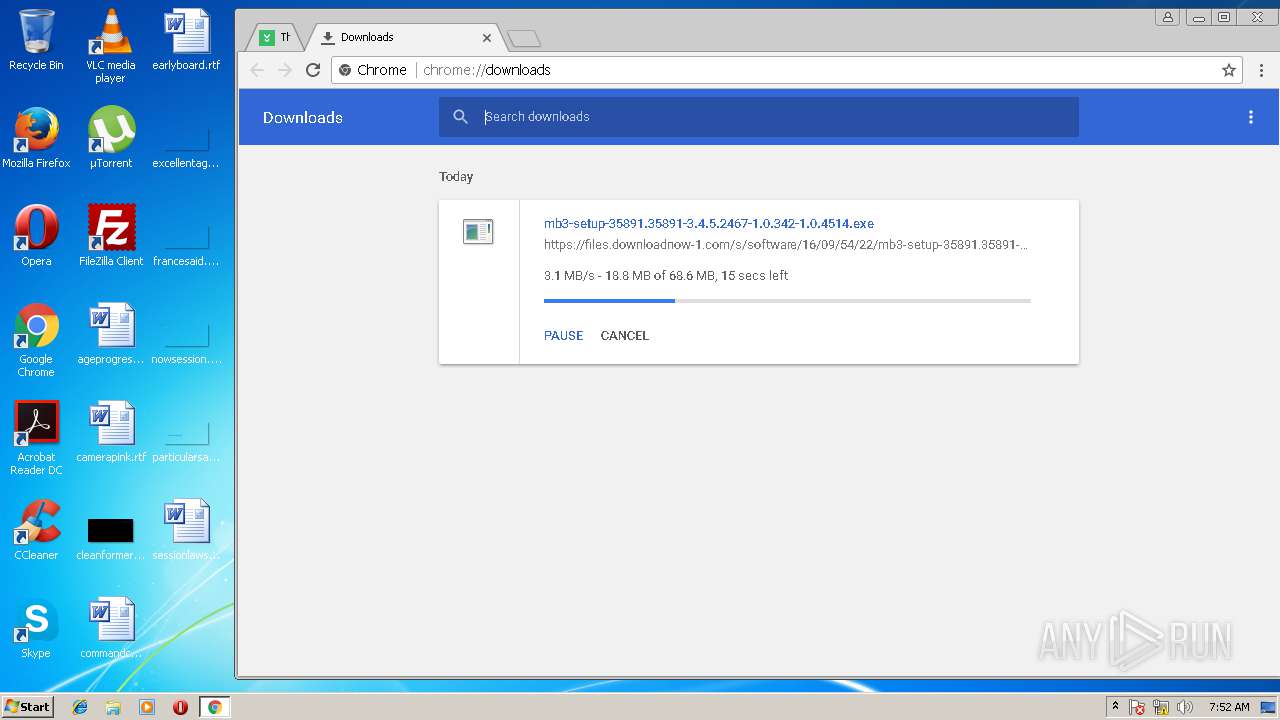
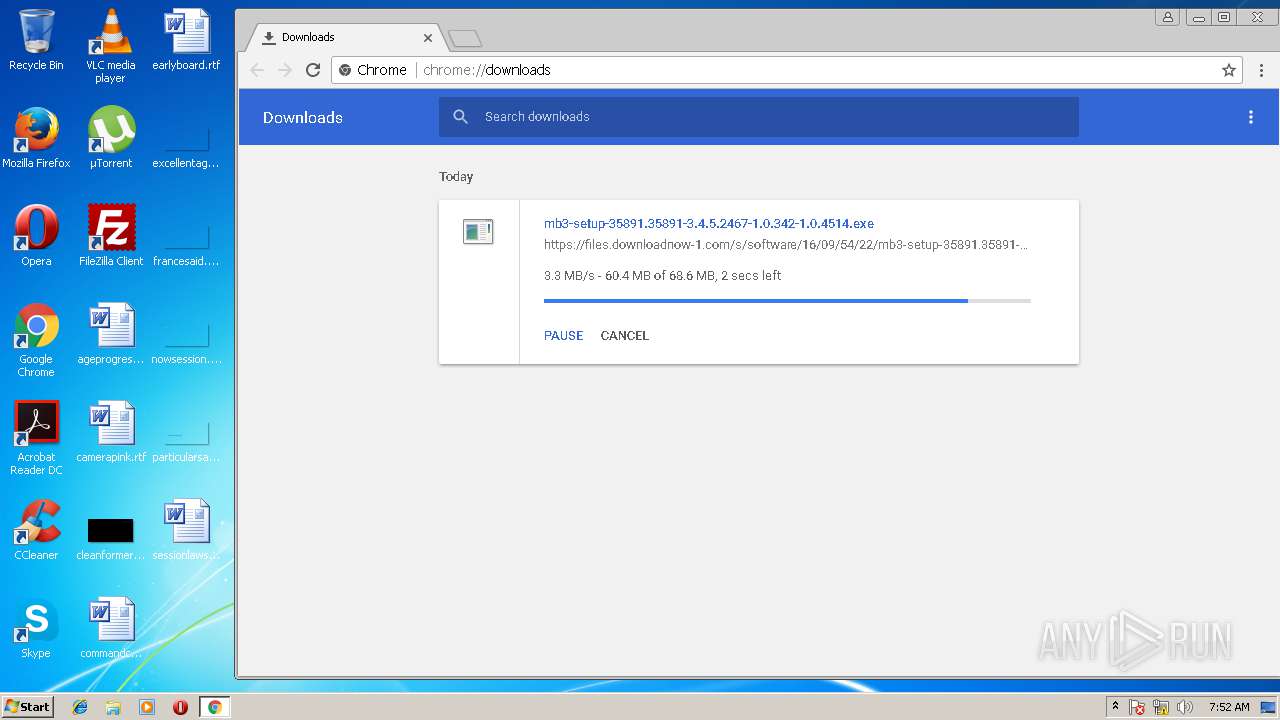
| download: | setup.exe |
| Full analysis: | https://app.any.run/tasks/402b8012-e898-4d90-b3e9-f9c0d0ba83c5 |
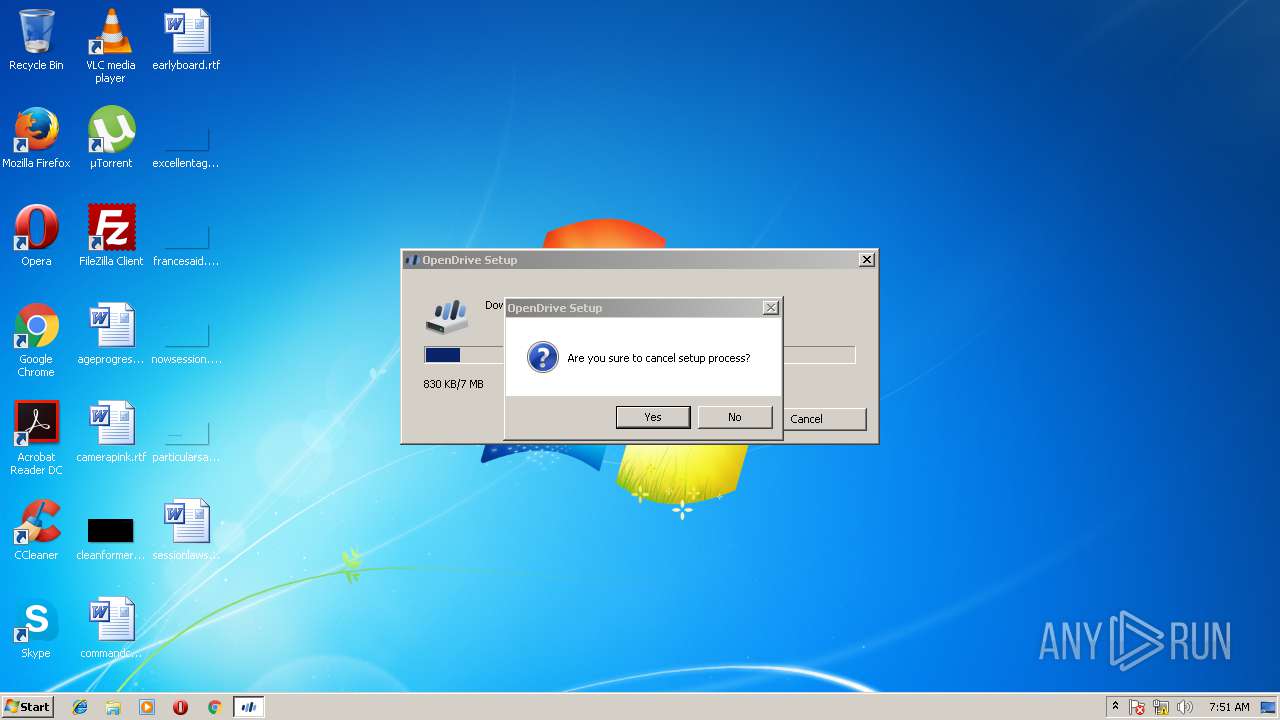
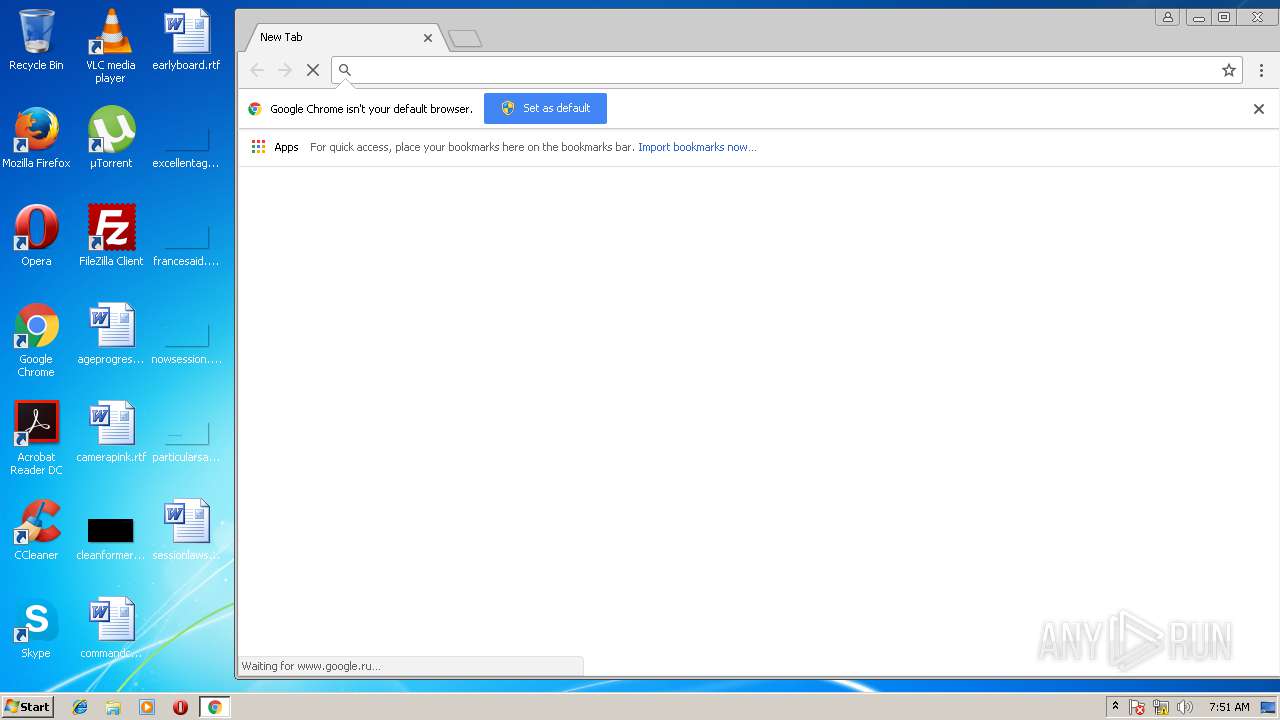
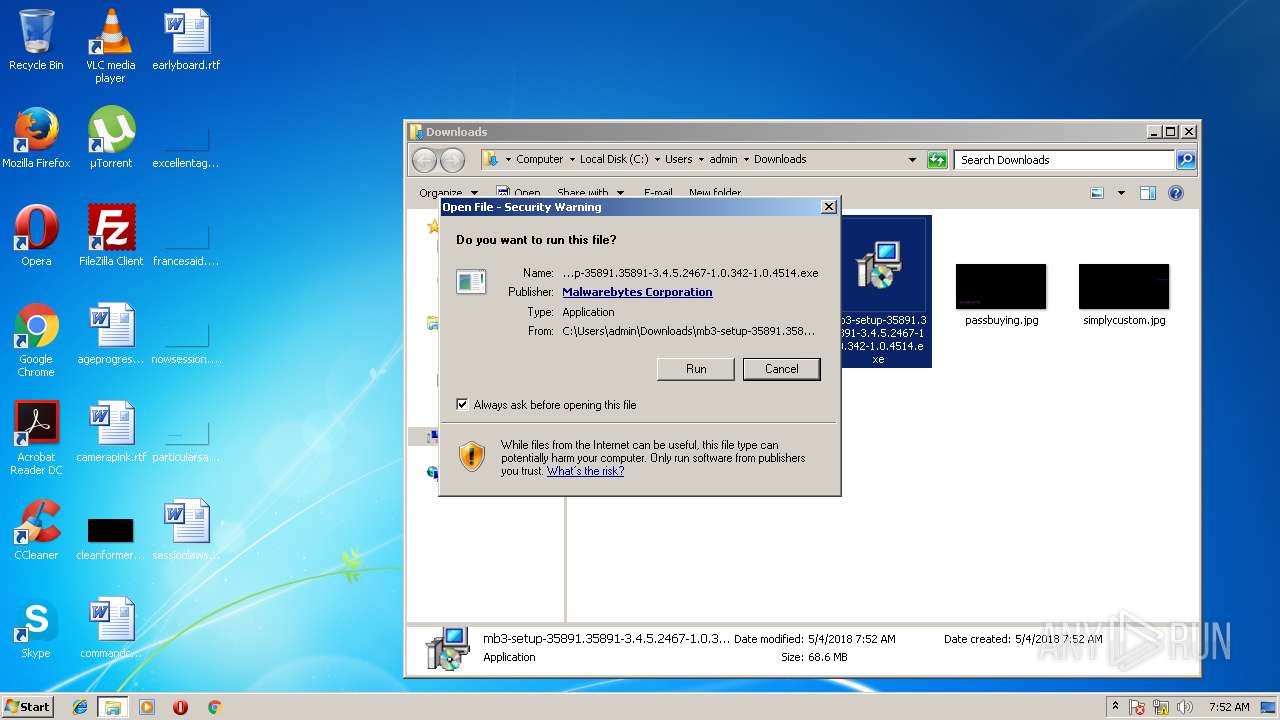
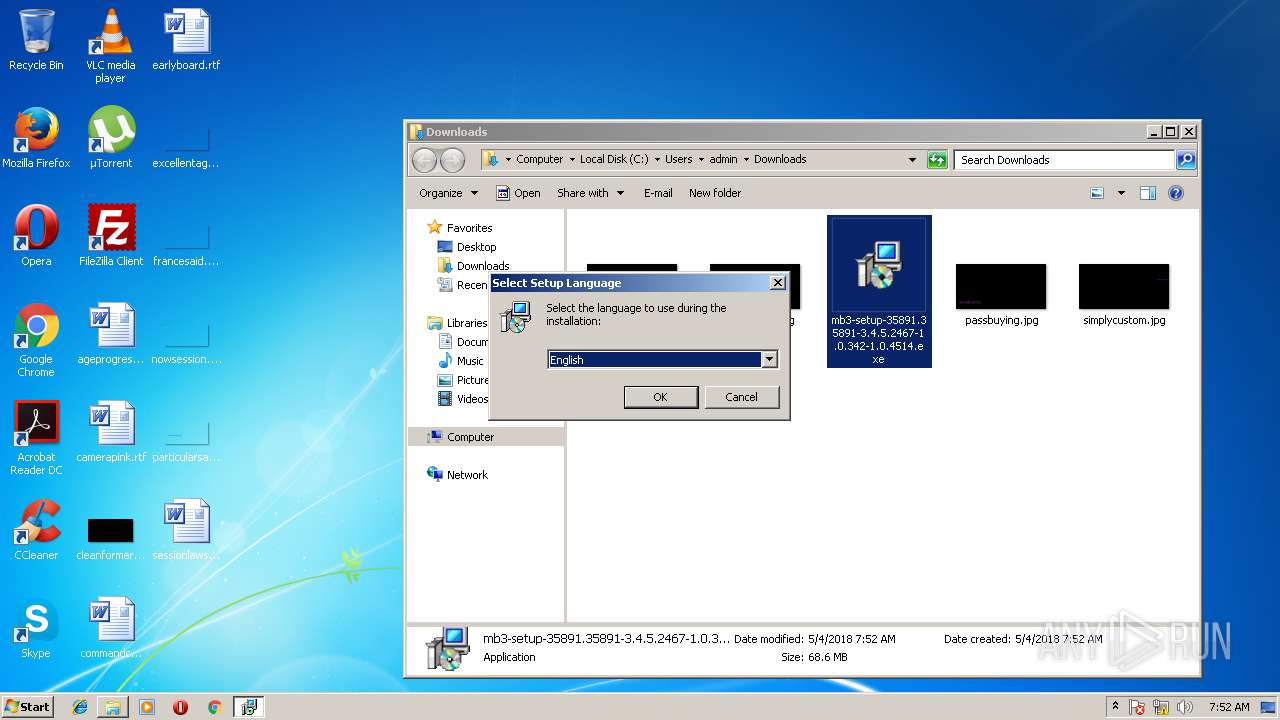
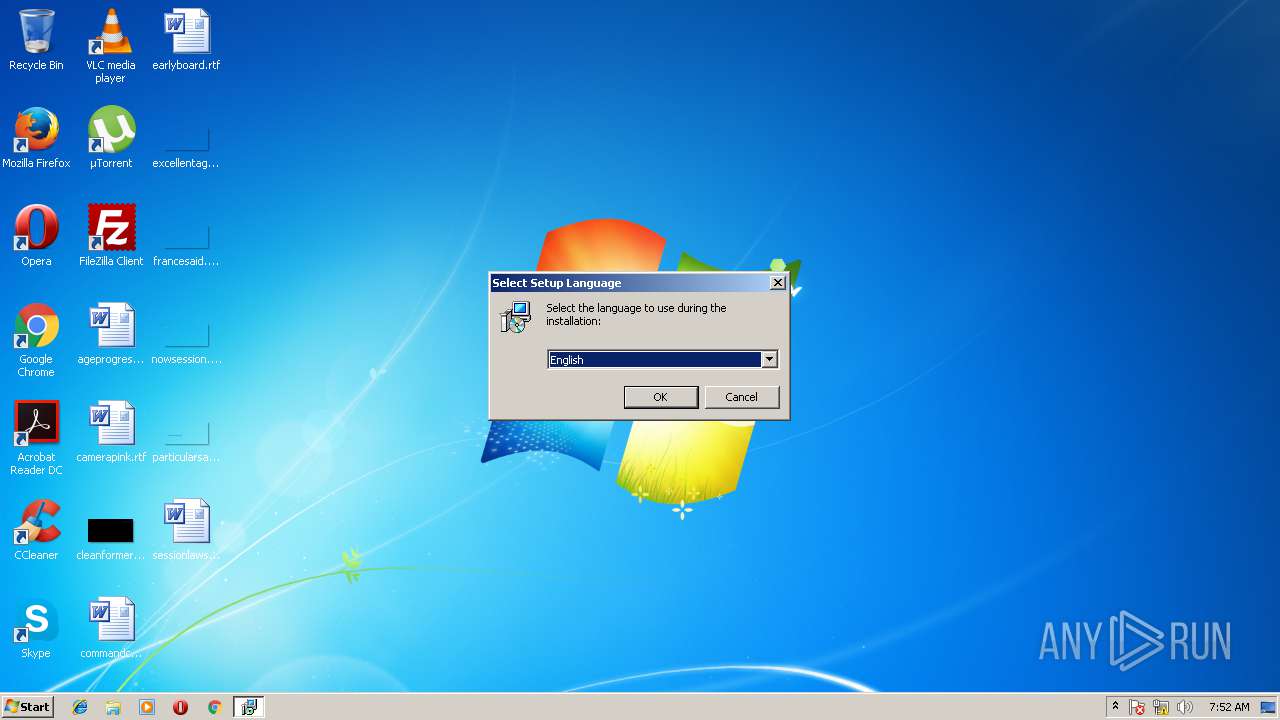
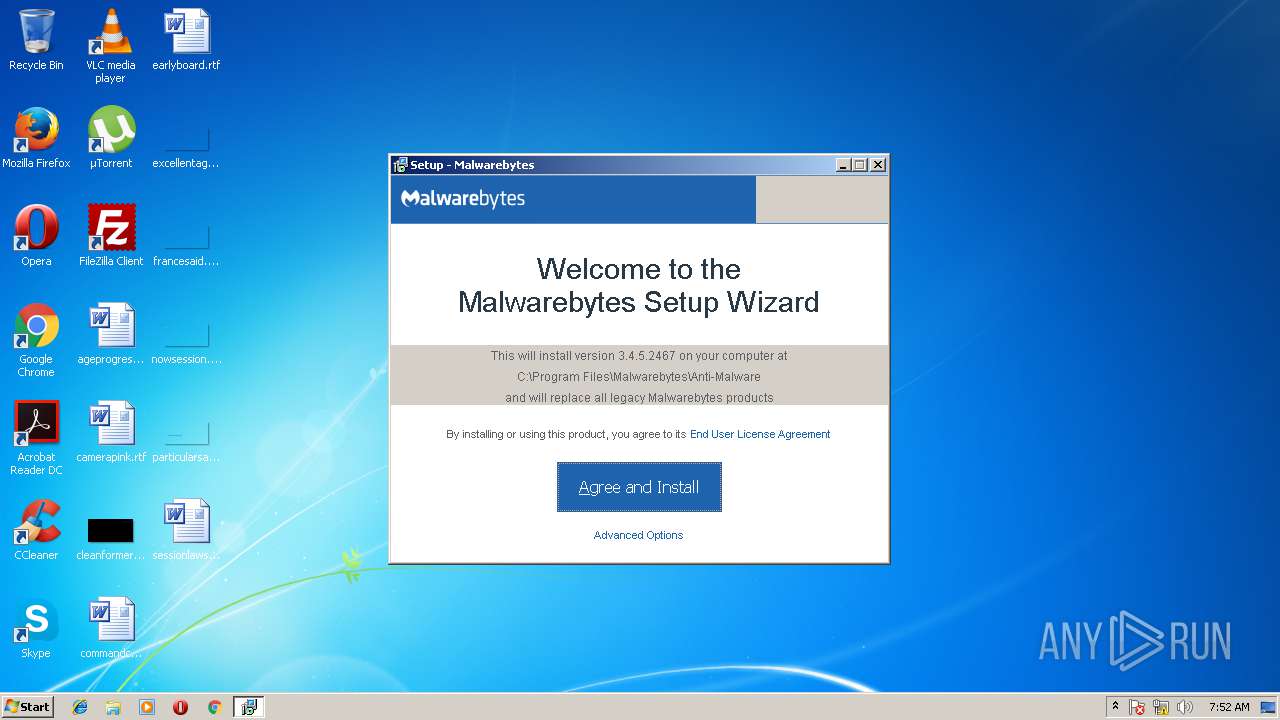
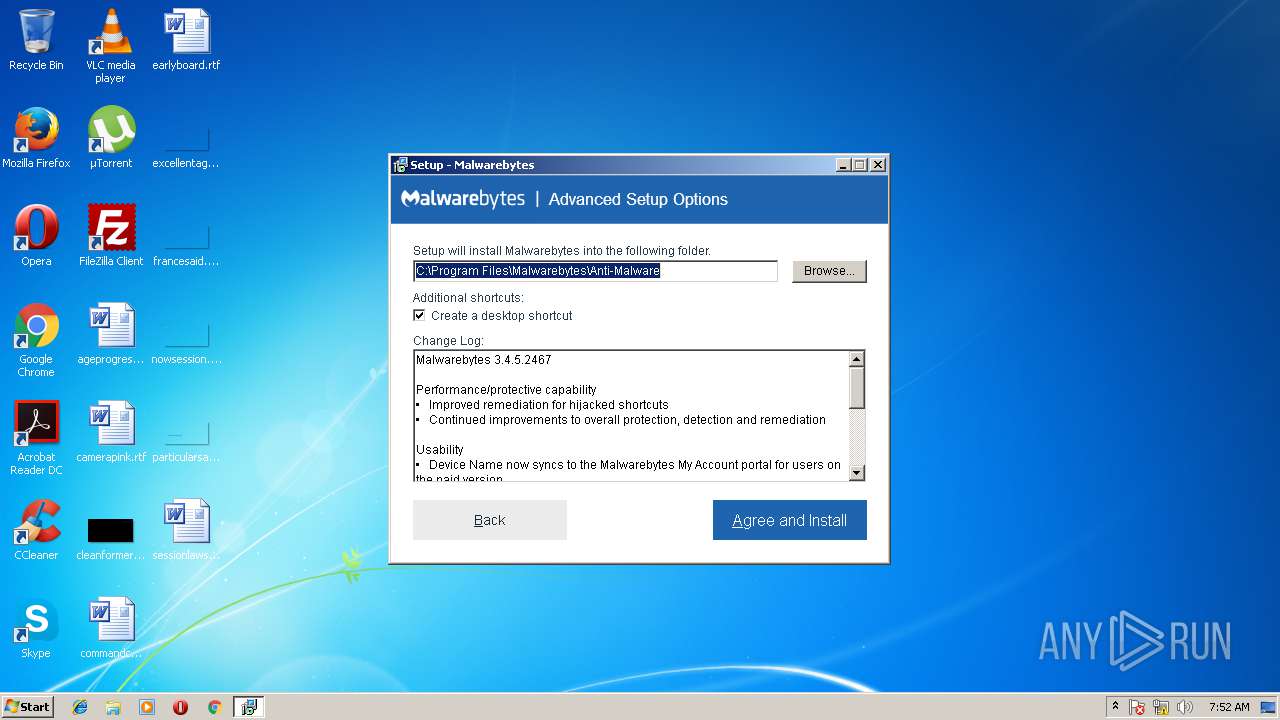
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2018, 06:51:03 |
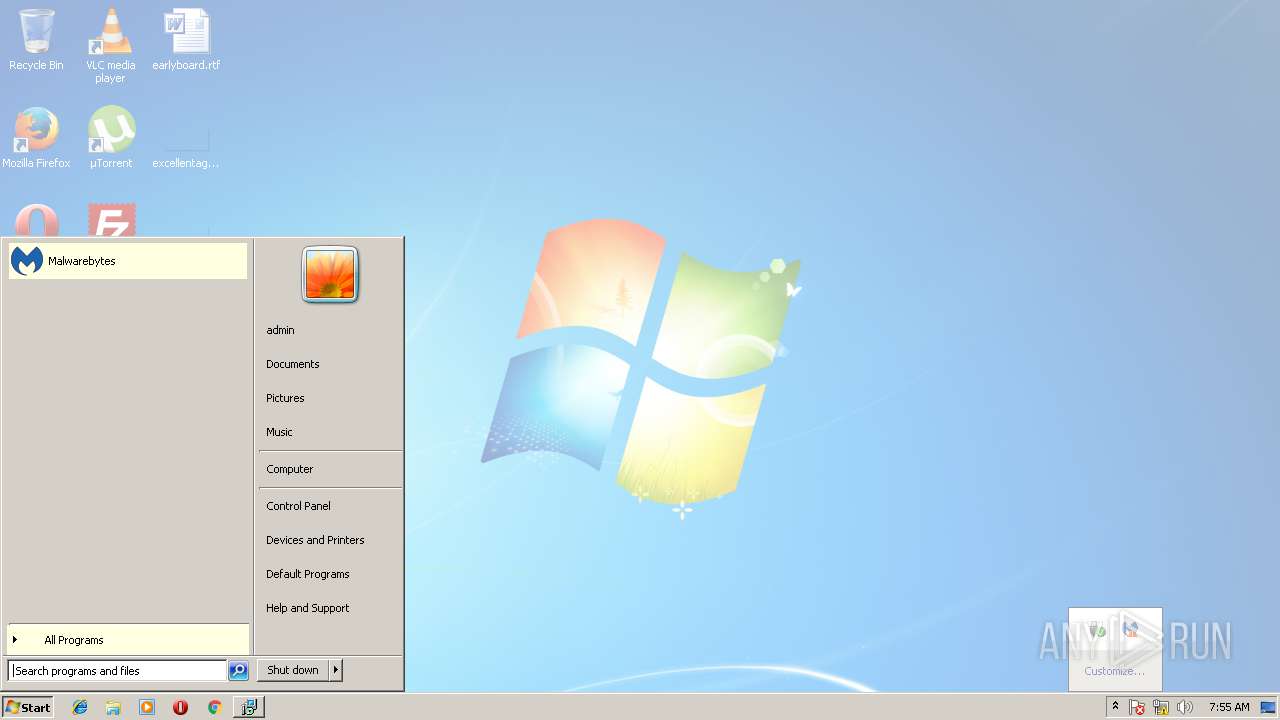
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7D8B9CB0727616D7B16935B29B70B56D |
| SHA1: | 5BA64C7345D2882023704998FBD1648F487F3B22 |
| SHA256: | 6DB8E34B95C755618667F4DAAF7956B9BF38B61F0BC0D72B43975C7A22098F73 |
| SSDEEP: | 12288:nFVqrbuBF1U3QDJcldvhTt8r3gxQ2HsbhSjlmXPu0oUf:nmnuBF1U3QDJcldvhlxQ2HsbhSRmXPz5 |
MALICIOUS
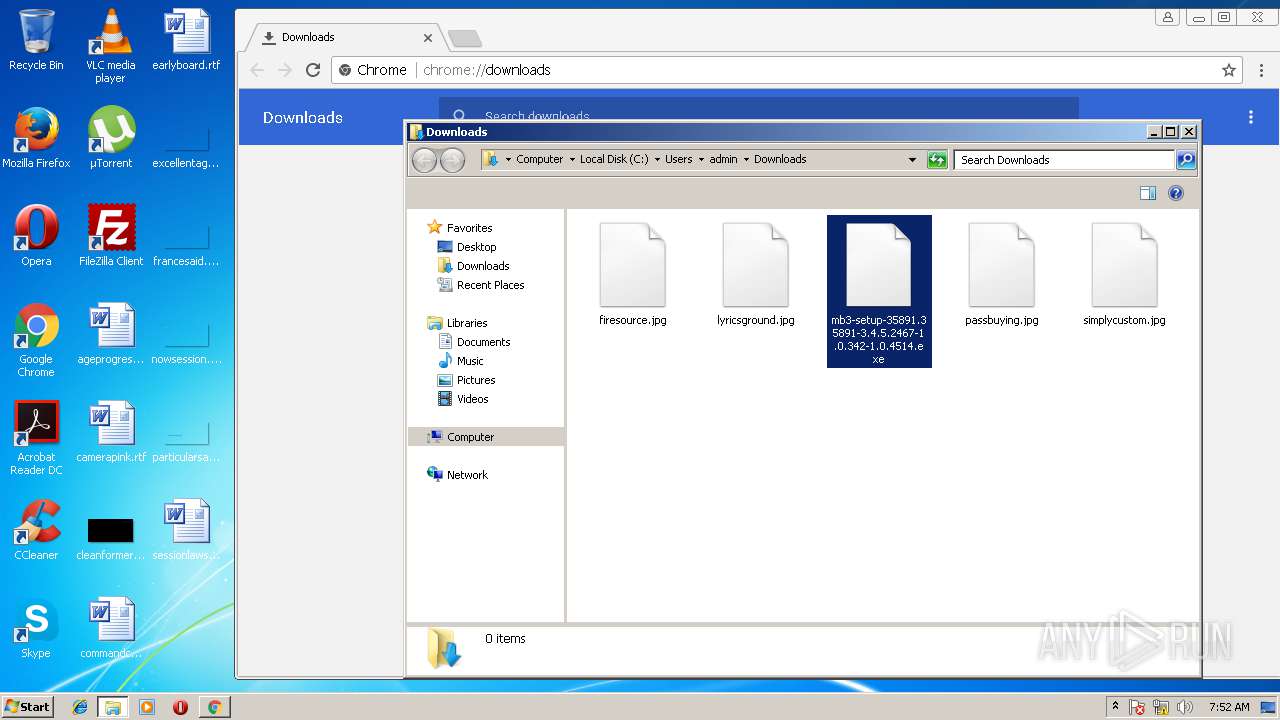
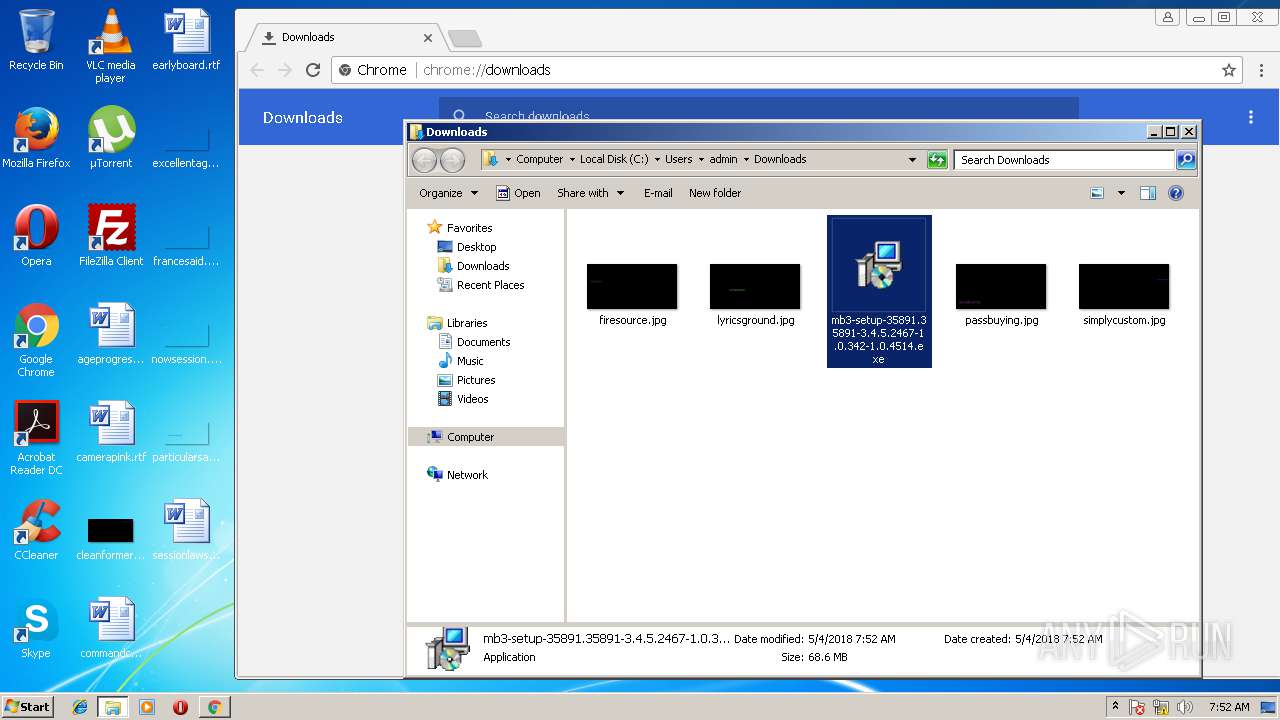
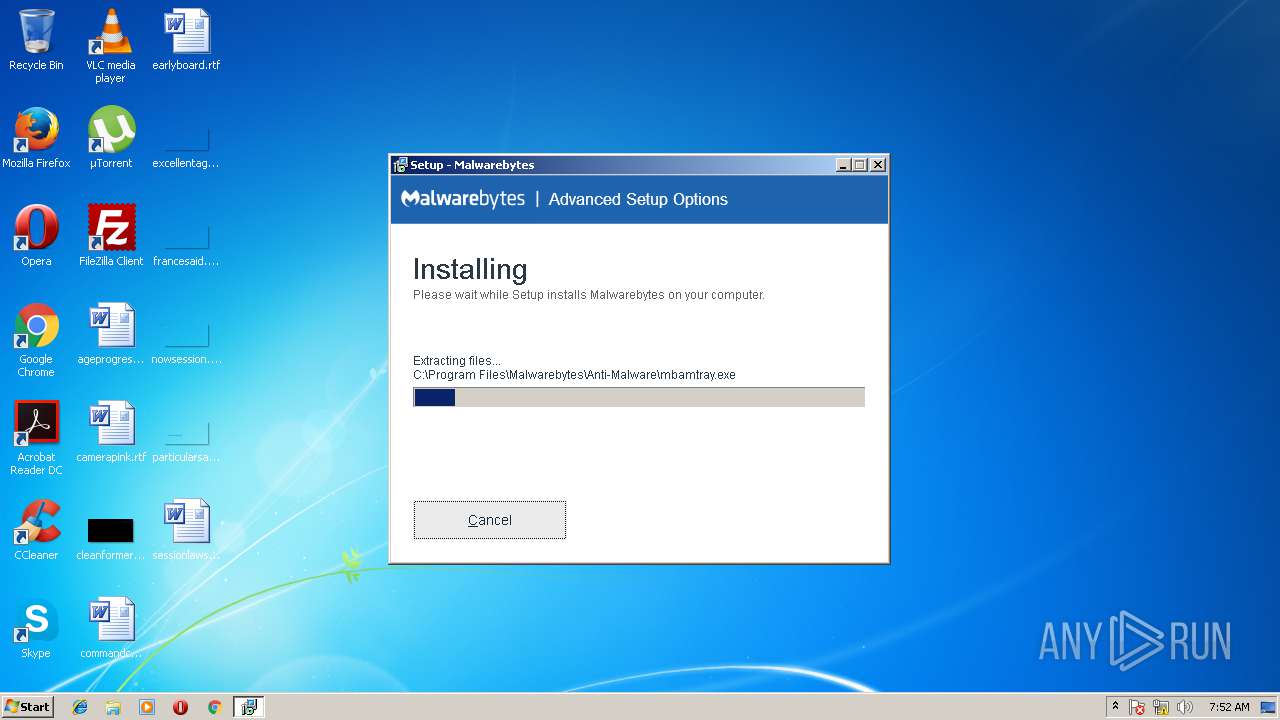
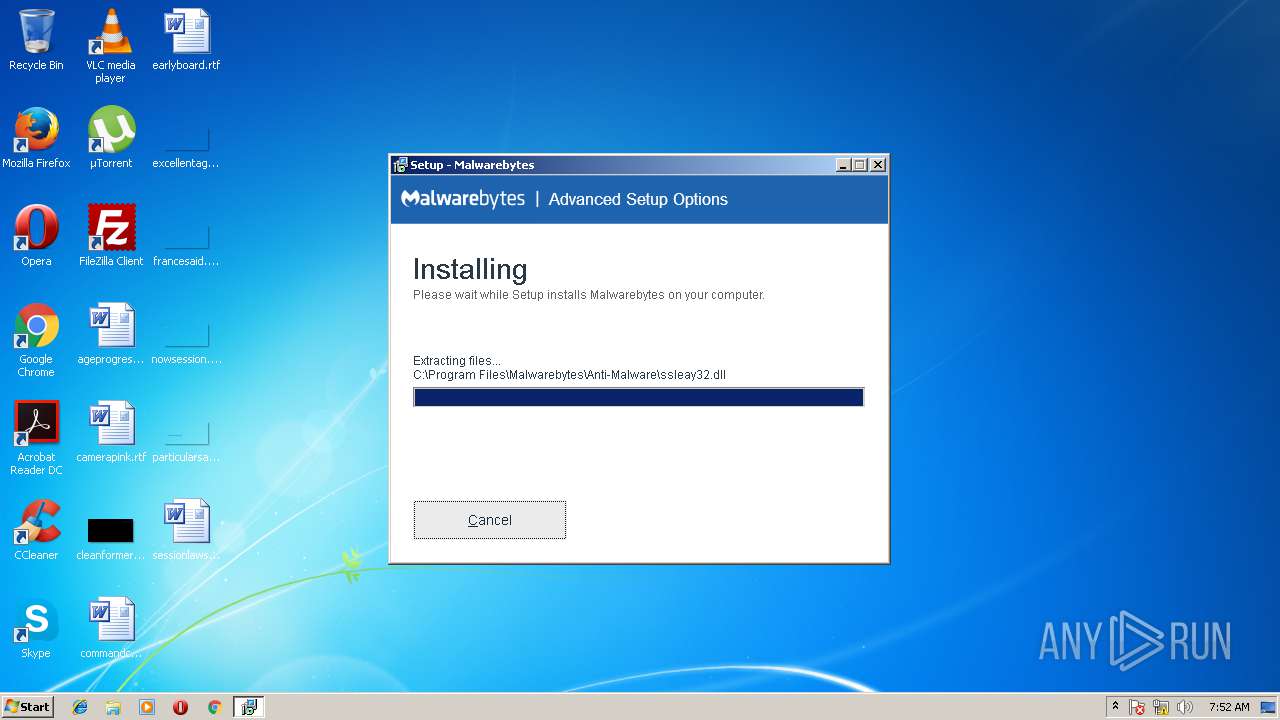
Application was dropped or rewritten from another process
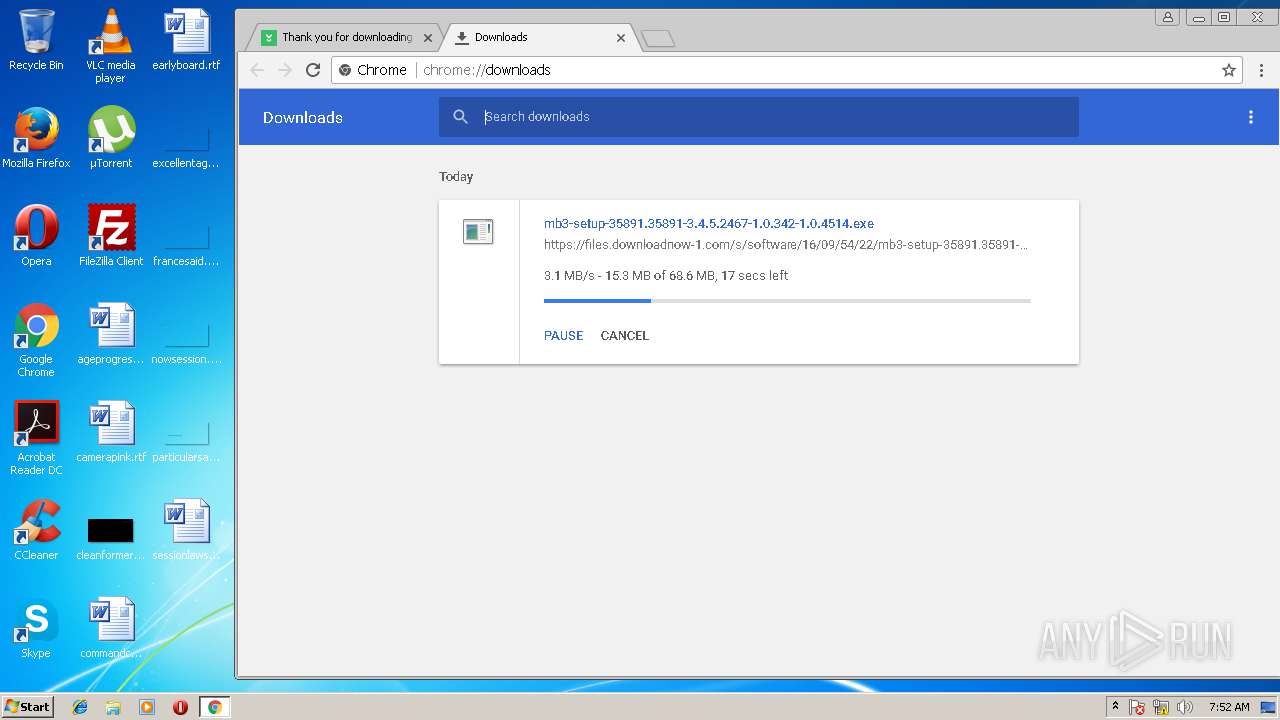
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.exe (PID: 3328)
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.exe (PID: 3268)
- mbamtray.exe (PID: 2452)
- mbamservice.exe (PID: 3960)
- mbamservice.exe (PID: 3488)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 3208)
Changes settings of System certificates
- certutil.exe (PID: 1632)
- certutil.exe (PID: 3272)
Application loaded dropped or rewritten executable
- mbamservice.exe (PID: 3488)
- mbamtray.exe (PID: 2452)
Changes internet zones settings
- mbamservice.exe (PID: 3488)
SUSPICIOUS
Application launched itself
- software_reporter_tool.exe (PID: 3208)
Creates files in the Windows directory
