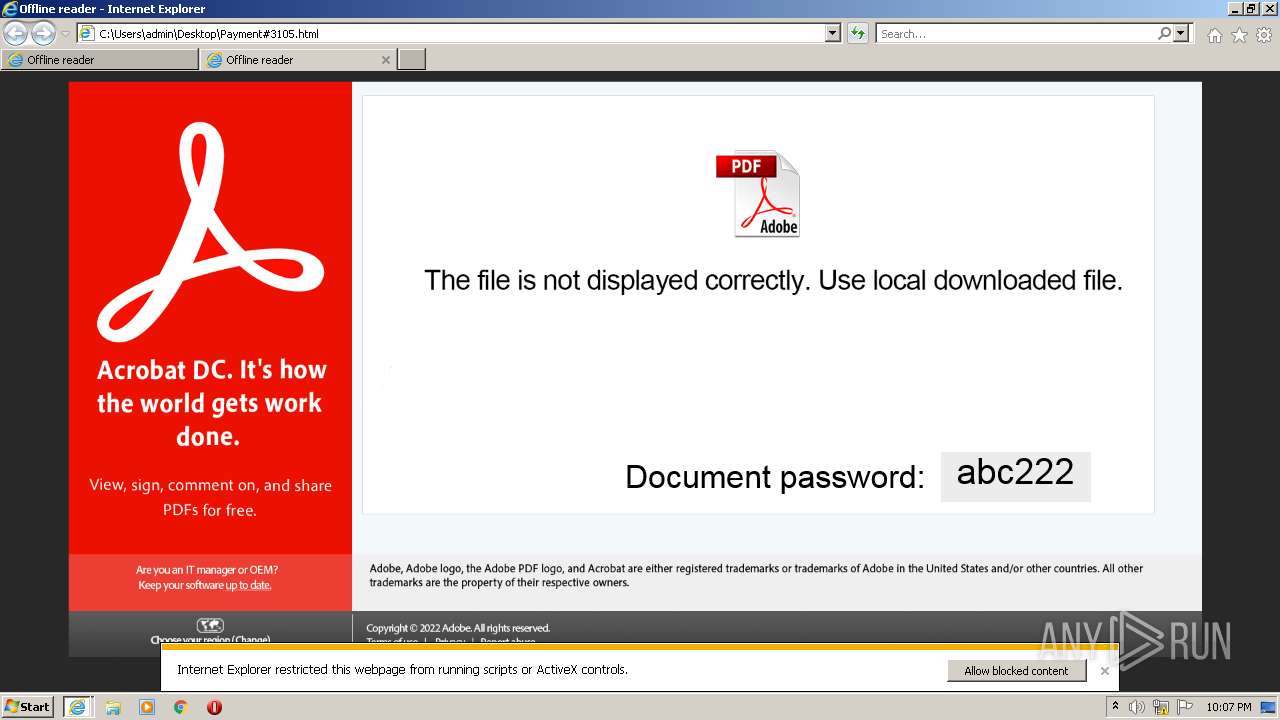
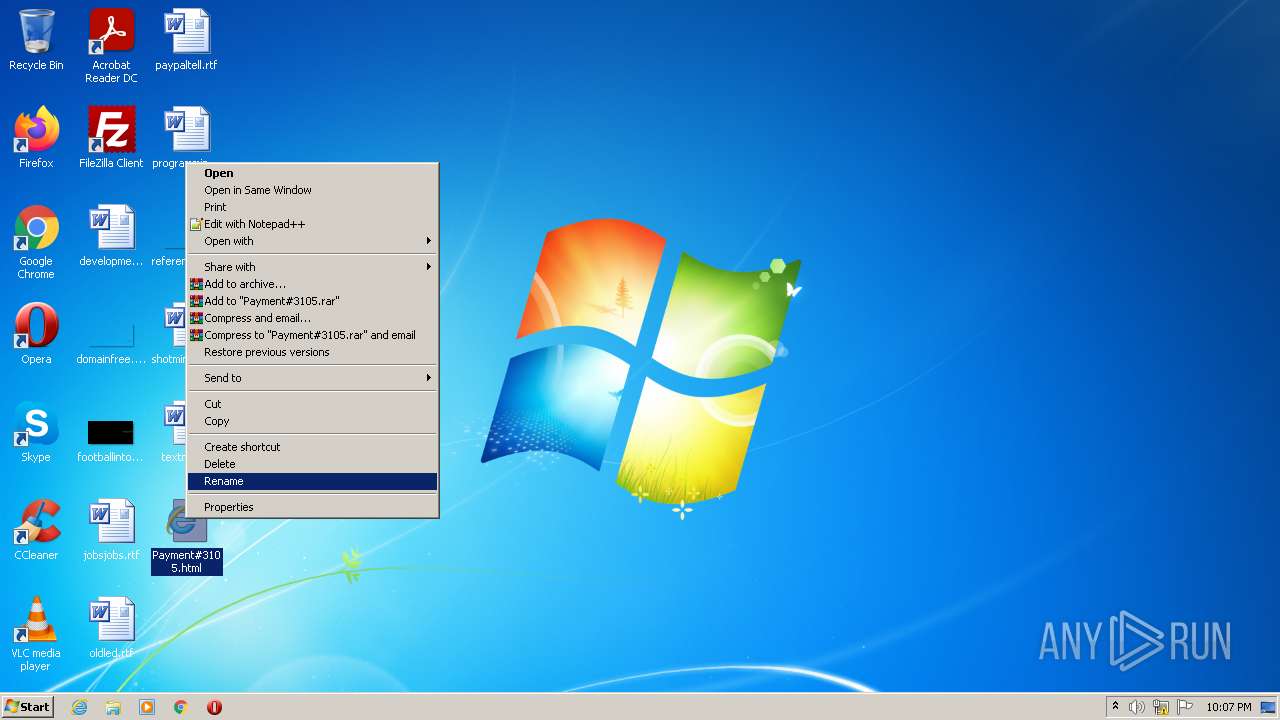
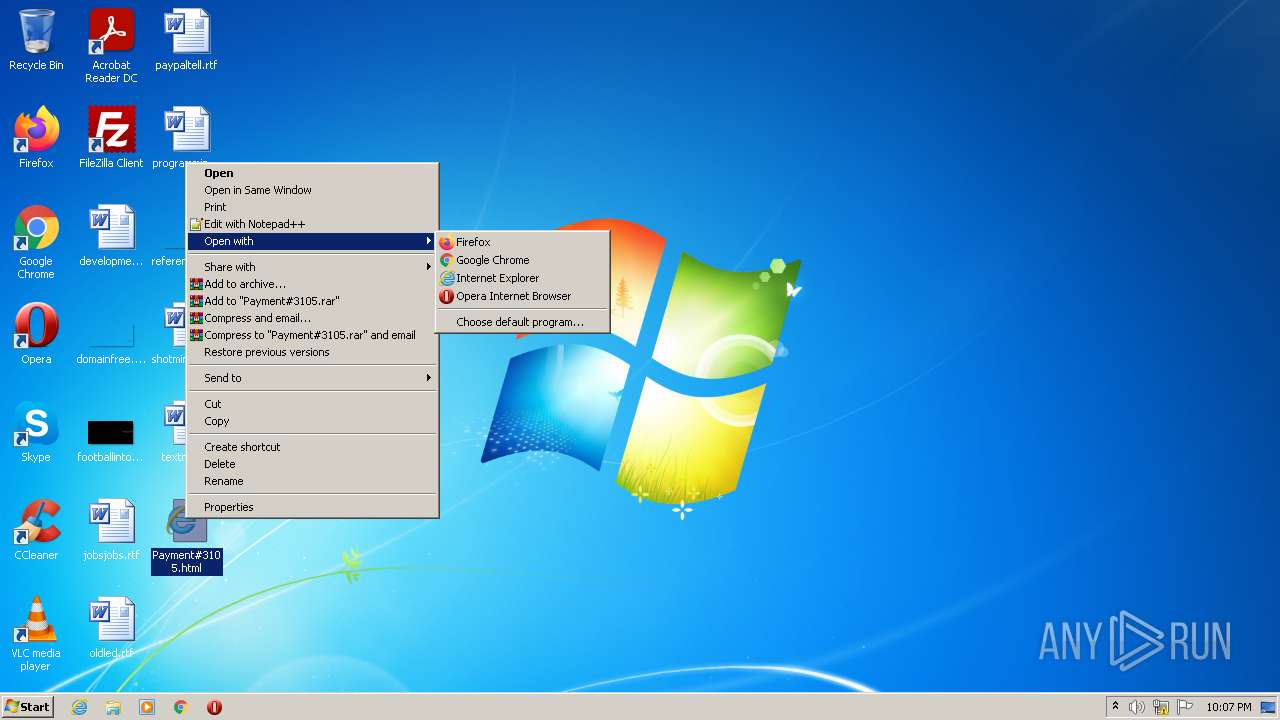
| File name: | Payment#3105.html |
| Full analysis: | https://app.any.run/tasks/fb92f7a0-c6cd-4dc8-8f66-de73cb16e30a |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 21:07:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | D0A63FEF4F9252563A65E00CA92731BC |
| SHA1: | CB5E0E9ACD27F62D72D9C138DC49287CAA7CC7F4 |
| SHA256: | 6D412D2F9B1C6B3226ED1F6CFEDE3E7A925D54D563FFB7A7B99034BD010A69E7 |
| SSDEEP: | 24576:sPPyYJS3kEQS+fLtK7VJmx2lNVUWWsydo0Buy4OvTgx0Hj9LJpvNnd:7BMx2vox8x0l1d |
MALICIOUS
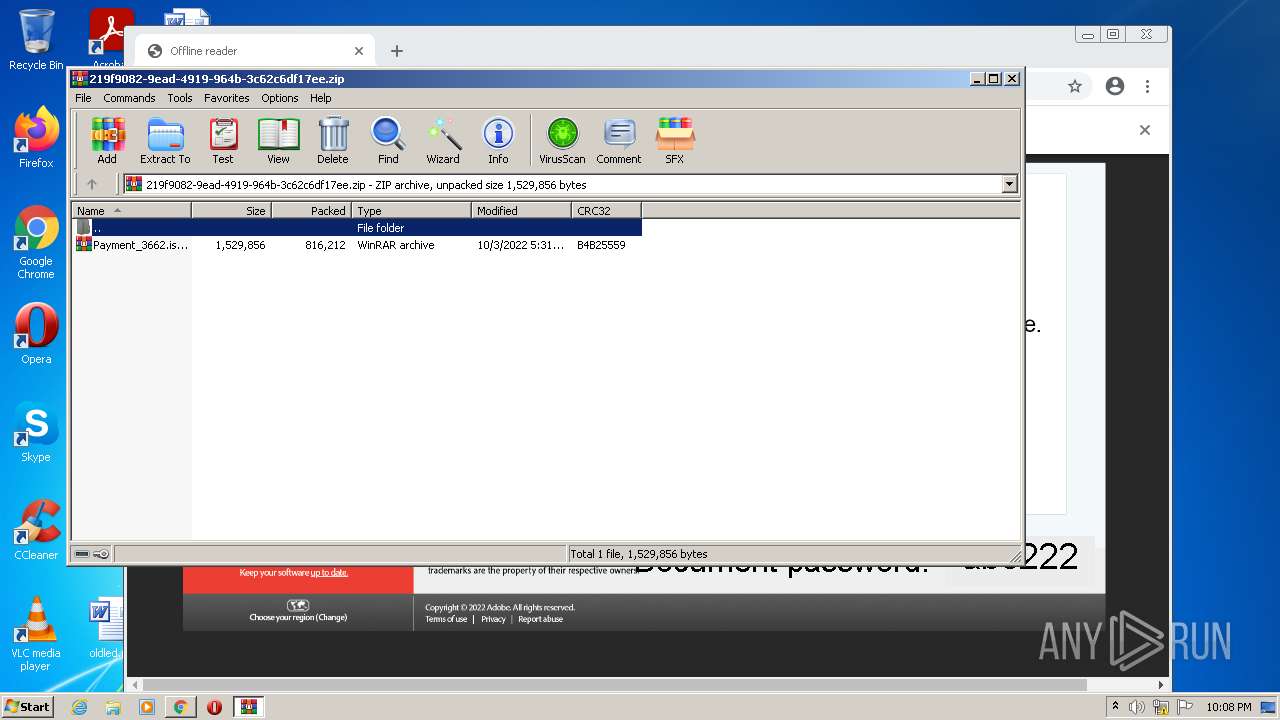
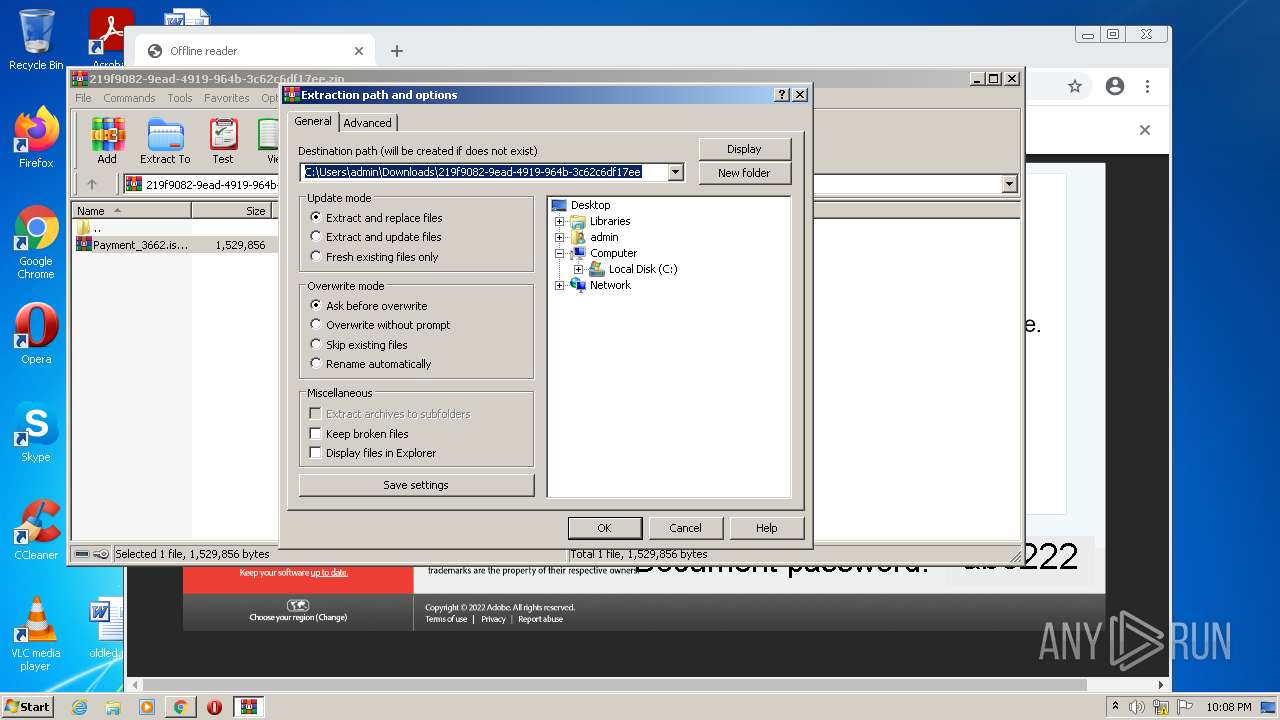
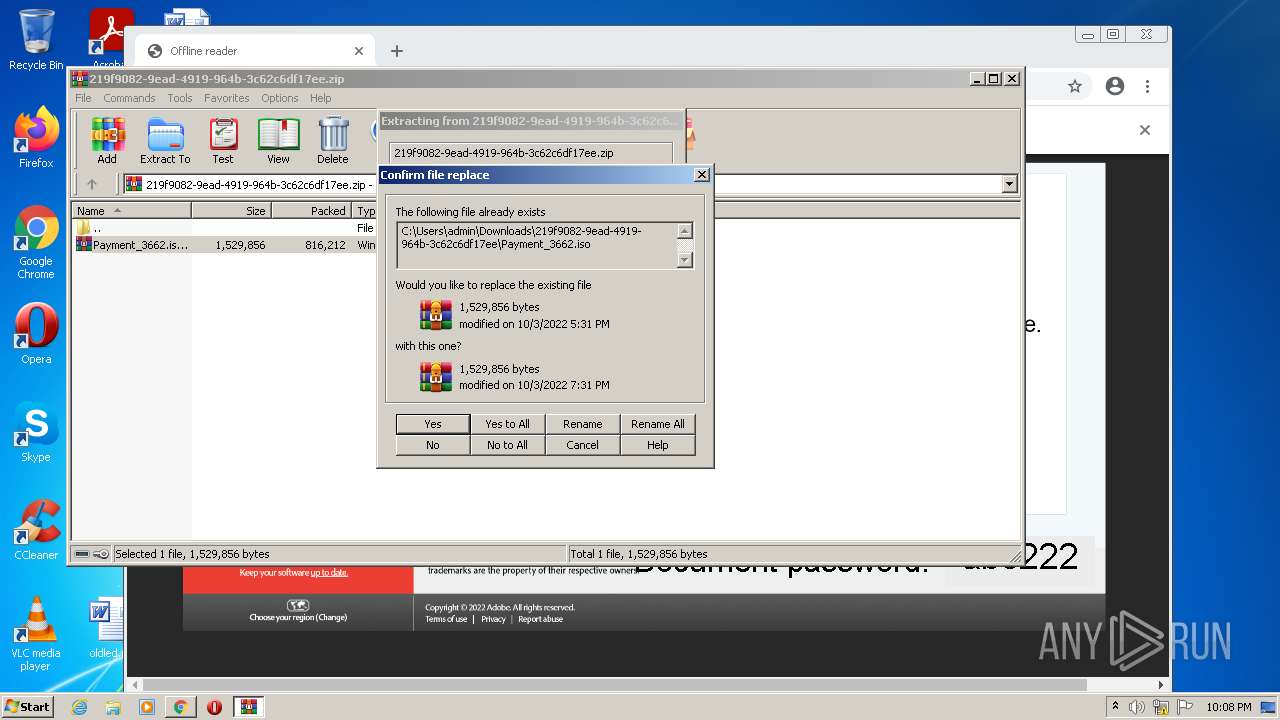
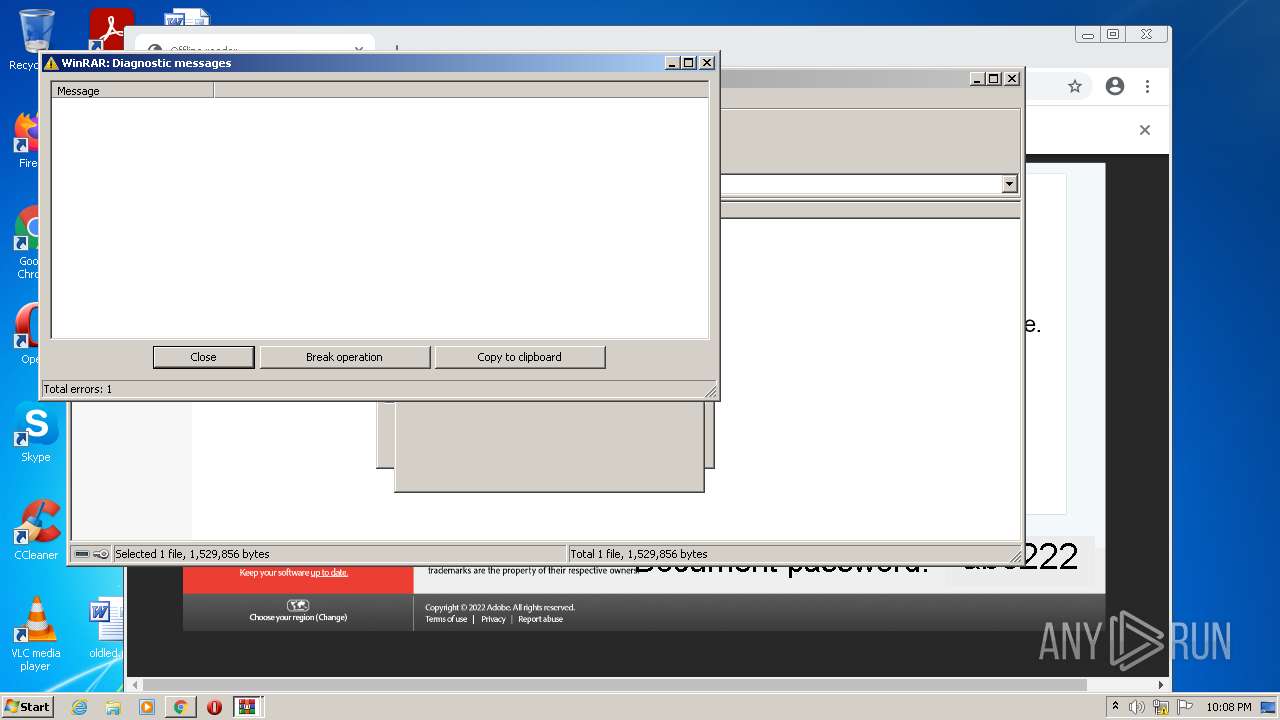
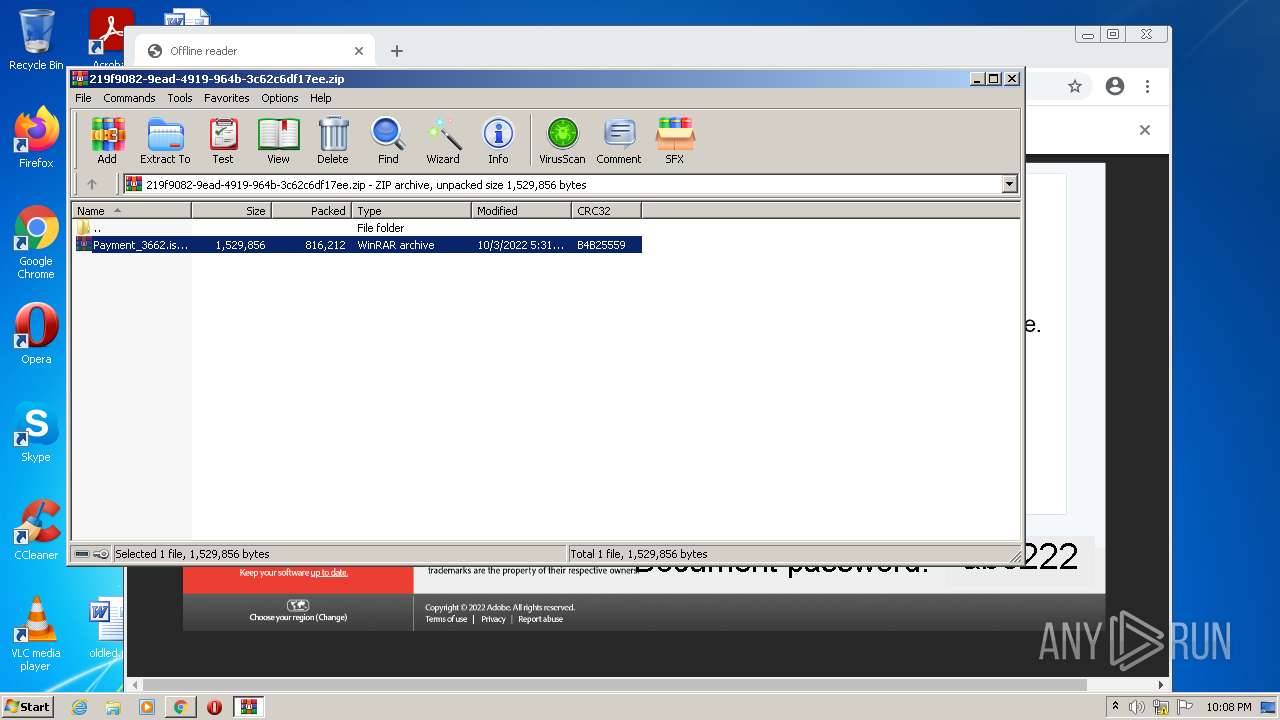
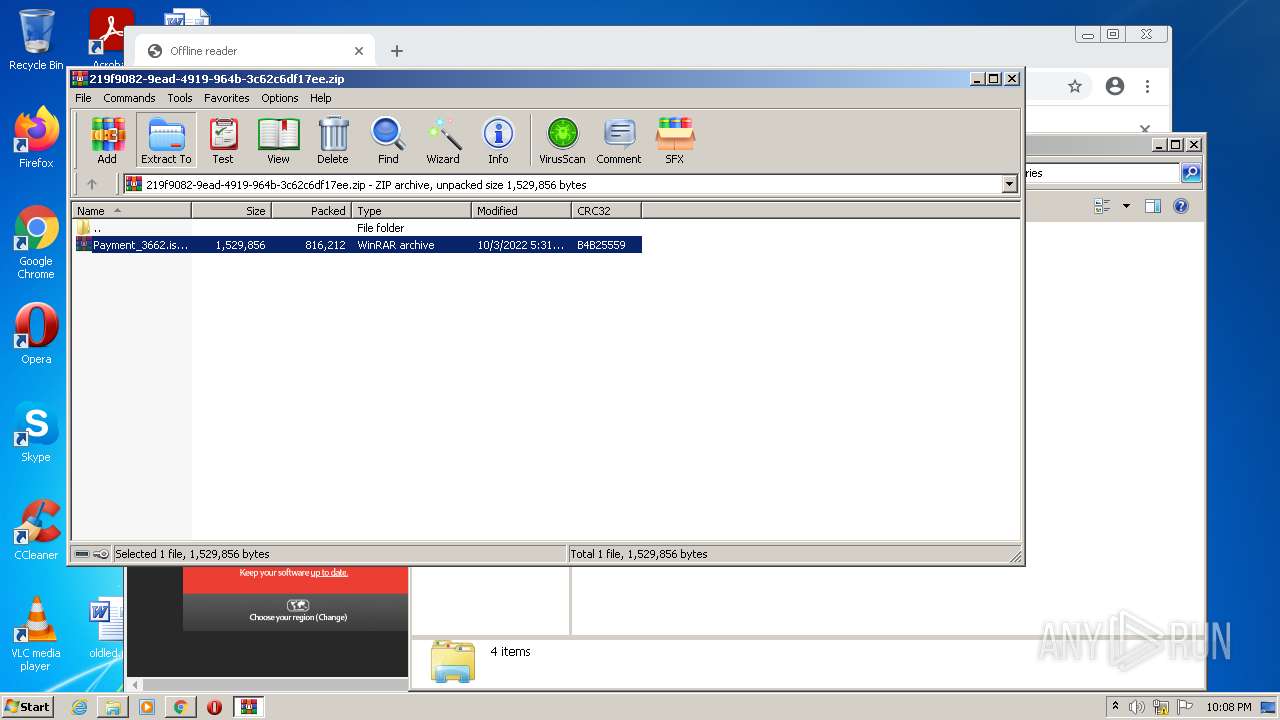
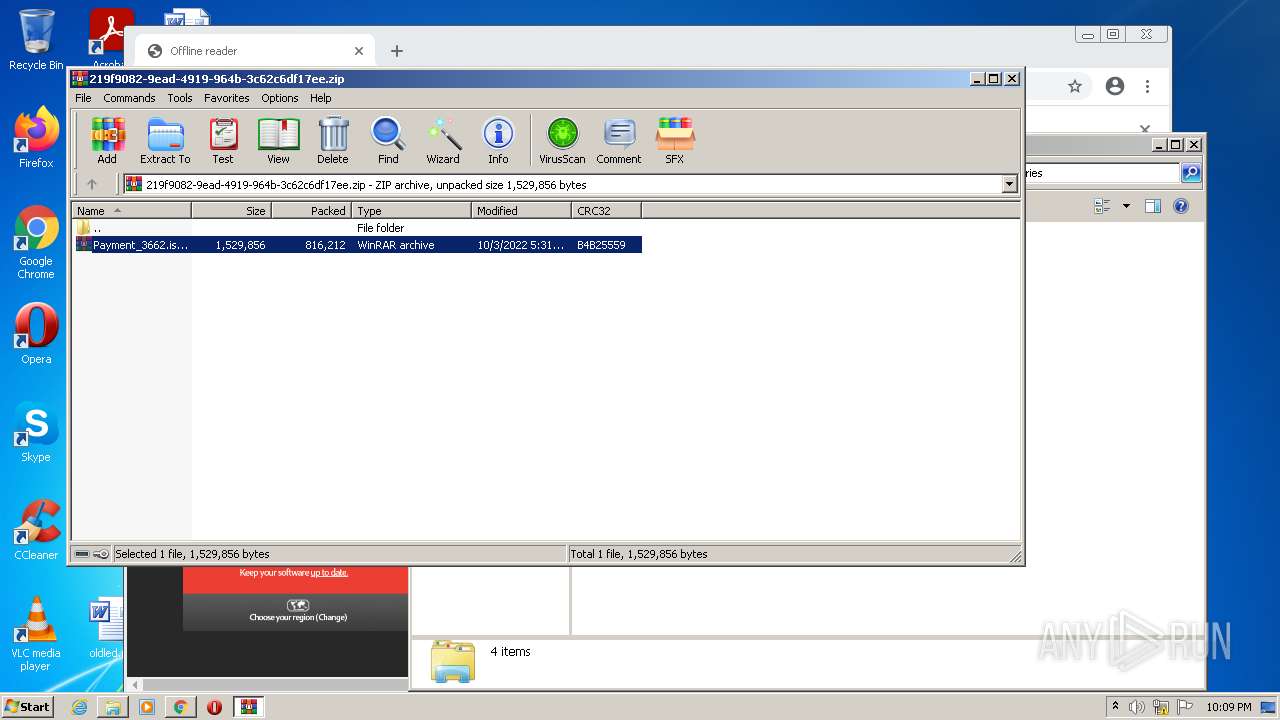
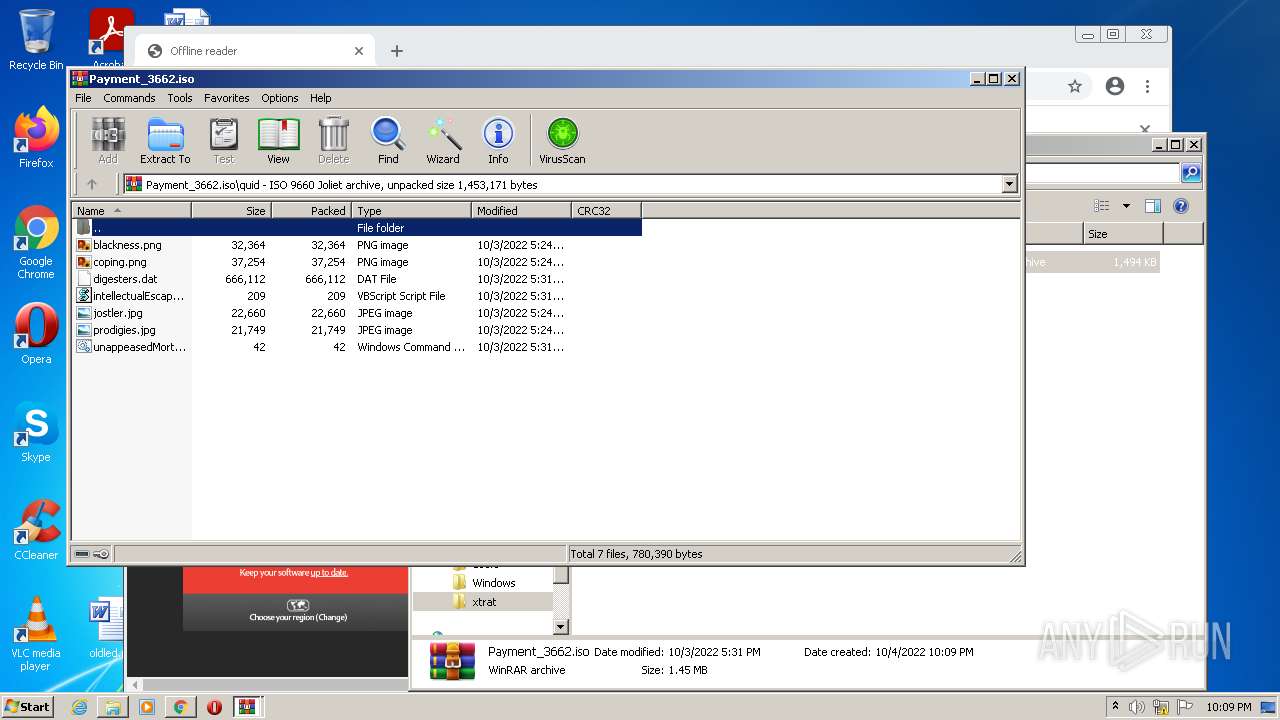
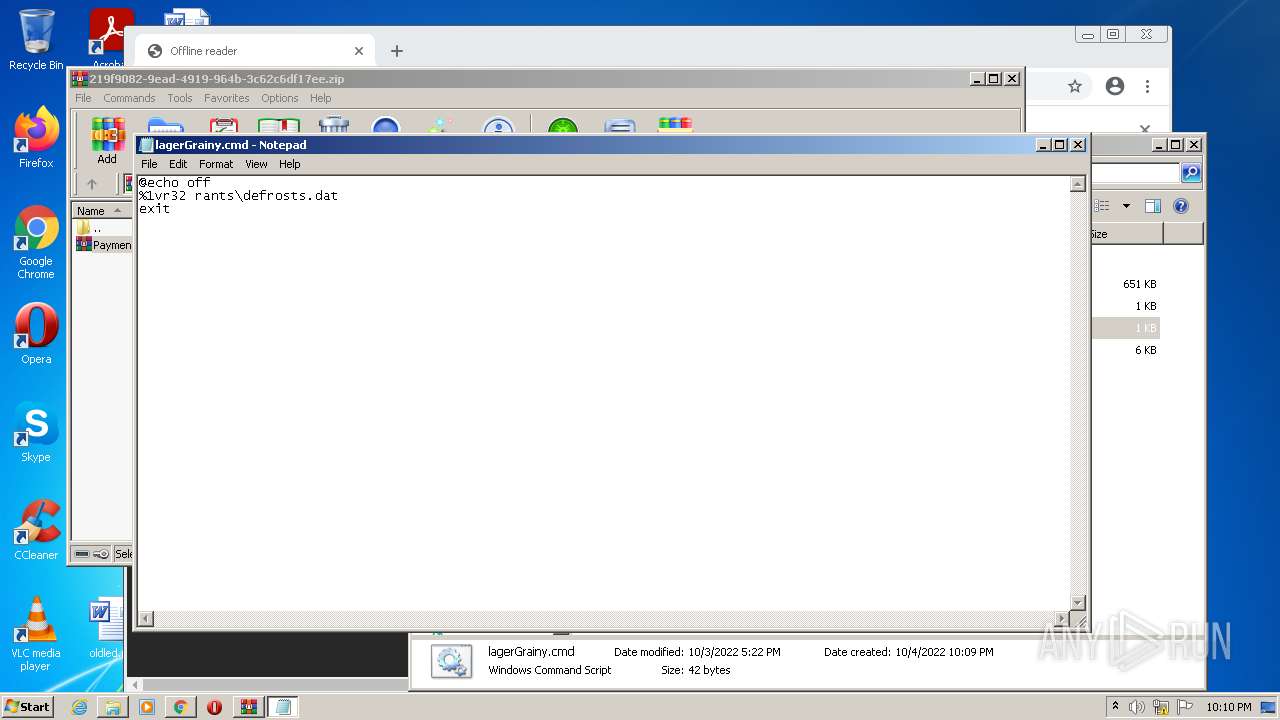
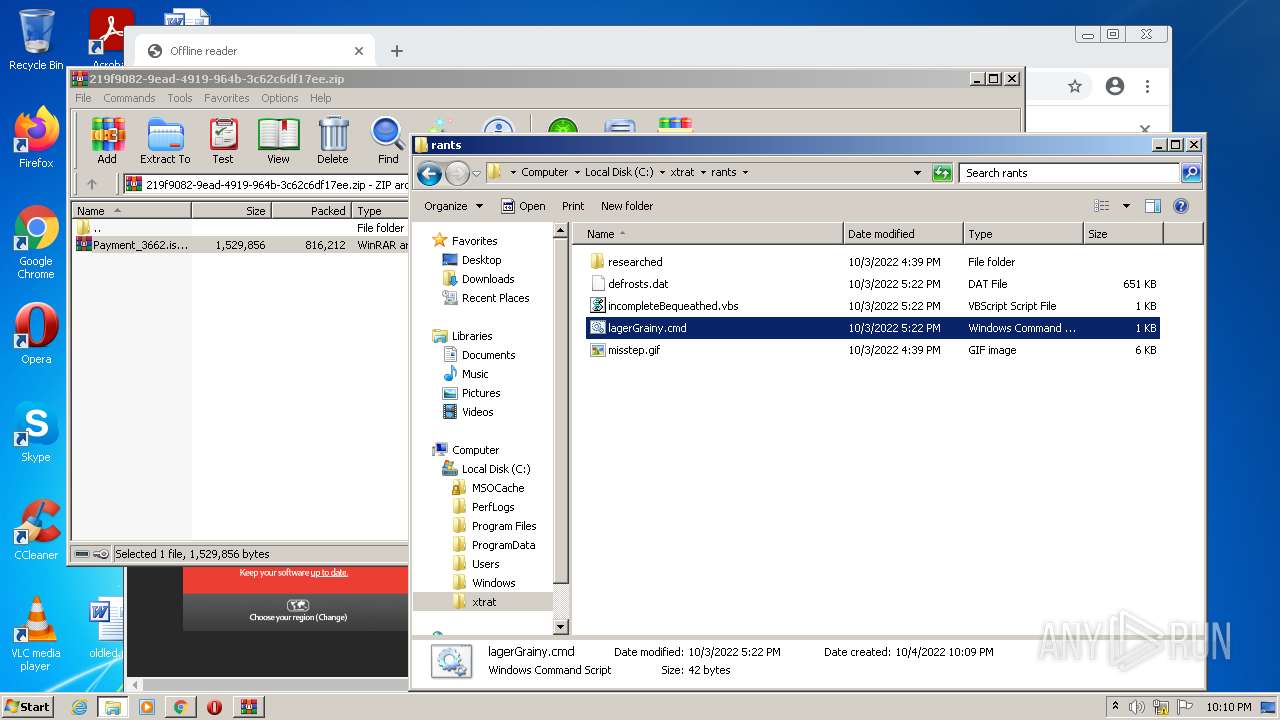
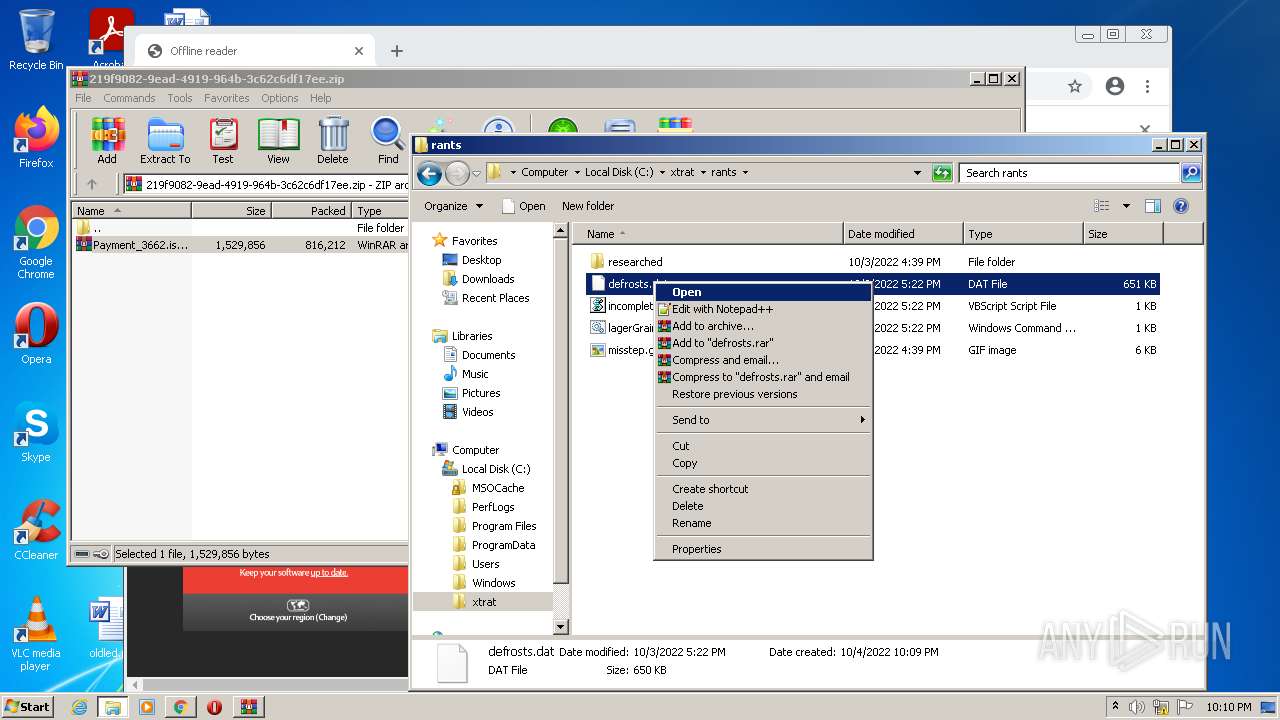
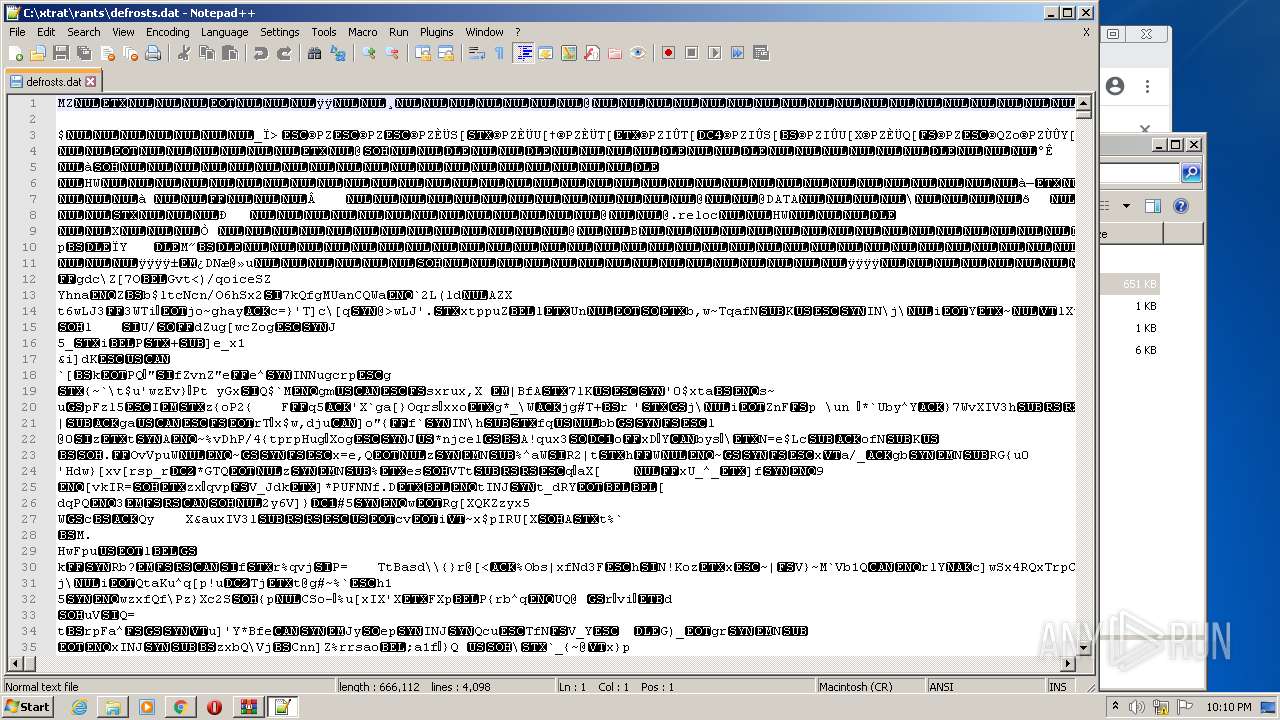
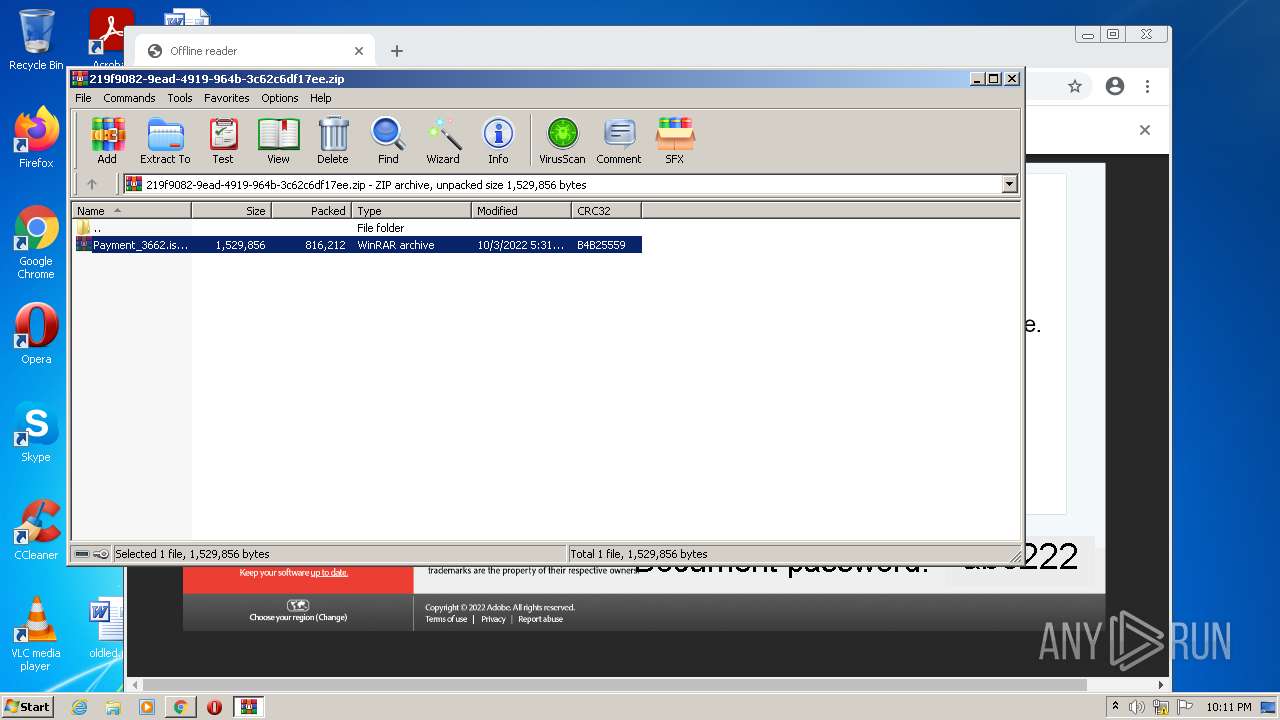
Drops executable file immediately after starts
- chrome.exe (PID: 2628)
- chrome.exe (PID: 2152)
- WinRAR.exe (PID: 2784)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2504)
- chrome.exe (PID: 2628)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3784)
- chrome.exe (PID: 3028)
- iexplore.exe (PID: 188)
Checks supported languages
- WinRAR.exe (PID: 2972)
- WinRAR.exe (PID: 3880)
- WinRAR.exe (PID: 2784)
- notepad++.exe (PID: 2464)
- notepad++.exe (PID: 3428)
Reads the computer name
- WinRAR.exe (PID: 2972)
- WinRAR.exe (PID: 3880)
- WinRAR.exe (PID: 2784)
Drops a file with a compile date too recent
- chrome.exe (PID: 2628)
- chrome.exe (PID: 2152)
- WinRAR.exe (PID: 2784)
Executable content was dropped or overwritten
- chrome.exe (PID: 2152)
- WinRAR.exe (PID: 2784)
INFO
Checks supported languages
- iexplore.exe (PID: 3484)
- chrome.exe (PID: 2504)
- iexplore.exe (PID: 460)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 3640)
- iexplore.exe (PID: 3784)
- chrome.exe (PID: 744)
- chrome.exe (PID: 2988)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 2956)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 692)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 3604)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 344)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 568)
- chrome.exe (PID: 352)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 1296)
- chrome.exe (PID: 3040)
- explorer.exe (PID: 3896)
- chrome.exe (PID: 3408)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 2152)
- NOTEPAD.EXE (PID: 3876)
- Notepad.exe (PID: 3460)
- NOTEPAD.EXE (PID: 2976)
- iexplore.exe (PID: 2164)
- iexplore.exe (PID: 188)
- Notepad.exe (PID: 2240)
- Notepad.exe (PID: 1520)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 2404)
- chrome.exe (PID: 3980)
Reads the computer name
- iexplore.exe (PID: 3484)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 3640)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 2628)
- iexplore.exe (PID: 3784)
- iexplore.exe (PID: 460)
- chrome.exe (PID: 3604)
- chrome.exe (PID: 344)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 352)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 1296)
- chrome.exe (PID: 3408)
- explorer.exe (PID: 3896)
- iexplore.exe (PID: 2164)
- iexplore.exe (PID: 188)
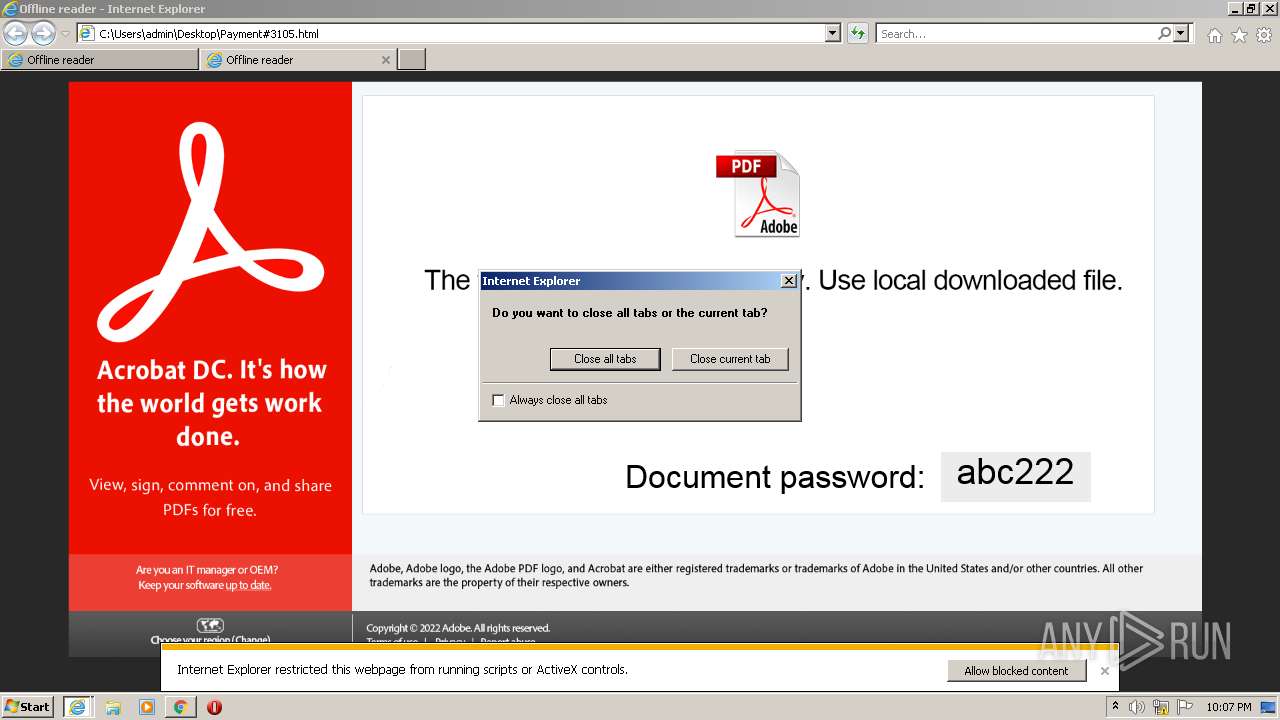
Application launched itself
- chrome.exe (PID: 2504)
- iexplore.exe (PID: 3484)
- chrome.exe (PID: 2628)
- iexplore.exe (PID: 3784)
- iexplore.exe (PID: 2164)
Changes internet zones settings
- iexplore.exe (PID: 3484)
- iexplore.exe (PID: 2164)
Reads the hosts file
- chrome.exe (PID: 2504)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 3604)
- chrome.exe (PID: 2628)
Reads internet explorer settings
- iexplore.exe (PID: 3784)
- iexplore.exe (PID: 188)
Manual execution by user
- chrome.exe (PID: 2504)
- chrome.exe (PID: 2628)
- explorer.exe (PID: 3896)
- WinRAR.exe (PID: 3880)
- WinRAR.exe (PID: 2784)
- NOTEPAD.EXE (PID: 3876)
- notepad++.exe (PID: 2464)
- NOTEPAD.EXE (PID: 2976)
- iexplore.exe (PID: 2164)
- Notepad.exe (PID: 3460)
- Notepad.exe (PID: 2240)
- notepad++.exe (PID: 3428)
- Notepad.exe (PID: 1520)
Checks Windows Trust Settings
- iexplore.exe (PID: 3484)
Reads settings of System Certificates
- iexplore.exe (PID: 3484)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 2628)
Reads the date of Windows installation
- iexplore.exe (PID: 3484)
- chrome.exe (PID: 1296)
- iexplore.exe (PID: 2164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
94
Monitored processes
50
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2164 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,1020712320570377403,5769129011347307512,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1132 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,1020712320570377403,5769129011347307512,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2448 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3484 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,1020712320570377403,5769129011347307512,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3544 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ed1d988,0x6ed1d998,0x6ed1d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,4309743080648133707,3401533754569581230,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,1020712320570377403,5769129011347307512,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
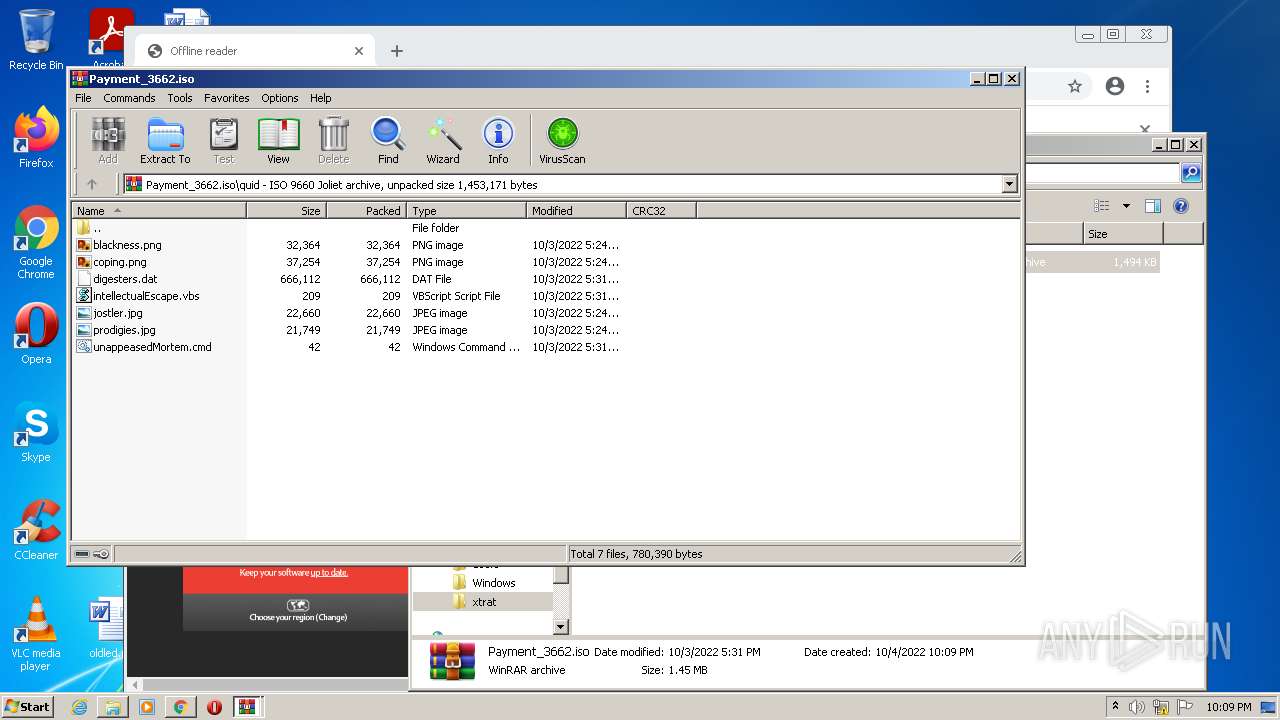
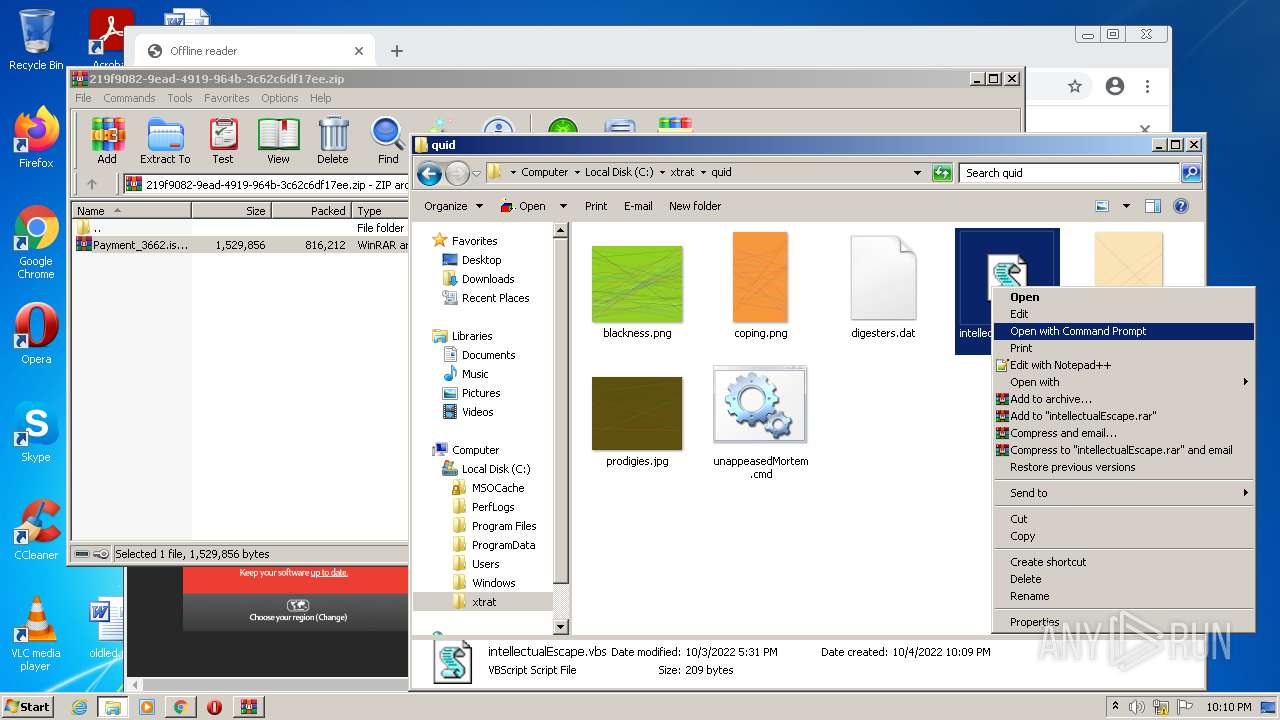
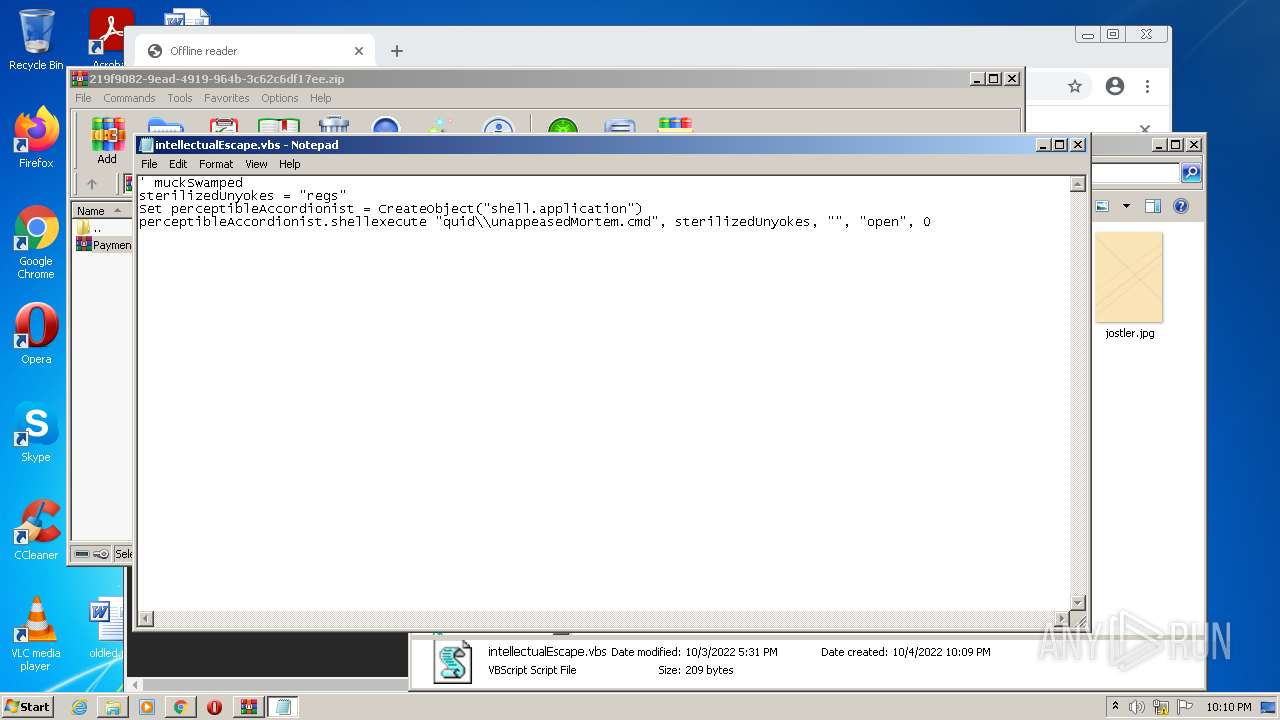
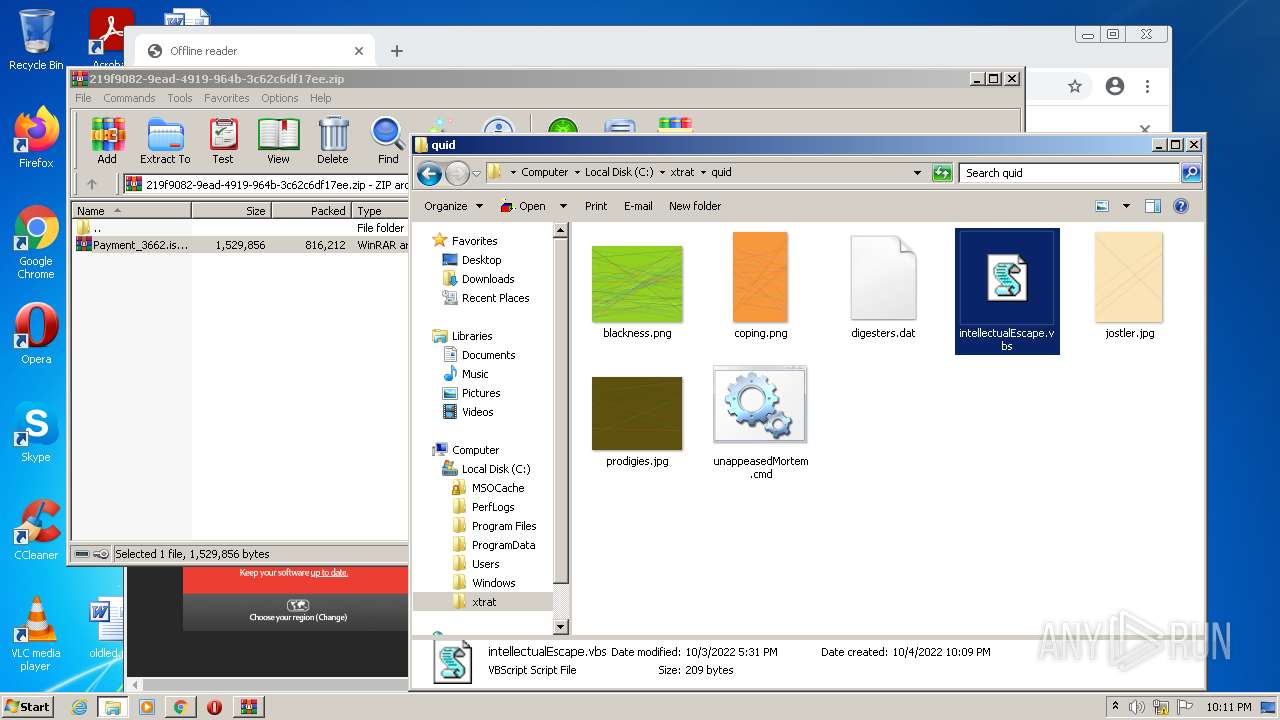
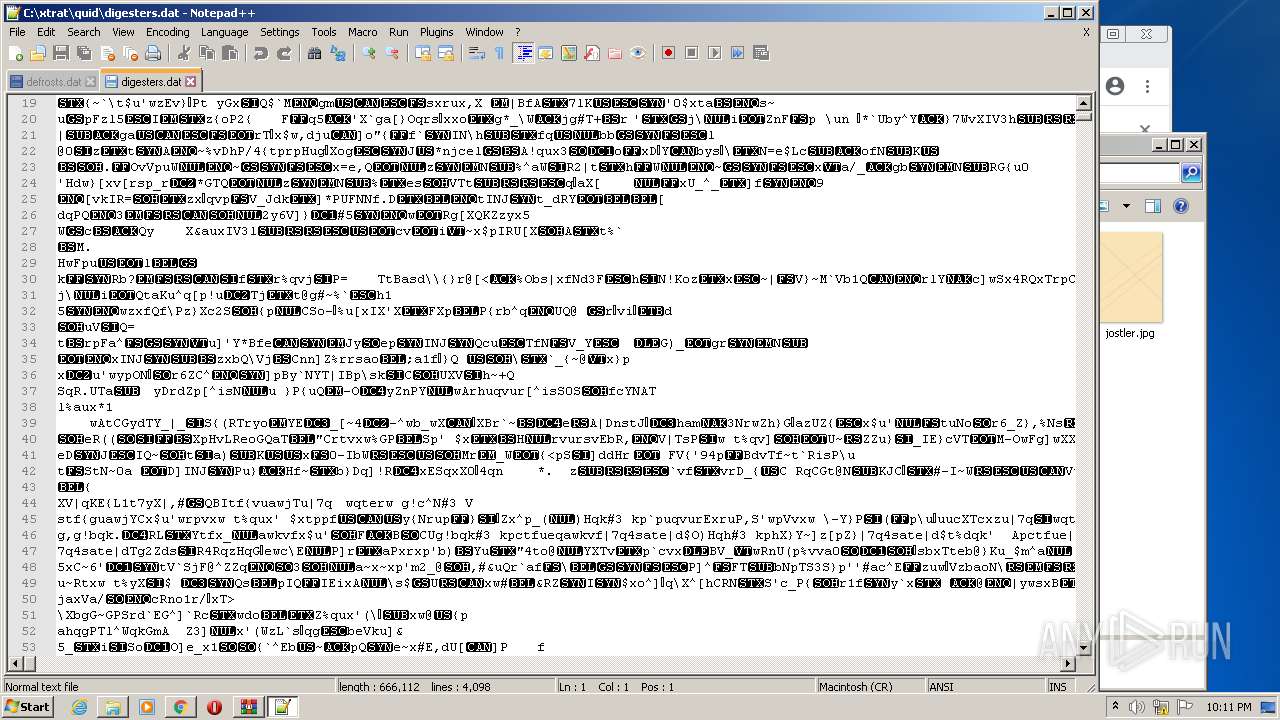
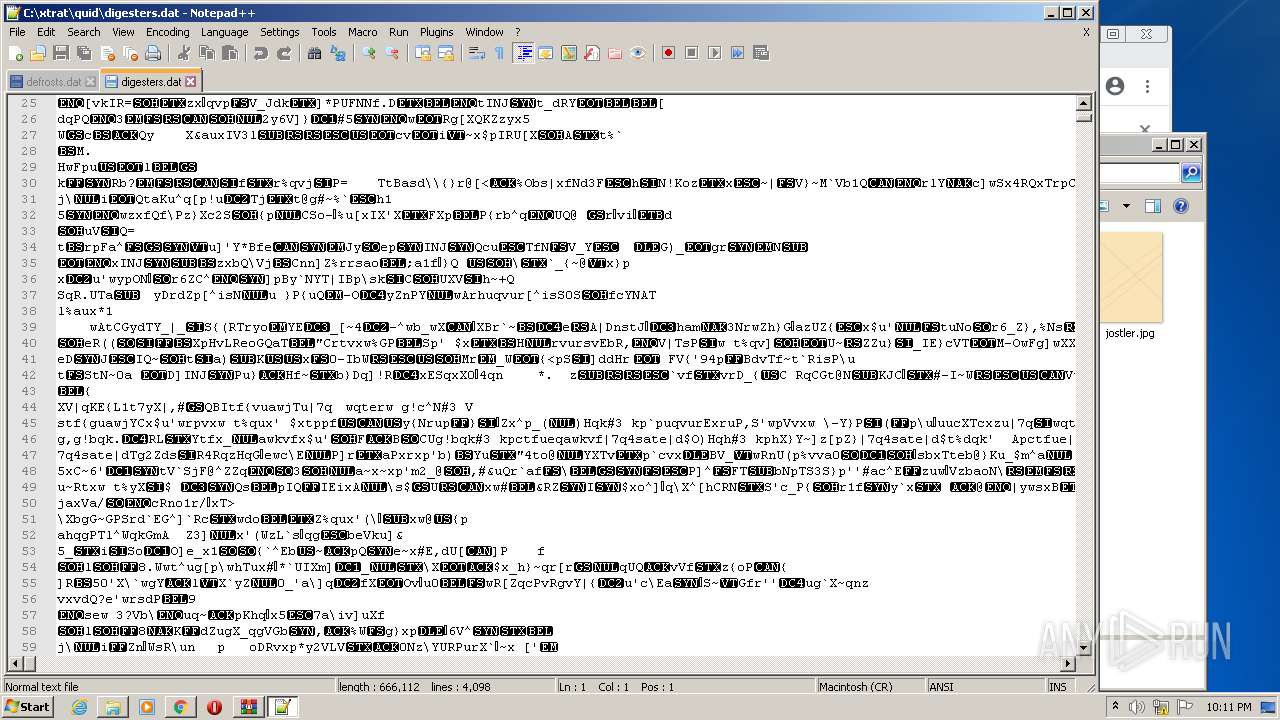
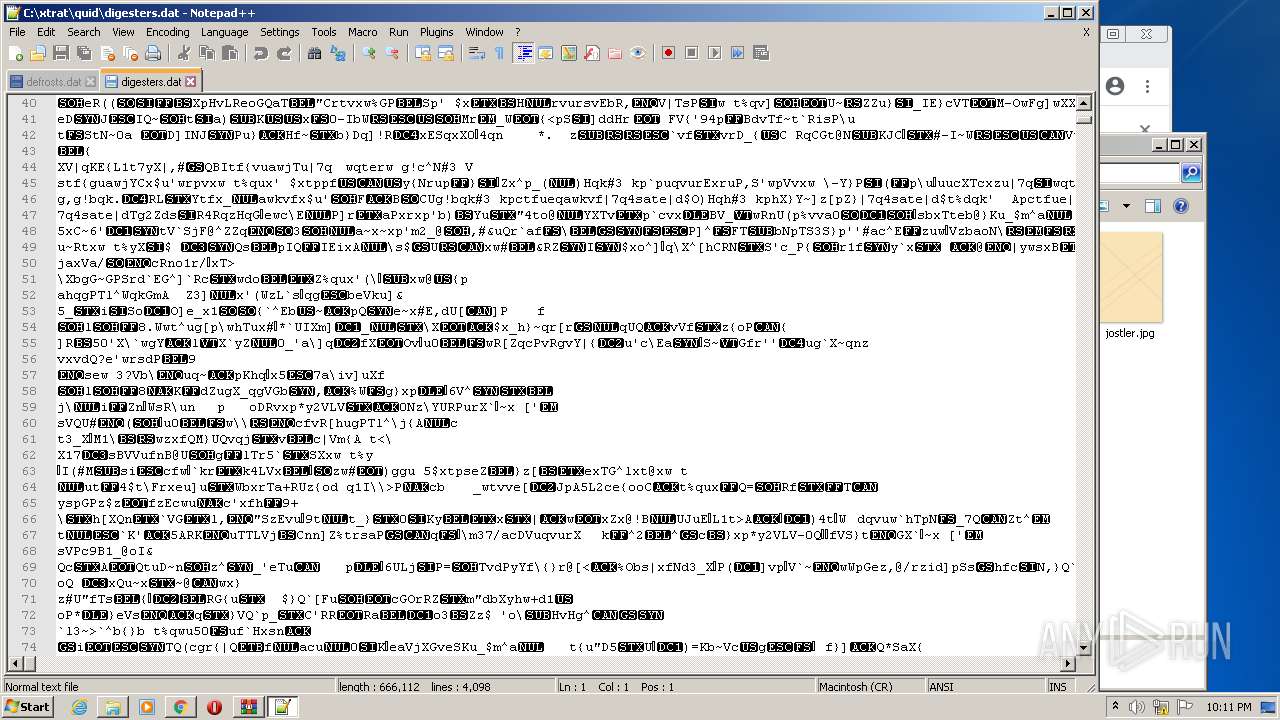
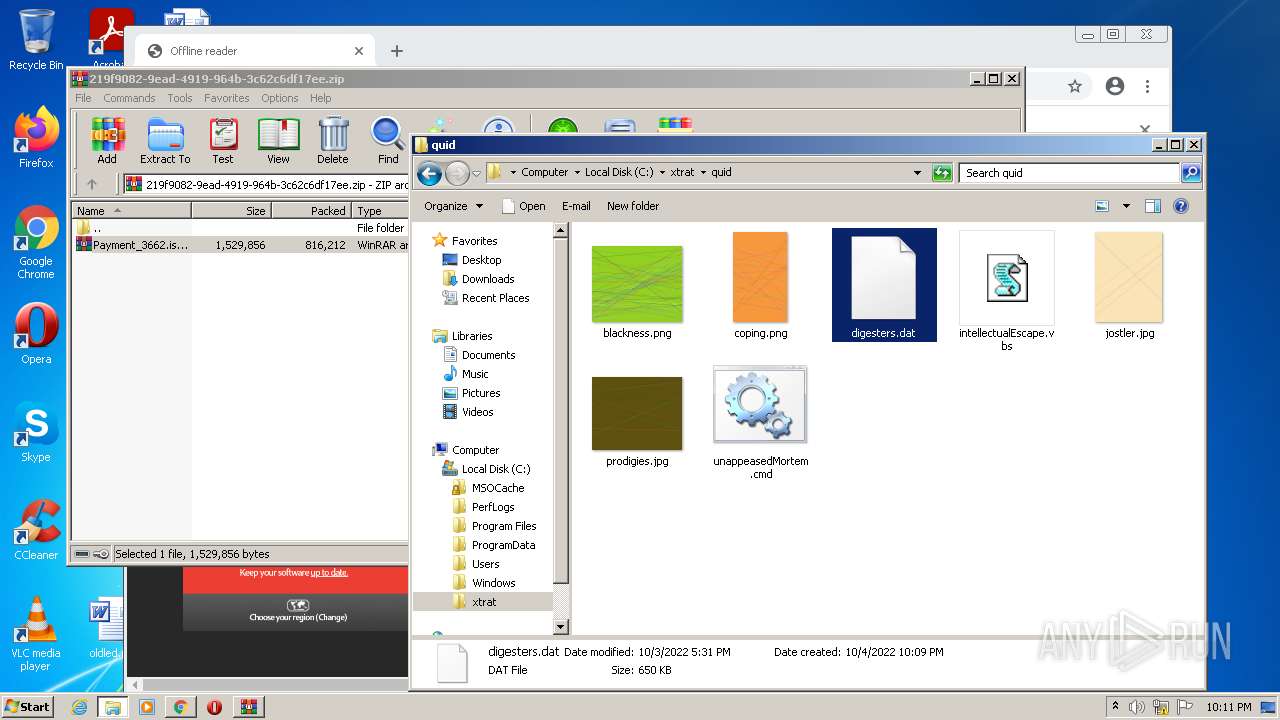
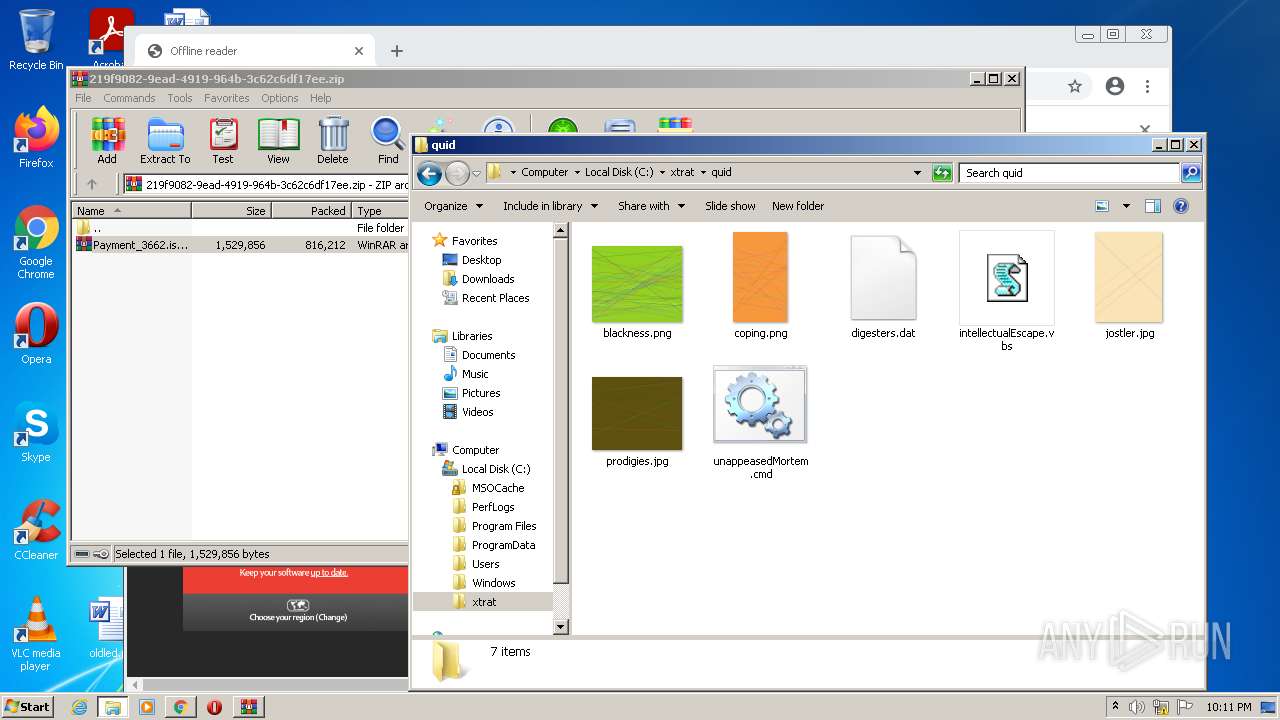
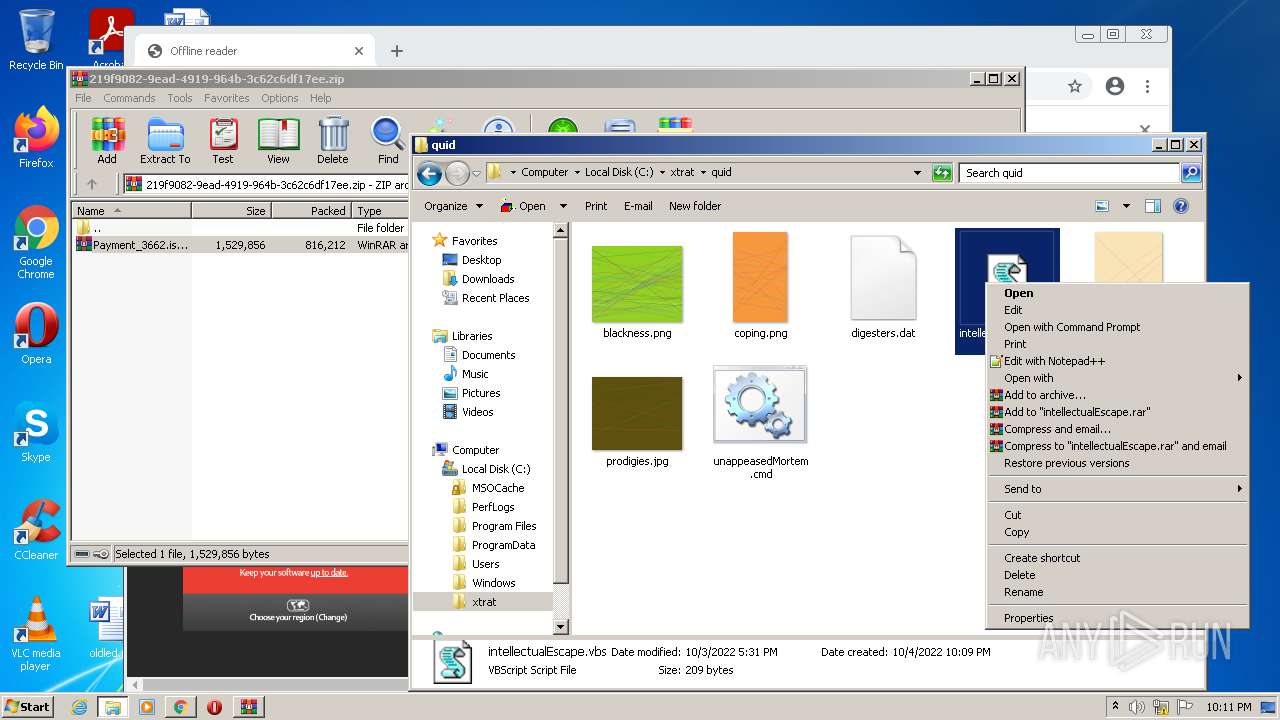
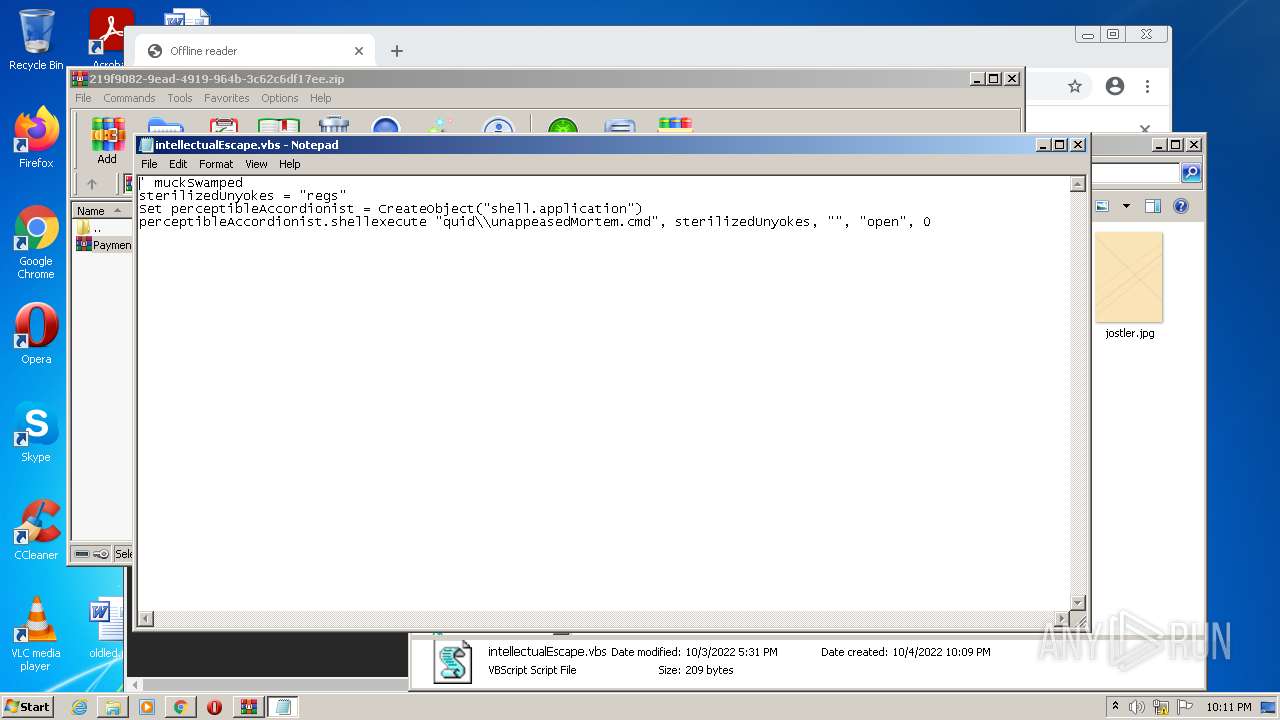
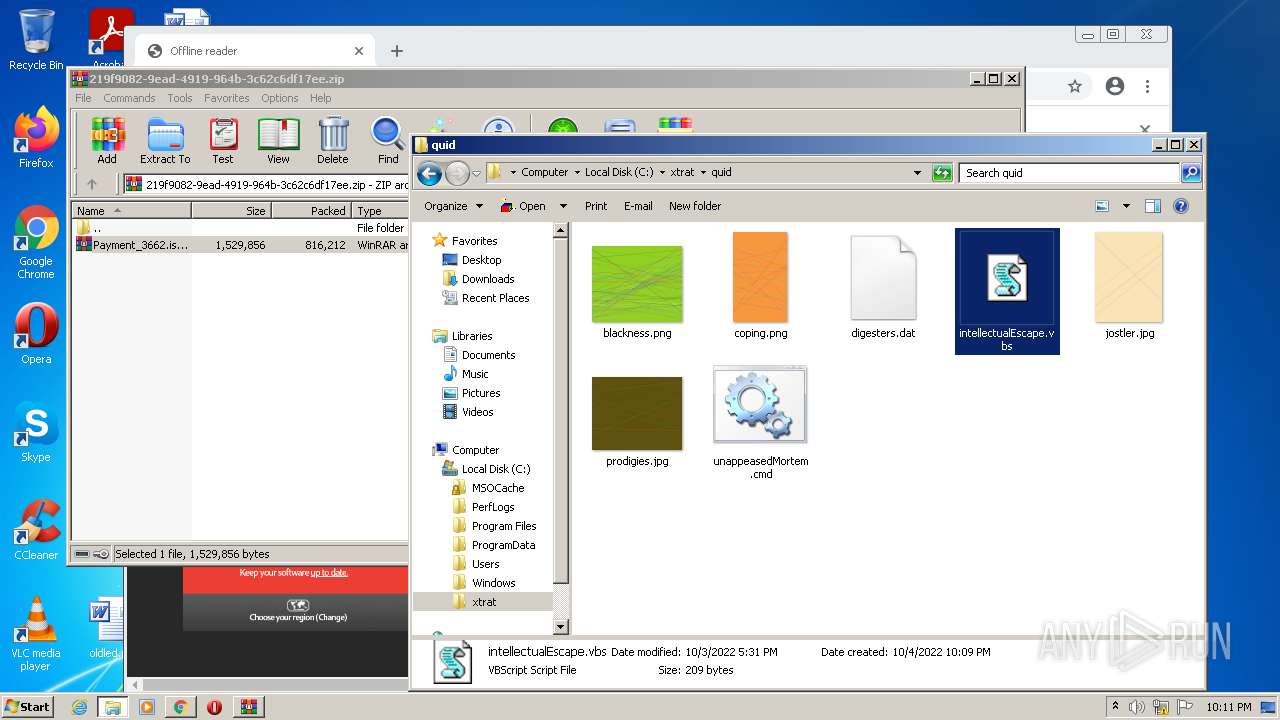
| 1520 | "C:\Windows\System32\Notepad.exe" C:\xtrat\quid\intellectualEscape.vbs | C:\Windows\System32\Notepad.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,1020712320570377403,5769129011347307512,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
27 924
Read events
27 462
Write events
453
Delete events
9
Modification events
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988341 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988341 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3484) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
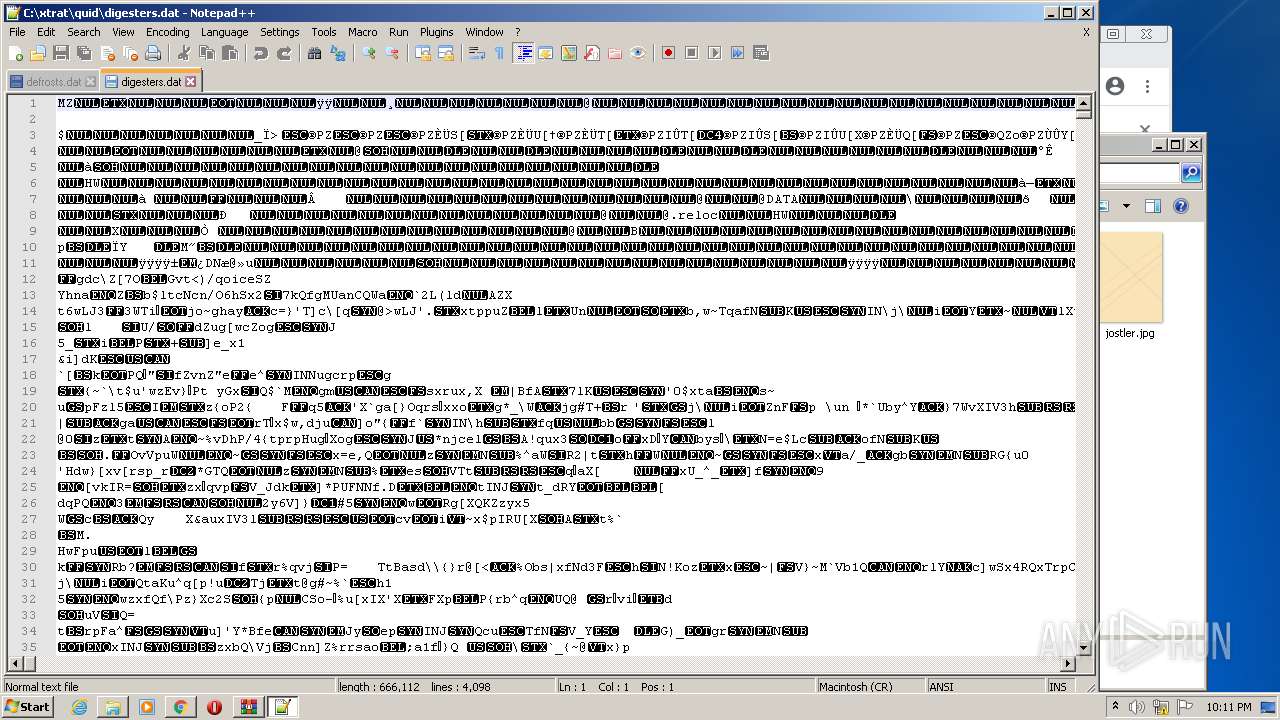
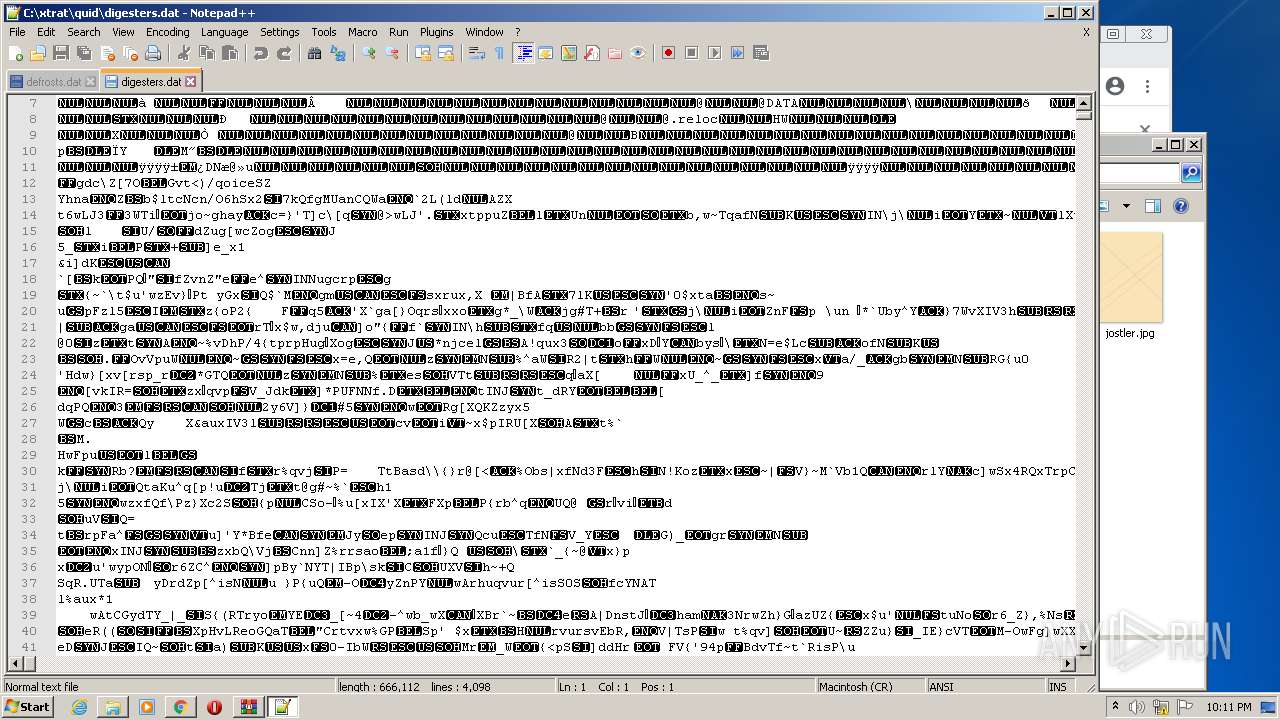
Executable files
3
Suspicious files
181
Text files
174
Unknown types
26
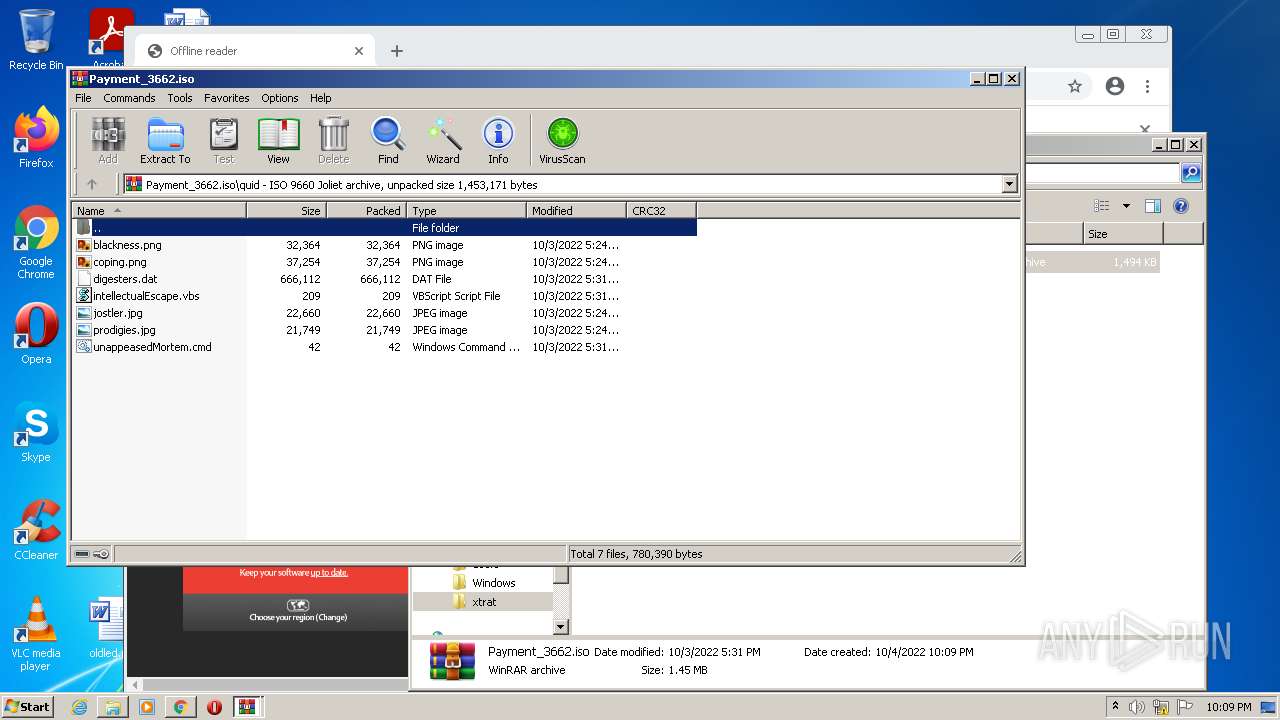
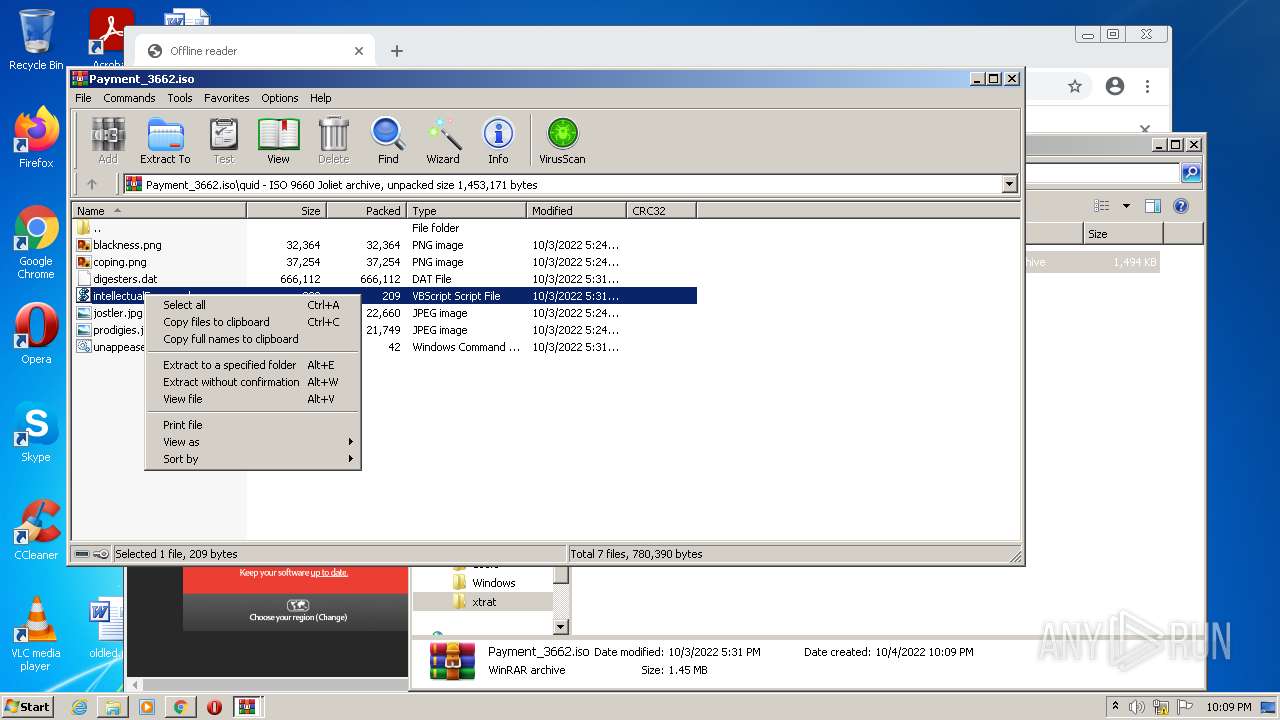
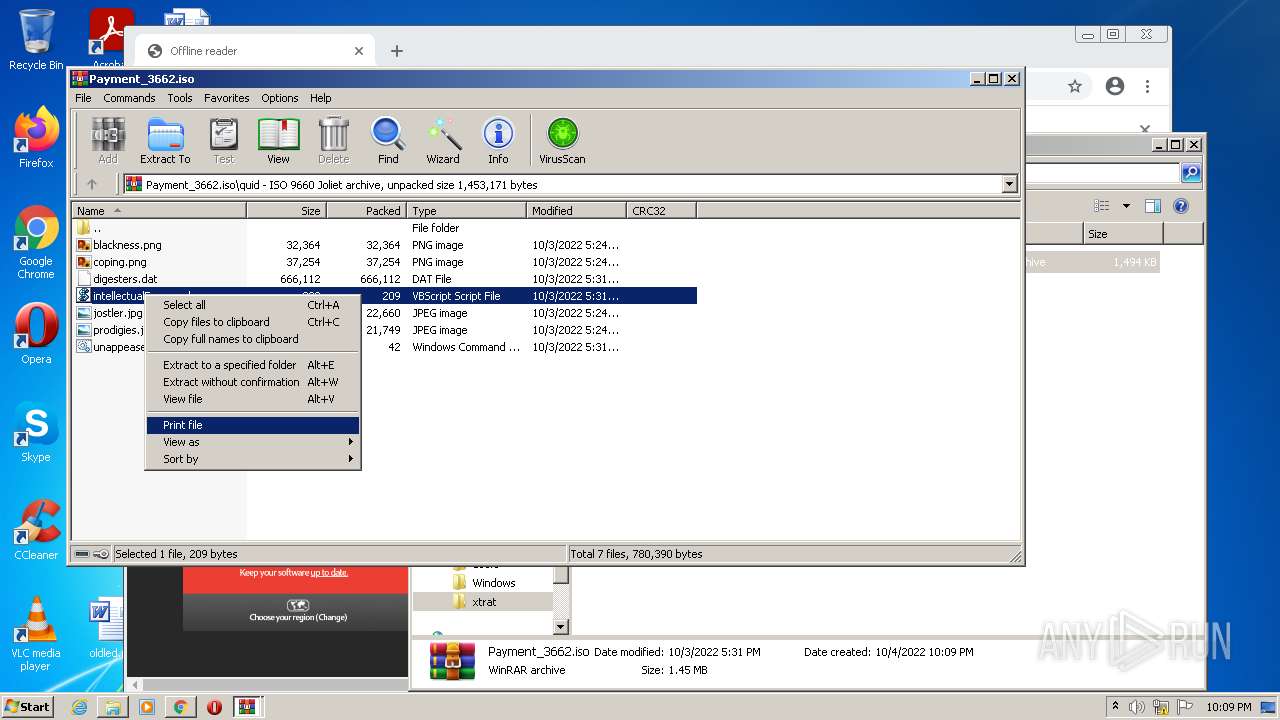
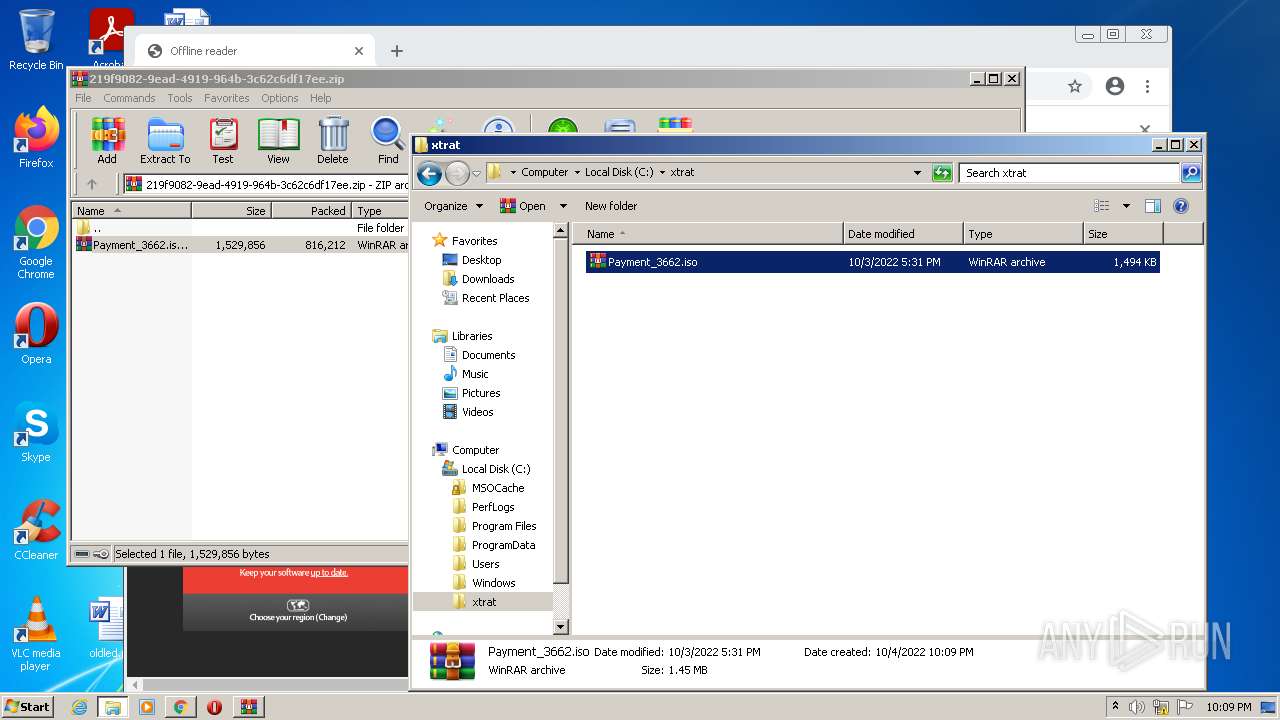
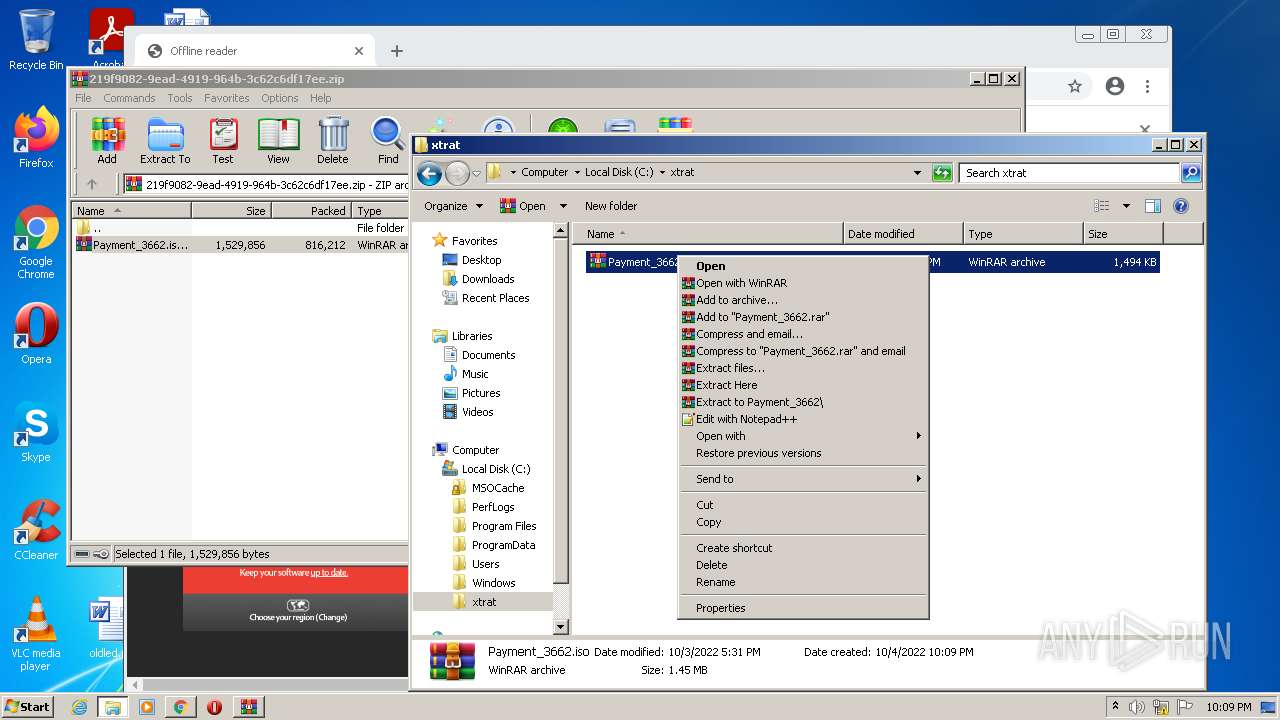
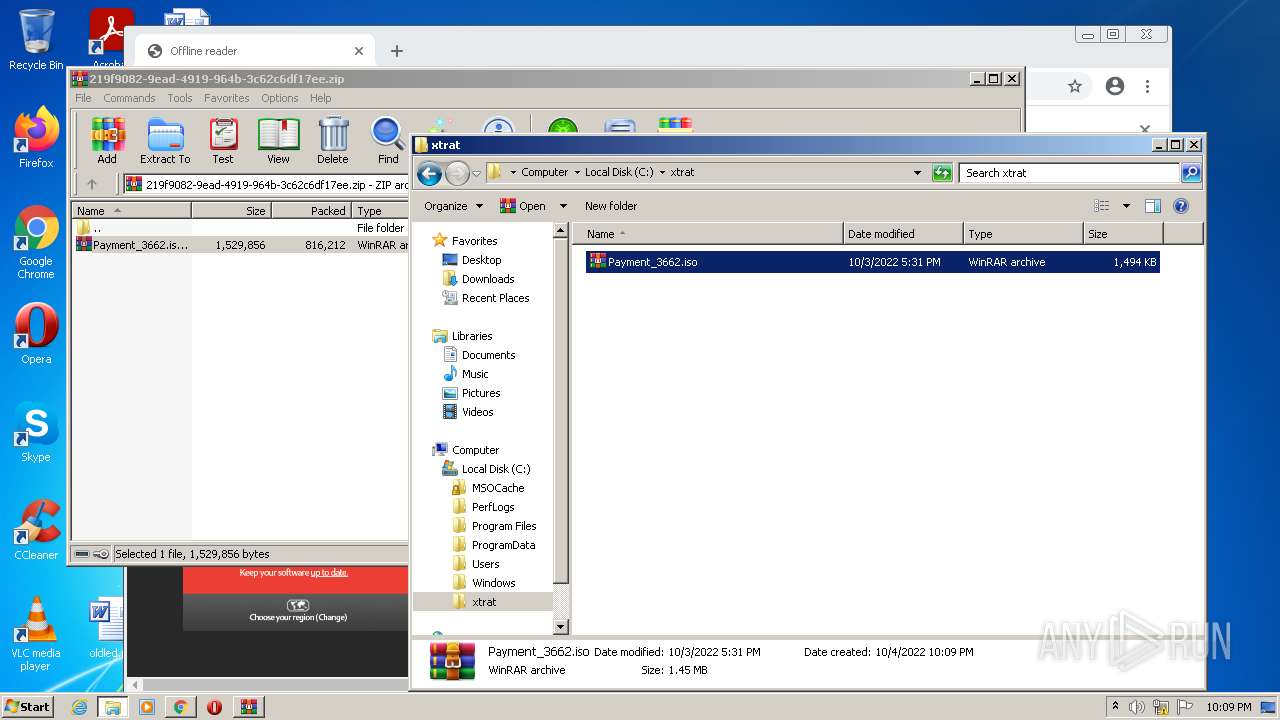
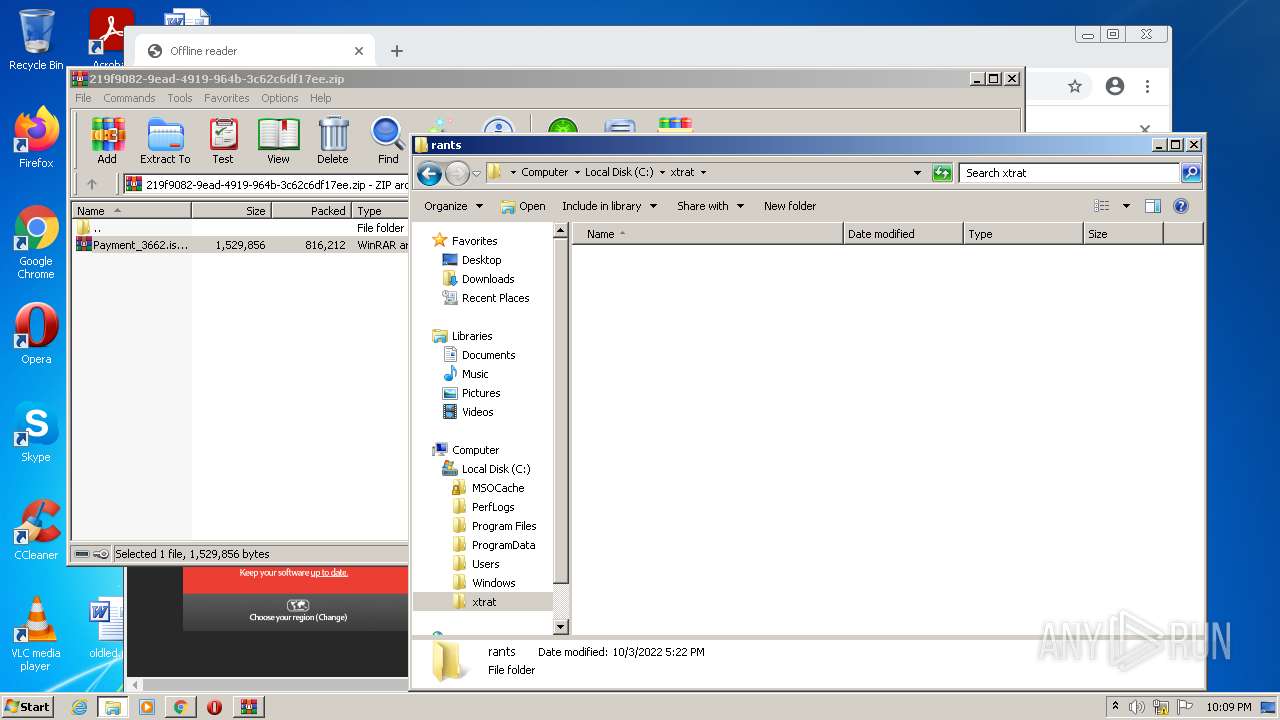
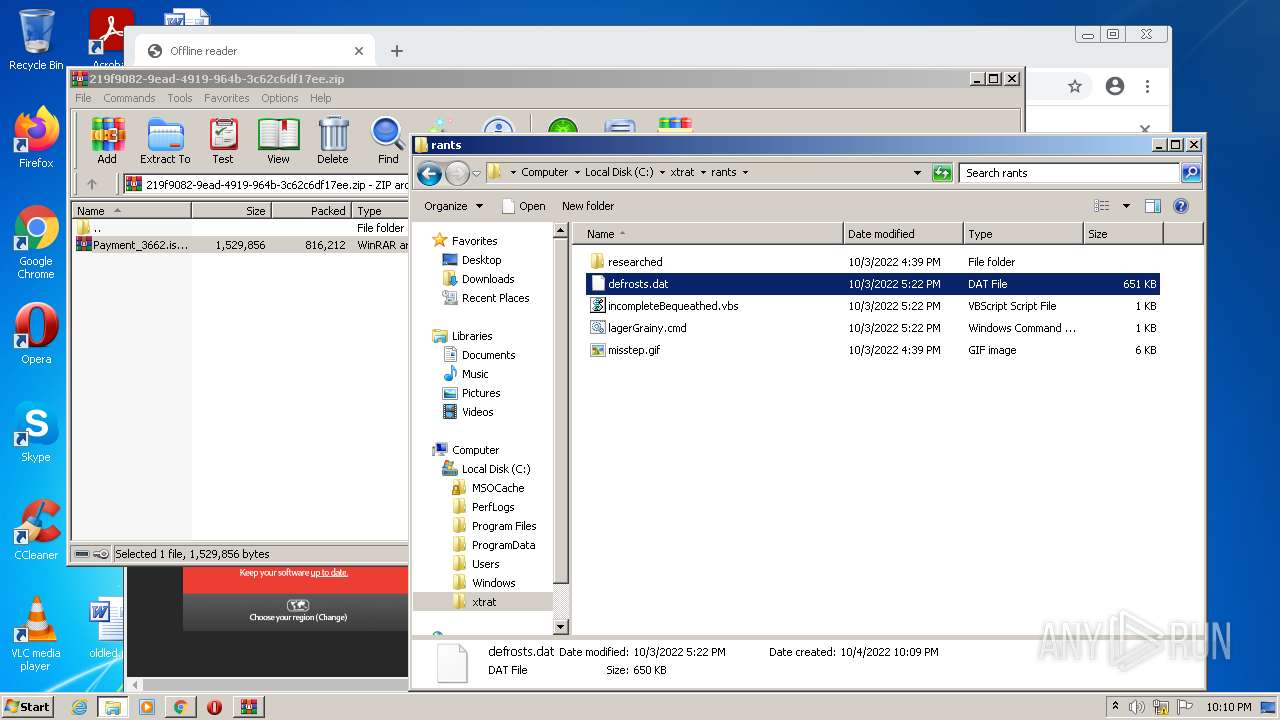
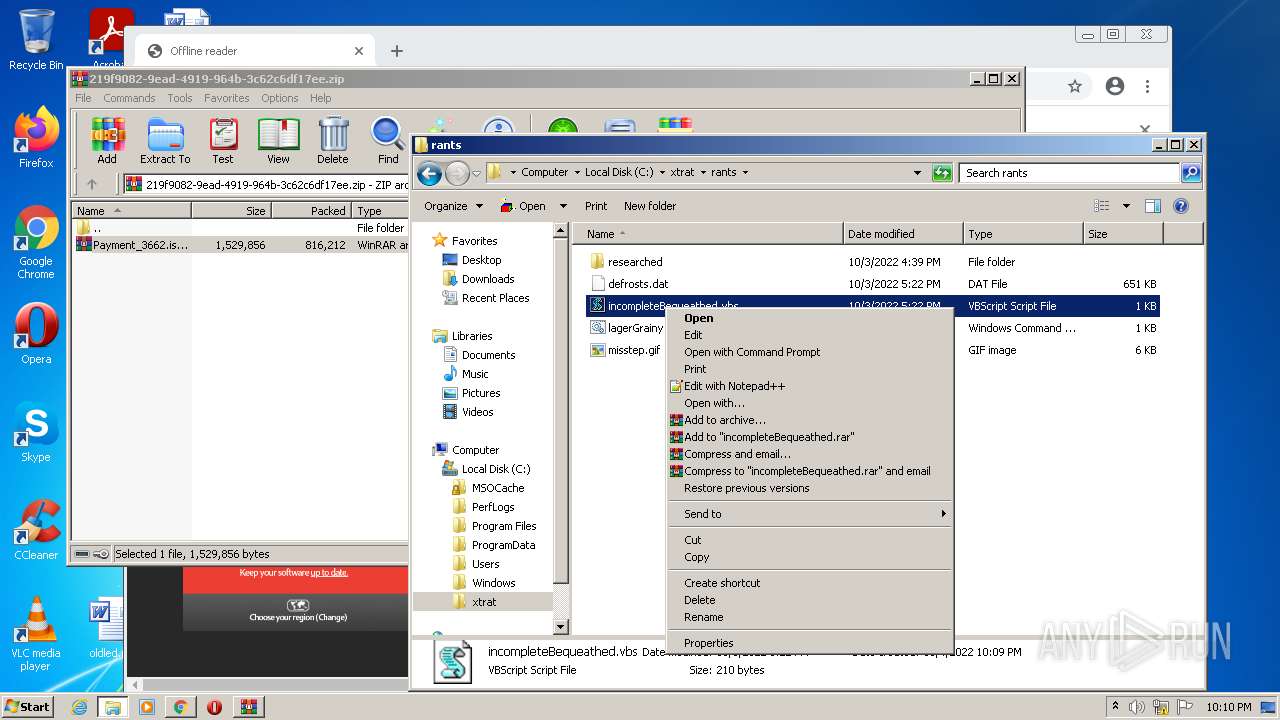
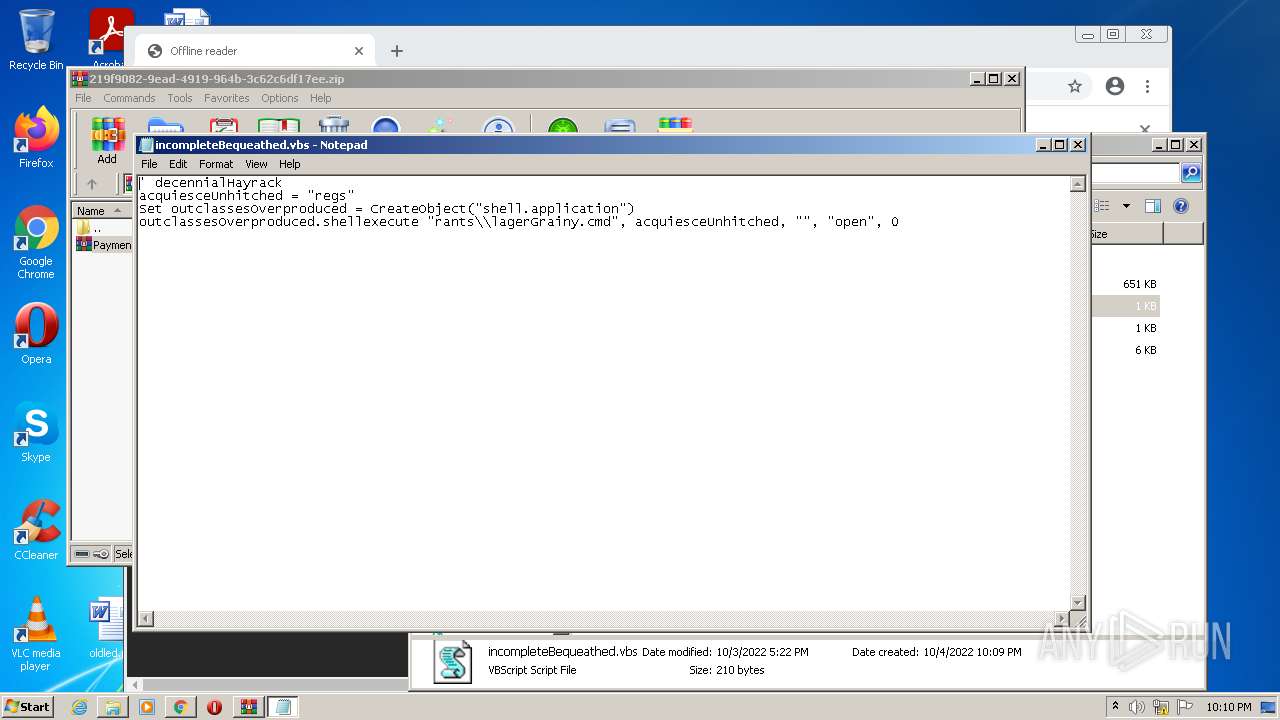
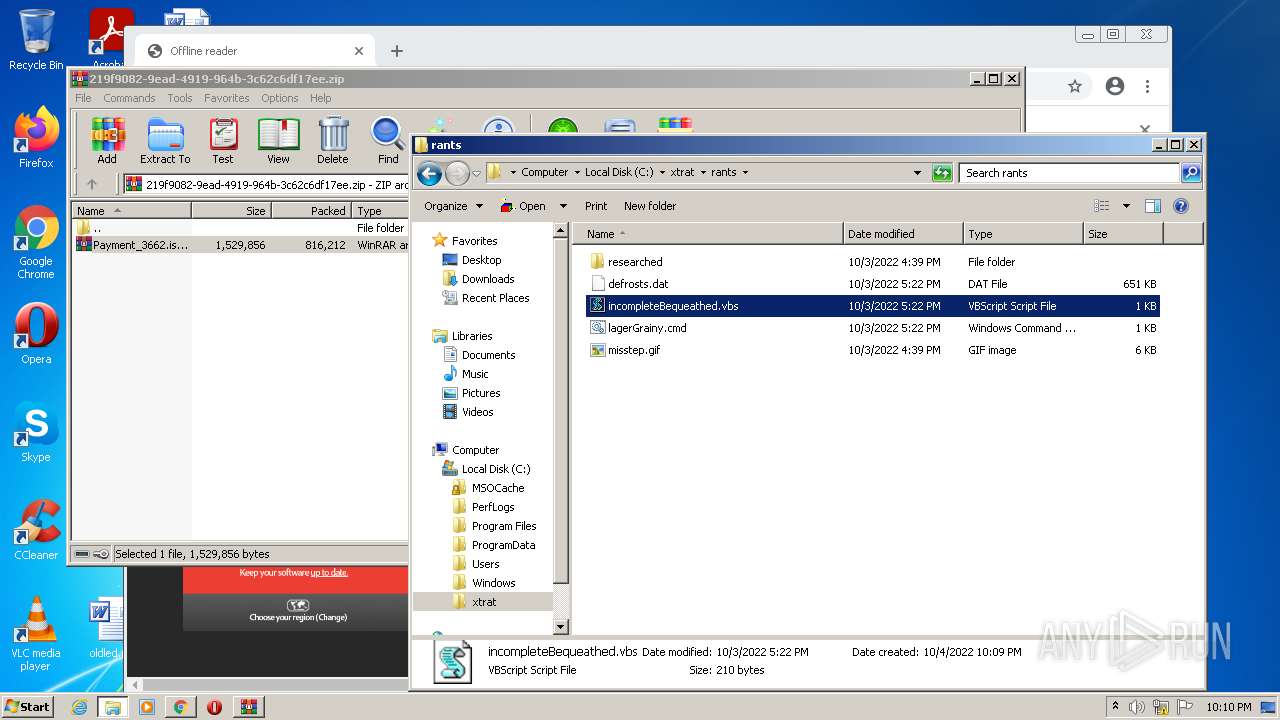
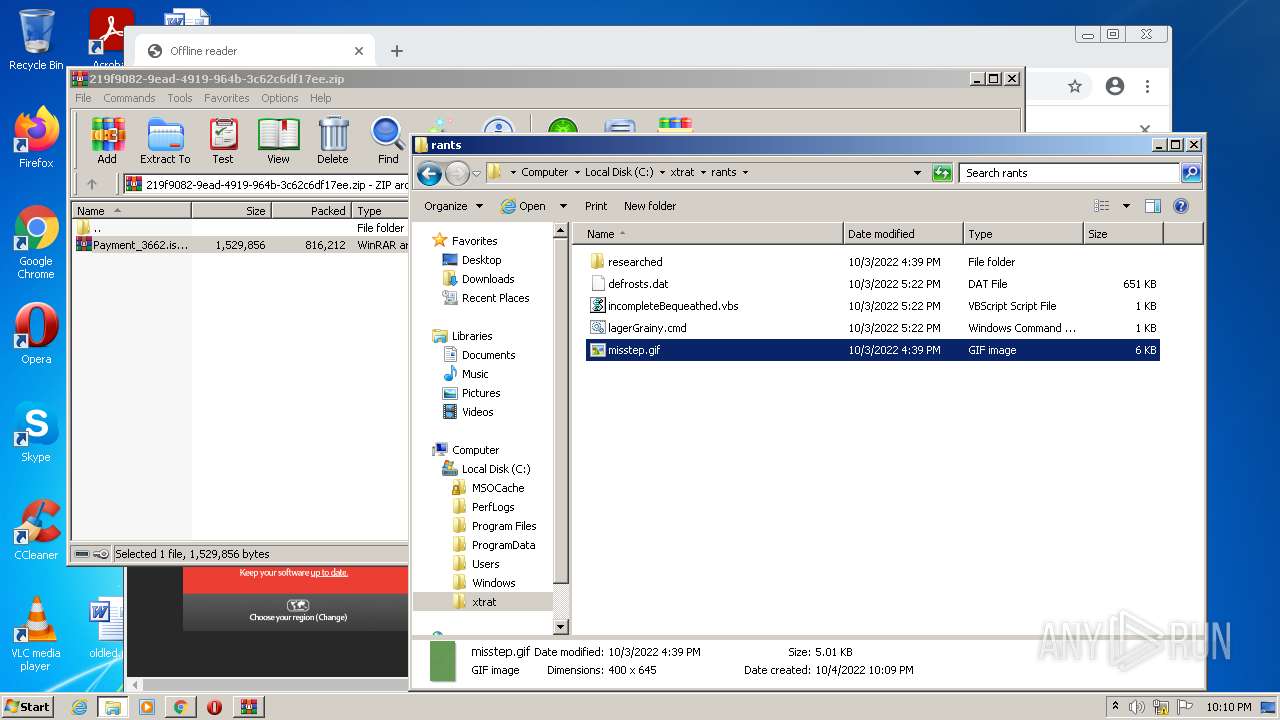
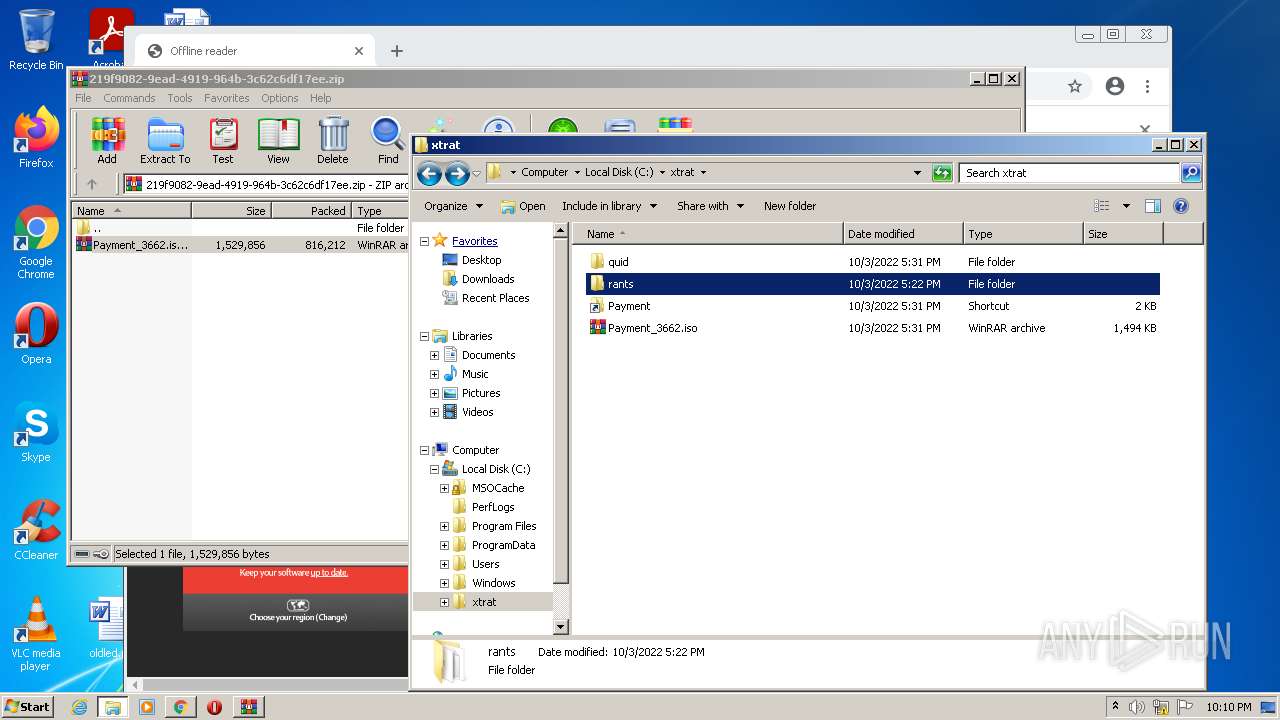
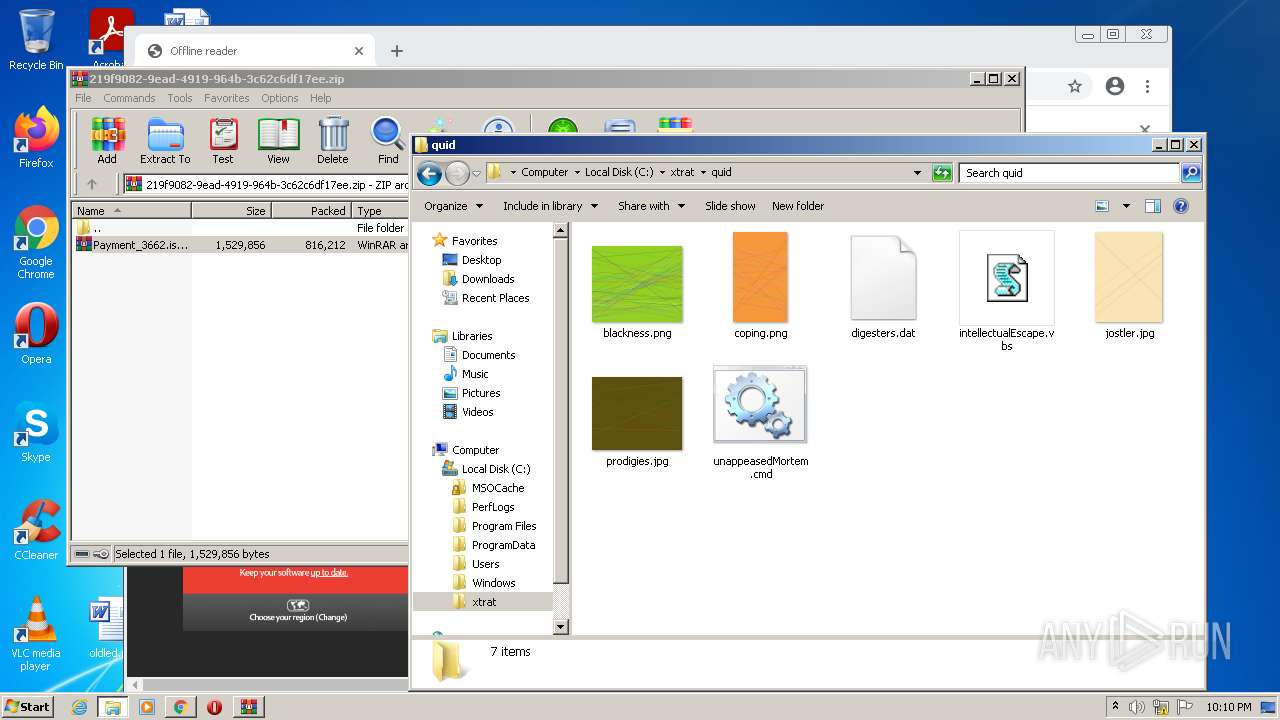
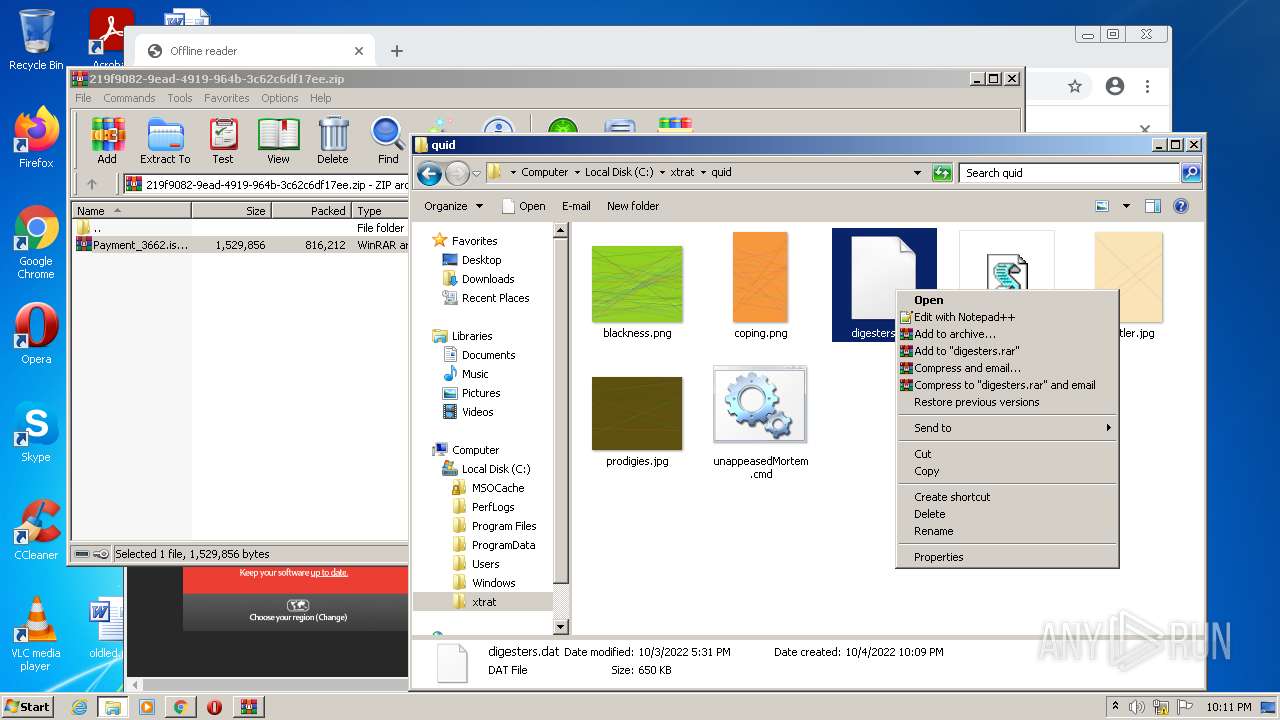
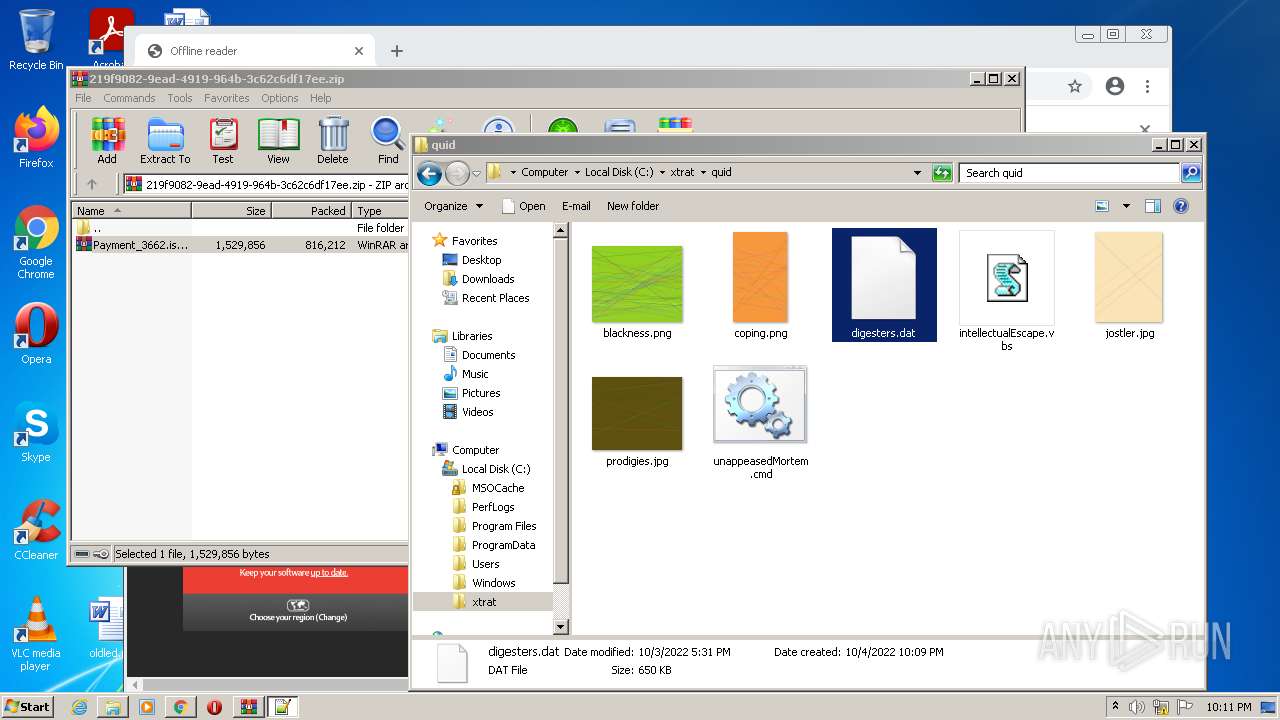
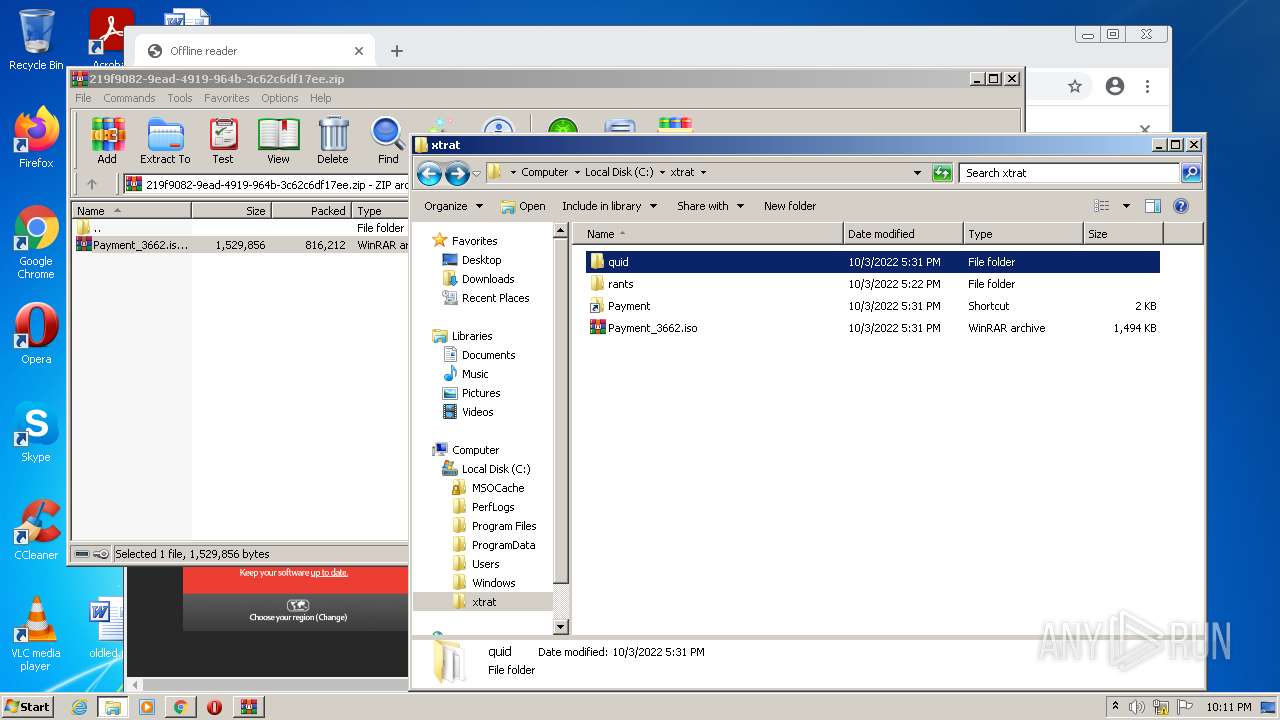
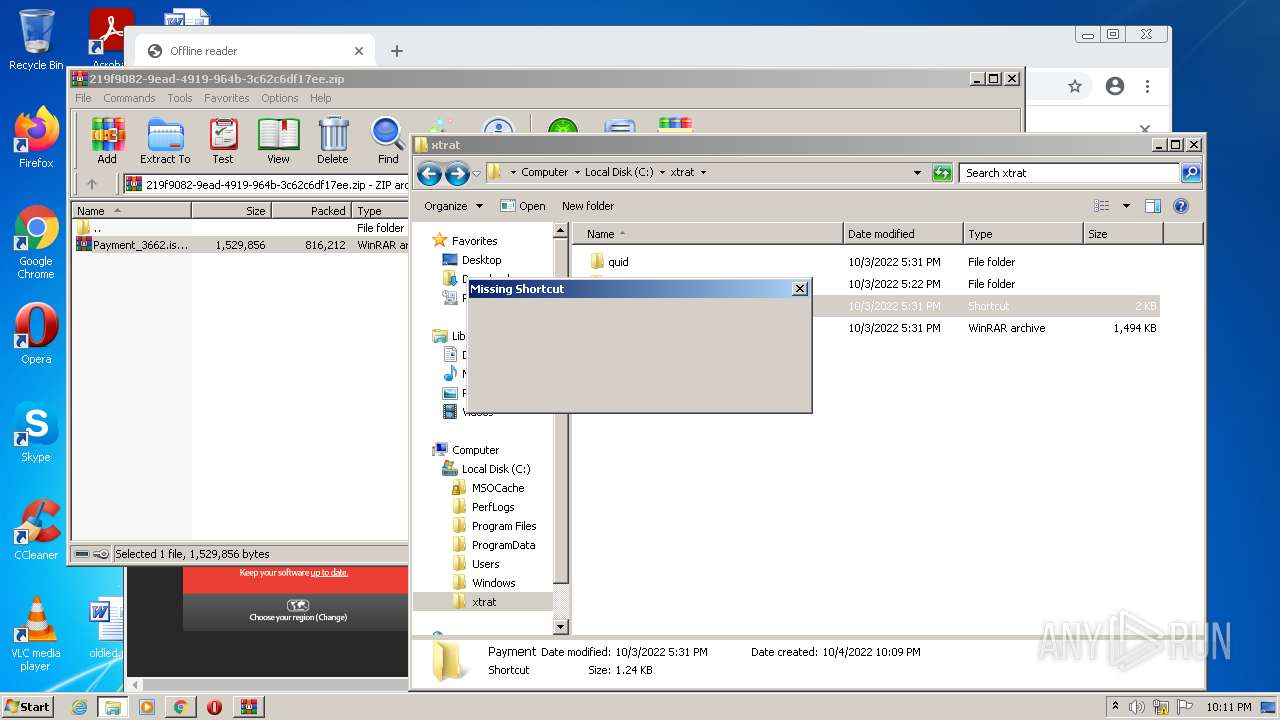
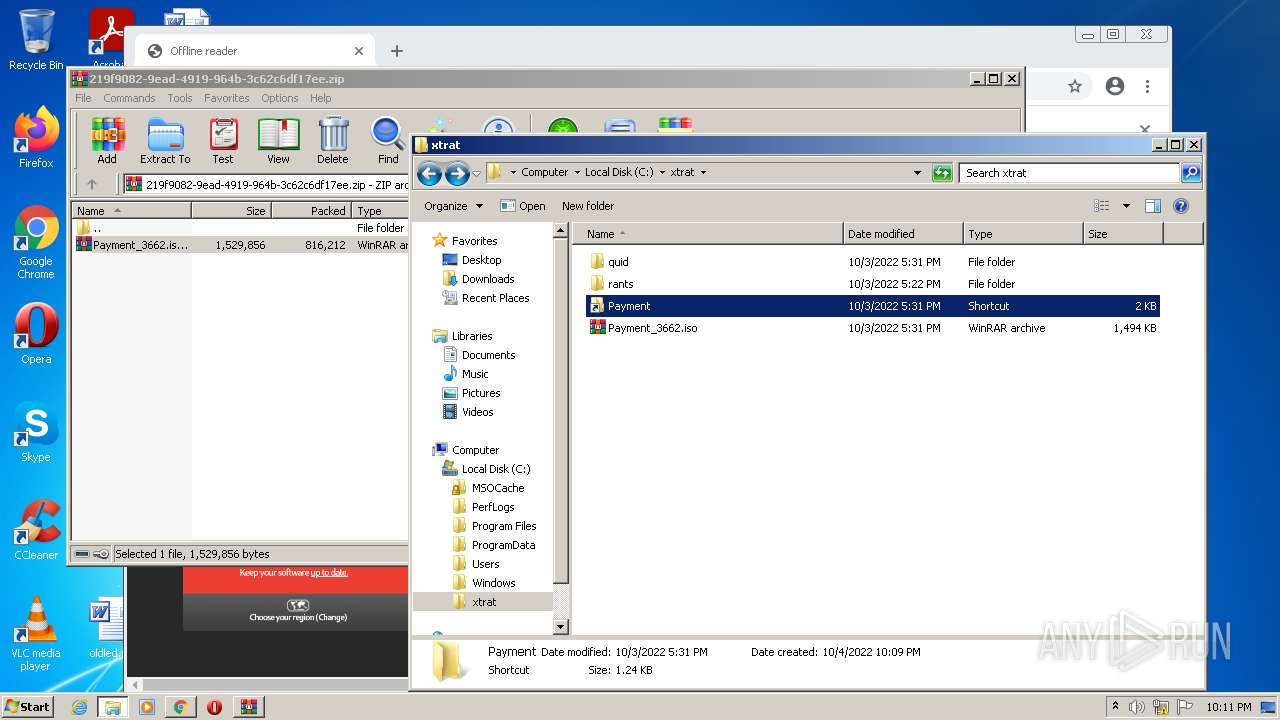
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-633CA081-9C8.pma | — | |
MD5:— | SHA256:— | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_0 | vxd | |
MD5:CF89D16BB9107C631DAABF0C0EE58EFB | SHA256:D6A5FE39CD672781B256E0E3102F7022635F1D4BB7CFCC90A80FFFE4D0F3877E | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4acd6967-bc8b-4677-948f-22e6b91870fc.tmp | text | |
MD5:— | SHA256:— | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1173e5.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 3136 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF11728d.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
35
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
808 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
808 | svchost.exe | HEAD | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac7nnsmhrfnfuraubqhiisbay5za_20220906.473124663/obedbbhbpmojnkanicioggnmelmoomoc_20220906.473124663_all_ENUS_mqjsfts67mmjlbap2zluobepvu.crx3 | US | — | — | whitelisted |
808 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.70 Kb | whitelisted |
808 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 20.9 Kb | whitelisted |
808 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 43.4 Kb | whitelisted |
3484 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
808 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 45.9 Kb | whitelisted |
808 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.70 Kb | whitelisted |
808 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 1.41 Mb | whitelisted |
808 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 45.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3484 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3564 | chrome.exe | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
3564 | chrome.exe | 142.250.180.238:443 | clients2.google.com | GOOGLE | US | whitelisted |
3484 | iexplore.exe | 8.248.137.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3604 | chrome.exe | 216.58.212.173:443 | accounts.google.com | GOOGLE | US | whitelisted |
3564 | chrome.exe | 216.58.212.173:443 | accounts.google.com | GOOGLE | US | whitelisted |
3564 | chrome.exe | 172.217.17.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3484 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3484 | iexplore.exe | 13.107.21.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3564 | chrome.exe | 142.251.39.33:443 | clients2.googleusercontent.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|