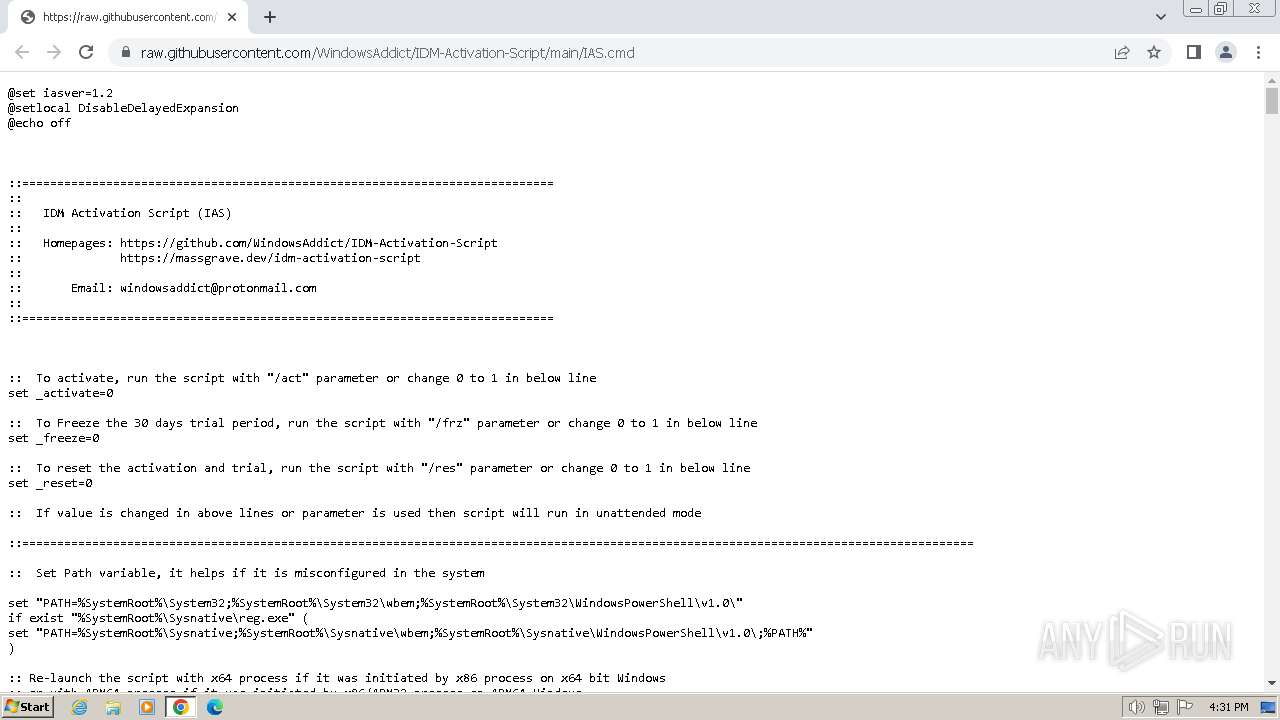
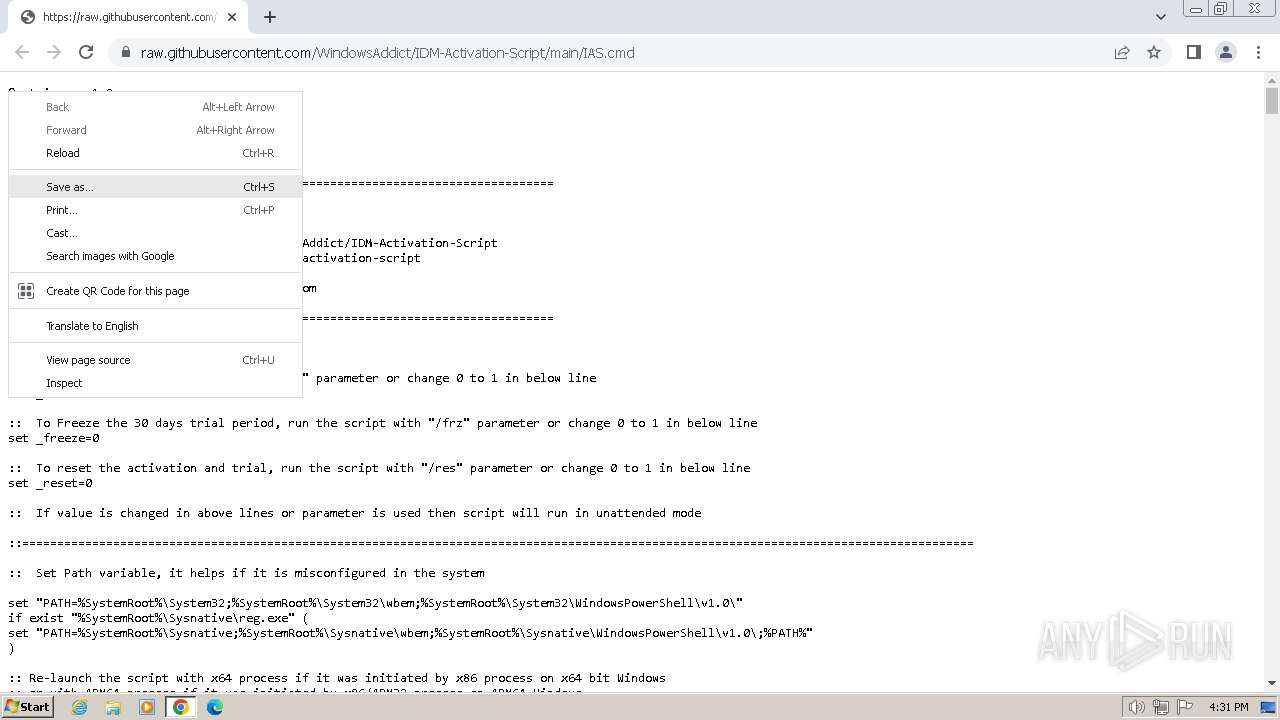
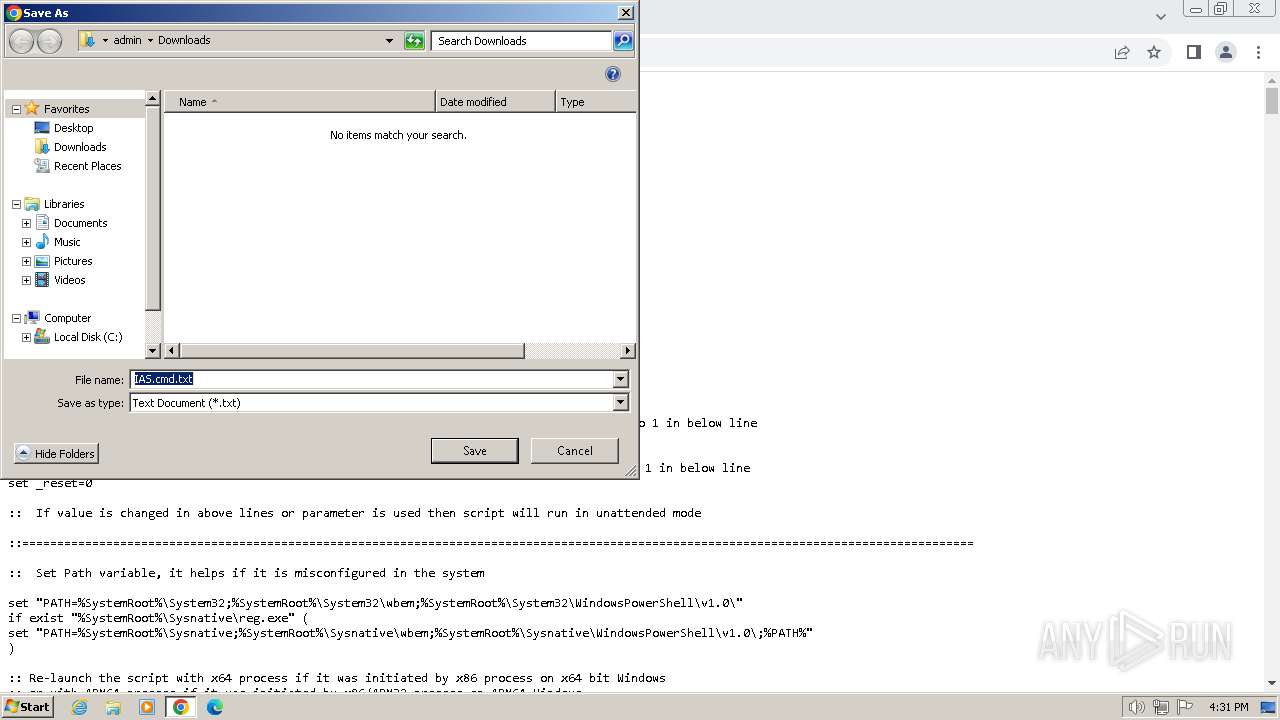
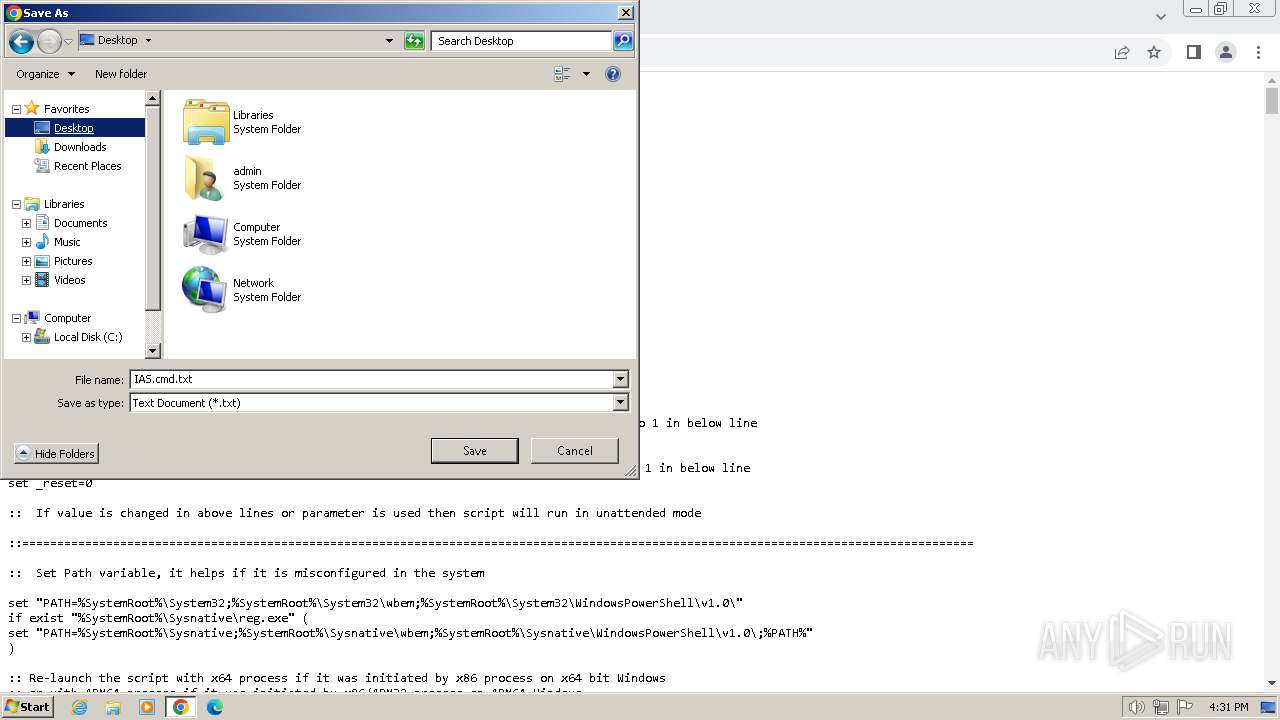
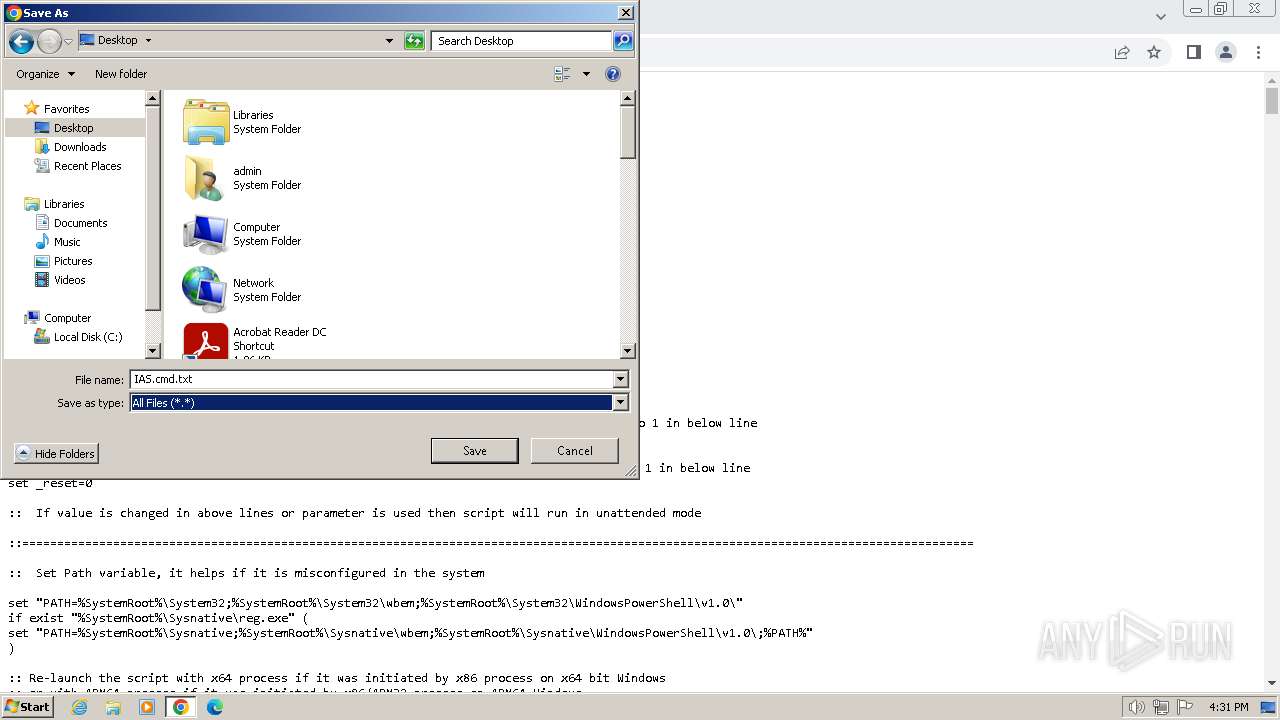
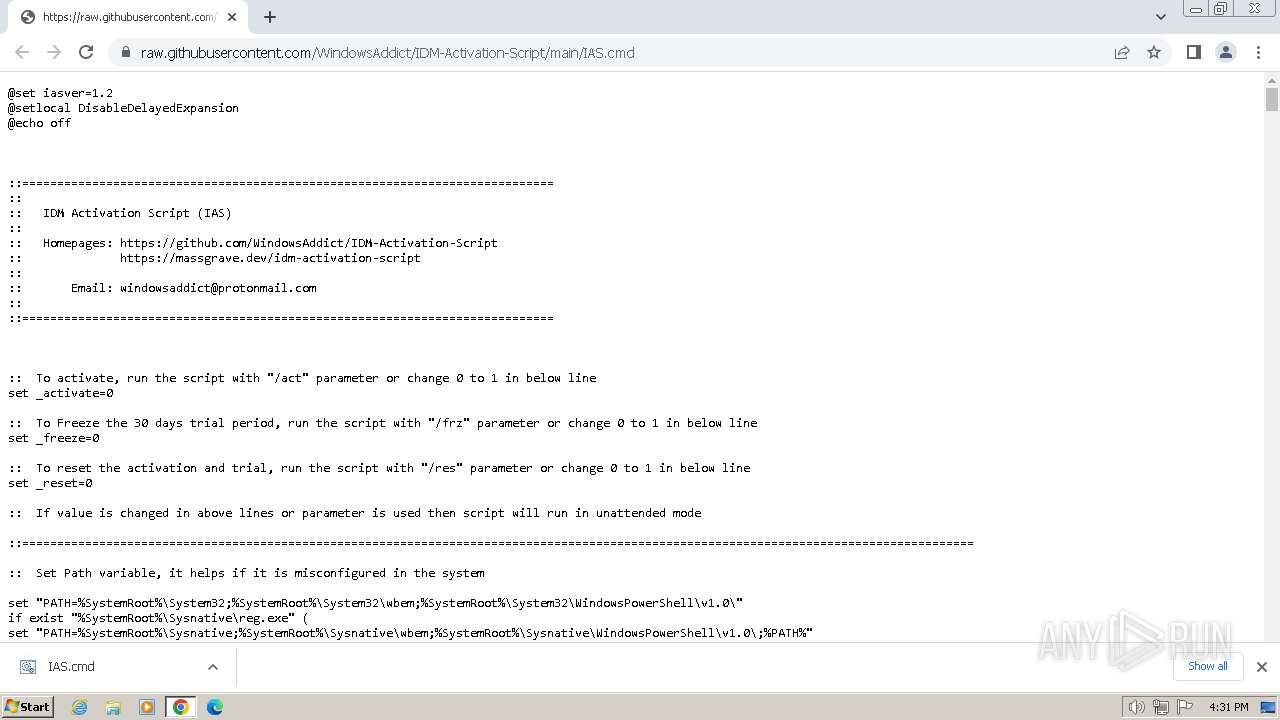
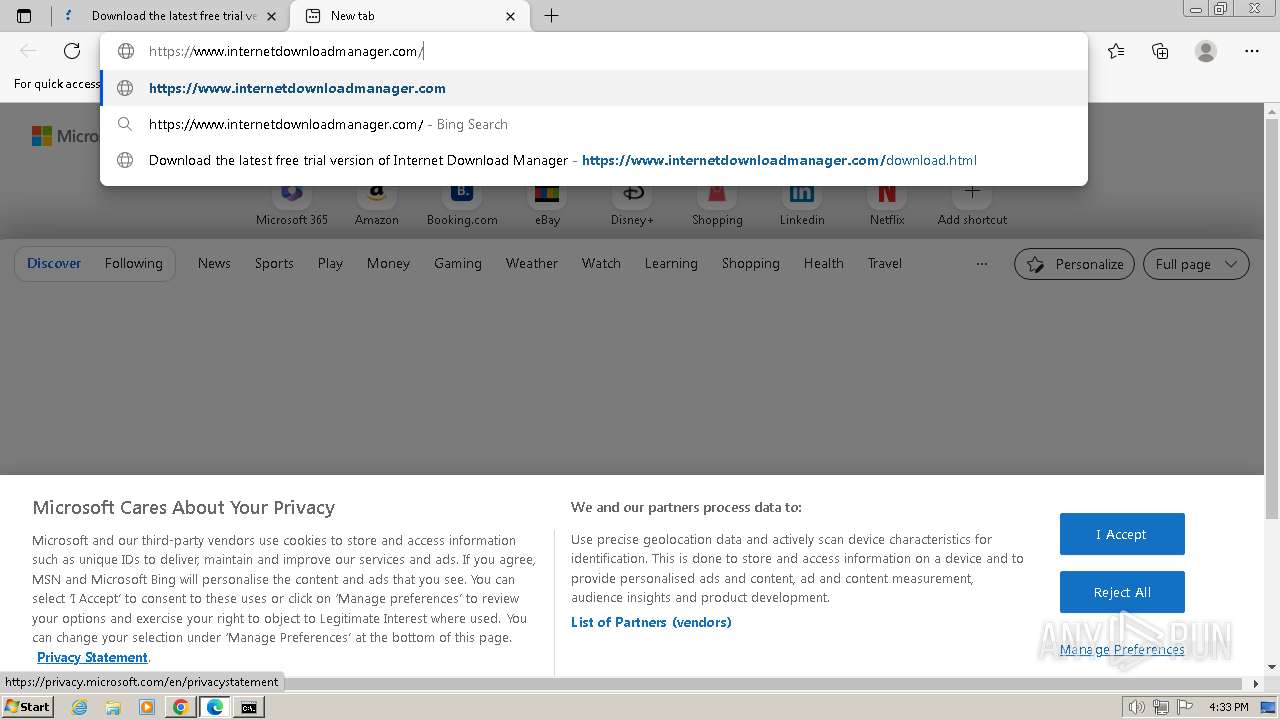
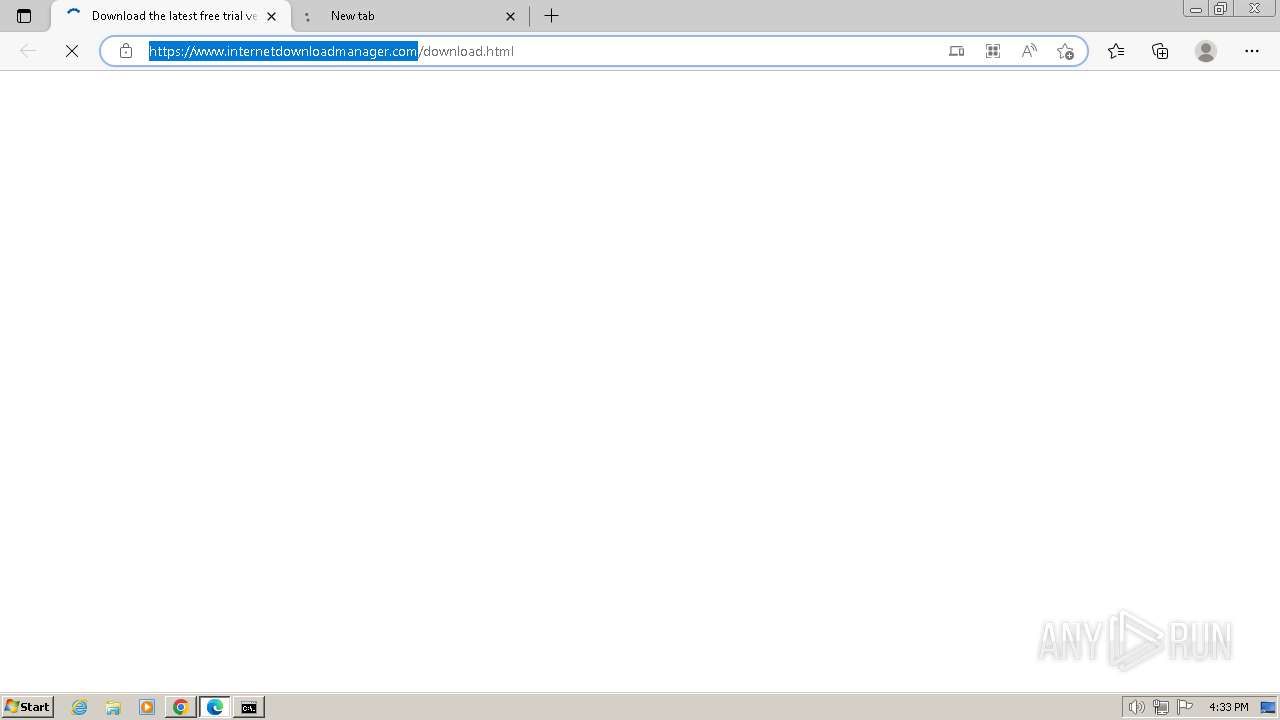
| URL: | https://raw.githubusercontent.com/WindowsAddict/IDM-Activation-Script/main/IAS.cmd |
| Full analysis: | https://app.any.run/tasks/78e4f1d2-f7a7-4eec-828c-d39904404e82 |
| Verdict: | Malicious activity |
| Analysis date: | July 01, 2024, 15:30:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1DFA2A22B6ED2BB877F72BE54E6FF40D |
| SHA1: | 45CA403AF90A50BC196892E0229D0F9CFA96A1B0 |
| SHA256: | 6DC4BD3BC3ABD5BD8F24AD13435E6E8AC865E714F64DED96AFFF114B1B6E4320 |
| SSDEEP: | 3:N8SGfALtGToD9Bx3SIRLLLGXUpEMLvLp:2FMGMDxSs/LGXUqMh |
MALICIOUS