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
- certutil.exe (PID: 3272)
- certutil.exe (PID: 1632)
- mbamservice.exe (PID: 3488)
Creates files in the driver directory
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
- mbamservice.exe (PID: 3488)
Reads the Windows organization settings
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
Creates files in the user directory
- chrome.exe (PID: 2420)
Reads Windows owner settings
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
Changes IE settings (feature browser emulation)
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
Modifies the open verb of a shell class
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
Removes files from Windows directory
- certutil.exe (PID: 1632)
- certutil.exe (PID: 3272)
- mbamservice.exe (PID: 3488)
Creates or modifies windows services
- mbamservice.exe (PID: 3960)
- mbamservice.exe (PID: 3488)
Creates files in the program directory
- mbamservice.exe (PID: 3488)
Creates COM task schedule object
- mbamservice.exe (PID: 3488)
Searches for installed software
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
INFO
Application launched itself
- chrome.exe (PID: 2420)
Application loaded dropped or rewritten executable
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
Changes settings of System certificates
- chrome.exe (PID: 2420)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2420)
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
- mbamservice.exe (PID: 3488)
Application was dropped or rewritten from another process
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 2128)
Creates a software uninstall entry
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
Dropped object may contain URL's
- chrome.exe (PID: 2420)
- mbamservice.exe (PID: 3488)
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
Creates files in the program directory
- mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp (PID: 3520)
Reads settings of System Certificates
- mbamservice.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:11:30 09:56:03+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 412672 |
| InitializedDataSize: | 195584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3fbda |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.7.3.1 |
| ProductVersionNumber: | 1.7.3.1 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
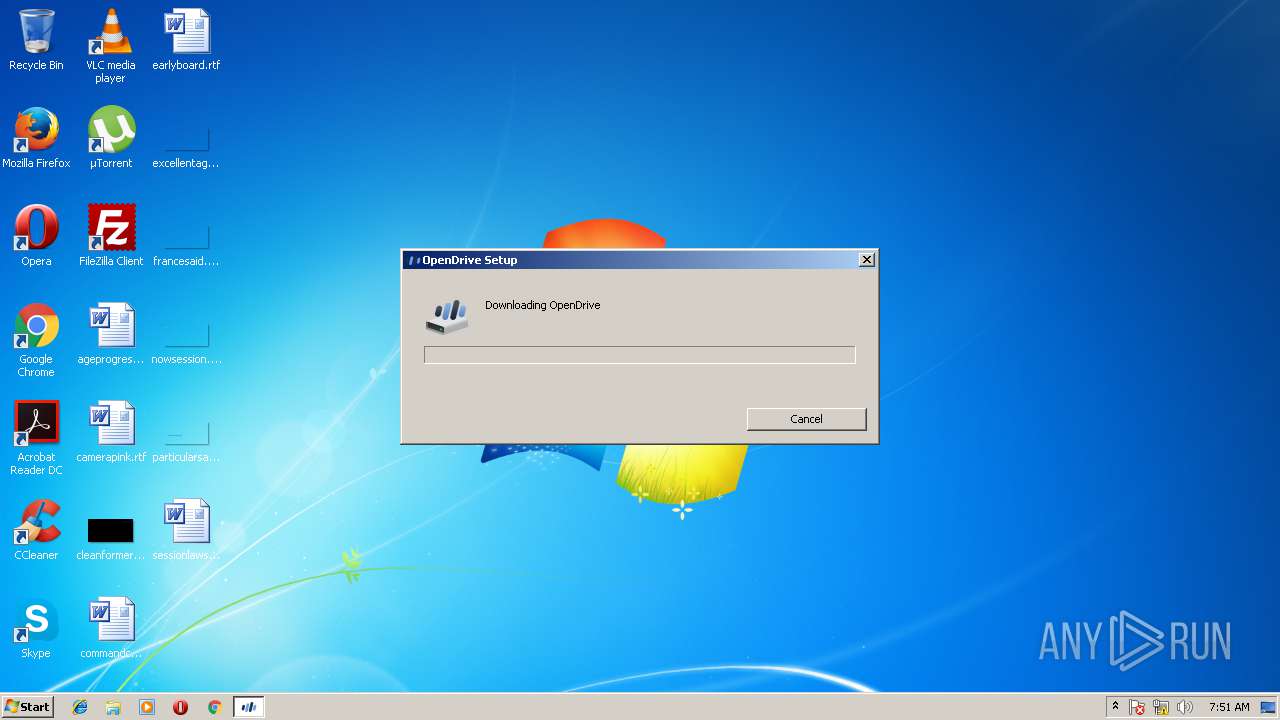
| CompanyName: | OpenDrive Inc. |
| FileDescription: | OpenDrive Drive Setup Bootstrapper |
| FileVersion: | 1,7,3,1 |
| InternalName: | OpenDrive Drive Setup Bootstrapper |
| LegalCopyright: | Copyright (c)OpenDrive Inc. 2017 |
| OriginalFileName: | Setup.exe |
| ProductName: | OpenDrive Drive for Windows |
| ProductVersion: | 1,7,3,1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Nov-2017 08:56:03 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | OpenDrive Inc. |
| FileDescription: | OpenDrive Drive Setup Bootstrapper |
| FileVersion: | 1,7,3,1 |
| InternalName: | OpenDrive Drive Setup Bootstrapper |
| LegalCopyright: | Copyright (c)OpenDrive Inc. 2017 |
| OriginalFilename: | Setup.exe |
| ProductName: | OpenDrive Drive for Windows |
| ProductVersion: | 1,7,3,1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 30-Nov-2017 08:56:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00064AE6 | 0x00064C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.595 |
.rdata | 0x00066000 | 0x0001B89A | 0x0001BA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05987 |
.data | 0x00082000 | 0x000045CC | 0x00003600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.64909 |
.gfids | 0x00087000 | 0x000007A4 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.92405 |
