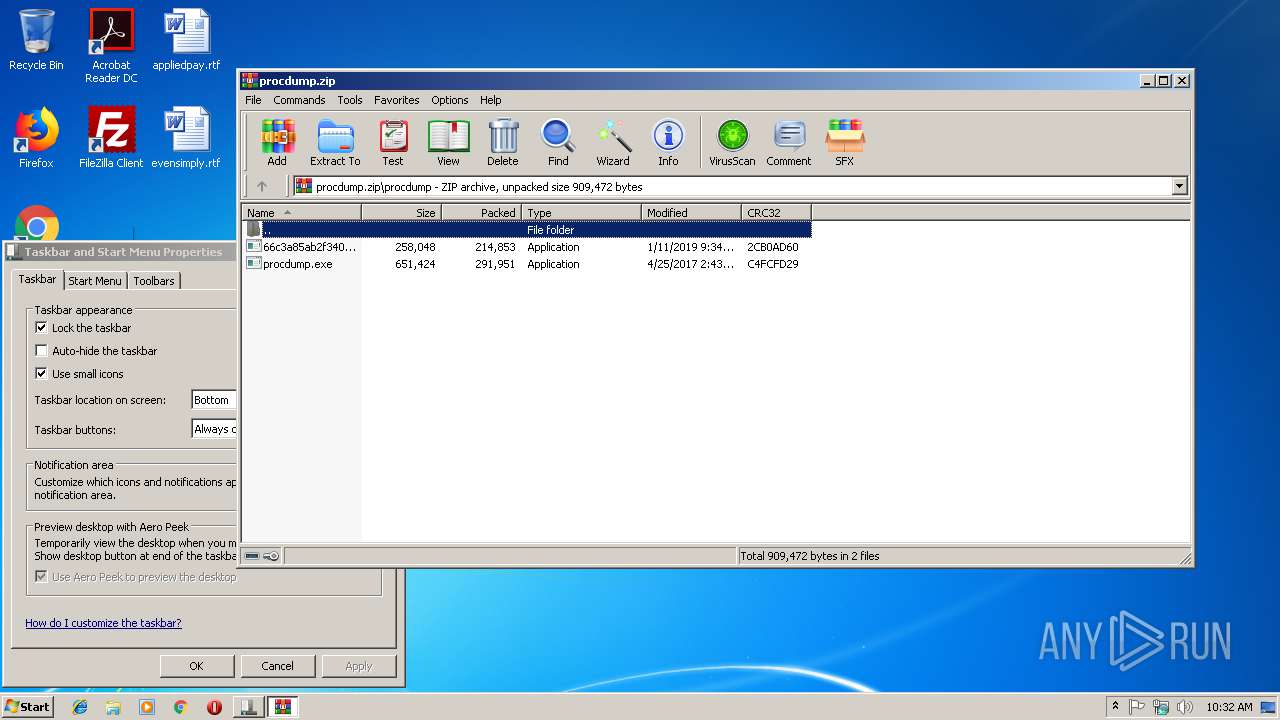
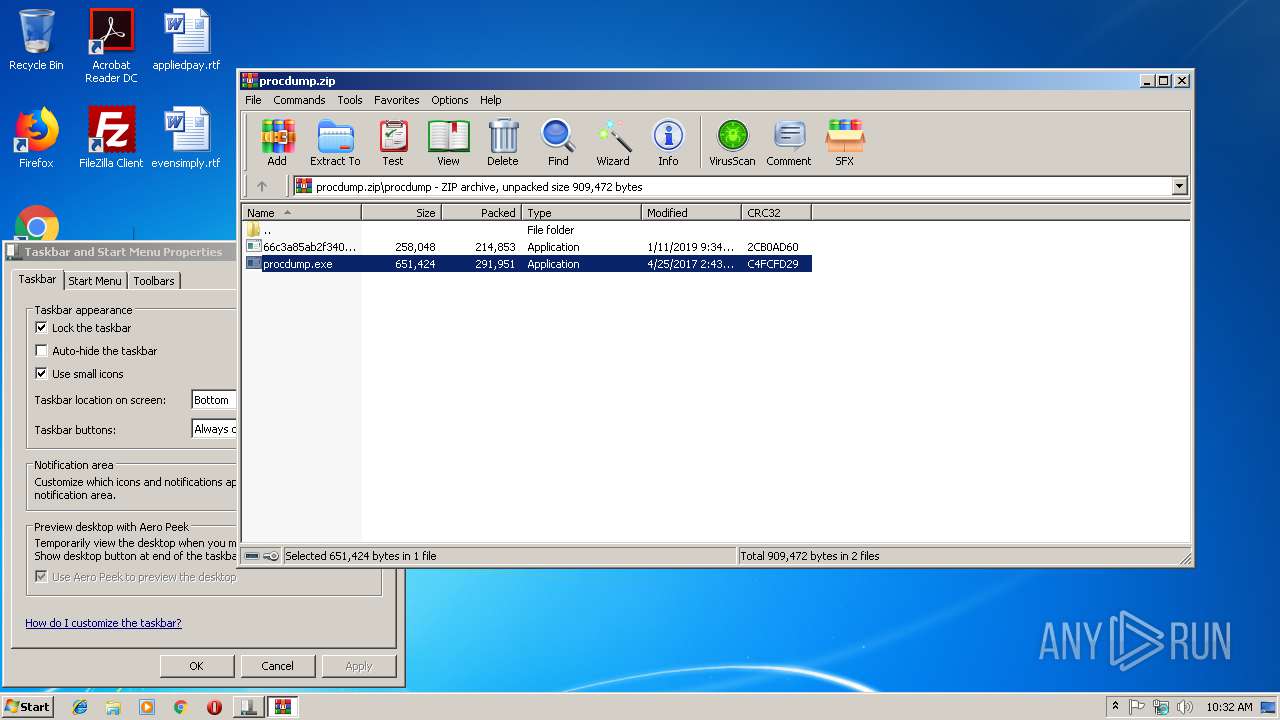
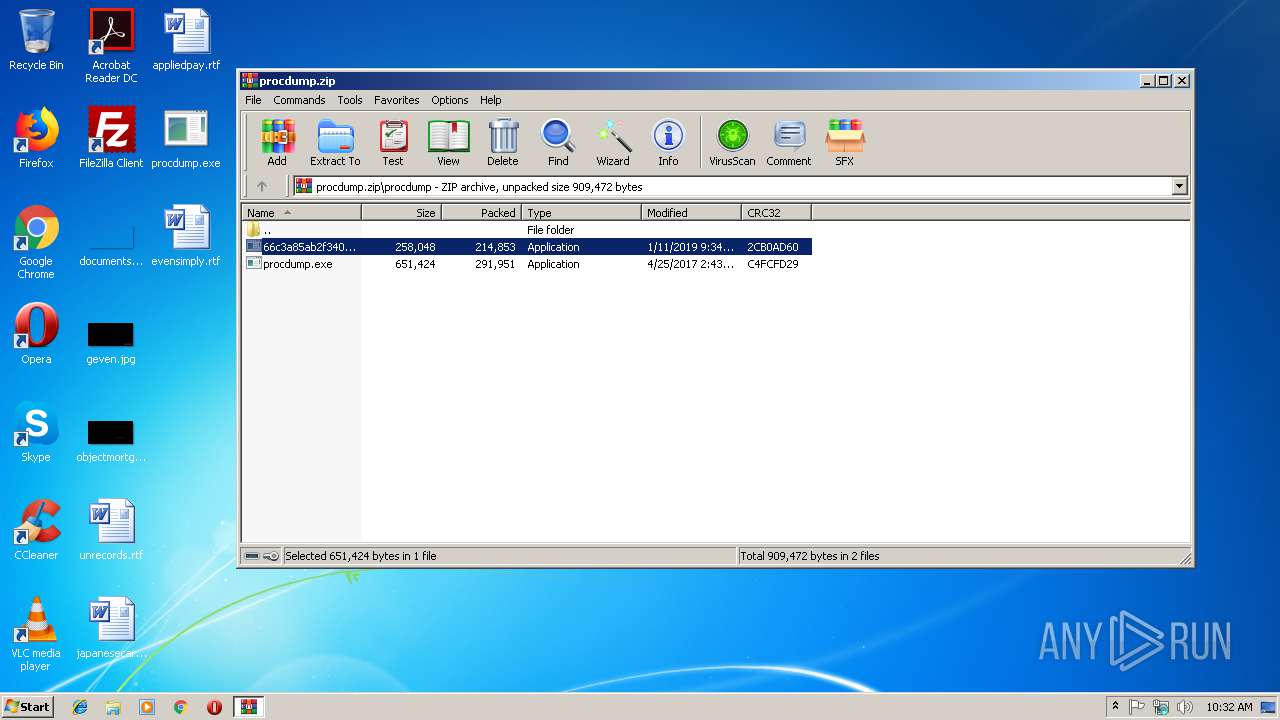
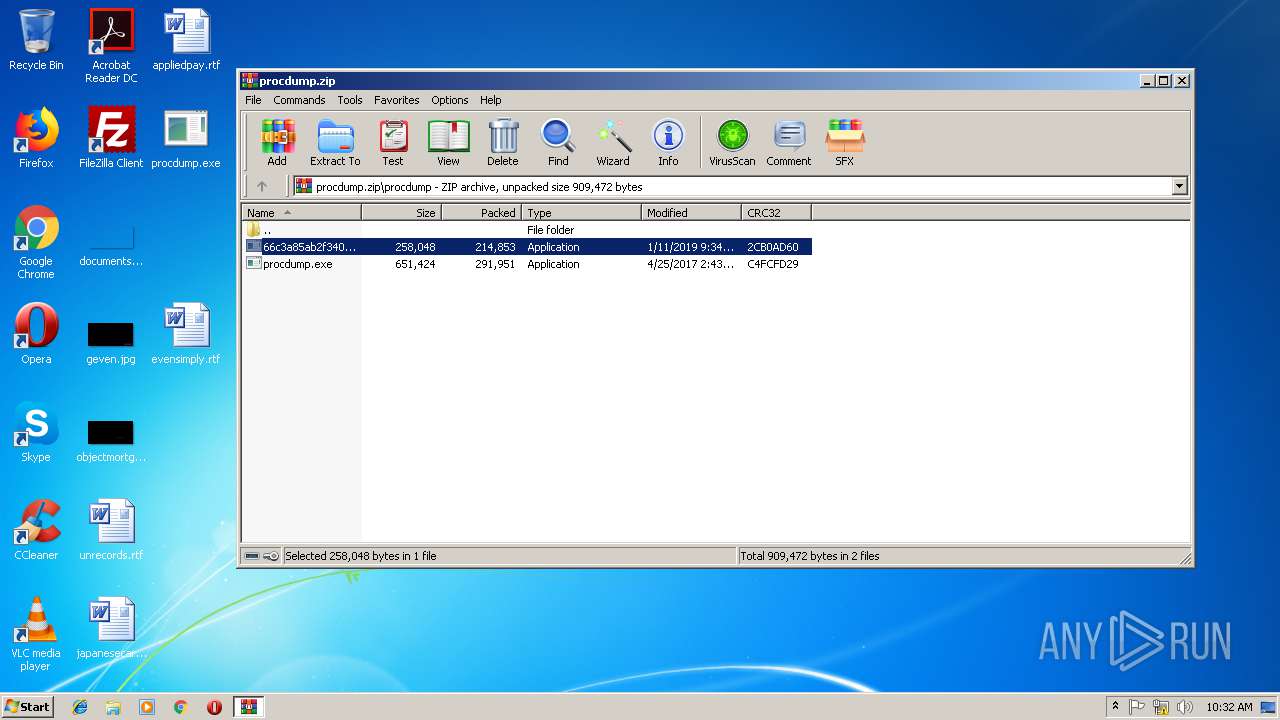
| File name: | procdump.zip |
| Full analysis: | https://app.any.run/tasks/6131e241-53df-4304-97ed-77ebdfbc3ef7 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 10:31:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E776262B1EE913732D7AA04A267E06A8 |
| SHA1: | 247F86F7FB83D718BC6D310EA55ED5CE8DC1DC08 |
| SHA256: | 6D351172237426D58FAAB846683E4C4B4048D8D7A316543A833EE8AC22B0F06A |
| SSDEEP: | 12288:KtRkcAK8Xr+38gCBPEMsh7ClO2ap9F5Ac91M+0ZcdC:Kv0b+sVshmk2yic1M+0ZX |
MALICIOUS
Application was dropped or rewritten from another process
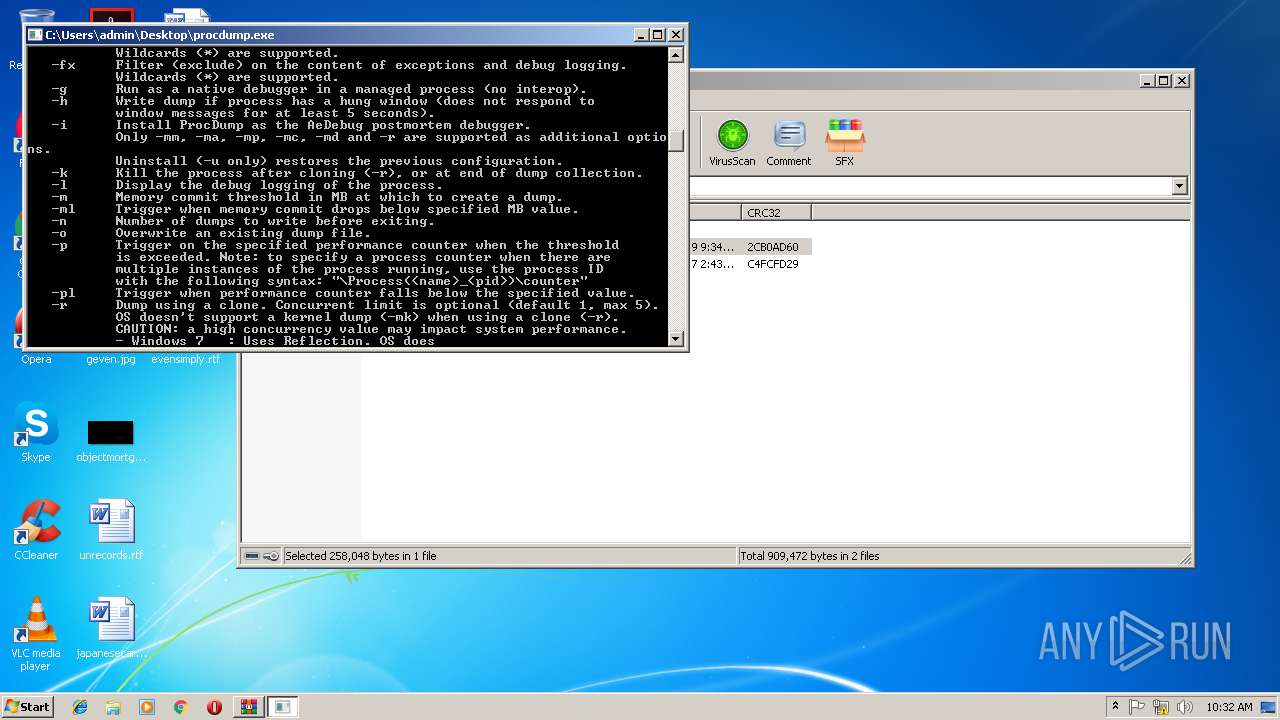
- procdump.exe (PID: 3100)
- procdump.exe (PID: 3288)
- 66c3a85ab2f34092fd15cf15e5c289cc70dd65bb86edf8308ca7b5ae1363abb5_c90wNyasXX1.exe (PID: 560)
- procdump.exe (PID: 3160)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2840)
Starts CMD.EXE for commands execution
- 66c3a85ab2f34092fd15cf15e5c289cc70dd65bb86edf8308ca7b5ae1363abb5_c90wNyasXX1.exe (PID: 560)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3596)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:01:18 13:26:20 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
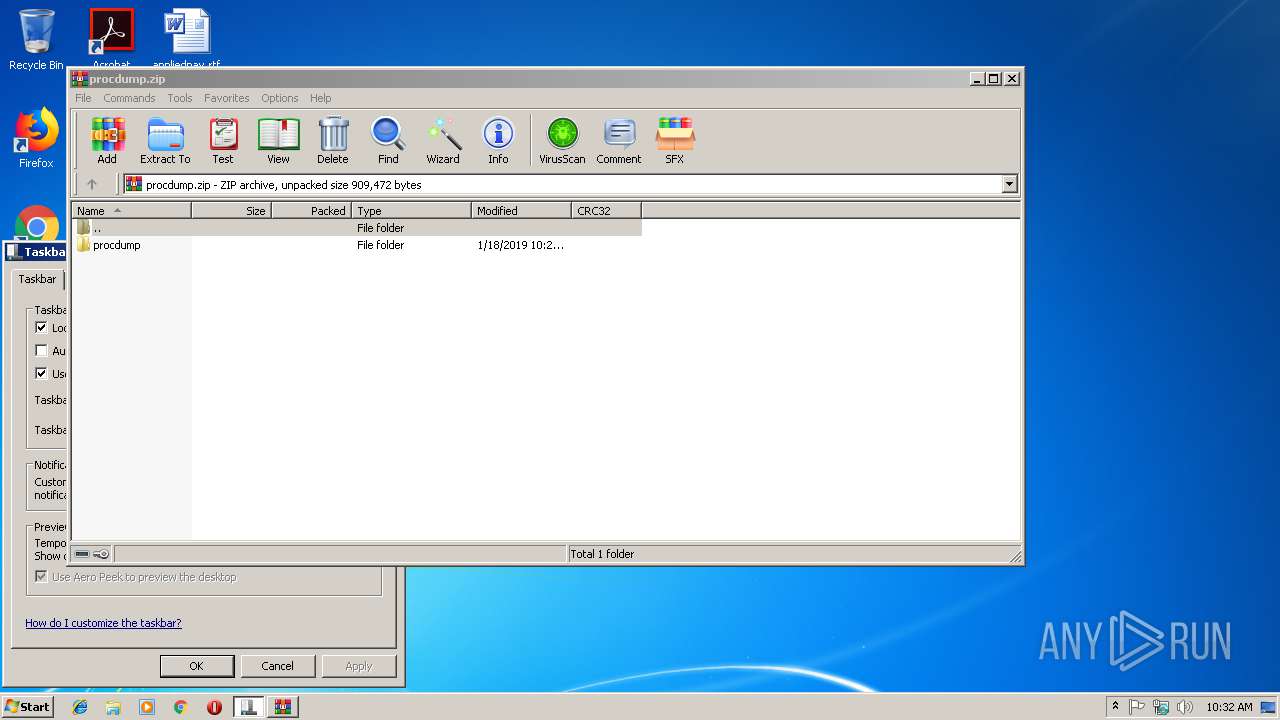
