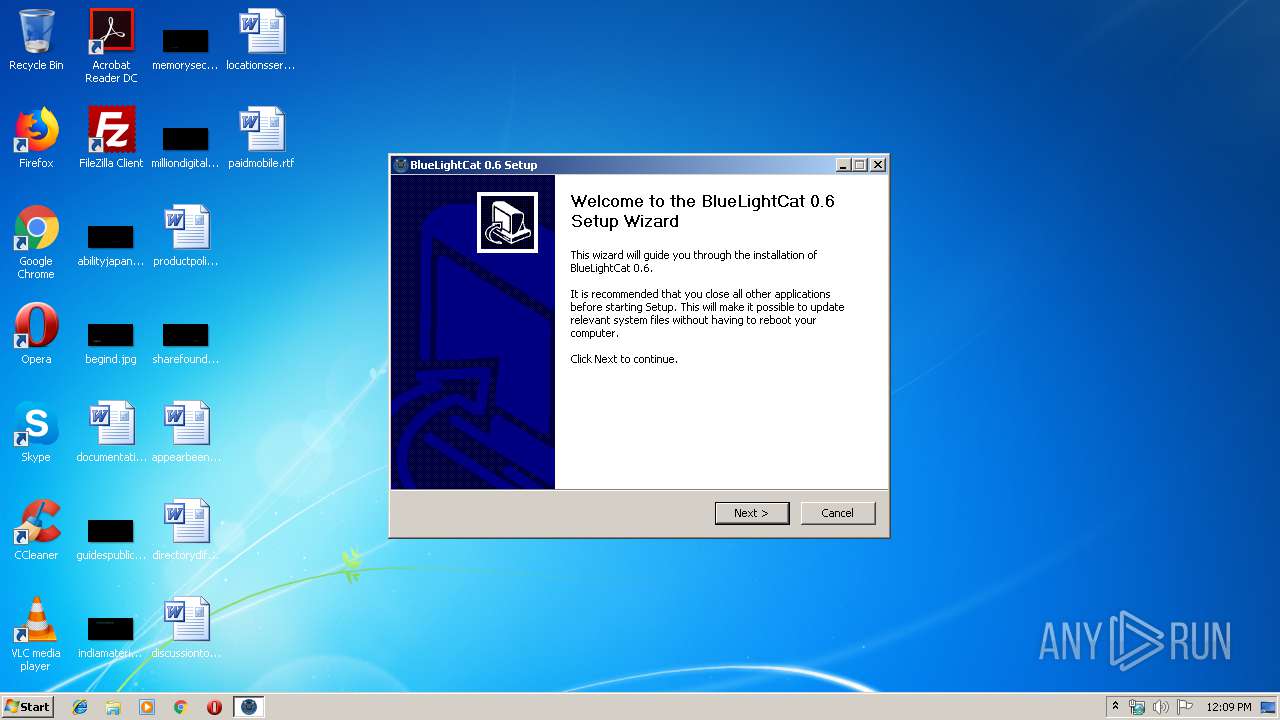
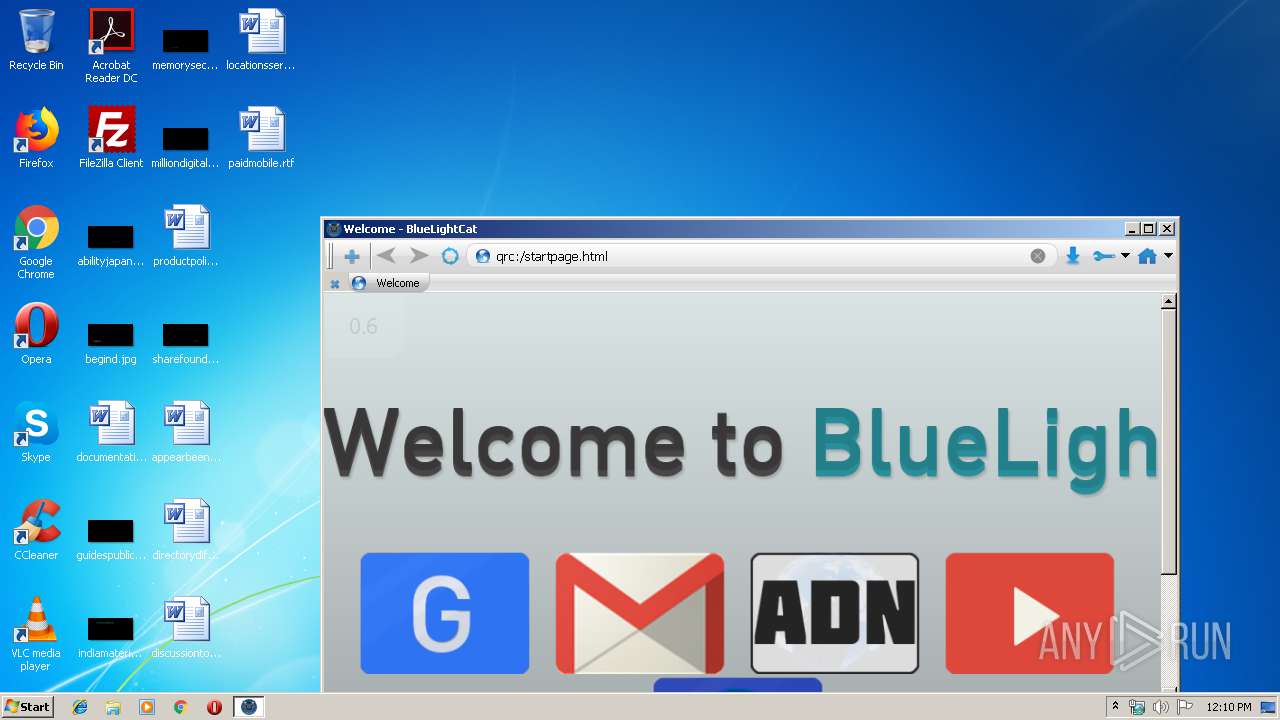
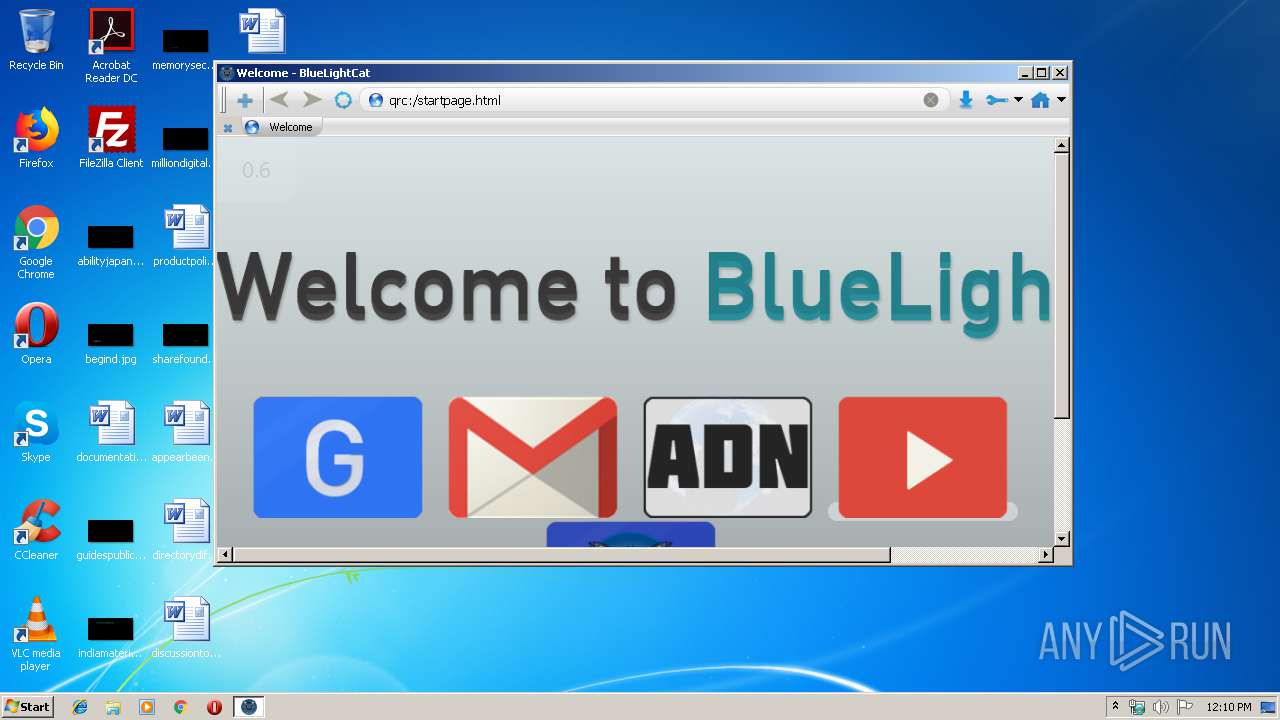
| File name: | BlueLightCat 0.6 Installer.exe |
| Full analysis: | https://app.any.run/tasks/bb821cfb-0354-4e2f-9995-ab1d6f1c9fbb |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2019, 12:09:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | BB5DD5686C57DD7396088641665777EF |
| SHA1: | B0EC15ECEC5E896DDB650C3A38E77ECFA99B8DD2 |
| SHA256: | 6DA8BA2D25B50503FD3E429D62BA945E14BF543FBFA8592E2CDB3238CA09EB2F |
| SSDEEP: | 196608:OaMORRWPfnKeW7yUN5ZpOvIjtZ5g4dV0U1eATdw04SMDAXujhcPq:O5ORQPftYZpOvsbgredf+zv |
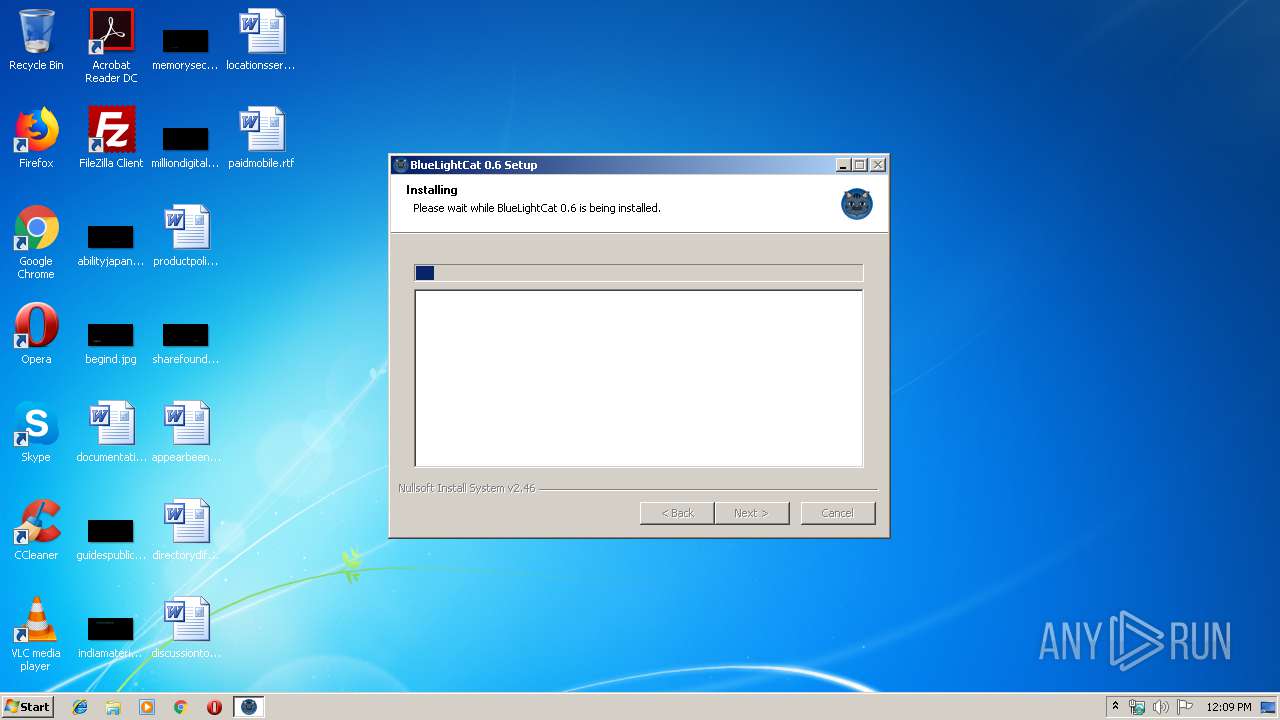
MALICIOUS
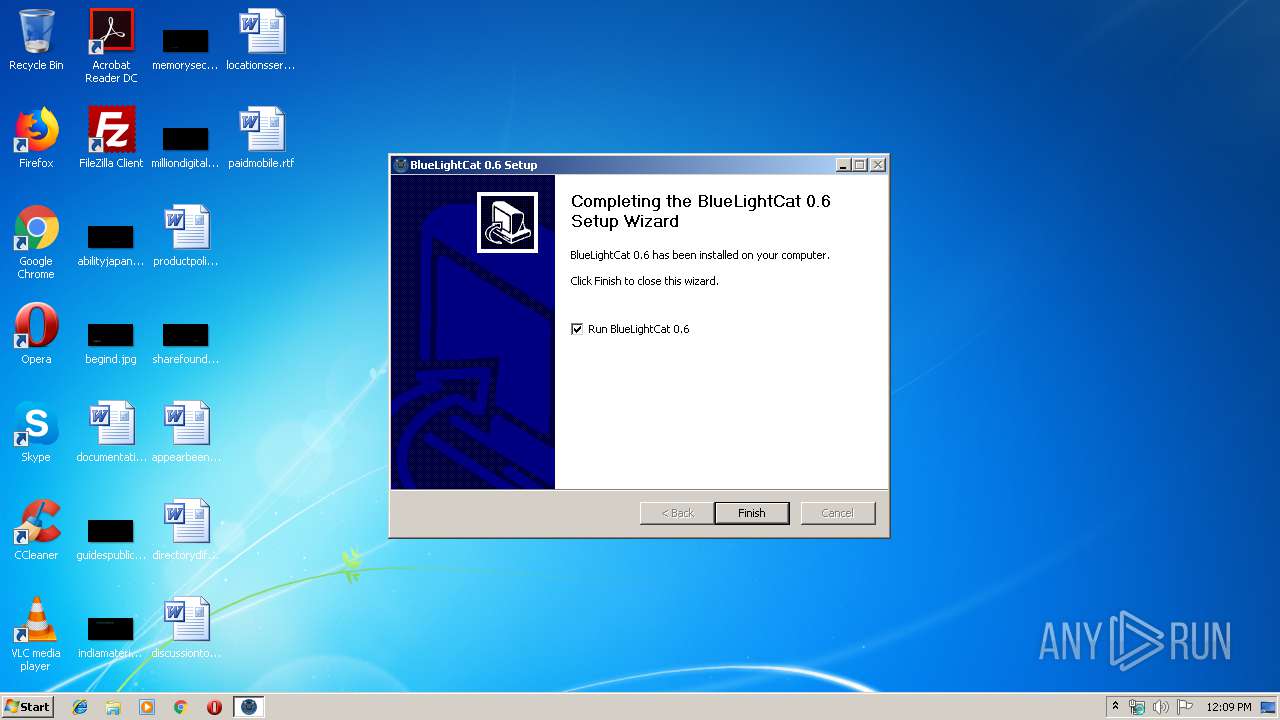
Loads dropped or rewritten executable
- BlueLightCat 0.6 Installer.exe (PID: 2956)
- bluelightcat.exe (PID: 1640)
Application was dropped or rewritten from another process
- bluelightcat.exe (PID: 1640)
SUSPICIOUS
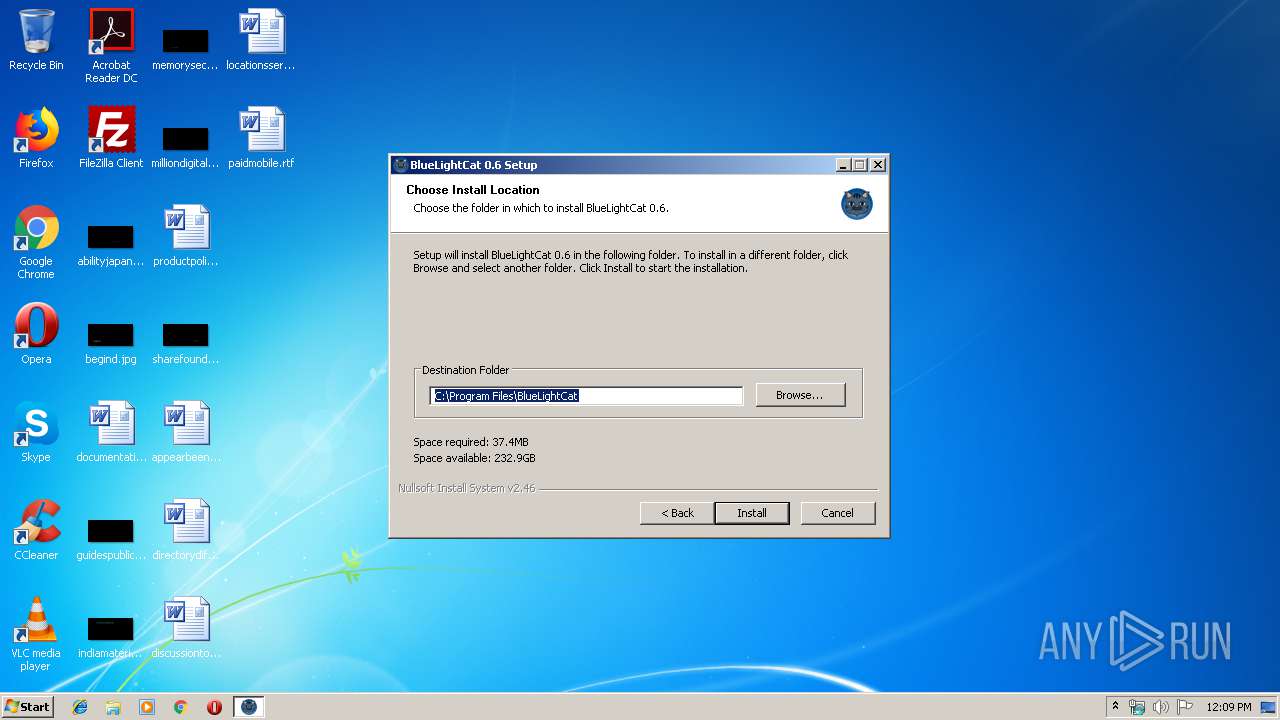
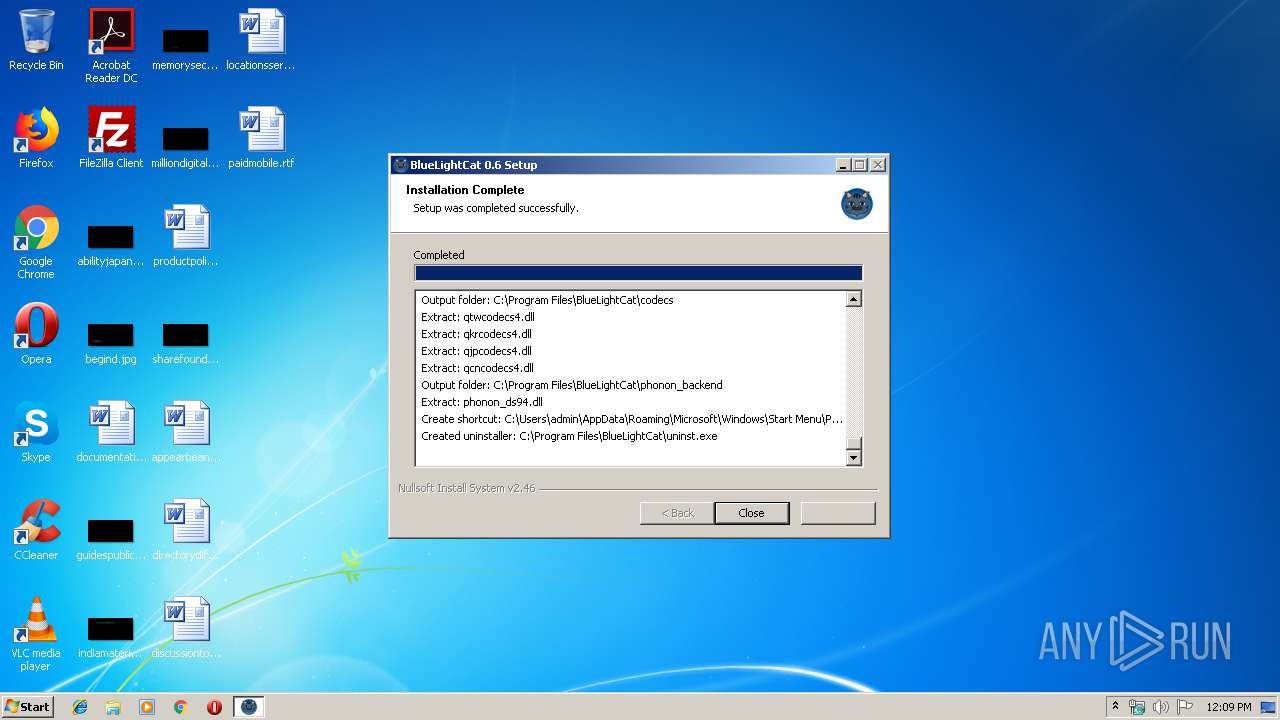
Creates a software uninstall entry
- BlueLightCat 0.6 Installer.exe (PID: 2956)
Executable content was dropped or overwritten
- BlueLightCat 0.6 Installer.exe (PID: 2956)
Creates files in the program directory
- BlueLightCat 0.6 Installer.exe (PID: 2956)
INFO
Dropped object may contain Bitcoin addresses
- BlueLightCat 0.6 Installer.exe (PID: 2956)
- bluelightcat.exe (PID: 1640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002D000 | 0x00056DD0 | 0x00056E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.26497 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.503 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 6.03915 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 6.26654 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 6.3929 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.6474 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
107 | 2.52183 | 160 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
35
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1640 | "C:\Program Files\BlueLightCat\bluelightcat.exe" | C:\Program Files\BlueLightCat\bluelightcat.exe | BlueLightCat 0.6 Installer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2592 | "C:\Users\admin\AppData\Local\Temp\BlueLightCat 0.6 Installer.exe" | C:\Users\admin\AppData\Local\Temp\BlueLightCat 0.6 Installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\Temp\BlueLightCat 0.6 Installer.exe" | C:\Users\admin\AppData\Local\Temp\BlueLightCat 0.6 Installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
429
Read events
374
Write events
55
Delete events
0
Modification events
| (PID) Process: | (2956) BlueLightCat 0.6 Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\bluelightcat.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\BlueLightCat\bluelightcat.exe | |||
| (PID) Process: | (2956) BlueLightCat 0.6 Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BlueLightCat |
| Operation: | write | Name: | DisplayName |
Value: BlueLightCat 0.6 | |||
| (PID) Process: | (2956) BlueLightCat 0.6 Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BlueLightCat |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\BlueLightCat\uninst.exe | |||
| (PID) Process: | (2956) BlueLightCat 0.6 Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BlueLightCat |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\BlueLightCat\bluelightcat.exe | |||
| (PID) Process: | (2956) BlueLightCat 0.6 Installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\BlueLightCat |
| Operation: | write | Name: | DisplayVersion |
Value: 0.6 | |||
| (PID) Process: | (1640) bluelightcat.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Program Files\BlueLightCat\iconengines |
| Operation: | write | Name: | qsvgicon4.dll |
Value: 40800 | |||
| (PID) Process: | (1640) bluelightcat.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Program Files\BlueLightCat\imageformats |
| Operation: | write | Name: | qgif4.dll |
Value: 40800 | |||
| (PID) Process: | (1640) bluelightcat.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Factory Cache 4.8\com.trolltech.Qt.QImageIOHandlerFactoryInterface:\C:\Program Files\BlueLightCat\imageformats |
| Operation: | write | Name: | qgif4.dll |
Value: 2012-03-11T14:31:28 | |||
| (PID) Process: | (1640) bluelightcat.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Plugin Cache 4.8.false\C:\Program Files\BlueLightCat\imageformats |
| Operation: | write | Name: | qico4.dll |
Value: 40800 | |||
| (PID) Process: | (1640) bluelightcat.exe | Key: | HKEY_CURRENT_USER\Software\Trolltech\OrganizationDefaults\Qt Factory Cache 4.8\com.trolltech.Qt.QImageIOHandlerFactoryInterface:\C:\Program Files\BlueLightCat\imageformats |
| Operation: | write | Name: | qico4.dll |
Value: 2012-03-11T14:31:48 | |||
Executable files
26
Suspicious files
82
Text files
12
Unknown types
85
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | BlueLightCat 0.6 Installer.exe | C:\Users\admin\AppData\Local\Temp\nskA030.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2956 | BlueLightCat 0.6 Installer.exe | C:\Program Files\BlueLightCat\htmlToXBel.exe | o | |
MD5:— | SHA256:— | |||
| 2956 | BlueLightCat 0.6 Installer.exe | C:\Program Files\BlueLightCat\bluelightcat-placesimport.exe | o | |
MD5:— | SHA256:— | |||
| 2956 | BlueLightCat 0.6 Installer.exe | C:\Program Files\BlueLightCat\bluelightcat-cacheinfo.exe | o | |
MD5:— | SHA256:— | |||
| 2956 | BlueLightCat 0.6 Installer.exe | C:\Program Files\BlueLightCat\locale\cs_CZ.qm | qm | |
MD5:— | SHA256:— | |||
| 2956 | BlueLightCat 0.6 Installer.exe | C:\Program Files\BlueLightCat\locale\ast.qm | qm | |
MD5:— | SHA256:— | |||
| 2956 | BlueLightCat 0.6 Installer.exe | C:\Users\admin\AppData\Local\Temp\nskA030.tmp\KillProcDLL.dll | executable | |
MD5:83142EAC84475F4CA889C73F10D9C179 | SHA256:AE2F1658656E554F37E6EAC896475A3862841A18FFC6FAD2754E2D3525770729 | |||
| 2956 | BlueLightCat 0.6 Installer.exe | C:\Program Files\BlueLightCat\QtSql4.dll | executable | |
MD5:— | SHA256:— | |||
| 2956 | BlueLightCat 0.6 Installer.exe | C:\Program Files\BlueLightCat\phonon4.dll | executable | |
MD5:— | SHA256:— | |||
| 2956 | BlueLightCat 0.6 Installer.exe | C:\Program Files\BlueLightCat\QtScript4.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
98
TCP/UDP connections
34
DNS requests
18
Threats
0
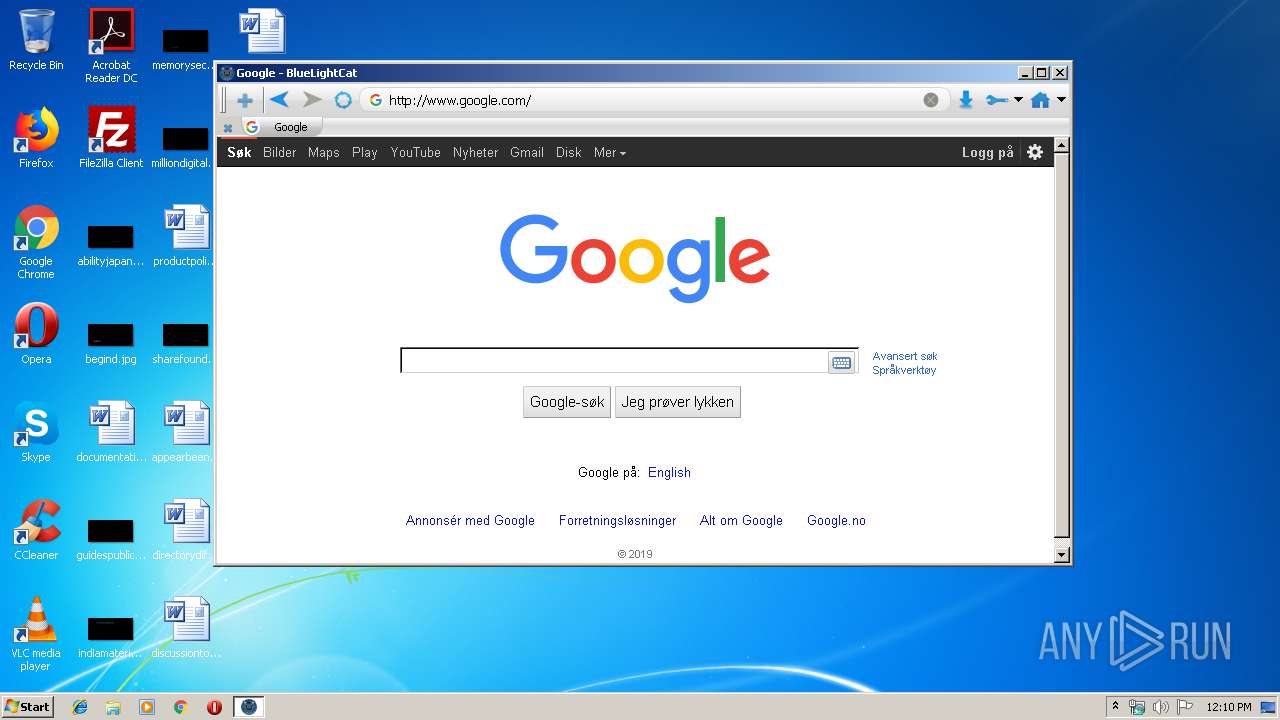
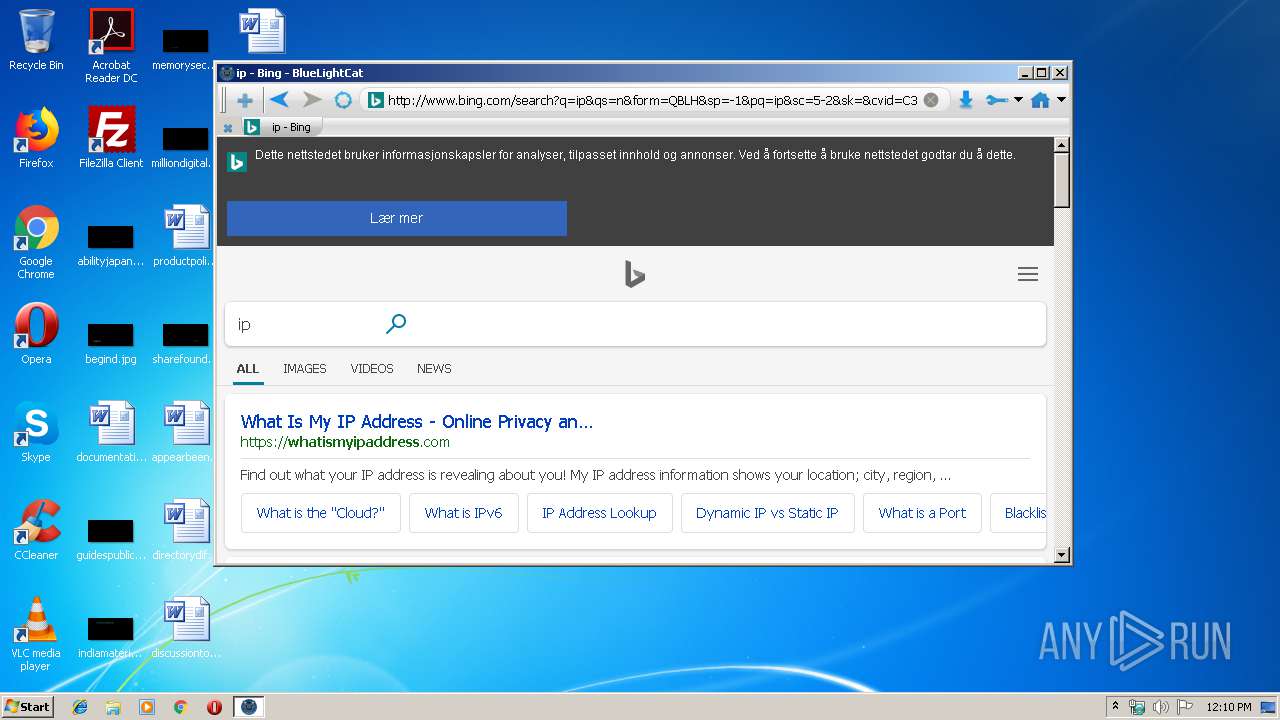
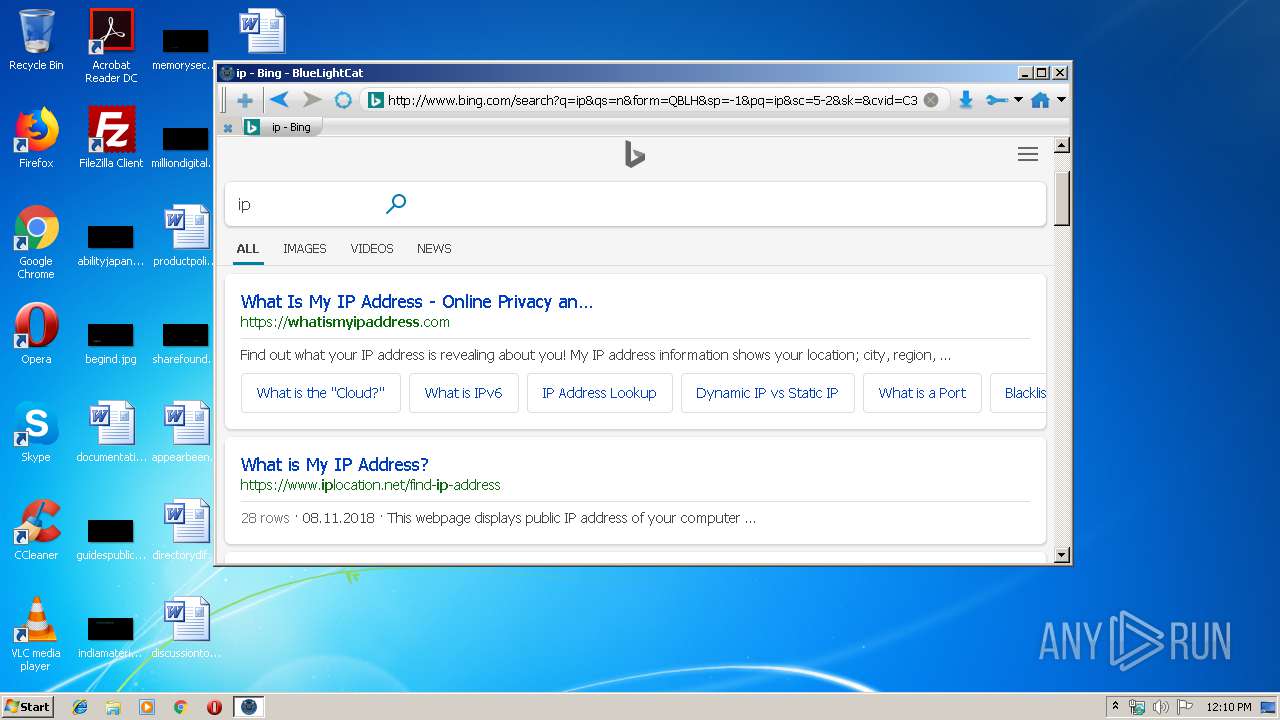
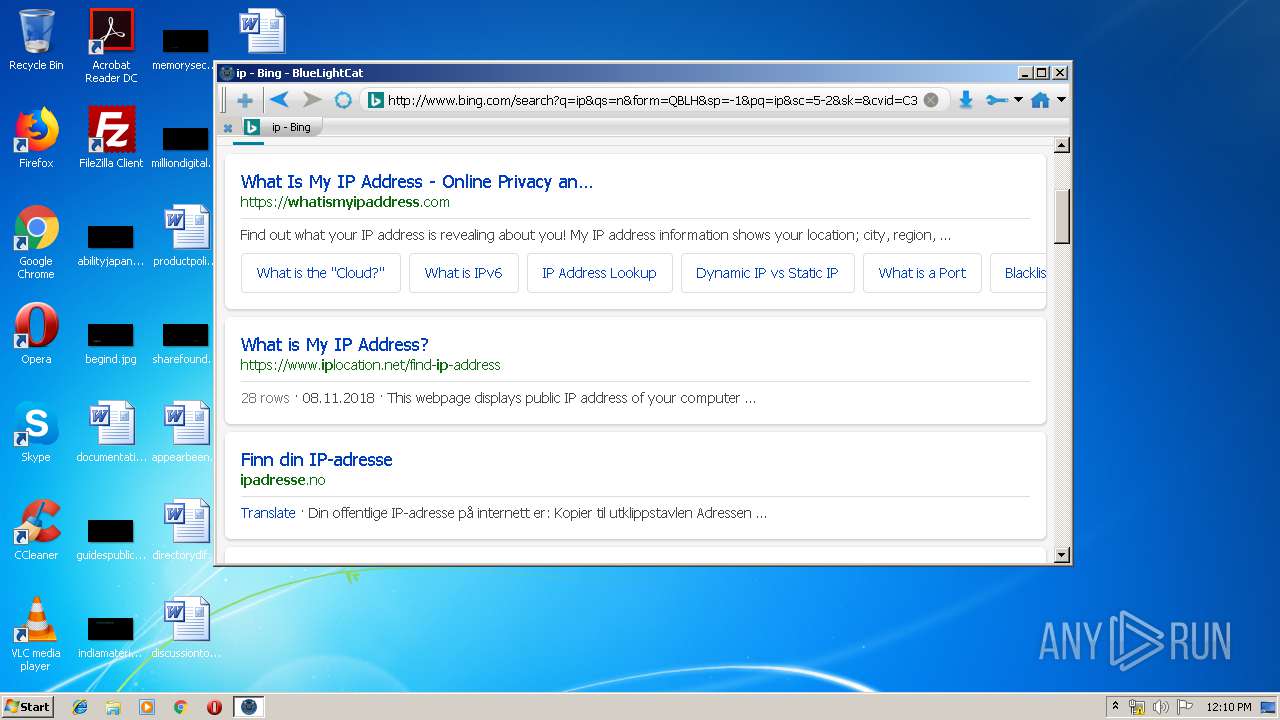
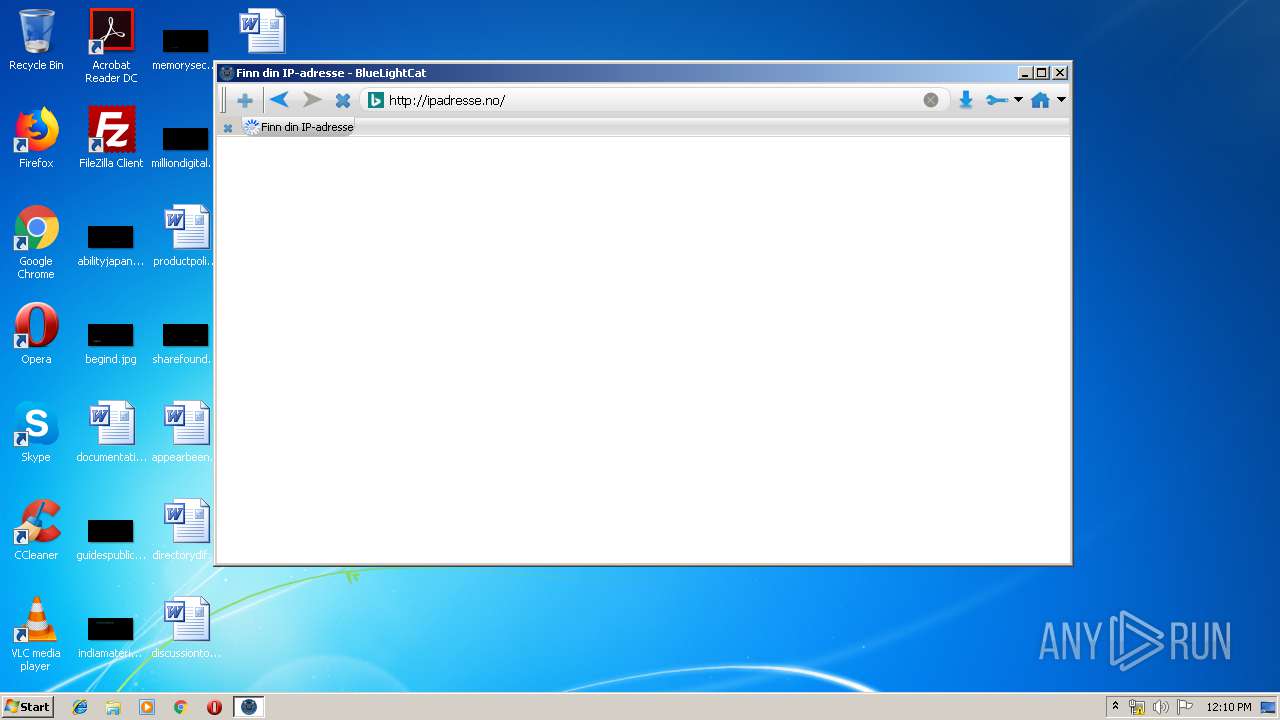
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
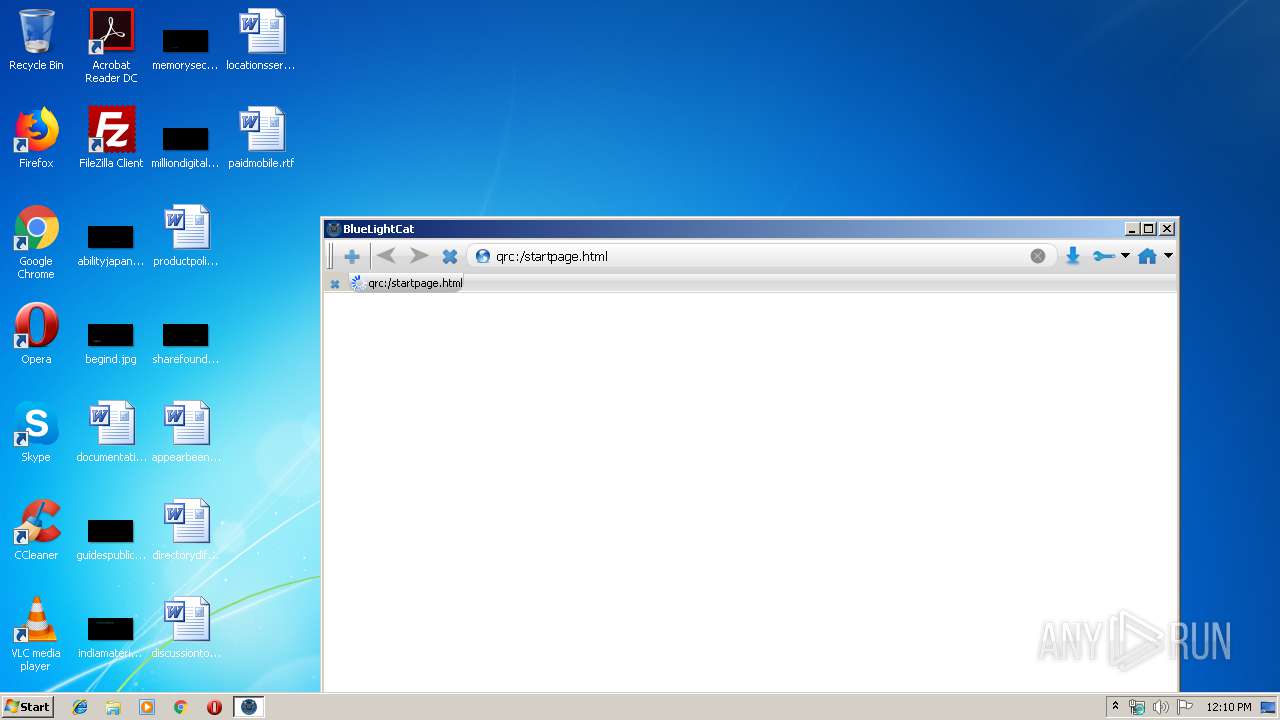
1640 | bluelightcat.exe | GET | — | 216.58.207.36:80 | http://www.google.com/images/branding/googlelogo/1x/googlelogo_white_background_color_272x92dp.png | US | — | — | malicious |
1640 | bluelightcat.exe | GET | 204 | 216.58.207.36:80 | http://www.google.com/client_204?&atyp=i&biw=853&bih=426&ei=ntCUXOvTI4ivkwXN06OoBg | US | — | — | malicious |
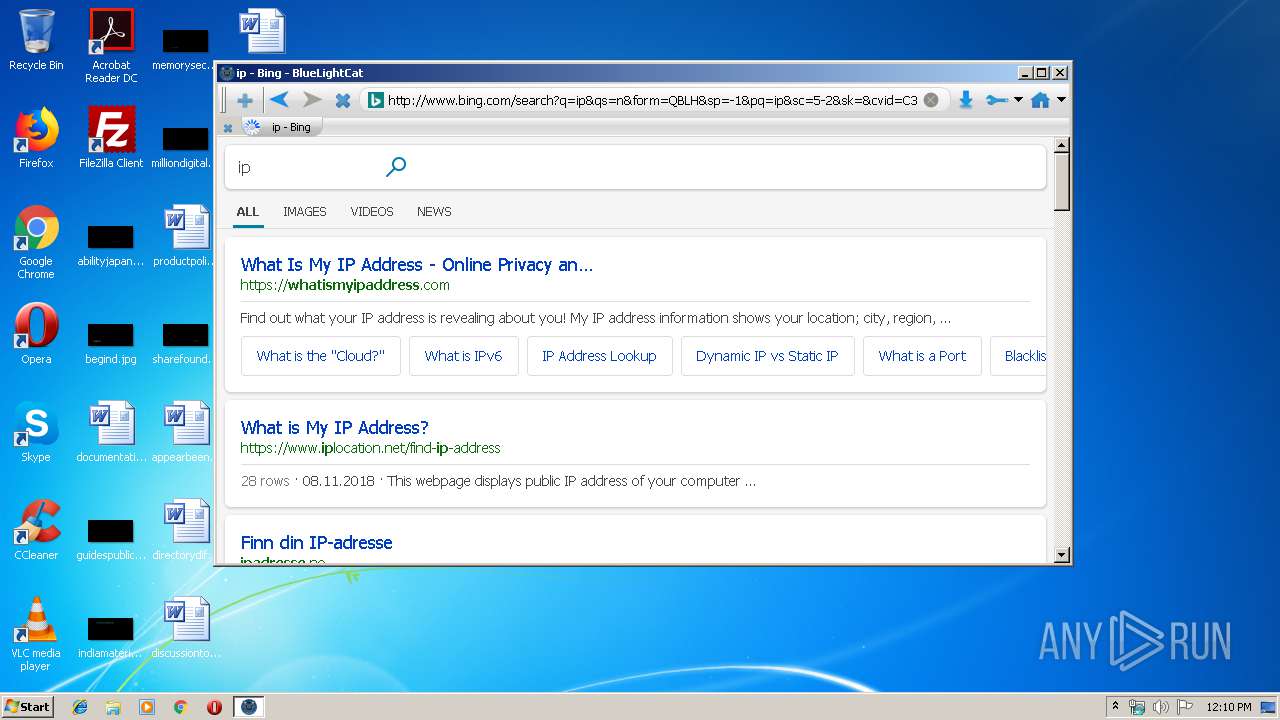
1640 | bluelightcat.exe | GET | 301 | 204.79.197.200:80 | http://bing.com/ | US | — | — | whitelisted |
1640 | bluelightcat.exe | GET | 204 | 172.217.16.142:80 | http://clients1.google.com/generate_204 | US | — | — | whitelisted |
1640 | bluelightcat.exe | GET | — | 216.58.207.36:80 | http://www.google.com/textinputassistant/tia.png | US | — | — | malicious |
1640 | bluelightcat.exe | GET | 200 | 172.217.22.99:80 | http://ssl.gstatic.com/gb/js/sem_5d0e9a88d640580d12b41844f0901e23.js | US | text | 20.2 Kb | whitelisted |
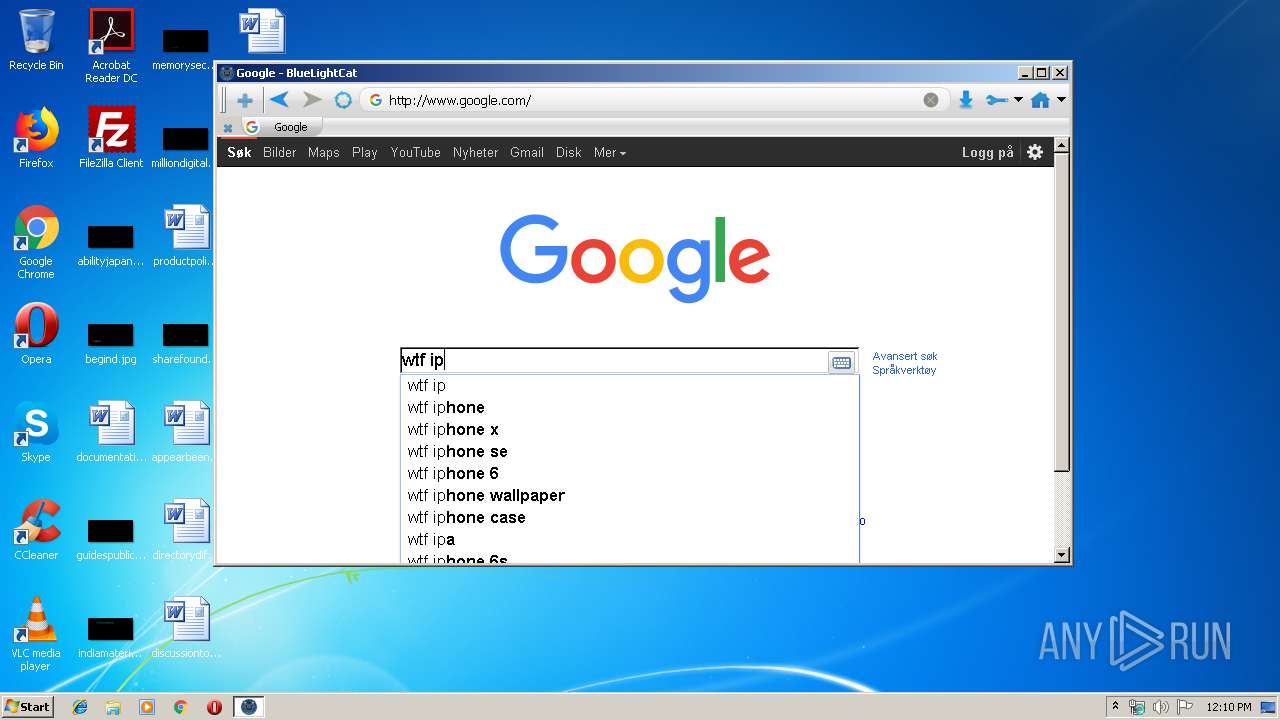
1640 | bluelightcat.exe | GET | 200 | 172.217.16.142:80 | http://clients1.google.com/complete/search?client=heirloom-hp&hl=no&gs_rn=34&gs_ri=heirloom-hp&cp=2&gs_id=7&q=wt | US | text | 184 b | whitelisted |
1640 | bluelightcat.exe | GET | 200 | 216.58.207.36:80 | http://www.google.com/xjs/_/js/k=xjs.hp.en.un0kSKBuyvA.O/m=sb_he,d/am=IqgF/rt=j/d=1/rs=ACT90oF3I6ylM-rWGmstFQR8qtGAZv-57A | US | text | 53.1 Kb | malicious |
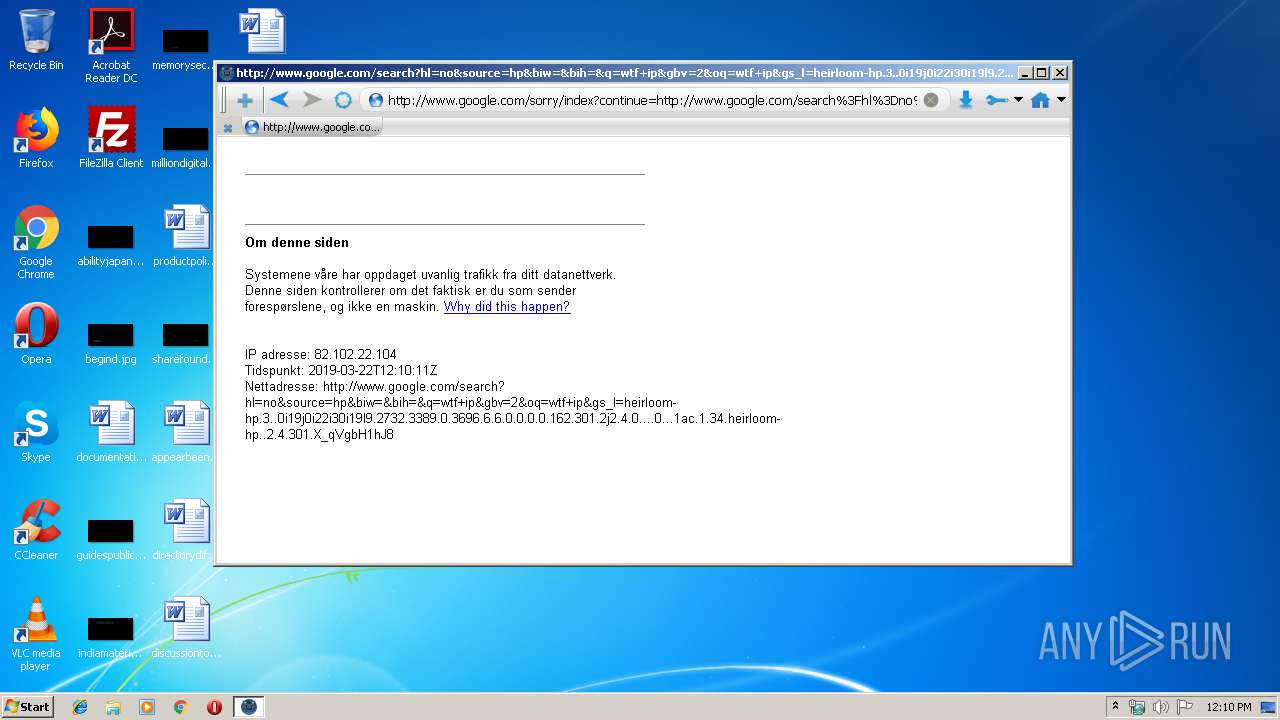
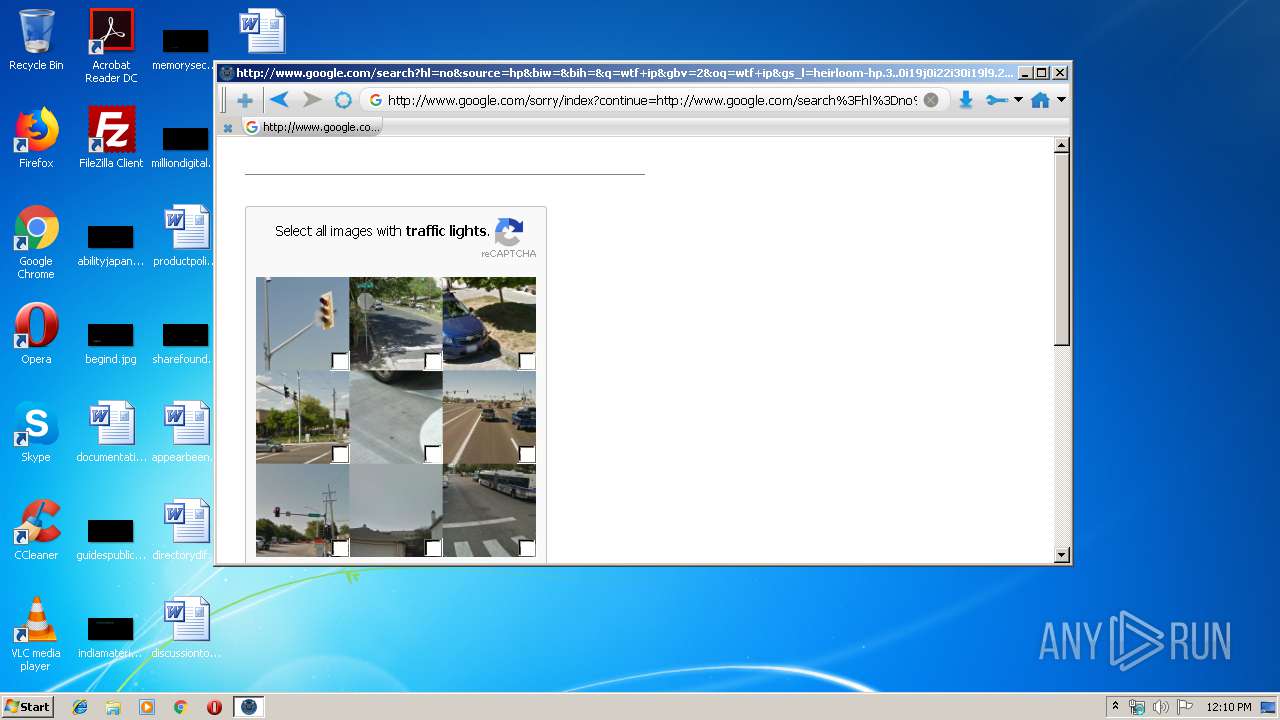
1640 | bluelightcat.exe | GET | 302 | 216.58.207.36:80 | http://www.google.com/search?hl=no&source=hp&biw=&bih=&q=wtf+ip&gbv=2&oq=wtf+ip&gs_l=heirloom-hp.3..0i19j0i22i30i19l9.2732.3389.0.3696.6.6.0.0.0.0.162.301.2j2.4.0....0...1ac.1.34.heirloom-hp..2.4.301.X_qVgbH1hJ8 | US | html | 560 b | malicious |
1640 | bluelightcat.exe | GET | 200 | 172.217.16.142:80 | http://clients1.google.com/complete/search?client=heirloom-hp&hl=no&gs_rn=34&gs_ri=heirloom-hp&cp=1&gs_id=4&q=w | US | text | 219 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1640 | bluelightcat.exe | 140.211.166.81:80 | adblockplus.mozdev.org | Network for Education and Research in Oregon (NERO) | US | suspicious |
1640 | bluelightcat.exe | 216.58.205.238:80 | — | Google Inc. | US | whitelisted |
1640 | bluelightcat.exe | 88.99.186.148:443 | easylist-downloads.adblockplus.org | Hetzner Online GmbH | DE | unknown |
1640 | bluelightcat.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1640 | bluelightcat.exe | 216.58.207.36:80 | www.google.com | Google Inc. | US | whitelisted |
1640 | bluelightcat.exe | 172.217.22.99:80 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1640 | bluelightcat.exe | 172.217.16.142:80 | clients1.google.com | Google Inc. | US | whitelisted |
1640 | bluelightcat.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
1640 | bluelightcat.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1640 | bluelightcat.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
adblockplus.mozdev.org |
| suspicious |
easylist-downloads.adblockplus.org |
| suspicious |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
Process | Message |
|---|---|
bluelightcat.exe | QFont::setPixelSize: Pixel size <= 0 (0)
|
bluelightcat.exe | QNetworkReplyImplPrivate::error: Internal problem, this method must only be called once.
|
bluelightcat.exe | QNetworkReplyImplPrivate::error: Internal problem, this method must only be called once.
|