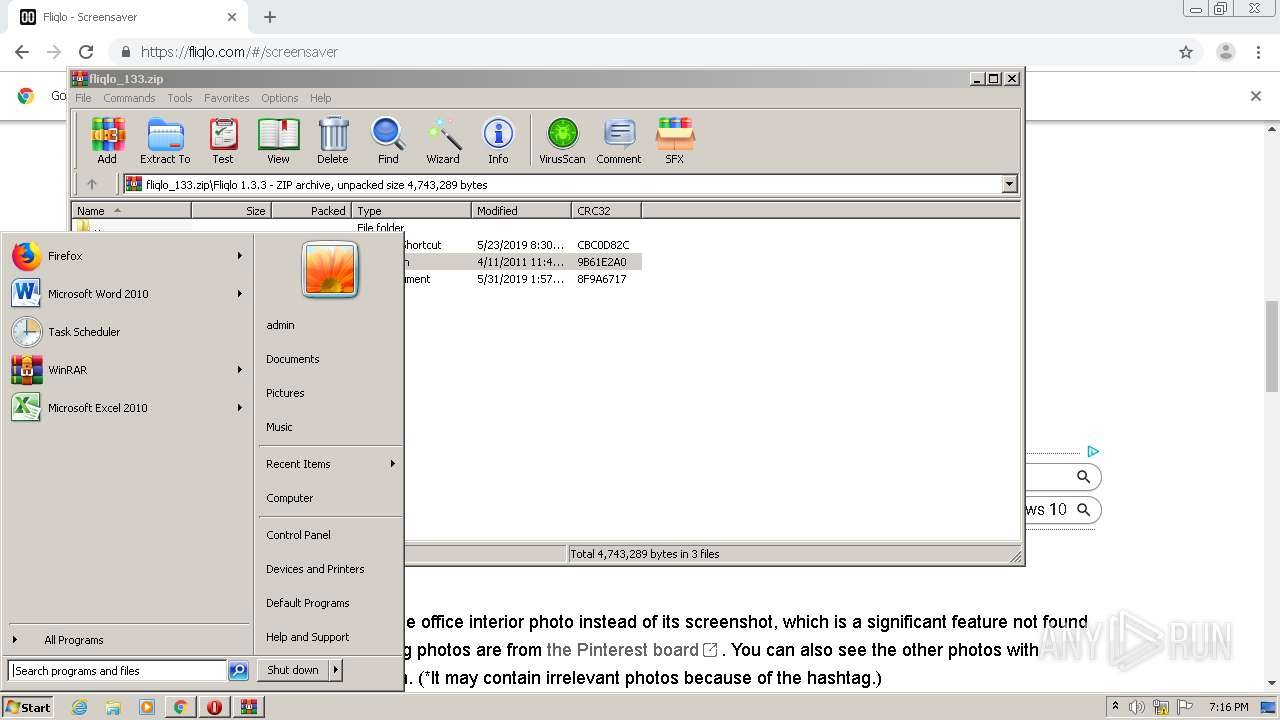
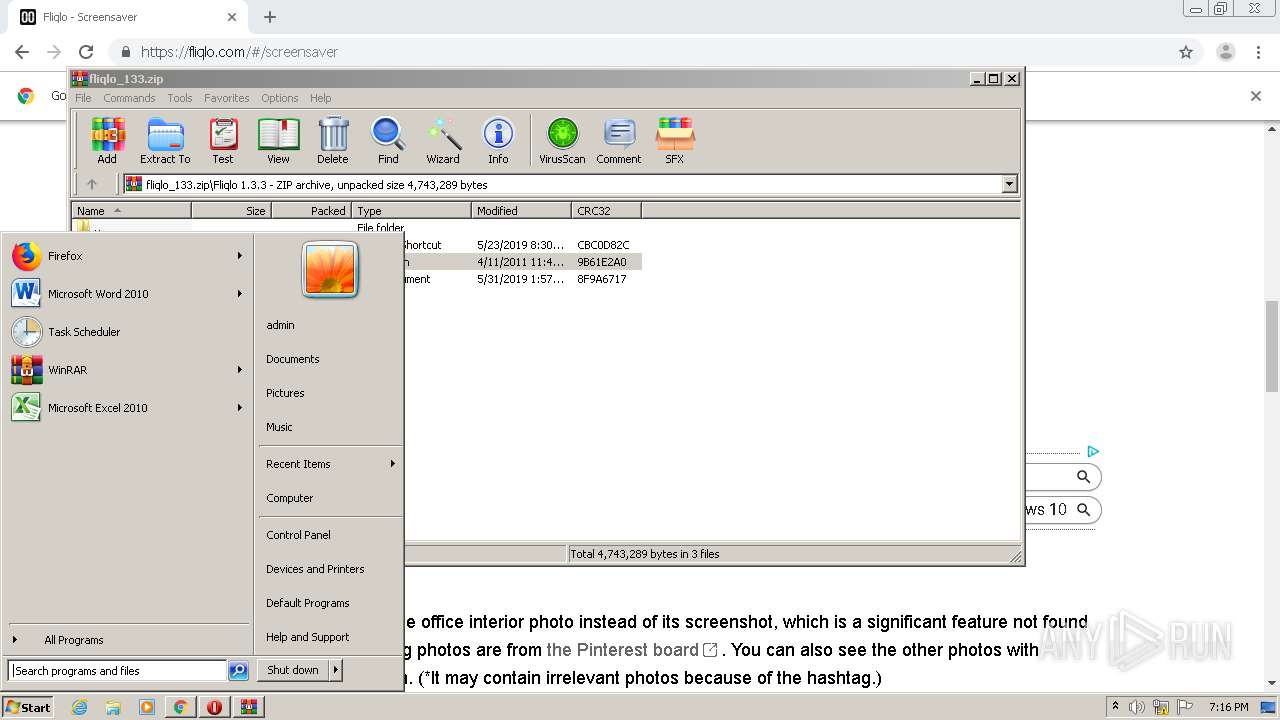
Manual execution by user
- explorer.exe (PID: 3084)
- opera.exe (PID: 2376)
- Fliqlo Setup.exe (PID: 2192)
- Fliqlo Setup.exe (PID: 3092)
Creates files in the user directory
- opera.exe (PID: 2376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
38
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,12374428996855974147,17257351658234255004,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9548084074587335541 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3800 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
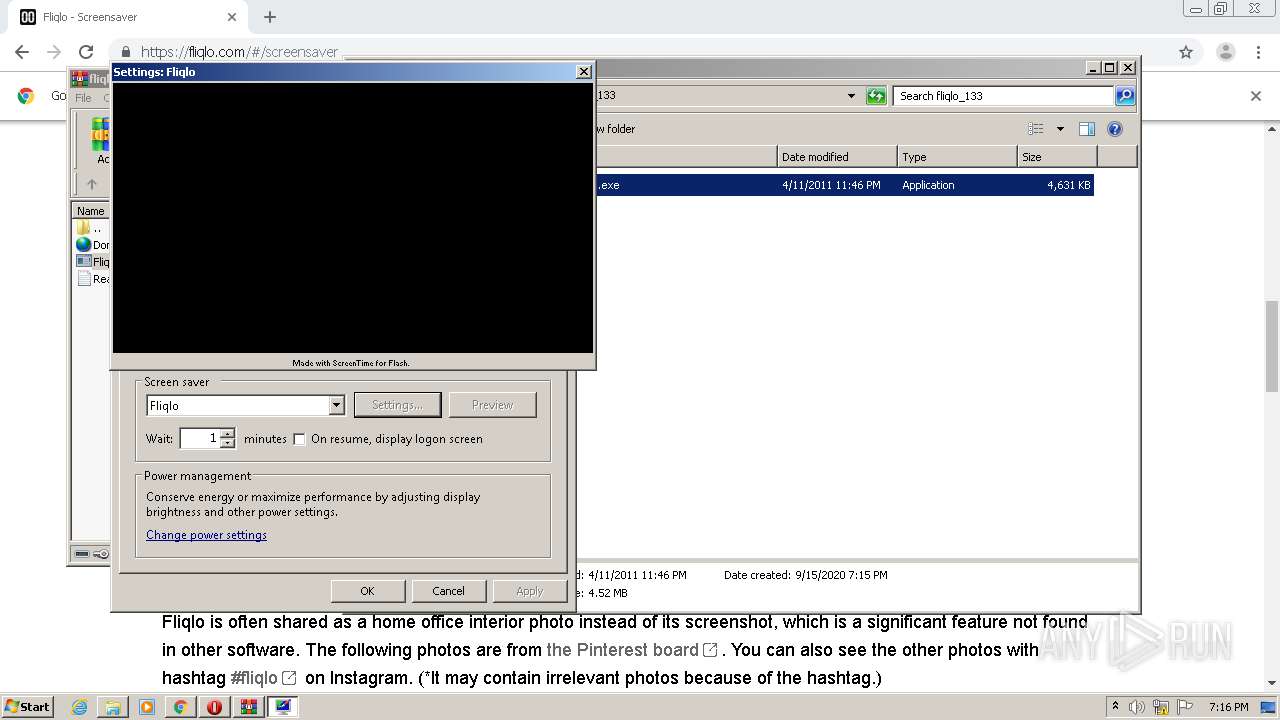
| 560 | C:\Windows\system32\Fliqlo.scr /p 131752 | C:\Windows\system32\Fliqlo.scr | — | rundll32.exe | |||||||||||
User: admin Company: ScreenTime Media Integrity Level: HIGH Description: ScreenTime Screensaver Engine Exit code: 0 Version: 4.0.2 Modules
| |||||||||||||||
| 608 | C:\Windows\system32\Fliqlo.scr /p 66178 | C:\Windows\system32\Fliqlo.scr | — | rundll32.exe | |||||||||||
User: admin Company: ScreenTime Media Integrity Level: MEDIUM Description: ScreenTime Screensaver Engine Exit code: 0 Version: 4.0.2 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,12374428996855974147,17257351658234255004,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=350708308418413654 --mojo-platform-channel-handle=4040 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,12374428996855974147,17257351658234255004,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9868549605231305241 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://fliqlo.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6cbca9d0,0x6cbca9e0,0x6cbca9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,12374428996855974147,17257351658234255004,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15323832308963265257 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,12374428996855974147,17257351658234255004,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13076734992968436973 --mojo-platform-channel-handle=4536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,12374428996855974147,17257351658234255004,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15093342914938819799 --mojo-platform-channel-handle=4240 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 852
Read events
2 622
Write events
226
Delete events
4
Modification events
| (PID) Process: | (1144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1144-13244667200654500 |
Value: 259 | |||
| (PID) Process: | (1144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (1144) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
30
Suspicious files
112
Text files
202
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ebf5d59e-1ac3-4919-92ce-f6920d6f1e94.tmp | — | |
MD5:— | SHA256:— | |||
| 1144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFed647.TMP | text | |
MD5:— | SHA256:— | |||
| 1144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFed628.TMP | text | |
MD5:— | SHA256:— | |||
| 1144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 1144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFed7ed.TMP | — | |
MD5:— | SHA256:— | |||
| 1144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
100
DNS requests
45
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3012 | chrome.exe | GET | 200 | 173.194.5.232:80 | http://r3---sn-aigzrn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=185.192.70.18&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1600193542&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 834 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3012 | chrome.exe | 157.7.44.174:443 | fliqlo.com | GMO Internet,Inc | JP | suspicious |
3012 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 104.17.79.107:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3012 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 93.184.220.66:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3012 | chrome.exe | 216.58.207.72:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3012 | chrome.exe | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
3012 | chrome.exe | 23.210.248.189:443 | assets.pinterest.com | Akamai International B.V. | NL | whitelisted |
3012 | chrome.exe | 216.58.210.2:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fliqlo.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
cdnjs.cloudflare.com |
| whitelisted |
code.jquery.com |
| whitelisted |
platform.twitter.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
assets.pinterest.com |
| whitelisted |