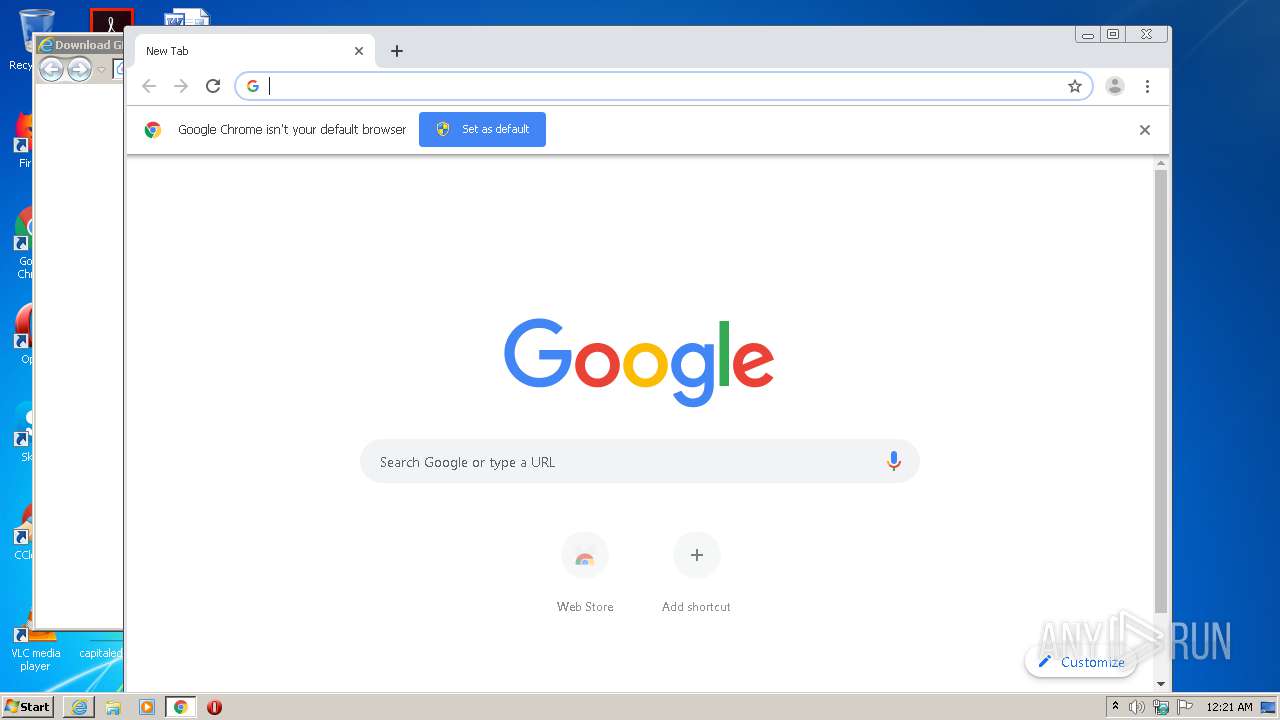
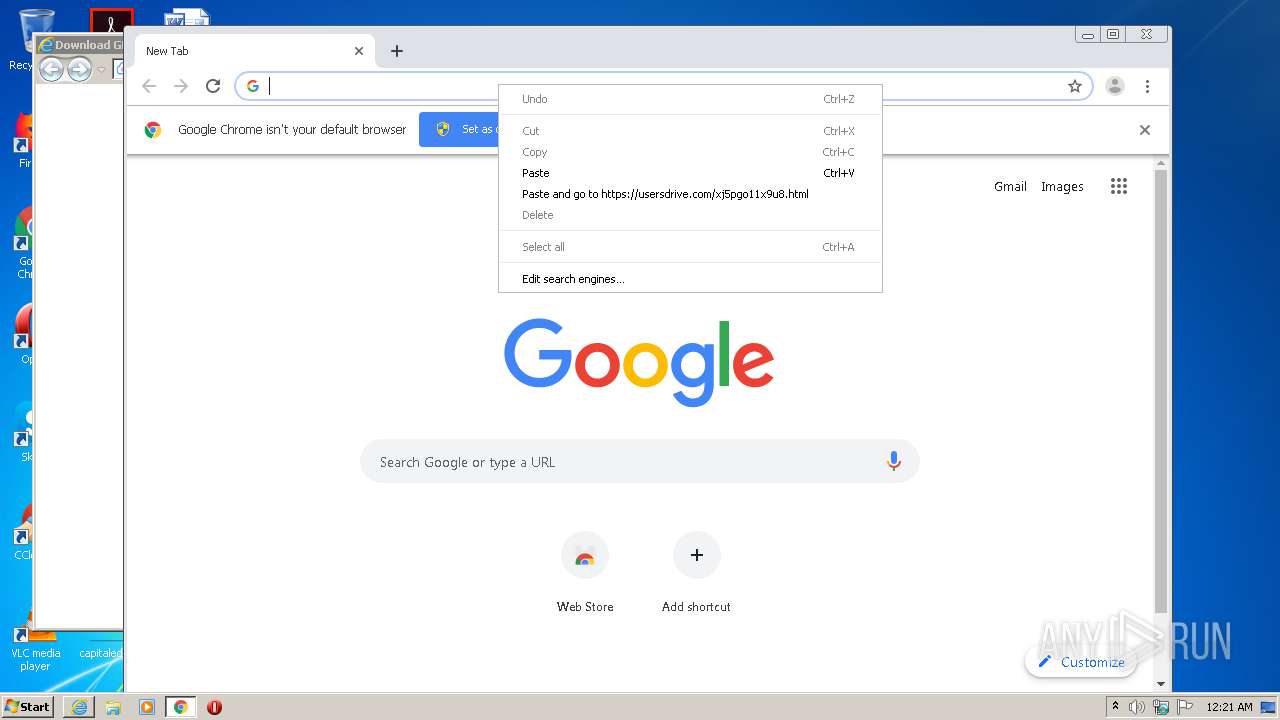
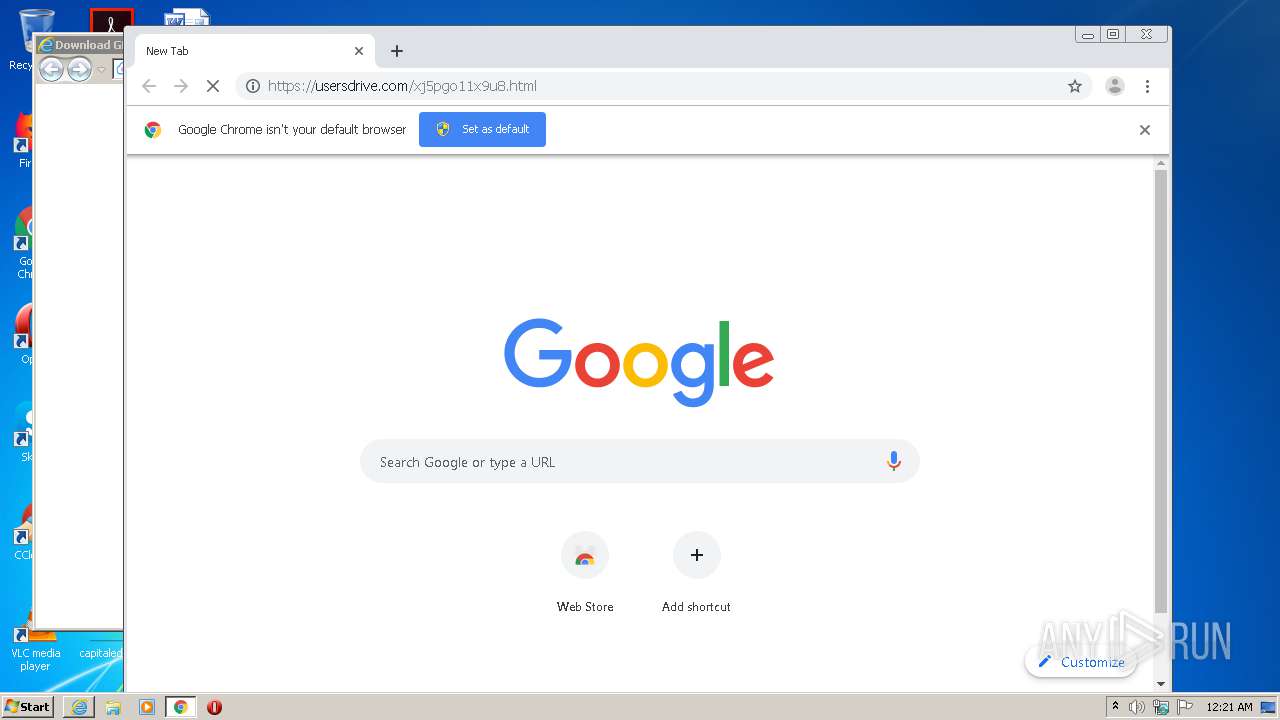
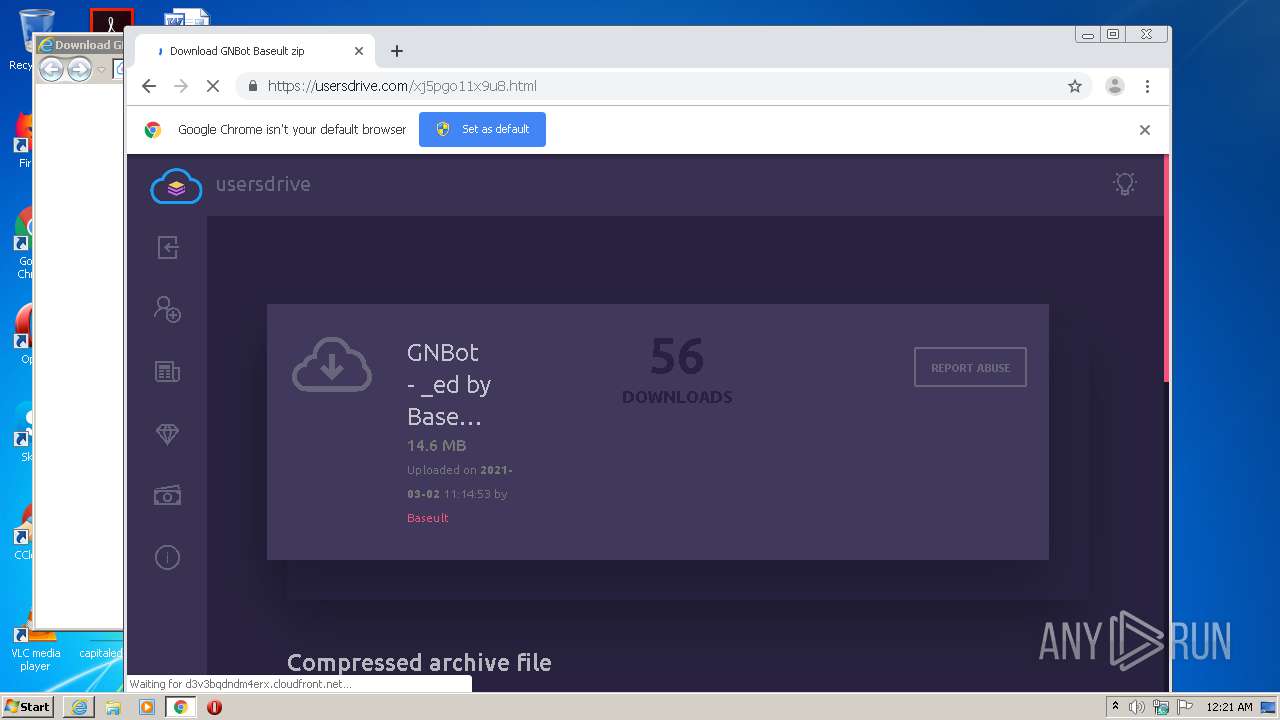
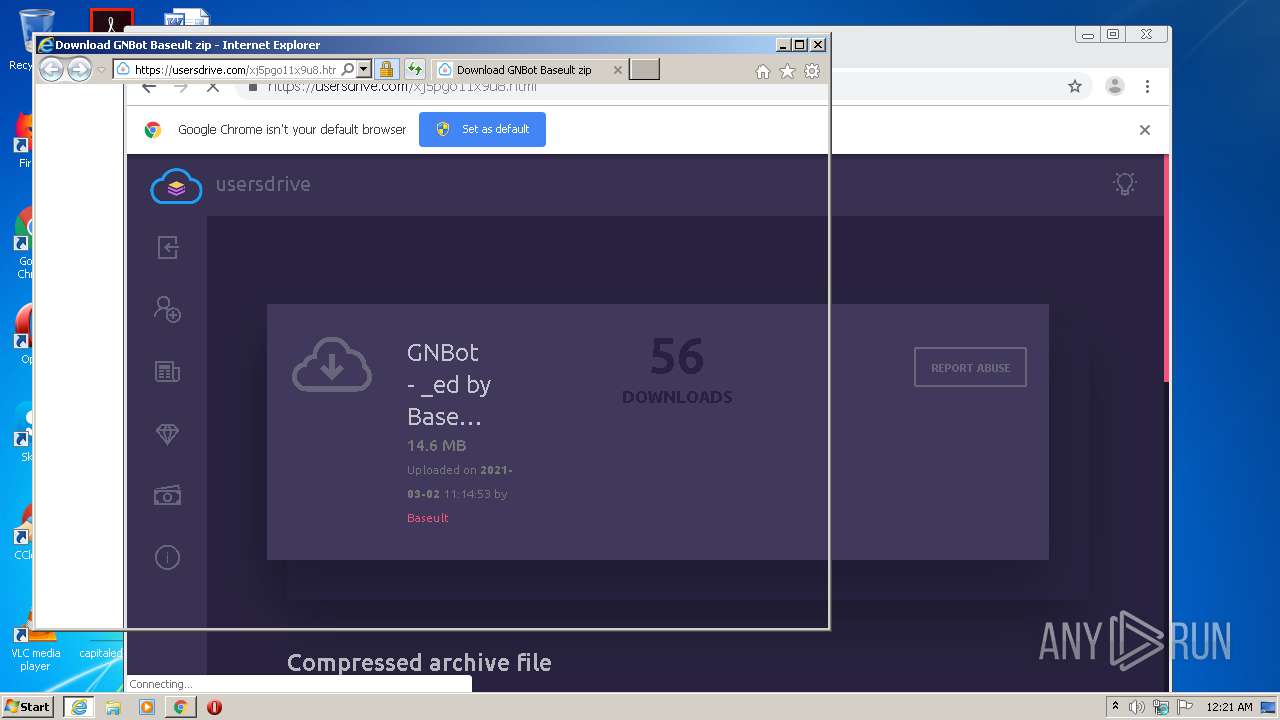
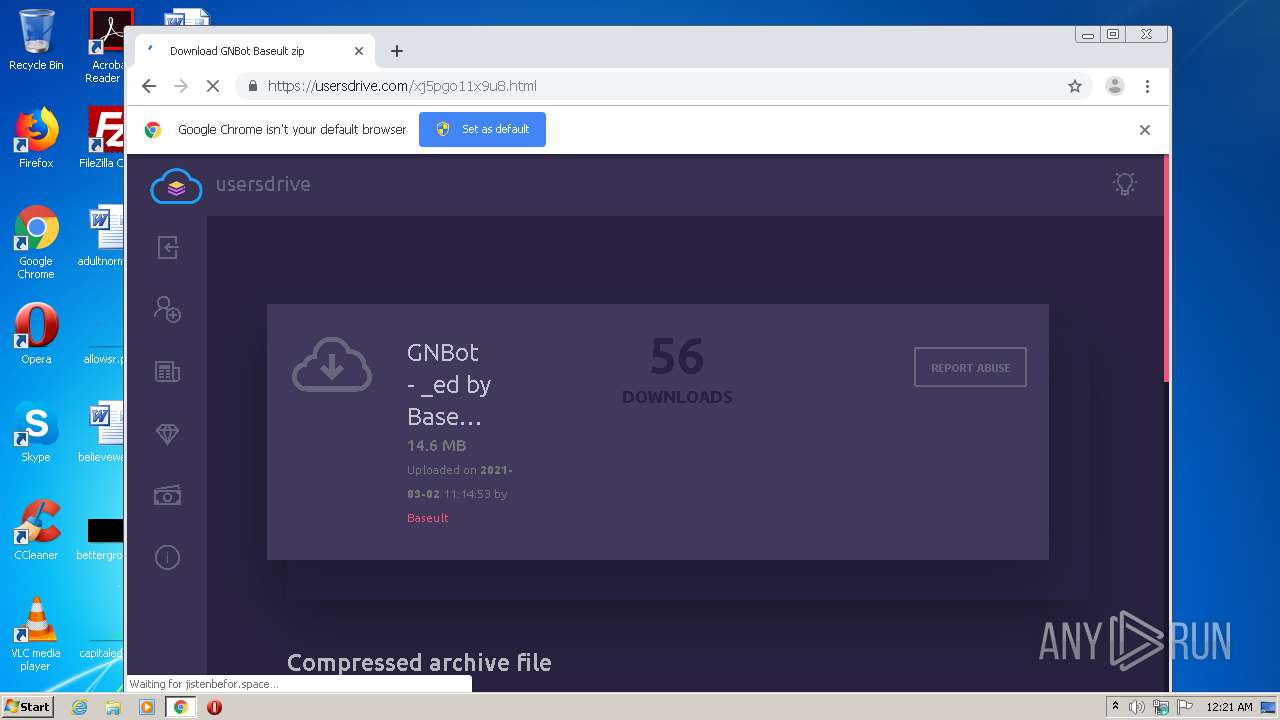
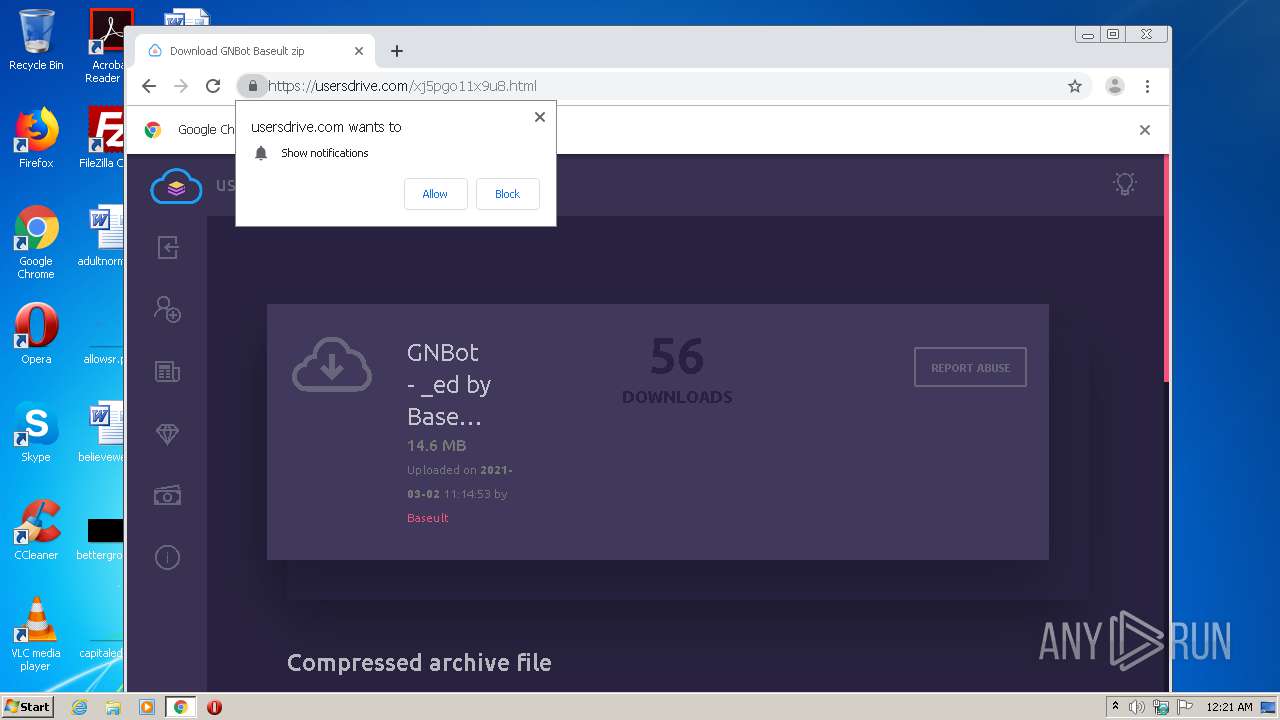
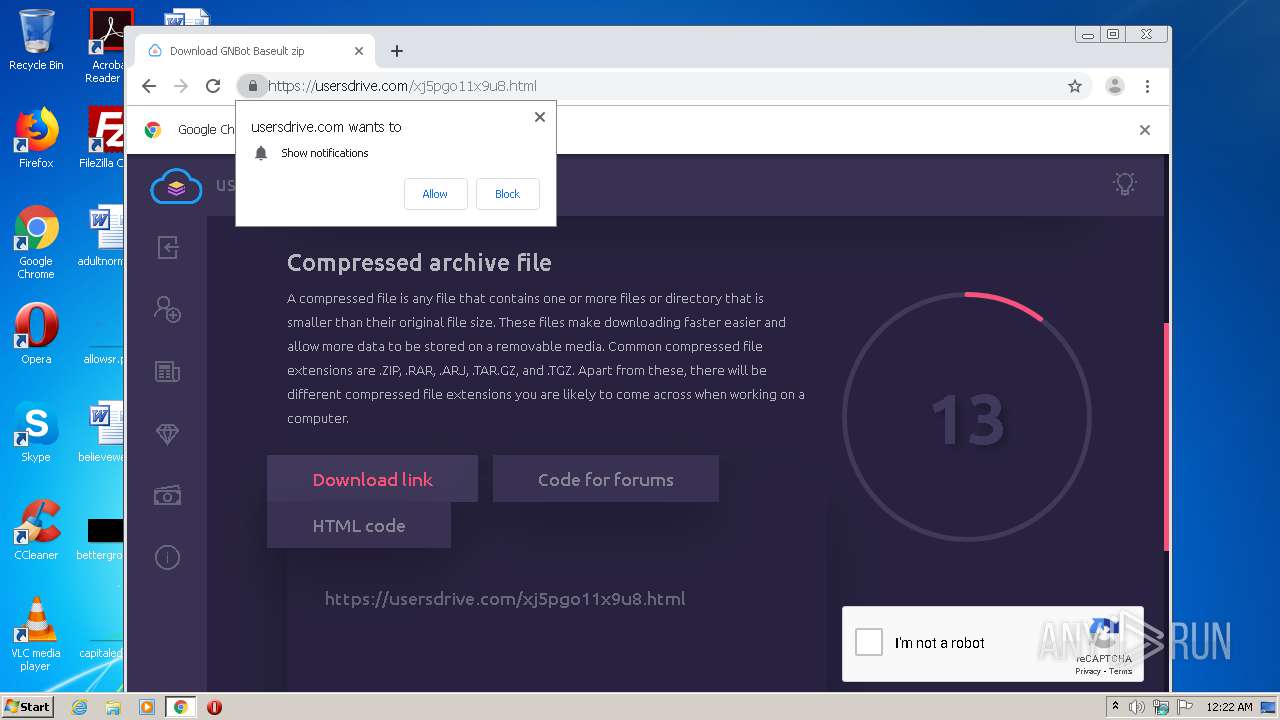
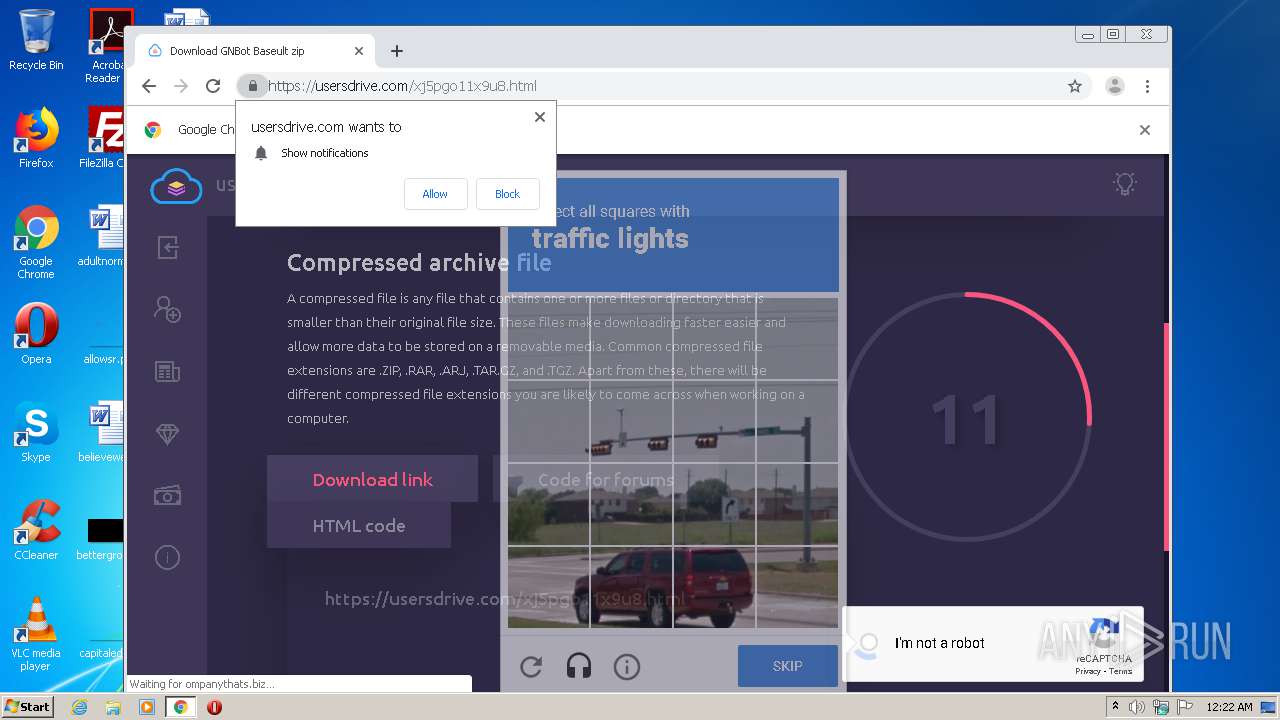
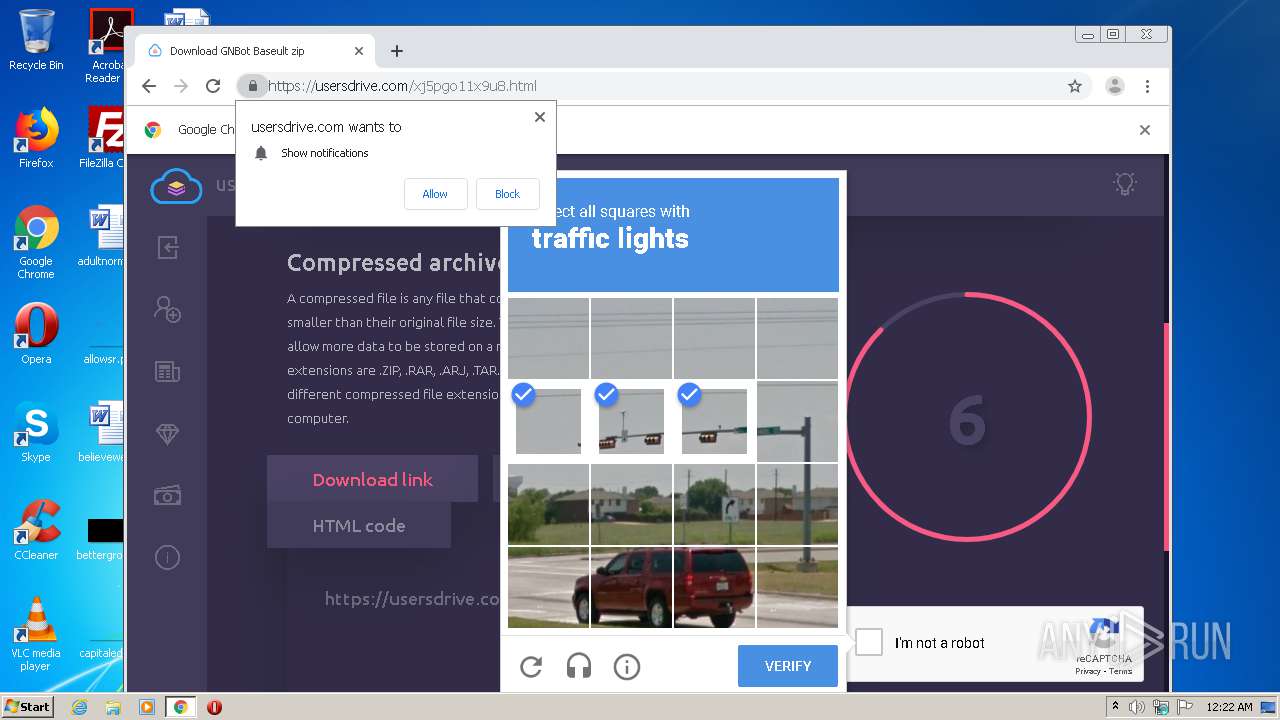
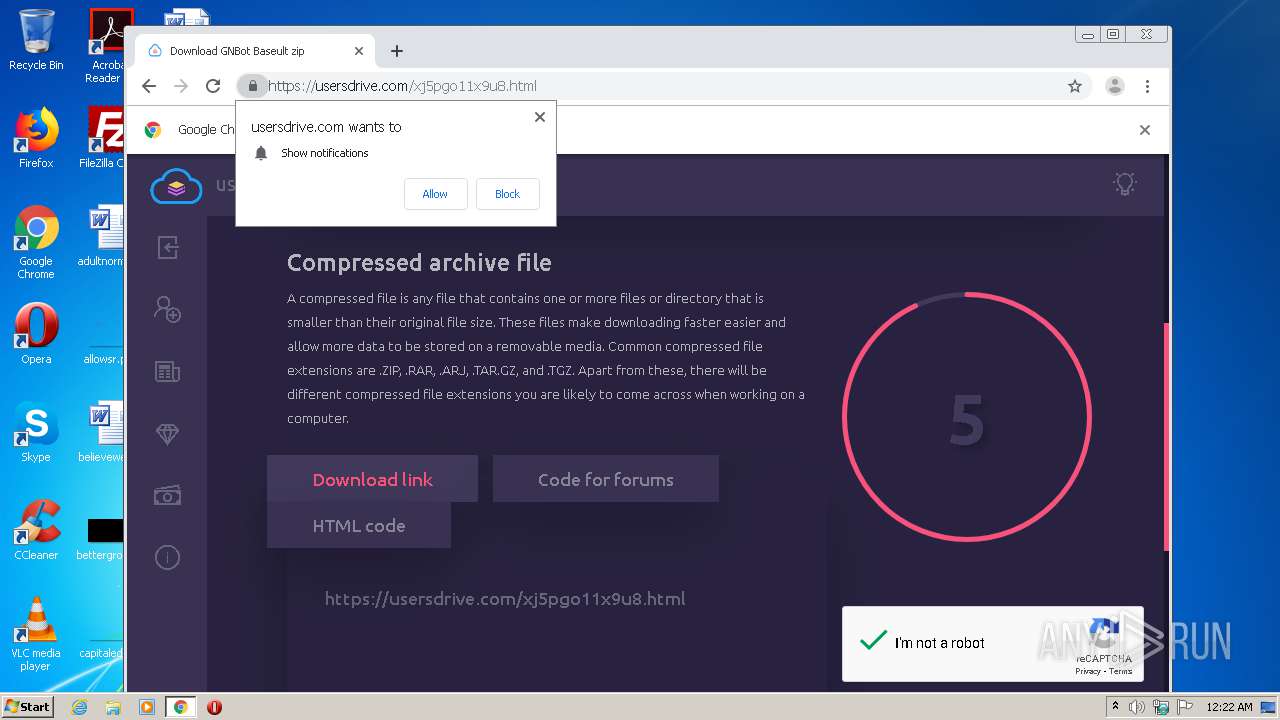
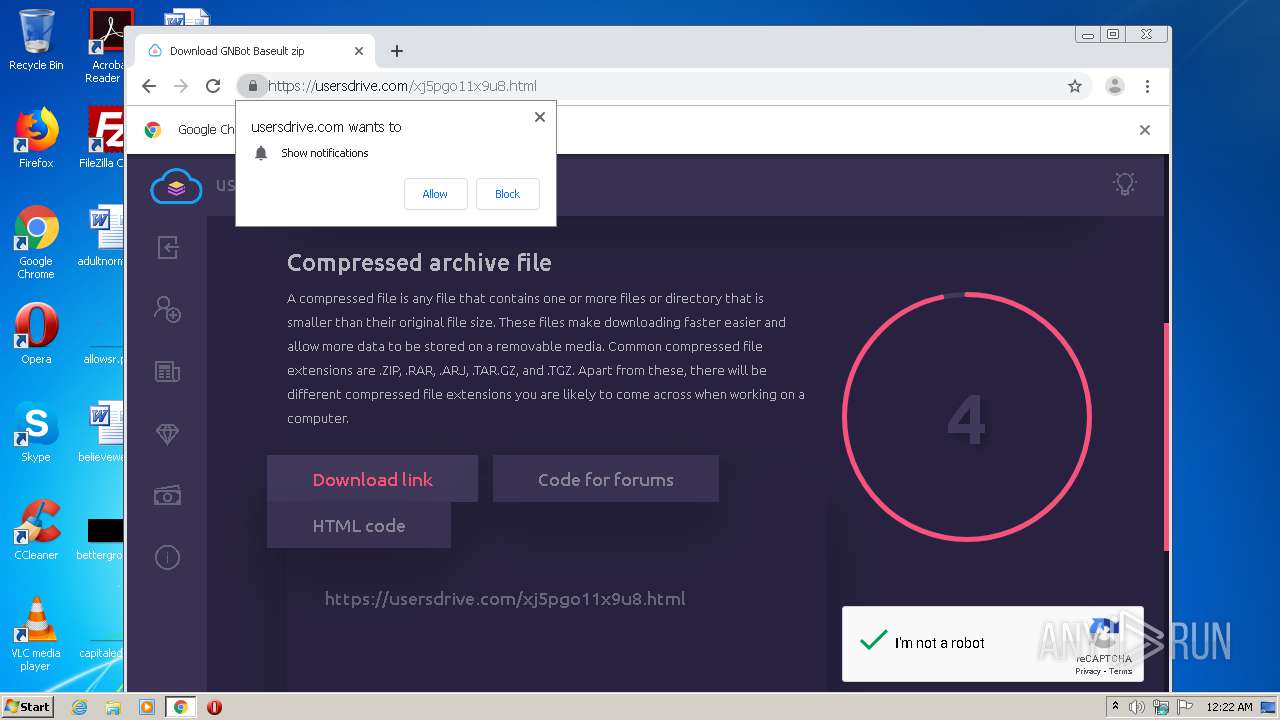
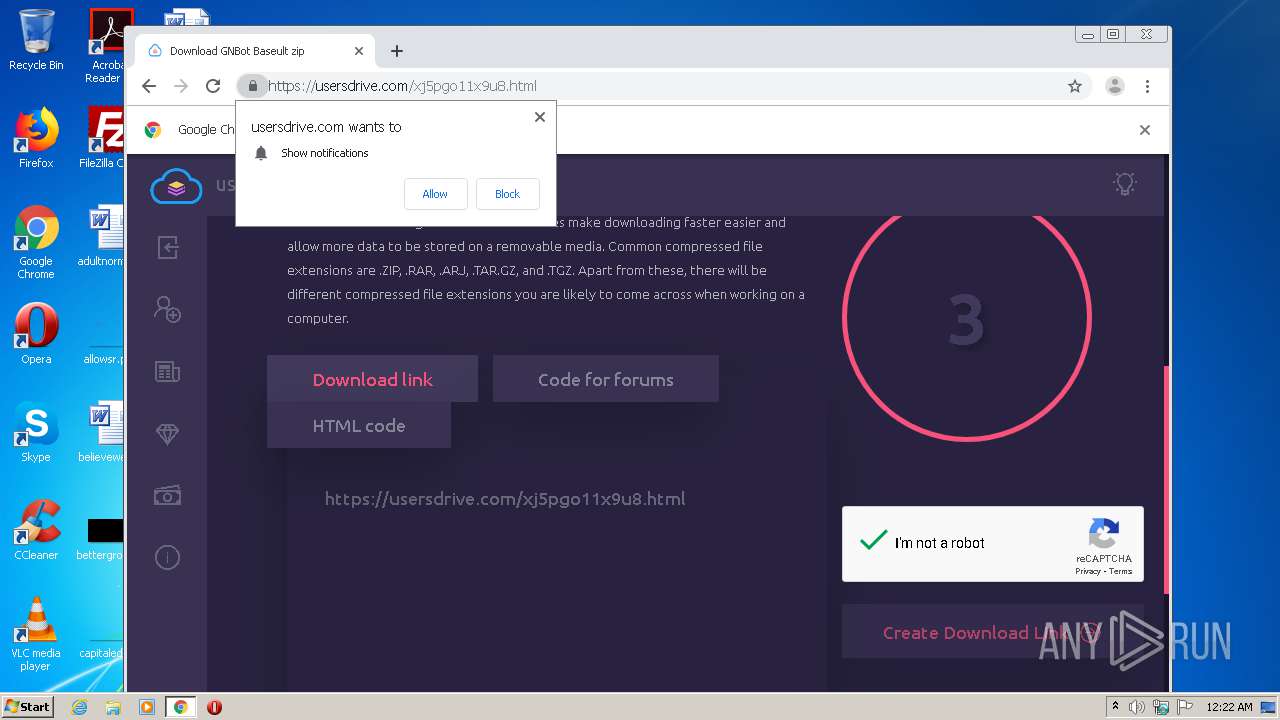
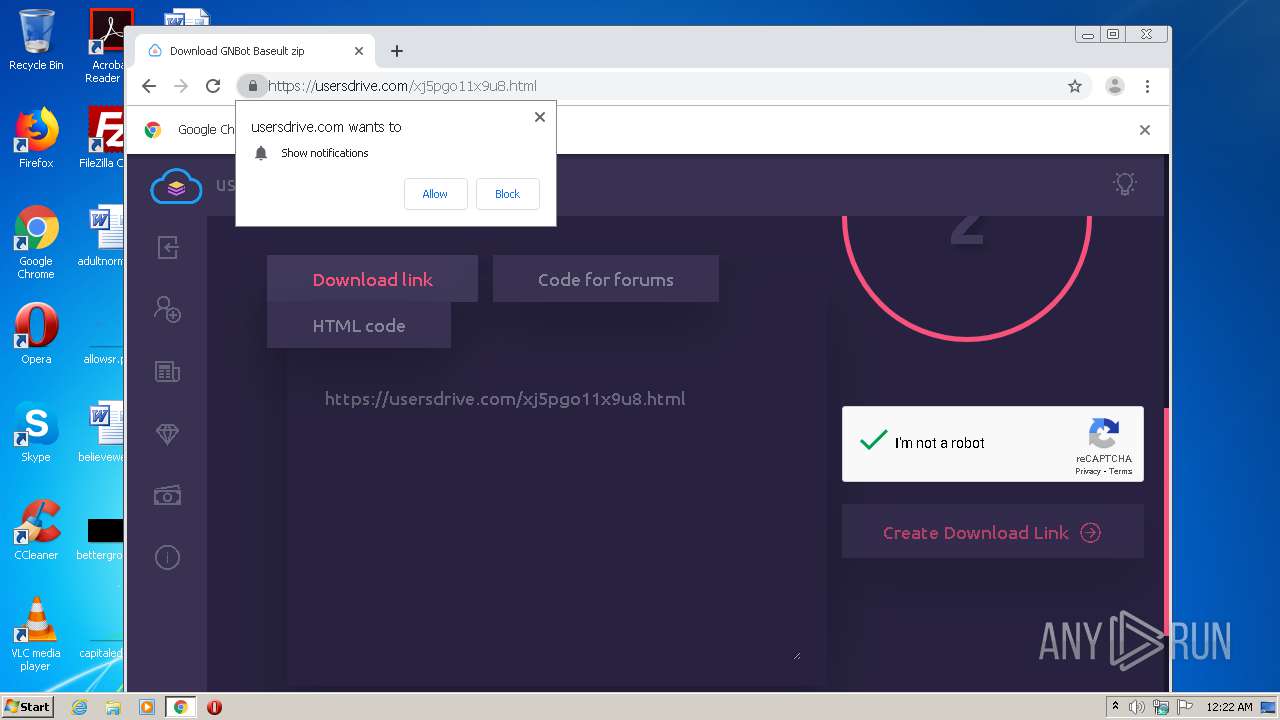
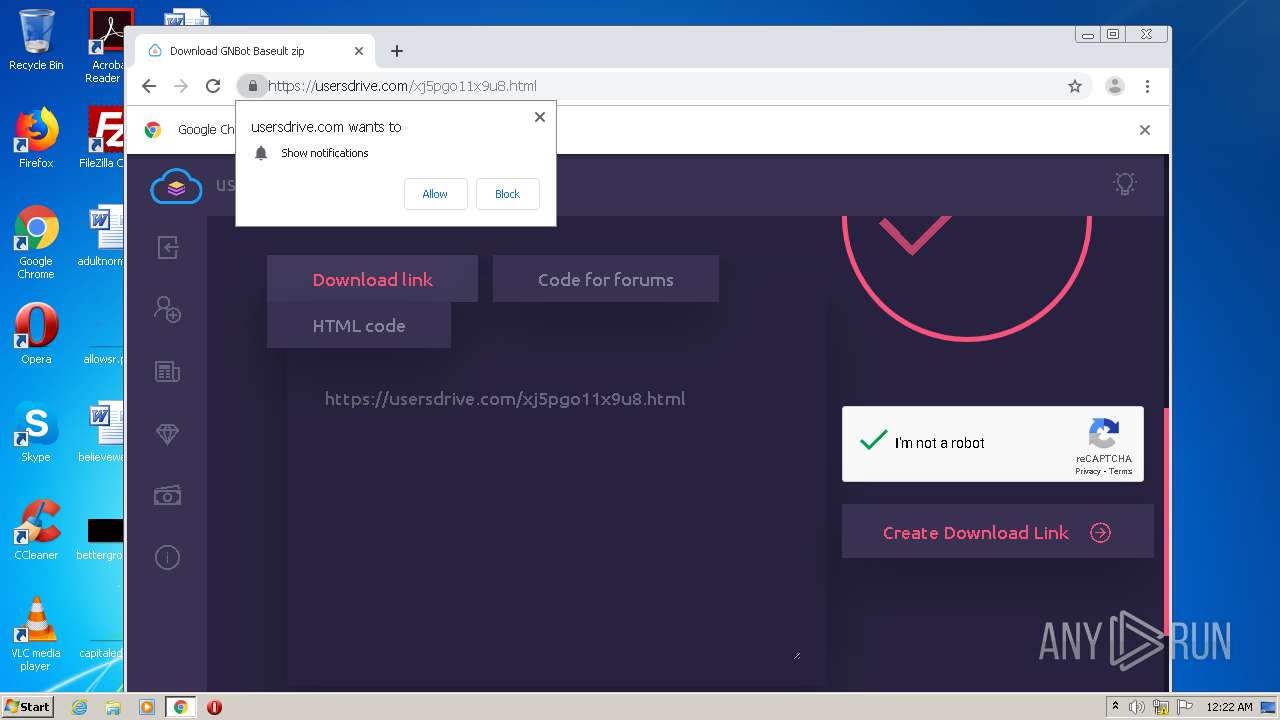
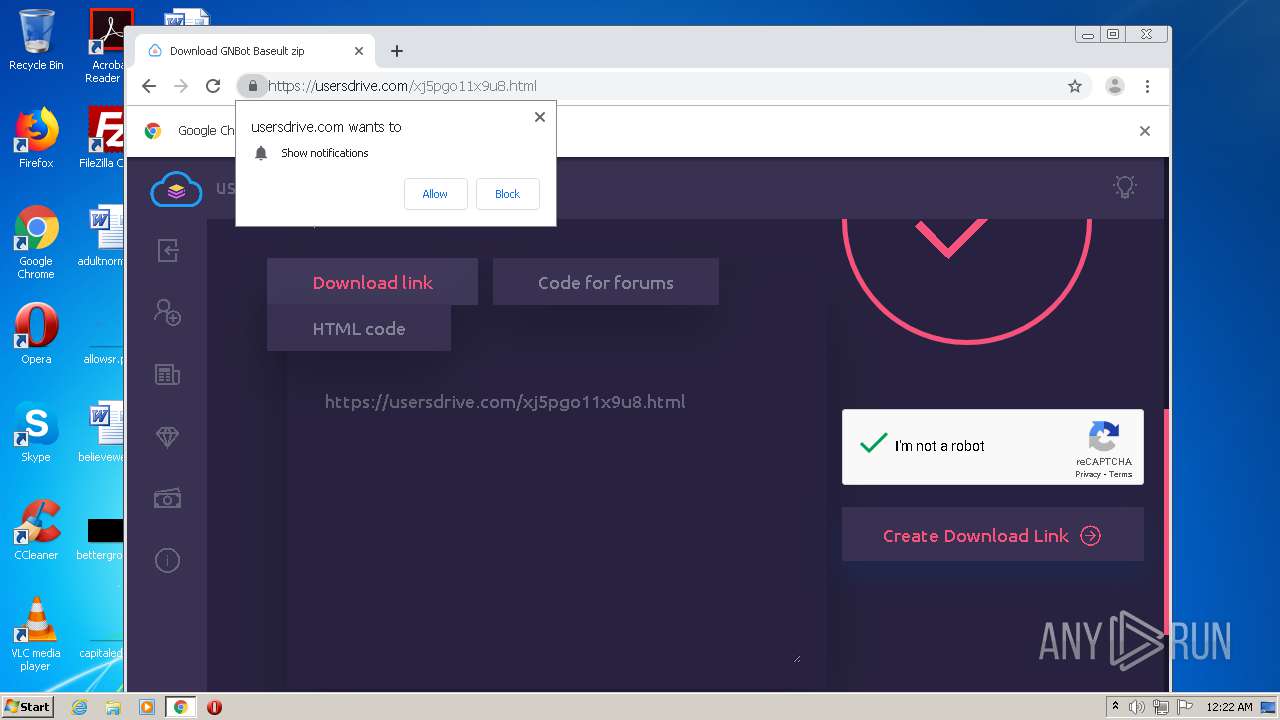
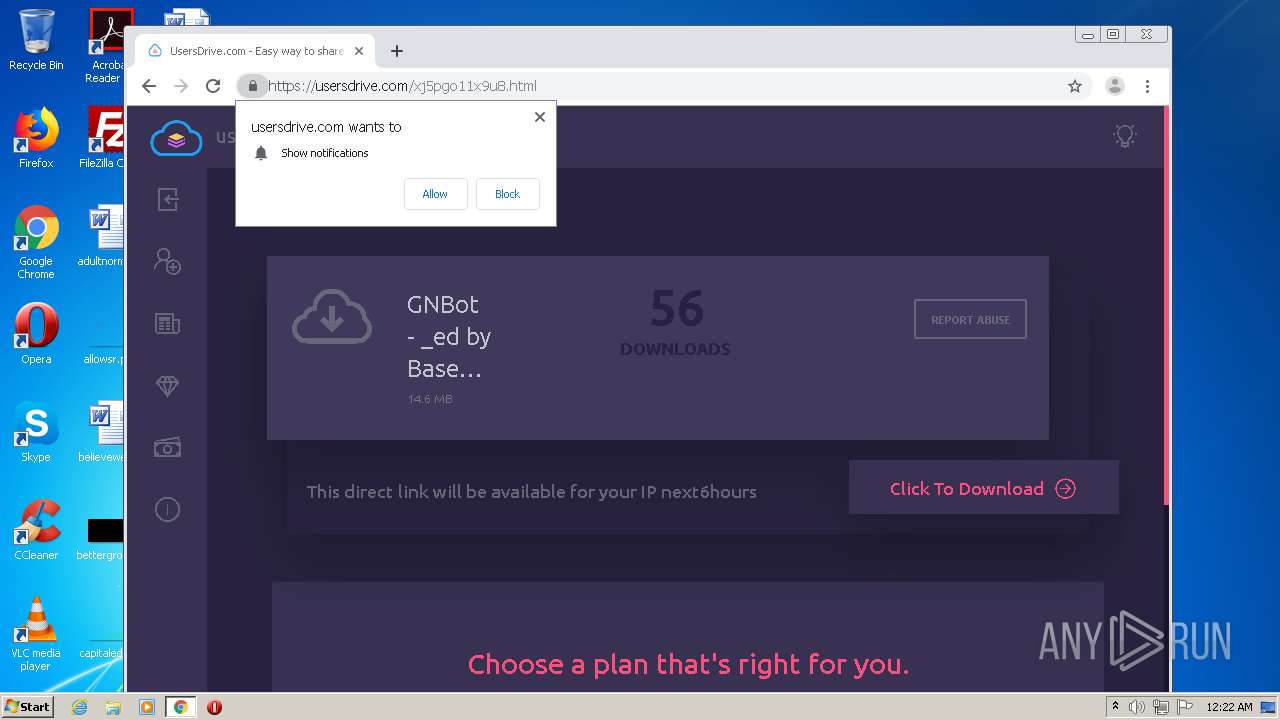
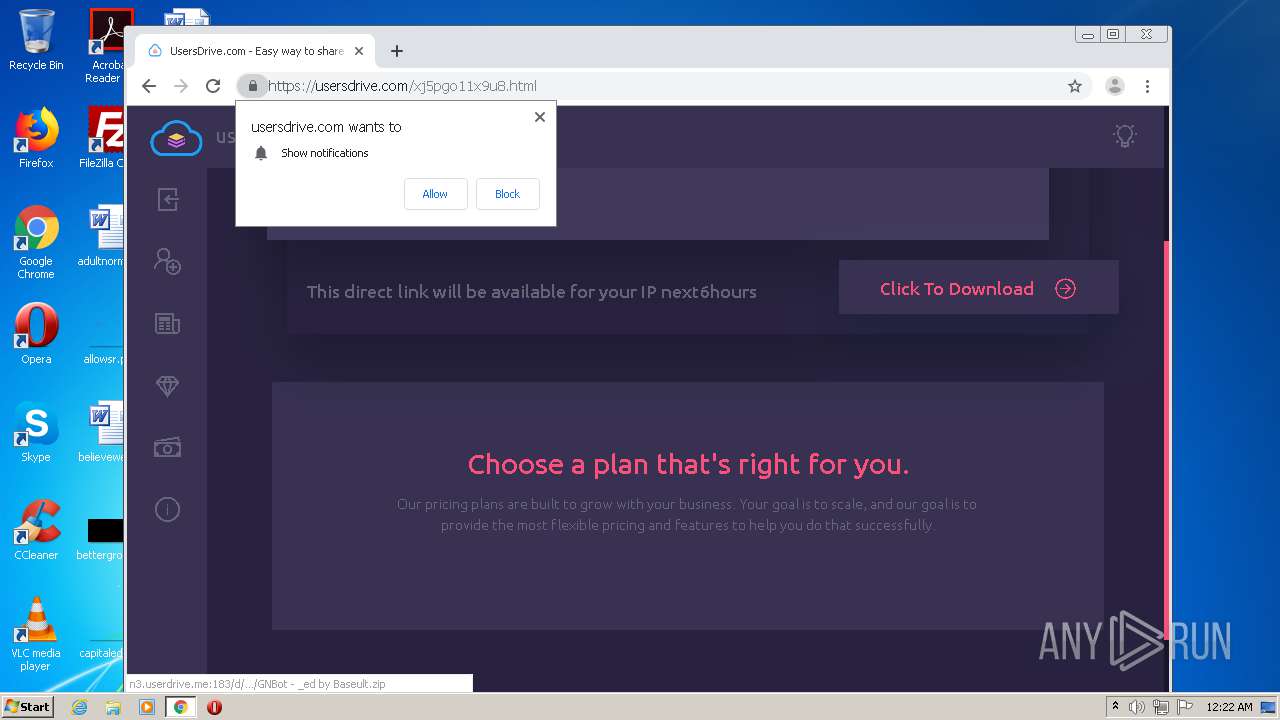
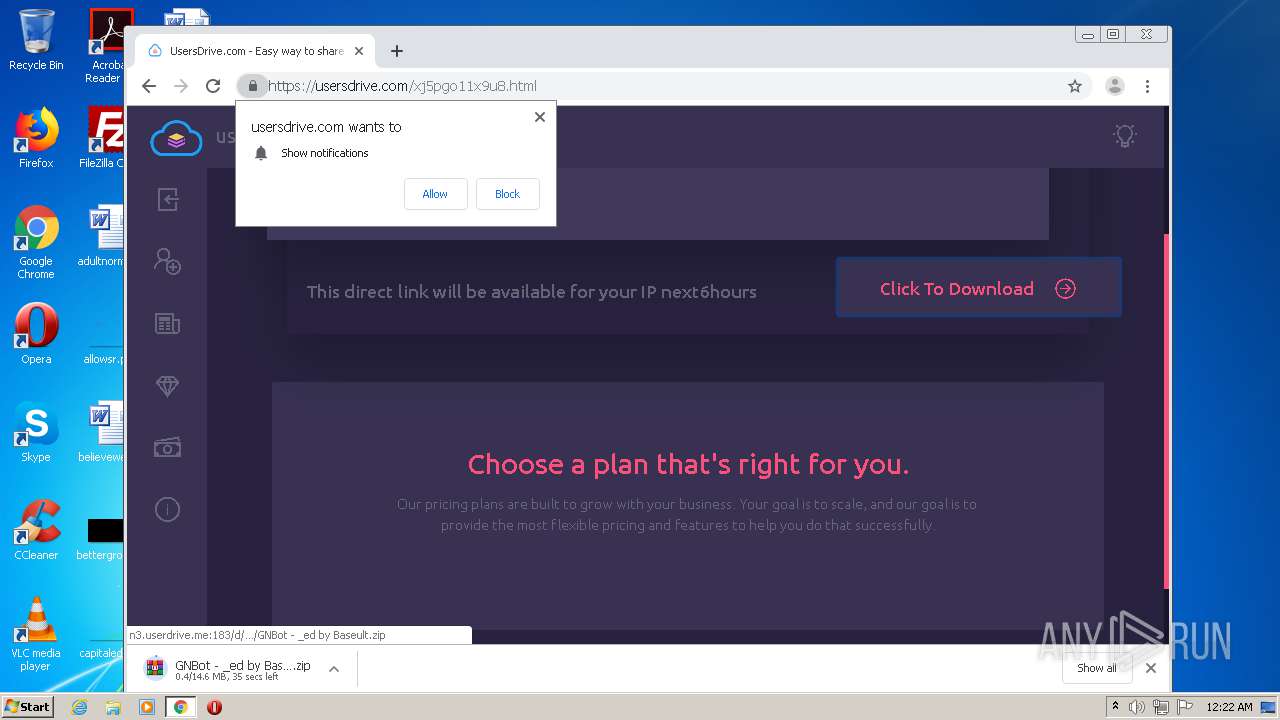
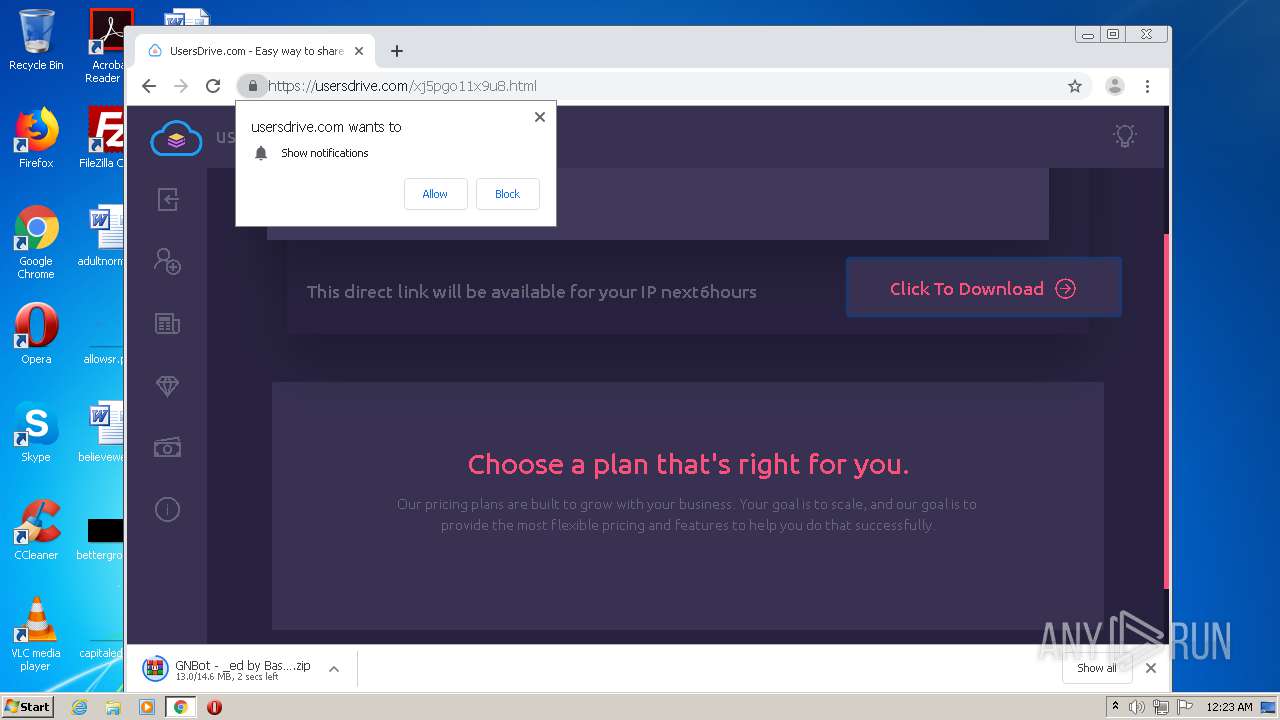
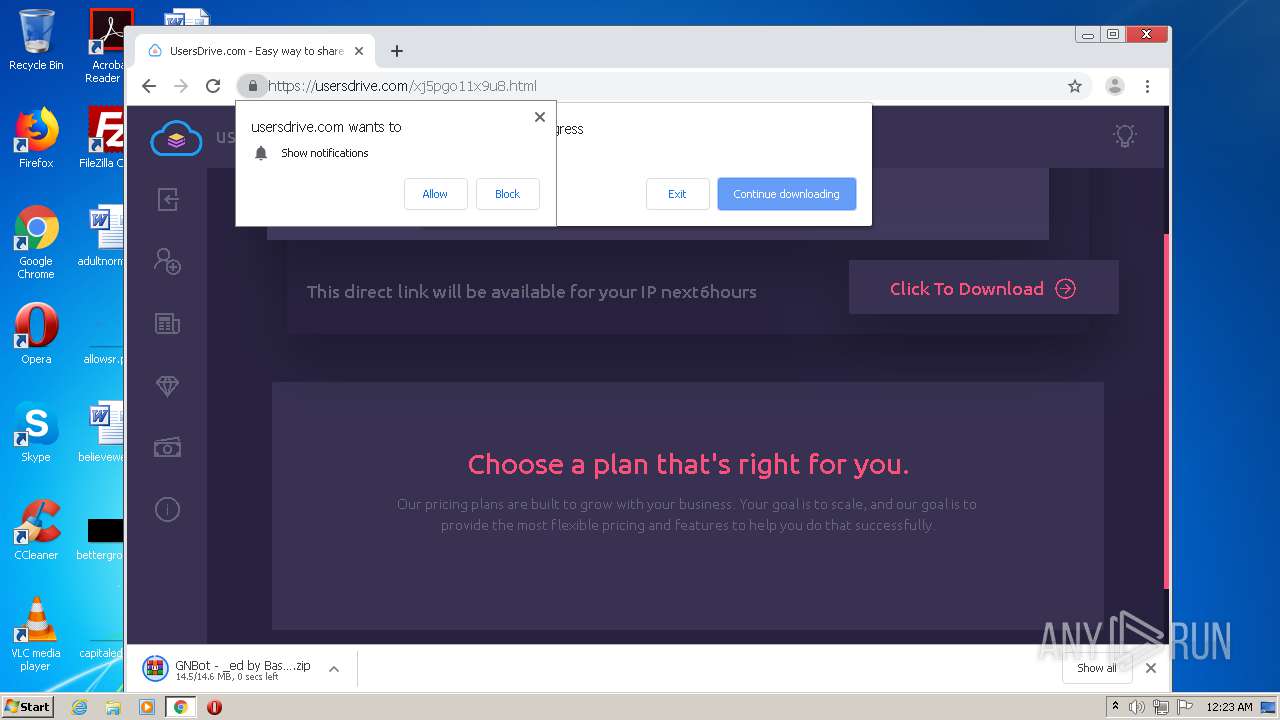
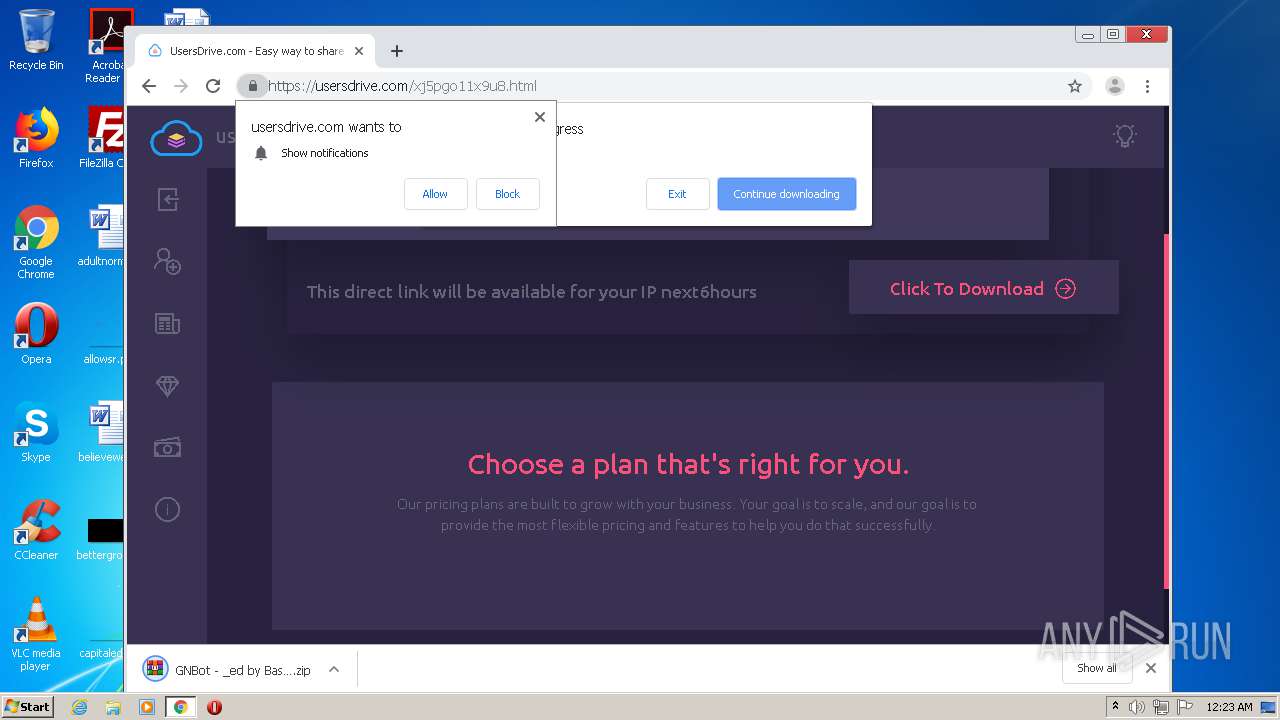
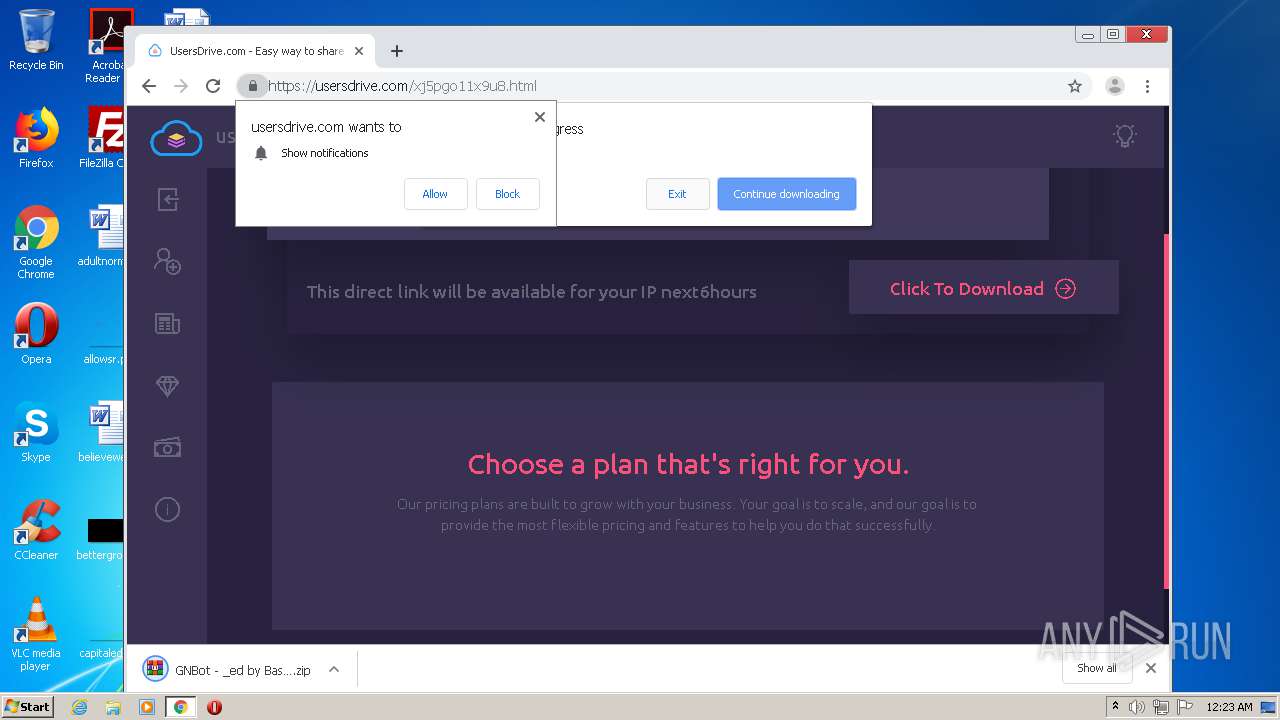
| URL: | https://usersdrive.com/xj5pgo11x9u8.html |
| Full analysis: | https://app.any.run/tasks/c1bcfc37-c345-453a-88ba-4dce23a12bfc |
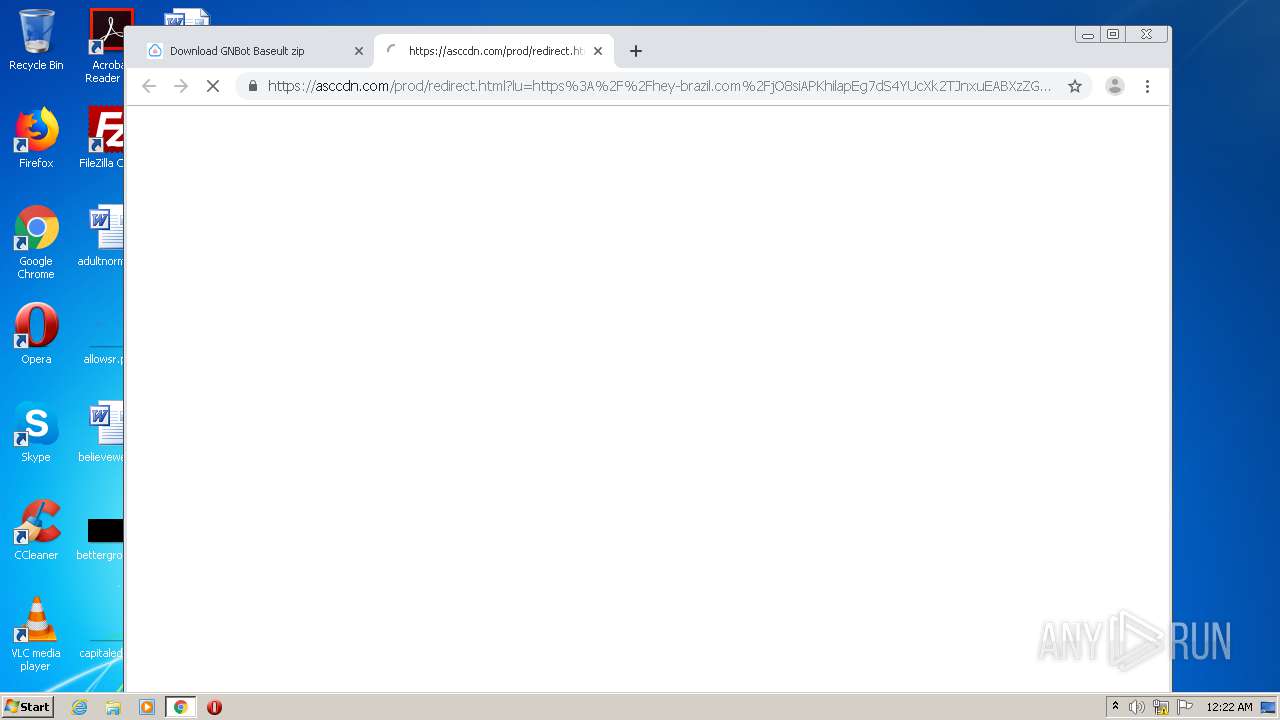
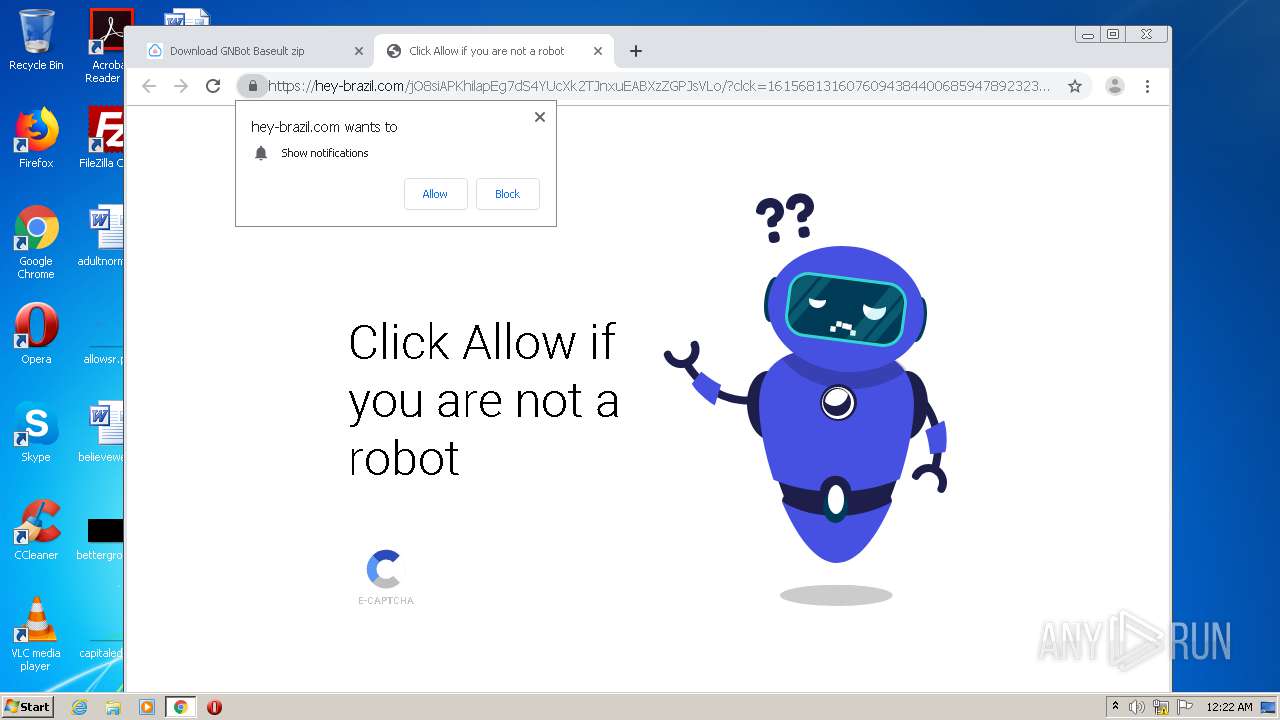
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2021, 00:21:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EFDBC5DB3D076DFB33EA75A2F45A0757 |
| SHA1: | 077E308B6096F2D83C819E0781A424BC8140434A |
| SHA256: | 6D5ECA62150430BDB222CF12CB99249FA36C06AF316BD4286DBCEFA1D8BA86BD |
| SSDEEP: | 3:N8FXSAZtPQVJUWLD0:2FXSfXz0 |
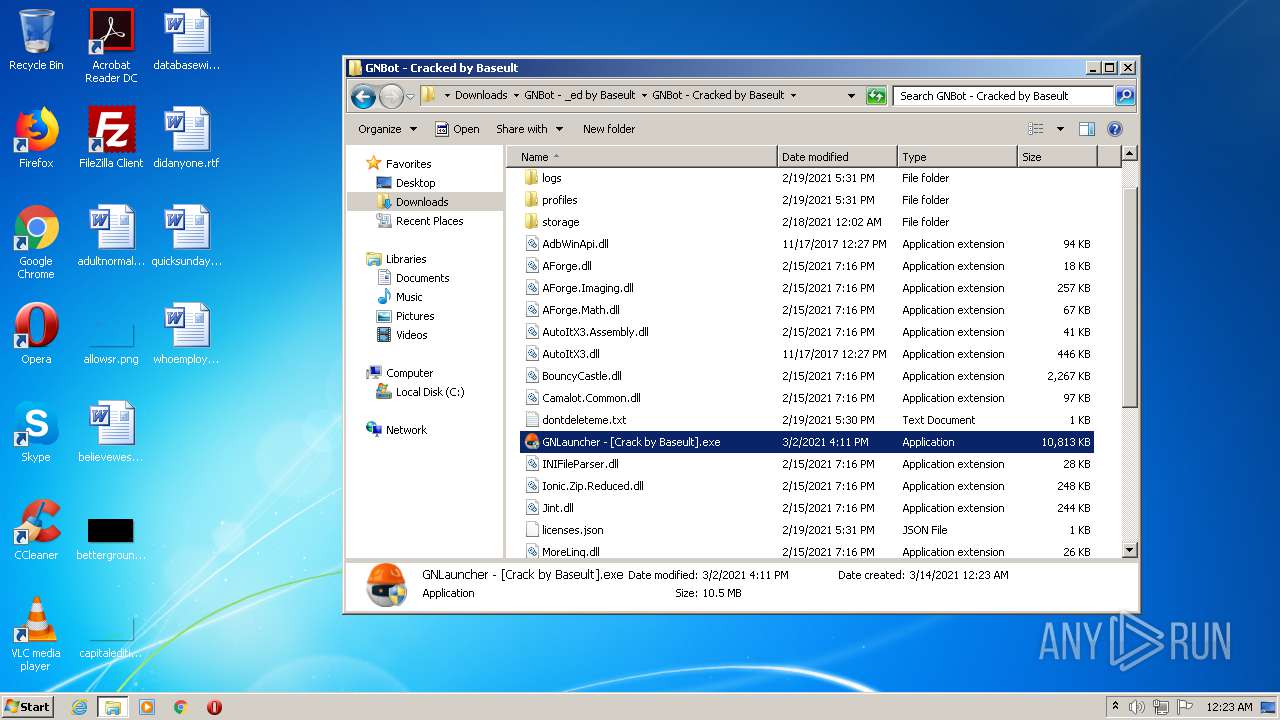
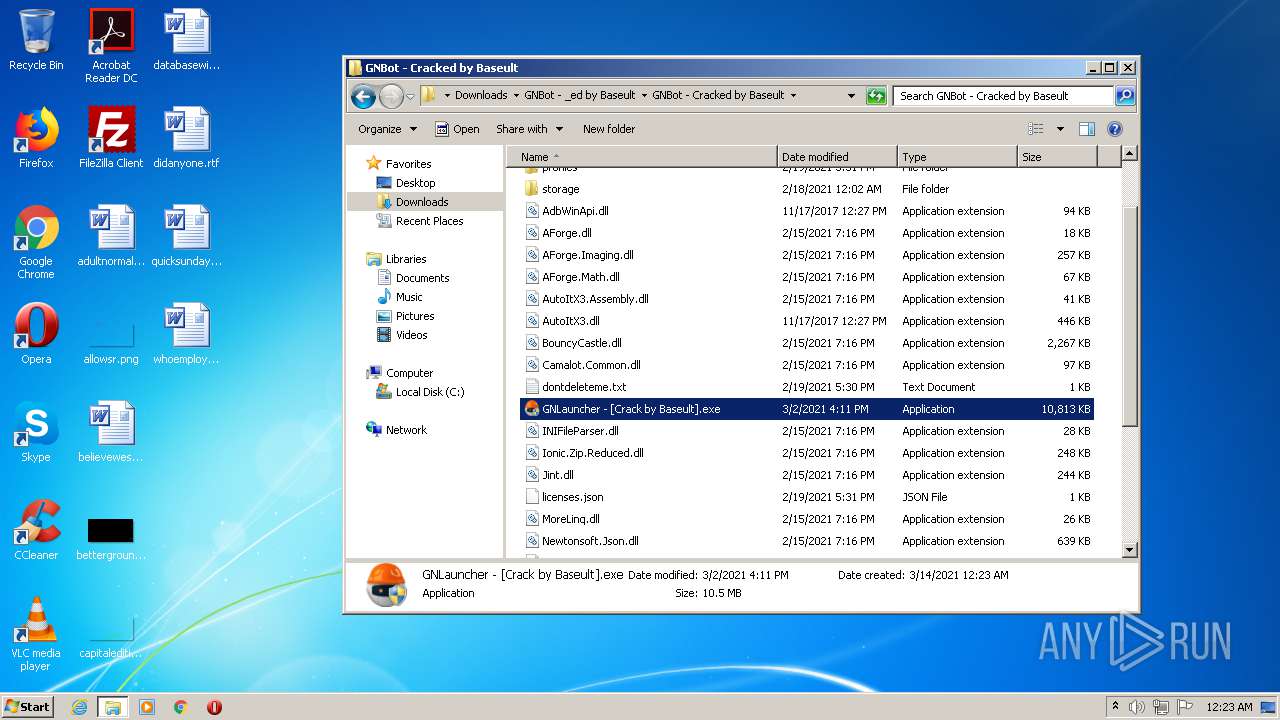
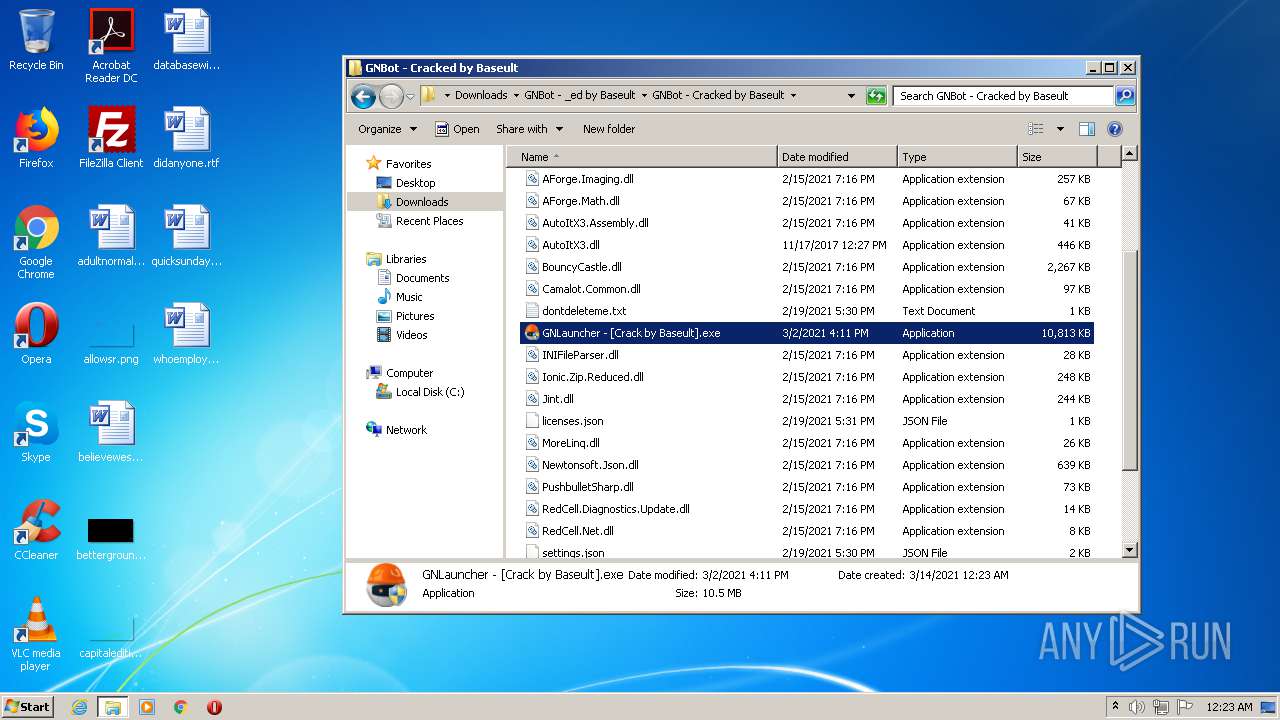
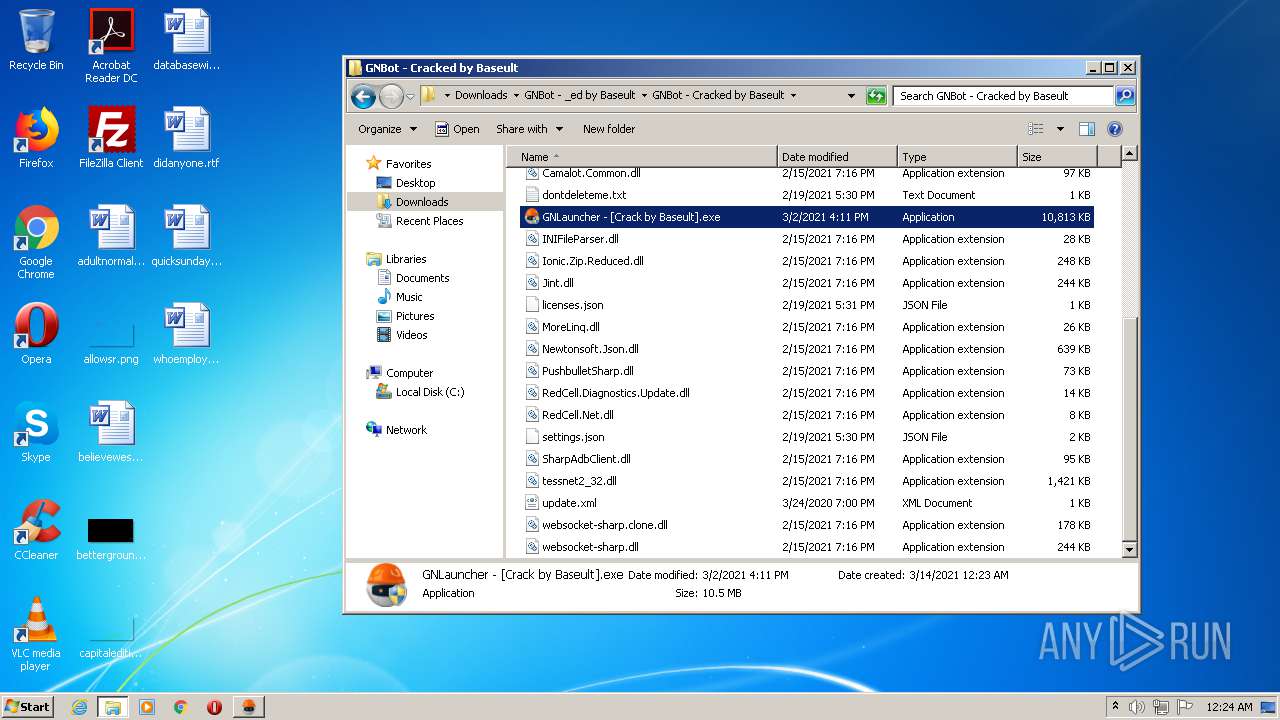
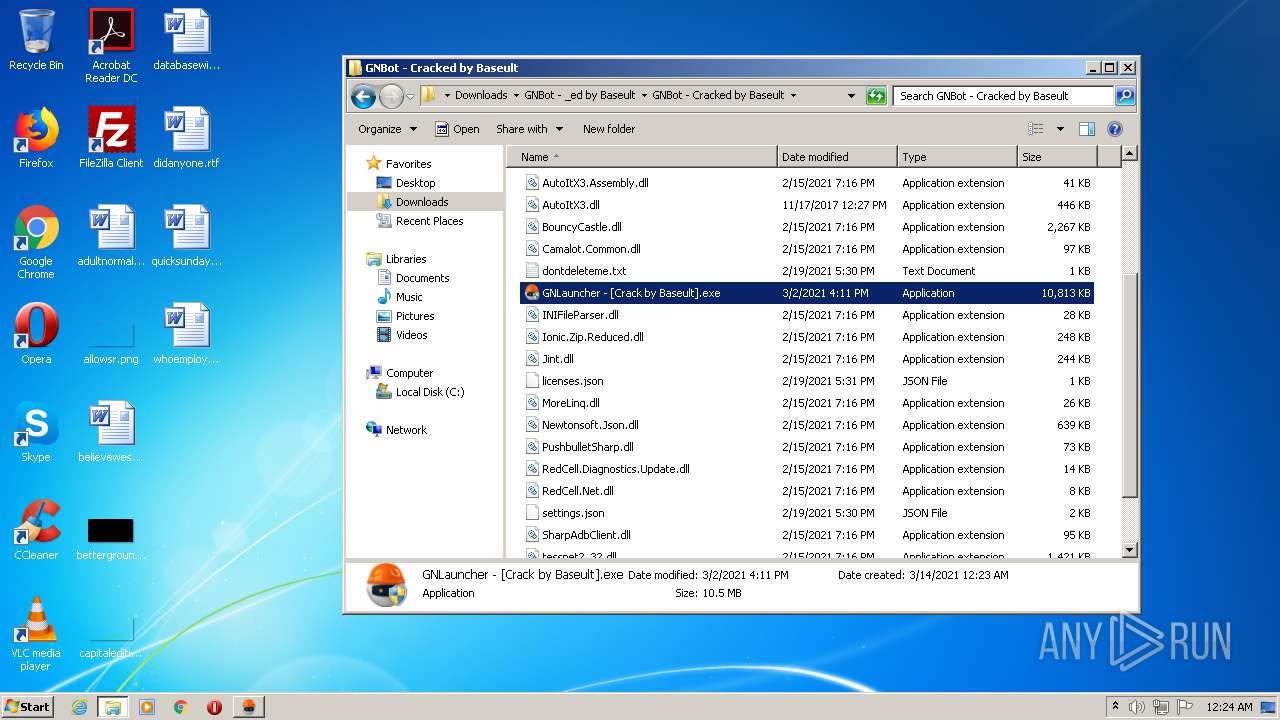
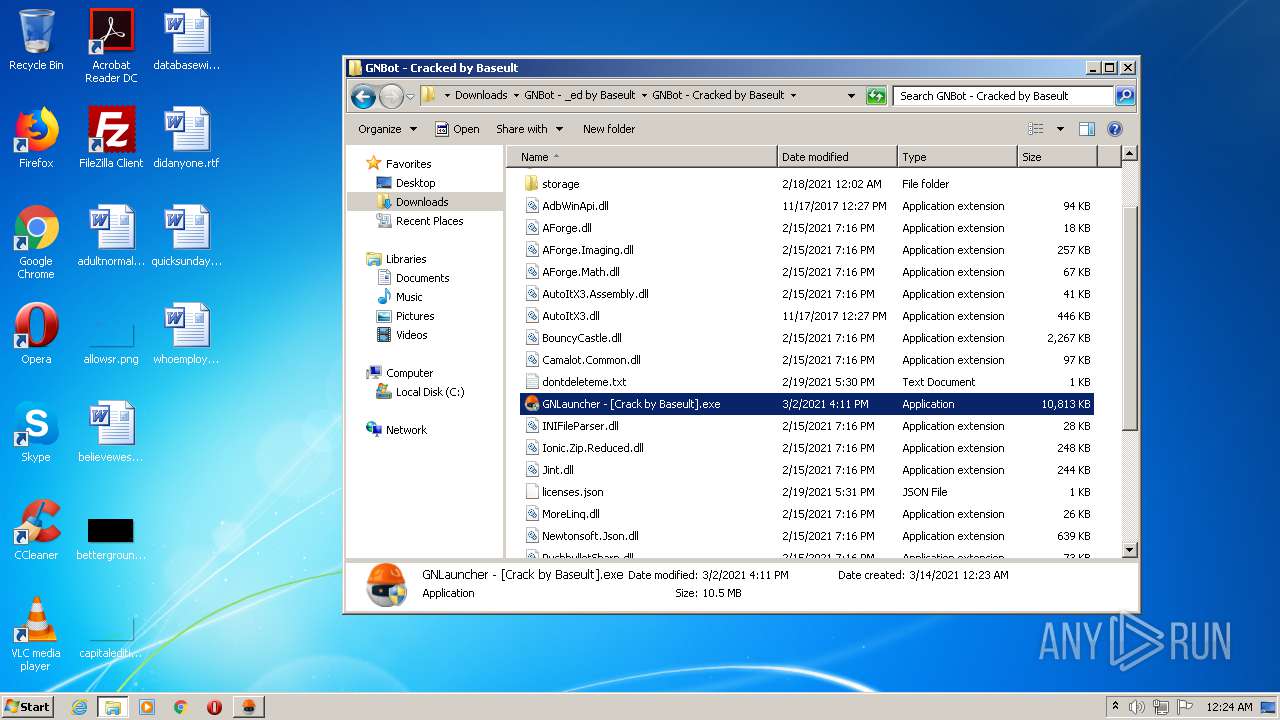
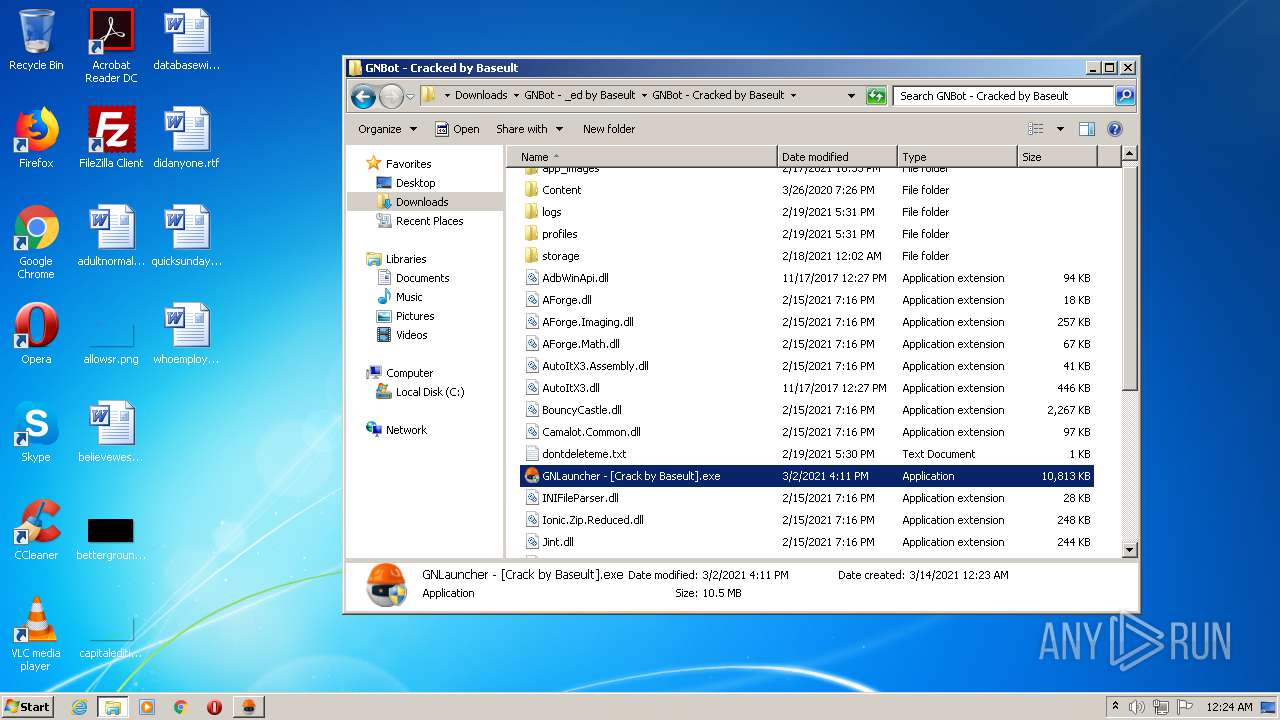
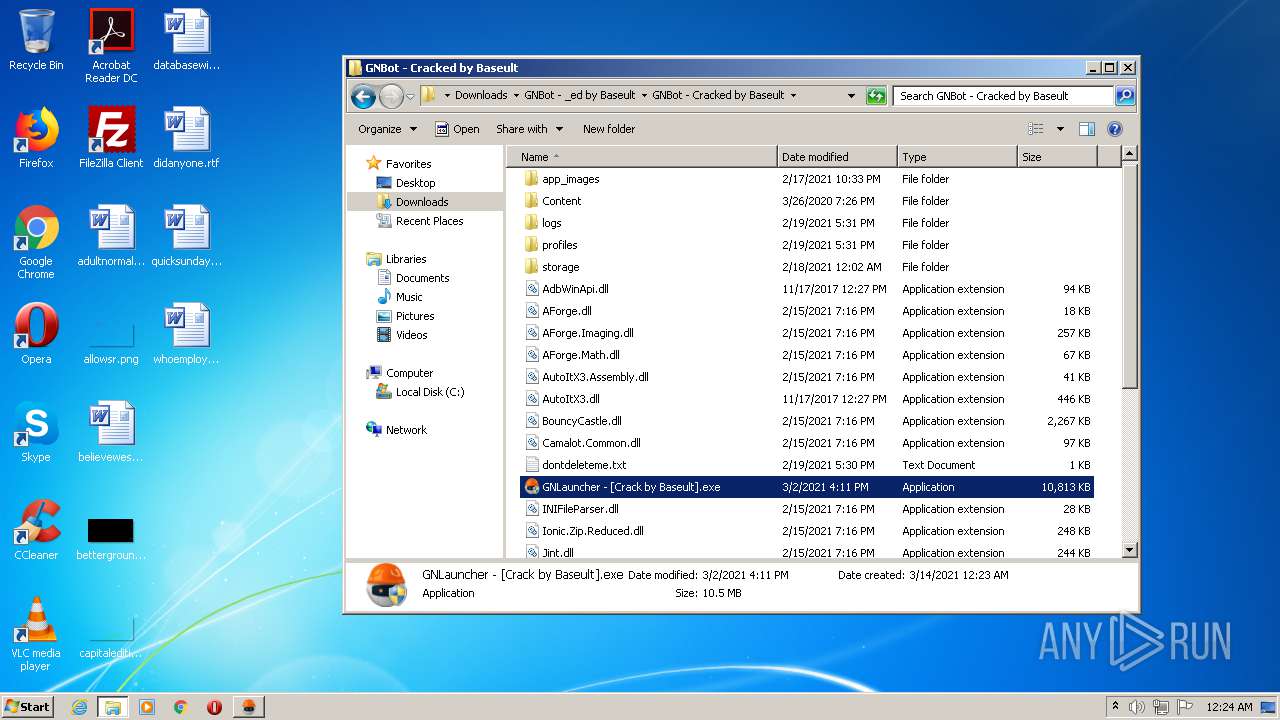
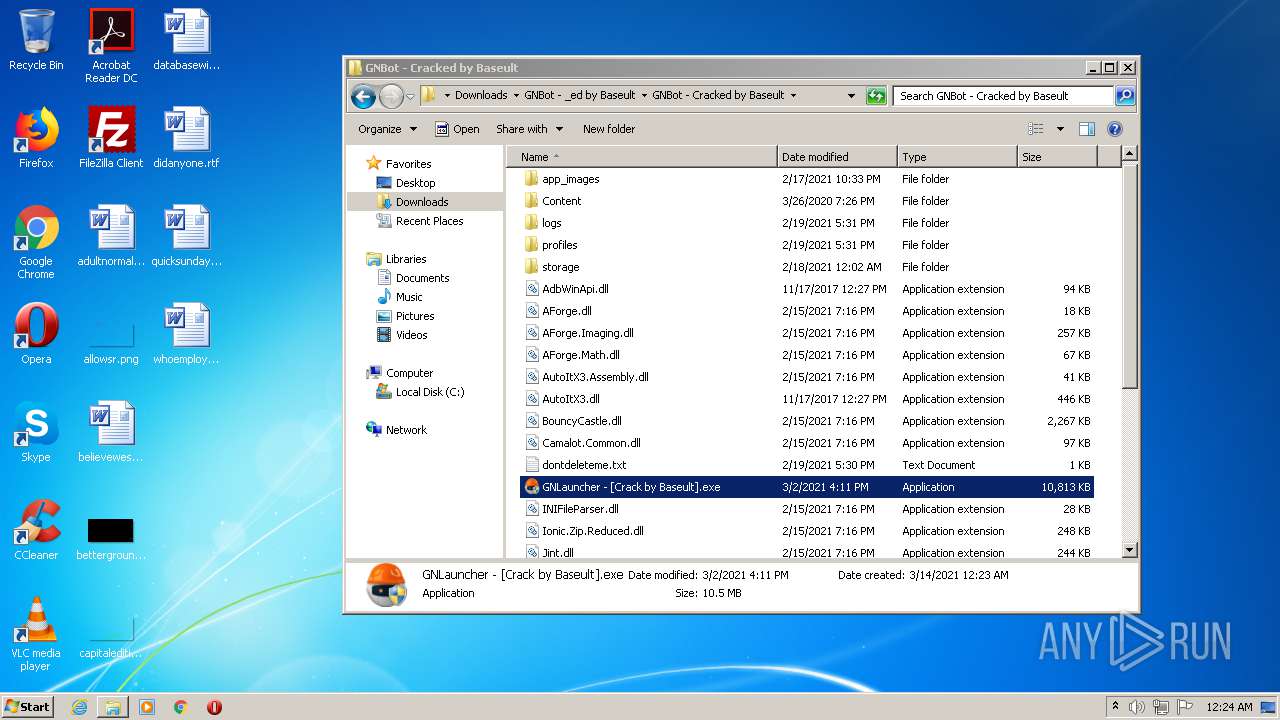
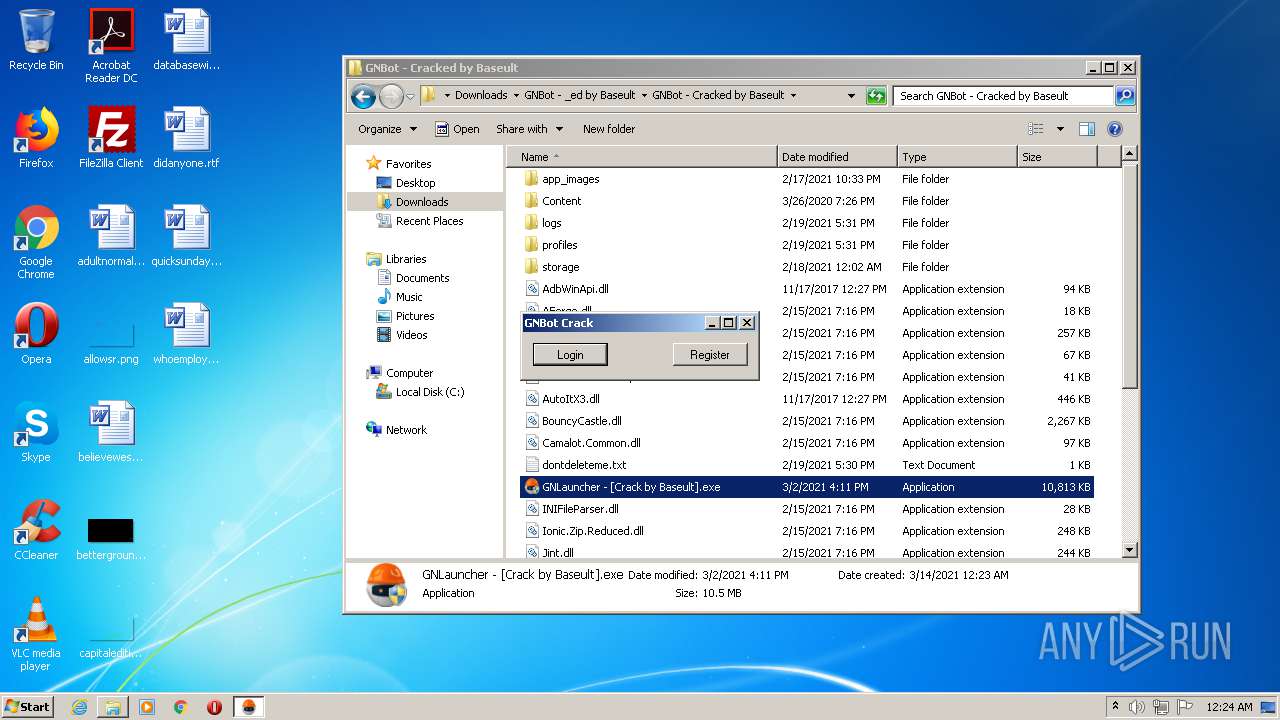
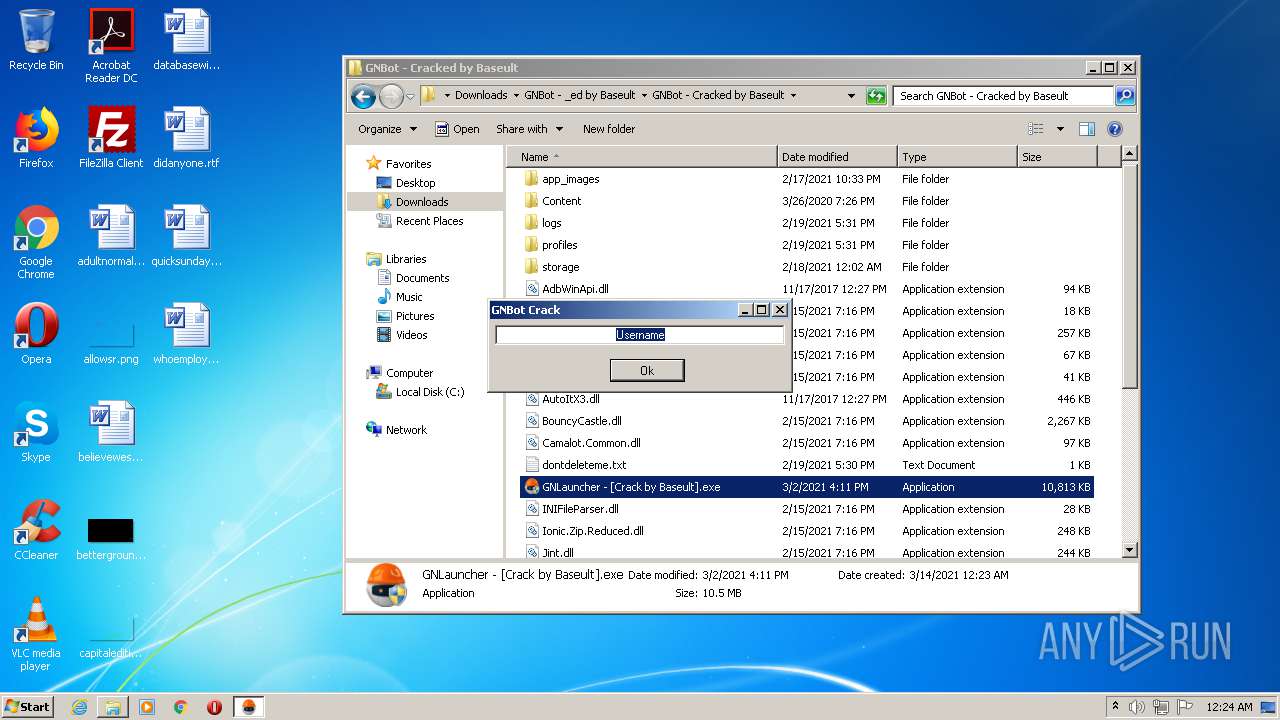
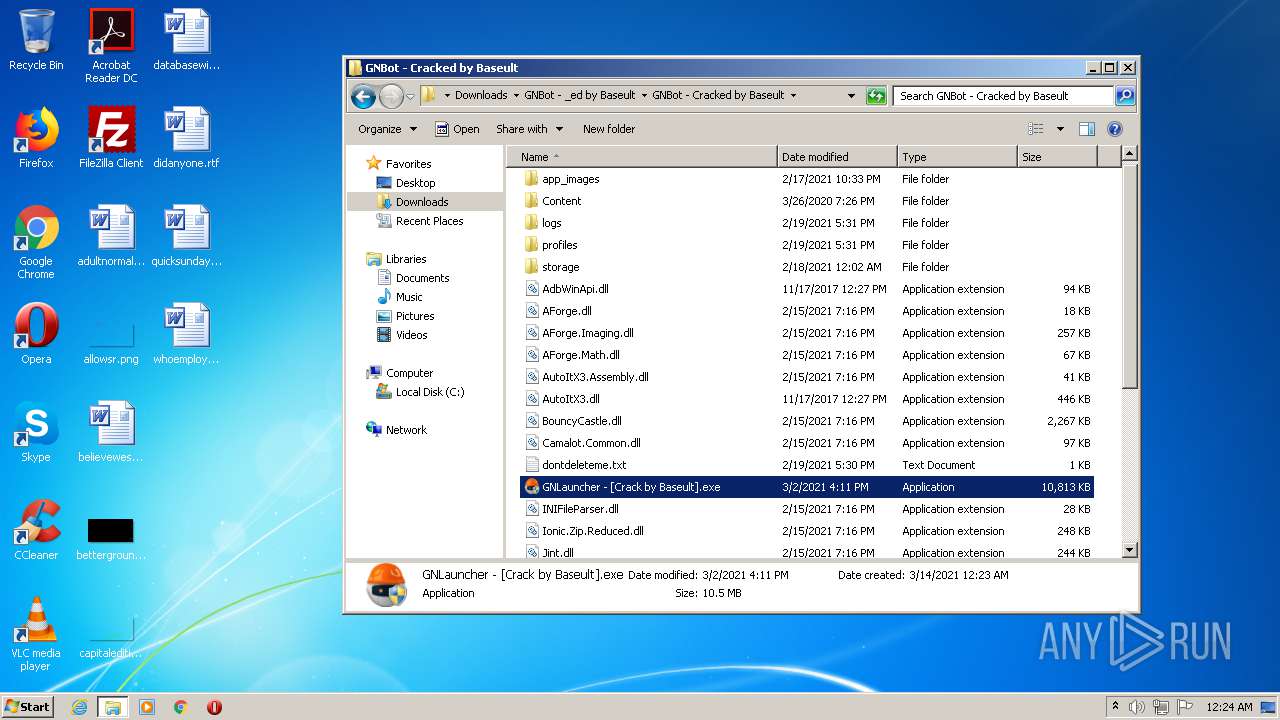
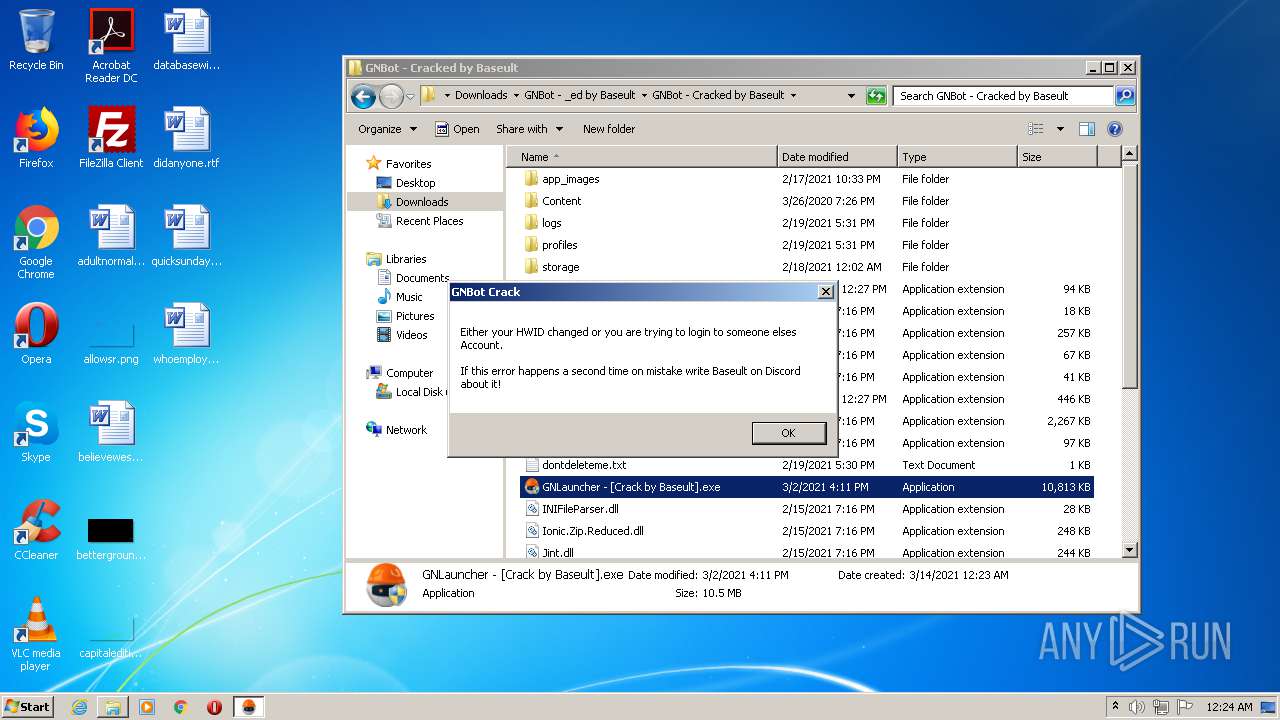
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3788)
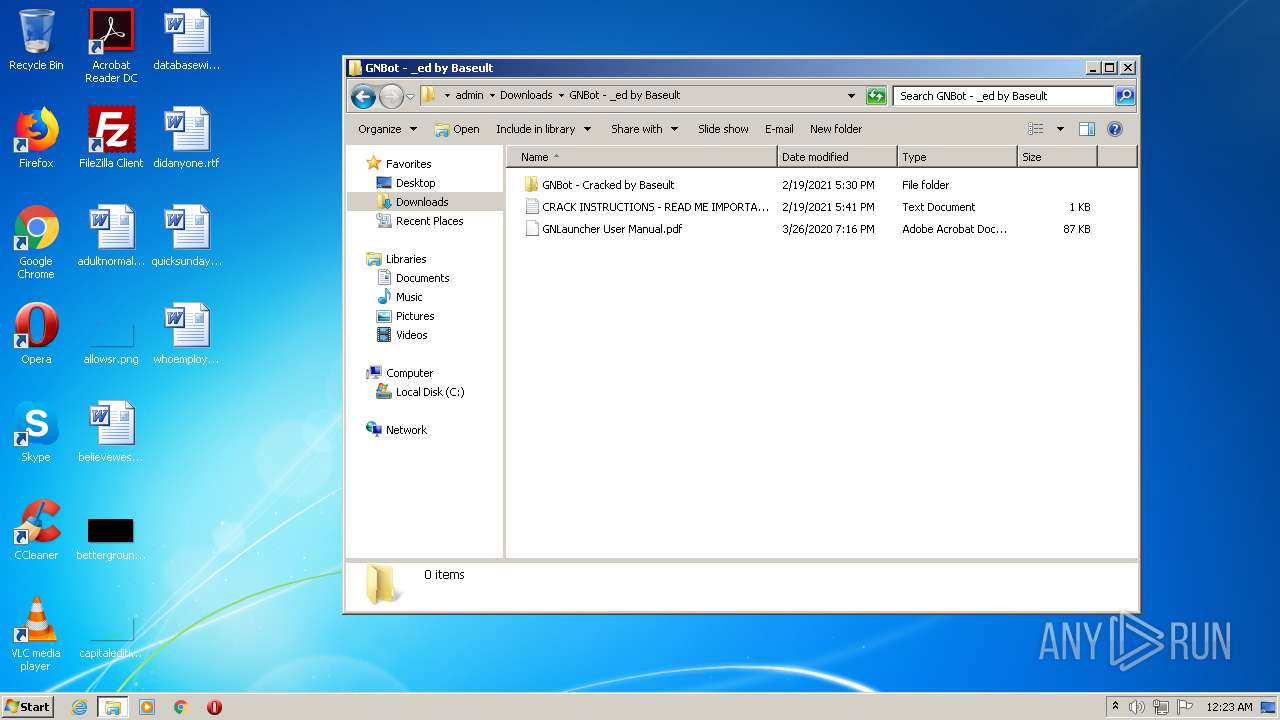
- GNLauncher - [Crack by Baseult].exe (PID: 3192)
- explorer.exe (PID: 376)
Application was dropped or rewritten from another process
- GNLauncher - [Crack by Baseult].exe (PID: 3840)
- GNLauncher - [Crack by Baseult].exe (PID: 3192)
- GNLauncher - [Crack by Baseult].exe (PID: 3056)
- GNLauncher - [Crack by Baseult].exe (PID: 1436)
Changes settings of System certificates
- GNLauncher - [Crack by Baseult].exe (PID: 3192)
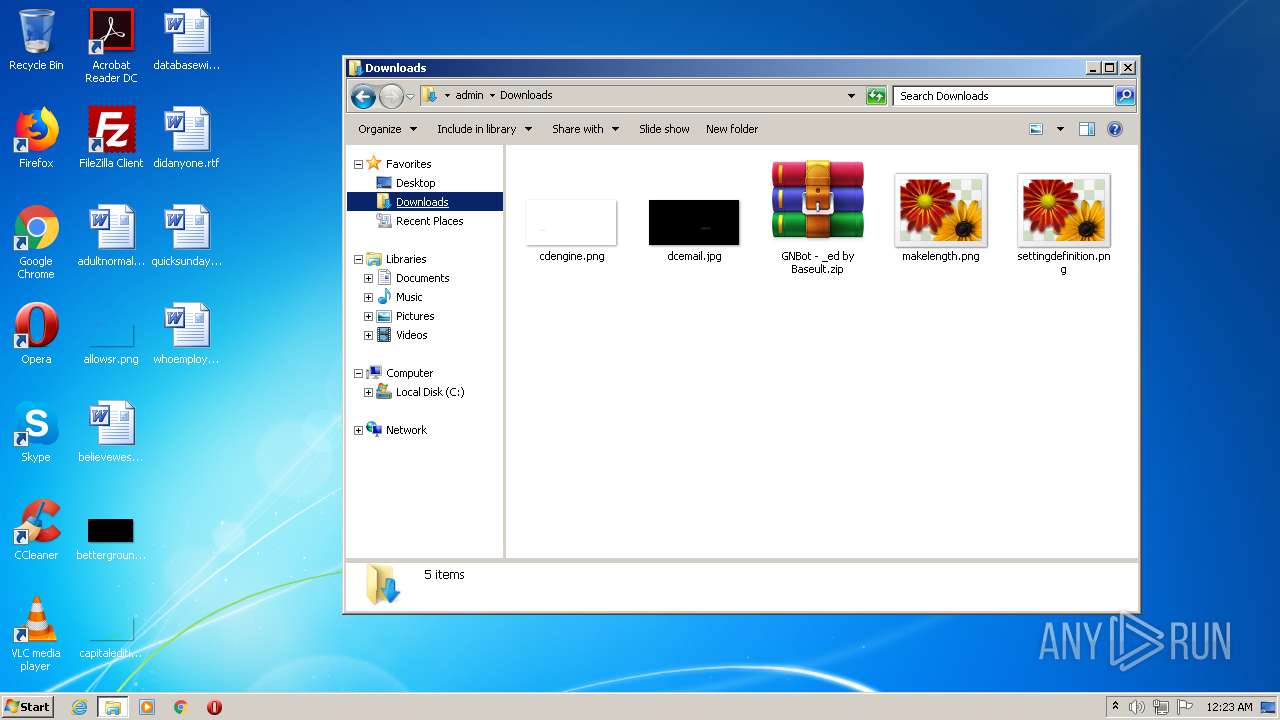
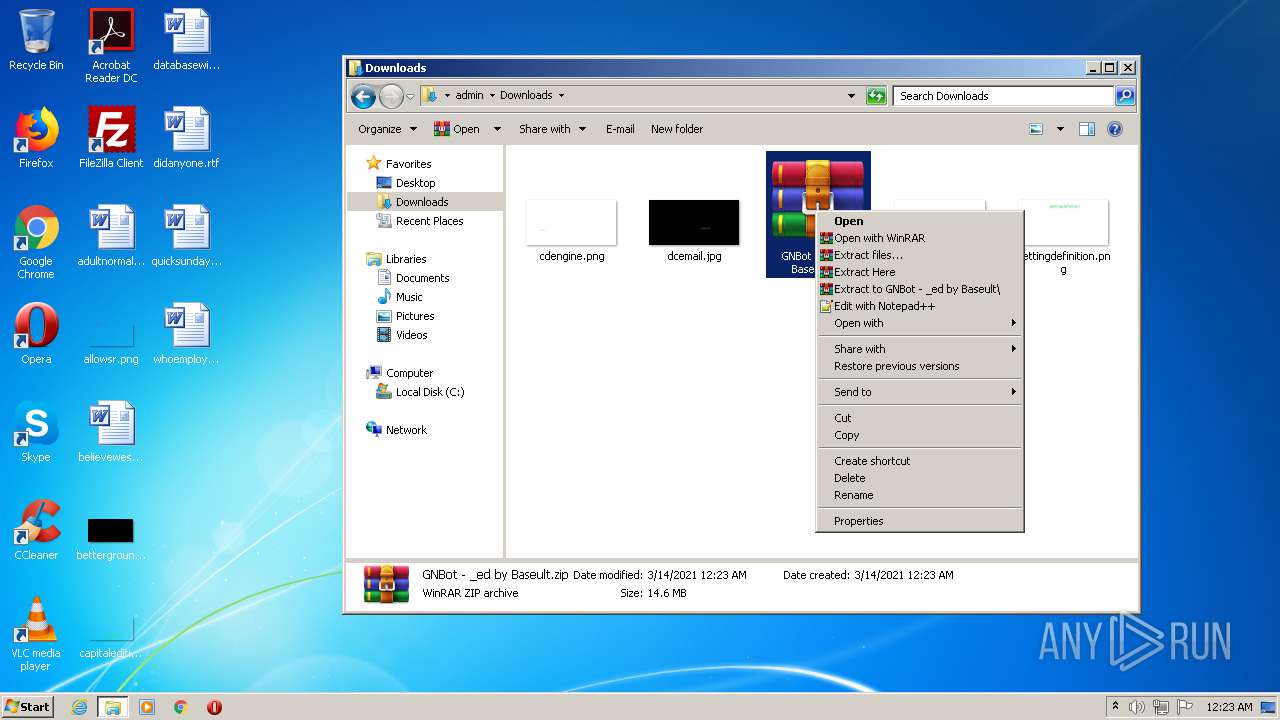
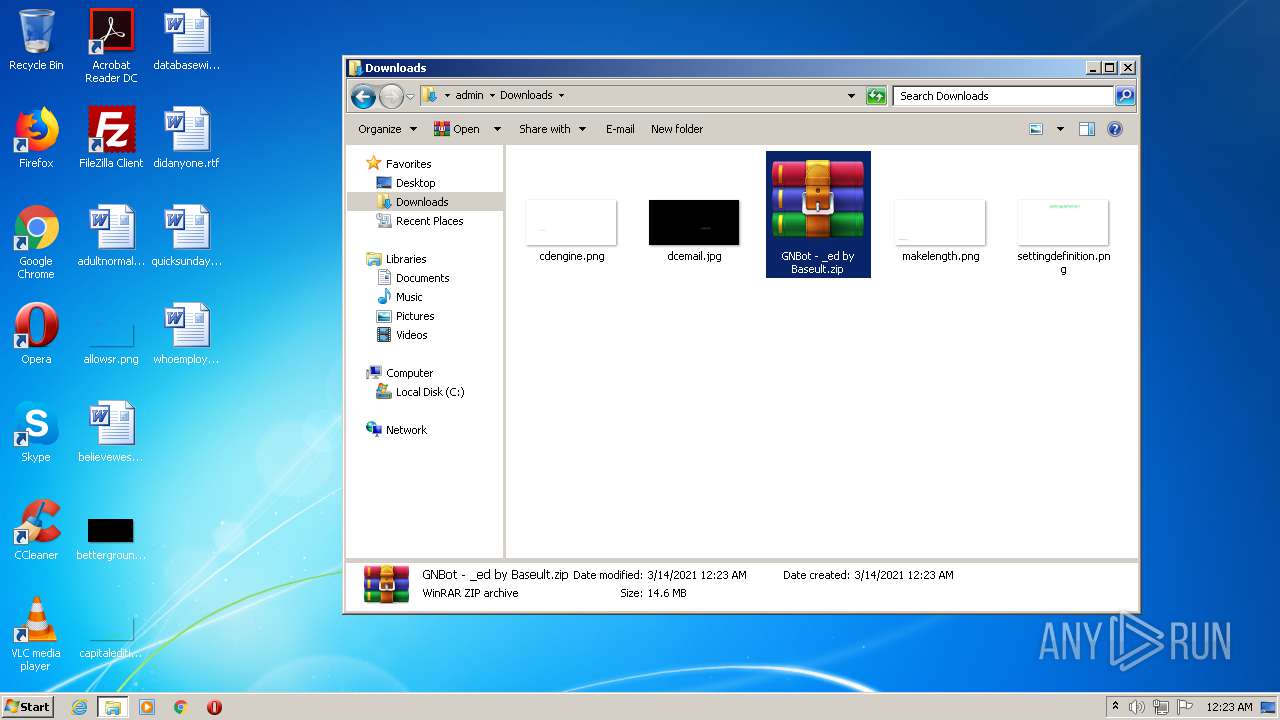
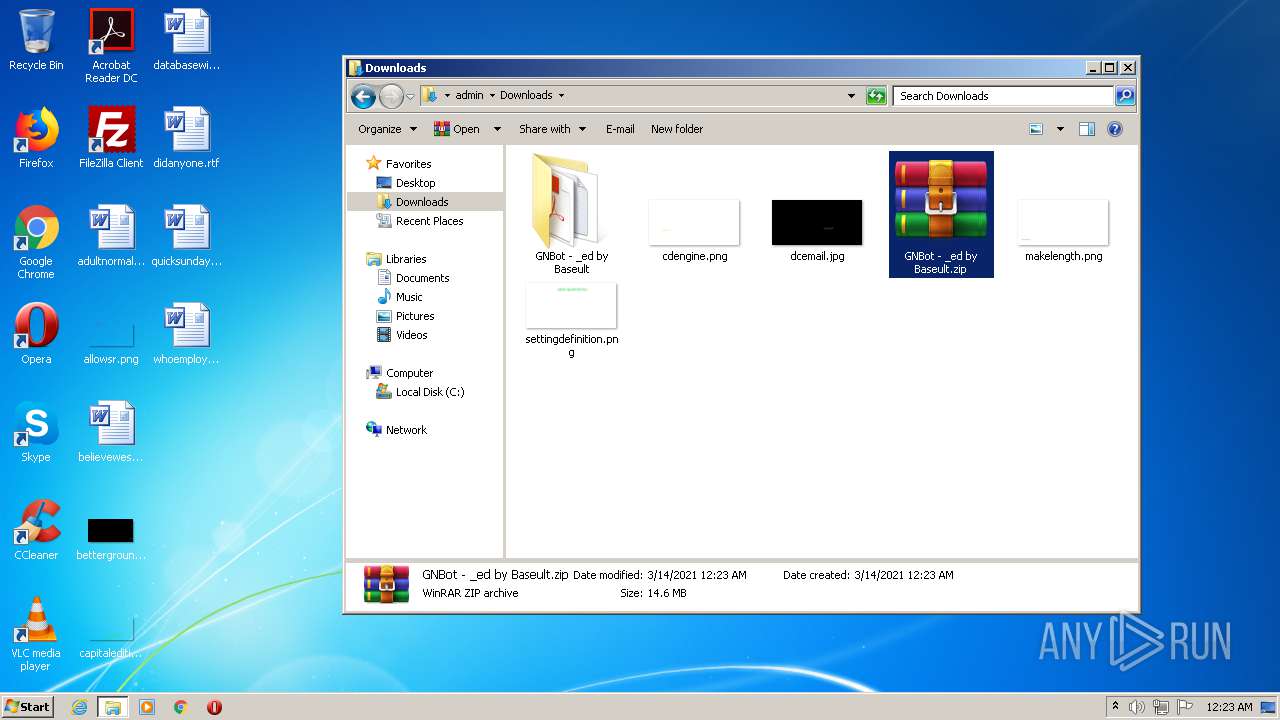
Drops executable file immediately after starts
- WinRAR.exe (PID: 1512)
SUSPICIOUS
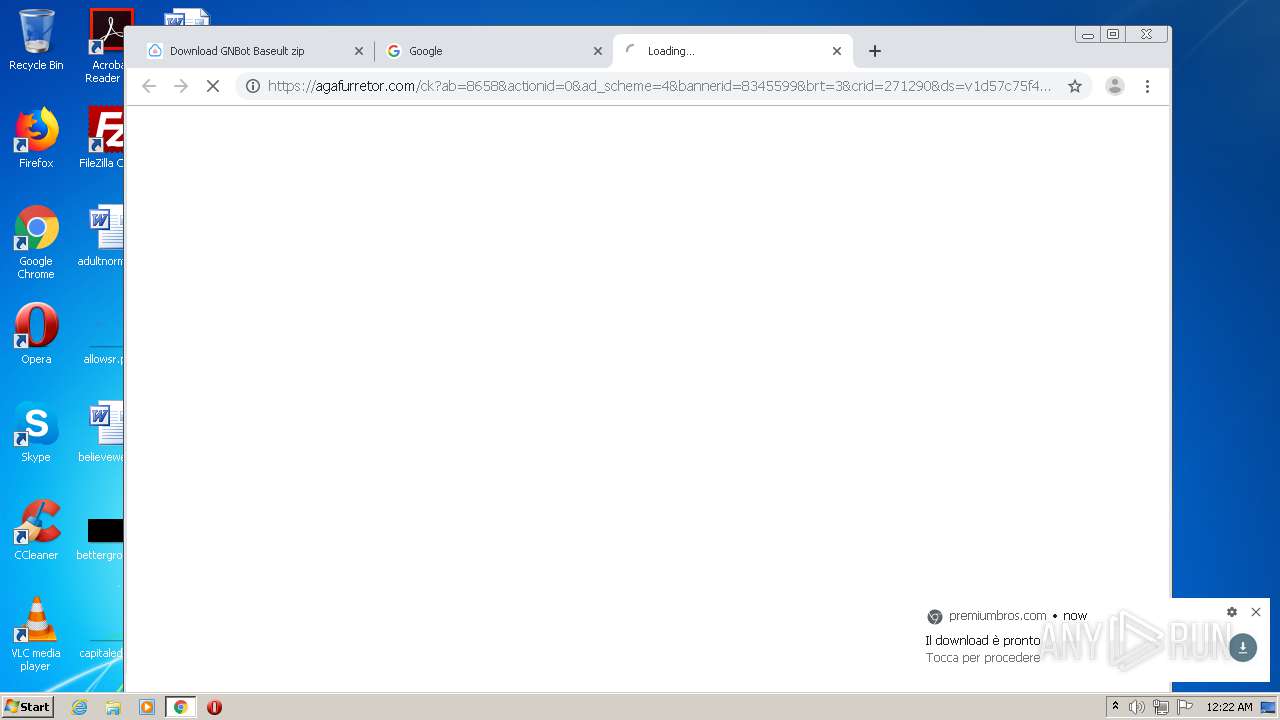
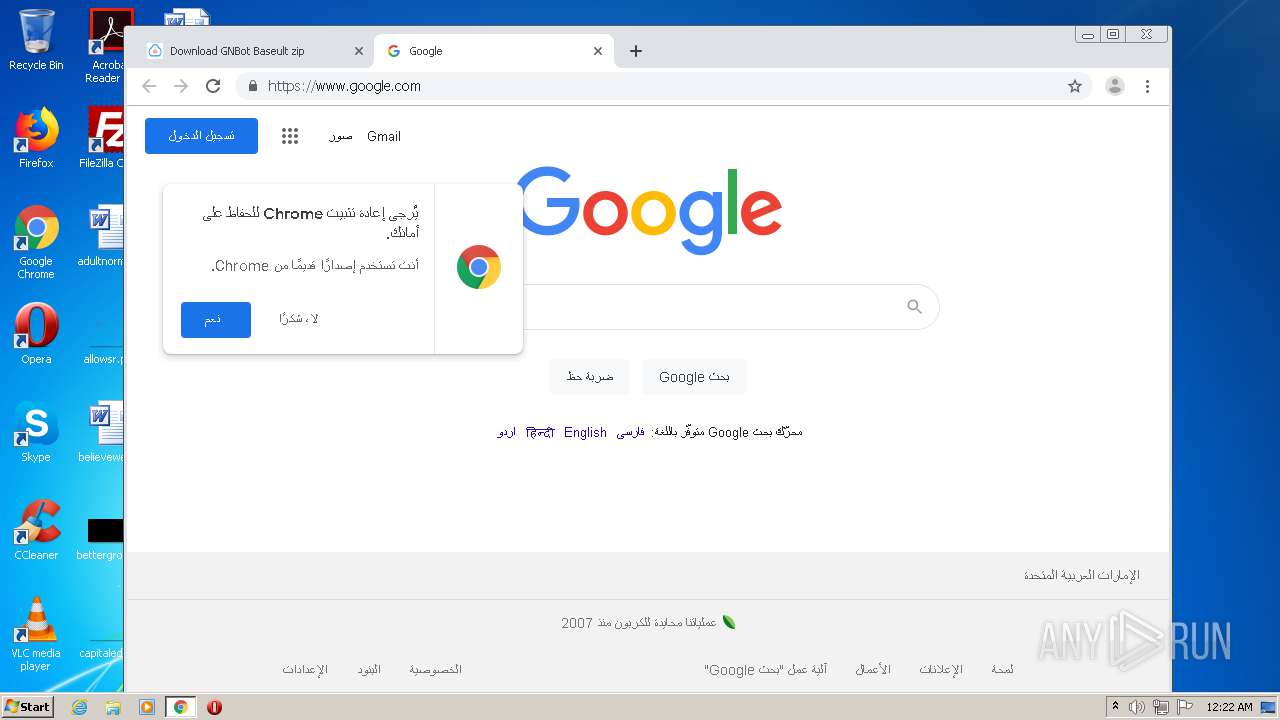
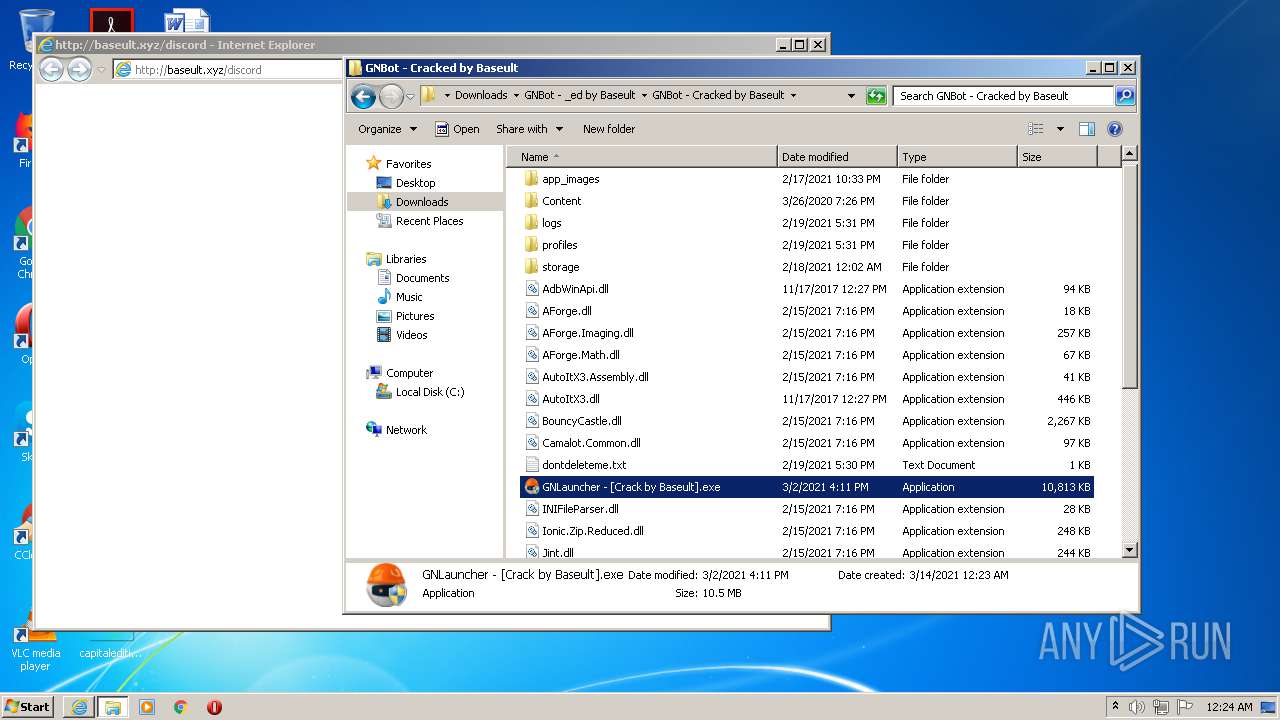
Starts Internet Explorer
- explorer.exe (PID: 376)
- GNLauncher - [Crack by Baseult].exe (PID: 3056)
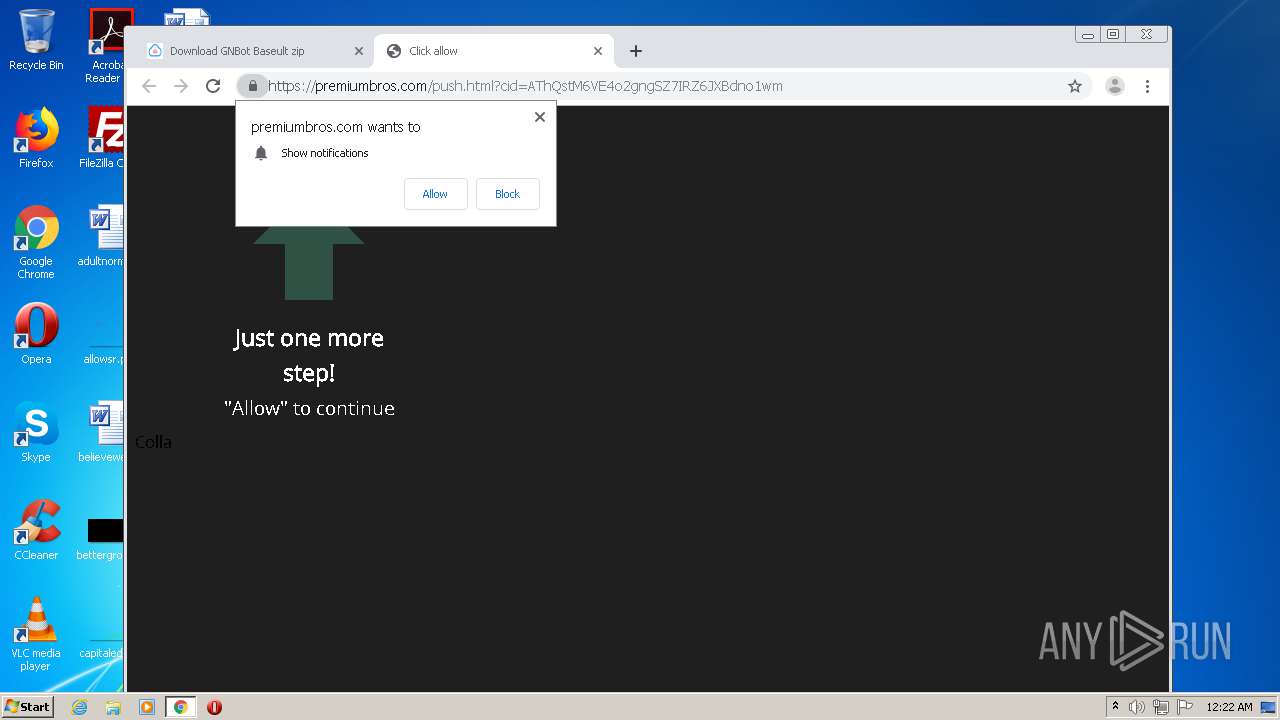
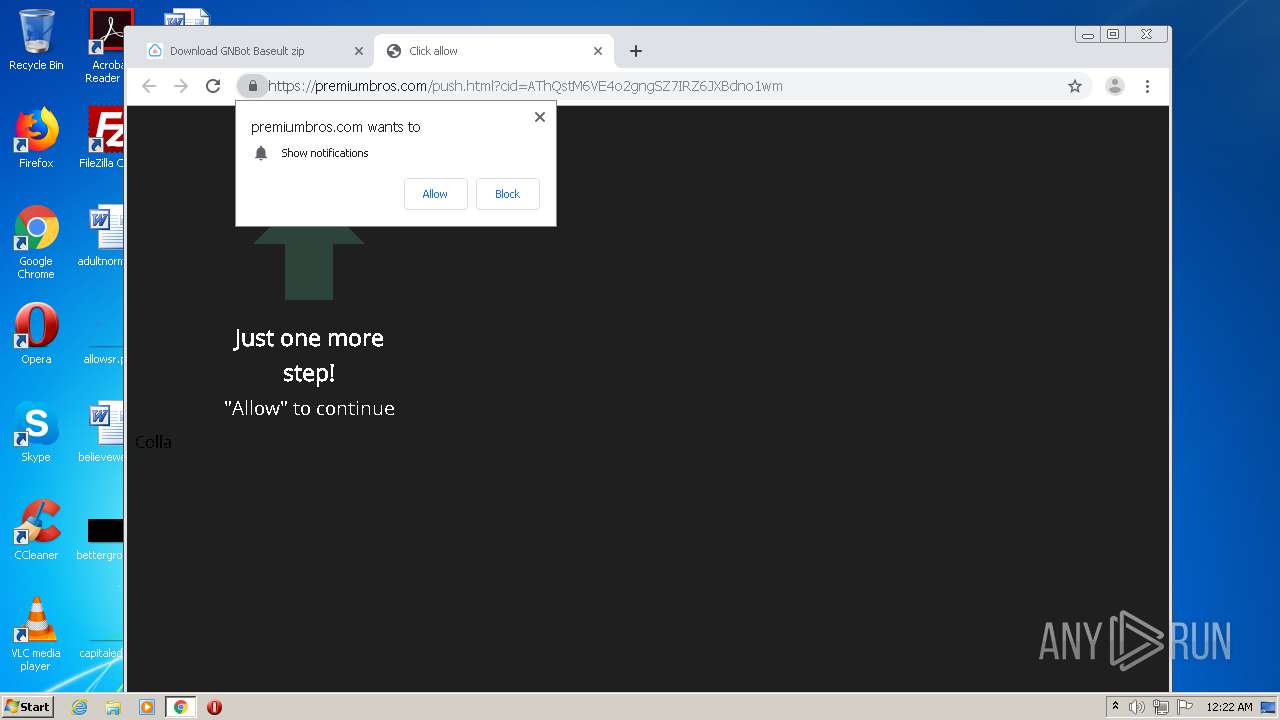
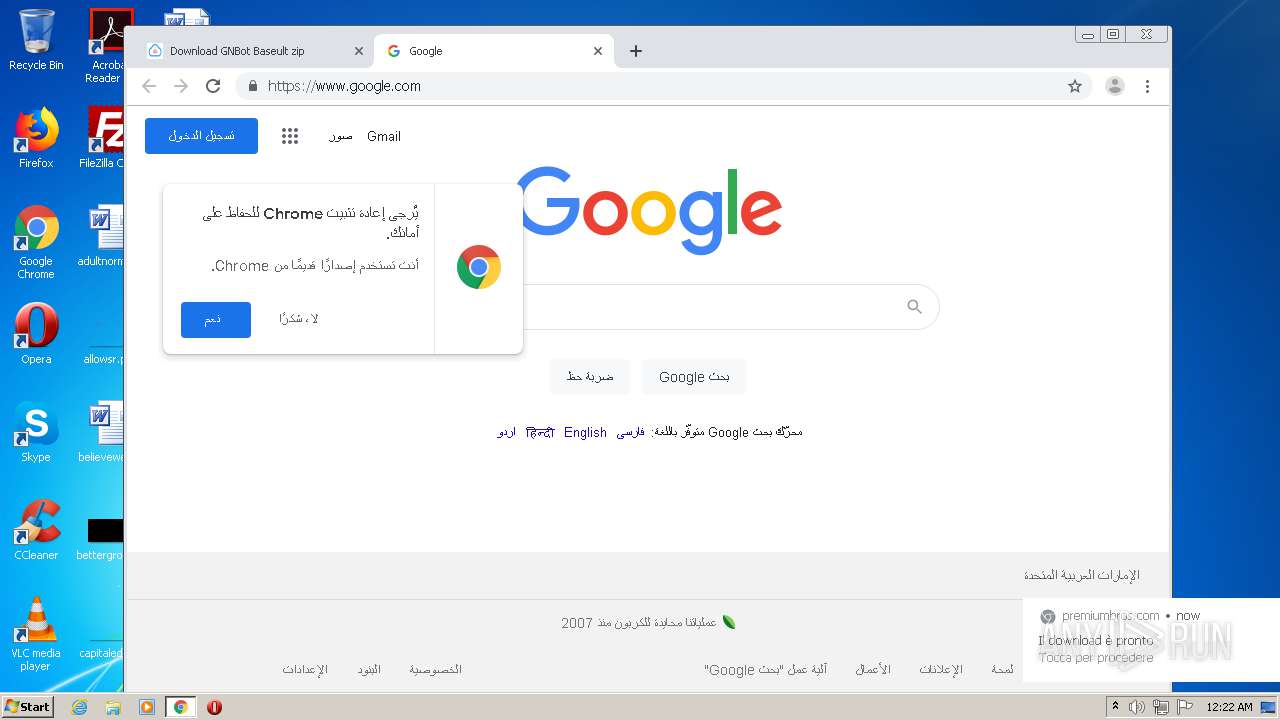
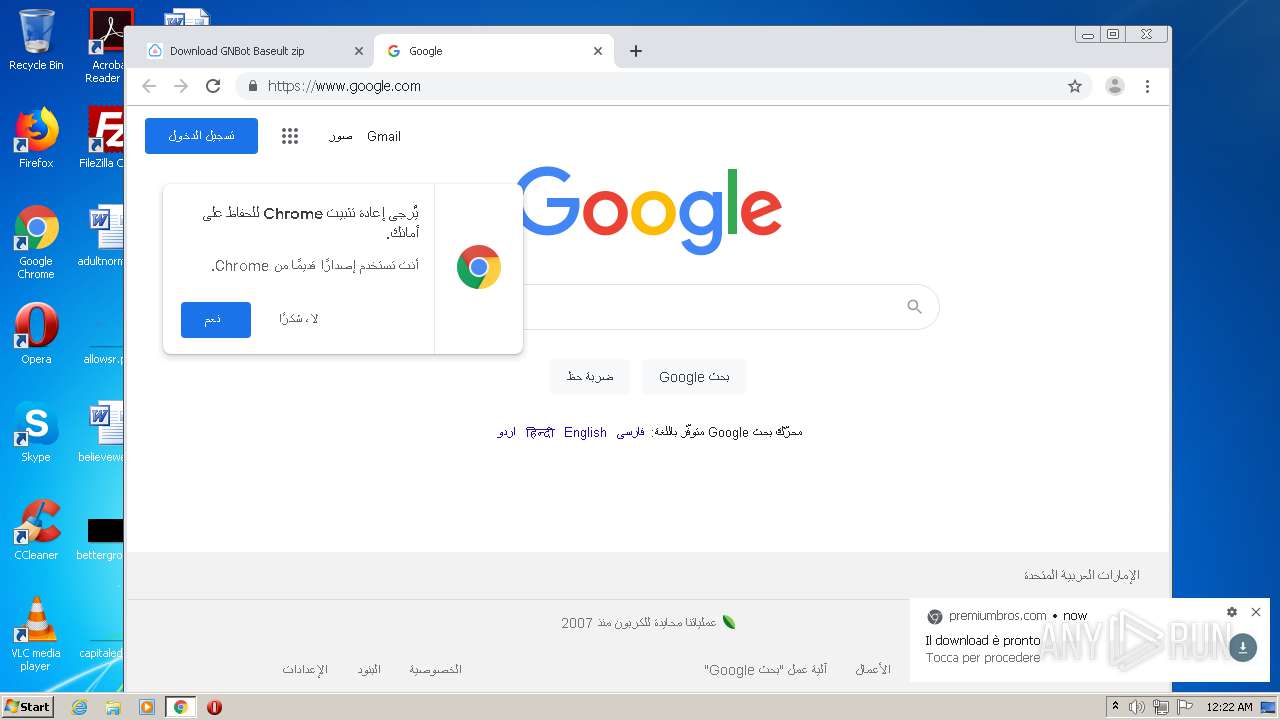
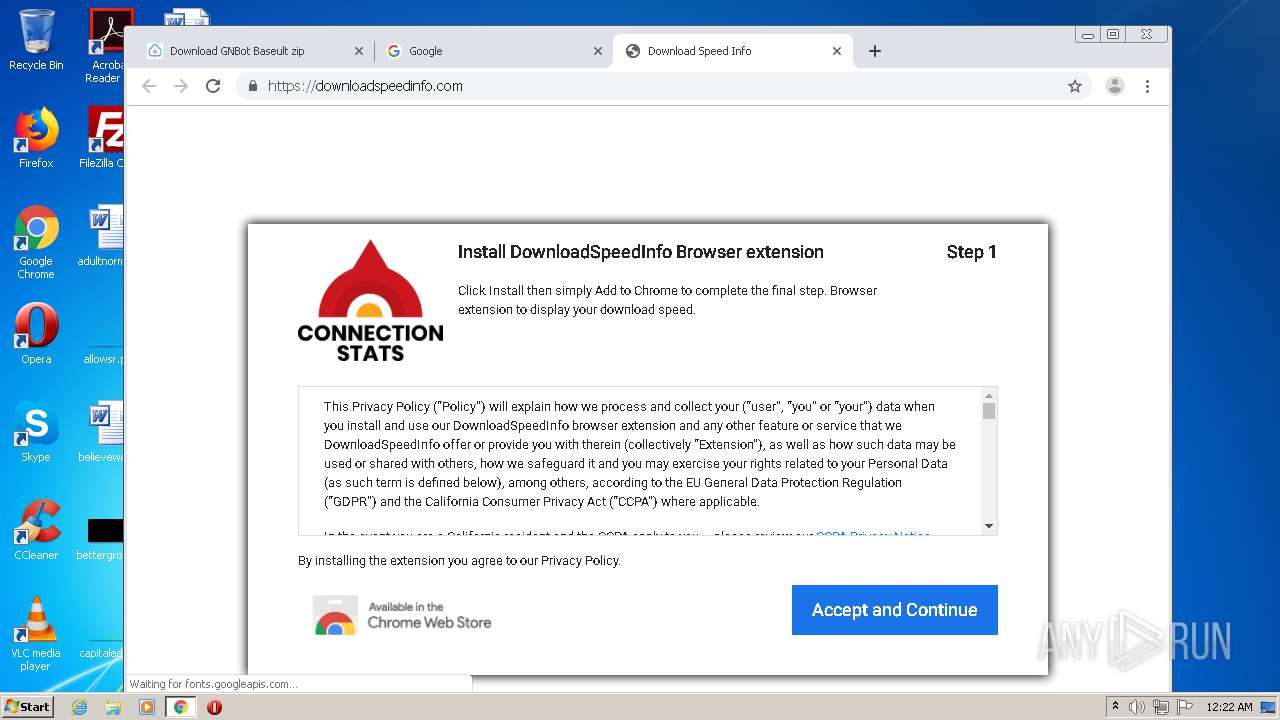
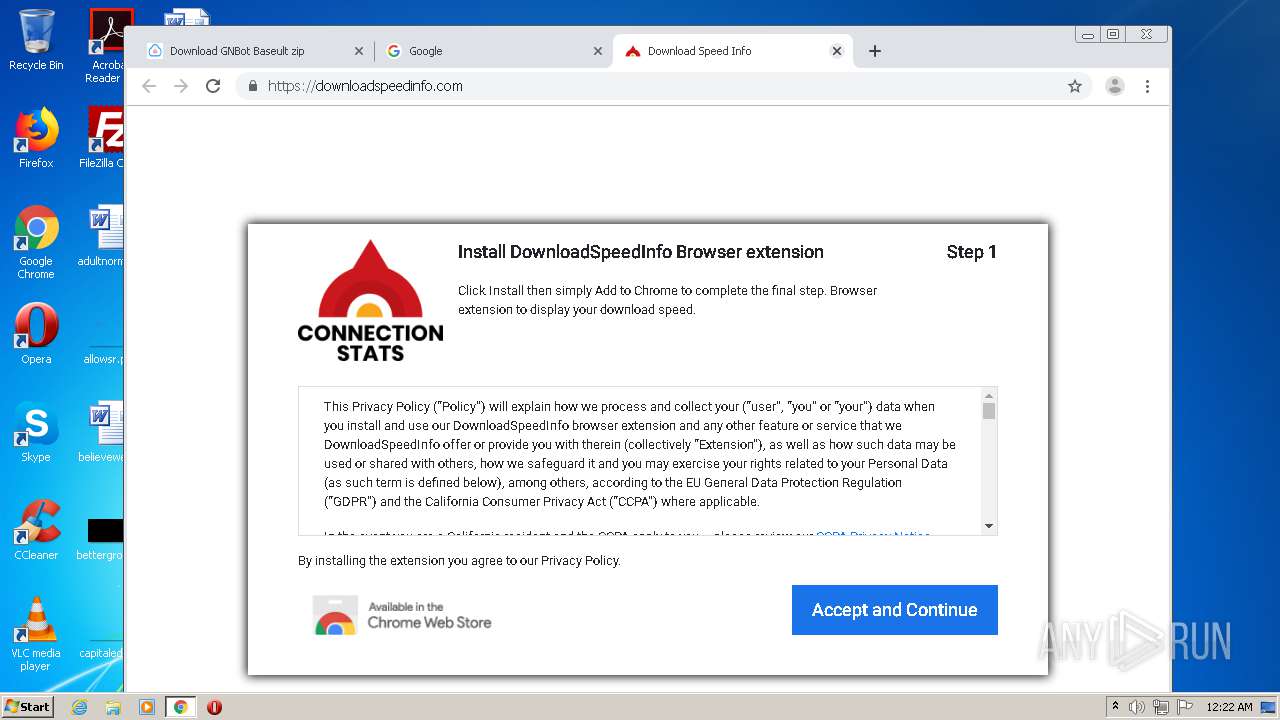
Modifies files in Chrome extension folder
- chrome.exe (PID: 3824)
Drops a file with a compile date too recent
- chrome.exe (PID: 3824)
Drops a file with too old compile date
- WinRAR.exe (PID: 1512)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1512)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1512)
Reads Environment values
- GNLauncher - [Crack by Baseult].exe (PID: 3192)
- GNLauncher - [Crack by Baseult].exe (PID: 3056)
Adds / modifies Windows certificates
- GNLauncher - [Crack by Baseult].exe (PID: 3192)
INFO
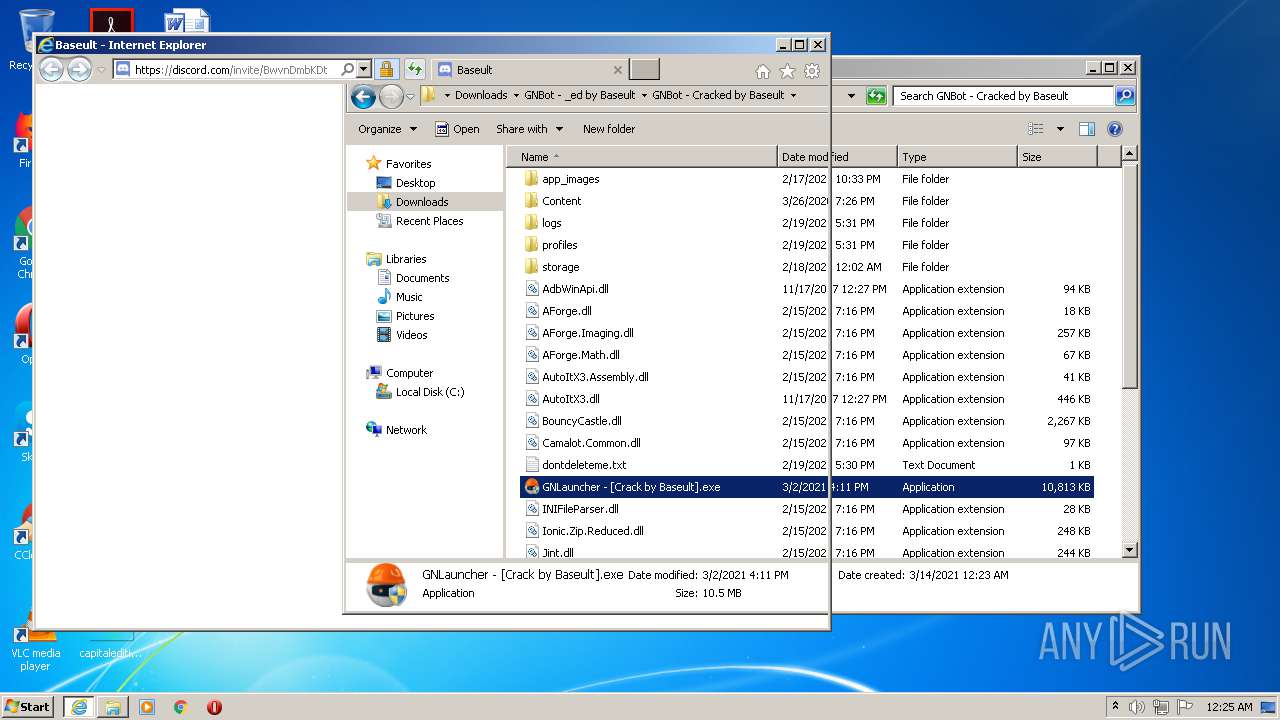
Application launched itself
- iexplore.exe (PID: 2800)
- chrome.exe (PID: 3824)
- iexplore.exe (PID: 3600)
Changes internet zones settings
- iexplore.exe (PID: 2800)
- iexplore.exe (PID: 3600)
Reads settings of System Certificates
- iexplore.exe (PID: 2800)
- iexplore.exe (PID: 2556)
- GNLauncher - [Crack by Baseult].exe (PID: 3192)
- GNLauncher - [Crack by Baseult].exe (PID: 3056)
- iexplore.exe (PID: 2576)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2800)
- iexplore.exe (PID: 2576)
Creates files in the user directory
- iexplore.exe (PID: 2556)
- iexplore.exe (PID: 2800)
- chrome.exe (PID: 3824)
- iexplore.exe (PID: 2576)
Changes settings of System certificates
- iexplore.exe (PID: 2800)
- iexplore.exe (PID: 2576)
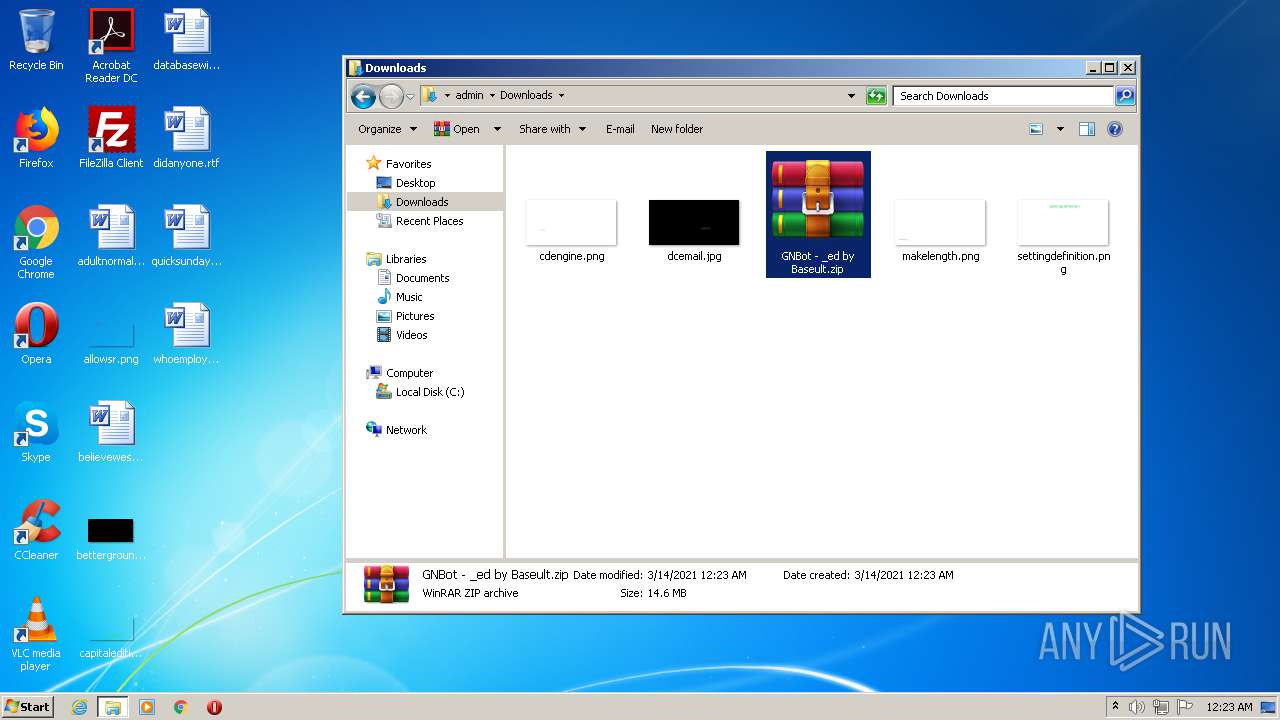
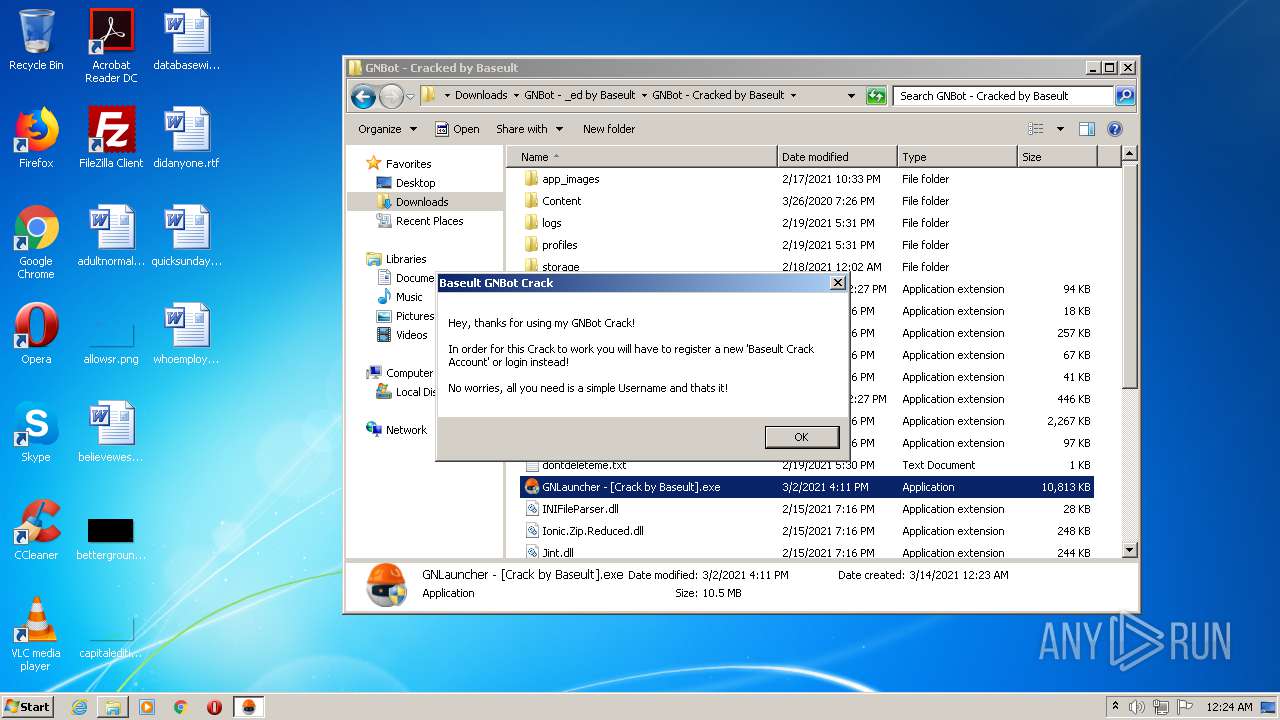
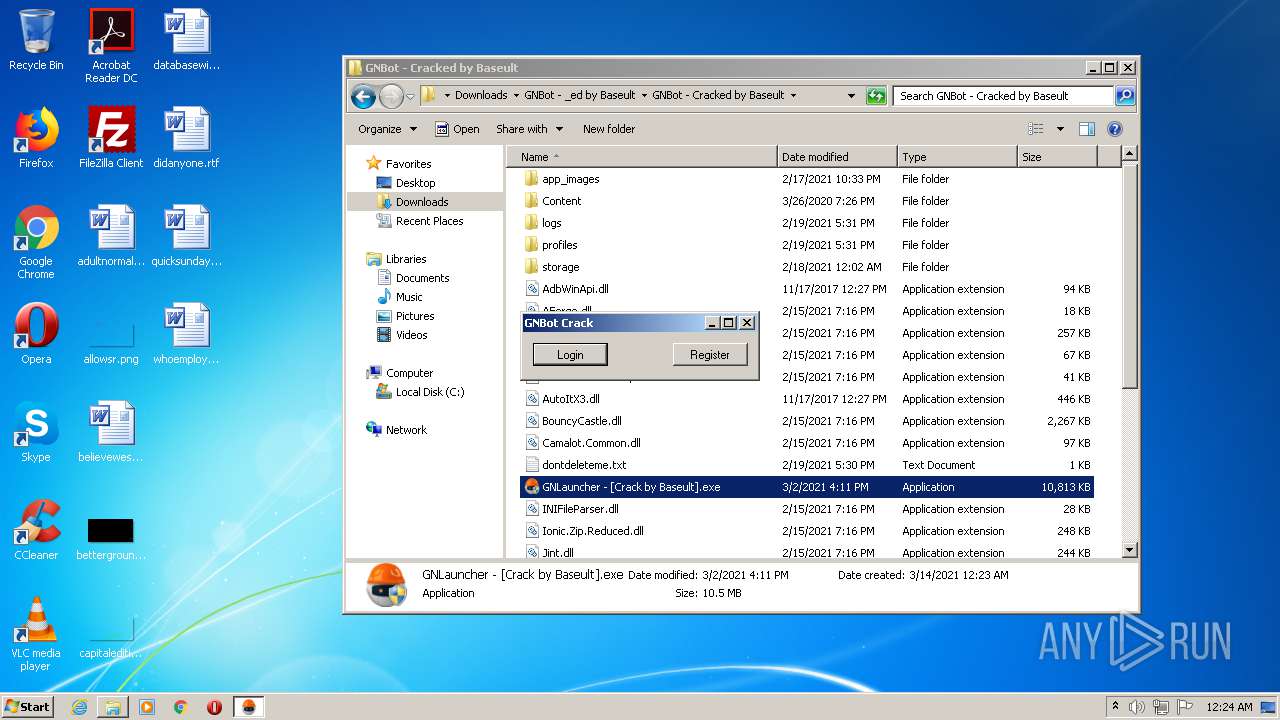
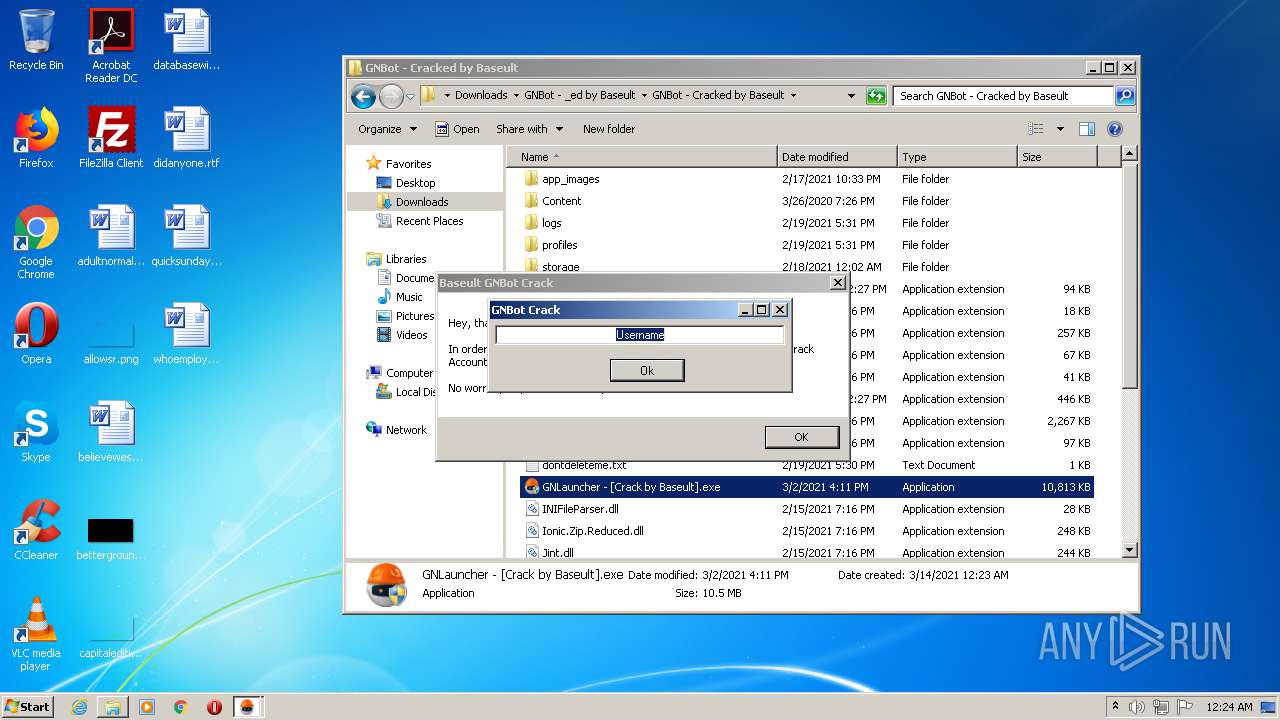
Manual execution by user
- explorer.exe (PID: 2896)
- chrome.exe (PID: 3824)
- WinRAR.exe (PID: 1512)
- GNLauncher - [Crack by Baseult].exe (PID: 3056)
- GNLauncher - [Crack by Baseult].exe (PID: 3192)
- GNLauncher - [Crack by Baseult].exe (PID: 3840)
- GNLauncher - [Crack by Baseult].exe (PID: 1436)
Reads internet explorer settings
- iexplore.exe (PID: 2556)
- iexplore.exe (PID: 2576)
Reads the hosts file
- chrome.exe (PID: 2516)
- chrome.exe (PID: 3824)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
109
Monitored processes
59
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,13403870020167165411,16687064836631959219,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6502841441515662671 --mojo-platform-channel-handle=4228 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,13403870020167165411,16687064836631959219,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18294371390039048922 --mojo-platform-channel-handle=3824 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 376 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6a34a9d0,0x6a34a9e0,0x6a34a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,13403870020167165411,16687064836631959219,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6184929387721731191 --mojo-platform-channel-handle=4948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,13403870020167165411,16687064836631959219,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5253926532960079981 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,13403870020167165411,16687064836631959219,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15661677981559849697 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,13403870020167165411,16687064836631959219,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12470175267787297984 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,13403870020167165411,16687064836631959219,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6479950407088900879 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3560 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,13403870020167165411,16687064836631959219,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6980702021155627783 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 552
Read events
2 912
Write events
630
Delete events
10
Modification events
| (PID) Process: | (376) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 93240616 | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30873704 | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
21
Suspicious files
215
Text files
425
Unknown types
63
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9BC3.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9BC4.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_D9F881E1F961D6F8B49F8B469D150B33 | binary | |
MD5:5F9B59F54ECB8110A8F8A1301886FDBF | SHA256:096E0C91B1731938F5BDC5216414575E382492923670B6BD370F3F71242BF4B2 | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:5A2FF66251CAB90CCB28A6D9EF3F34CB | SHA256:316D99342727E8C7E431A8BBC8FC3E61112B9D6D61F45921A0797C60280F80D4 | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:9E0452539EFA08611B2D8953AAA61D40 | SHA256:308FFE4AAC6310E56901F60495A7444271F4666DBE3DFAB420FF3AF563842A96 | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_8F3602ACF8FC41F142C7284385467024 | binary | |
MD5:2F0C753DC4DB3040C8C937046BA3E2B0 | SHA256:4BBDFF6D371482FACF1706D13FF40CE811CEF55172DB97A242EDD21CC9565293 | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_8F3602ACF8FC41F142C7284385467024 | der | |
MD5:AF844A7A0205247CE36C67C69B5C948D | SHA256:BF71D9C8225819244A5FD24A85D40B3E43F2B42DE6533C33B8C41B218E8BCAFC | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_D9F881E1F961D6F8B49F8B469D150B33 | der | |
MD5:48ACF1D2D42C851997A1E1AC74F3E0A5 | SHA256:C9E4824CCA7A97E7469FE8A16686D7DDED404C460D9150DA9B222D90350FBC5E | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\paging[1].js | html | |
MD5:14285B326BFE8E94F741B8602243314A | SHA256:AB74DA71057179EC29375C143CE27D61701C5372CF8CB737ED225AA7402F3F66 | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\sw[1].js | text | |
MD5:BF6FD2F028FD688127C66F7ED658E54E | SHA256:1078BD4C3AC5B02F849FE8213E88C2757AB416F053D82001E09D4EA93A068743 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
147
DNS requests
90
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2556 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA6DLDjiXblFjYtF4FSOjzY%3D | US | der | 278 b | whitelisted |
2556 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAWKr0p%2F2vn5LFrU8BrgrmU%3D | US | der | 280 b | whitelisted |
2556 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2556 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2556 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA6DLDjiXblFjYtF4FSOjzY%3D | US | der | 278 b | whitelisted |
2556 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2556 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2556 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2556 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEHNn1O351wPHAwAAAADLno8%3D | US | der | 471 b | whitelisted |
2556 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2556 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2556 | iexplore.exe | 104.21.13.101:443 | usersdrive.com | Cloudflare Inc | US | unknown |
2556 | iexplore.exe | 142.250.185.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2556 | iexplore.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
2556 | iexplore.exe | 13.32.23.164:443 | d3v3bqdndm4erx.cloudfront.net | Amazon.com, Inc. | US | unknown |
2556 | iexplore.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
2556 | iexplore.exe | 142.250.185.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2556 | iexplore.exe | 54.237.125.12:443 | jistenbefor.space | Amazon.com, Inc. | US | suspicious |
2556 | iexplore.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
2800 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
usersdrive.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
d3v3bqdndm4erx.cloudfront.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.google.com |
| malicious |
ocsp.pki.goog |
| whitelisted |
jistenbefor.space |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2576 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2576 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |