| File name: | 01062025_1434_13.vbs |
| Full analysis: | https://app.any.run/tasks/d86be30c-4a46-4750-9589-7c4e0a2c4e8e |
| Verdict: | Malicious activity |
| Analysis date: | June 01, 2025, 14:40:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text |
| MD5: | 0A8088B58AC914A3717CC91932B6C28A |
| SHA1: | 7BE27F7807F485367649E668CD8F6F4B47D230F2 |
| SHA256: | 6D22E034B72328D1D63DDFBCBB8D0F3397A057467321098EDF36801A742CA1E4 |
| SSDEEP: | 6:j6Nqsks8XI+gPVmLyFPbGVzLh8JdDh8iB8XIYAGQO0wKjFl8u8v:Jsd8XIPPs+FPbGVvGHDh8O8XIYAHpwoe |
MALICIOUS
Changes powershell execution policy (RemoteSigned)
- wscript.exe (PID: 2852)
- powershell.exe (PID: 7376)
SUSPICIOUS
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 2852)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 2852)
- powershell.exe (PID: 7376)
The process executes Powershell scripts
- wscript.exe (PID: 2852)
- powershell.exe (PID: 7376)
Manipulates environment variables
- powershell.exe (PID: 7376)
Downloads file from URI via Powershell
- powershell.exe (PID: 7376)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2852)
- powershell.exe (PID: 7376)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2852)
Application launched itself