| ZipFileName: | procdump/ |
Total processes
40
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Users\admin\Desktop\66c3a85ab2f34092fd15cf15e5c289cc70dd65bb86edf8308ca7b5ae1363abb5_c90wNyasXX1.exe" | C:\Users\admin\Desktop\66c3a85ab2f34092fd15cf15e5c289cc70dd65bb86edf8308ca7b5ae1363abb5_c90wNyasXX1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2340 | attrib -r -s -h "C:\Users\admin\Desktop\66c3a85ab2f34092fd15cf15e5c289cc70dd65bb86edf8308ca7b5ae1363abb5_c90wNyasXX1.exe" | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
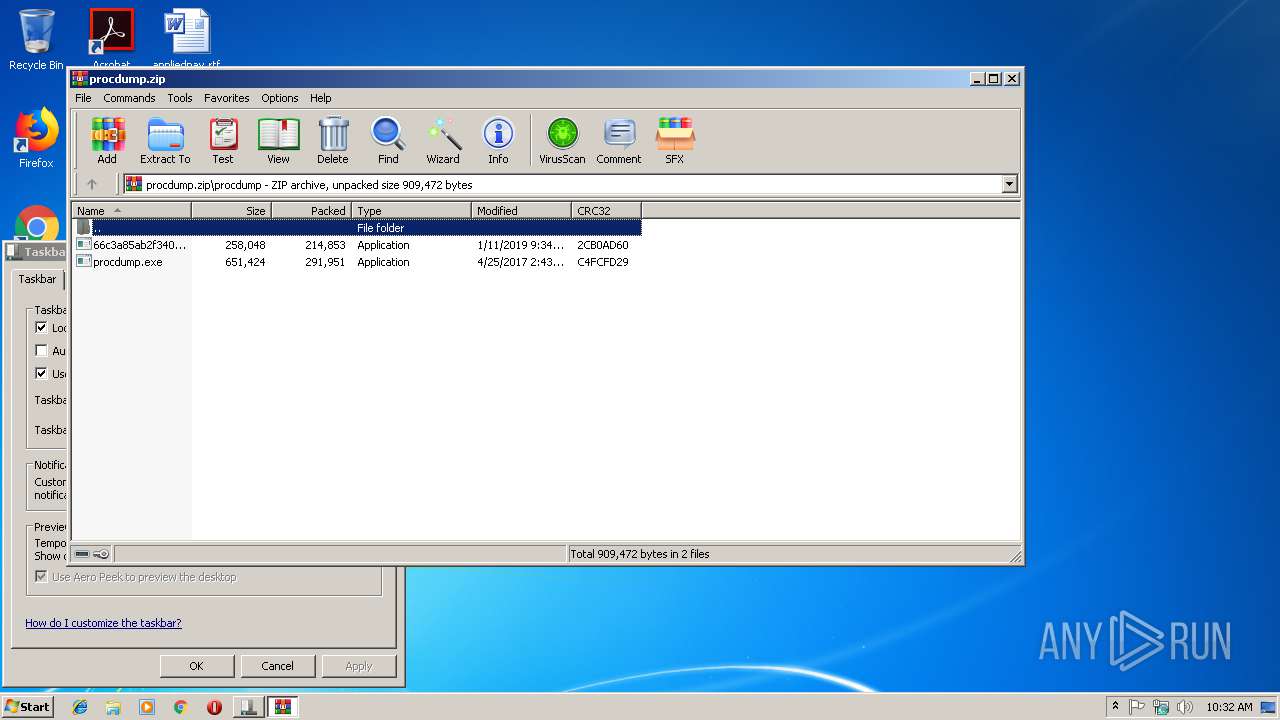
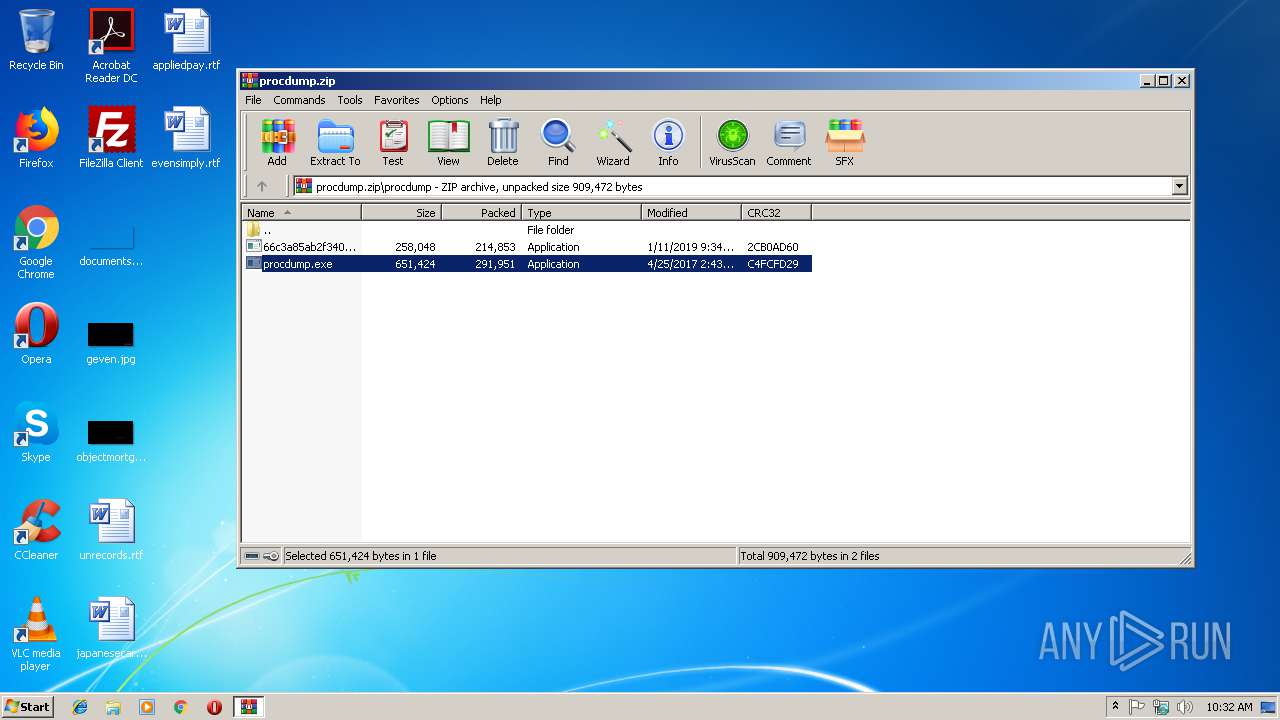
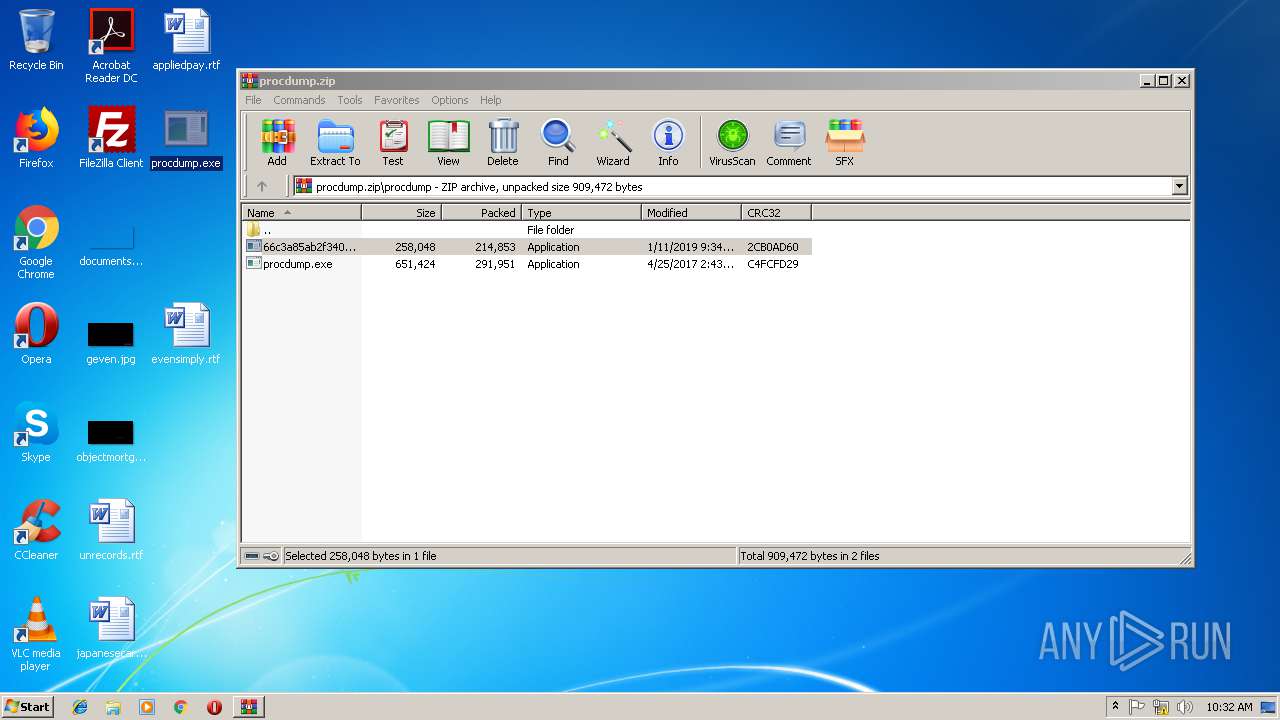
| 2840 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\procdump.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
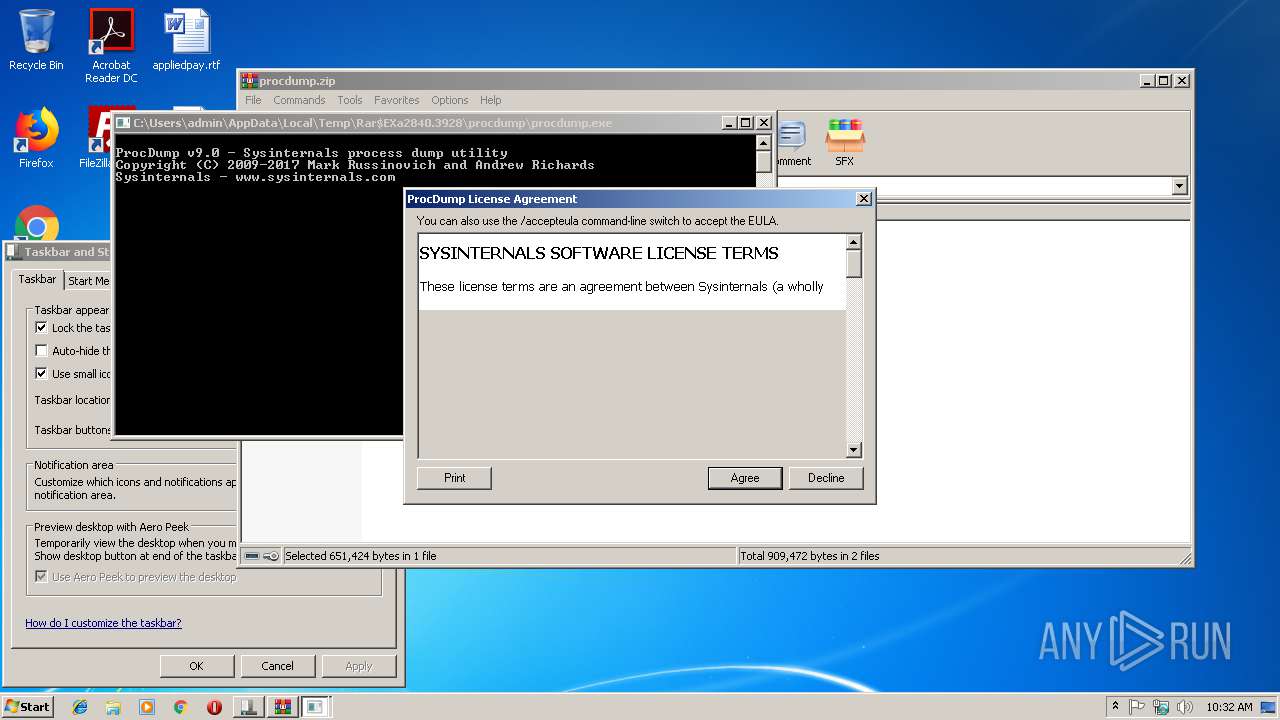
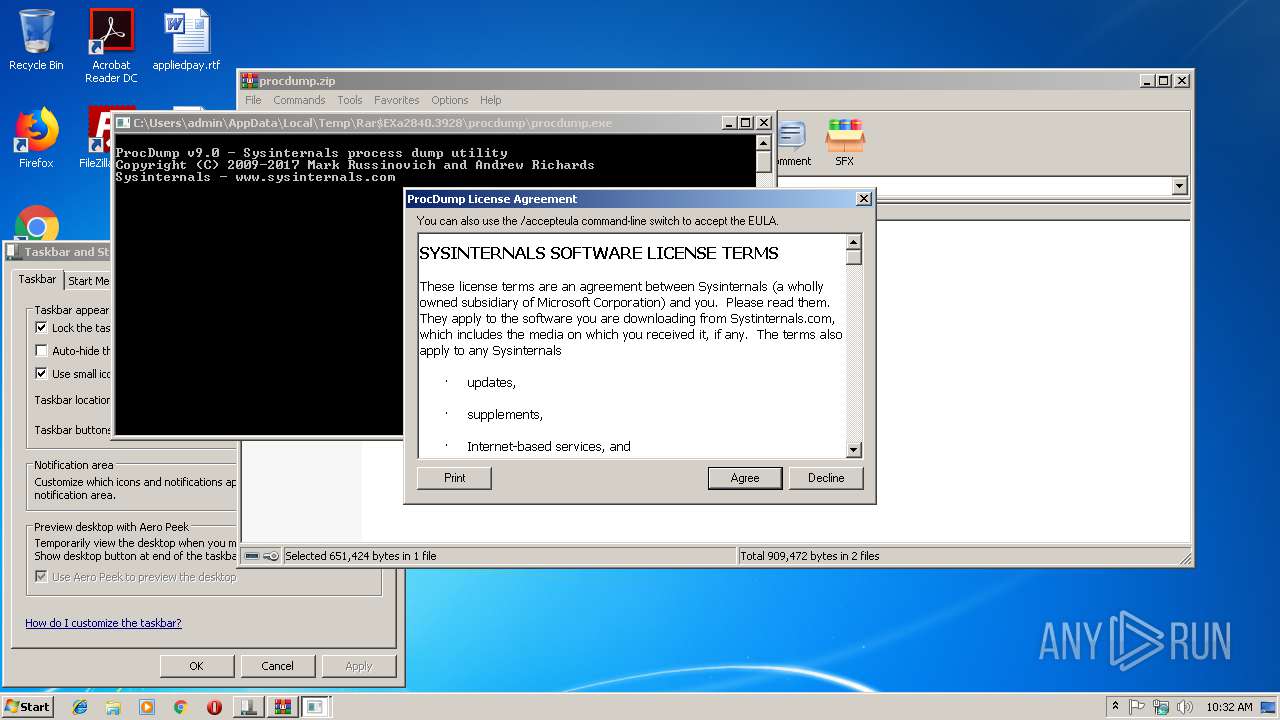
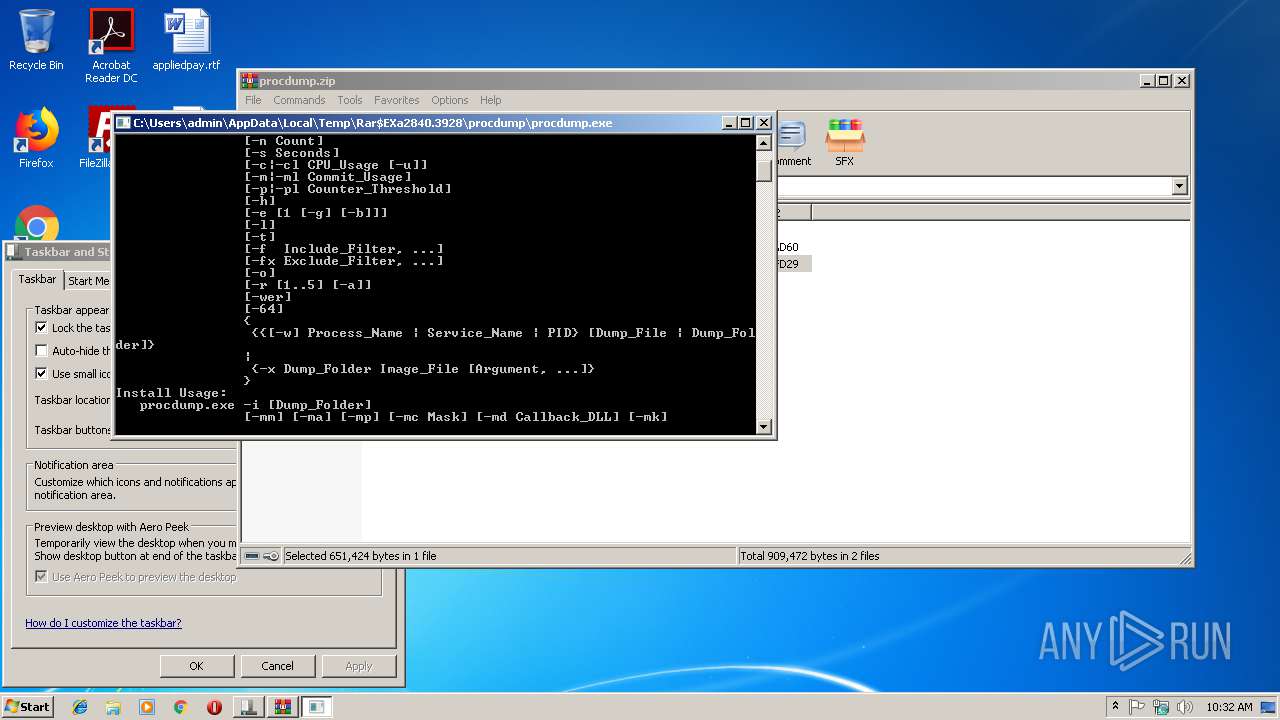
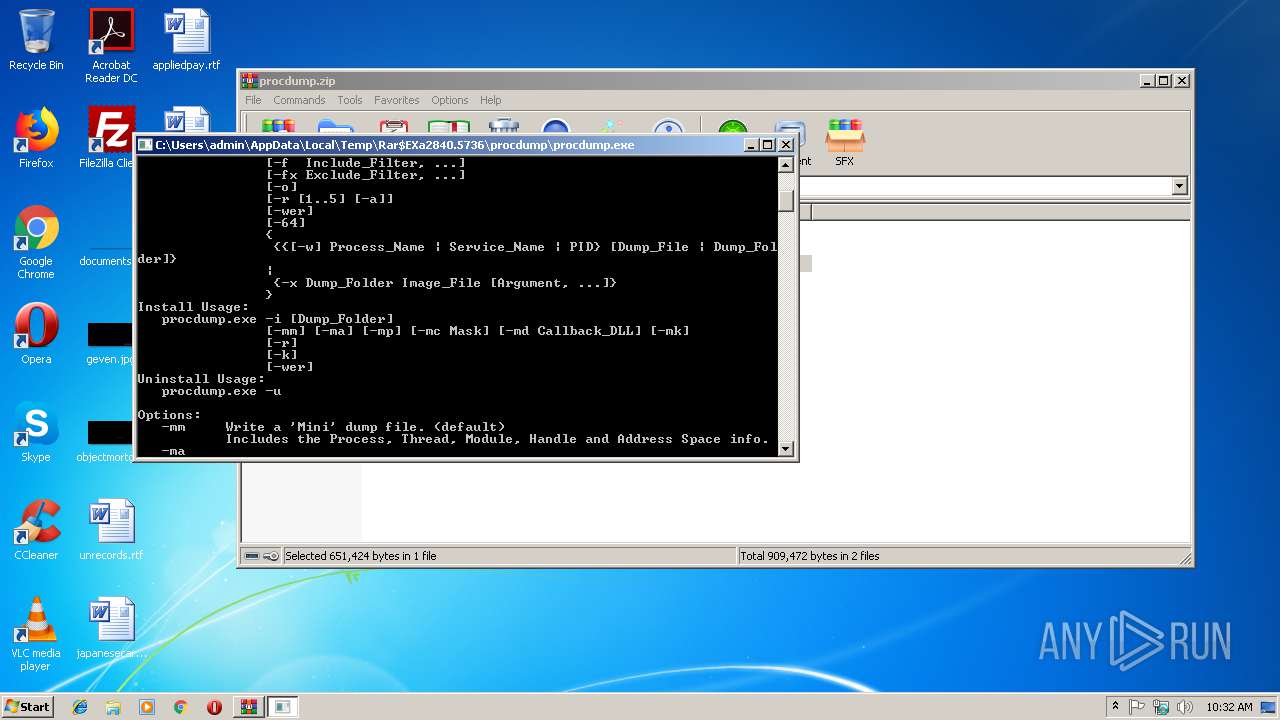
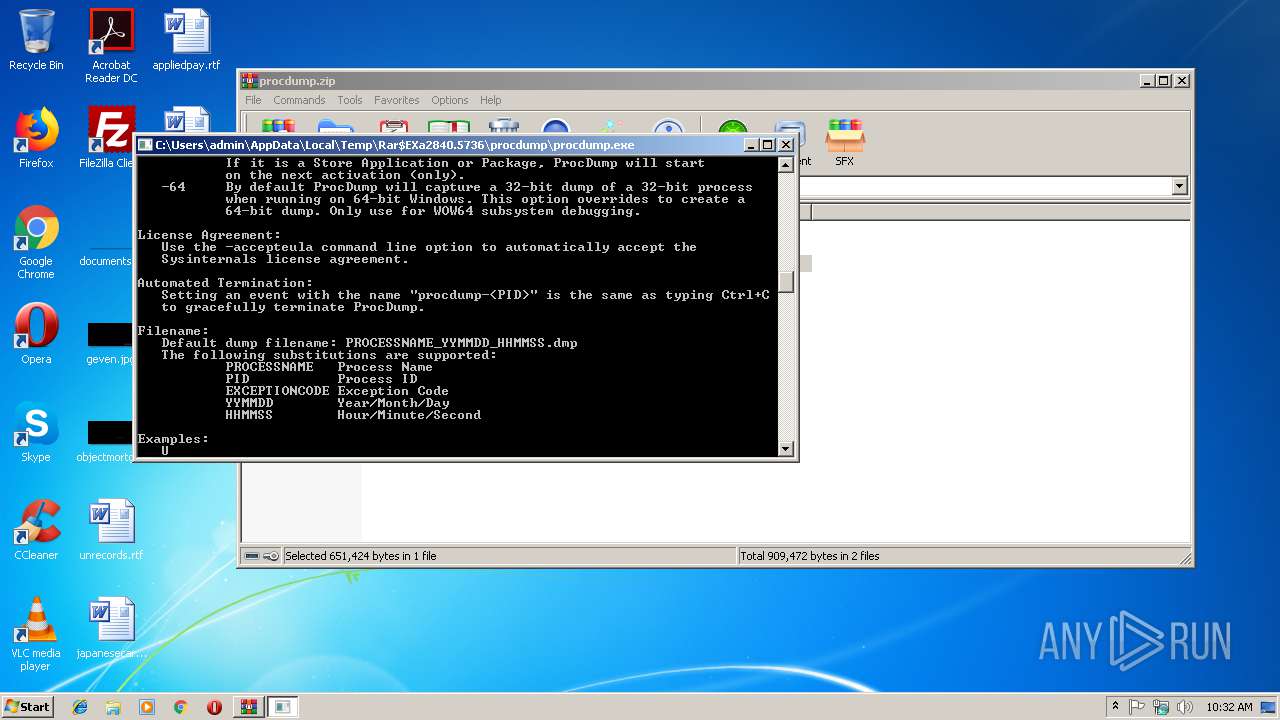
| 3100 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2840.3928\procdump\procdump.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2840.3928\procdump\procdump.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Sysinternals process dump utility Exit code: 4294967295 Version: 9.0 Modules
| |||||||||||||||
| 3160 | "C:\Users\admin\Desktop\procdump.exe" | C:\Users\admin\Desktop\procdump.exe | — | explorer.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Sysinternals process dump utility Exit code: 4294967295 Version: 9.0 Modules
| |||||||||||||||
| 3288 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2840.5736\procdump\procdump.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2840.5736\procdump\procdump.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Sysinternals process dump utility Exit code: 4294967295 Version: 9.0 Modules
| |||||||||||||||
| 3596 | cmd /c ""C:\Users\admin\Desktop\1727265.bat" "C:\Users\admin\Desktop\66c3a85ab2f34092fd15cf15e5c289cc70dd65bb86edf8308ca7b5ae1363abb5_c90wNyasXX1.exe"" | C:\Windows\system32\cmd.exe | — | 66c3a85ab2f34092fd15cf15e5c289cc70dd65bb86edf8308ca7b5ae1363abb5_c90wNyasXX1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
497
Read events
478
Write events
19
Delete events
0
Modification events
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\procdump.zip | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
5
Suspicious files
0
Text files
0
Unknown types
0
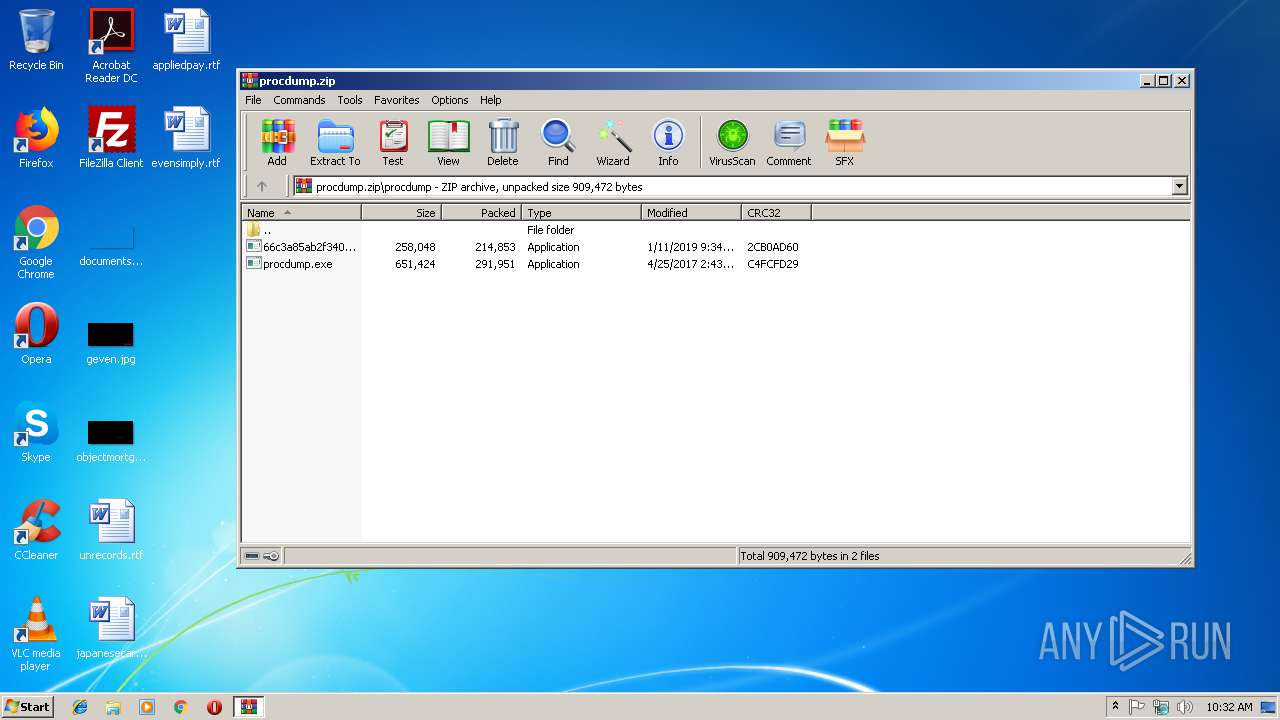
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
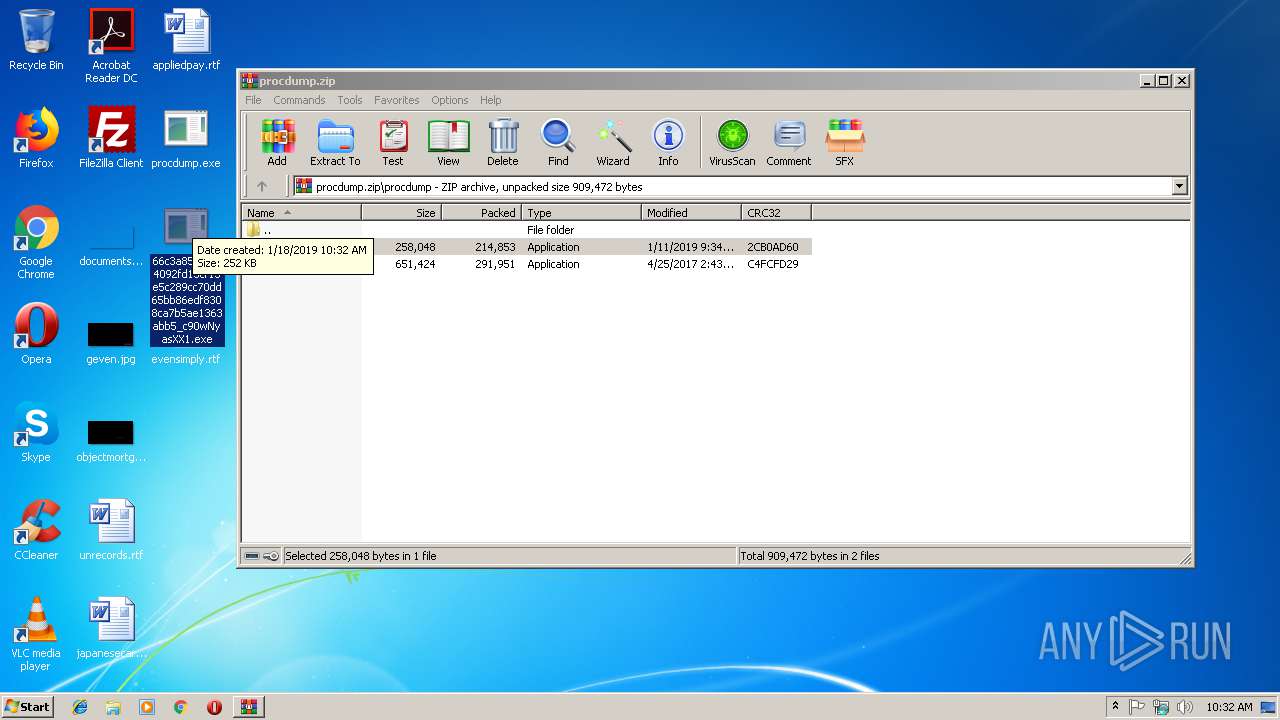
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2840.7559\procdump\66c3a85ab2f34092fd15cf15e5c289cc70dd65bb86edf8308ca7b5ae1363abb5_c90wNyasXX1.exe | — | |
MD5:— | SHA256:— | |||
| 560 | 66c3a85ab2f34092fd15cf15e5c289cc70dd65bb86edf8308ca7b5ae1363abb5_c90wNyasXX1.exe | C:\Users\admin\Desktop\1727265.bat | — | |
MD5:— | SHA256:— | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2840.3928\procdump\procdump.exe | executable | |
MD5:6A09BC6C19C4236C0BD8A01953371A29 | SHA256:05732E84DE58A3CC142535431B3AA04EFBE034CC96E837F93C360A6387D8FAAD | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2840.5736\procdump\procdump.exe | executable | |
MD5:6A09BC6C19C4236C0BD8A01953371A29 | SHA256:05732E84DE58A3CC142535431B3AA04EFBE034CC96E837F93C360A6387D8FAAD | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2840.3928\procdump\66c3a85ab2f34092fd15cf15e5c289cc70dd65bb86edf8308ca7b5ae1363abb5_c90wNyasXX1.exe | executable | |
MD5:— | SHA256:— | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2840.5736\procdump\66c3a85ab2f34092fd15cf15e5c289cc70dd65bb86edf8308ca7b5ae1363abb5_c90wNyasXX1.exe | executable | |
MD5:— | SHA256:— | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2840.7375\procdump\procdump.exe | executable | |
MD5:6A09BC6C19C4236C0BD8A01953371A29 | SHA256:05732E84DE58A3CC142535431B3AA04EFBE034CC96E837F93C360A6387D8FAAD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report