.tls | 0x00088000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00089000 | 0x00008BA0 | 0x00008C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.98827 |
.reloc | 0x00092000 | 0x00006588 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.57891 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06216 | 651 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.28649 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.52982 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.70079 | 2440 | UNKNOWN | English - United States | RT_ICON |
5 | 2.92489 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.61476 | 9640 | UNKNOWN | English - United States | RT_ICON |
101 | 2.64638 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
102 | 2.0815 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
313 | 3.02219 | 628 | UNKNOWN | English - United States | RT_STRING |
319 | 3.15623 | 332 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
65
Monitored processes
23
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1612,10034190741378799504,670375284918697755,131072 --service-pipe-token=4075EC33A5994EC2A4DD6BC3833FB4C7 --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=4075EC33A5994EC2A4DD6BC3833FB4C7 --renderer-client-id=4 --mojo-platform-channel-handle=1624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 1632 | "certutil.exe" -f -addStore root "C:\Users\admin\AppData\Local\Temp\is-3PENL.tmp\DigiCertEVRoot.crt" | C:\Windows\system32\certutil.exe | — | mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2128 | "C:\Users\admin\AppData\Local\Temp\is-T7OQK.tmp\mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp" /SL5="$301D4,71401317,119296,C:\Users\admin\Downloads\mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.exe" | C:\Users\admin\AppData\Local\Temp\is-T7OQK.tmp\mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.tmp | — | mb3-setup-35891.35891-3.4.5.2467-1.0.342-1.0.4514.