- powershell.exe (PID: 7376)
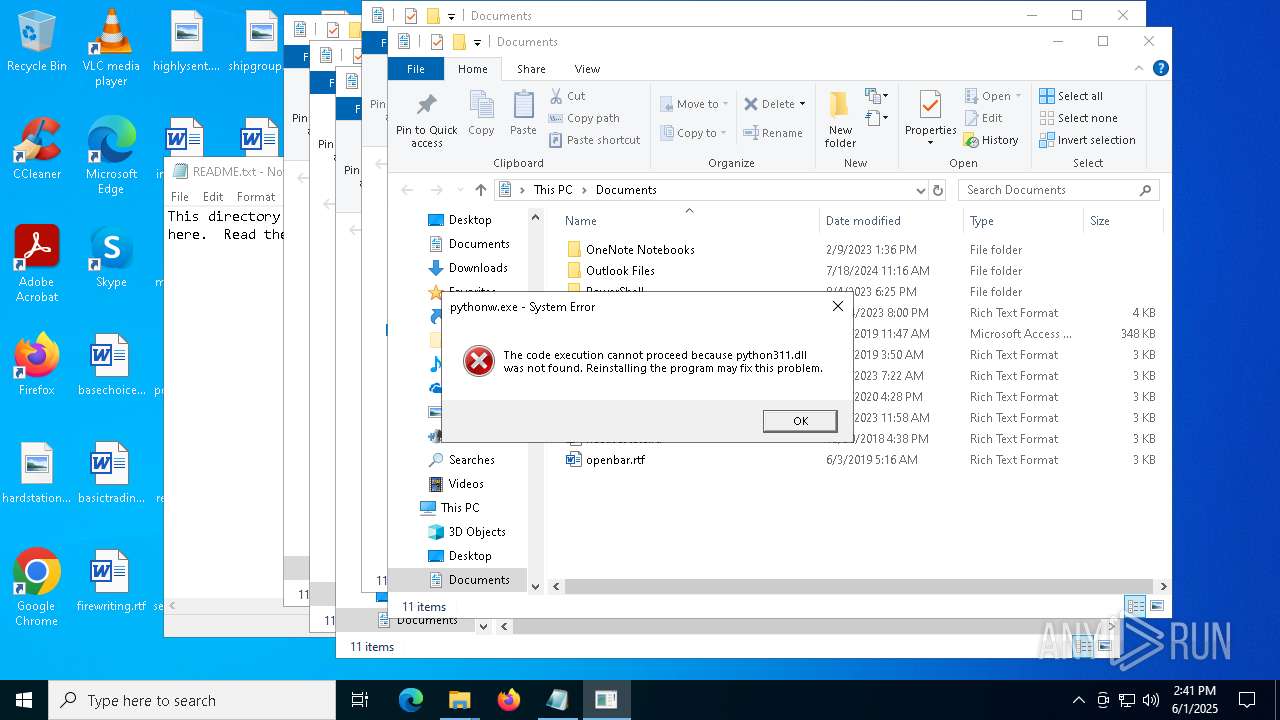
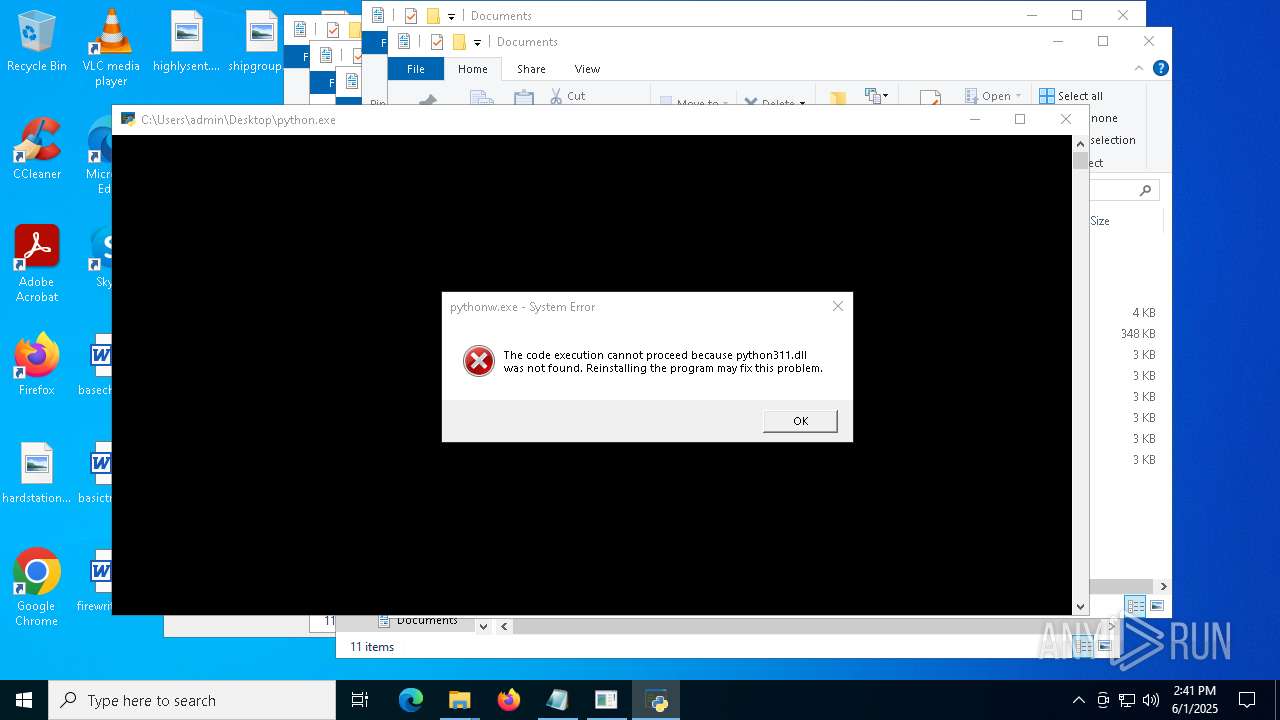
The process drops C-runtime libraries
- powershell.exe (PID: 5176)
Process drops legitimate windows executable
- powershell.exe (PID: 5176)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 5176)
Checks for external IP
- svchost.exe (PID: 2196)
- powershell.exe (PID: 5176)
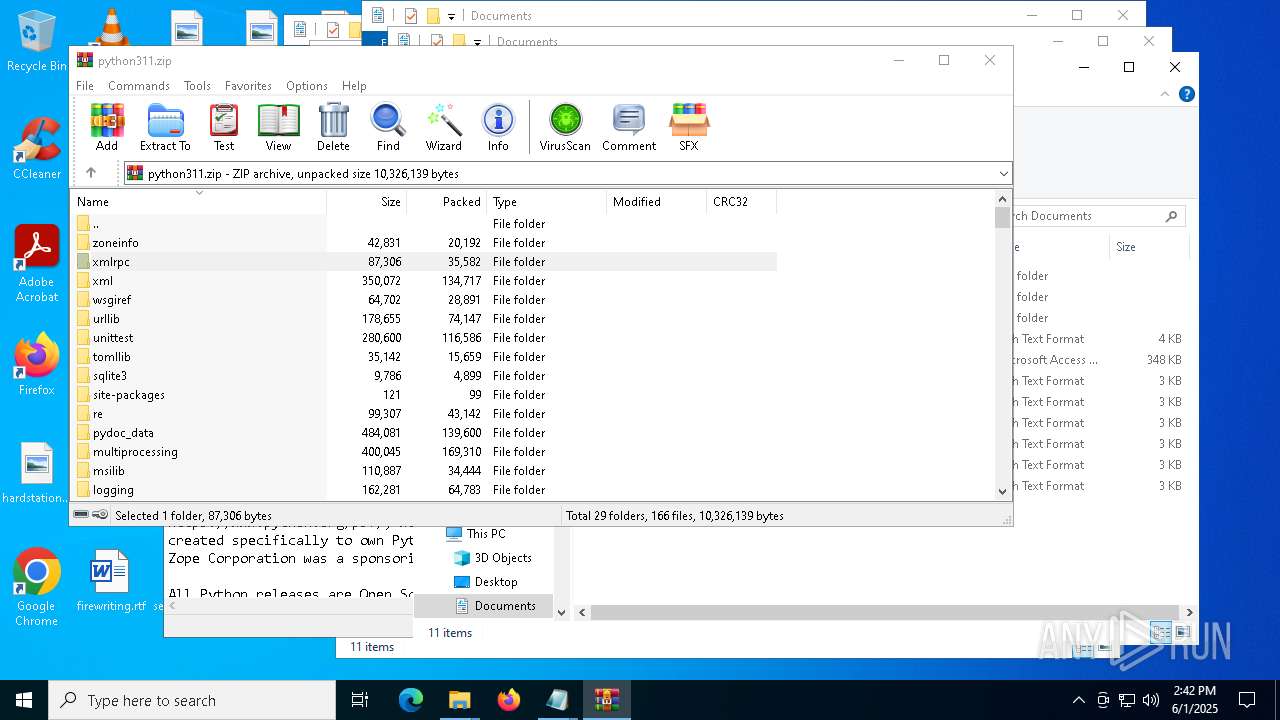
Process drops python dynamic module
- powershell.exe (PID: 5176)
Executable content was dropped or overwritten
- powershell.exe (PID: 5176)
- python.exe (PID: 856)
Loads Python modules
- python.exe (PID: 856)
Starts CMD.EXE for commands execution
- python.exe (PID: 856)
INFO
Checks proxy server information
- powershell.exe (PID: 7376)
- powershell.exe (PID: 5176)
- python.exe (PID: 856)
Disables trace logs
- powershell.exe (PID: 7376)
- powershell.exe (PID: 5176)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5176)
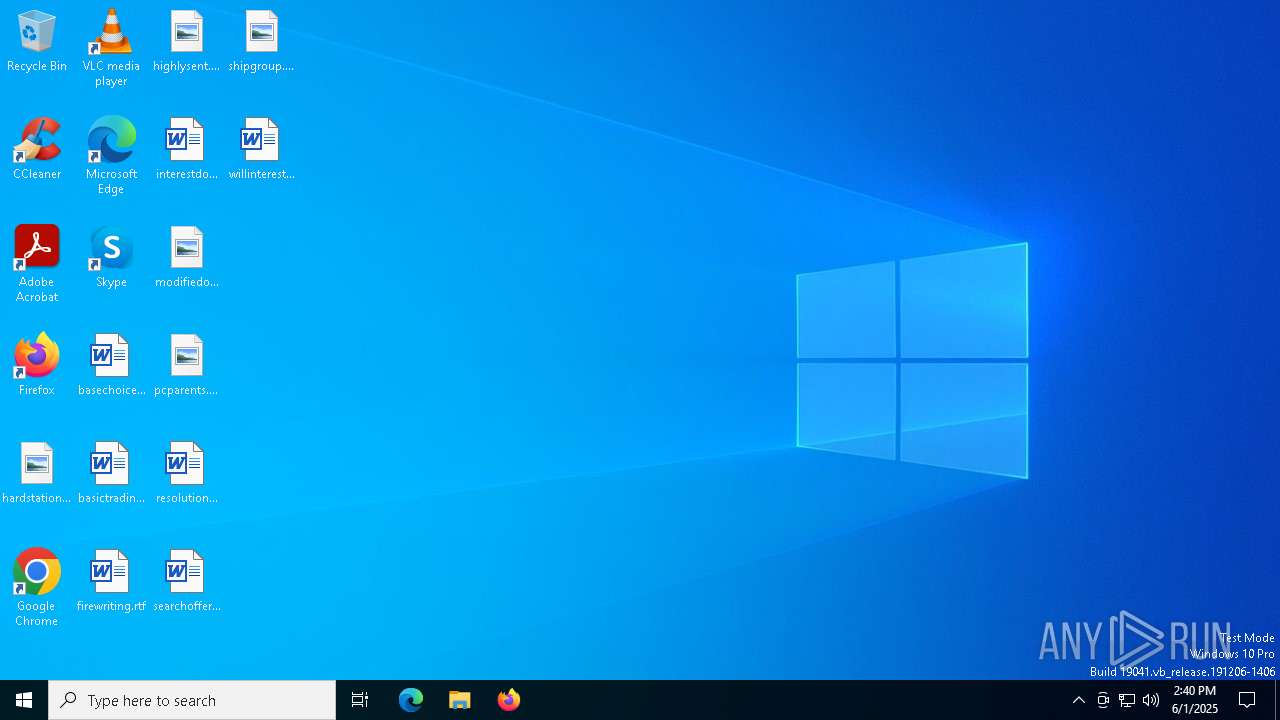
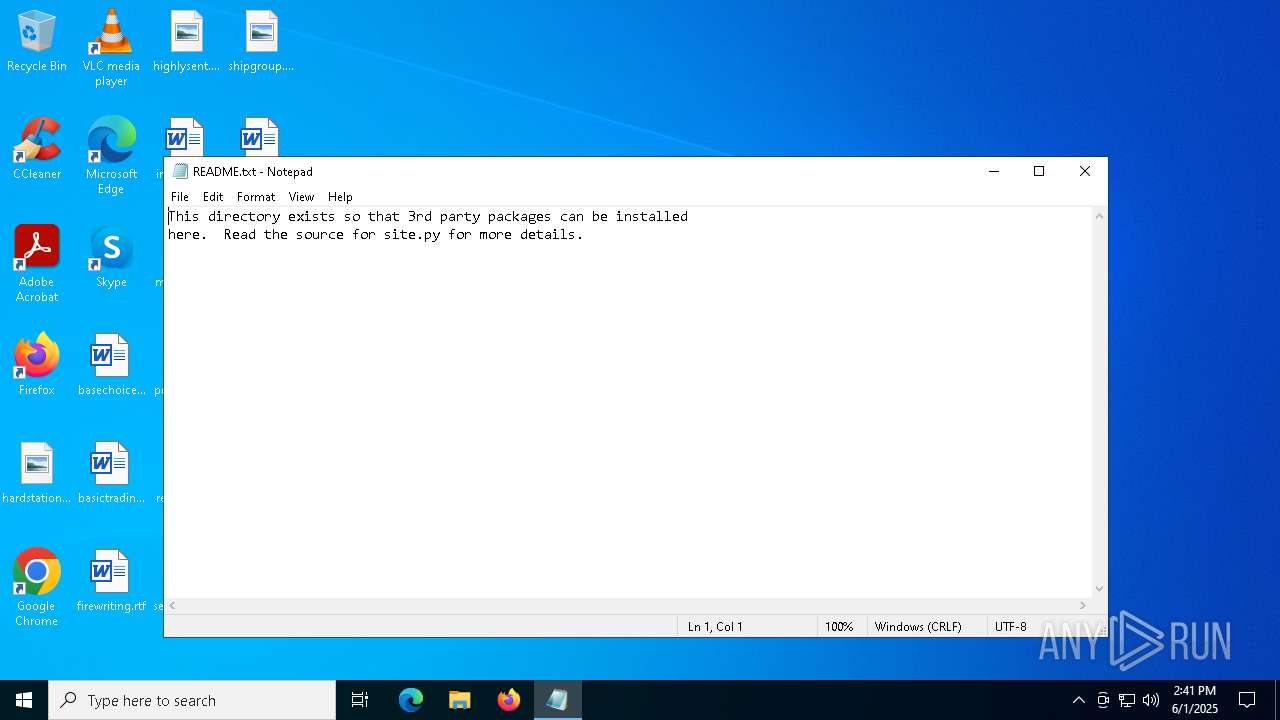
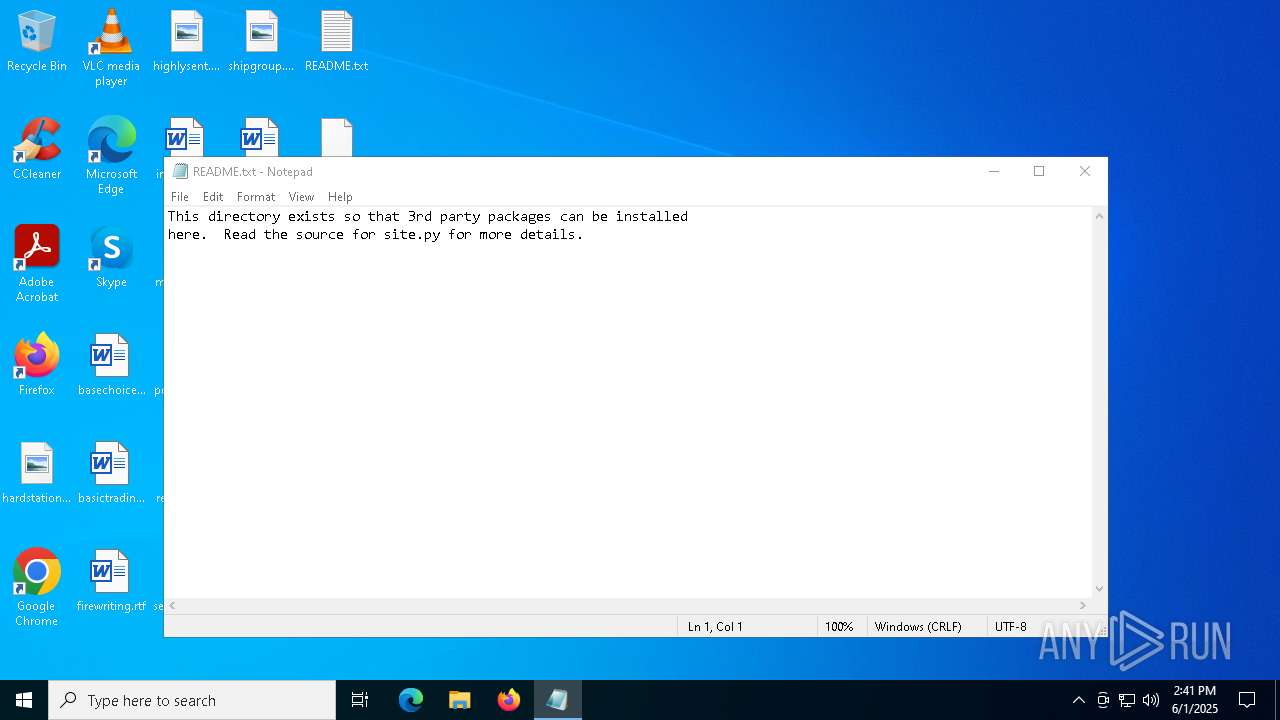
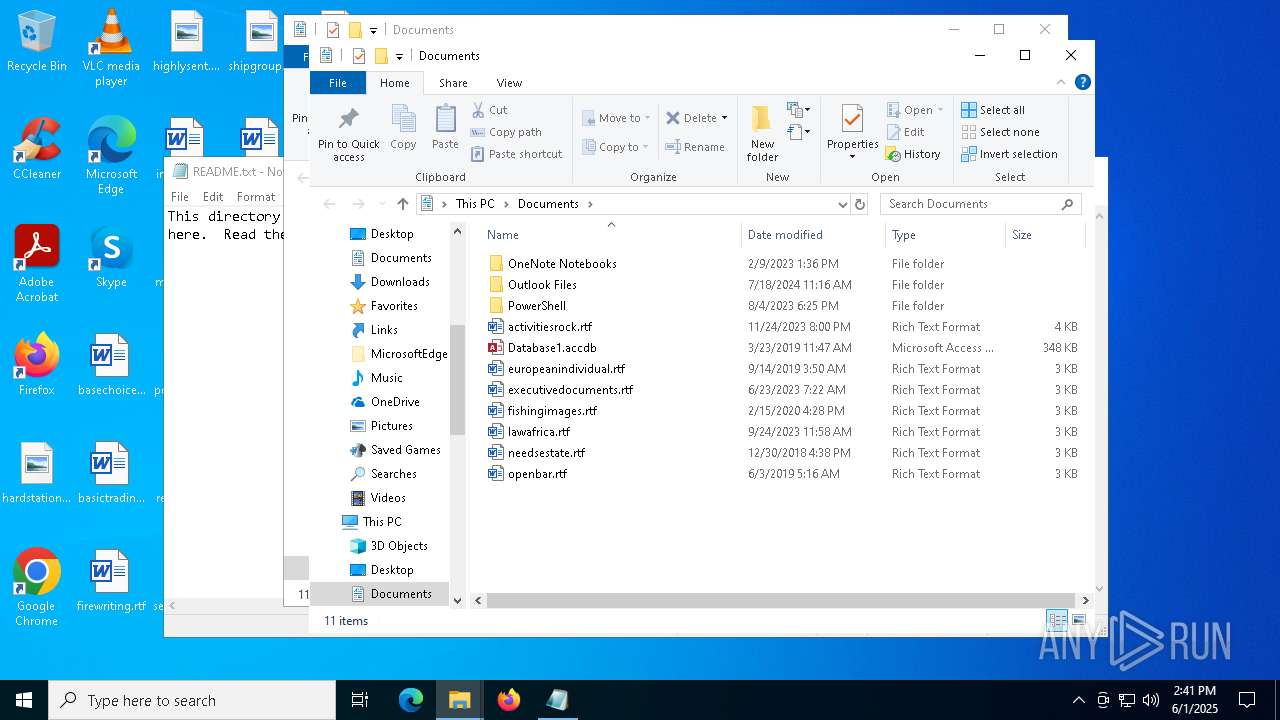
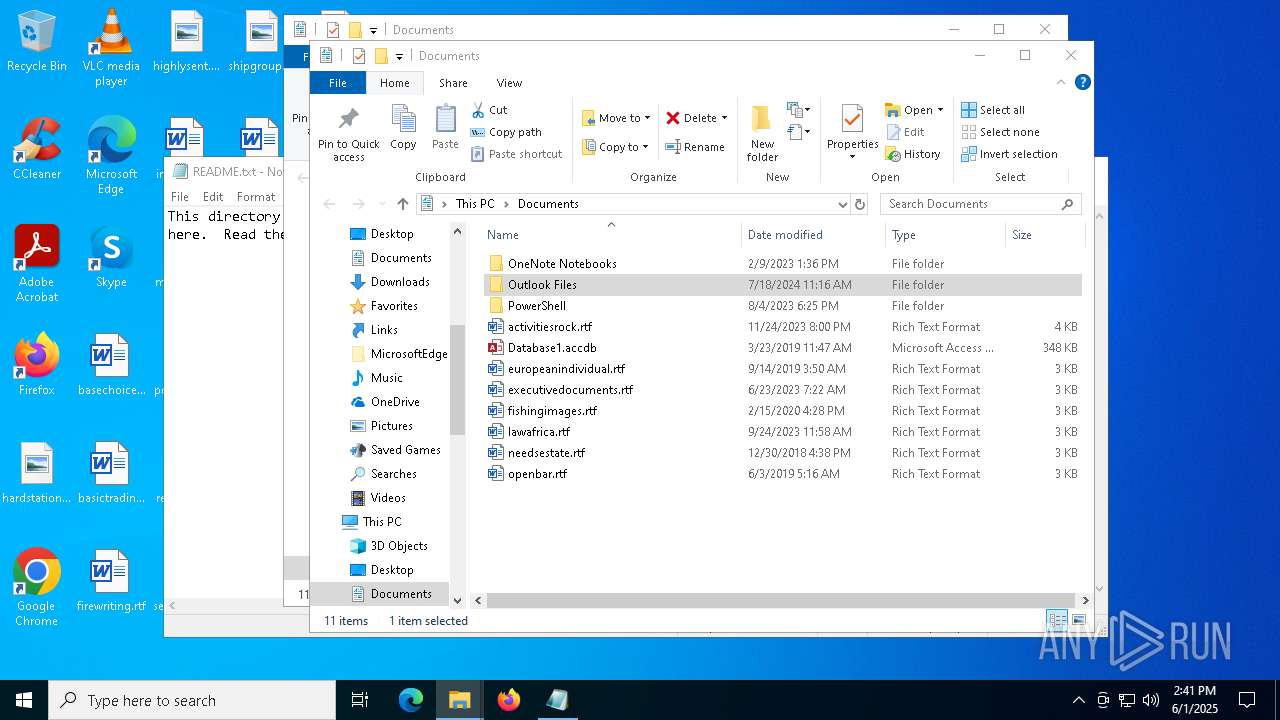
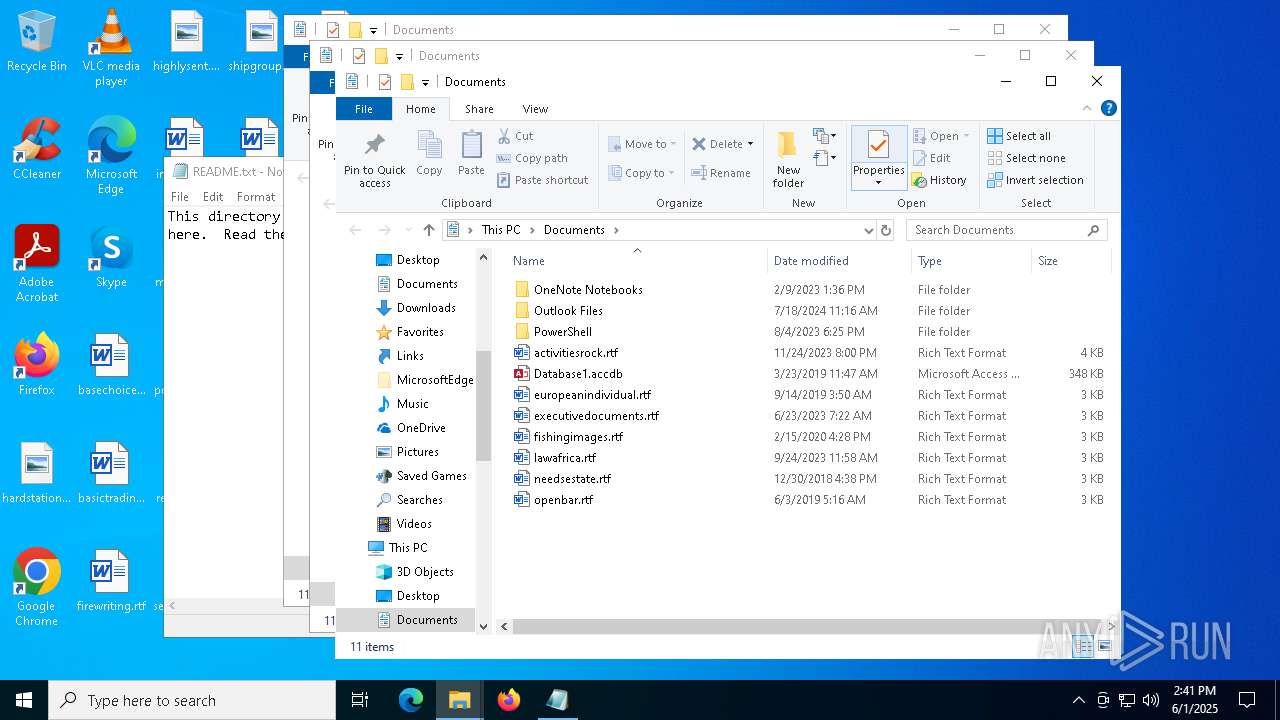
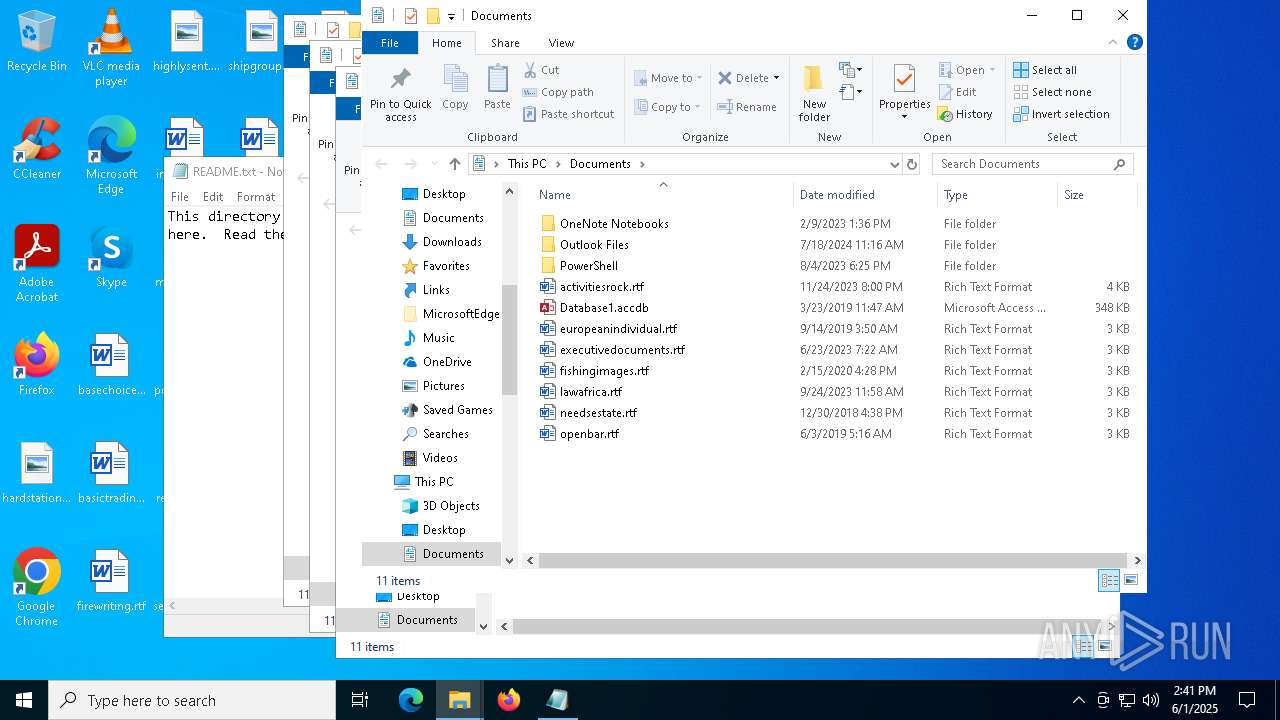
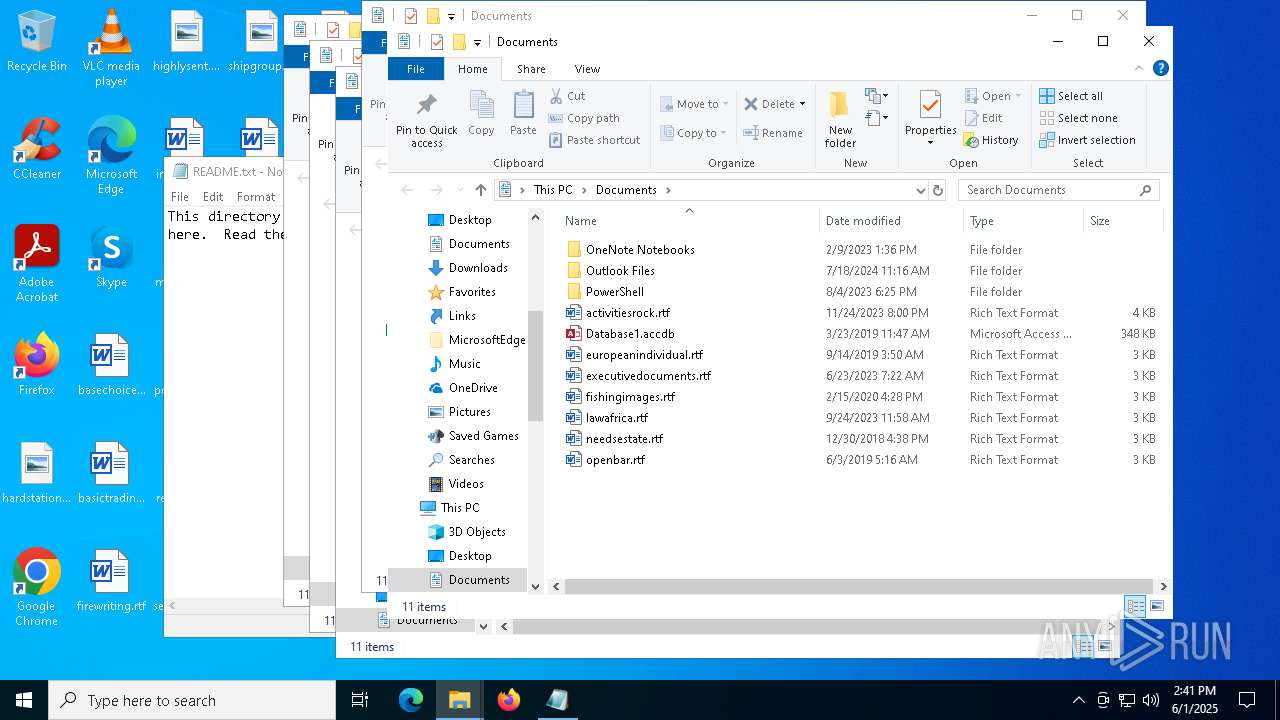
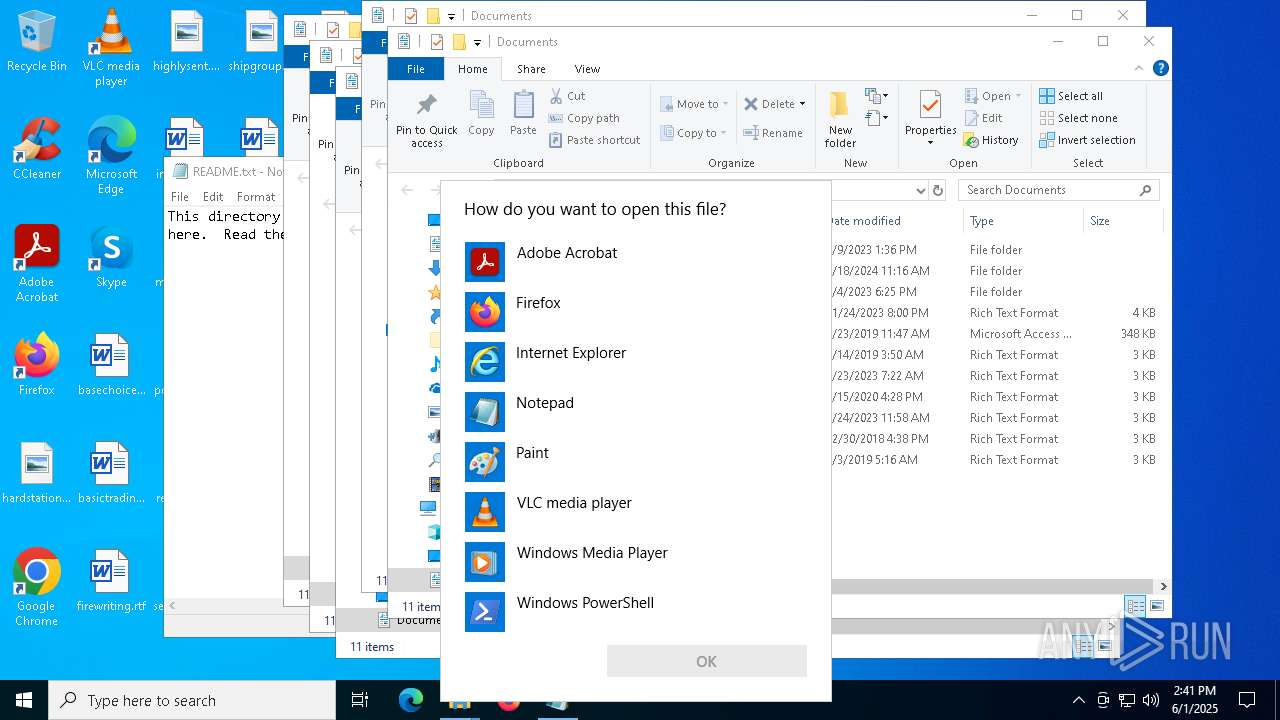
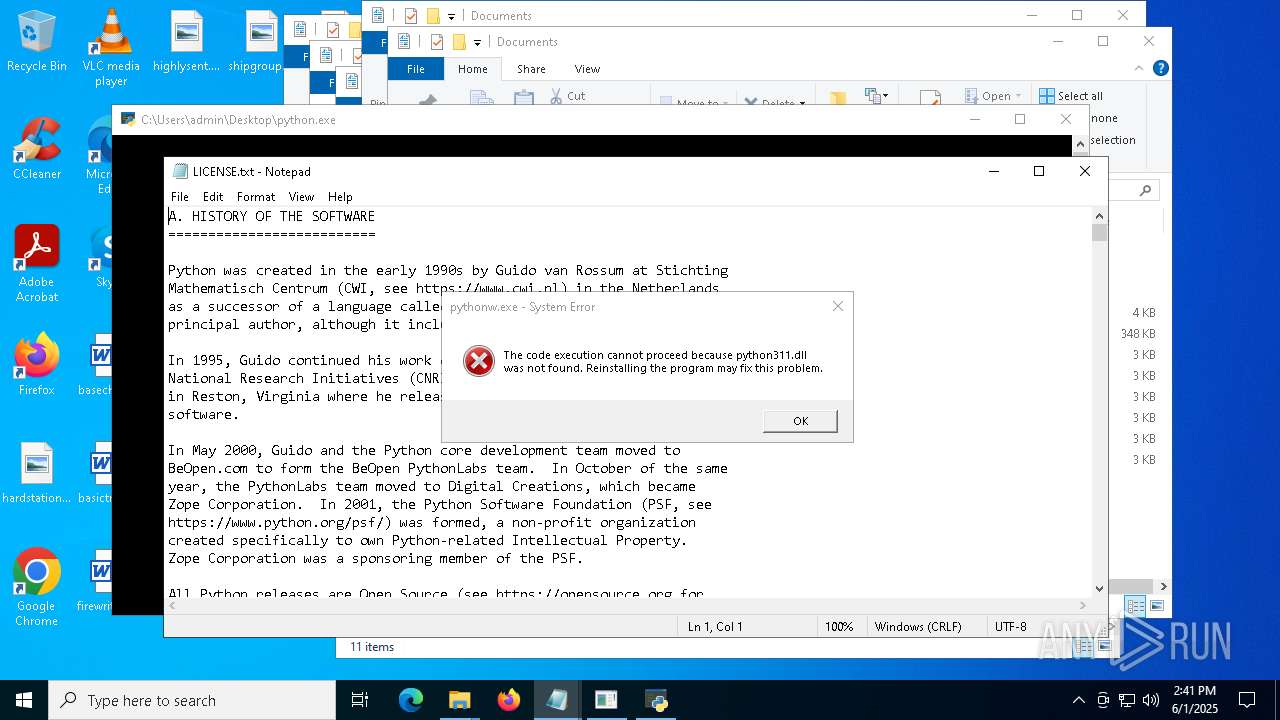
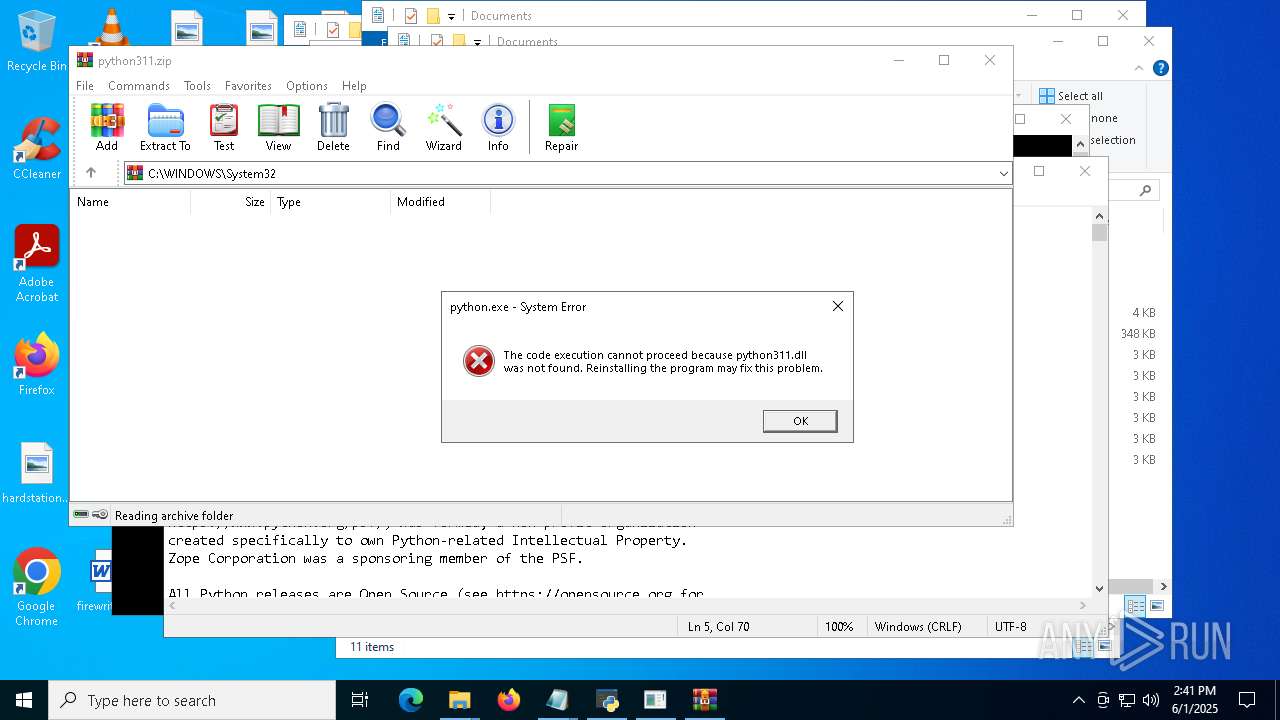
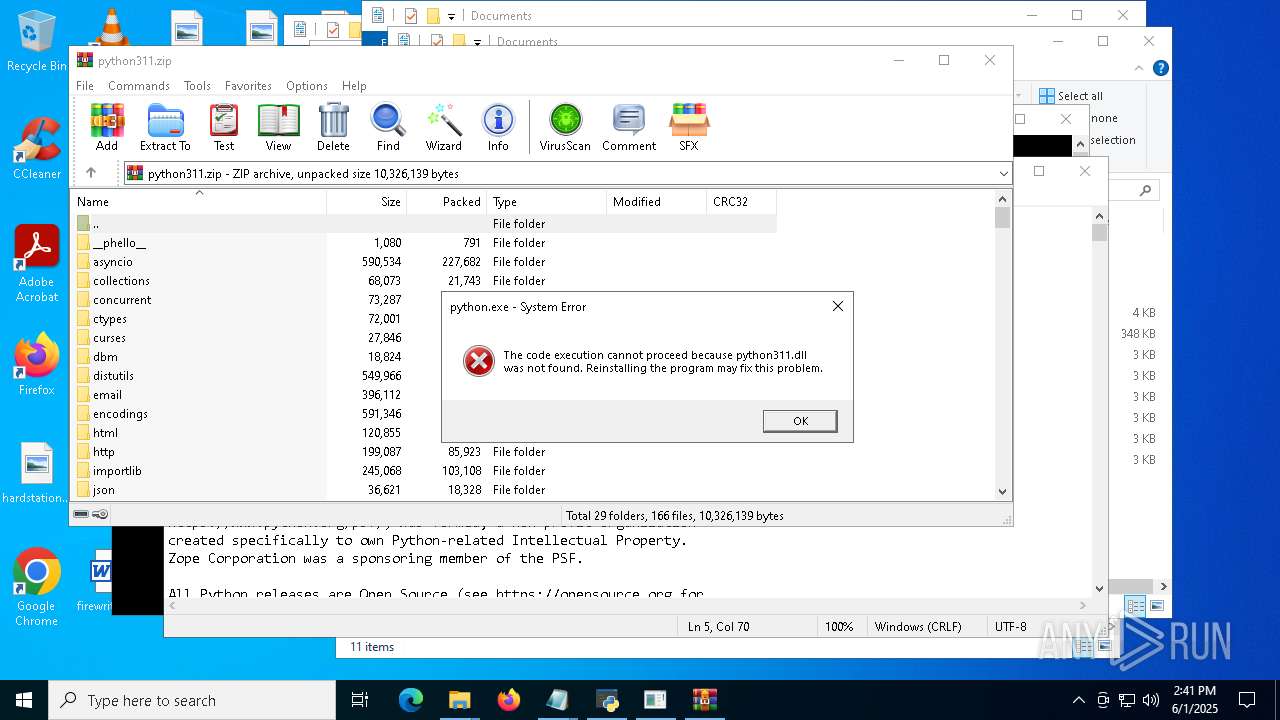
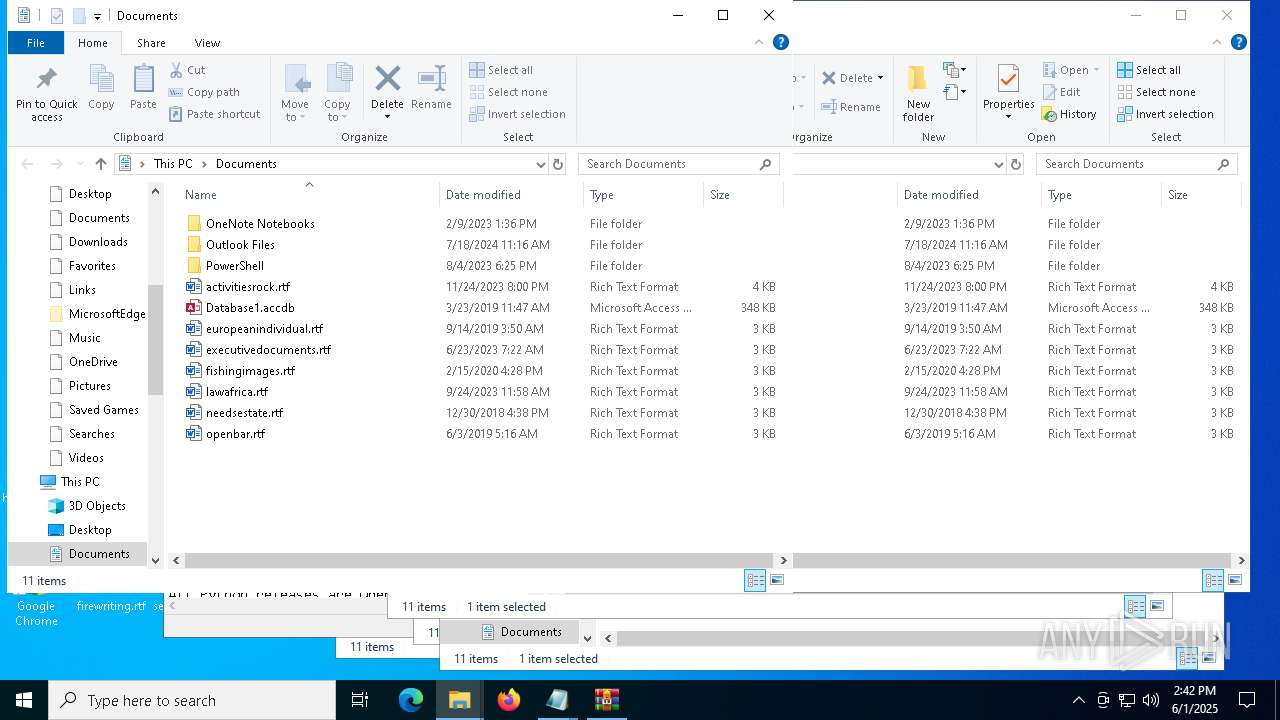
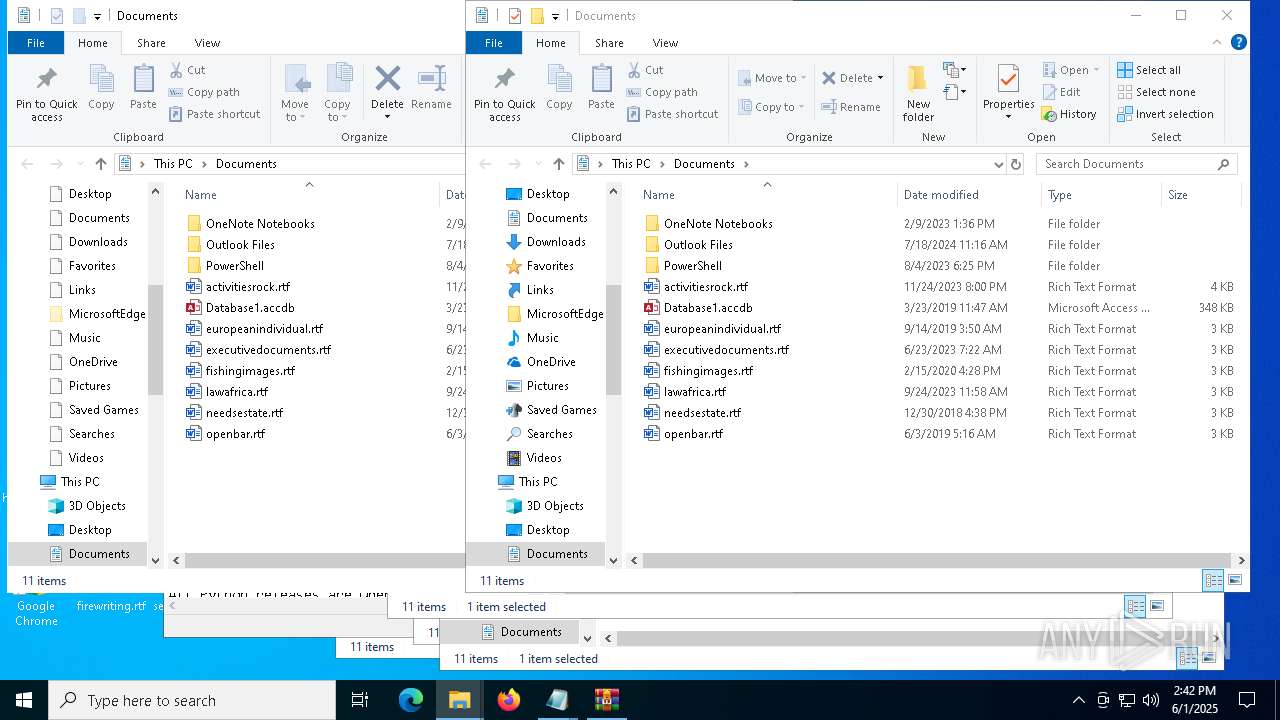
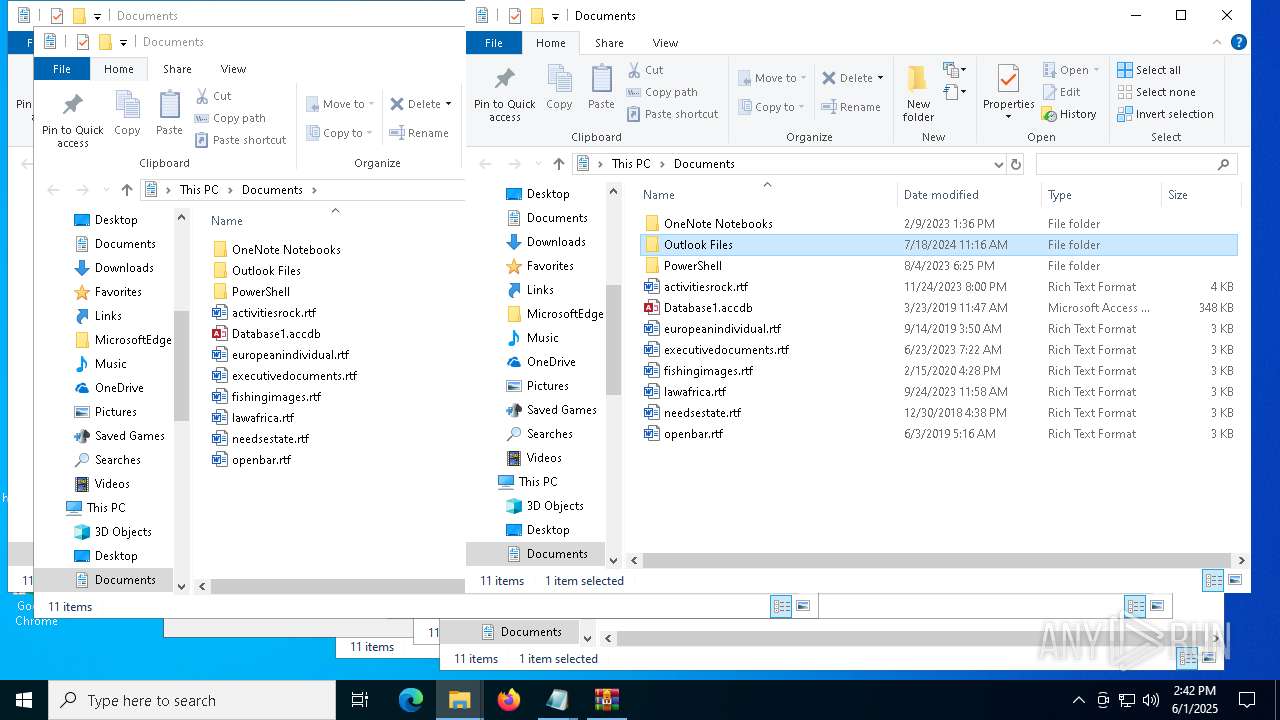
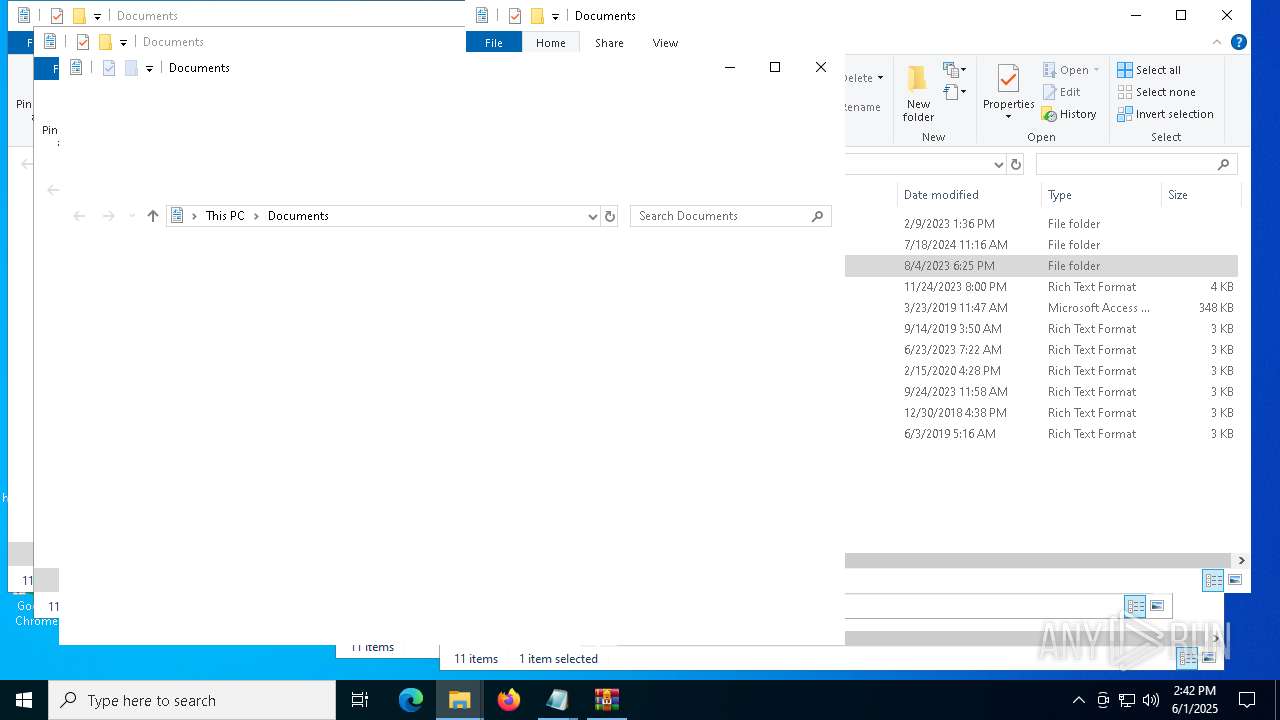
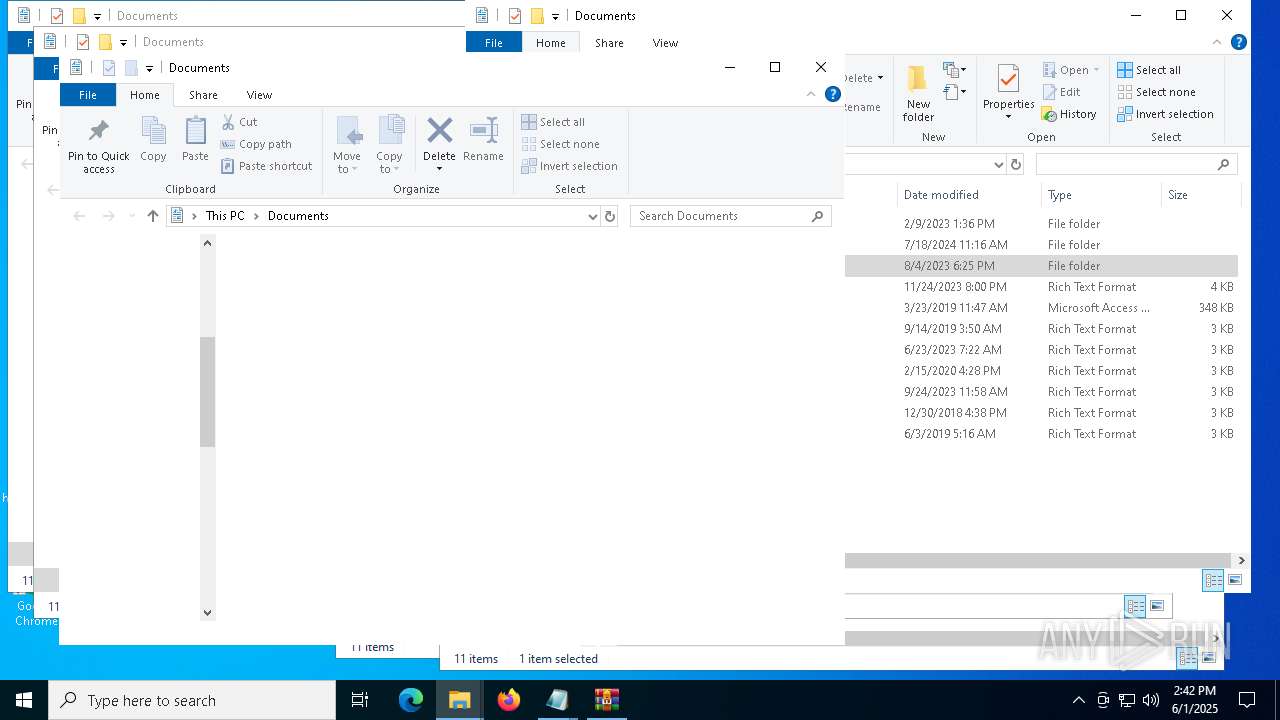
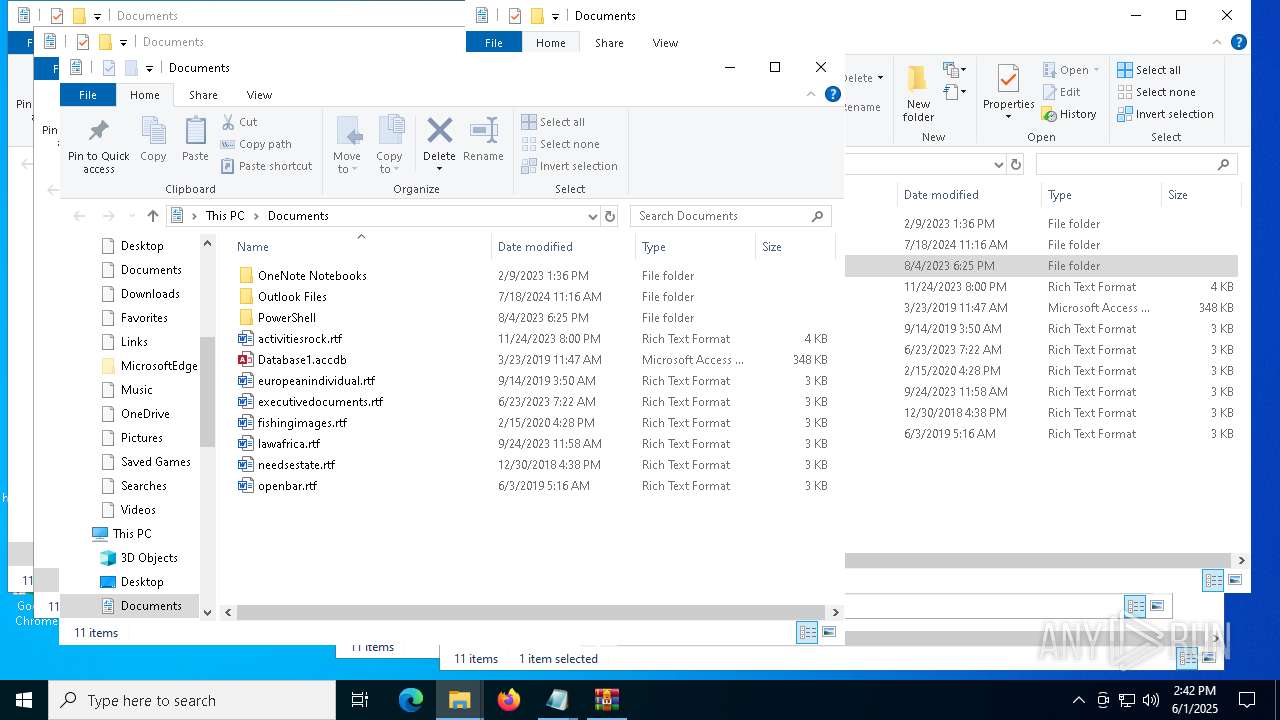
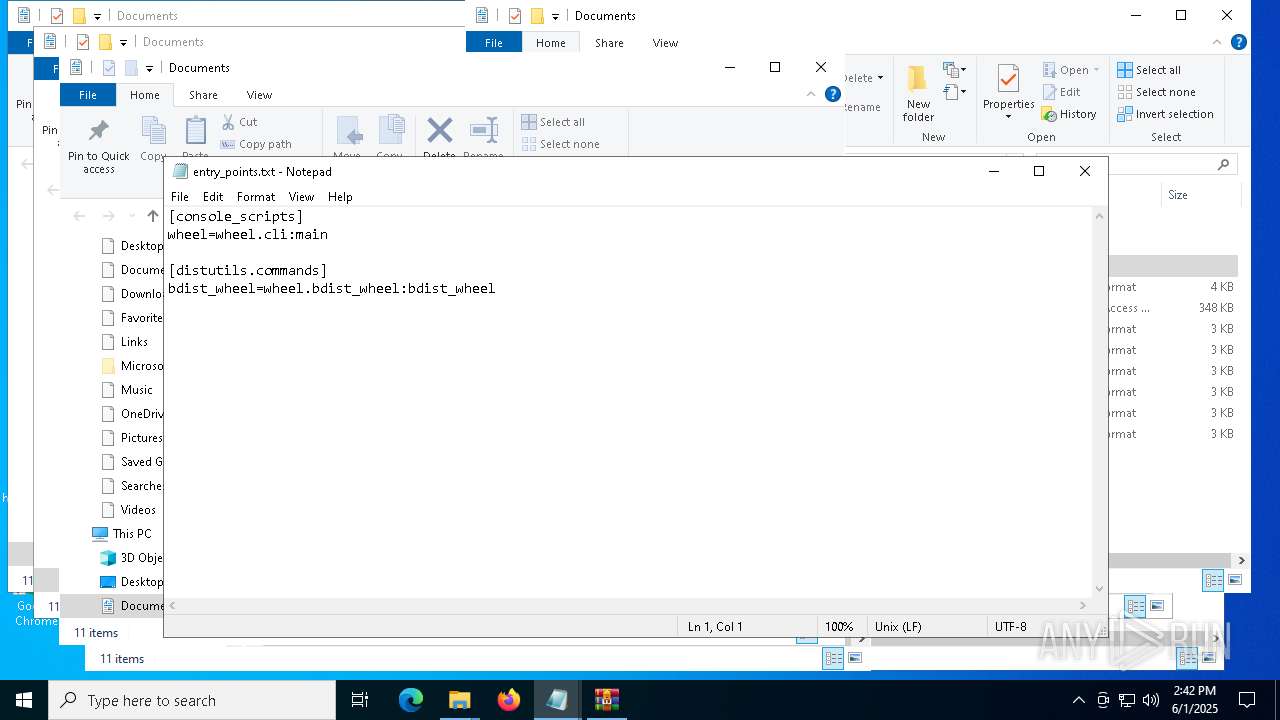
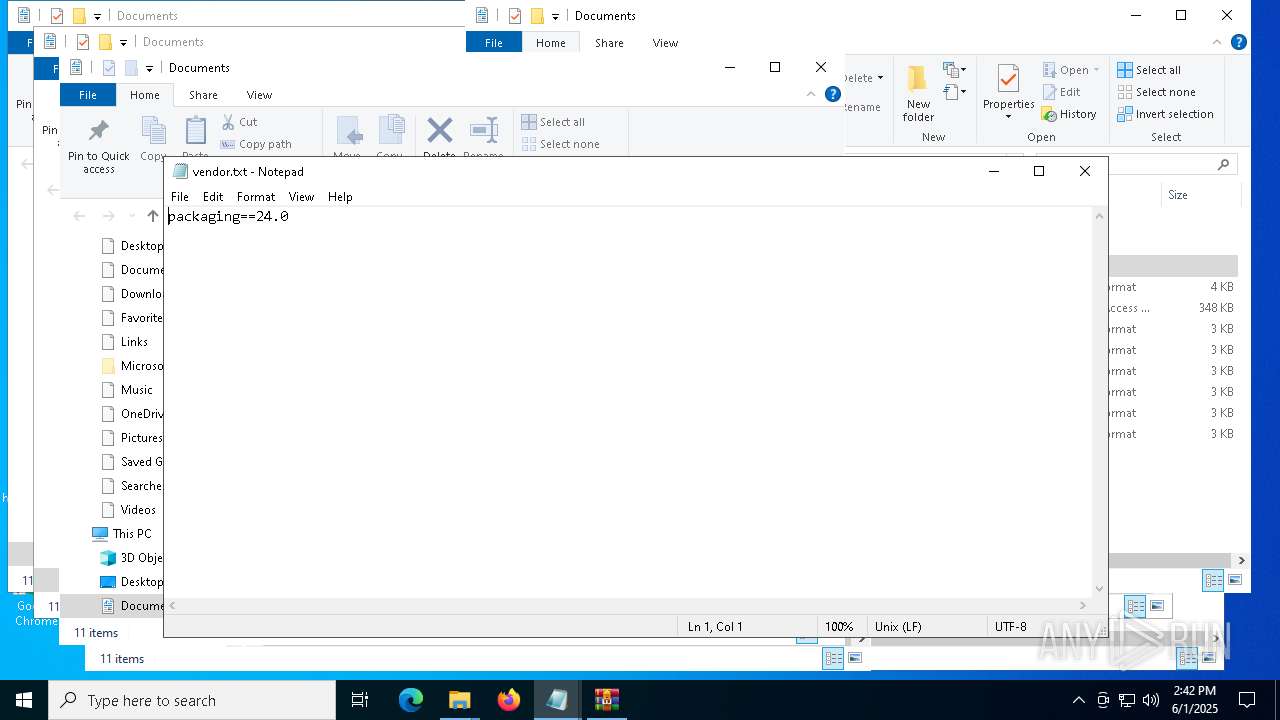
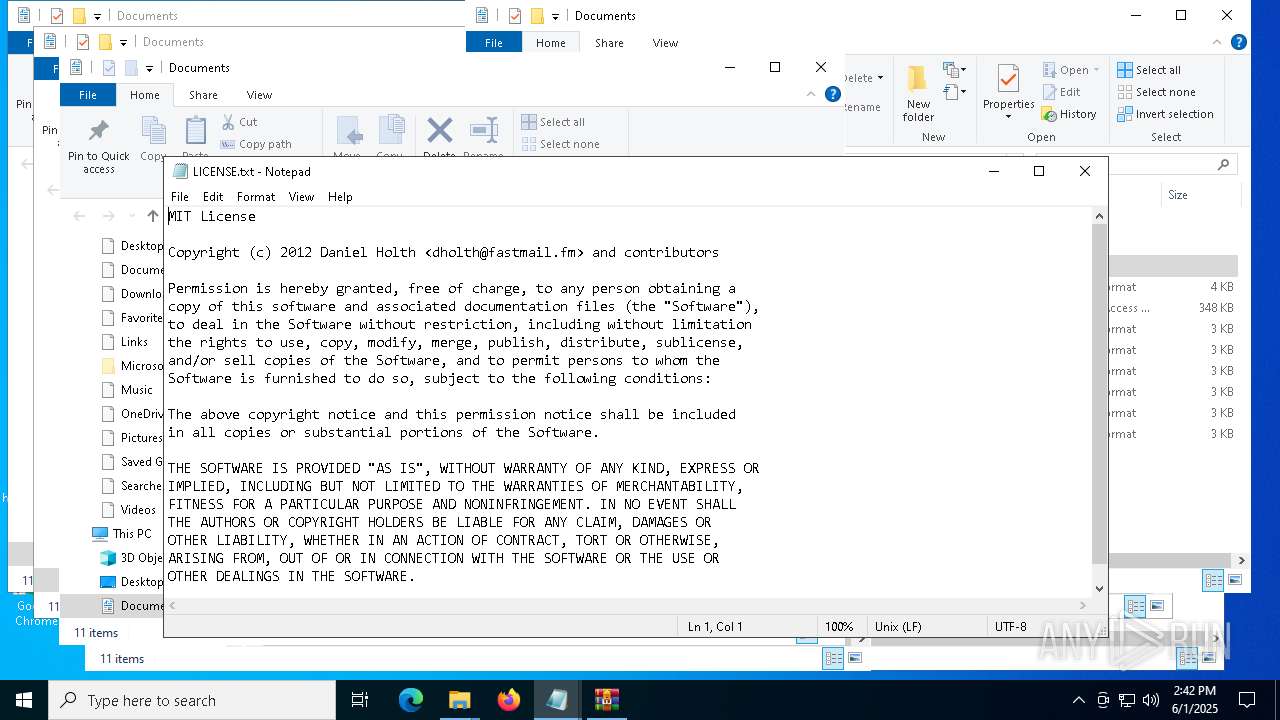
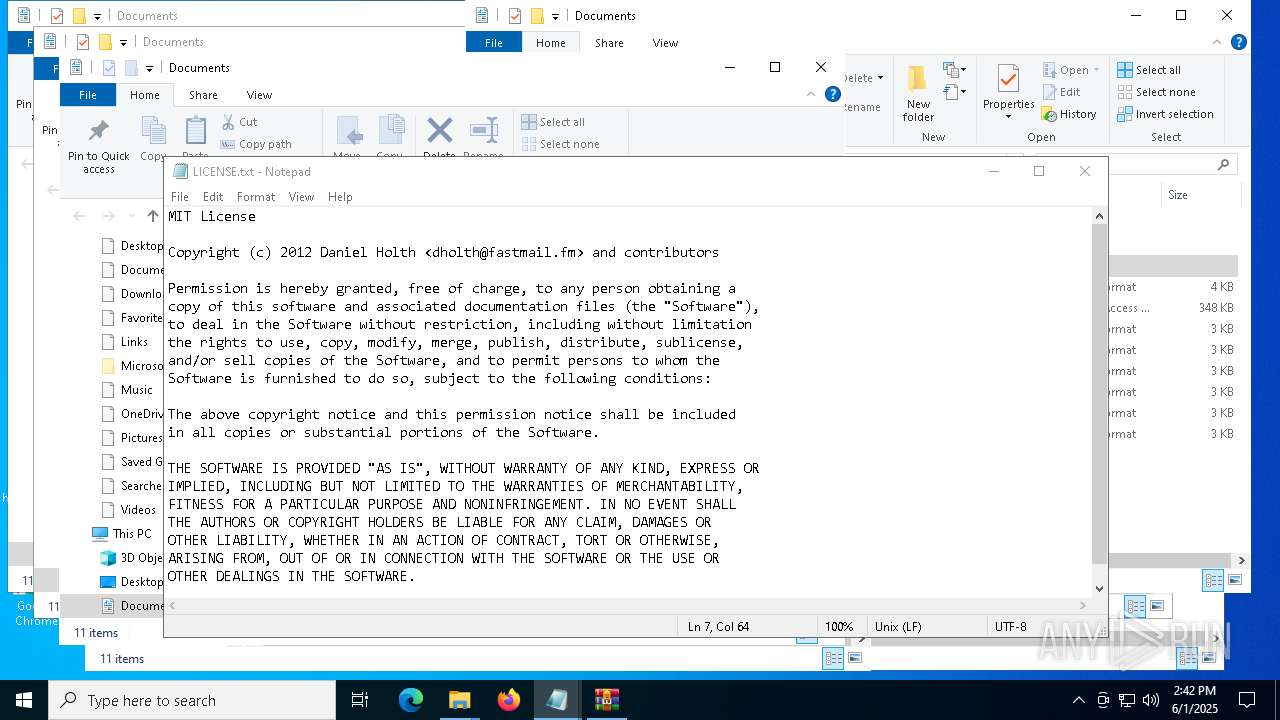
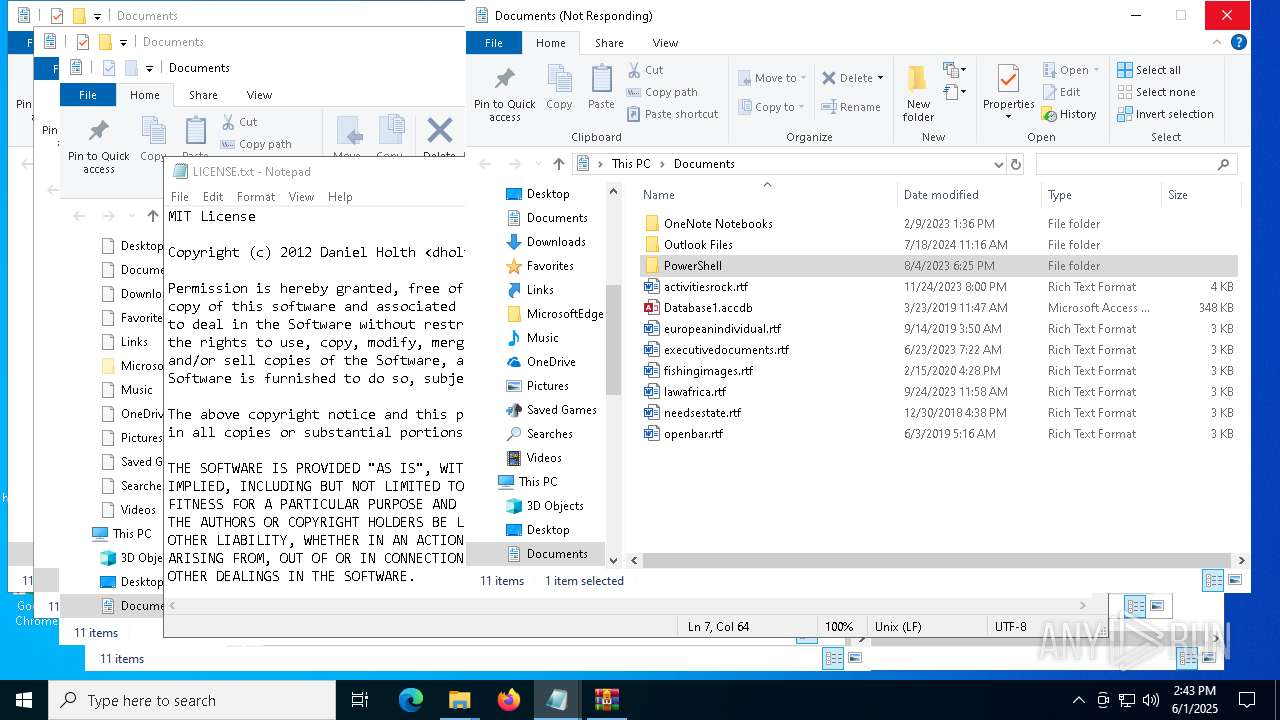
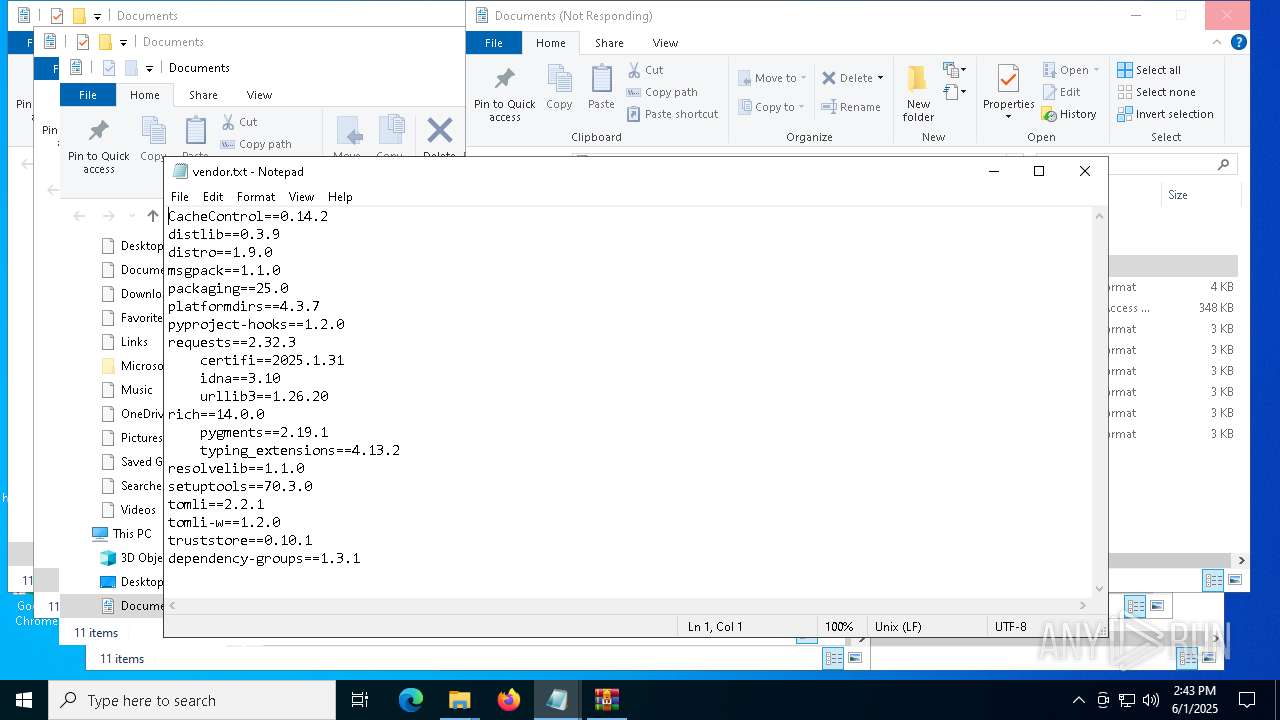
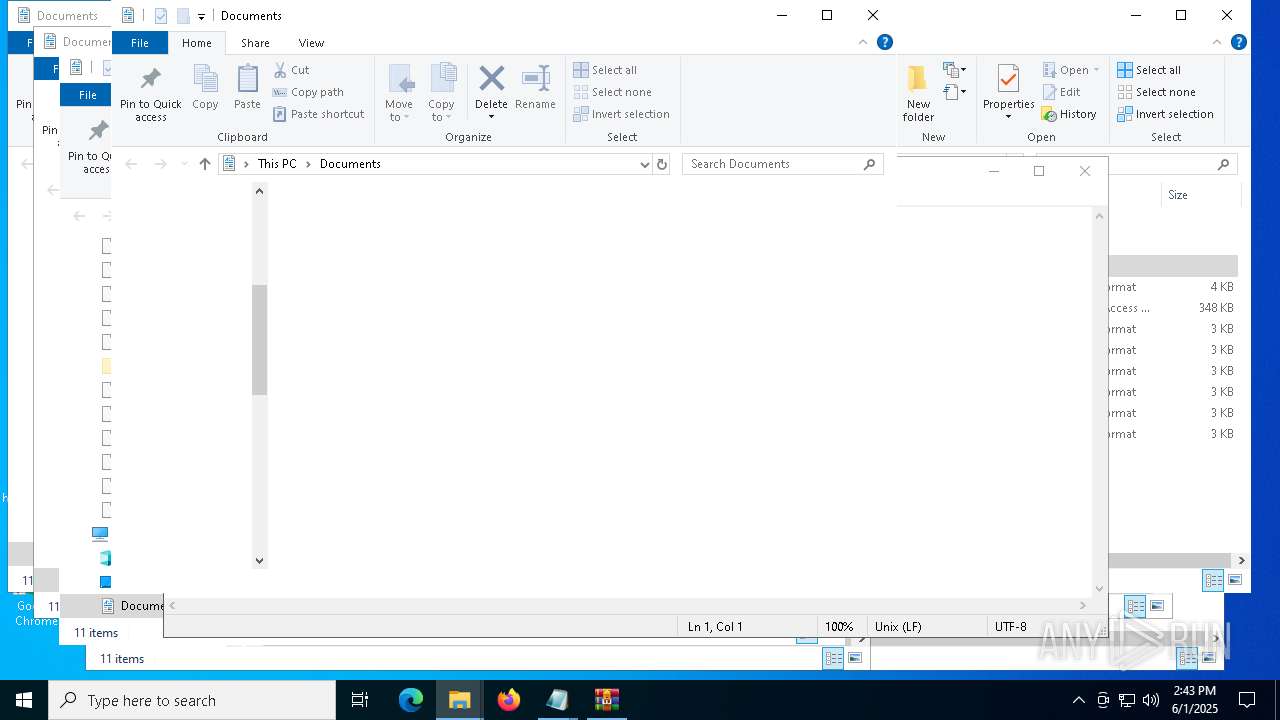
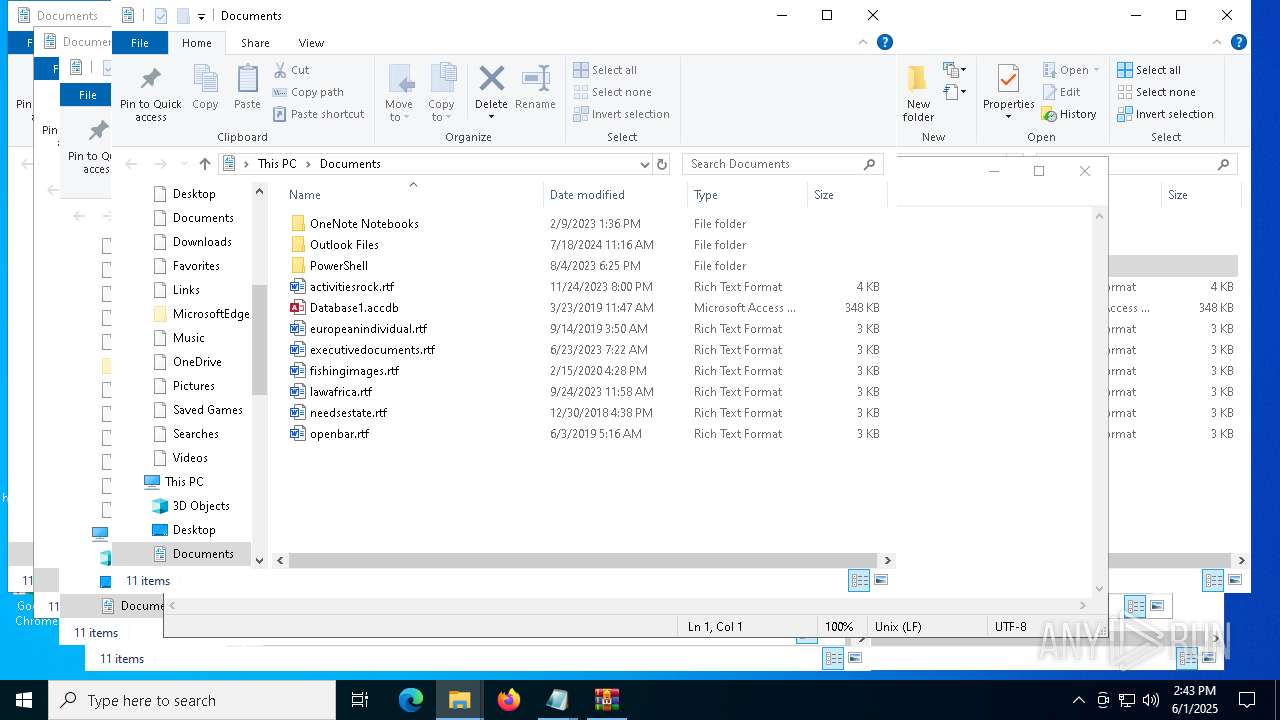
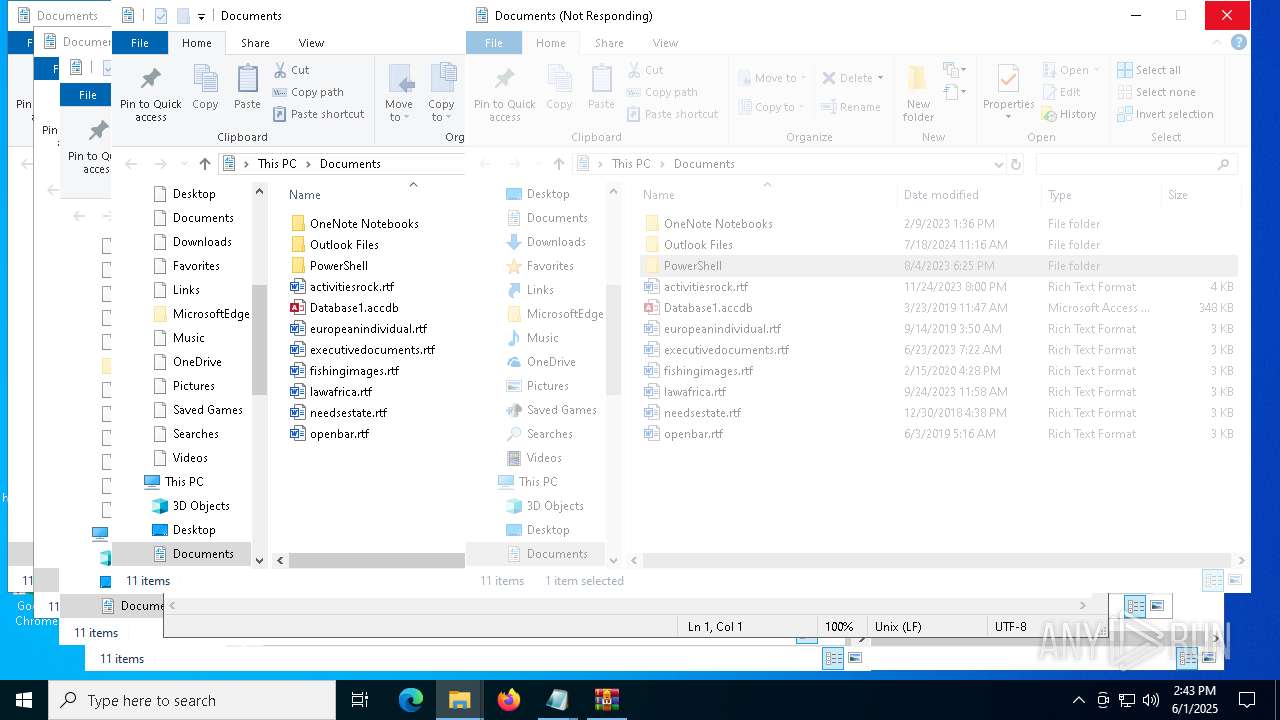
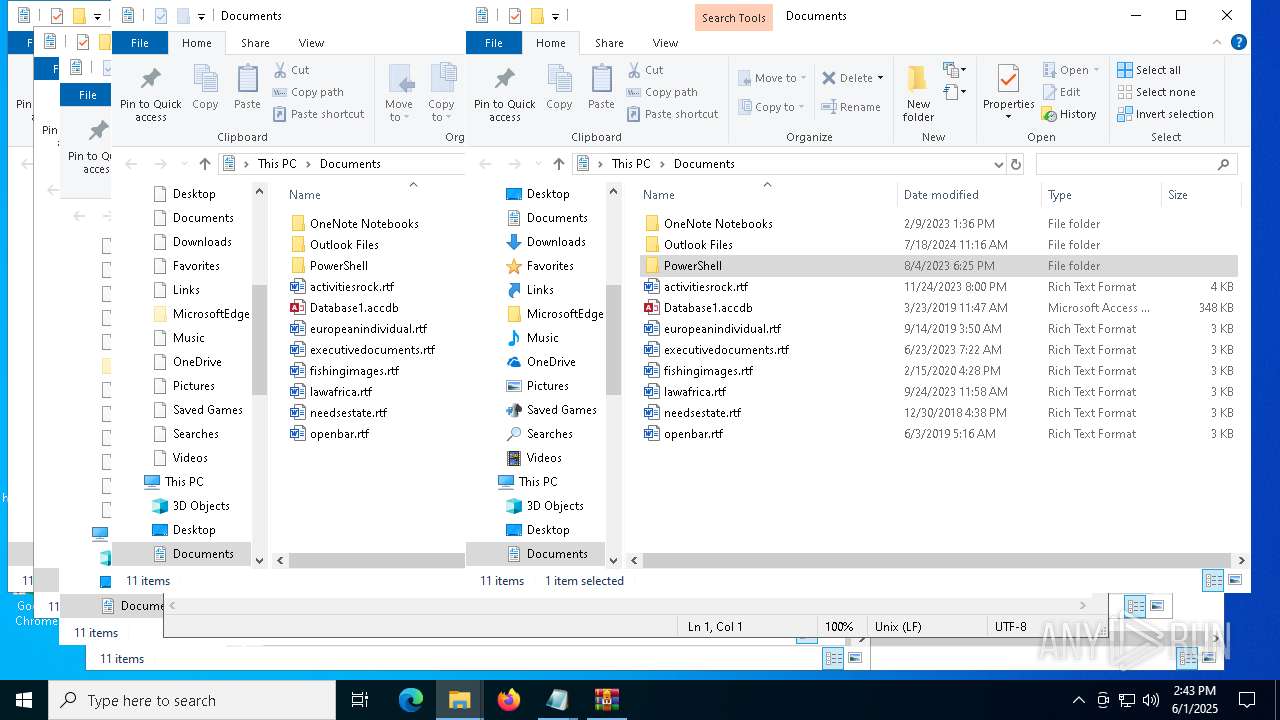
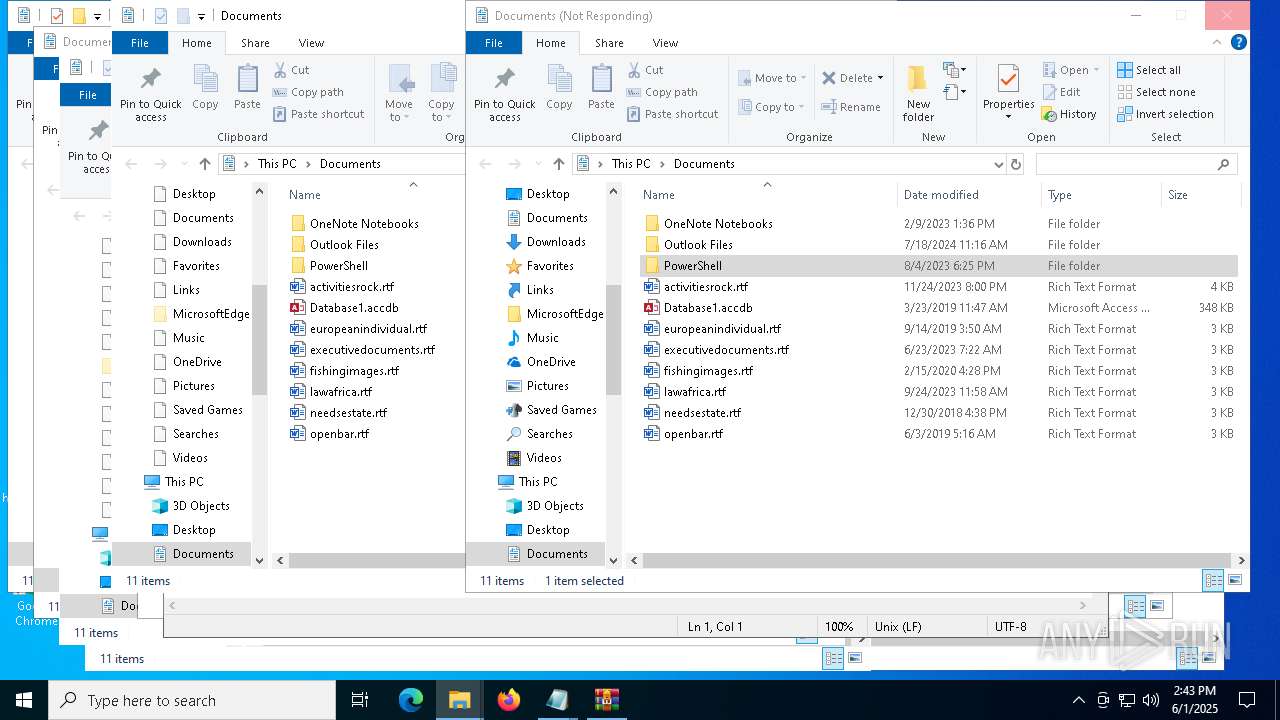
Manual execution by a user
- notepad.exe (PID: 8052)
- cmd.exe (PID: 7852)
- OpenWith.exe (PID: 8168)
- OpenWith.exe (PID: 4040)
- python.exe (PID: 772)
- pythonw.exe (PID: 456)
- notepad.exe (PID: 7976)
- notepad.exe (PID: 7964)
- OpenWith.exe (PID: 4020)
- notepad.exe (PID: 2392)
- notepad.exe (PID: 8088)
- notepad.exe (PID: 7824)
- notepad.exe (PID: 7748)
- notepad.exe (PID: 2616)
- WinRAR.exe (PID: 1696)
The sample compiled with english language support
- powershell.exe (PID: 5176)
- python.exe (PID: 856)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5176)
Reads security settings of Internet Explorer
- notepad.exe (PID: 8052)
- notepad.exe (PID: 2616)
Python executable
- python.exe (PID: 856)
- python.exe (PID: 772)
- pythonw.exe (PID: 456)
Checks supported languages
- python.exe (PID: 856)
Create files in a temporary directory
- python.exe (PID: 856)
Checks operating system version
- python.exe (PID: 856)
Reads the software policy settings
- python.exe (PID: 856)
Drops encrypted JS script (Microsoft Script Encoder)
- python.exe (PID: 856)
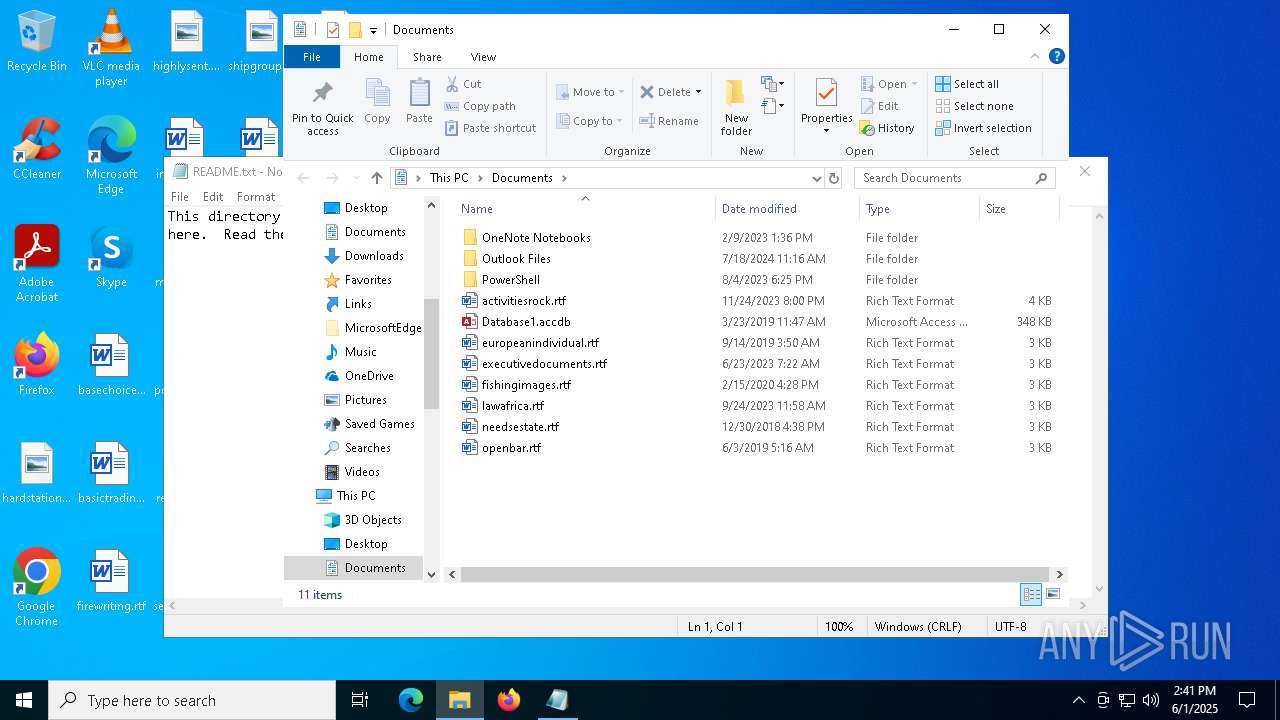
Creates files or folders in the user directory
- python.exe (PID: 856)
Reads the computer name
- python.exe (PID: 856)
Reads the machine GUID from the registry
- python.exe (PID: 856)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4040)
- OpenWith.exe (PID: 8168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
150
Monitored processes
26
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Users\admin\Desktop\pythonw.exe" | C:\Users\admin\Desktop\pythonw.exe | — | explorer.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 3221225781 Version: 3.11.8 Modules
| |||||||||||||||
| 660 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 772 | "C:\Users\admin\Desktop\python.exe" | C:\Users\admin\Desktop\python.exe | — | explorer.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 3221225781 Version: 3.11.8 Modules
| |||||||||||||||
| 856 | "C:\Temp\PortablePython\python.exe" C:\\Temp\PortablePython\get-pip.py | C:\Temp\PortablePython\python.exe | powershell.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Version: 3.11.8 Modules
| |||||||||||||||
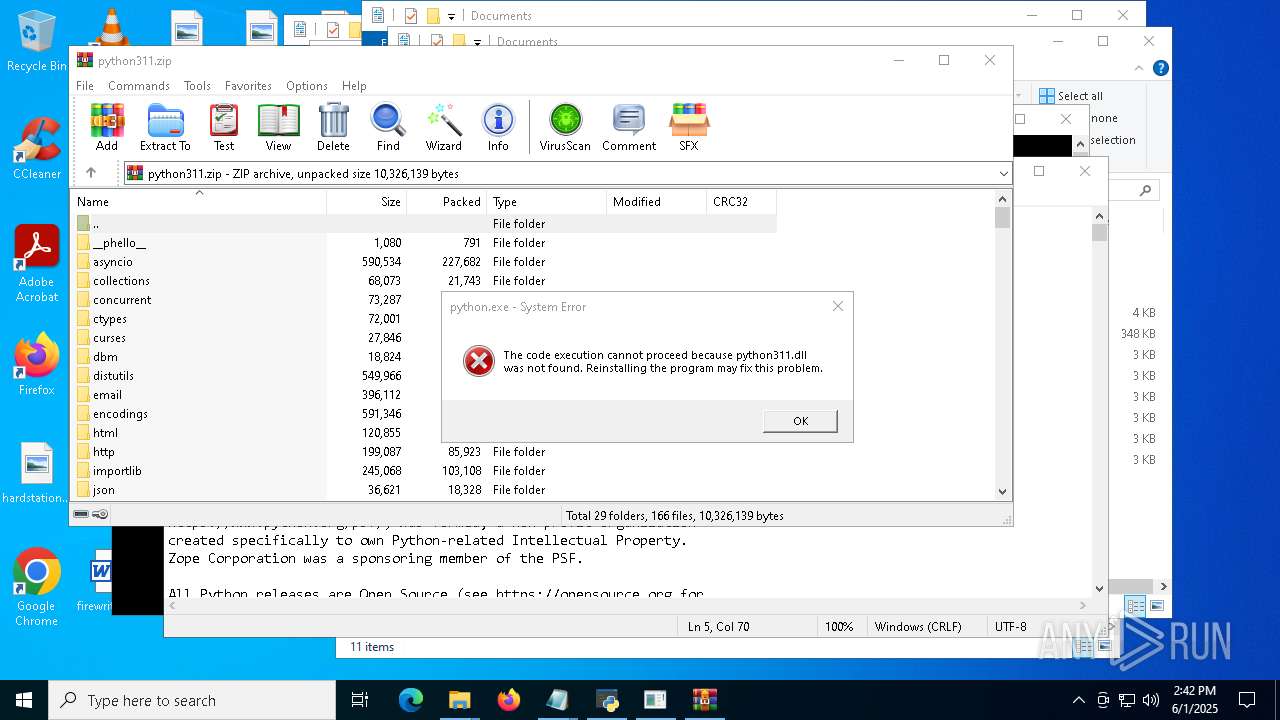
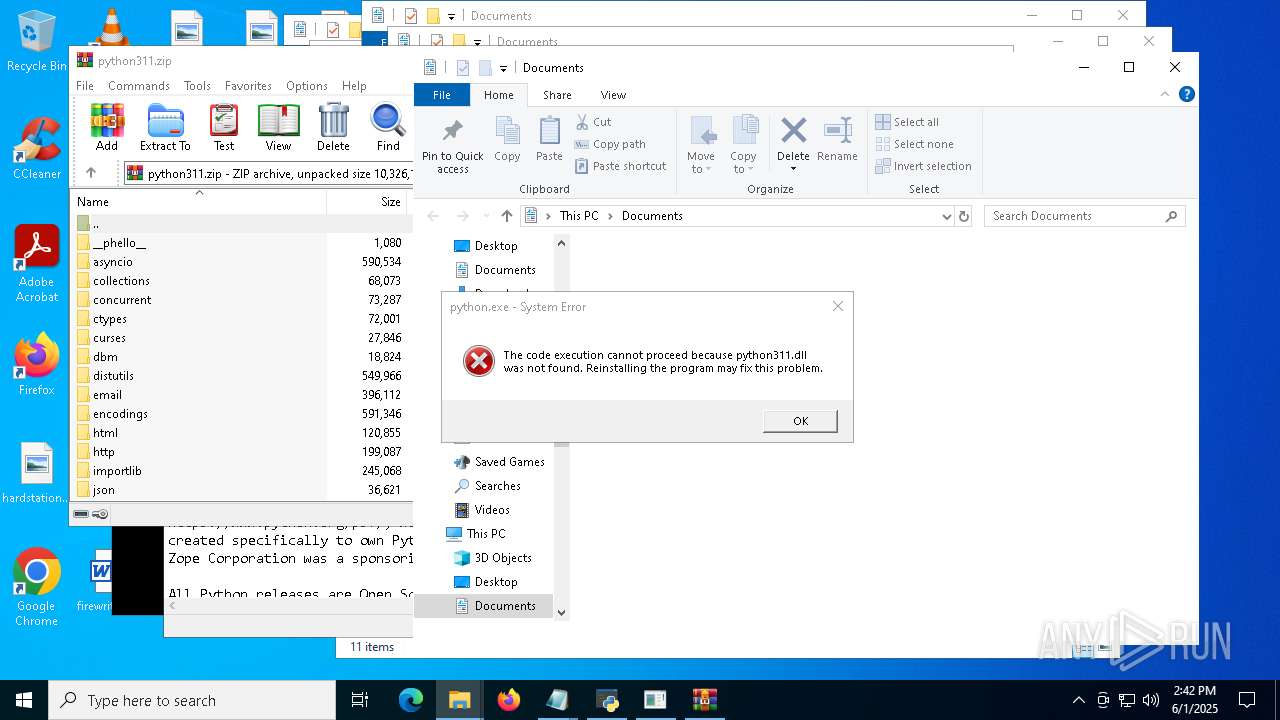
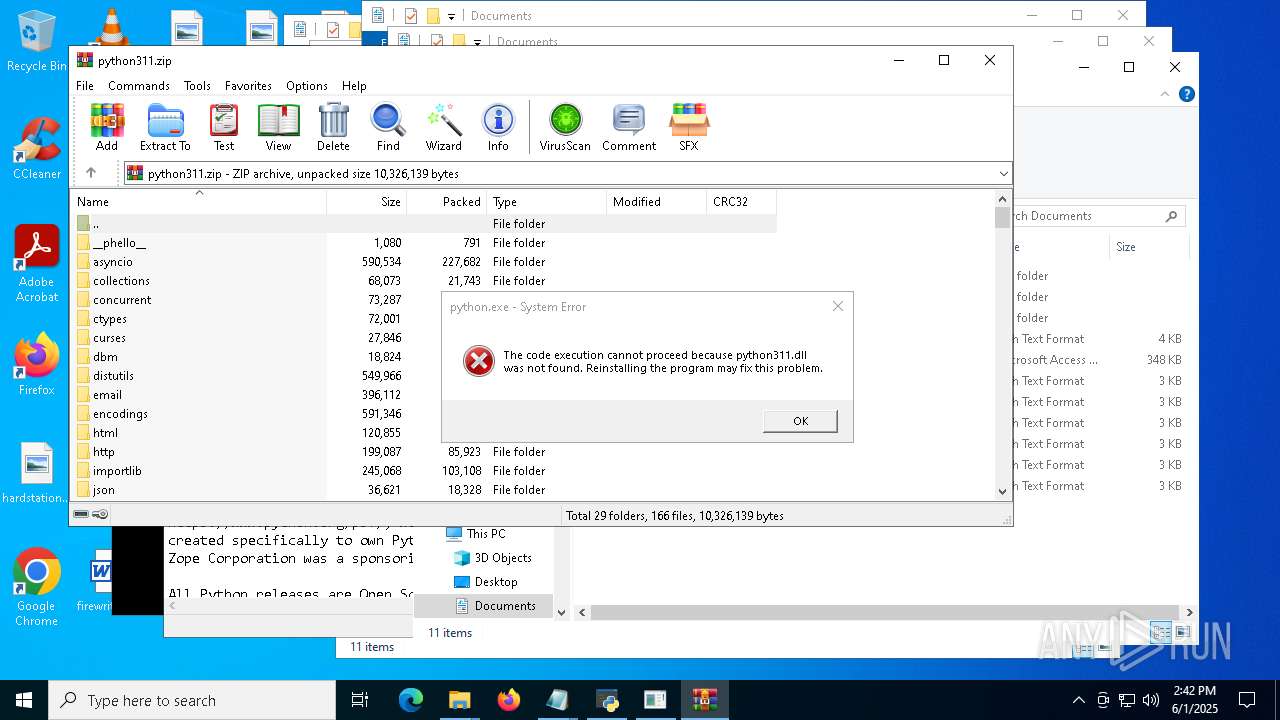
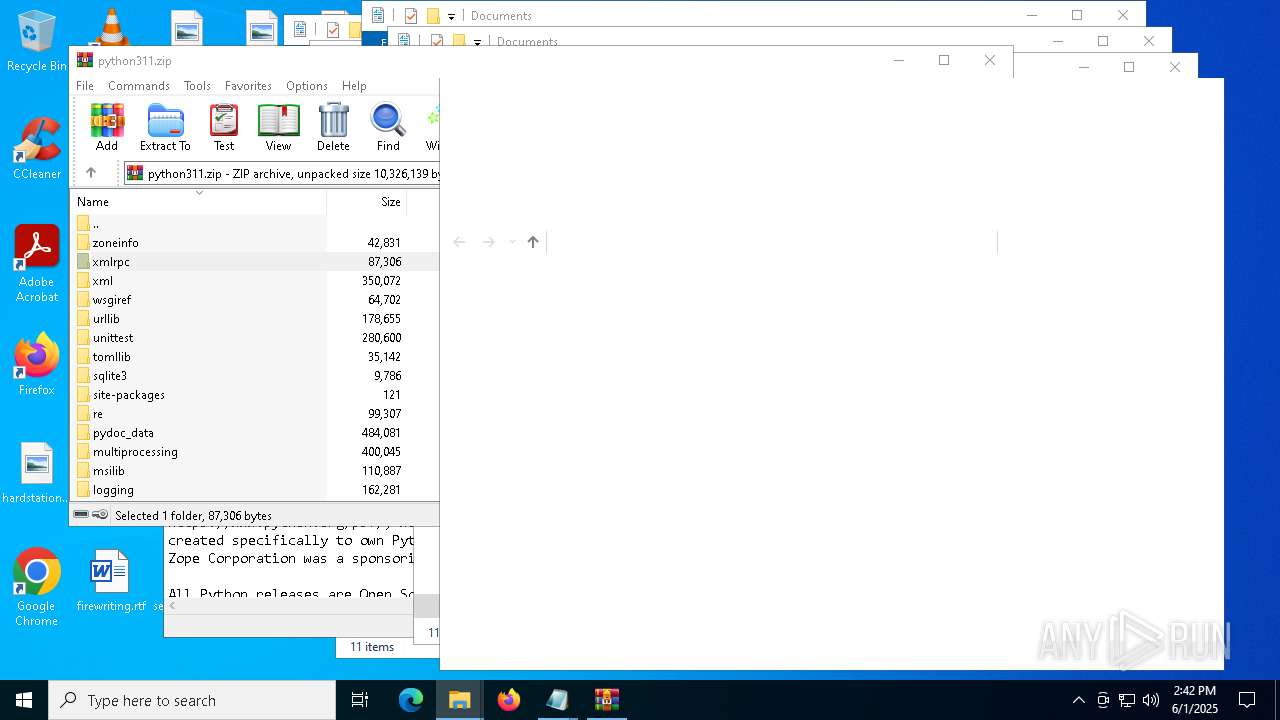
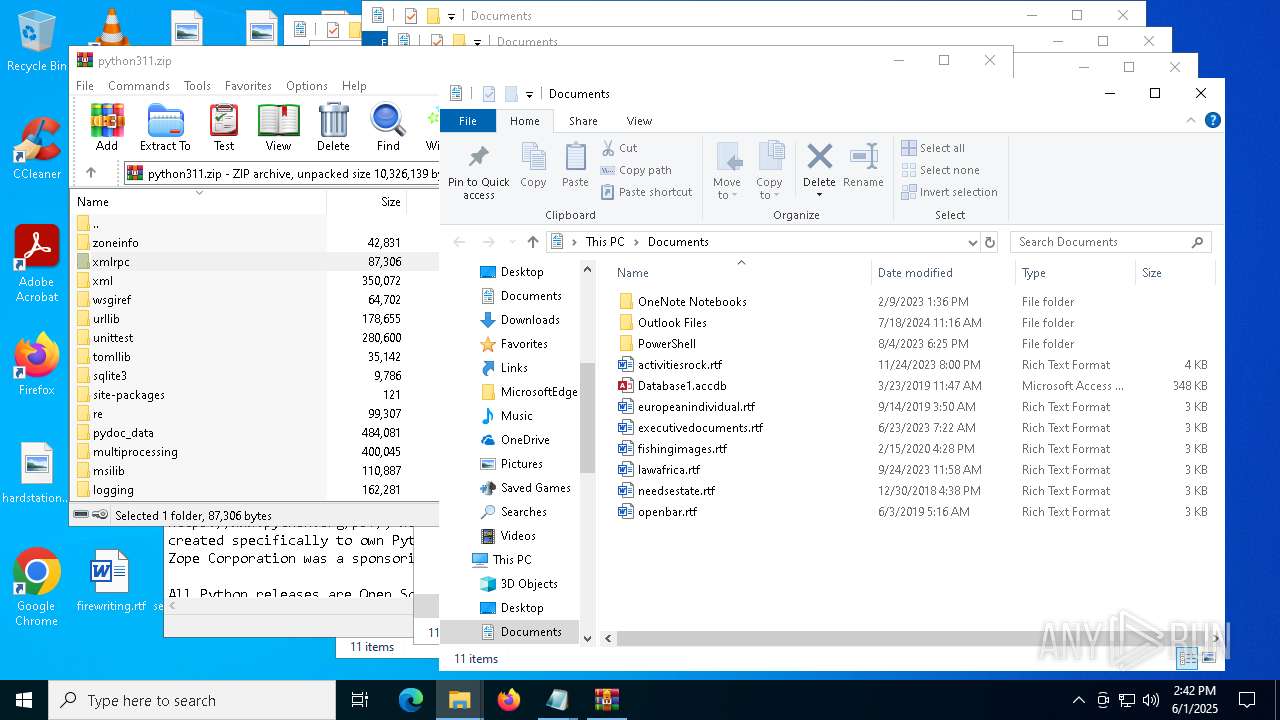
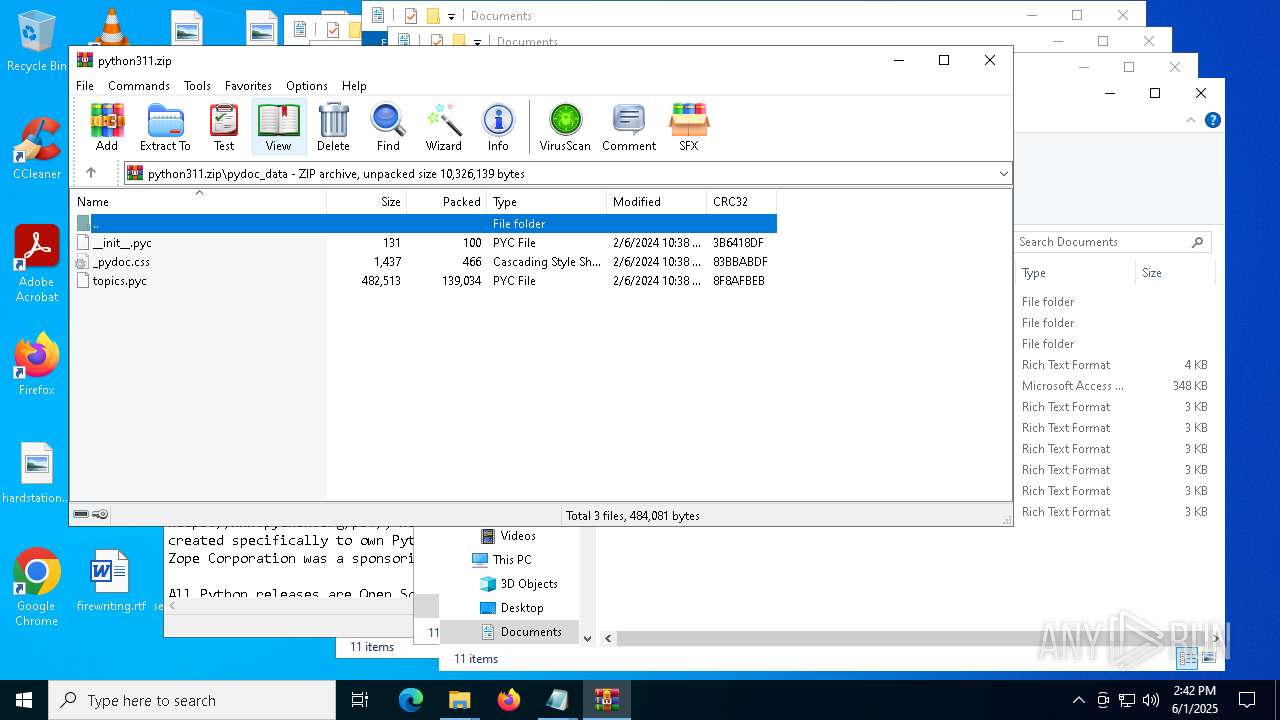
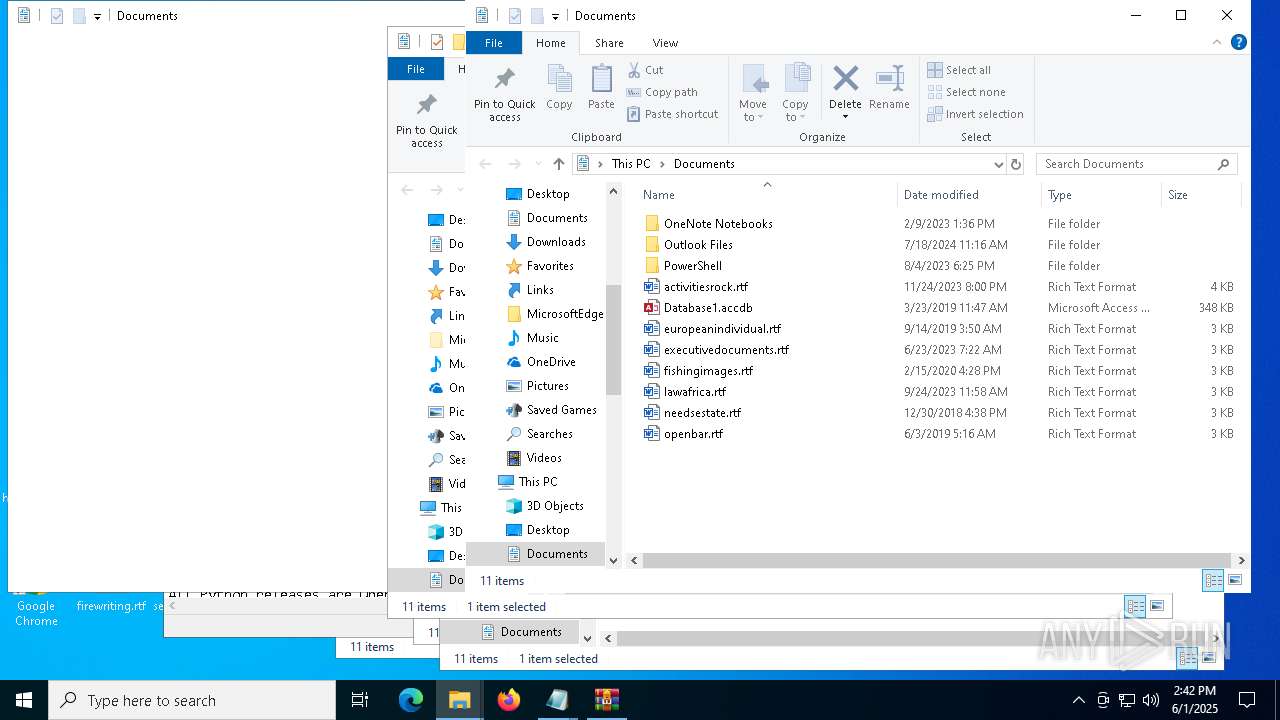
| 1696 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\python311.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\entry_points.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\LICENSE.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | "C:\WINDOWS\System32\WScript.exe" C:\Users\admin\Desktop\01062025_1434_13.vbs | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
22 846
Read events
22 836
Write events
10
Delete events
0
Modification events
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\python311.zip | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 0 | |||
Executable files
44
Suspicious files
1 061
Text files
946
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5176 | powershell.exe | C:\Temp\PortablePython\python.exe | executable | |
MD5:AF3E610BE9DCBF04D79C40C328316F81 | SHA256:01FD1819096D112696BD2152068C1195C9BD4F57B6AB776EDDD98D66D44B8259 | |||
| 5176 | powershell.exe | C:\Temp\PortablePython\python3.dll | executable | |
MD5:35DA4143951C5354262A28DEE569B7B2 | SHA256:920350A7C24C46339754E38D0DB34AB558E891DA0B3A389D5230A0D379BEE802 | |||
| 7376 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2x0rj1jx.1uq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5176 | powershell.exe | C:\Users\admin\AppData\Local\Temp\python-embed.zip | compressed | |
MD5:9199879FBAD4884ED93DDF77E8764920 | SHA256:6347068CA56BF4DD6319F7EF5695F5A03F1ADE3E9AA2D6A095AB27FAA77A1290 | |||
| 5176 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wgp24zyg.jip.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5176 | powershell.exe | C:\Temp\PortablePython\pythonw.exe | executable | |
MD5:837DD66E580DDC9B5DCC191156A202C2 | SHA256:E65ECC6B135F8C2269A2163F5C906376F2FEA3B61571D312D779F36F772CEAC1 | |||
| 5176 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_k5qflizk.xfq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7376 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gqvo3fjb.tce.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5176 | powershell.exe | C:\Temp\PortablePython\pyexpat.pyd | executable | |
MD5:D7ECC2746314FEC5CA46B64C964EA93E | SHA256:58B95F03A2D7EC49F5260E3E874D2B9FB76E95ECC80537E27ABEF0C74D03CB00 | |||
| 5176 | powershell.exe | C:\Temp\PortablePython\select.pyd | executable | |
MD5:E07AE2F7F28305B81ADFD256716AE8C6 | SHA256:FB06AC13F8B444C3F7AE5D2AF15710A4E60A126C3C61A1F1E1683F05F685626C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
54
DNS requests
21
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7576 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7576 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7576 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7576 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 20.3.187.198:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
— | — | POST | 200 | 20.190.159.73:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.73:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | POST | 200 | 40.126.32.136:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | POST | 200 | 40.126.32.136:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7552 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1056 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7376 | powershell.exe | 104.21.15.124:443 | duwesfm.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
duwesfm.com |
| unknown |
ifconfig.me |
| shared |
www.python.org |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Lookup Domain (ifconfig .me) |
5176 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5176 | powershell.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ifconfig .me) |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5176 | powershell.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Hosting Service Domain Domain in DNS Lookup (files .pythonhosted .org) |
856 | python.exe | Misc activity | ET INFO Observed File Hosting Service Domain (files .pythonhosted .org in TLS SNI) |