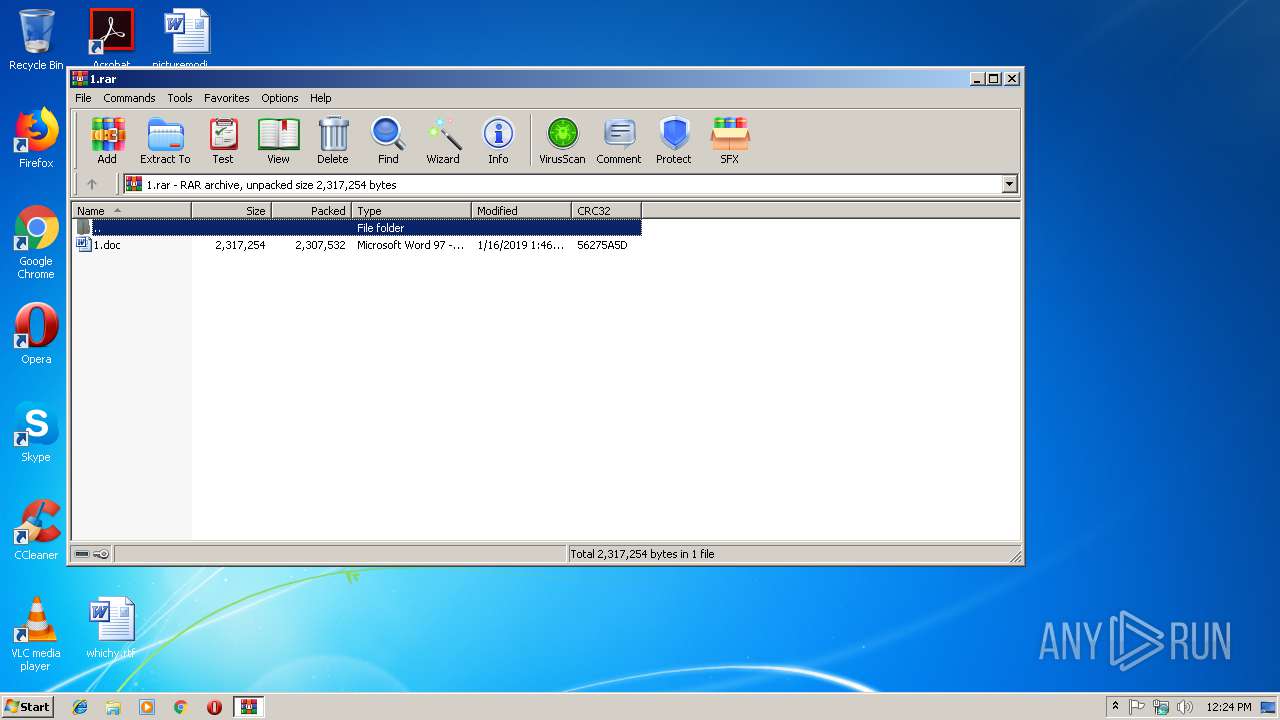
| File name: | 1.rar |
| Full analysis: | https://app.any.run/tasks/1a77ef3e-bd63-4263-90a7-fb5867d86555 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 12:24:22 |
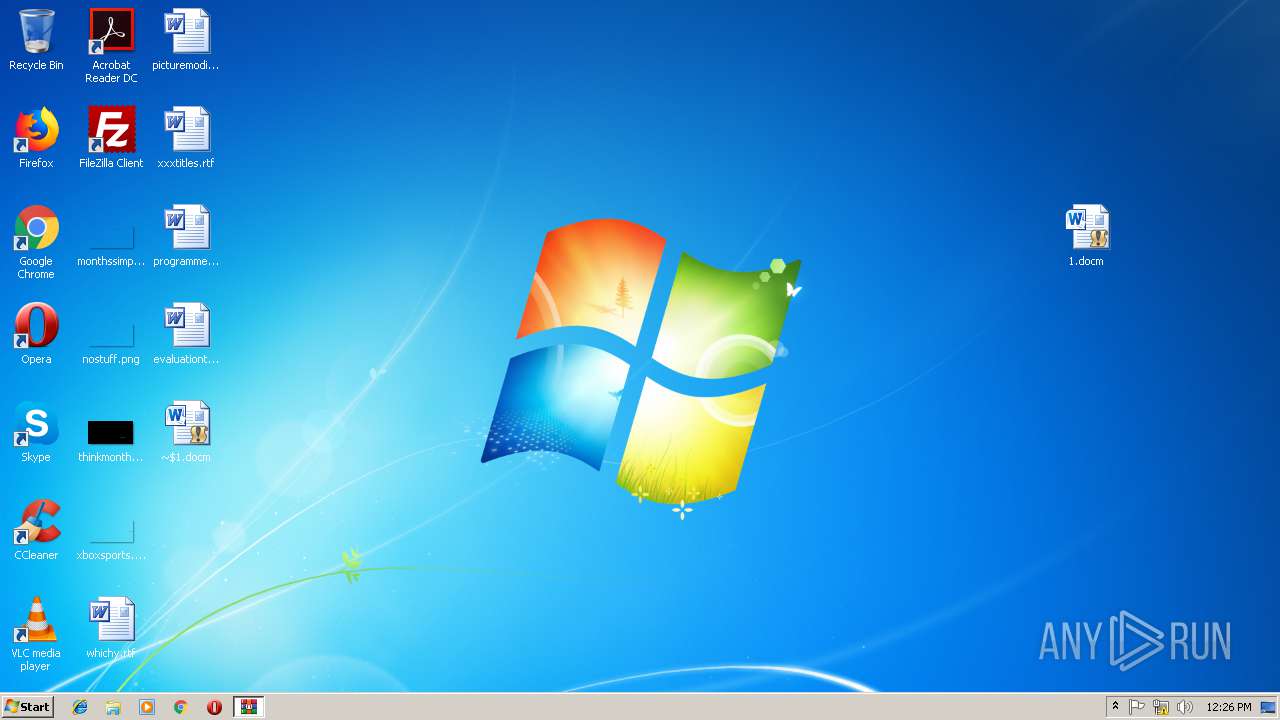
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F82AB700CD2FB98D56415DF0DEAB4298 |
| SHA1: | 692EE6DF56CBF1CC77C68D257535E6C6E727C55B |
| SHA256: | 6D8194234CA6BB6A49C182E146D6C03ABF6C625DCE9433C94F491AB40B8A034A |
| SSDEEP: | 49152:mborzAL58MZ7Vj+plKdCa6LdMqOW3YZOvWrNwOQ796bclXI:EcAL5rVj+pla96BMZaluSx6Ql4 |
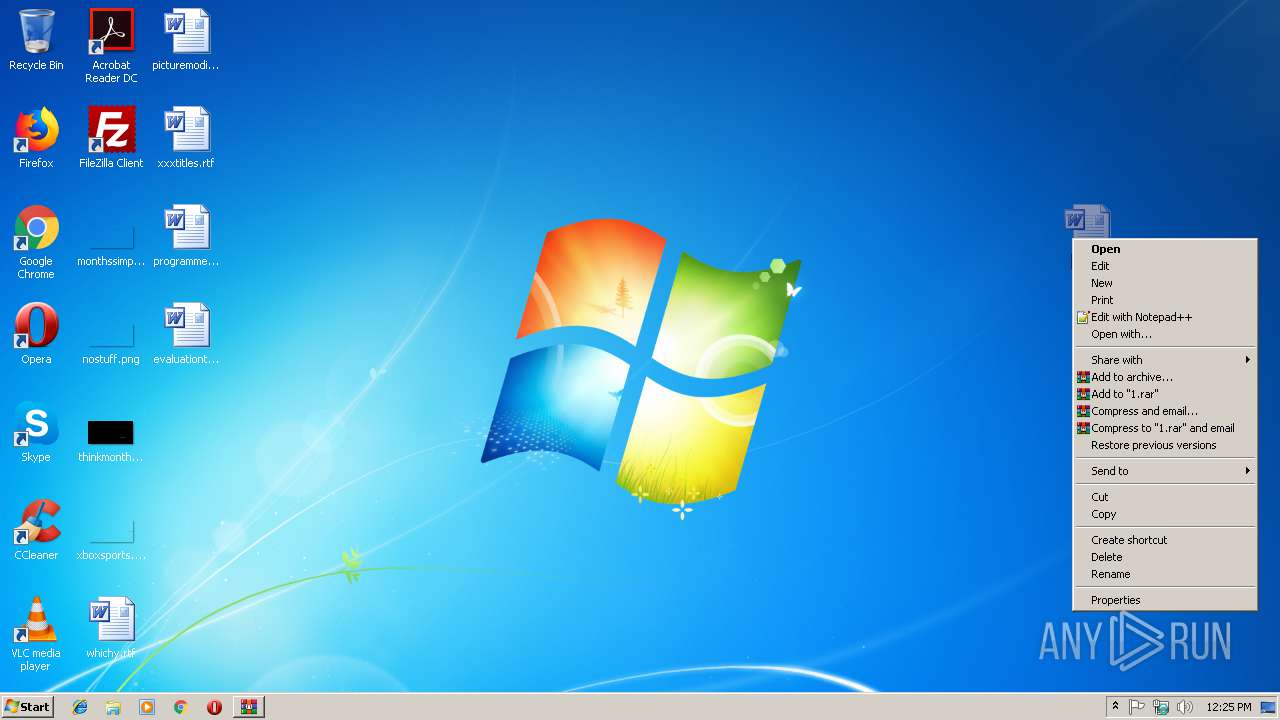
MALICIOUS
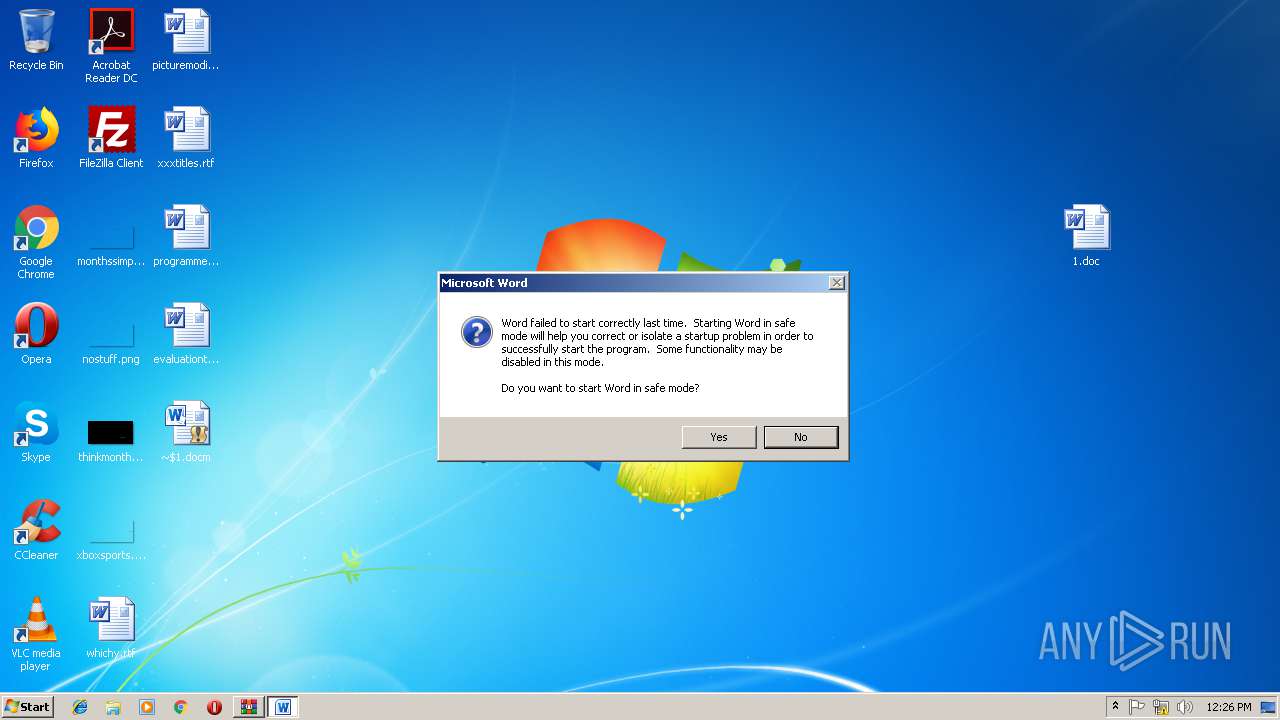
Changes the autorun value in the registry
- reg.exe (PID: 3524)
- reg.exe (PID: 3576)
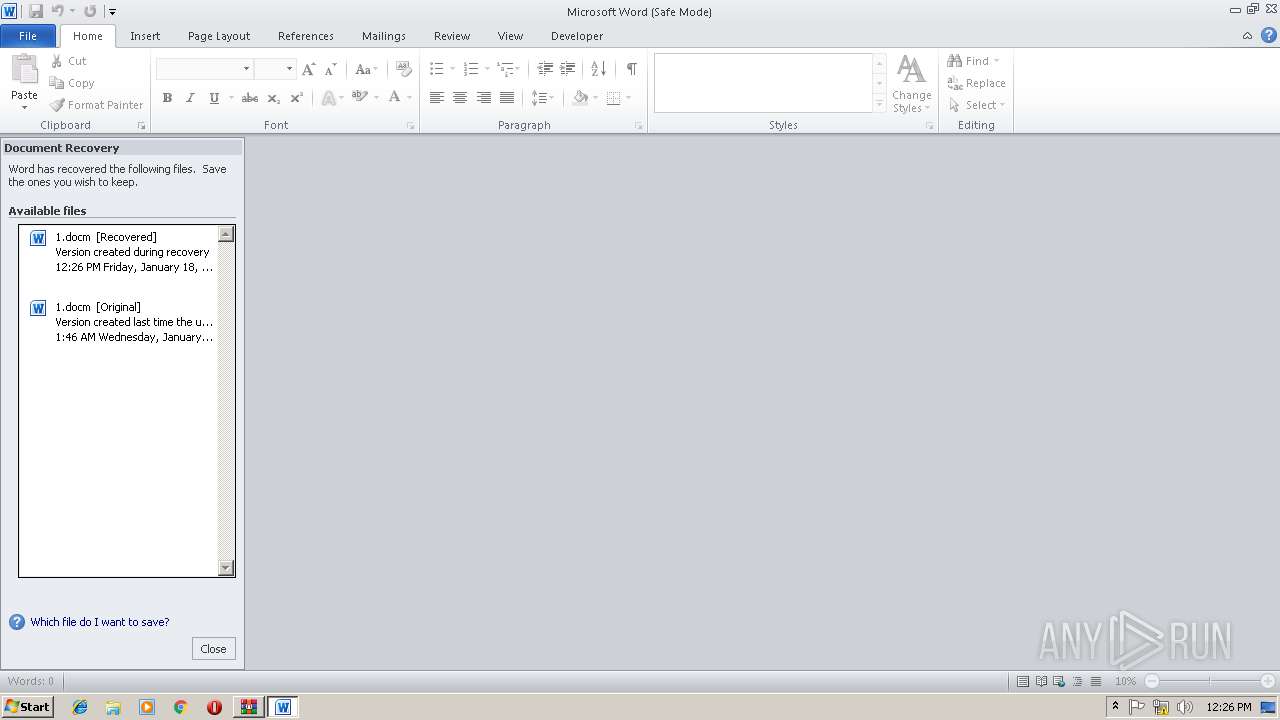
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2756)