No malicious indicators.SUSPICIOUS
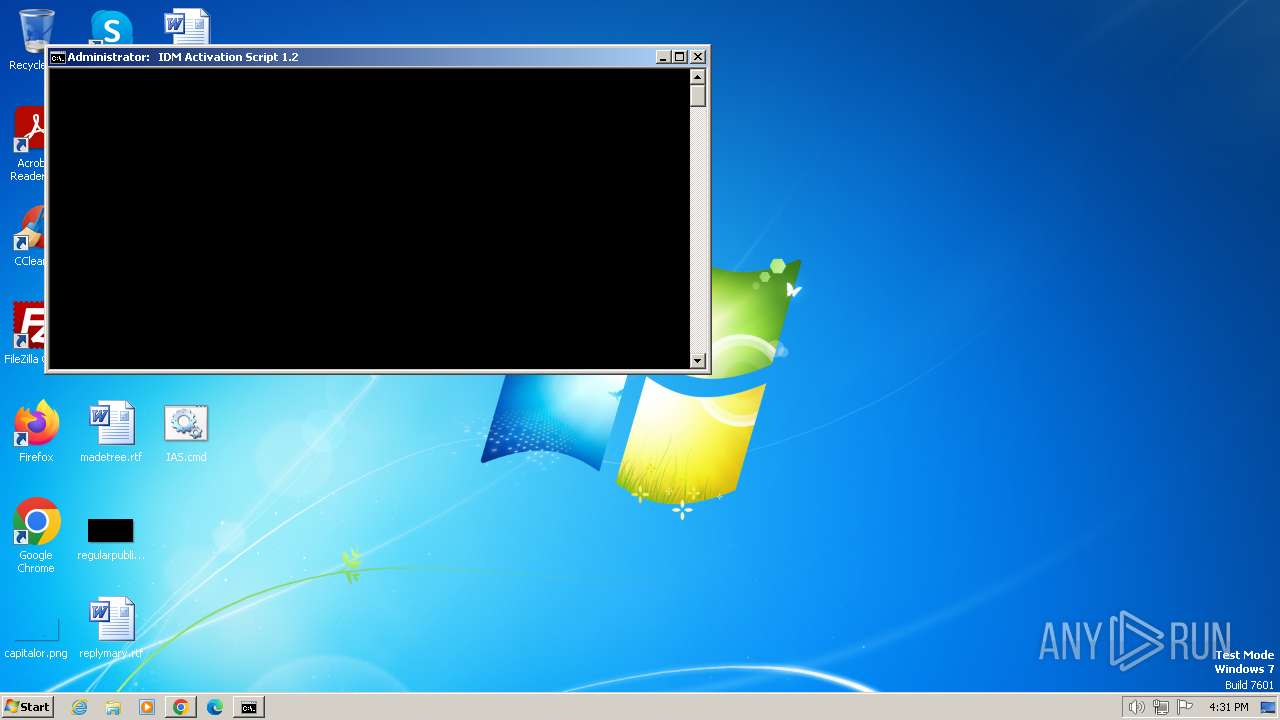
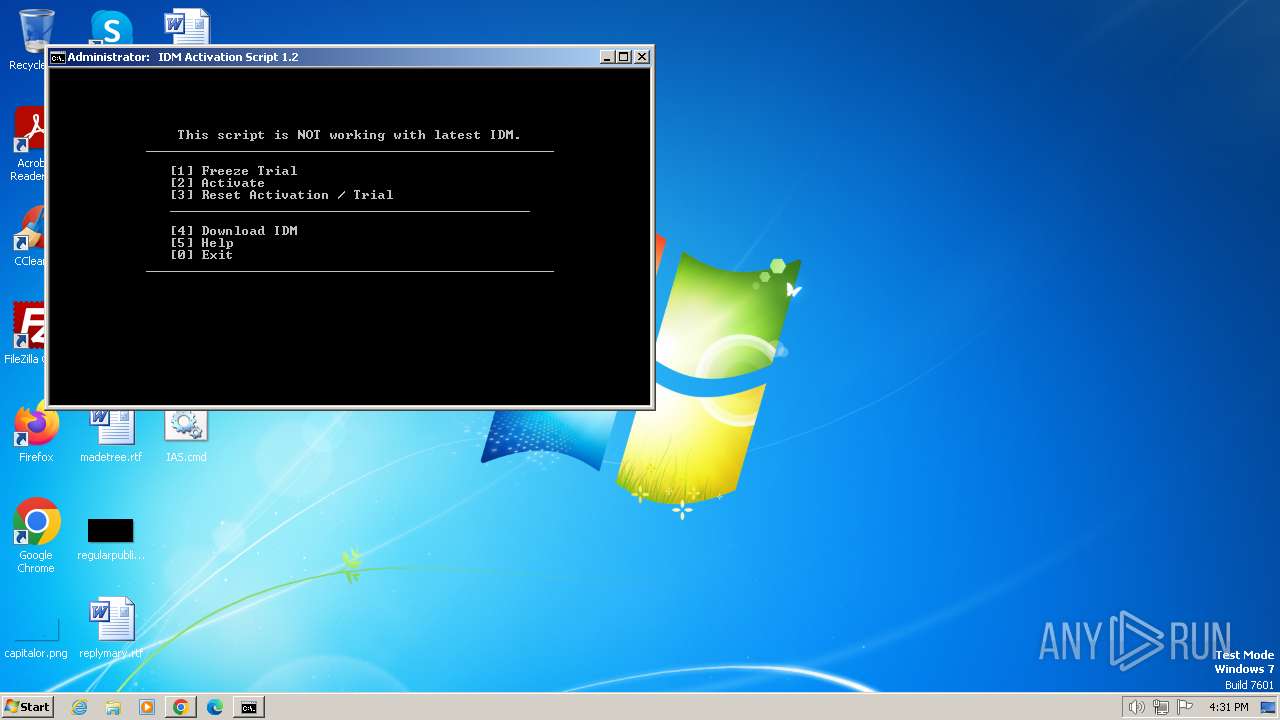
Application launched itself
- cmd.exe (PID: 2276)
- cmd.exe (PID: 2400)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2276)
- cmd.exe (PID: 2400)
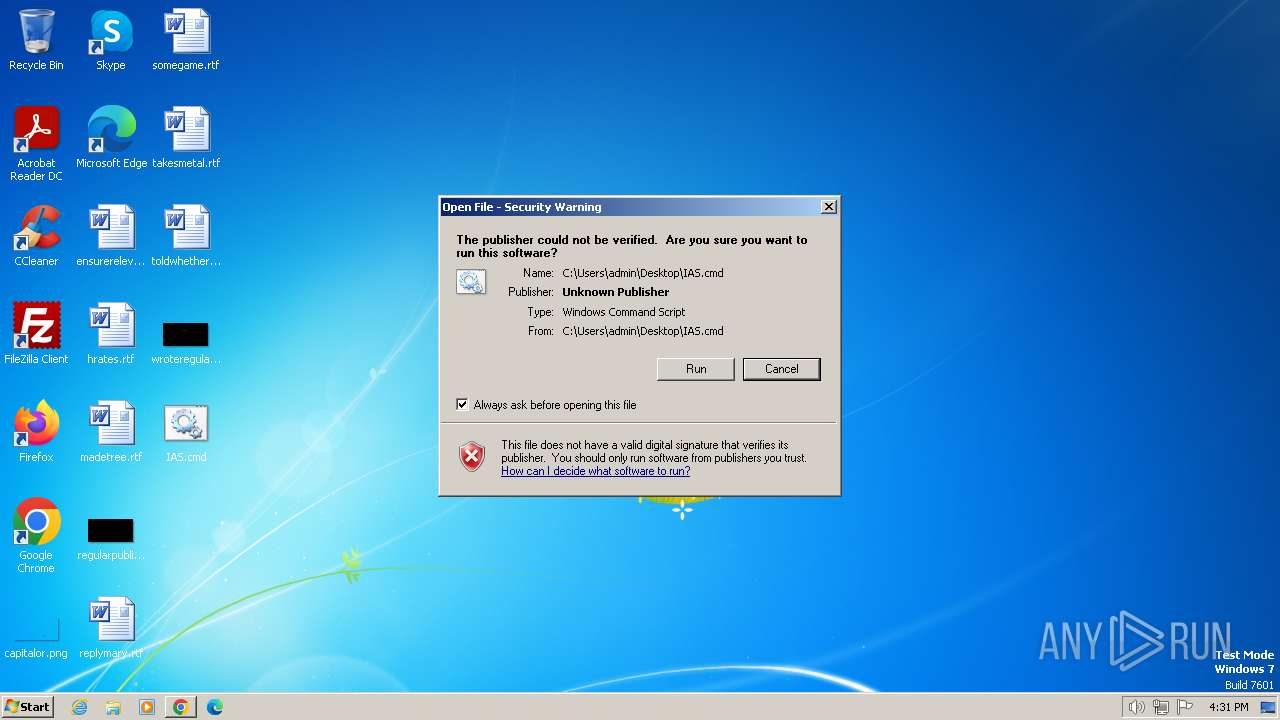
Executing commands from ".cmd" file
- cmd.exe (PID: 2276)
- powershell.exe (PID: 2284)
- cmd.exe (PID: 2400)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2276)
- cmd.exe (PID: 2400)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2276)
- powershell.exe (PID: 2284)
- cmd.exe (PID: 2400)
Starts SC.EXE for service management
- cmd.exe (PID: 2276)
- cmd.exe (PID: 2400)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2276)
- cmd.exe (PID: 2400)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2276)
- cmd.exe (PID: 2400)
- cmd.exe (PID: 2752)
Reads the Internet Settings