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2316 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Company: OpenDrive Inc. Integrity Level: HIGH Description: OpenDrive Drive Setup Bootstrapper Exit code: 1602 Version: 1,7,3,1 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Malwarebytes\Anti-Malware\mbamtray.exe" | C:\Program Files\Malwarebytes\Anti-Malware\mbamtray.exe | mbamservice.exe | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: Malwarebytes Tray Application Exit code: 0 Version: 3.0.0.1429 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2168 --on-initialized-event-handle=296 --parent-handle=300 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1612,10034190741378799504,670375284918697755,131072 --disable-direct-composition --use-gl=swiftshader-webgl --supports-dual-gpus=false --gpu-driver-bug-workarounds=9,12,13,22,23,24,27,49,84 --disable-gl-extensions="GL_KHR_blend_equation_advanced GL_KHR_blend_equation_advanced_coherent" --disable-accelerated-video-decode --gpu-vendor-id=0x1234 --gpu-device-id=0x1111 --gpu-driver-vendor="Google Inc." --gpu-driver-version=3.3.0.2 --gpu-driver-date=2017/04/07 --service-request-channel-token=BCABD84A89C573E9DF326118897340BC --mojo-platform-channel-handle=3336 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1612,10034190741378799504,670375284918697755,131072 --service-pipe-token=CF0B29C39E3DED17FB1D8D22D0D48788 --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=CF0B29C39E3DED17FB1D8D22D0D48788 --renderer-client-id=7 --mojo-platform-channel-handle=3828 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 2776 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: OpenDrive Inc. Integrity Level: MEDIUM Description: OpenDrive Drive Setup Bootstrapper Exit code: 3221226540 Version: 1,7,3,1 Modules
| |||||||||||||||
Total events
2 994
Read events
1 590
Write events
1 384
Delete events
20
Modification events
| (PID) Process: | (2316) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\setup_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2316) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\setup_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2316) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\setup_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2316) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\setup_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2316) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\setup_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2316) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\setup_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2316) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\setup_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2316) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\setup_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2316) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\setup_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2316) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\setup_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
97
Suspicious files
144
Text files
144
Unknown types
52
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2316 | setup.exe | C:\Users\admin\AppData\Local\Temp\OpenDrive\49B20A5A.msi | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000038.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c947a25c-94d2-4a65-ab57-c473a456ce33.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\b5828dd7cc3b943f8890a5bb6e3b1b63e8ee8703\index.txt.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\b5828dd7cc3b943f8890a5bb6e3b1b63e8ee8703\1c4bf5a9-d74e-4240-bf2b-8567d0555f90\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\ScriptCache\4cb013792b196a35_0 | binary | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\IndexedDB\https_www.google.ru_0.indexeddb.leveldb\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2316 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JZR4RKAB\OpenDrive_Setup_1_7_3_8[1].msi | binary | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFfc450.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
78
TCP/UDP connections
192
DNS requests
102
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
— | — | GET | — | 38.108.185.63:80 | http://aw2.opendrive.com/releases/win/OpenDrive_Setup_1_7_3_8.msi | US | — | — | suspicious |
— | — | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
— | — | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
— | — | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
— | — | GET | 302 | 2.16.186.80:80 | http://b.scorecardresearch.com/b?c1=2&c2=3005086&rn=0.09864170303386244&c7=http%3A%2F%2Fdownload.cnet.com%2Fmalwarebytes-anti-malware%2Fwindows.html%3Fhlndr%3D1%26part%3Ddl-x%26lang%3Des&c3=&c4=3000086&c5=&c6=&c15=&c16=&c8=Bienvenidos%20usuarios%20de%20Malwarebytes&c9=&cv=1.6 | unknown | — | — | whitelisted |
— | — | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
— | — | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
— | — | GET | 302 | 138.108.96.100:80 | http://secure-us.imrworldwide.com/cgi-bin/m?ci=us-304254h&cg=0&cc=1&si=http%3A//download.cnet.com/malwarebytes-anti-malware/windows.html%3Fhlndr%3D1%26part%3Ddl-x%26lang%3Des&rp=&ts=compact&rnd=1525416720946 | US | — | — | whitelisted |
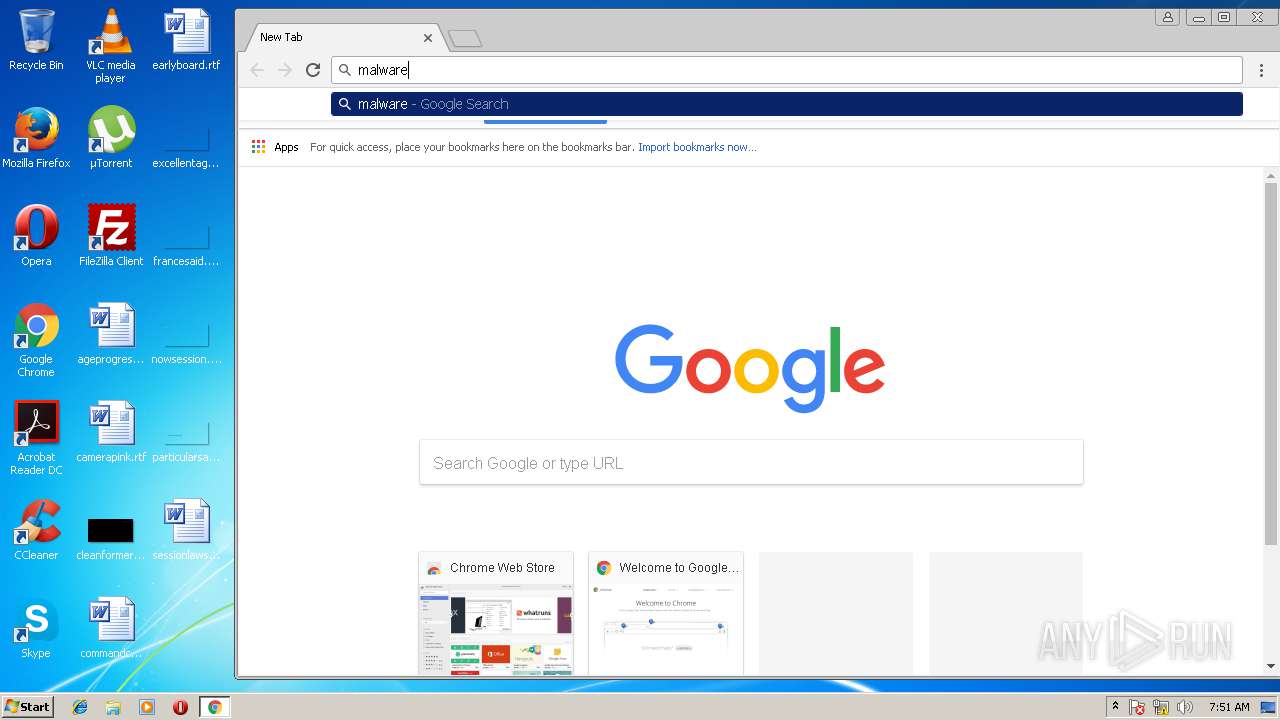
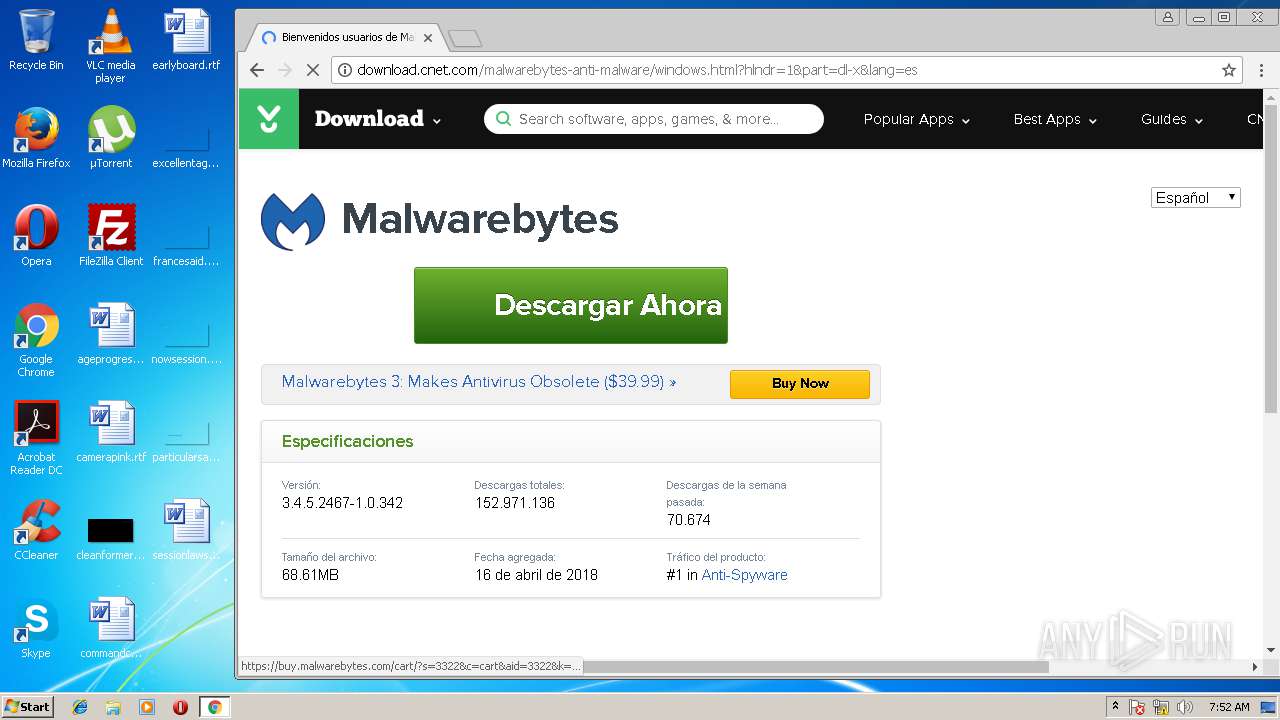
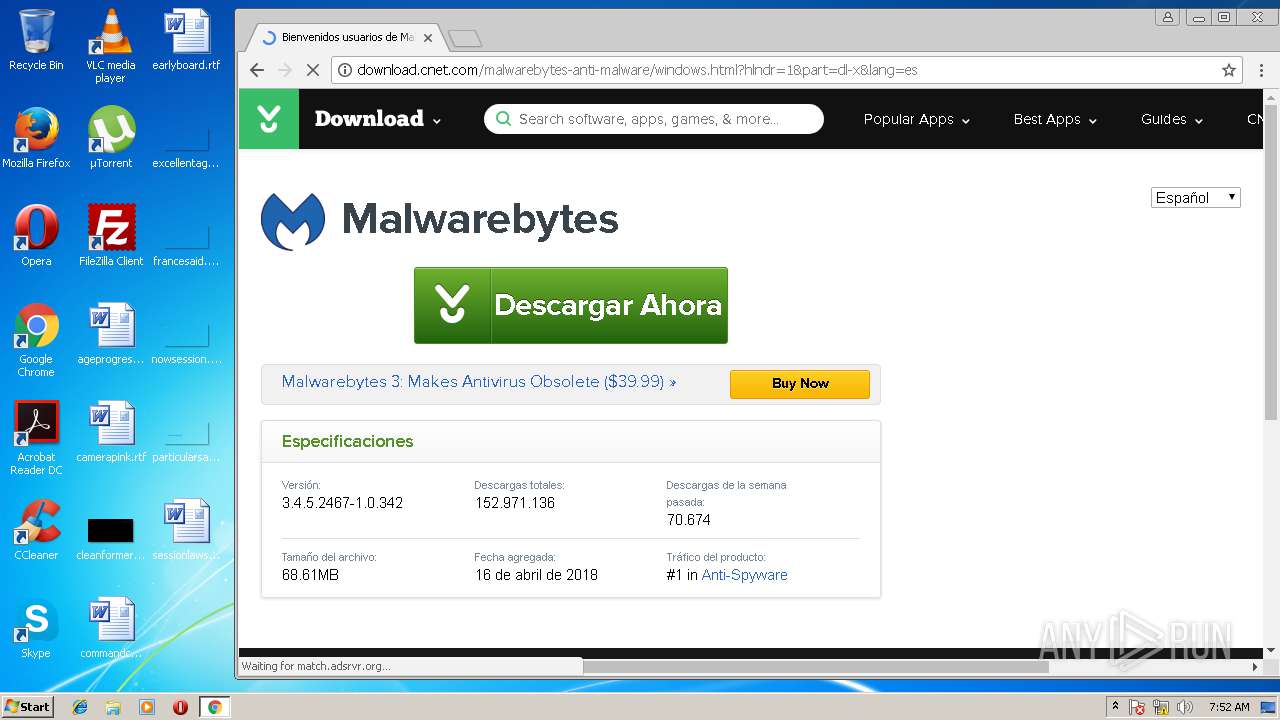
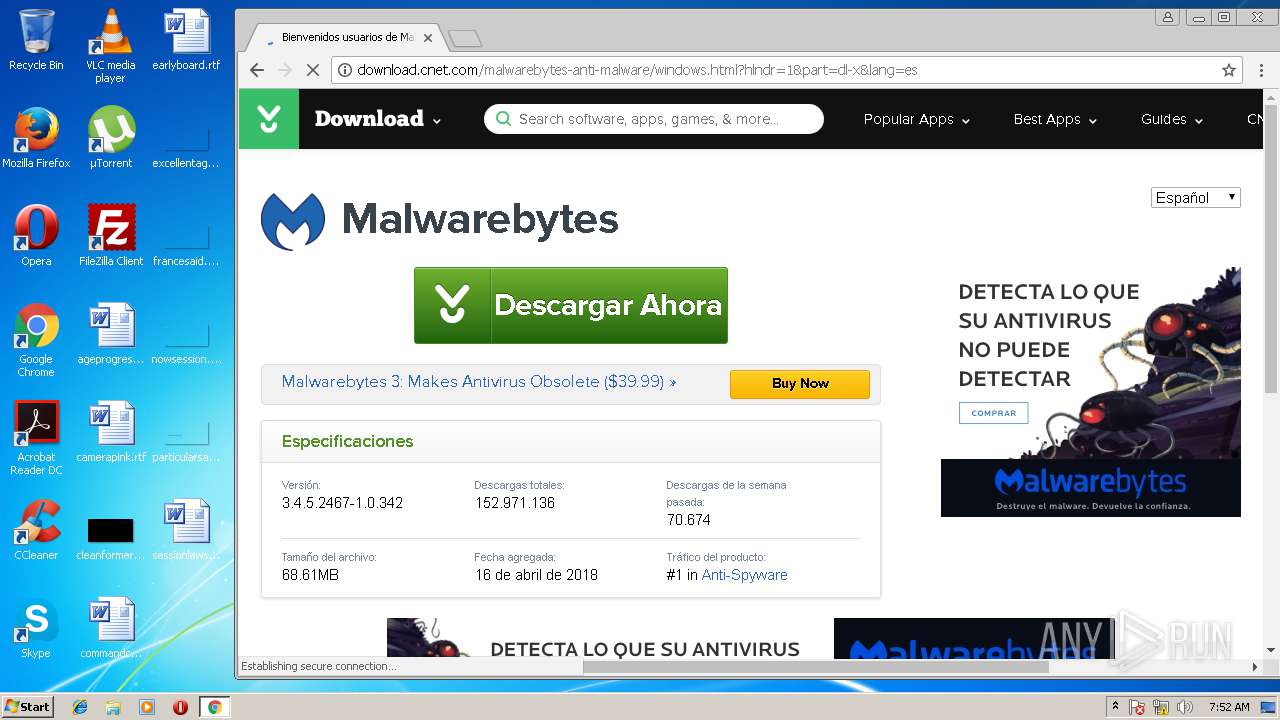
— | — | GET | 200 | 172.227.114.64:80 | http://download.cnet.com/malwarebytes-anti-malware/windows.html?hlndr=1&part=dl-x&lang=es | US | html | 32.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 38.108.185.63:80 | aw2.opendrive.com | Cogent Communications | US | suspicious |
— | — | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.163:443 | www.google.ru | Google Inc. | US | whitelisted |
— | — | 216.58.208.42:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.78:443 | apis.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.74:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
— | — | 23.23.98.158:443 | 262855726.log.optimizely.com | Amazon.com, Inc. | US | unknown |
— | — | 184.30.214.147:443 | cdn3.optimizely.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
aw2.opendrive.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
www.google.ru |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
mbamtray.exe | QAxBase::setControl: requested control {F36AD0D0-B5F0-4C69-AF08-603D177FEF0E} could not be instantiated
|
mbamtray.exe | Code : 16389
|
mbamtray.exe | Code : 16389
|
mbamtray.exe | Source :
|
mbamtray.exe | Description:
|
mbamtray.exe | Help :
|
mbamtray.exe | Connect to the exception(int,QString,QString,QString) signal to catch this exception
|
mbamtray.exe | void __thiscall TrayLicenseNotificationsModel::CheckRenewLink(void) : Renewal Link: ""
|
mbamtray.exe | "2018-05-04T07:52:59" void __thiscall TrayLicenseNotificationsModel::OnConfigUpdated(void) LicenseController has sent a config update notification!
|
mbamtray.exe | "2018-05-04T07:53:01" void __thiscall TrayLicenseNotificationsModel::OnConfigUpdated(void) LicenseController has sent a config update notification!
|