- WINWORD.EXE (PID: 3888)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2756)
- WINWORD.EXE (PID: 3888)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2756)
- WINWORD.EXE (PID: 3888)
SUSPICIOUS
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3448)
- cmd.exe (PID: 2856)
INFO
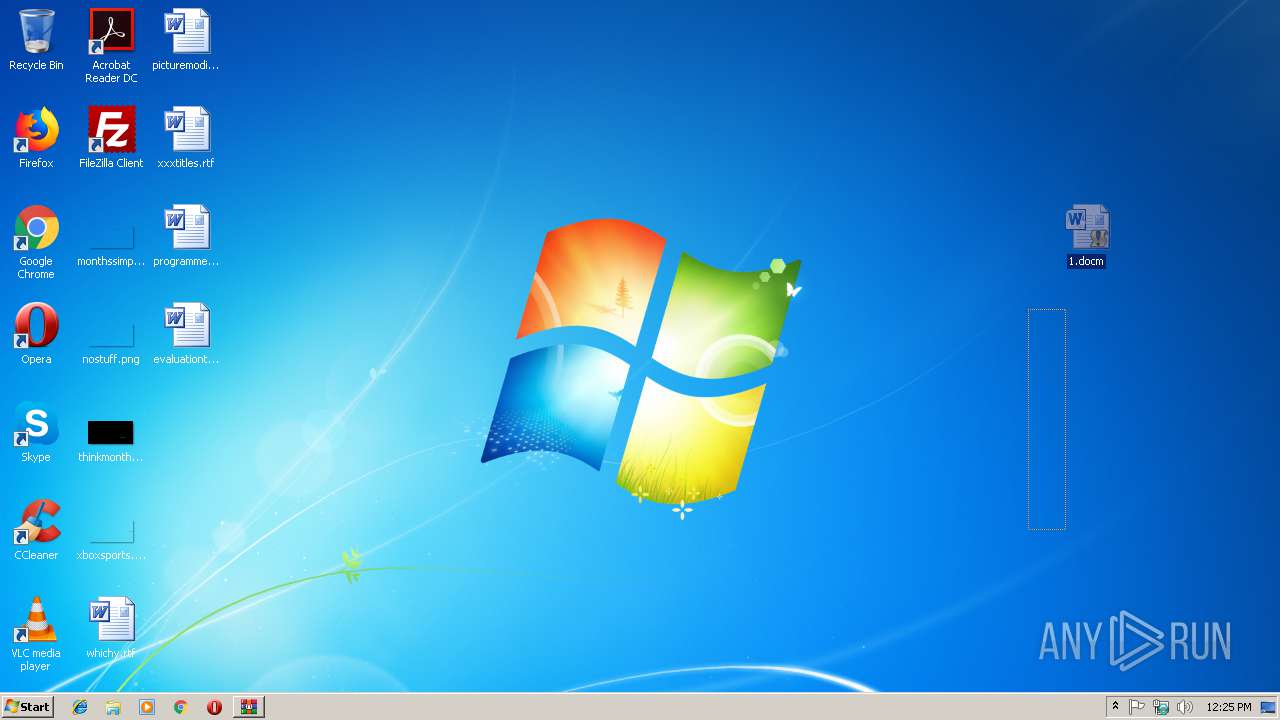
Creates files in the user directory
- WINWORD.EXE (PID: 2756)
- WINWORD.EXE (PID: 3888)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3424)
- WINWORD.EXE (PID: 3888)
- WINWORD.EXE (PID: 2756)
Reads settings of System Certificates
- WINWORD.EXE (PID: 3424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
48
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
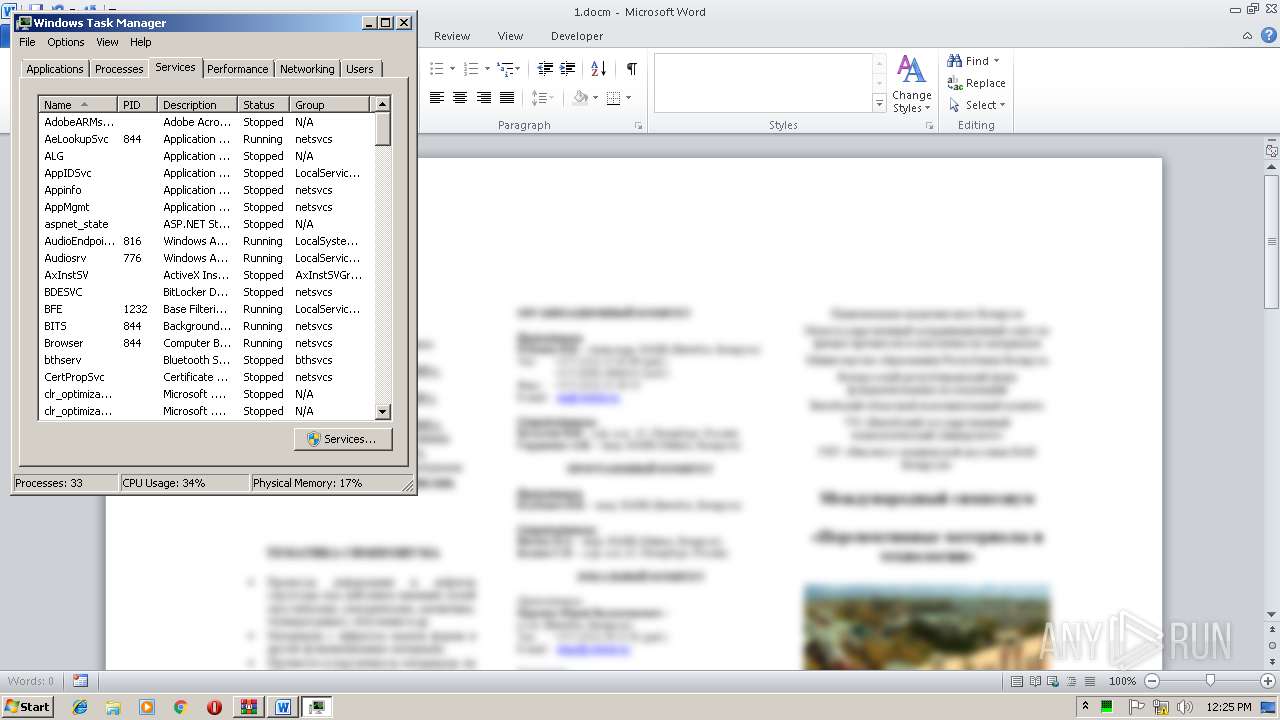
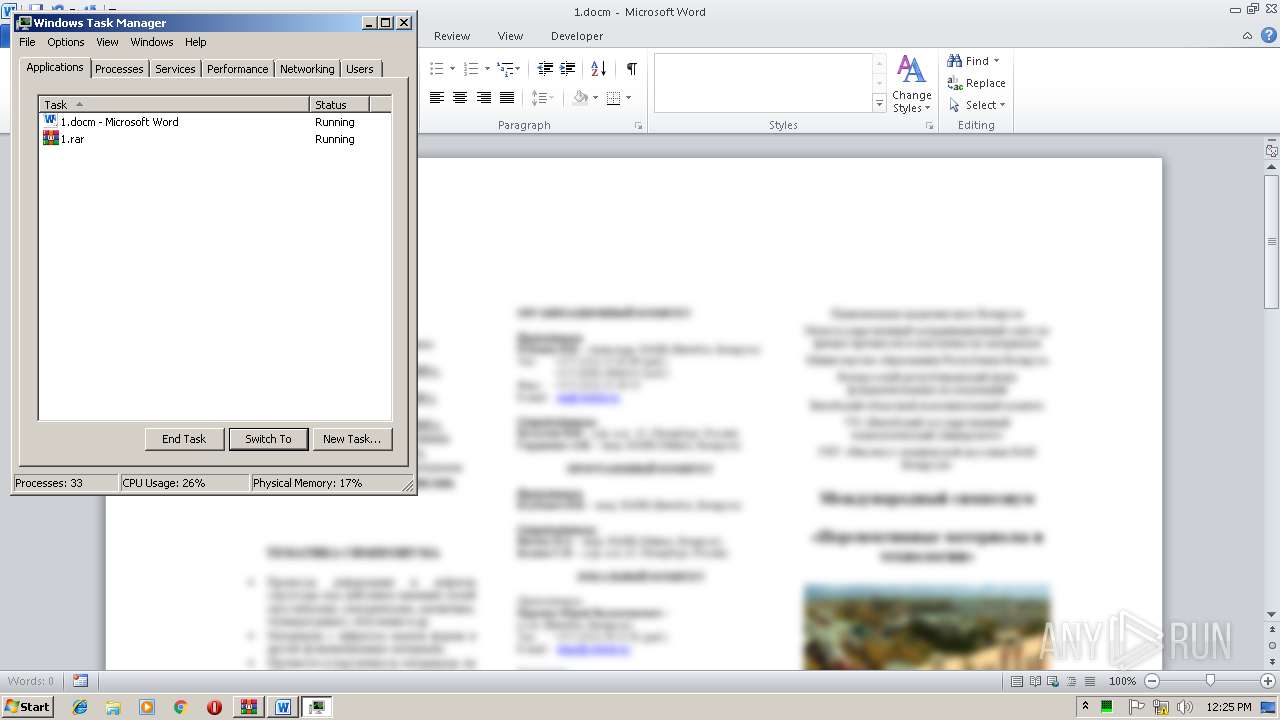
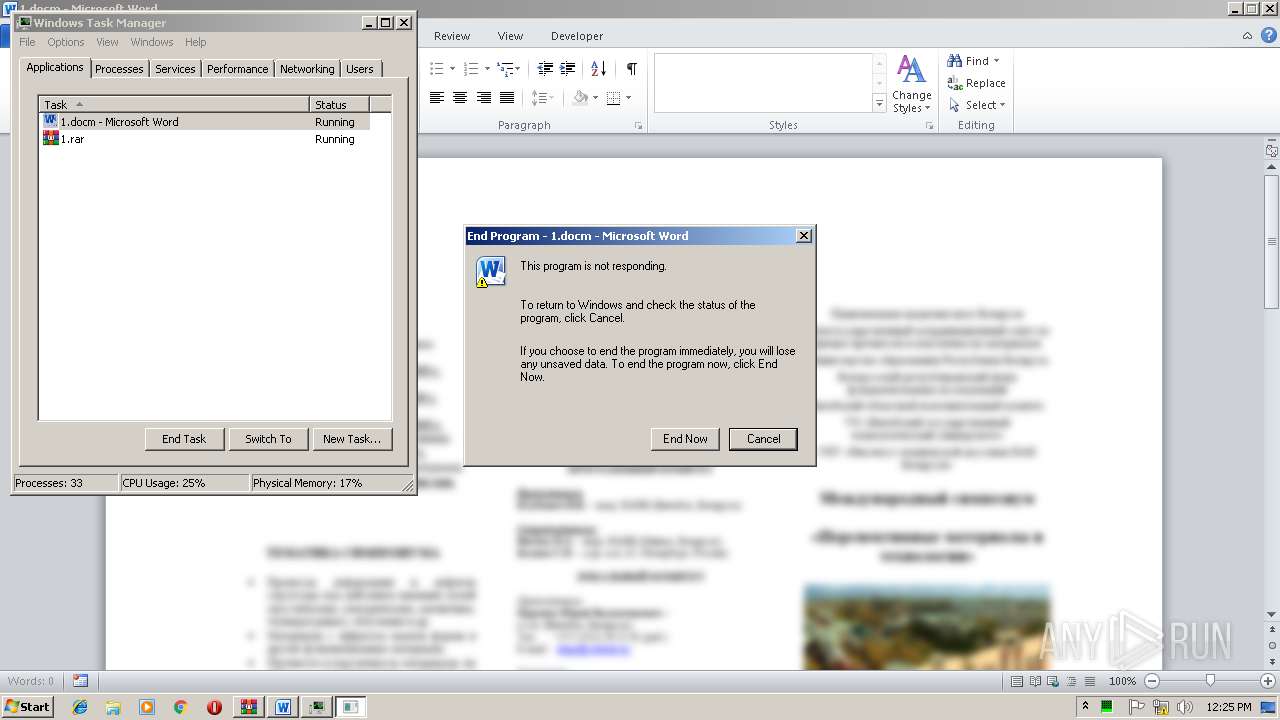
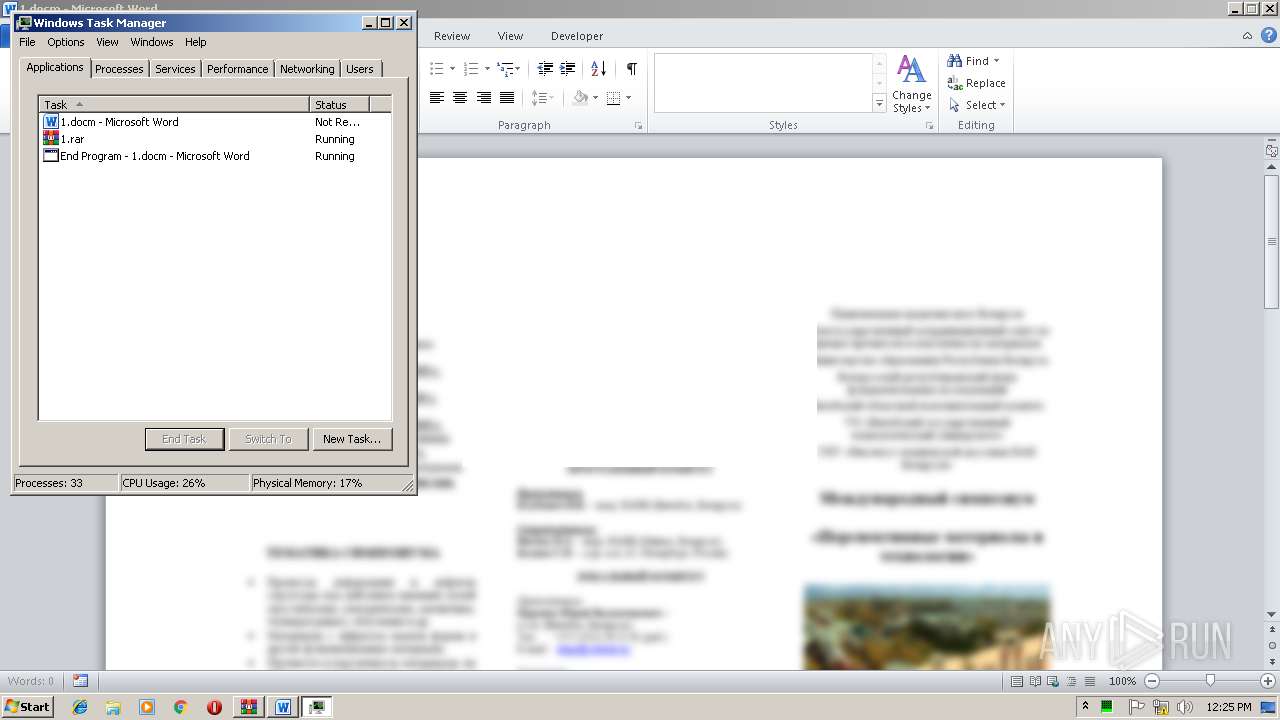
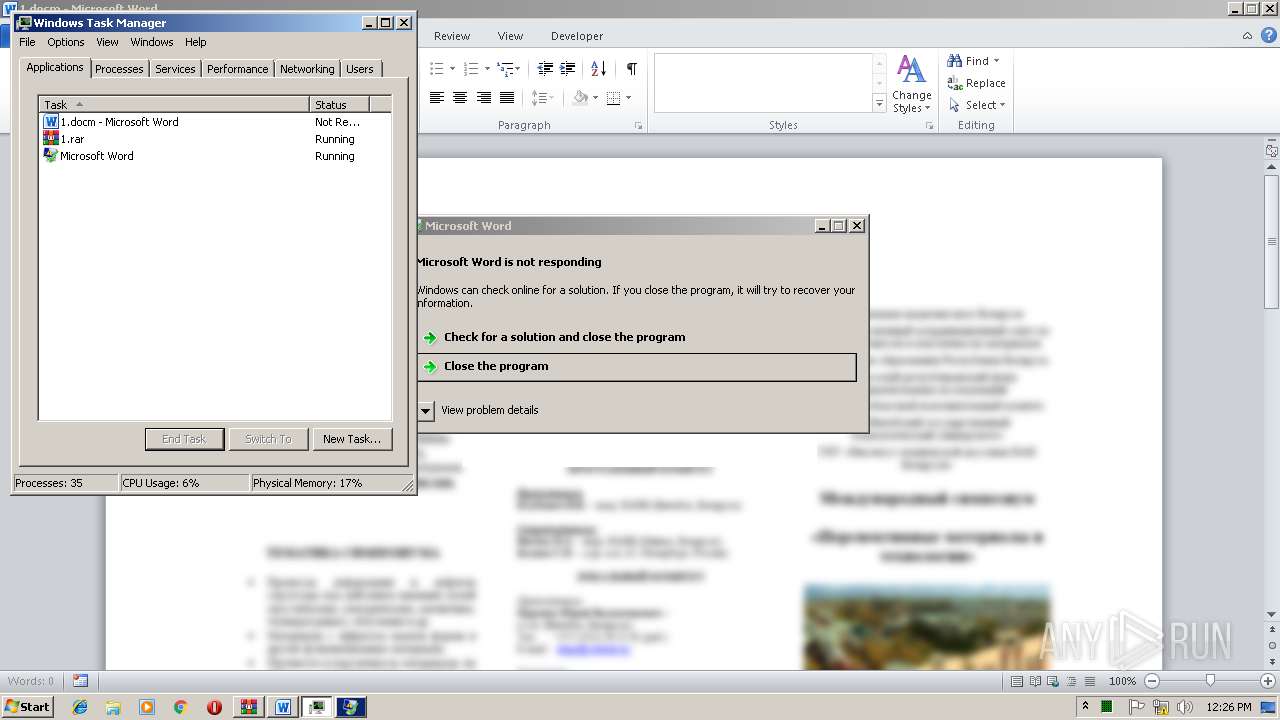