- powershell.exe (PID: 2284)
- cmd.exe (PID: 2400)
Hides command output
- cmd.exe (PID: 2752)
- cmd.exe (PID: 3840)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3840)
- cmd.exe (PID: 2400)
INFO
Checks operating system version
- cmd.exe (PID: 2276)
- cmd.exe (PID: 2400)
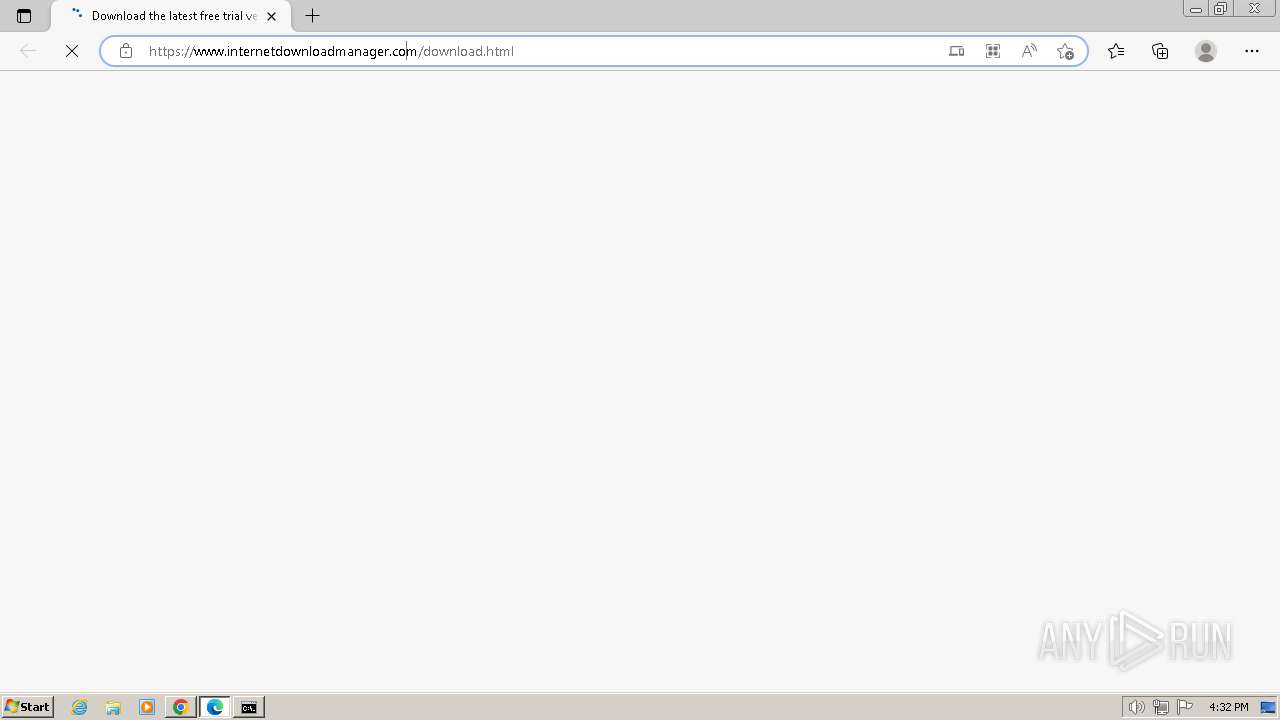
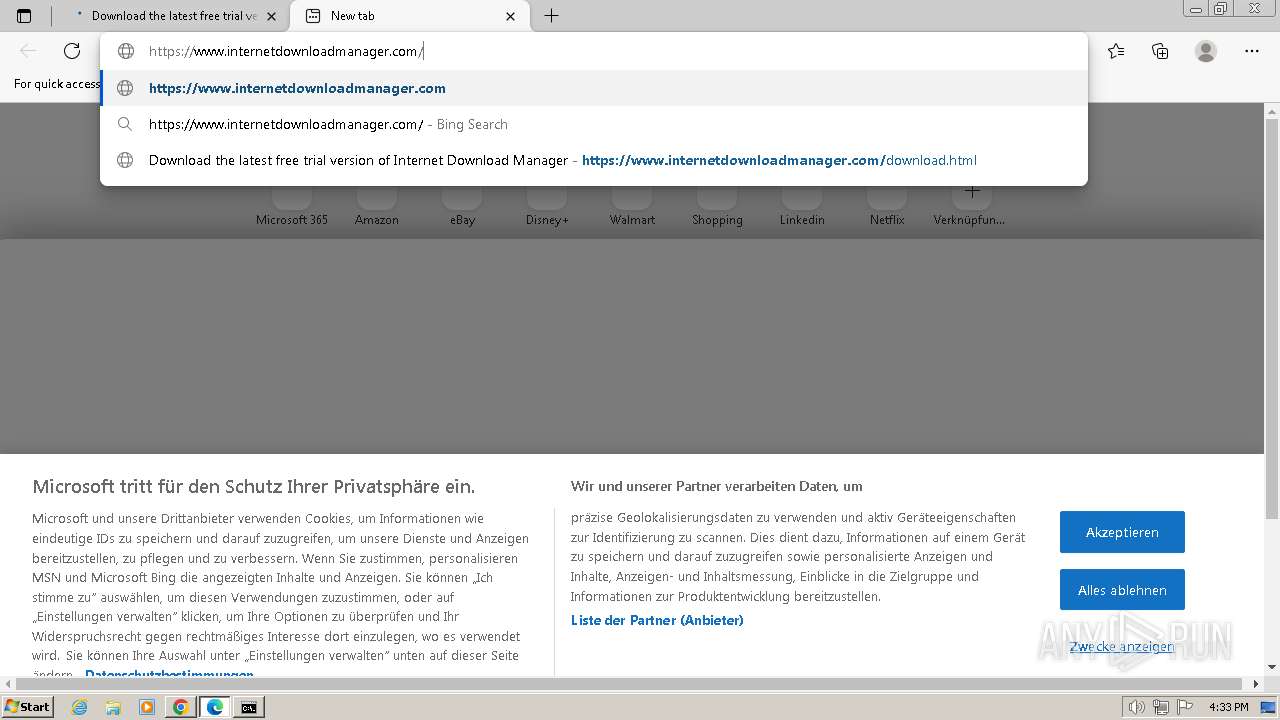
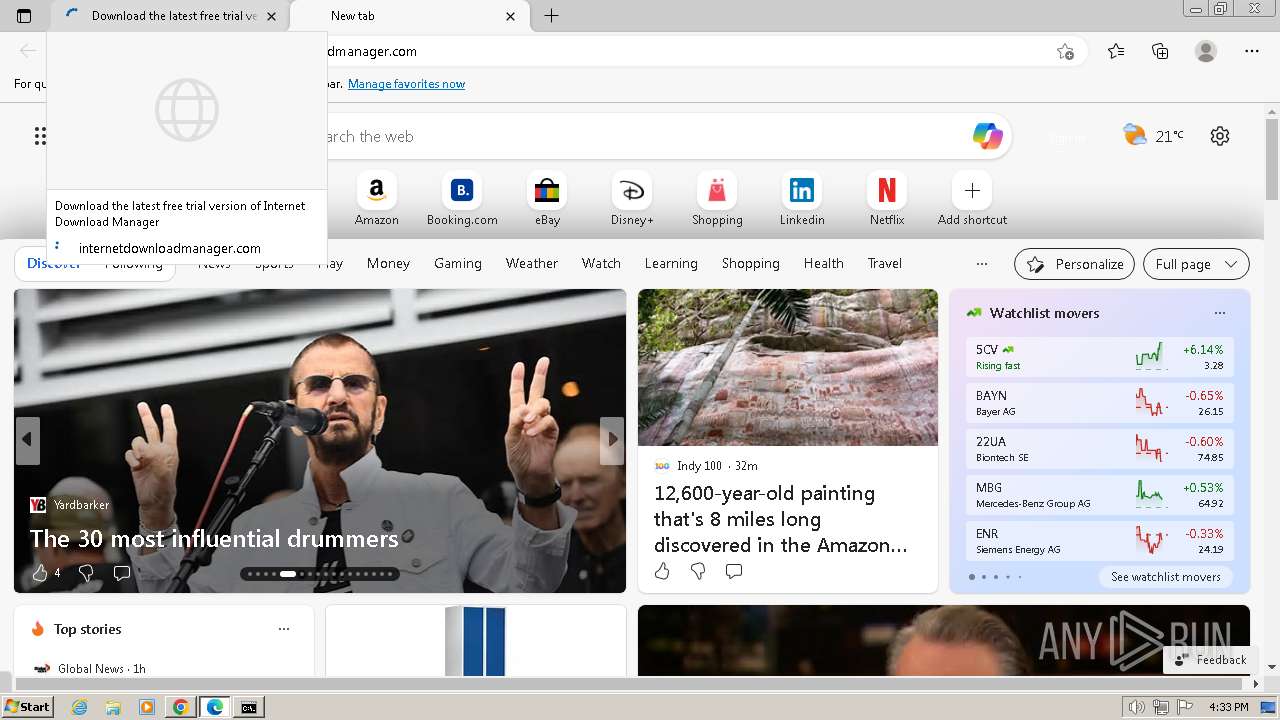
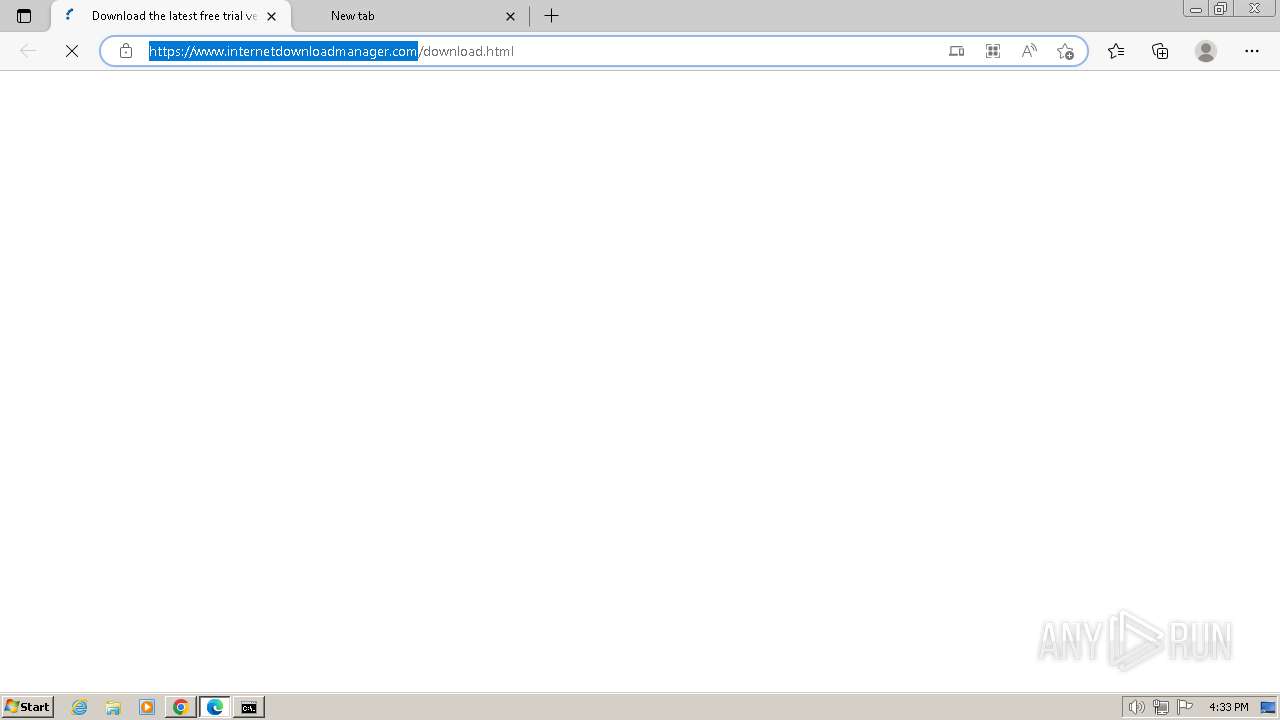
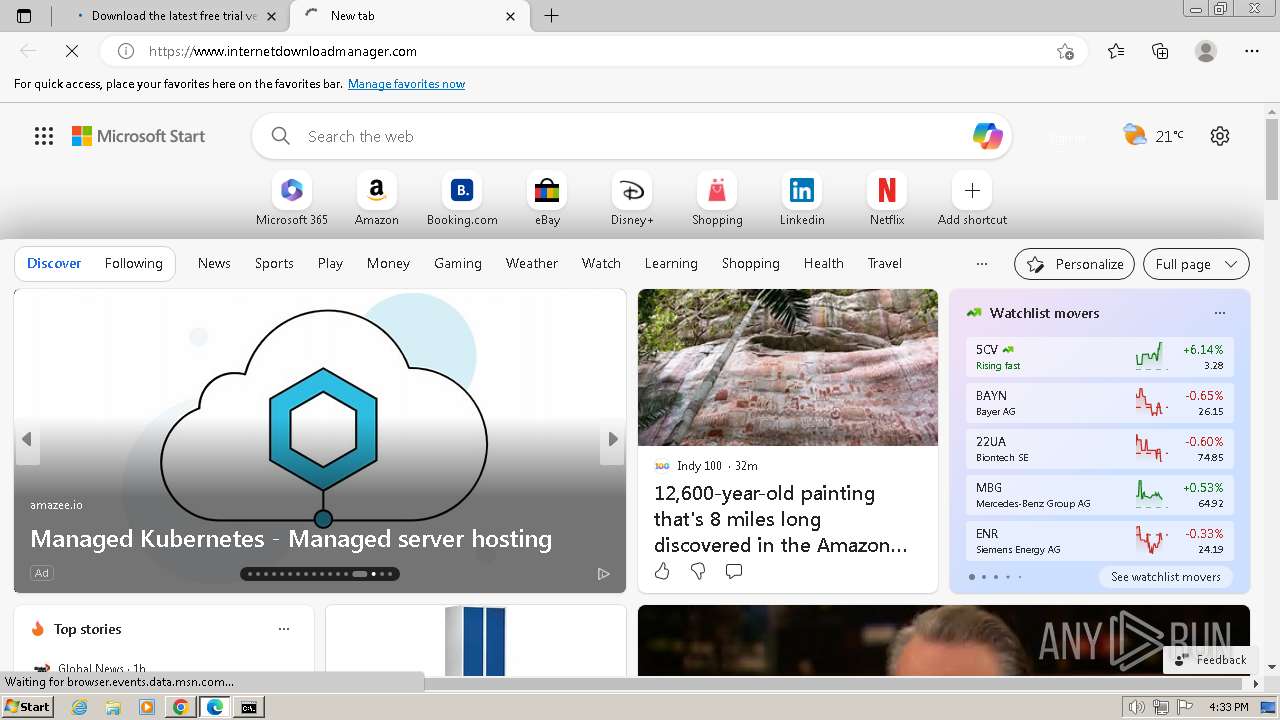
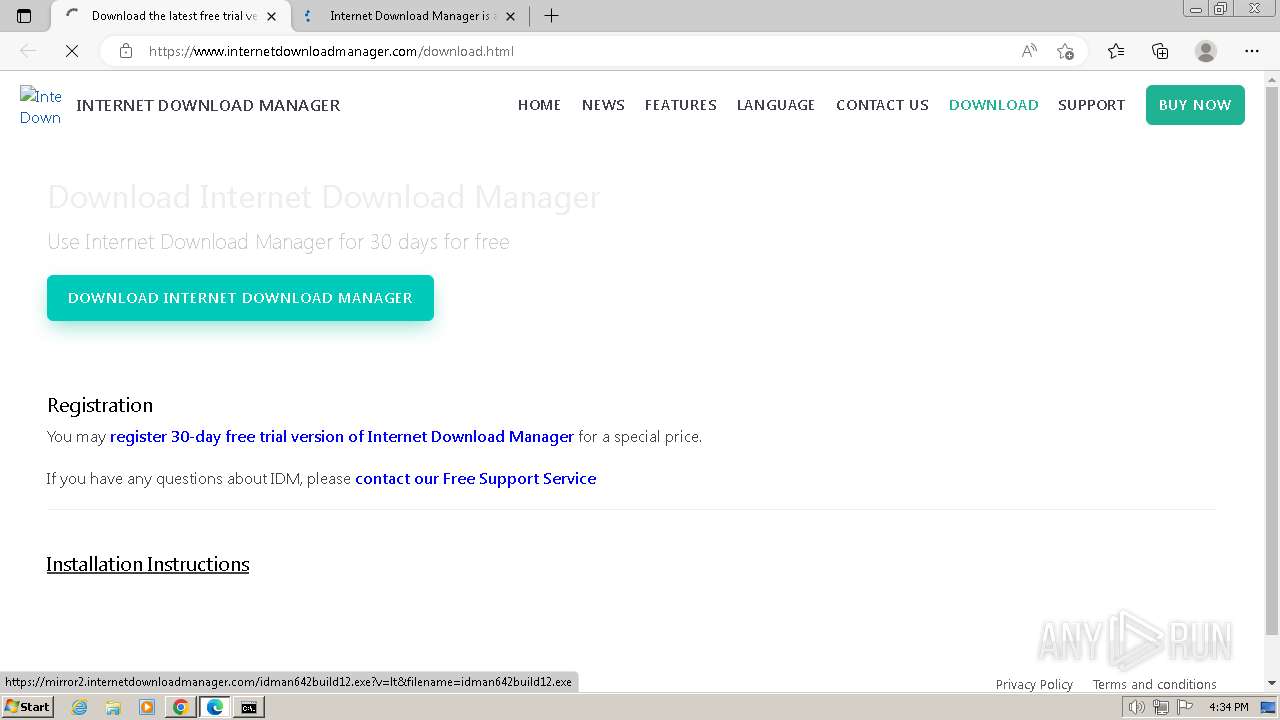
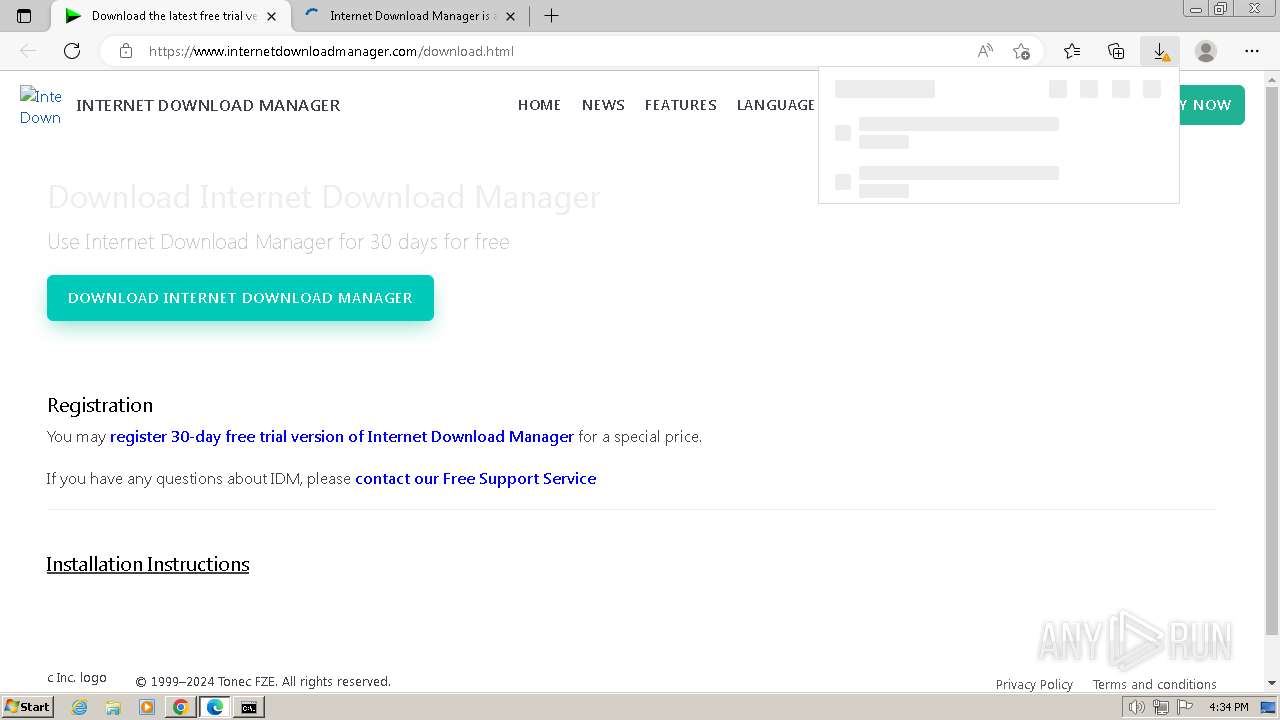
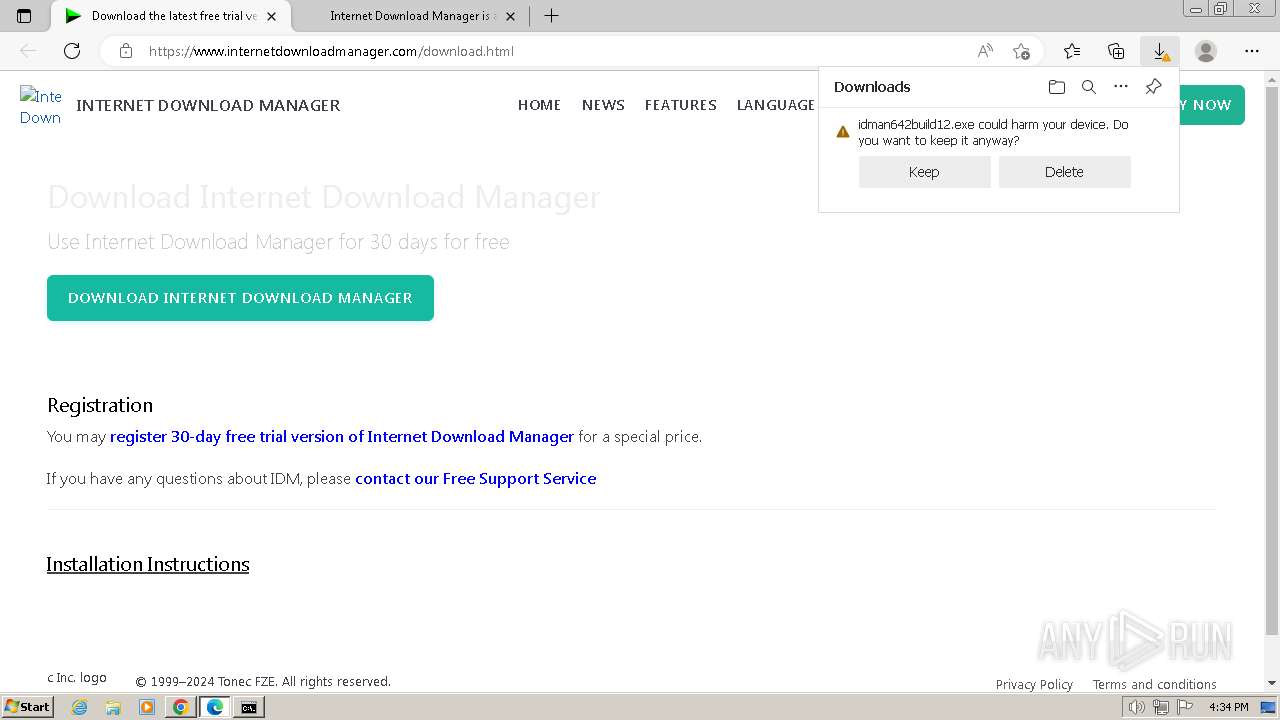
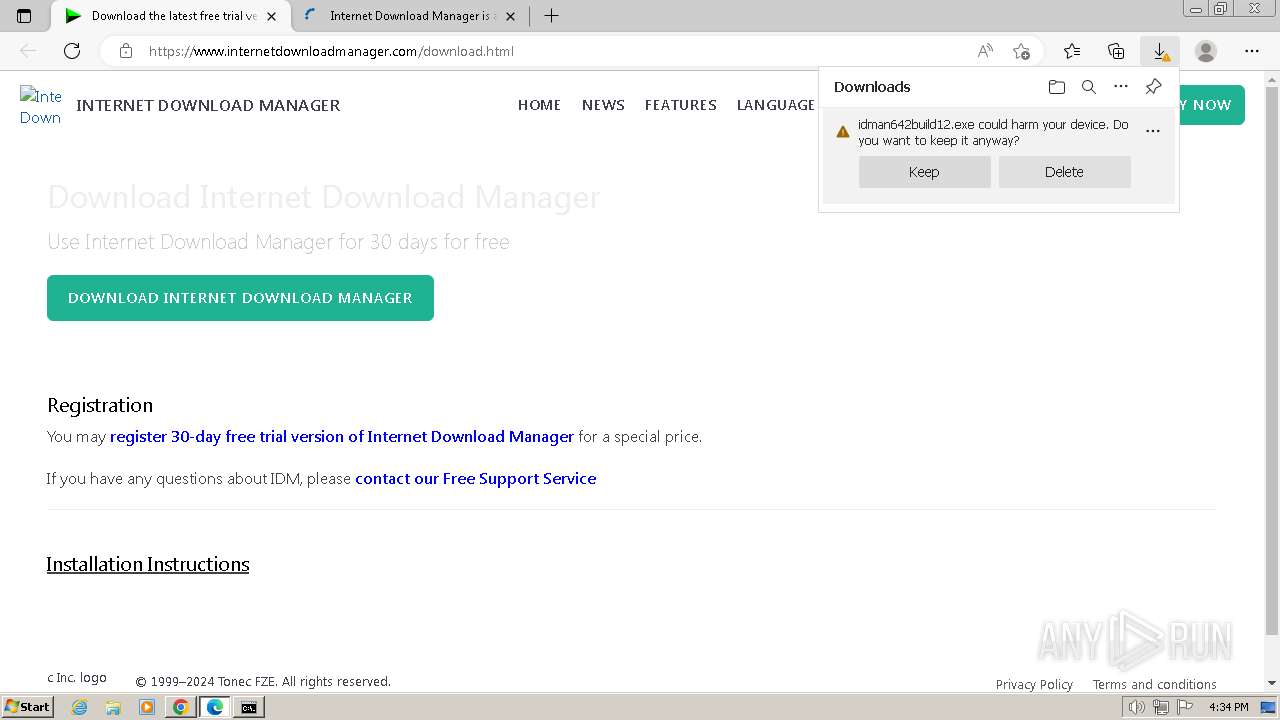
Manual execution by a user
- cmd.exe (PID: 2276)
- msedge.exe (PID: 3820)
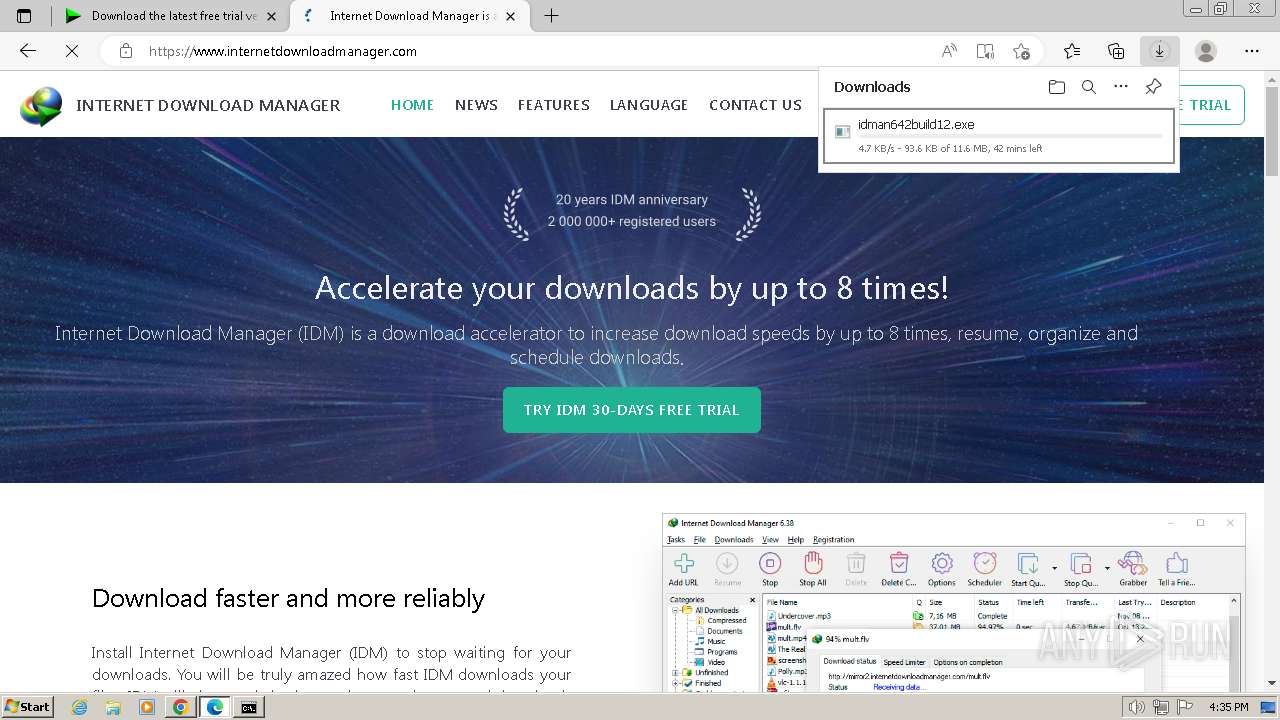
The process uses the downloaded file
- chrome.exe (PID: 2320)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3820)
- powershell.exe (PID: 3508)
Application launched itself
- chrome.exe (PID: 3268)
- msedge.exe (PID: 1420)
- msedge.exe (PID: 3820)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 3820)
- powershell.exe (PID: 3508)
Checks supported languages
- mode.com (PID: 1072)
- mode.com (PID: 2180)
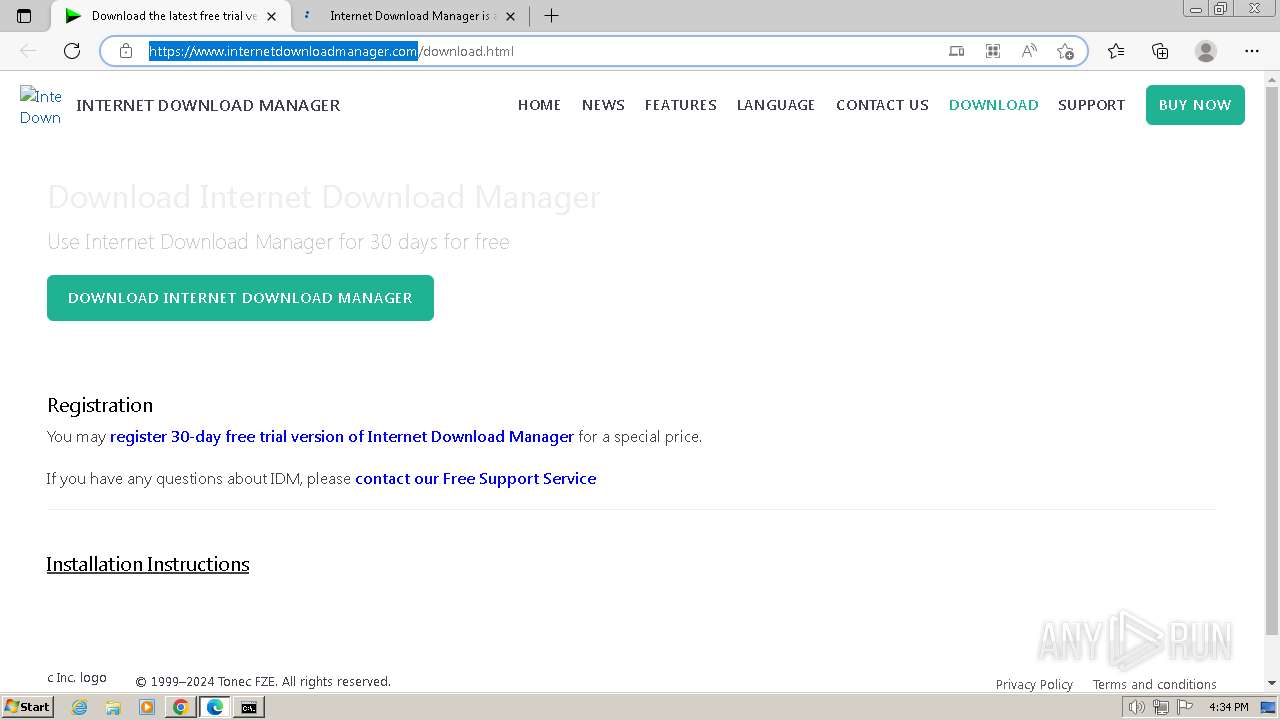
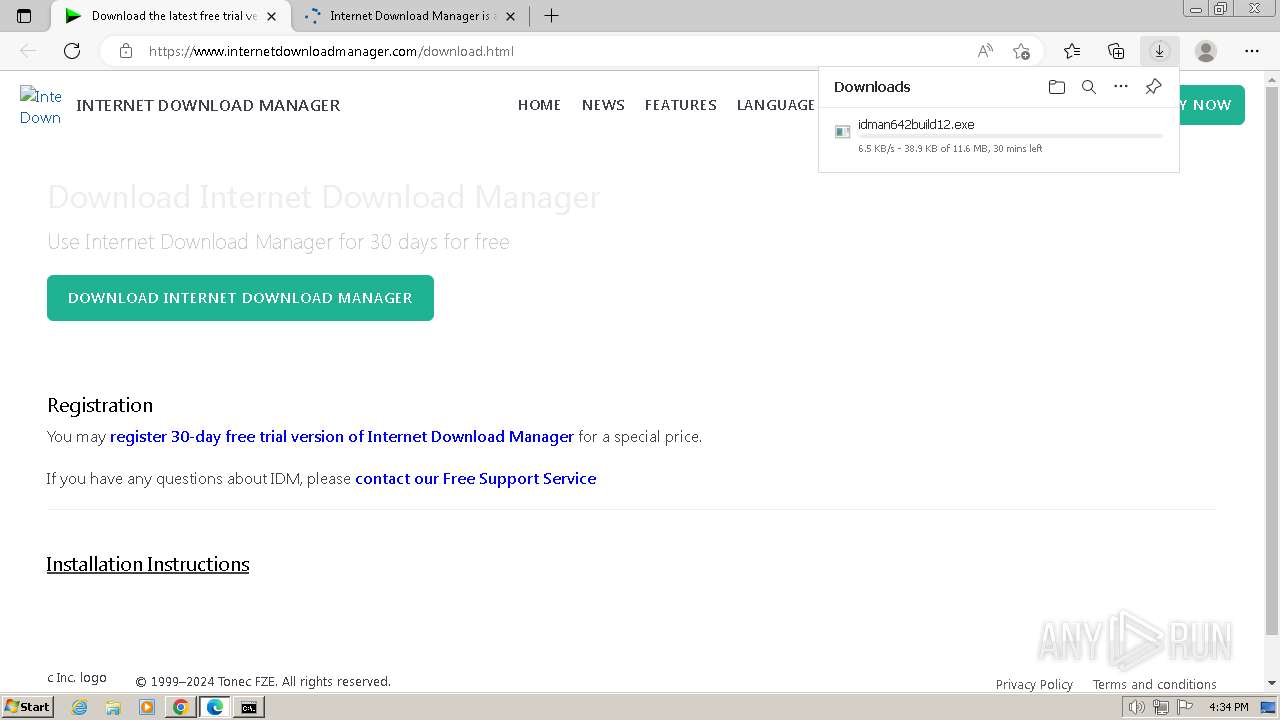
Executable content was dropped or overwritten
- msedge.exe (PID: 3820)
Drops the executable file immediately after the start
- chrome.exe (PID: 3268)
- msedge.exe (PID: 3820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
135
Monitored processes
89
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --mojo-platform-channel-handle=2600 --field-trial-handle=1292,i,10386278065743306947,9077815743202004906,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 684 | fltmc | C:\Windows\System32\fltMC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Filter Manager Control Program Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 880 | sc query Null | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 972 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xf0,0x6a56f598,0x6a56f5a8,0x6a56f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3616 --field-trial-handle=1292,i,10386278065743306947,9077815743202004906,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1072 | mode 75, 28 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1080 | sc query Null | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=3704 --field-trial-handle=1292,i,10386278065743306947,9077815743202004906,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1144 | powershell.exe write-host -back '"Black"' -fore '"Gray"' '" "' -NoNewline; write-host -back '"Black"' -fore '"Green"' '"Enter a menu option in the Keyboard [1,2,3,4,5,0]"' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1164 | powershell.exe write-host -back '"Black"' -fore '"Gray"' '" "' -NoNewline; write-host -back '"Black"' -fore '"Green"' '"Enter a menu option in the Keyboard [1,2,3,4,5,0]"' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
49 646
Read events
49 415
Write events
212
Delete events
19
Modification events
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
15
Suspicious files
511
Text files
115
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF4eb27.TMP | — | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF4ee54.TMP | text | |
MD5:BF244CDEBD39A0D20444C1578C0200BE | SHA256:CC7E247D7764DA50D4137E894838F918281D4915FE0823B4FC0CB763BF582F4D | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | text | |
MD5:7CC8F2B9E0FB4C25D7DEC651196EF439 | SHA256:D9D73DECB3BA242315B2D4DCB84D5CDF2B568FA632F548DB2857B27D6144C11A | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF4f420.TMP | — | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old | text | |
MD5:6344721DA60A3CF7027C43288C8991C6 | SHA256:DA3AD5C3641E42979DFB9D4178EDE8533F887C3ACF9C49BE9737D83CEDA55473 | |||
| 3268 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF5019d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
75
DNS requests
97
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 217.20.57.18:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 217.20.57.18:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
3564 | msedge.exe | GET | 204 | 13.107.6.158:80 | http://edge-http.microsoft.com/captiveportal/generate_204 | unknown | — | — | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
2936 | chrome.exe | POST | 200 | 142.250.186.131:80 | http://update.googleapis.com/service/update2/json?cup2key=12:7uGSFKpee2XVcV0YgRV2A-vofgmWMB7lDWU1KLu6ywM&cup2hreq=4b2b0d052ce9250a2bd84f668144e12fef9318cd6b3f9fbc508dee1534afd6a2 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1372 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2936 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | unknown |
3268 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2936 | chrome.exe | 185.199.108.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
2936 | chrome.exe | 142.250.185.196:443 | www.google.com | GOOGLE | US | whitelisted |
3268 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
raw.githubusercontent.com |
| shared |
www.google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
iasupdatecheck.massgrave.dev |
| unknown |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2936 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2936 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |