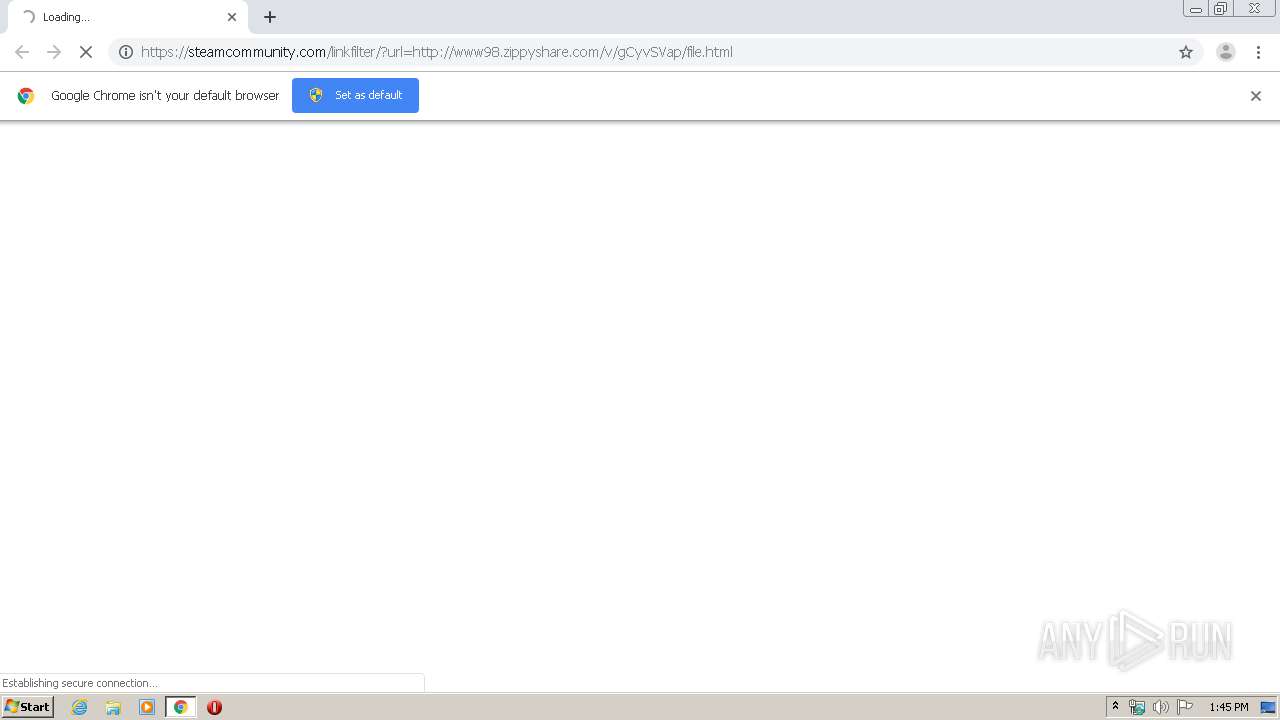
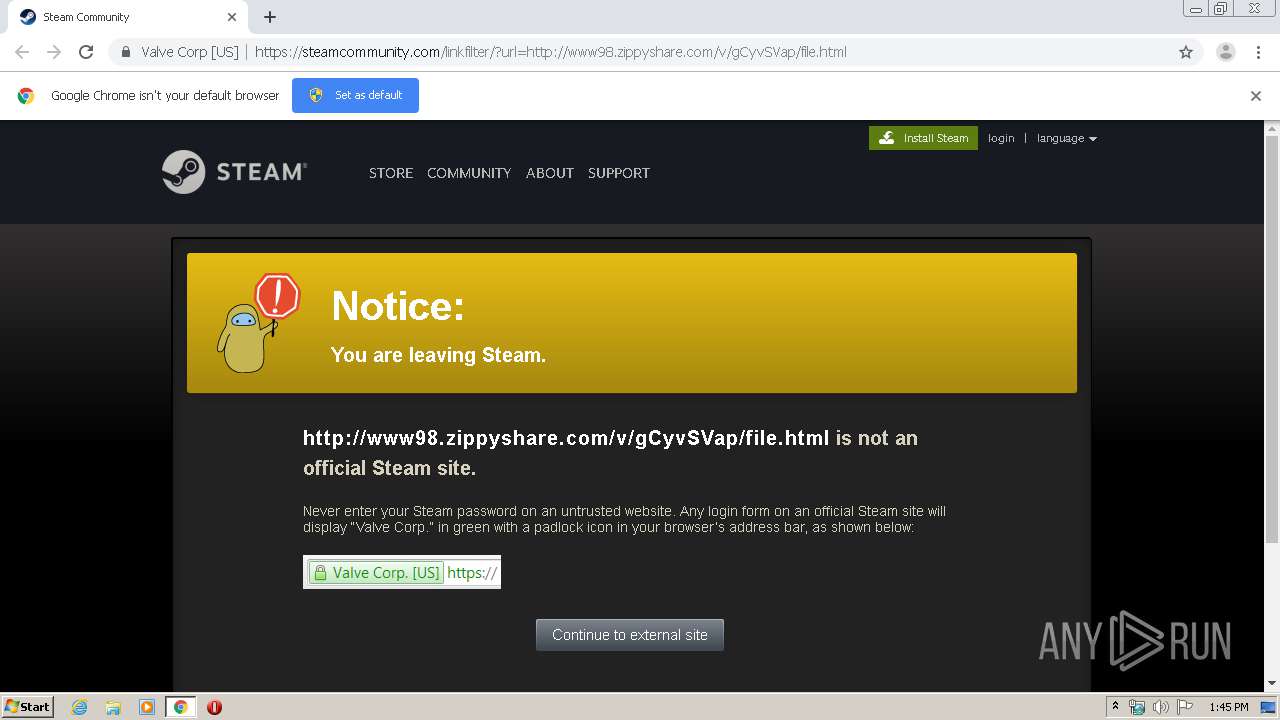
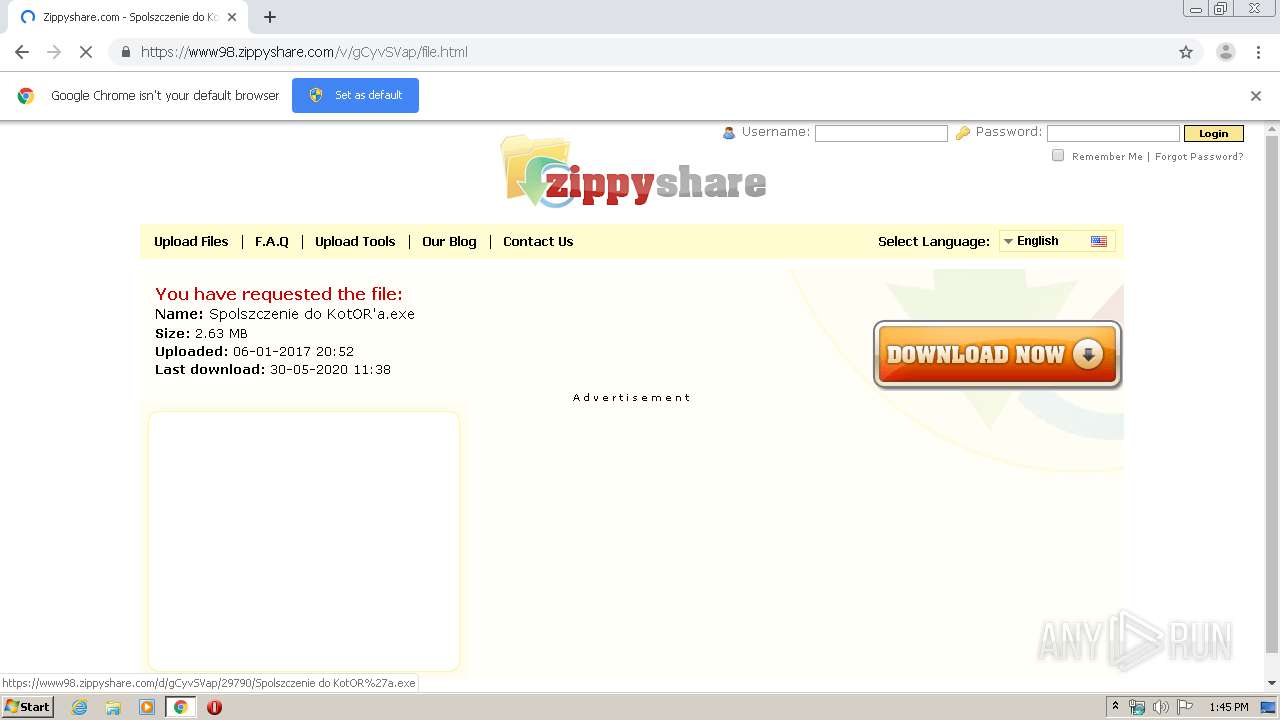
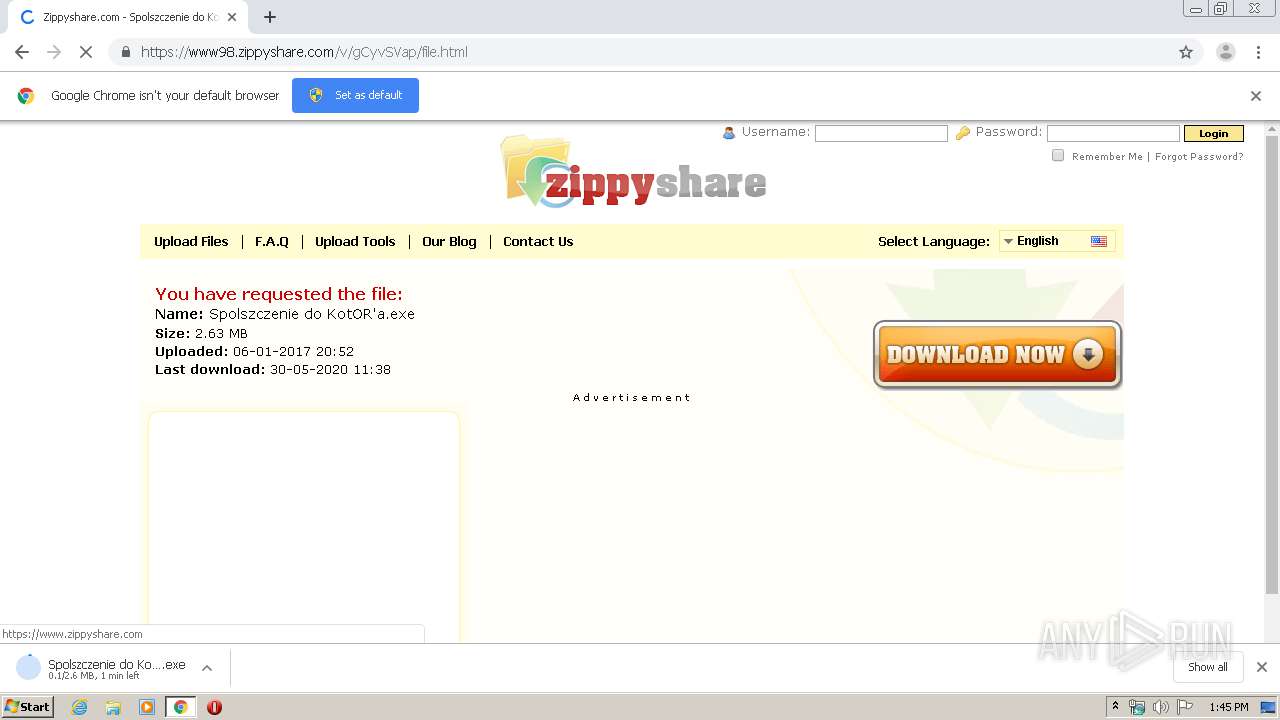
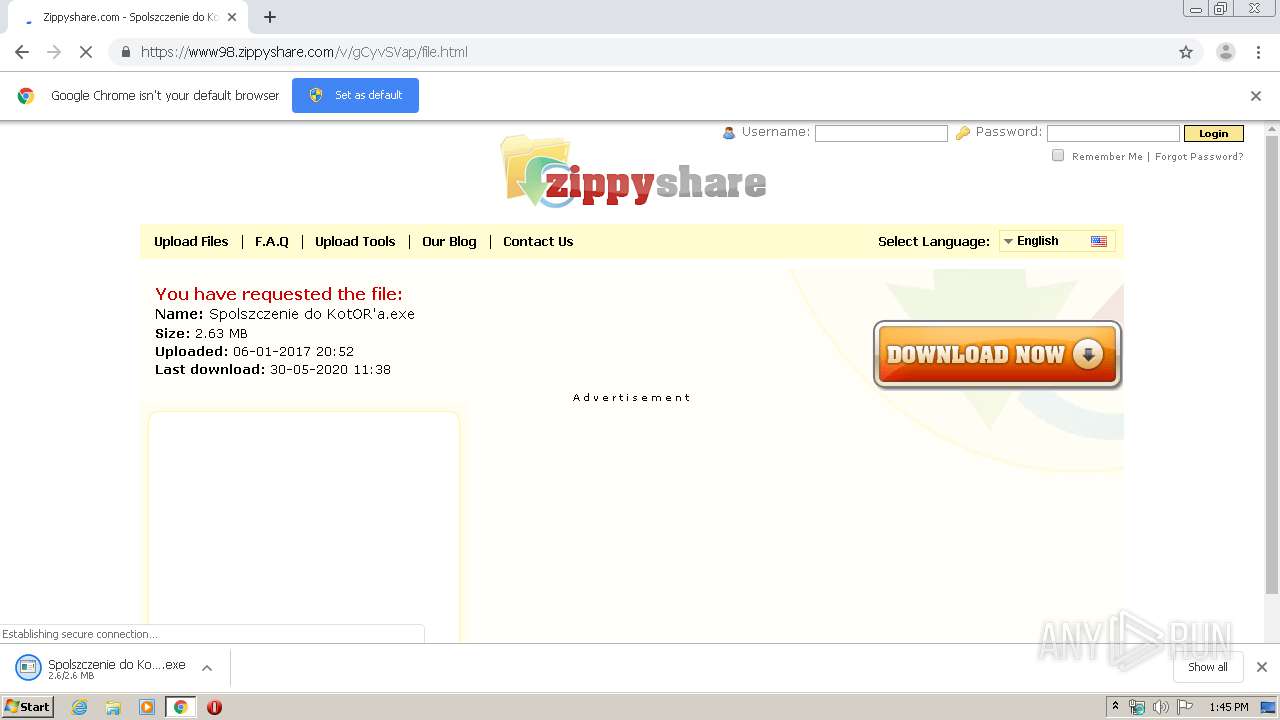
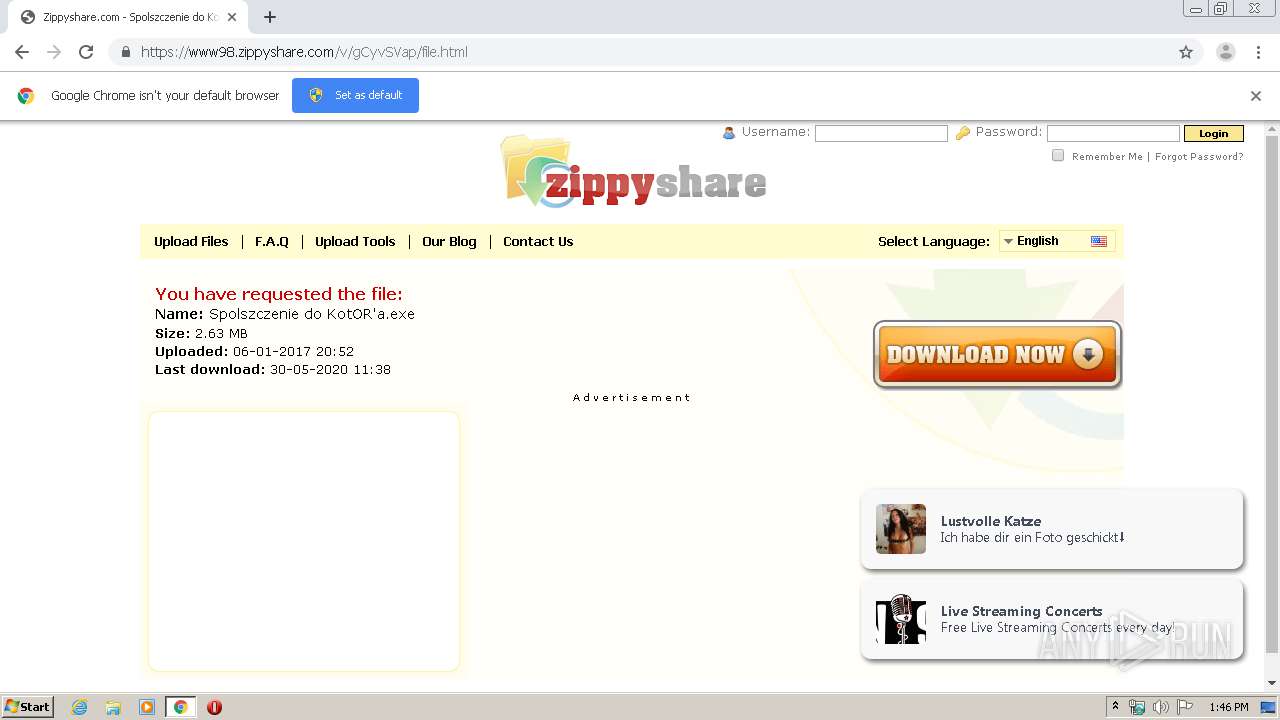
| URL: | https://steamcommunity.com/linkfilter/?url=http://www98.zippyshare.com/v/gCyvSVap/file.html |
| Full analysis: | https://app.any.run/tasks/902b0414-81d2-478c-865b-39584b3ed9ea |
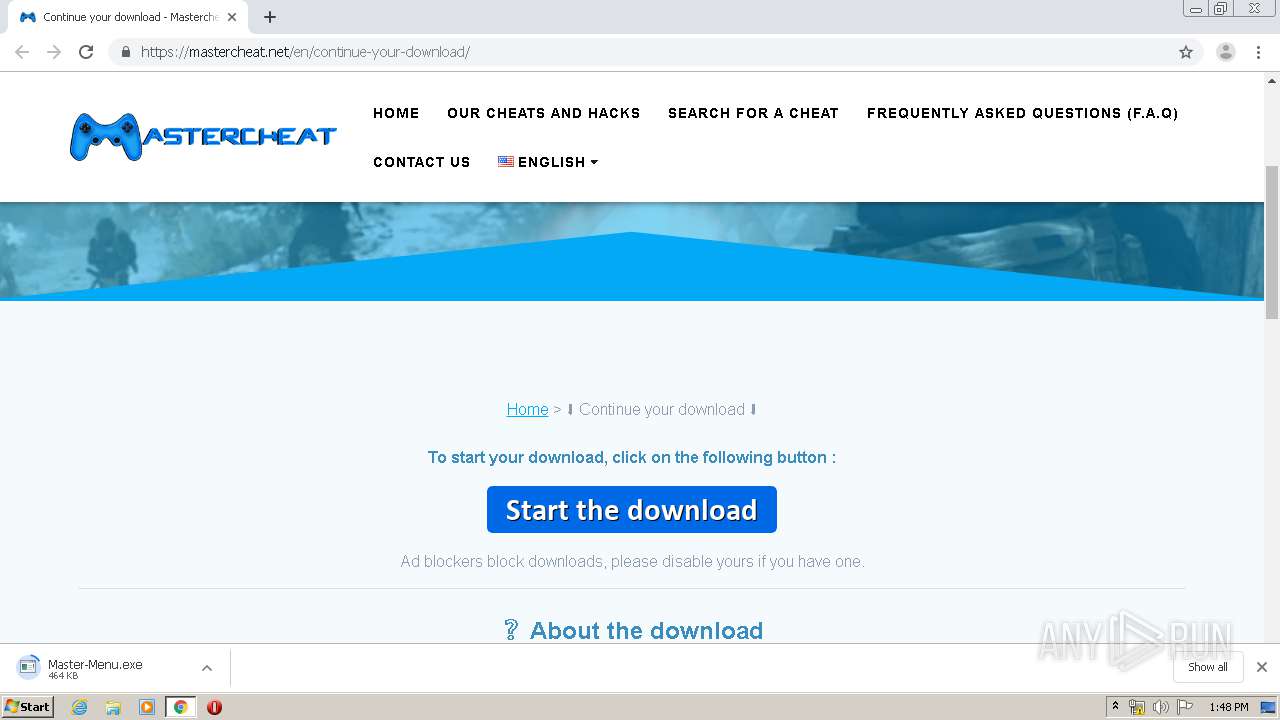
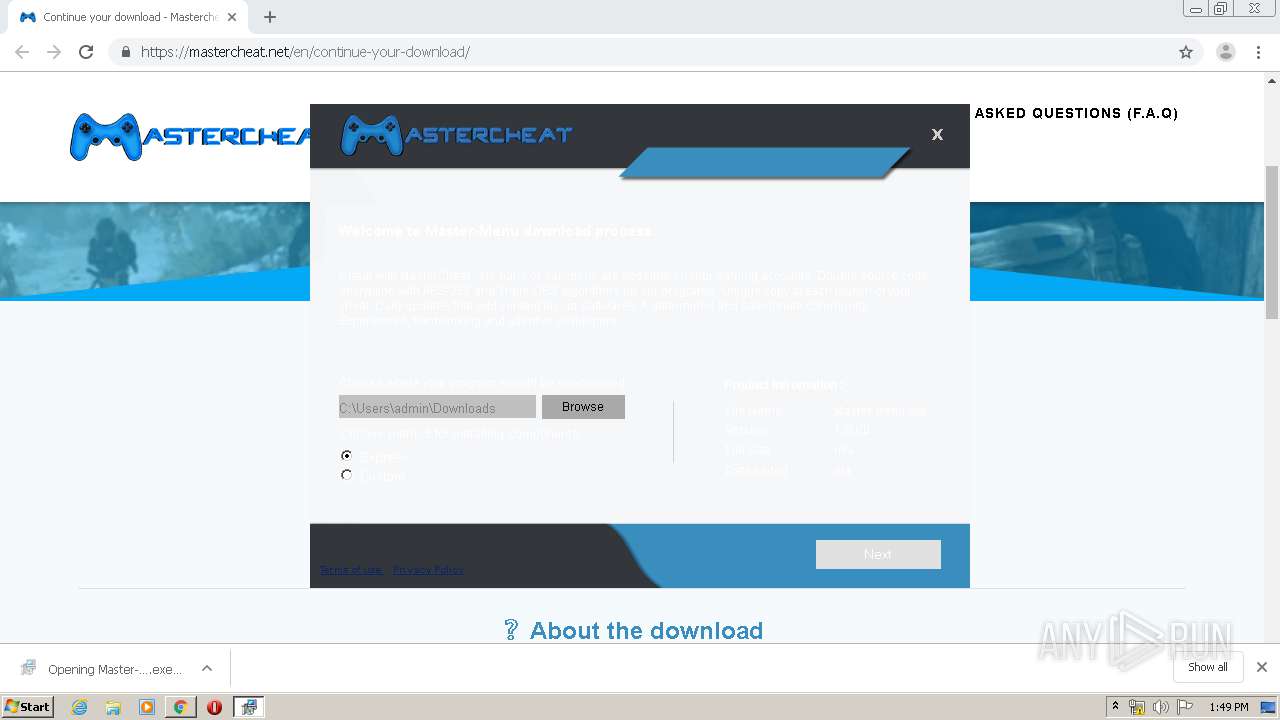
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 12:45:23 |
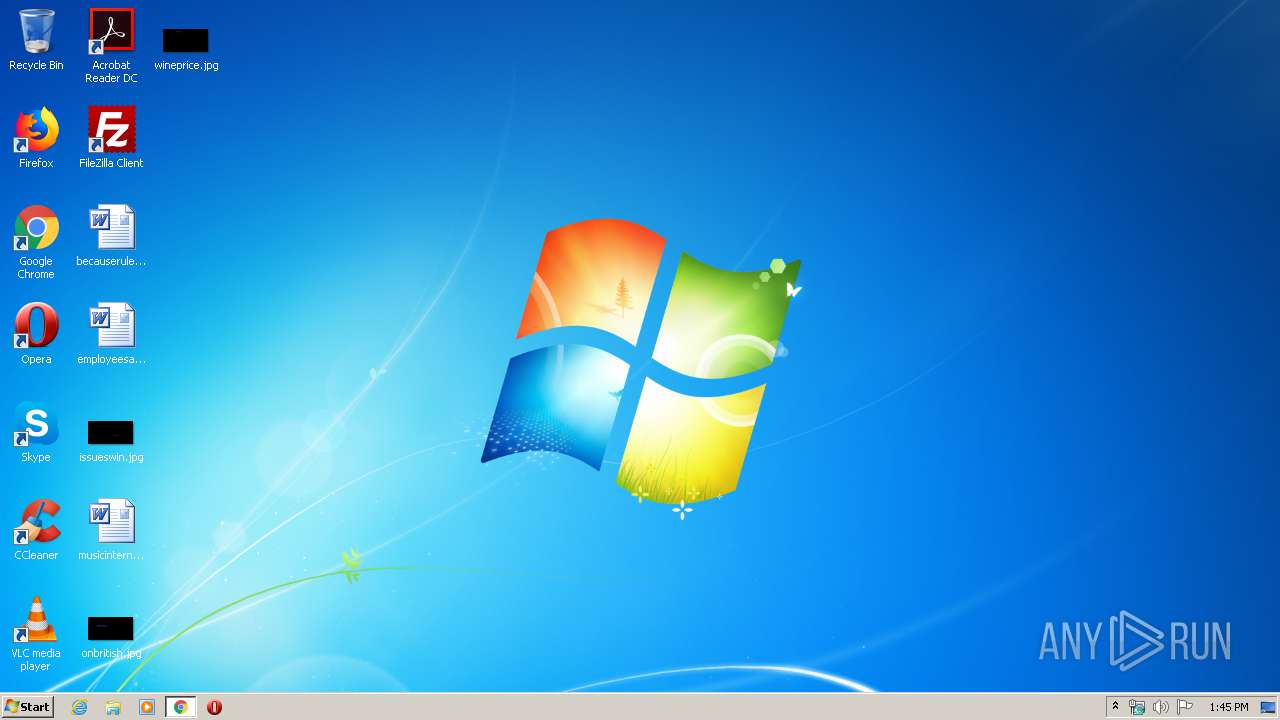
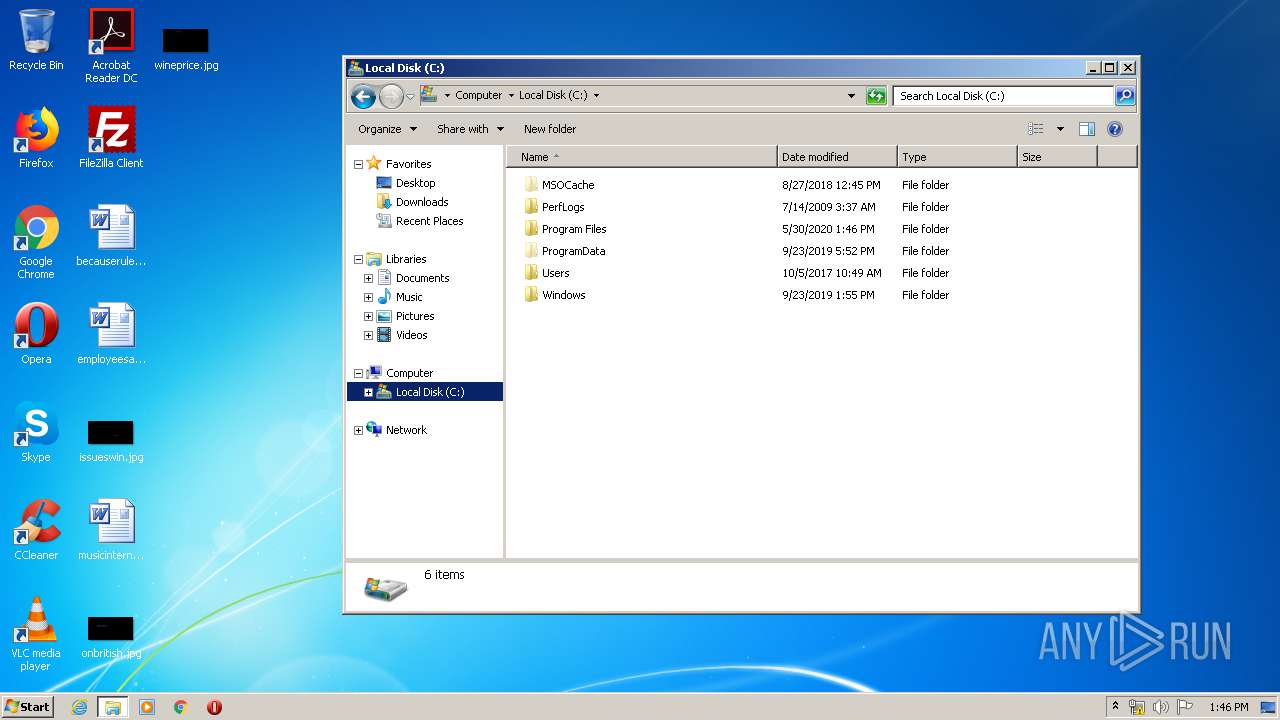
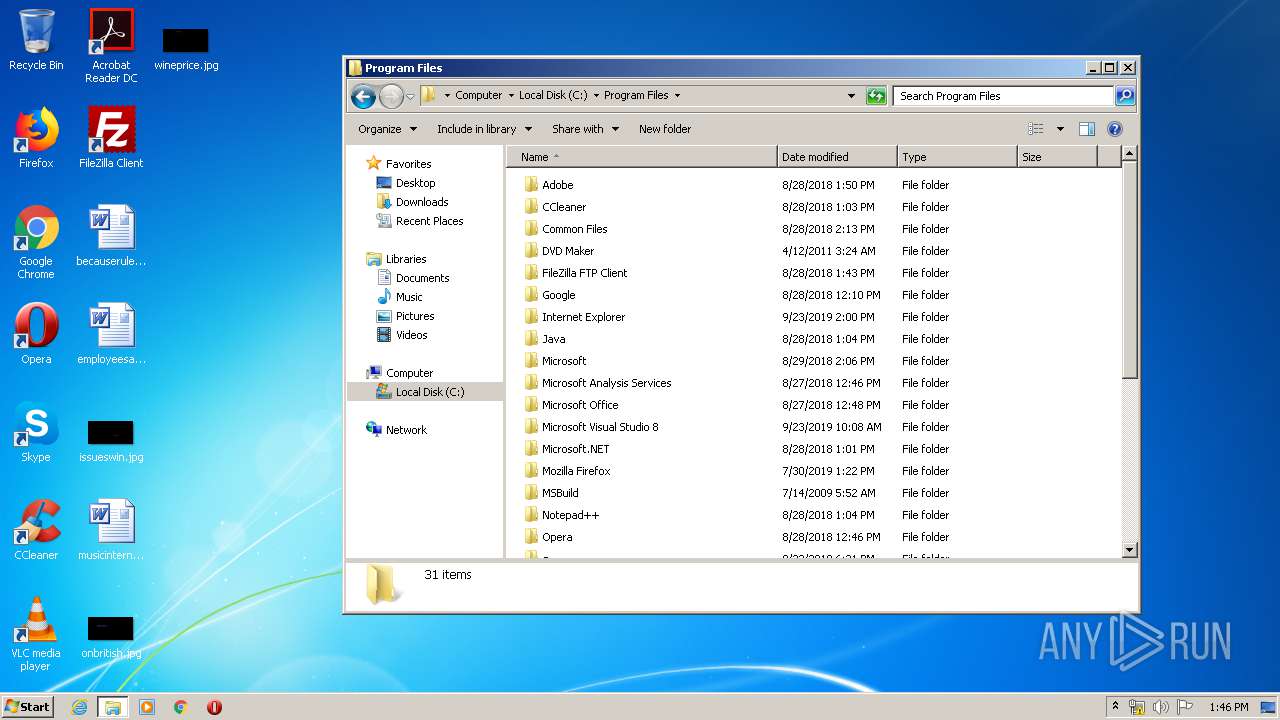
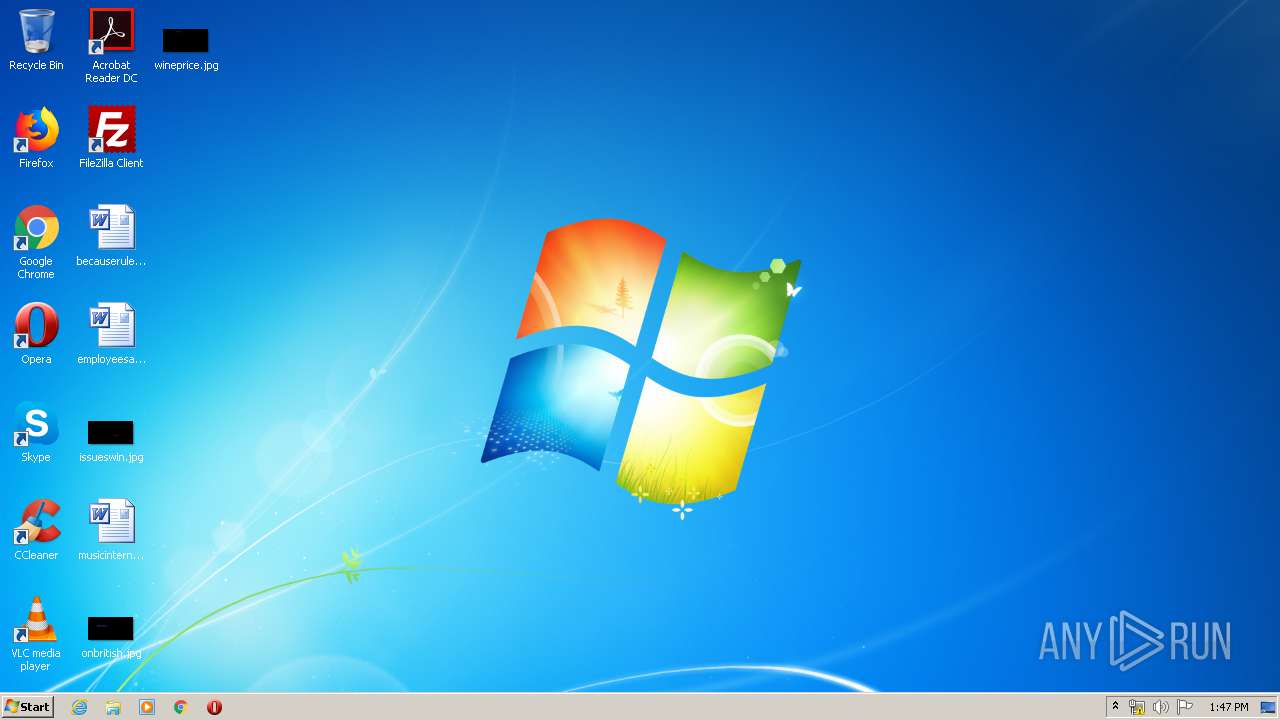
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F064EFD1E67333FA749050838270F9E5 |
| SHA1: | FA9ADAA415C141CB8B6FF5AB82060944EEA81A01 |
| SHA256: | 6DA4247819C879D4614BF8BD4A7ECF6DF4FA46CAFE4429971825BAB424447483 |
| SSDEEP: | 3:N8cDMWIKCoMJPuV8SvdLk/hGKjKk7J:2cDMHoMJWJFUGjk7J |
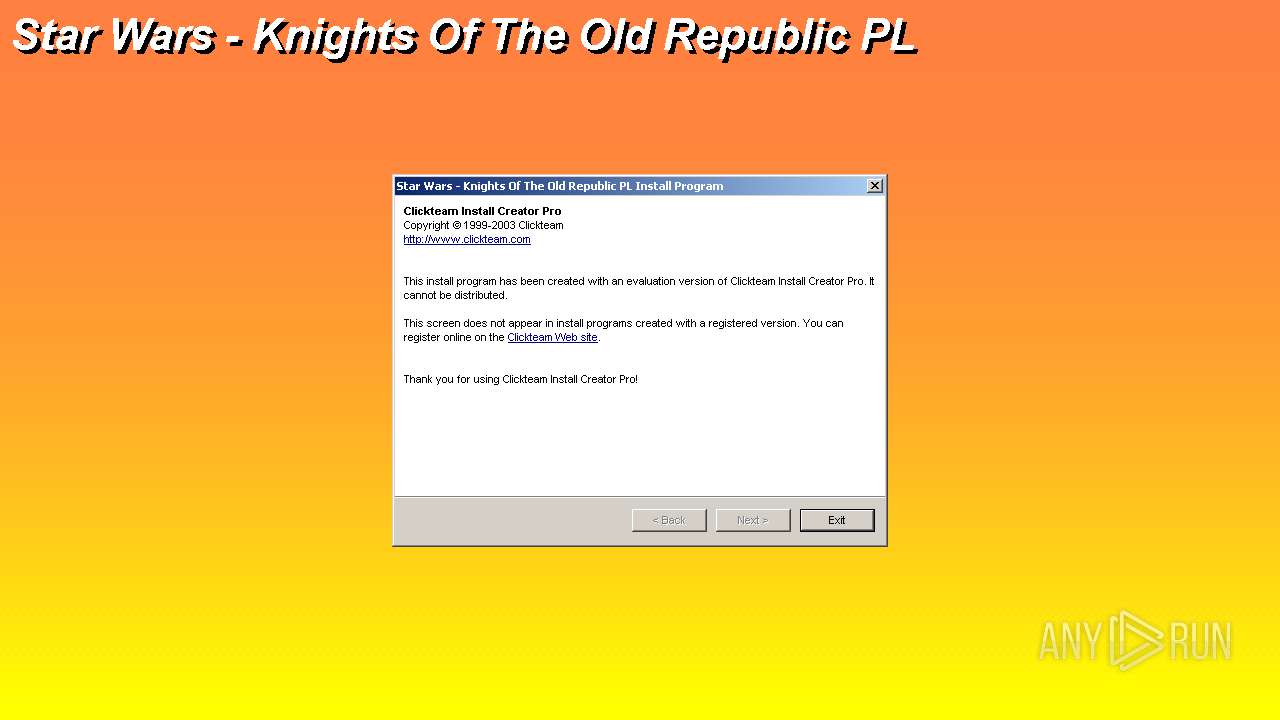
MALICIOUS
Application was dropped or rewritten from another process
- Spolszczenie do KotOR'a.exe (PID: 968)
- Spolszczenie do KotOR'a.exe (PID: 3980)
- Spolszczenie do KotOR'a.exe (PID: 2688)
- Spolszczenie do KotOR'a.exe (PID: 1816)
- Master-Menu.exe (PID: 3596)
- Master-Menu.exe (PID: 2780)
Changes settings of System certificates
- Master-Menu.exe (PID: 2780)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3172)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 1868)
- chrome.exe (PID: 3840)
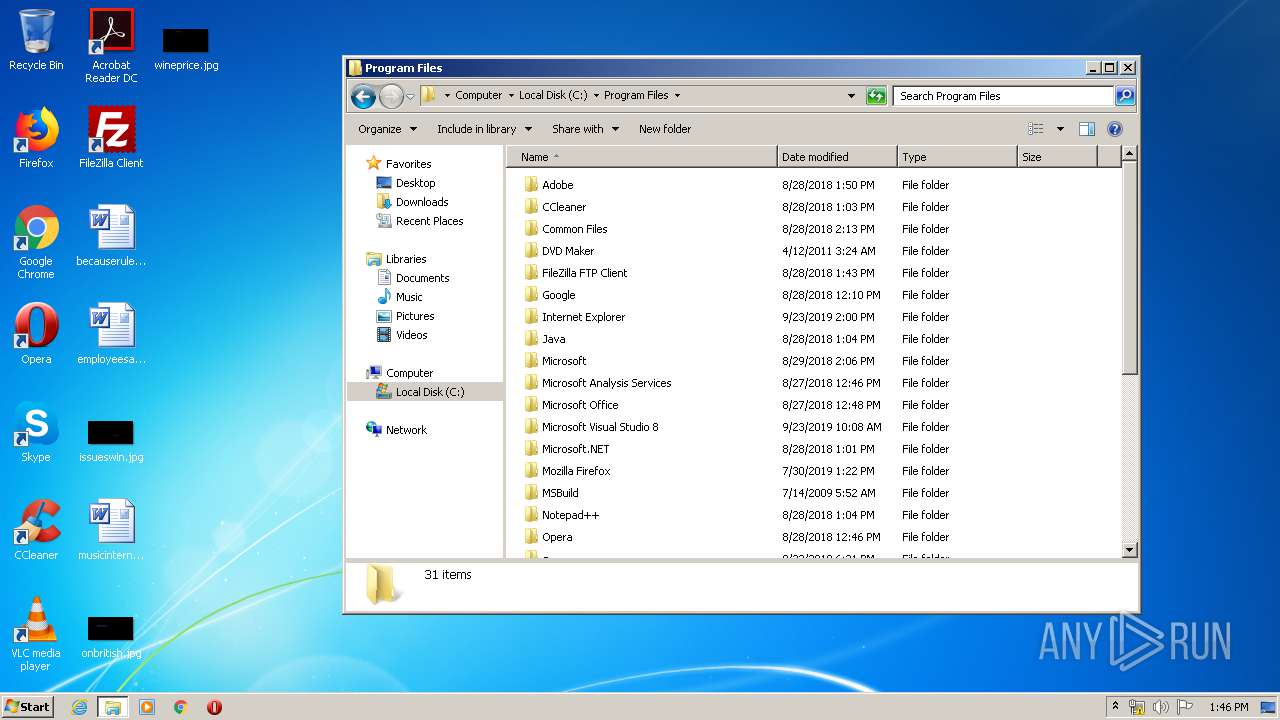
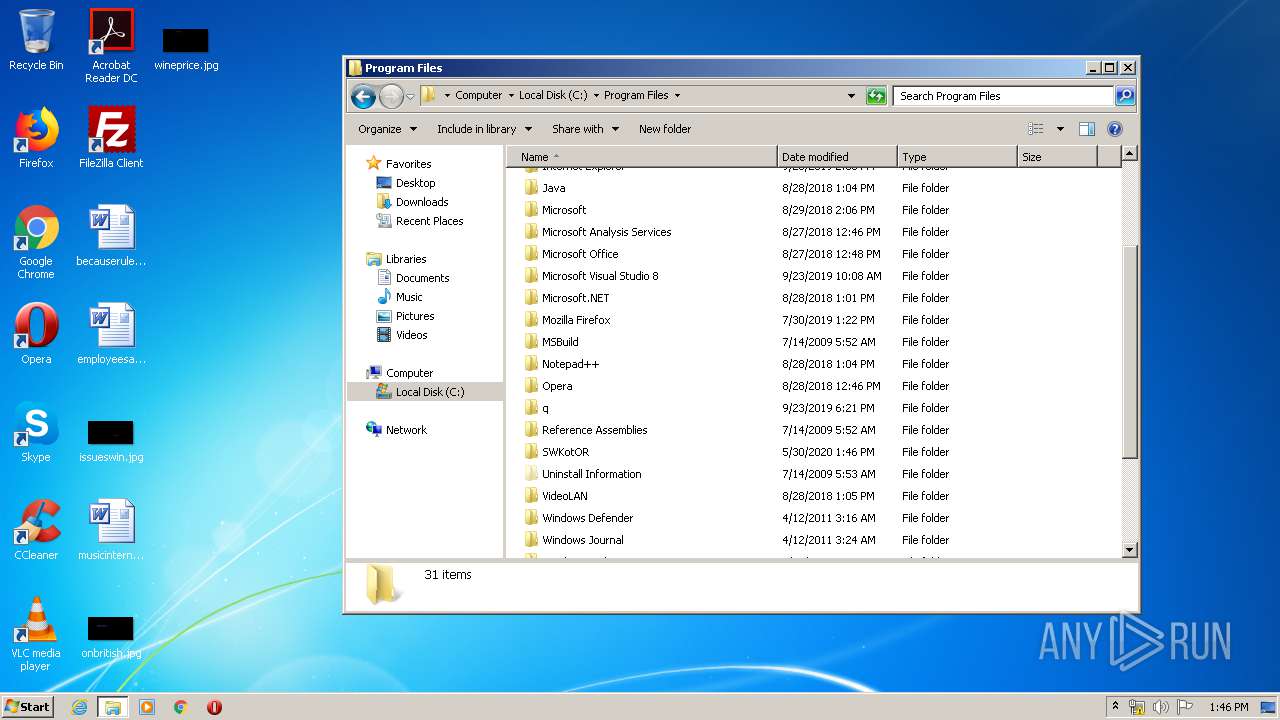
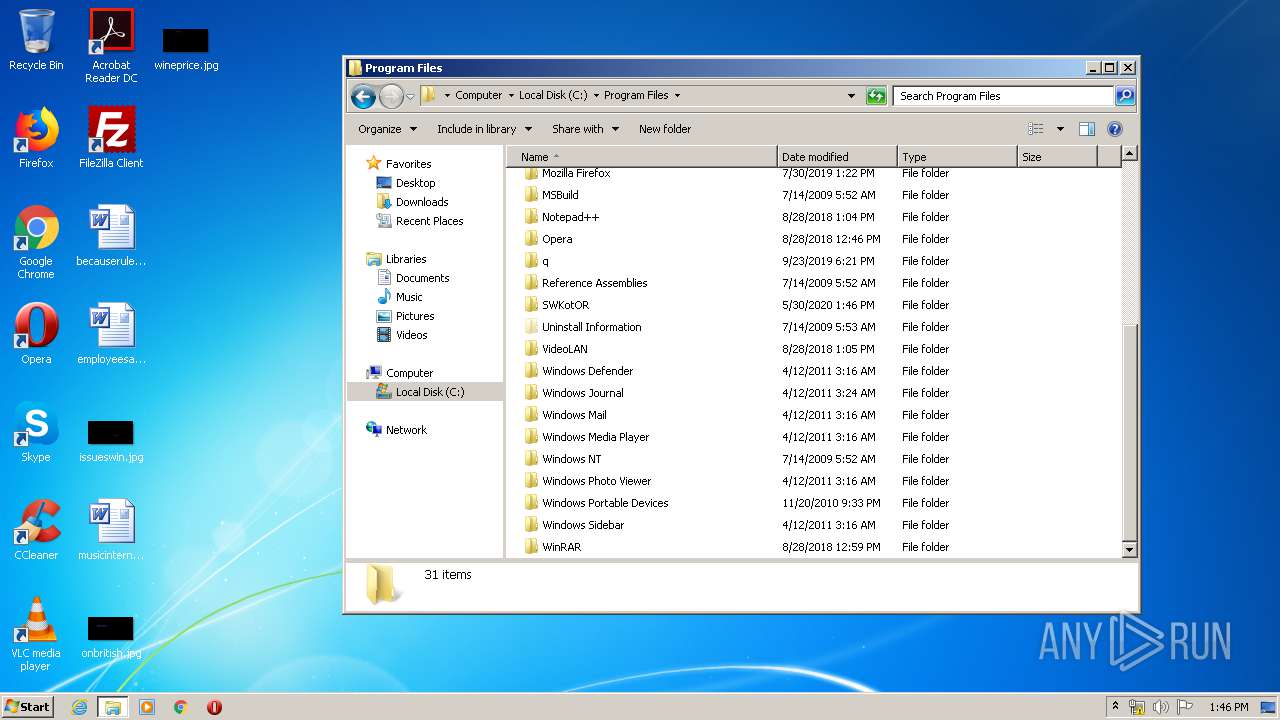
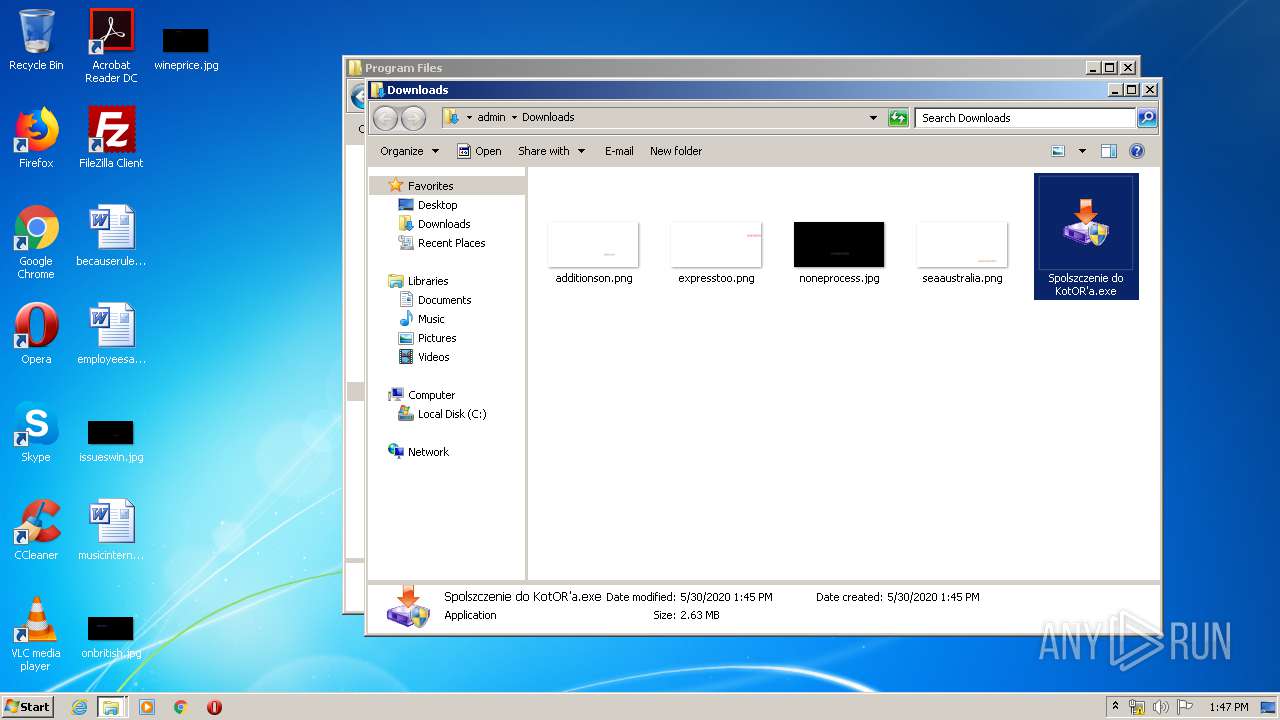
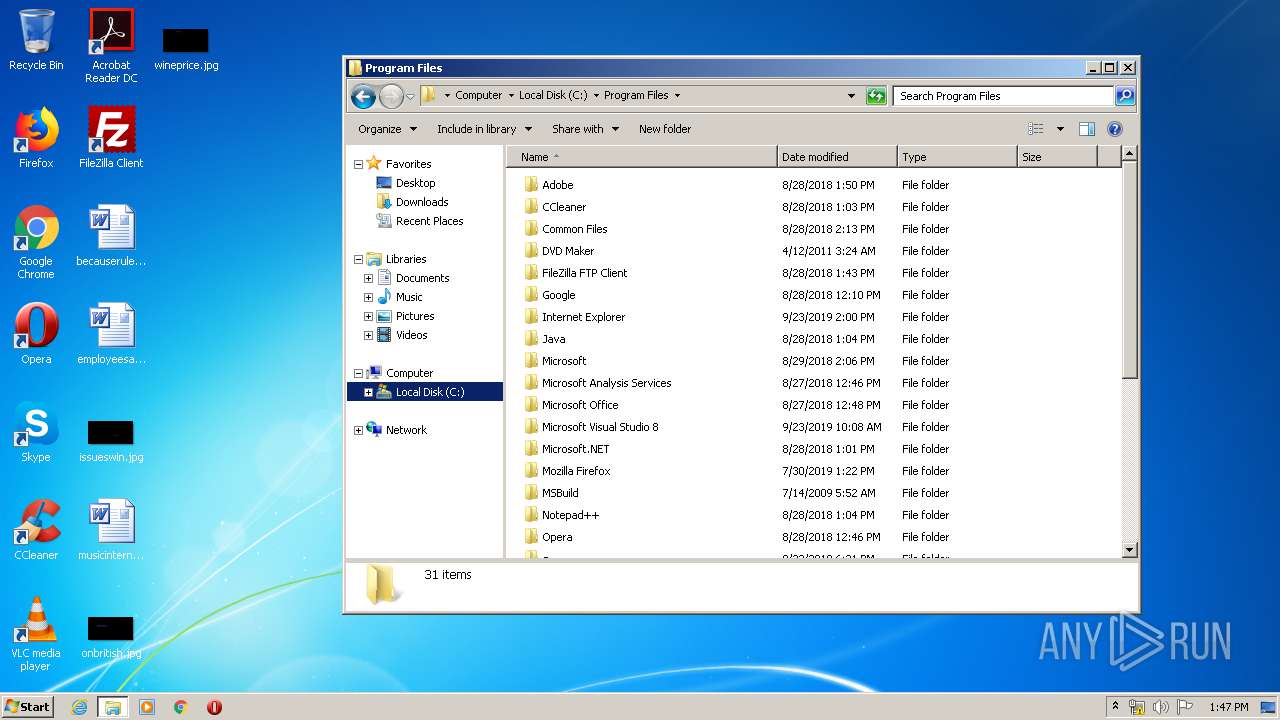
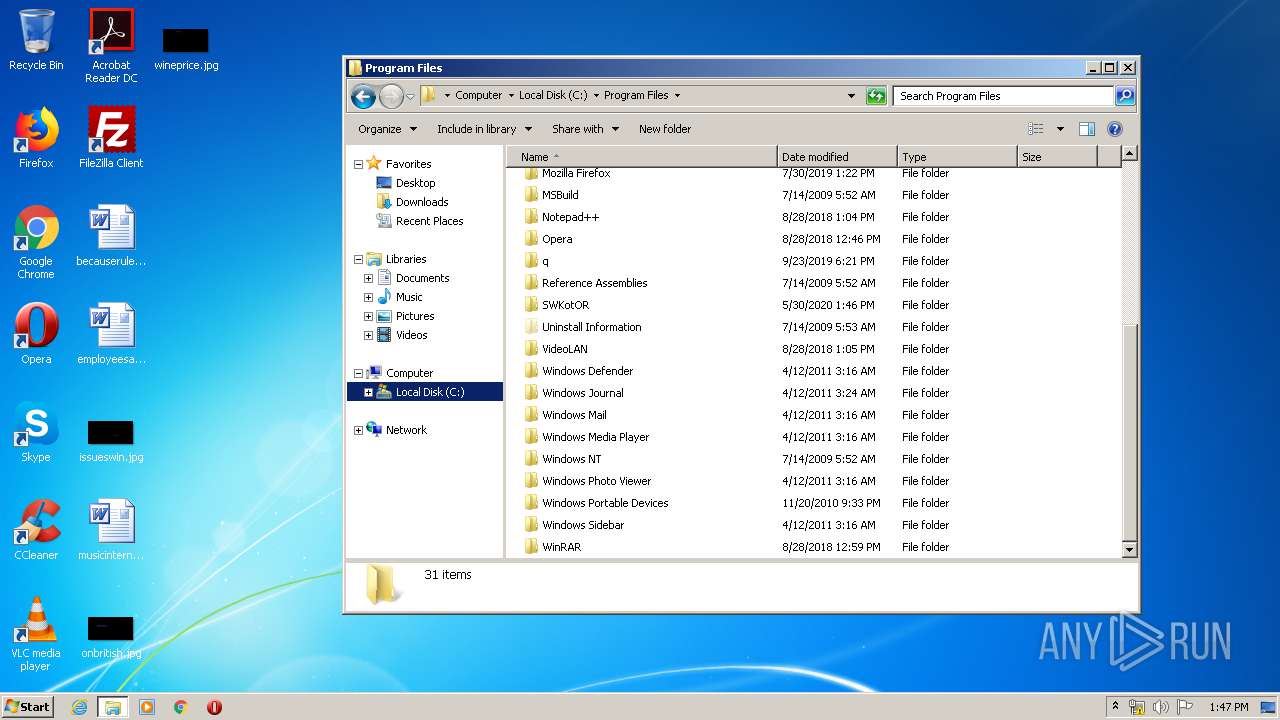
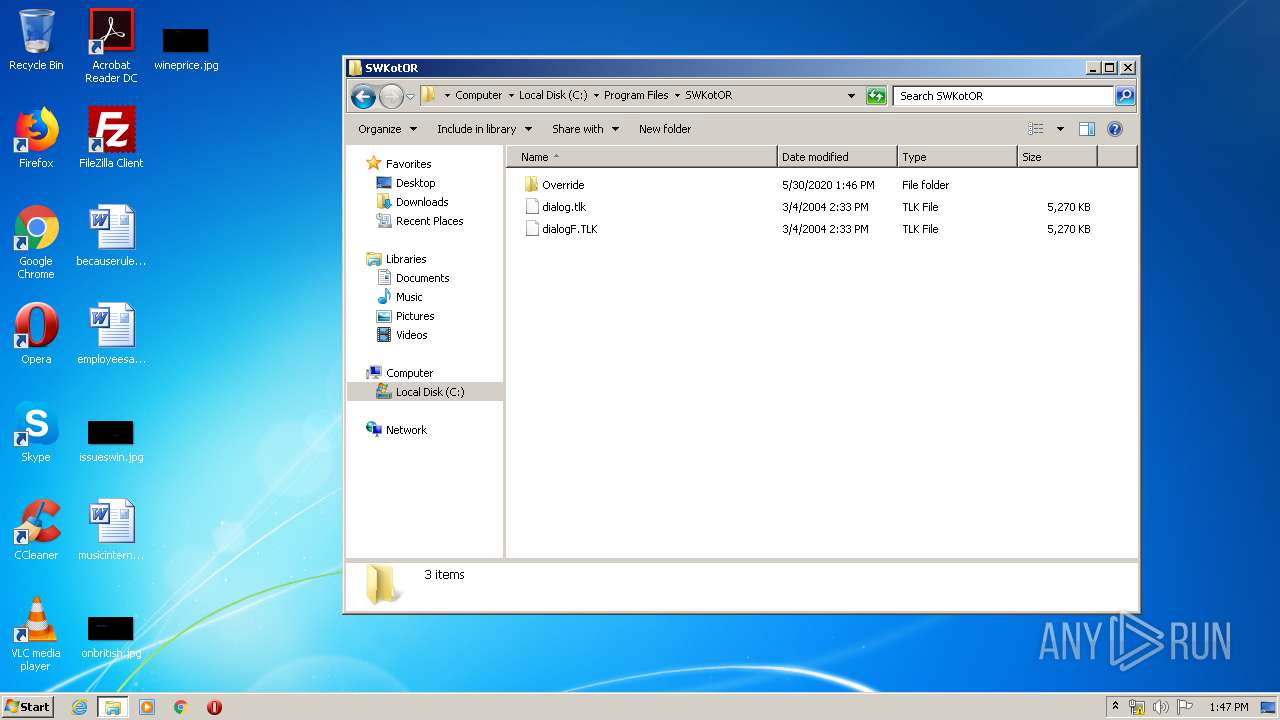
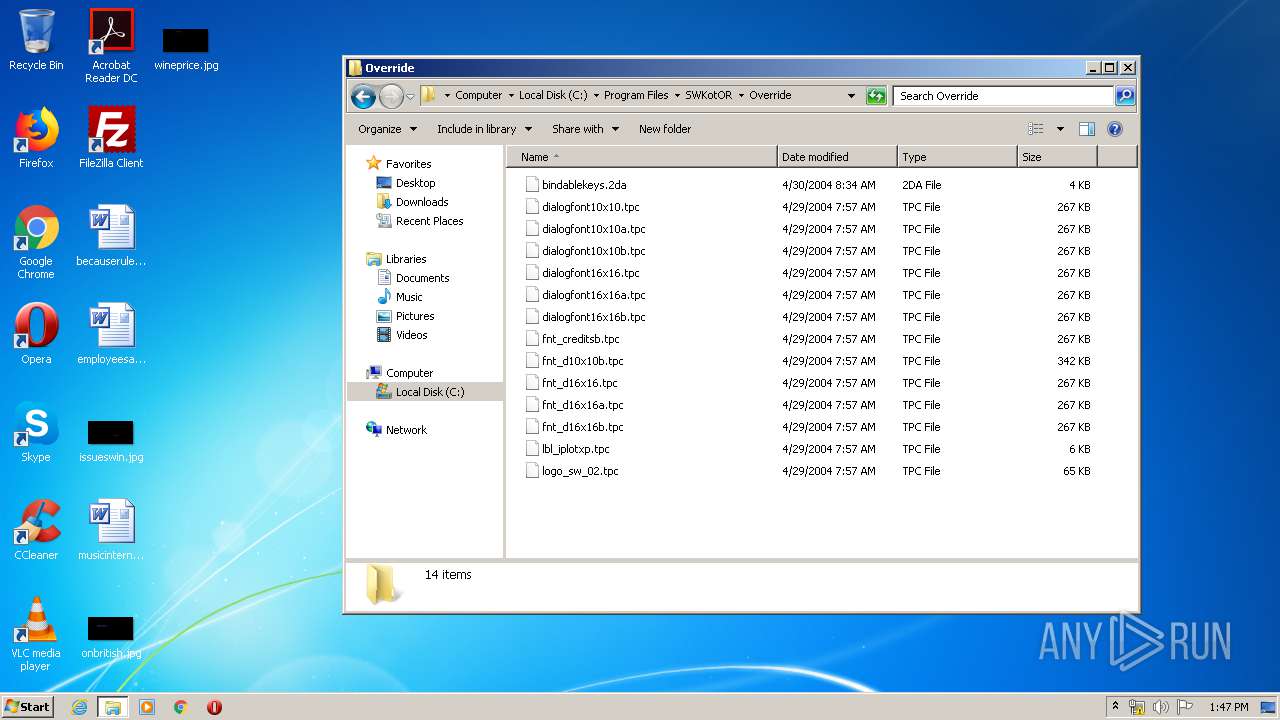
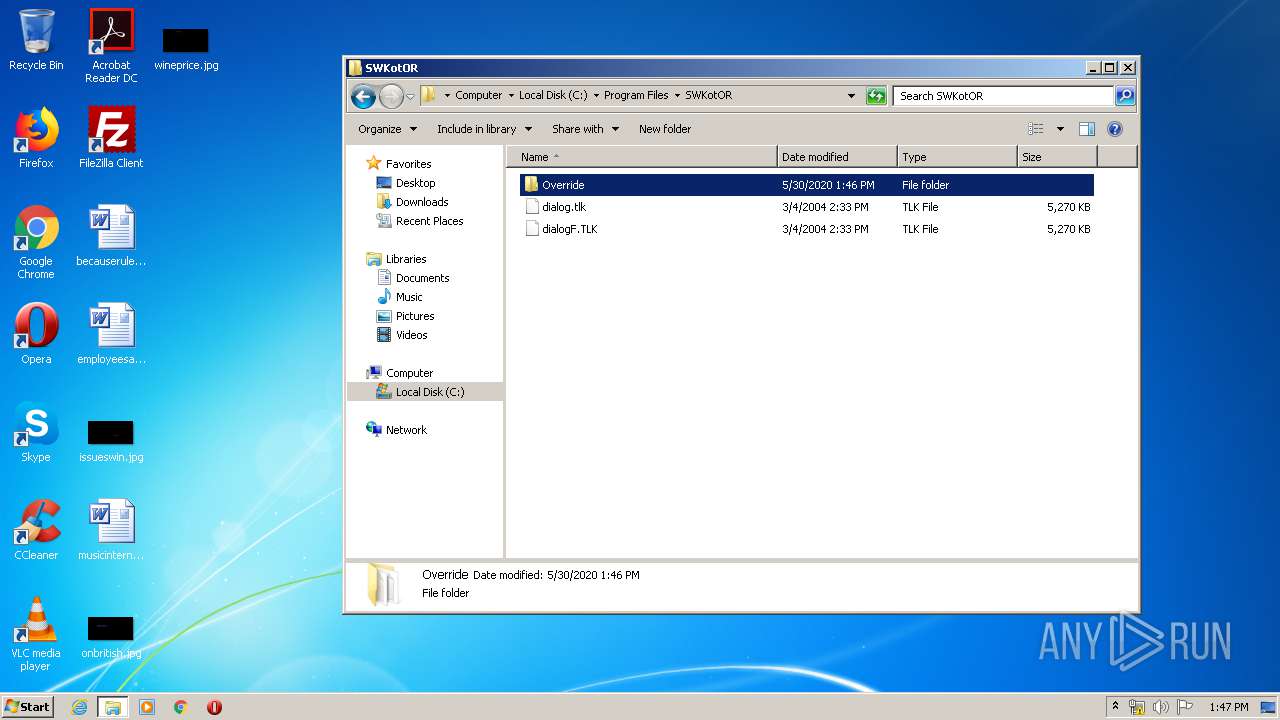
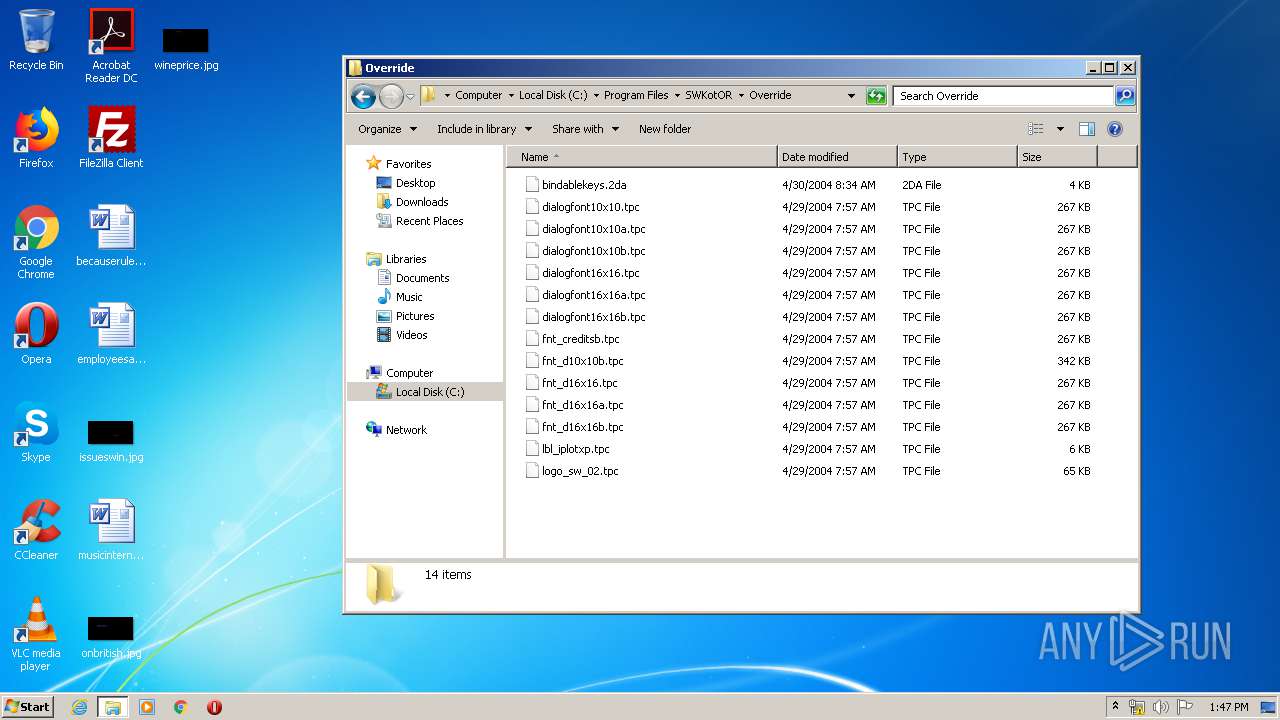
Creates files in the program directory
- Spolszczenie do KotOR'a.exe (PID: 3980)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3172)
Reads Environment values
- Master-Menu.exe (PID: 2780)
Creates files in the user directory
- Master-Menu.exe (PID: 2780)
Adds / modifies Windows certificates
- Master-Menu.exe (PID: 2780)
Reads internet explorer settings
- Master-Menu.exe (PID: 2780)
INFO
Reads the hosts file
- chrome.exe (PID: 3172)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 1868)
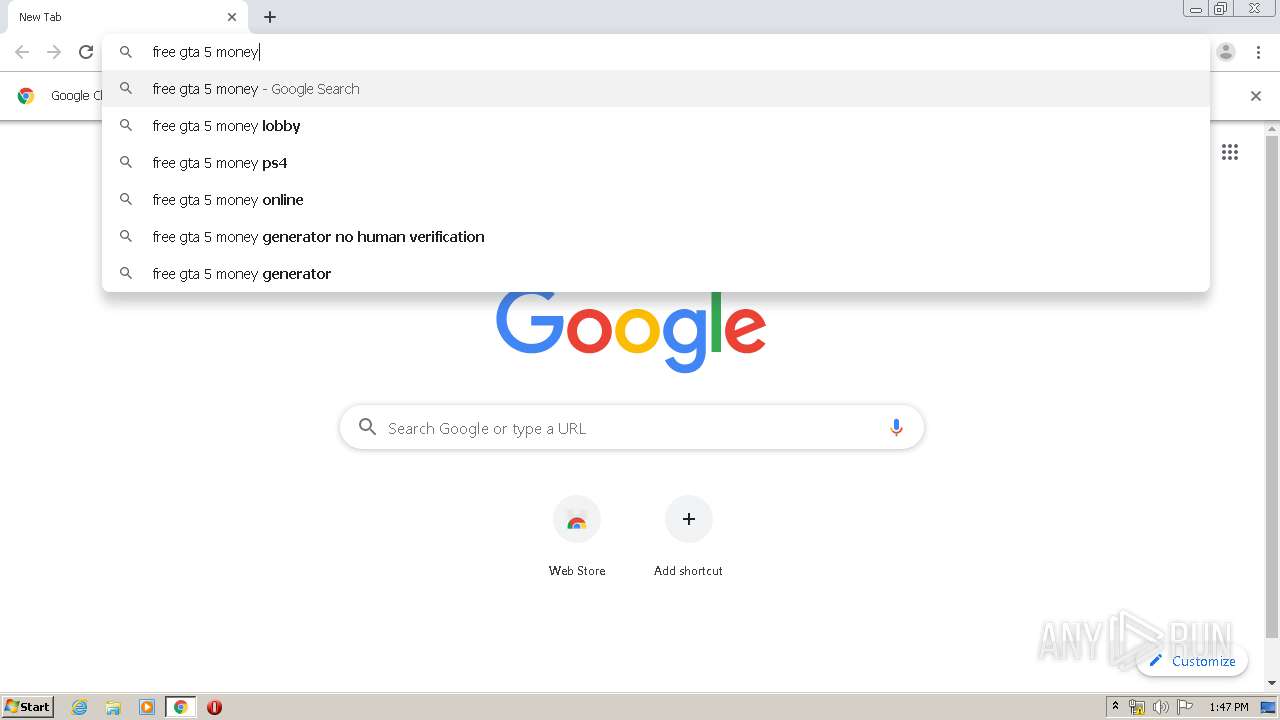
Application launched itself
- chrome.exe (PID: 3172)
- chrome.exe (PID: 1868)
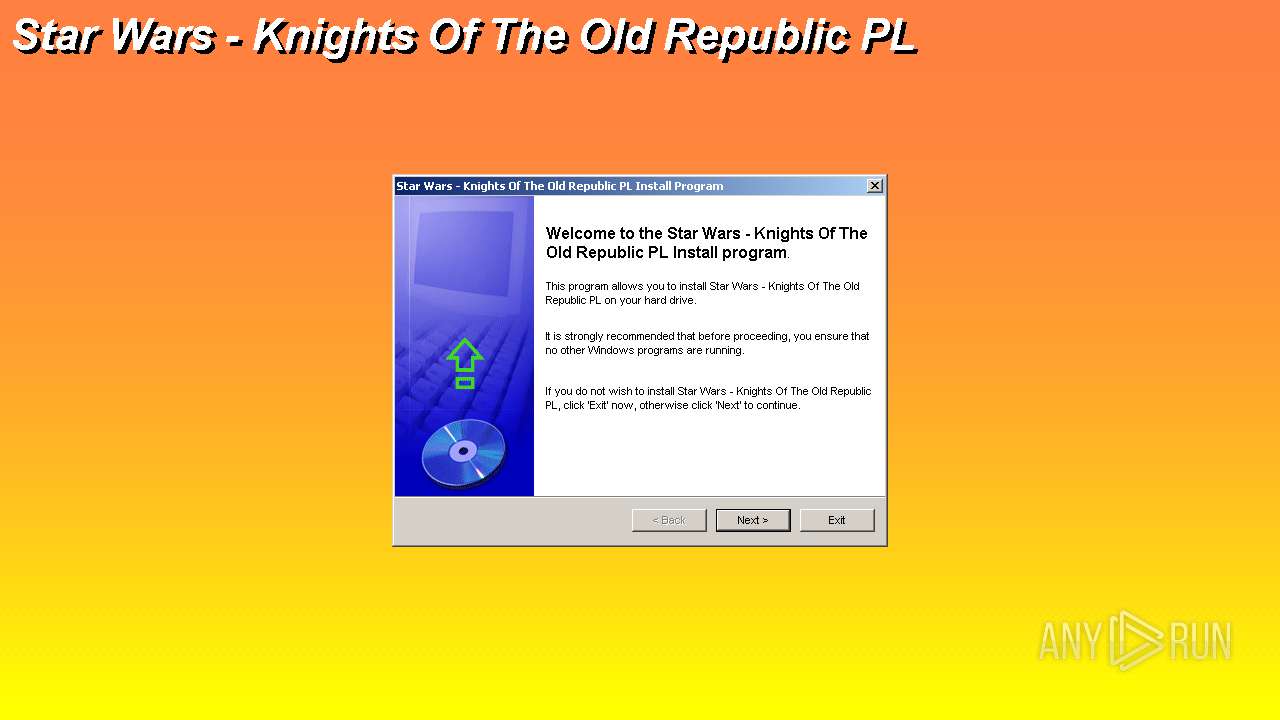
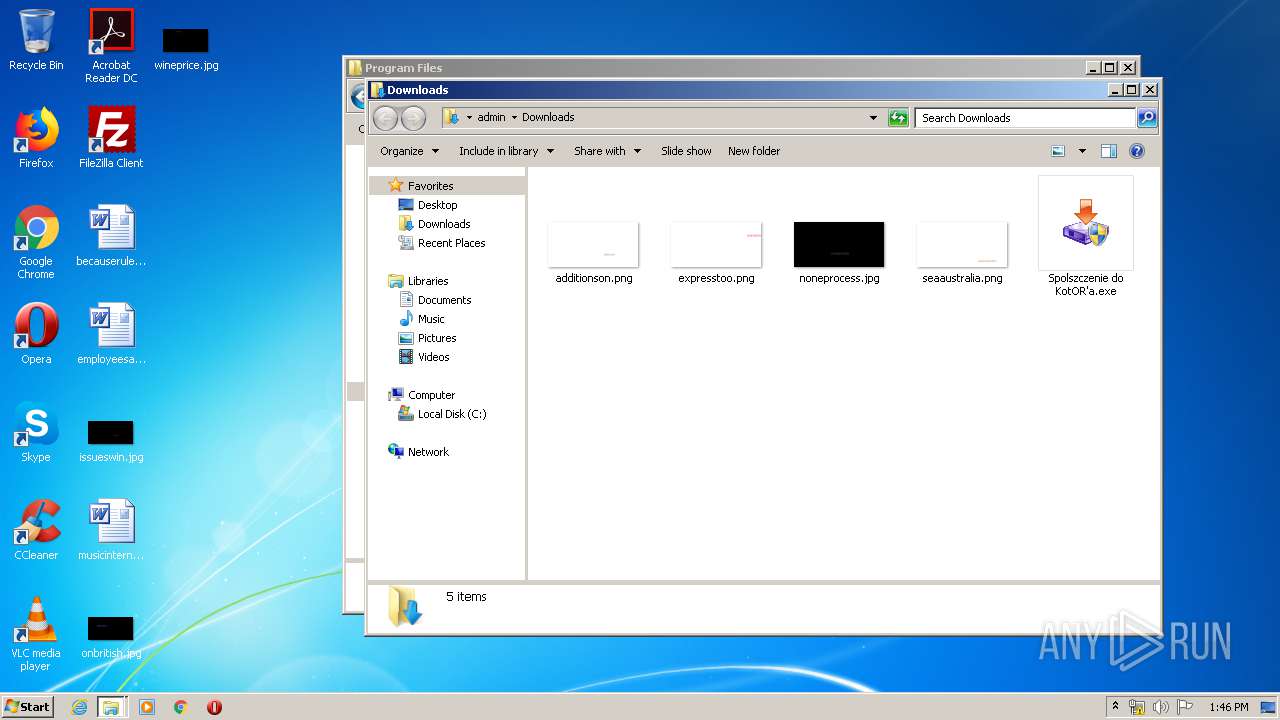
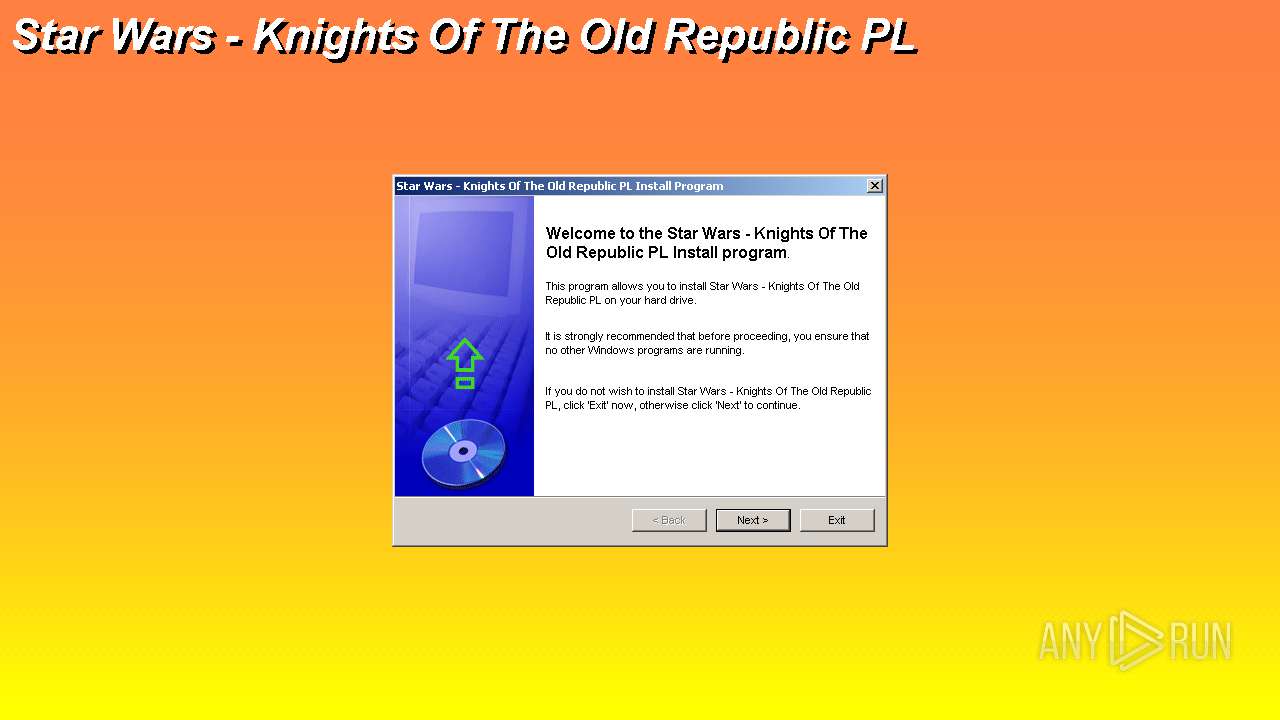
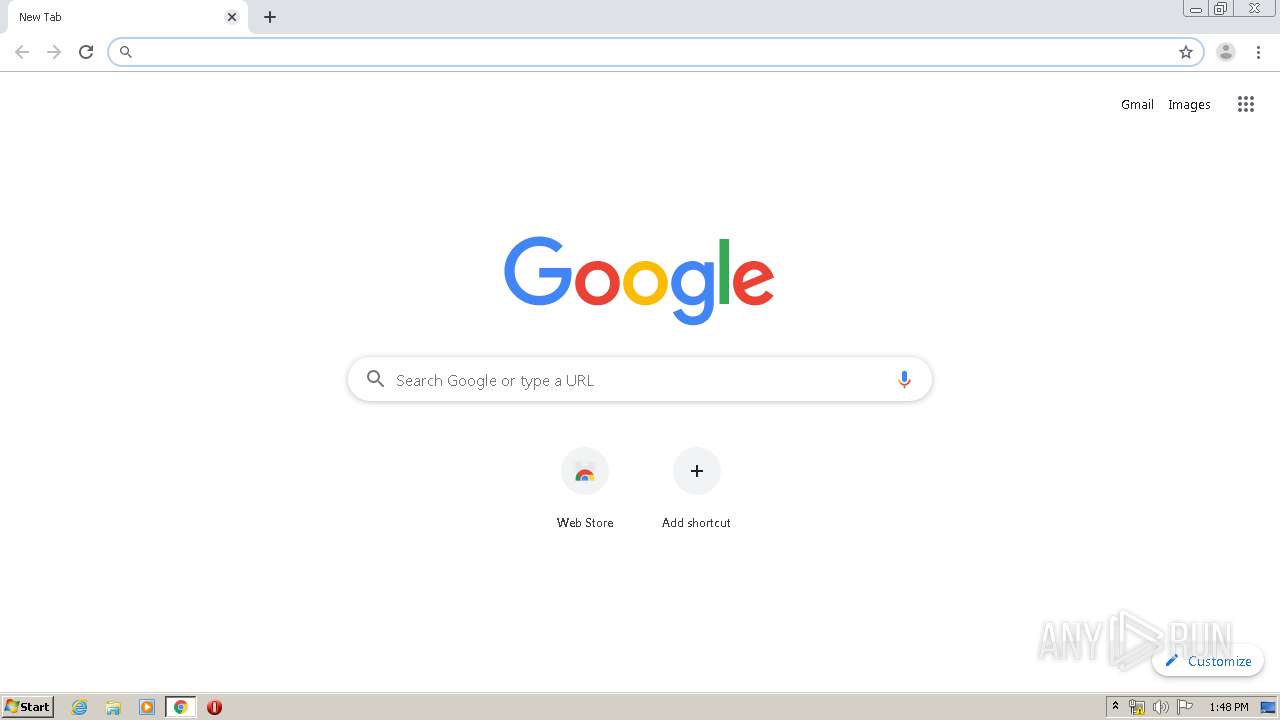
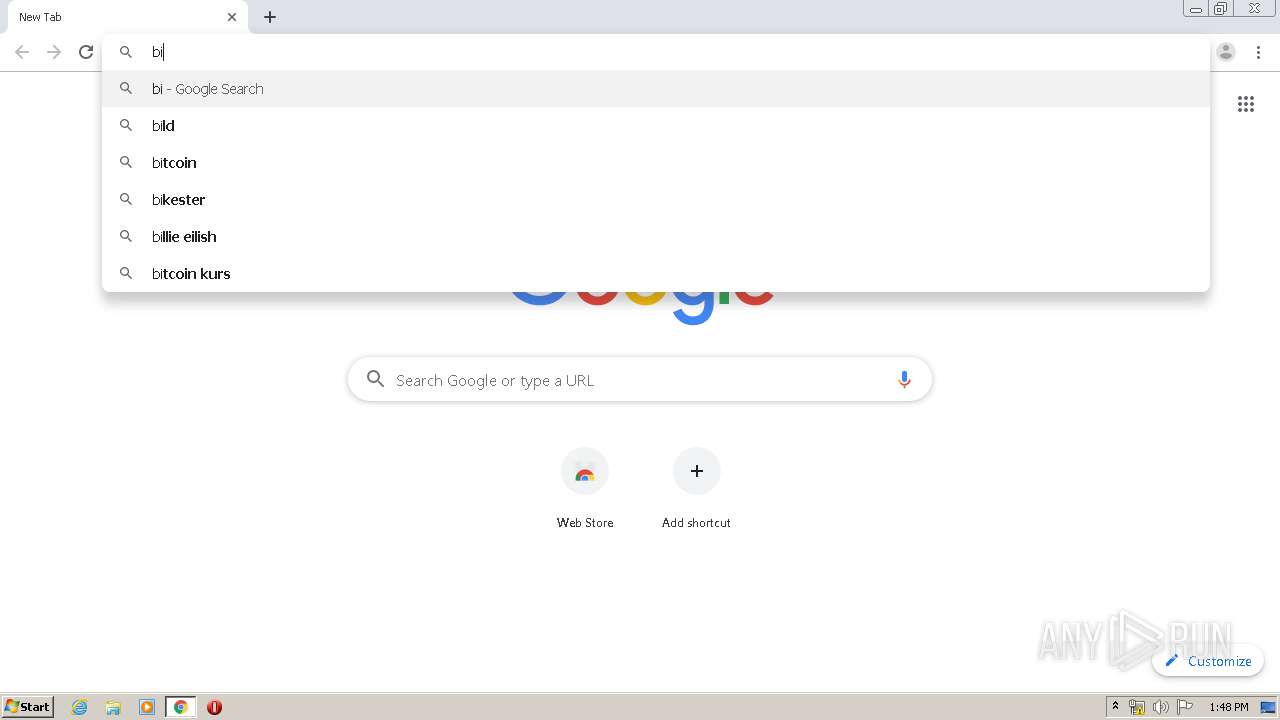
Manual execution by user
- Spolszczenie do KotOR'a.exe (PID: 2688)
- explorer.exe (PID: 2720)
- Spolszczenie do KotOR'a.exe (PID: 1816)
- chrome.exe (PID: 1868)
Reads Internet Cache Settings
- chrome.exe (PID: 3172)
- chrome.exe (PID: 1868)
Creates files in the user directory
- chrome.exe (PID: 1868)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3840)
Reads settings of System Certificates
- chrome.exe (PID: 3840)
- chrome.exe (PID: 2912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
121
Monitored processes
68
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,7823530388000899367,6766234835501189298,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4124432537564156936 --mojo-platform-channel-handle=3360 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,7823530388000899367,6766234835501189298,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5936508266427773542 --mojo-platform-channel-handle=3736 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,7823530388000899367,6766234835501189298,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5552082463769768517 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,7823530388000899367,6766234835501189298,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10846722102327813415 --mojo-platform-channel-handle=3636 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13824579226850691583,15965482429709775105,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3920455787736993743 --mojo-platform-channel-handle=4980 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13824579226850691583,15965482429709775105,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16423376380690925395 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13824579226850691583,15965482429709775105,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13336392315057309613 --mojo-platform-channel-handle=4768 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,7823530388000899367,6766234835501189298,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10566992214658106792 --mojo-platform-channel-handle=3140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,7823530388000899367,6766234835501189298,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17790984673717126064 --mojo-platform-channel-handle=2836 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 968 | "C:\Users\admin\Downloads\Spolszczenie do KotOR'a.exe" | C:\Users\admin\Downloads\Spolszczenie do KotOR'a.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2, 0, 0, 21 Modules
| |||||||||||||||
Total events
3 232
Read events
2 947
Write events
276
Delete events
9
Modification events
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3172-13235316337253375 |
Value: 259 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
11
Suspicious files
207
Text files
409
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED25571-C64.pma | — | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1ec0b686-19ed-4593-8fef-414fd9851aaa.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF15d56a.TMP | text | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15d6d2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
102
DNS requests
56
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2912 | chrome.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
2912 | chrome.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
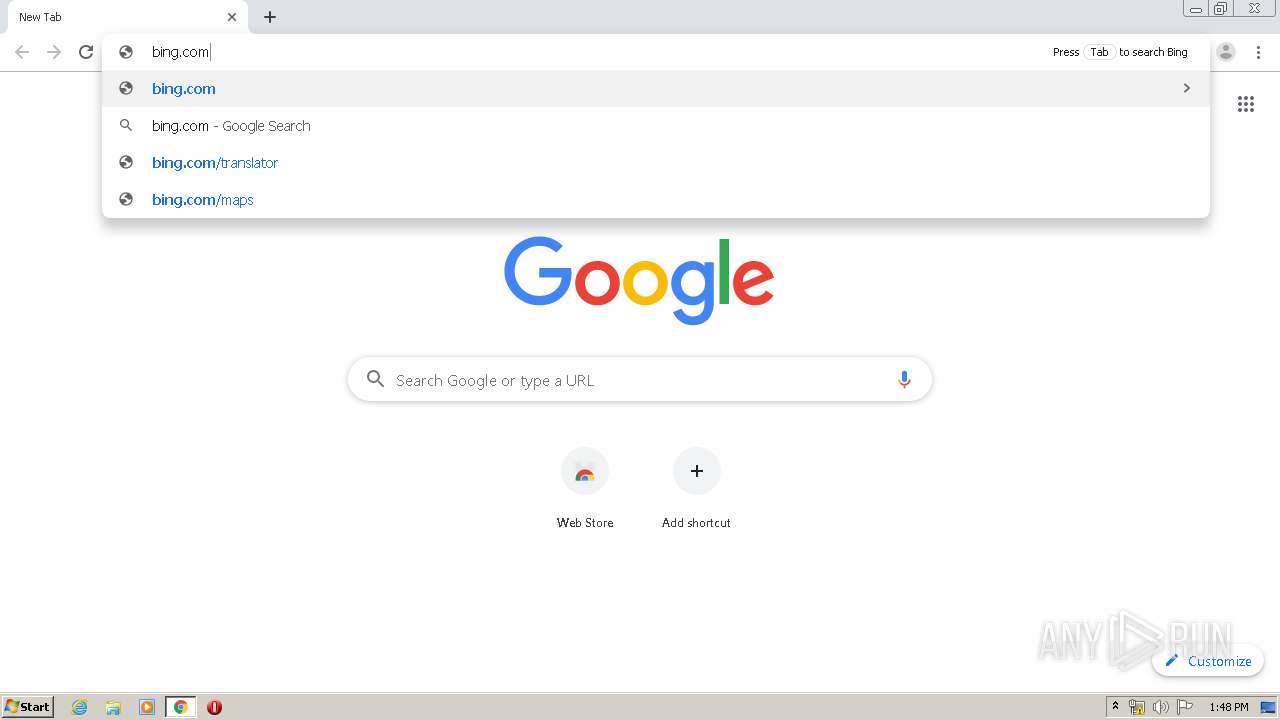
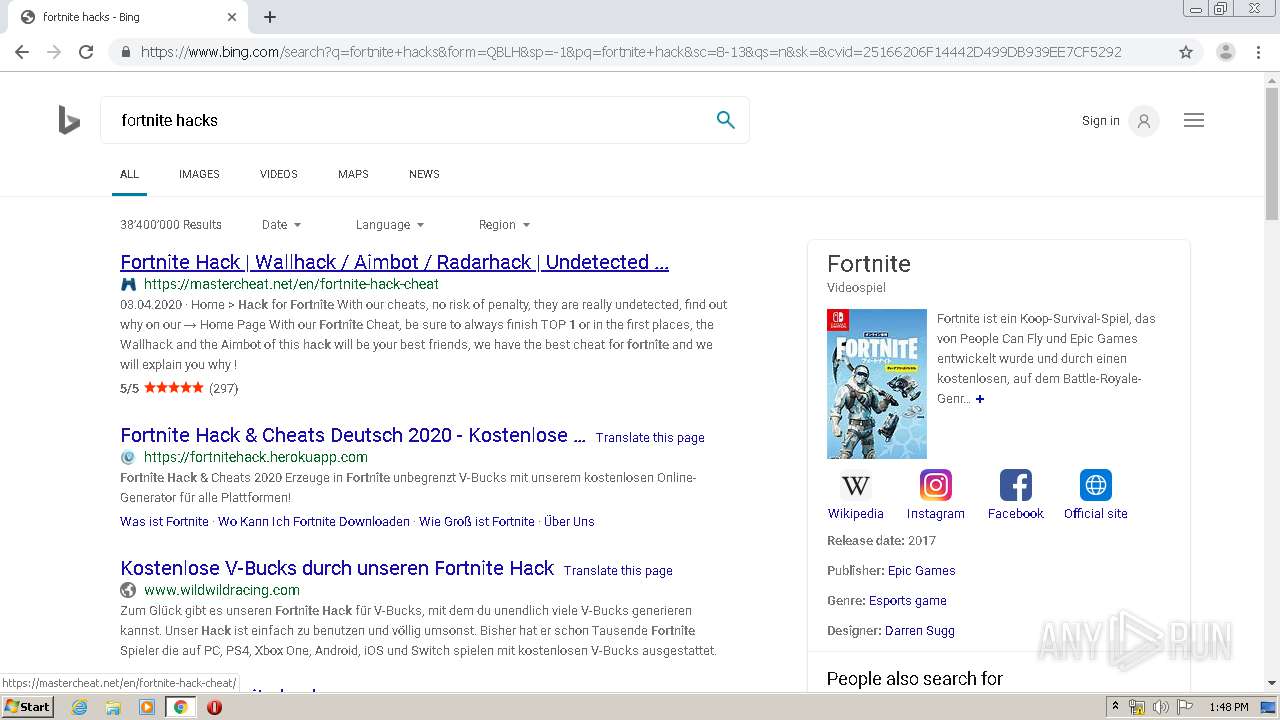
3840 | chrome.exe | GET | 301 | 13.107.21.200:80 | http://bing.com/ | US | — | — | whitelisted |
2912 | chrome.exe | GET | 302 | 108.177.126.100:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 521 b | whitelisted |
2912 | chrome.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
2912 | chrome.exe | GET | 302 | 108.177.126.100:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 526 b | whitelisted |
2912 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
2912 | chrome.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2912 | chrome.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
2912 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | chrome.exe | 108.177.126.94:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2912 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2912 | chrome.exe | 92.122.104.90:443 | steamcommunity.com | Akamai Technologies, Inc. | — | suspicious |
2912 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2912 | chrome.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2912 | chrome.exe | 216.58.212.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2912 | chrome.exe | 216.58.212.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2912 | chrome.exe | 52.222.157.14:443 | d10lumateci472.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
2912 | chrome.exe | 46.166.139.223:80 | www98.zippyshare.com | NForce Entertainment B.V. | NL | malicious |
2912 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
steamcommunity.com |
| whitelisted |
accounts.google.com |
| shared |
ocsp.digicert.com |
| whitelisted |
steamcommunity-a.akamaihd.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.google.com |
| malicious |
www98.zippyshare.com |
| suspicious |
d10lumateci472.cloudfront.net |
| whitelisted |