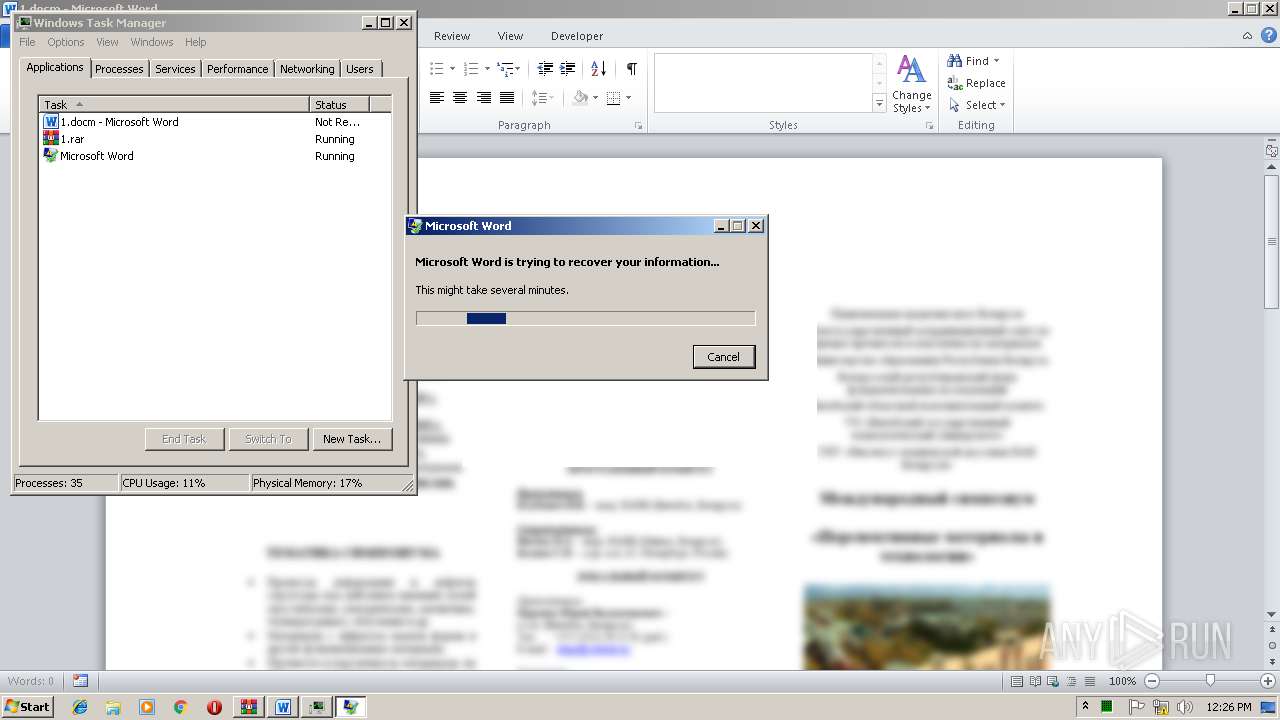
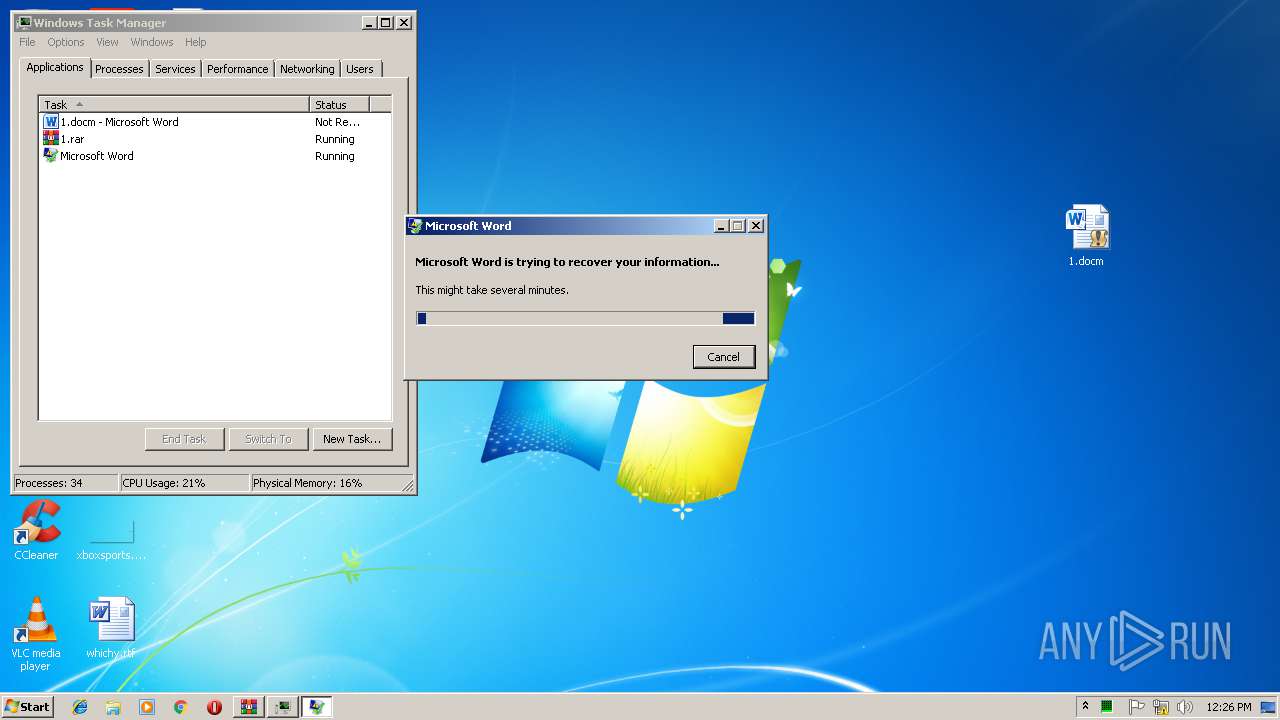
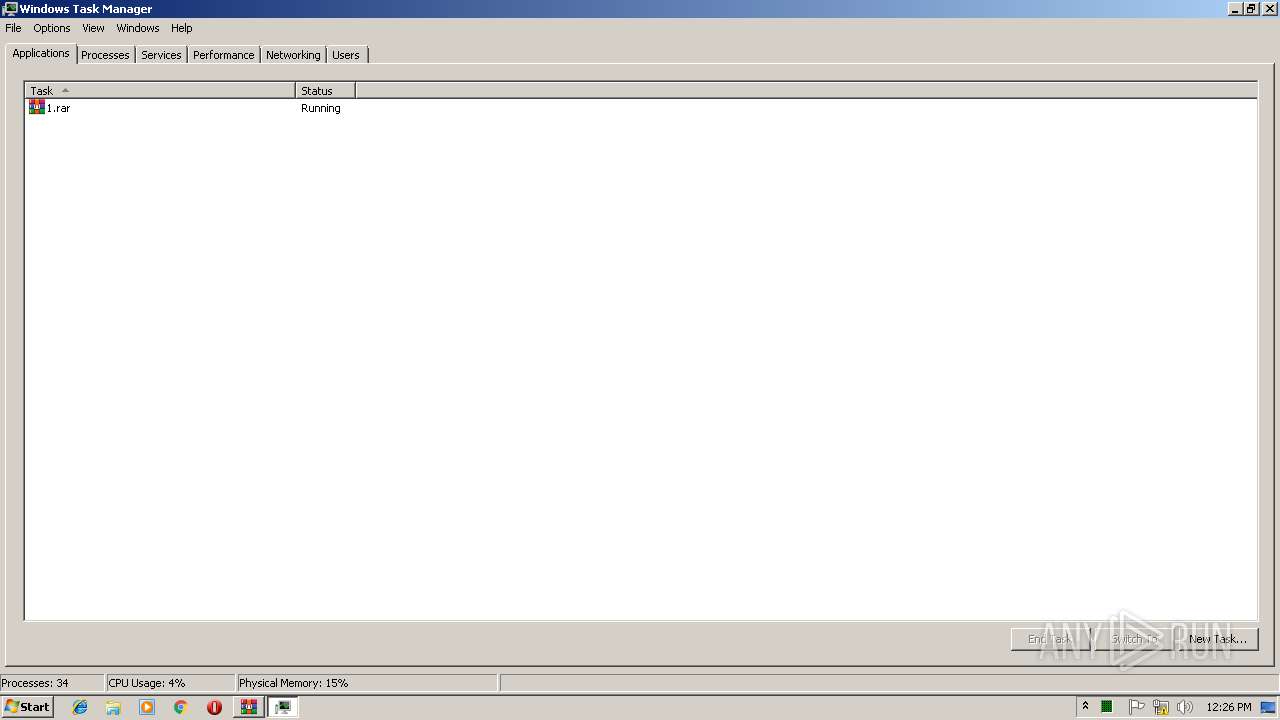
| 2120 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
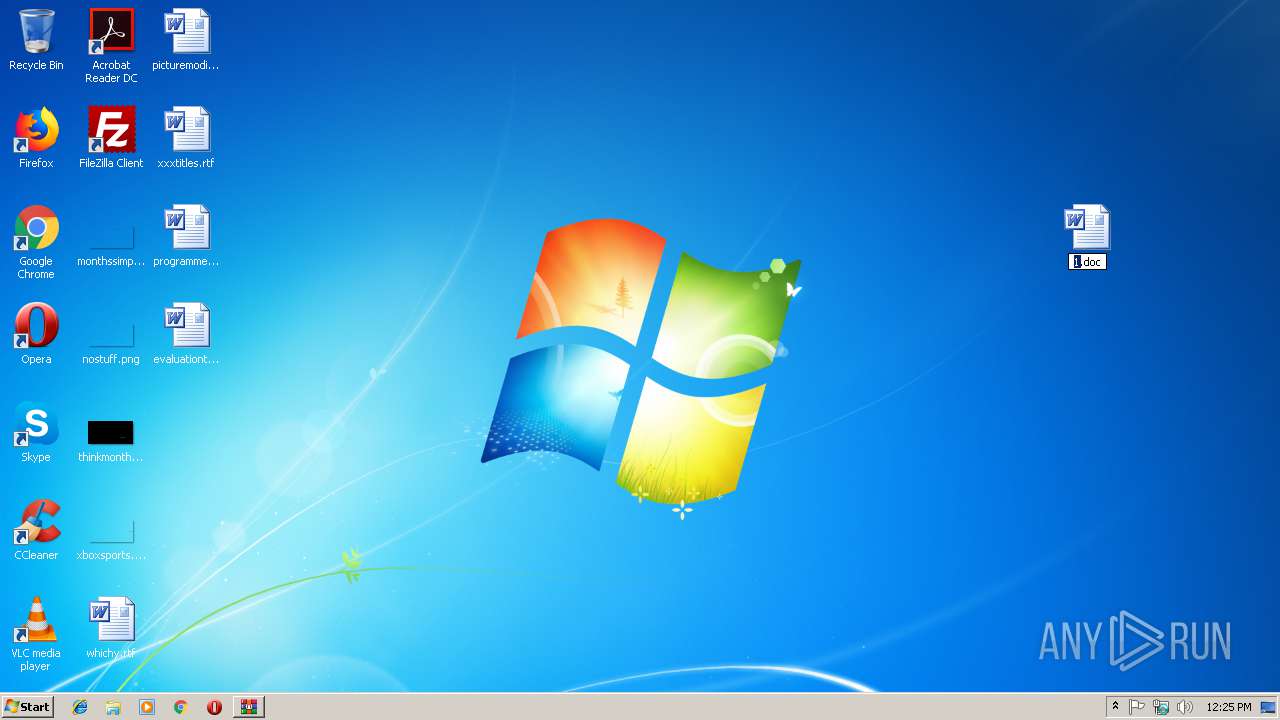
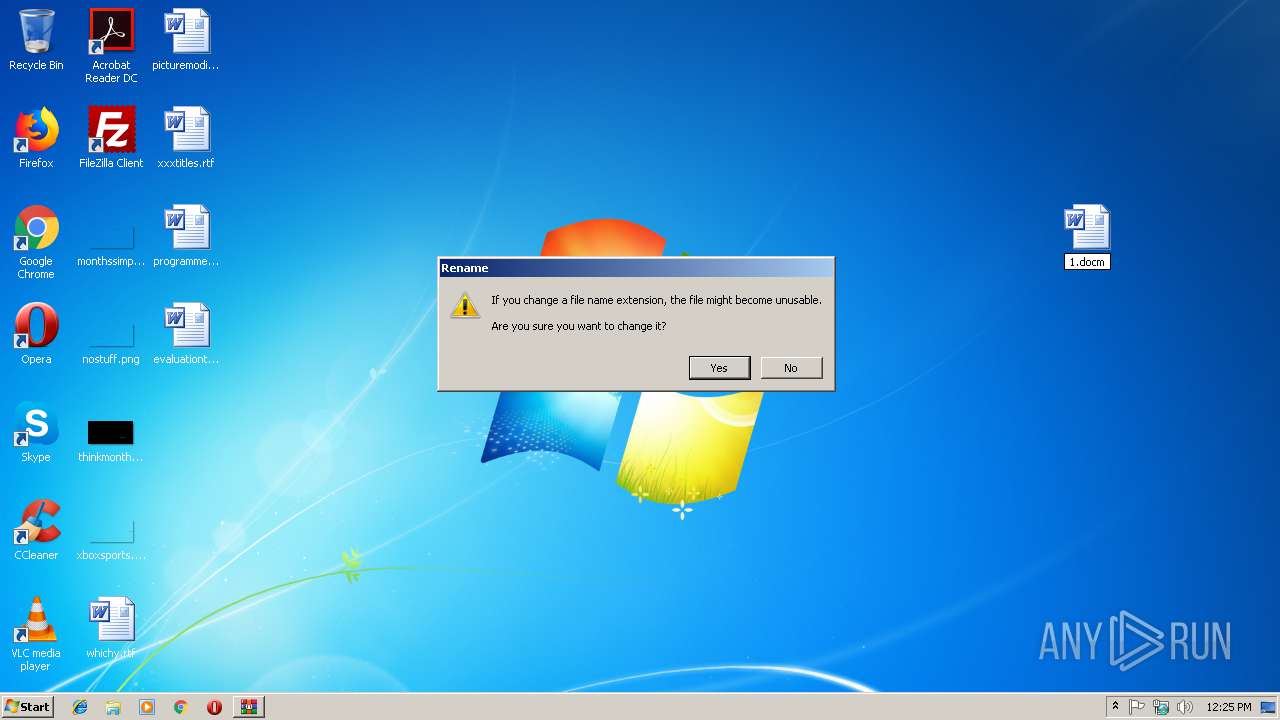
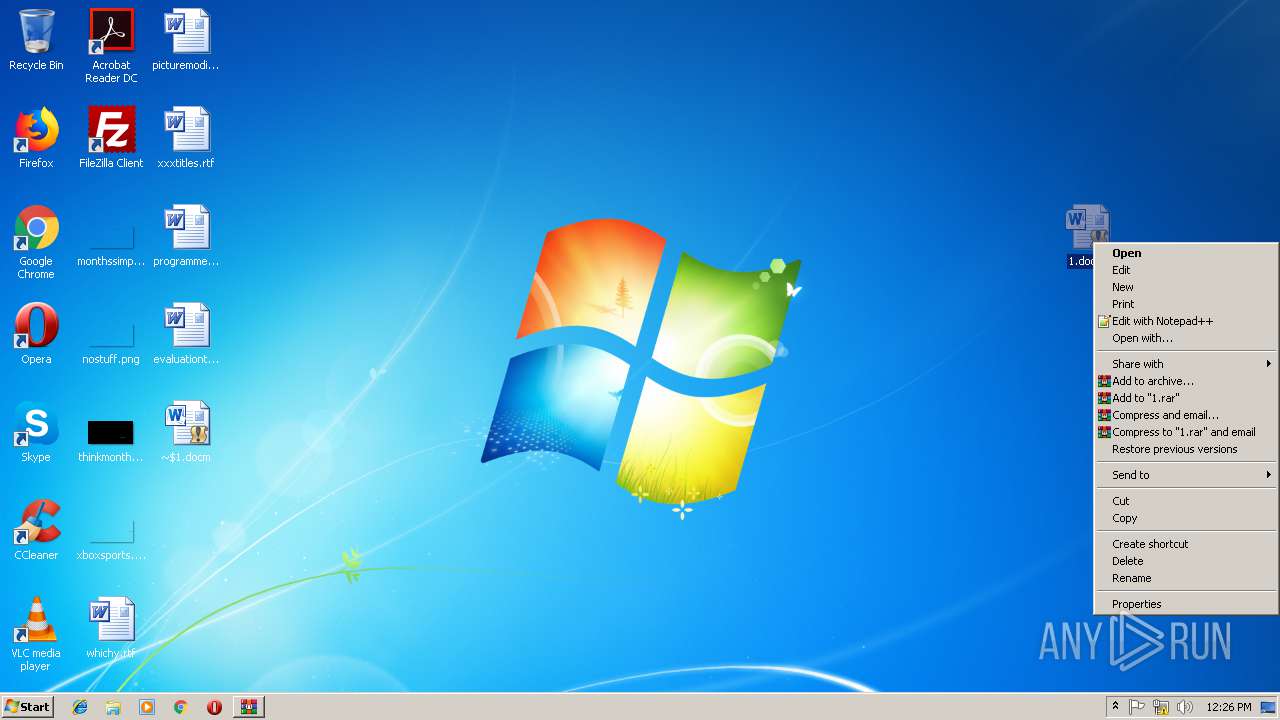
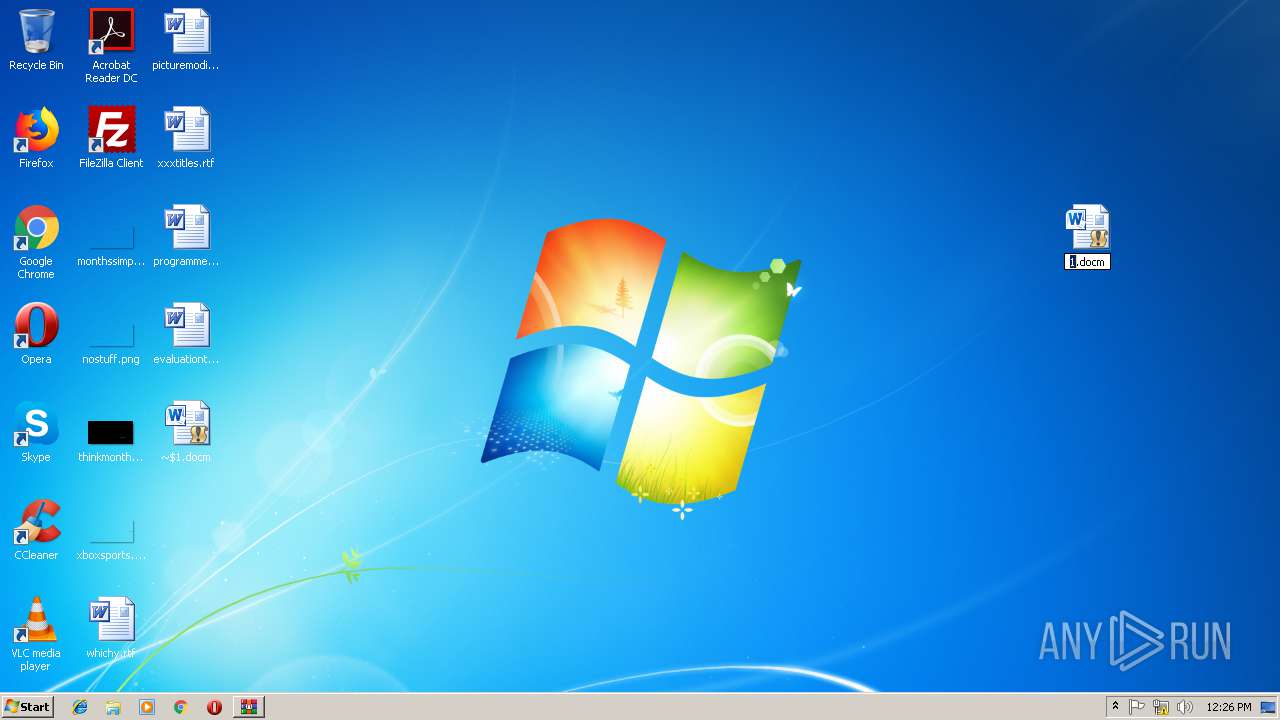
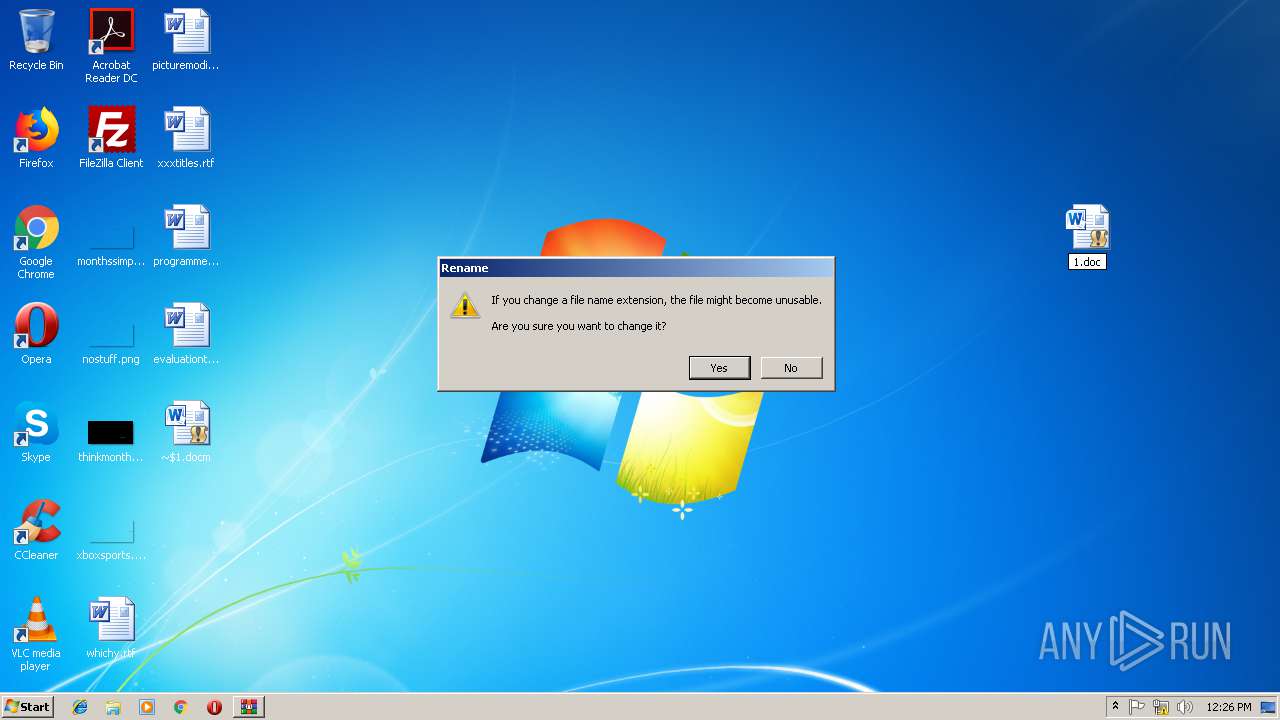
| 2756 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\1.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2856 | "C:\Windows\System32\cmd.exe" /k %Windir%\system32\reg.exe IMPORT %appdata%\ws.reg | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3424 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\1.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3448 | "C:\Windows\System32\cmd.exe" /k %Windir%\system32\reg.exe IMPORT %appdata%\ws.reg | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3524 | C:\Windows\system32\reg.exe IMPORT C:\Users\admin\AppData\Roaming\ws.reg | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3552 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\1.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3576 | C:\Windows\system32\reg.exe IMPORT C:\Users\admin\AppData\Roaming\ws.reg | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3888 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\1.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 064
Read events
2 193
Write events
843
Delete events
28
Modification events
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\1.rar | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | h$ |
Value: 7F682400C40A0000010000000000000000000000 | |||
| (PID) Process: | (2756) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
Executable files
2
Suspicious files
81
Text files
7
Unknown types
37
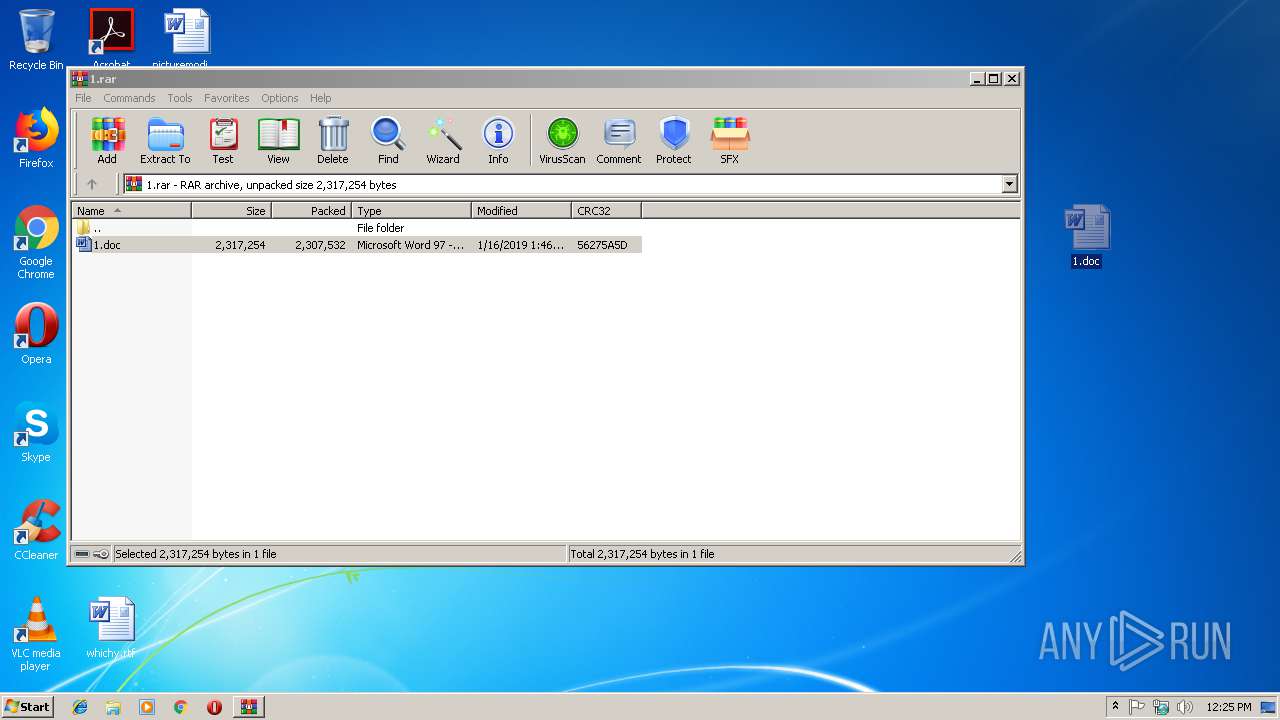
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3552.30288\1.doc | — | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Word\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{9731030F-DFC8-405B-AB60-C461802A78A6}.tmp | — | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B83E9CE9-FAB9-42C7-809A-4A2EBCE54789}.tmp | — | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{76182A57-D665-4893-8519-B04853DEB758}.tmp | — | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF14B0C3EA9113B36C.TMP | — | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9B31FCC0.png | — | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\457926FB.png | — | |
MD5:— | SHA256:— | |||
| 2756 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF4ED22508041F8D82.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
9
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3424 | WINWORD.EXE | GET | 200 | 2.16.186.10:80 | http://clienttemplates.content.office.net/support/templates/en-us/tp01790489.cab | unknown | compressed | 65.6 Kb | whitelisted |
3424 | WINWORD.EXE | GET | 200 | 2.16.186.10:80 | http://clienttemplates.content.office.net/support/templates/en-us/tp01793888.cab | unknown | compressed | 22.0 Kb | whitelisted |
3424 | WINWORD.EXE | GET | 200 | 2.16.186.10:80 | http://clienttemplates.content.office.net/support/templates/en-us/tp01793064.cab | unknown | compressed | 40.0 Kb | whitelisted |
3424 | WINWORD.EXE | GET | 200 | 2.16.186.10:80 | http://clienttemplates.content.office.net/support/templates/en-us/tp01793060.cab | unknown | compressed | 43.4 Kb | whitelisted |
3424 | WINWORD.EXE | GET | 200 | 2.16.186.10:80 | http://clienttemplates.content.office.net/support/templates/en-us/tp01793058.cab | unknown | compressed | 39.7 Kb | whitelisted |
3424 | WINWORD.EXE | GET | 200 | 2.16.186.10:80 | http://clienttemplates.content.office.net/support/templates/en-us/tp01793889.cab | unknown | compressed | 19.9 Kb | whitelisted |
3424 | WINWORD.EXE | GET | 200 | 2.16.186.10:80 | http://clienttemplates.content.office.net/support/templates/en-us/tp01790491.cab | unknown | compressed | 248 Kb | whitelisted |
3424 | WINWORD.EXE | GET | 200 | 2.16.186.10:80 | http://clienttemplates.content.office.net/support/templates/en-us/tp01790493.cab | unknown | compressed | 818 Kb | whitelisted |
3424 | WINWORD.EXE | GET | 200 | 2.16.186.10:80 | http://clienttemplates.content.office.net/support/templates/en-us/tp01790492.cab | unknown | compressed | 945 Kb | whitelisted |
3424 | WINWORD.EXE | GET | 200 | 52.109.88.8:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | NL | xml | 1.99 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3424 | WINWORD.EXE | 52.109.88.8:80 | office14client.microsoft.com | Microsoft Corporation | NL | whitelisted |
3424 | WINWORD.EXE | 172.227.98.8:443 | officestore.microsoft.com | Akamai Technologies, Inc. | US | whitelisted |
3424 | WINWORD.EXE | 2.16.186.10:80 | clienttemplates.content.office.net | Akamai International B.V. | — | whitelisted |
3424 | WINWORD.EXE | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
3424 | WINWORD.EXE | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
3424 | WINWORD.EXE | 104.107.216.163:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
office14client.microsoft.com |
| whitelisted |
officestore.microsoft.com |
| whitelisted |
clienttemplates.content.office.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |