| File name: | mrt100_app.dll |
| Full analysis: | https://app.any.run/tasks/685920b2-d71b-4a7d-be3b-c211ce0e9b11 |
| Verdict: | No threats detected |
| Analysis date: | July 04, 2019, 15:06:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (DLL) (GUI) x86-64, for MS Windows |
| MD5: | 9E6B0351C08EA598C85BD38570BF4D33 |
| SHA1: | ED6B981A9752A244B03438A1FF622614DF376F84 |
| SHA256: | 6D57C646566FBDE97324399D5FFC4F2420B8FF5BDBCC72D0D70AF768B35B5123 |
| SSDEEP: | 6144:r/6p6ANk75lEm45BTmuxEdwgo3uEGTN/gmXnRW3zOPaJr/KFbWSdZ/WVfirnwGvv:rI/glE4dFoeEGTN4mXnRW3ziH/Gf2ziO |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:01:29 01:13:34+01:00 |
| PEType: | PE32+ |
| LinkerVersion: | 14.11 |
| CodeSize: | 333312 |
| InitializedDataSize: | 93696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x81180 |
| OSVersion: | 6.2 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.27328.1 |
| ProductVersionNumber: | 2.2.27328.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft .NET Native Runtime |
| FileVersion: | 2.2.27328.1 built by: PROJECTNREL |
| InternalName: | mrt100_app.dll |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | mrt100_app.dll |
| ProductName: | Microsoft® .NET Framework |
| ProductVersion: | 2.2.27328.1 |
| Comments: | Flavor=Retail |
| PrivateBuild: | DDBLD200D |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jan-2019 00:13:34 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft .NET Native Runtime |
| FileVersion: | 2.2.27328.1 built by: PROJECTNREL |
| InternalName: | mrt100_app.dll |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | mrt100_app.dll |
| ProductName: | Microsoft® .NET Framework |
| ProductVersion: | 2.2.27328.1 |
| Comments: | Flavor=Retail |
| PrivateBuild: | DDBLD200D |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 38 |
| Time date stamp: | 29-Jan-2019 00:13:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.pad0 | 0x00001000 | 0x00000008 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.pad1 | 0x00002000 | 0x00000008 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.pad2 | 0x00003000 | 0x00000008 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.pad3 | 0x00004000 | 0x00000008 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.pad4 | 0x00005000 | 0x00000008 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.pad5 | 0x00006000 | 0x00000008 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.pad6 | 0x00007000 | 0x00000008 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.pad7 | 0x00008000 | 0x00000008 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.pad8 | 0x00009000 | 0x00000008 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.pad9 | 0x0000A000 | 0x00000008 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.54922 | 1012 | Latin 1 / Western European | English - United States | RT_VERSION |
CLRDEBUGINFOWINDOWSAMD64 | 4.24145 | 40 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
COREXTERNALDATAACCESSRESOURCE | 4.04542 | 204 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
MINIDUMP_AUXILIARY_PROVIDER | 3.25163 | 12 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
VCRUNTIME140_APP.dll |
api-ms-win-core-com-l1-1-1.dll |
api-ms-win-core-delayload-l1-1-1.dll |
api-ms-win-core-errorhandling-l1-1-1.dll |
api-ms-win-core-errorhandling-l1-1-3.dll (delay-loaded) |
api-ms-win-core-fibers-l1-1-1.dll |
api-ms-win-core-file-l1-2-1.dll |
api-ms-win-core-handle-l1-1-0.dll |
api-ms-win-core-heap-l1-2-0.dll |
api-ms-win-core-interlocked-l1-2-0.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
GetRuntimeException | 1 | 0x0003F6F0 |
ProcessFinalizers | 2 | 0x0003F8A0 |
RegisterCodeManager | 3 | 0x0004E4A0 |
RhAllocLocal | 4 | 0x0003E440 |
RhAllocLocal2 | 5 | 0x0003E410 |
RhAllocateThunk | 6 | 0x0003DB40 |
RhAllocateThunksMapping | 7 | 0x000482D0 |
RhArrayStoreCheckAny | 8 | 0x0003E490 |
RhBox | 9 | 0x0003E770 |
RhBoxAndNullCheck | 10 | 0x0003E470 |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
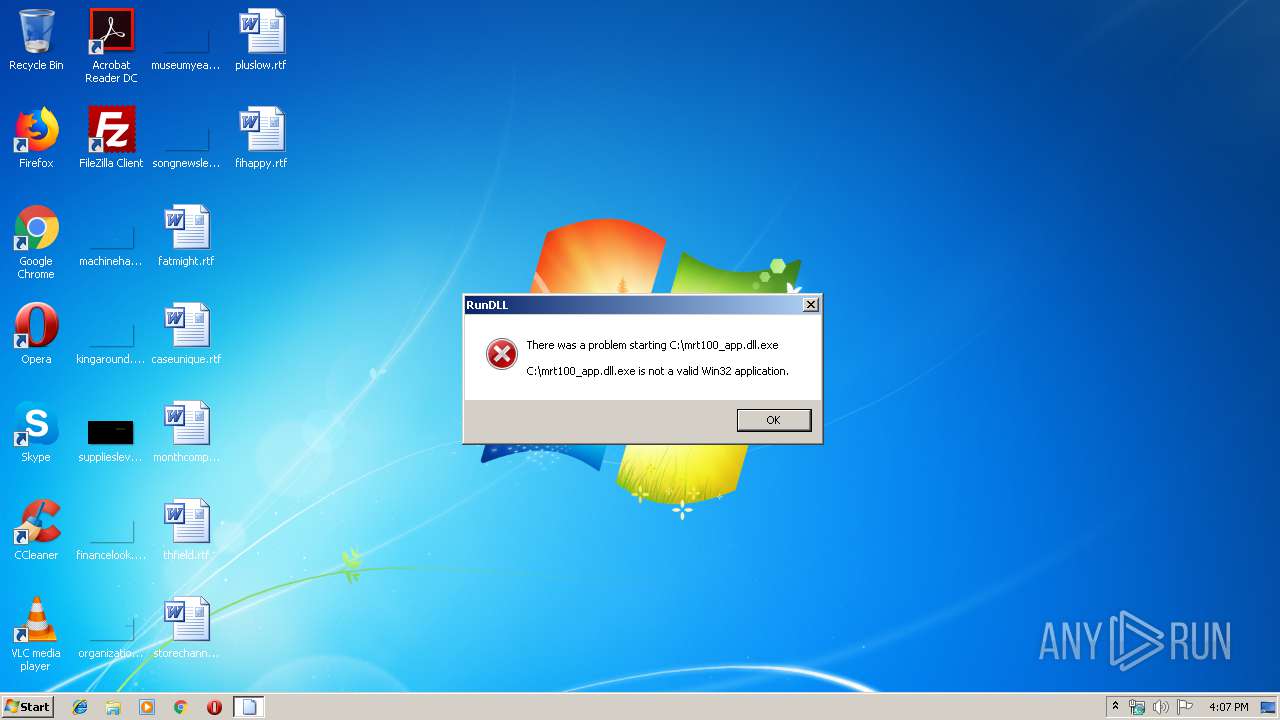
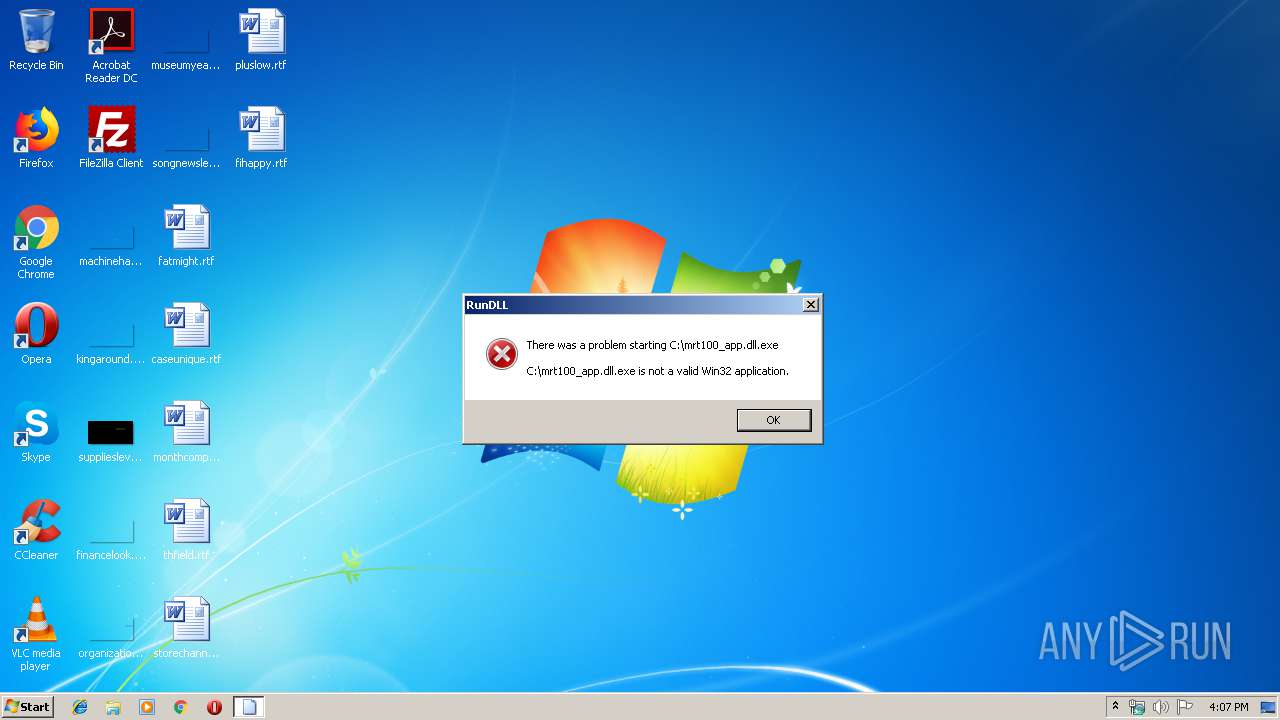
| 3144 | "C:\Windows\System32\rundll32.exe" "C:\mrt100_app.dll.exe", GetRuntimeException | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report