| File name: | Master.bat |
| Full analysis: | https://app.any.run/tasks/94e647d8-f713-4fea-9f95-689ee39416f7 |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | April 28, 2025, 11:44:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 5AA37CF43F4540288AE57E772A5ED41C |
| SHA1: | 469F03951E98ACF49FD6DA9B5760EB4C546CC1F2 |
| SHA256: | 6D200ED3F5BA7C83464E7819B45FFED8615490636DAC4AE75AA4408692EE0BD1 |
| SSDEEP: | 98304:Oyi35Ljc9Lsv3cV80dZ/dDZij4gtRRwmEvcN/fH8eLErT88Kg7GLMojy2S7EFcPy:G0T90/dkW |
MALICIOUS
DCRAT mutex has been found
- webCrt.exe (PID: 6108)
- wininit.exe (PID: 4188)
- webCrt.exe (PID: 968)
- fontdrvhost.exe (PID: 4380)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 6132)
Changes the autorun value in the registry
- webCrt.exe (PID: 6108)
- WinLocker.exe (PID: 6584)
DCRAT has been detected (YARA)
- wininit.exe (PID: 4188)
DARKCRYSTAL has been detected (SURICATA)
- wininit.exe (PID: 4188)
Connects to the CnC server
- wininit.exe (PID: 4188)
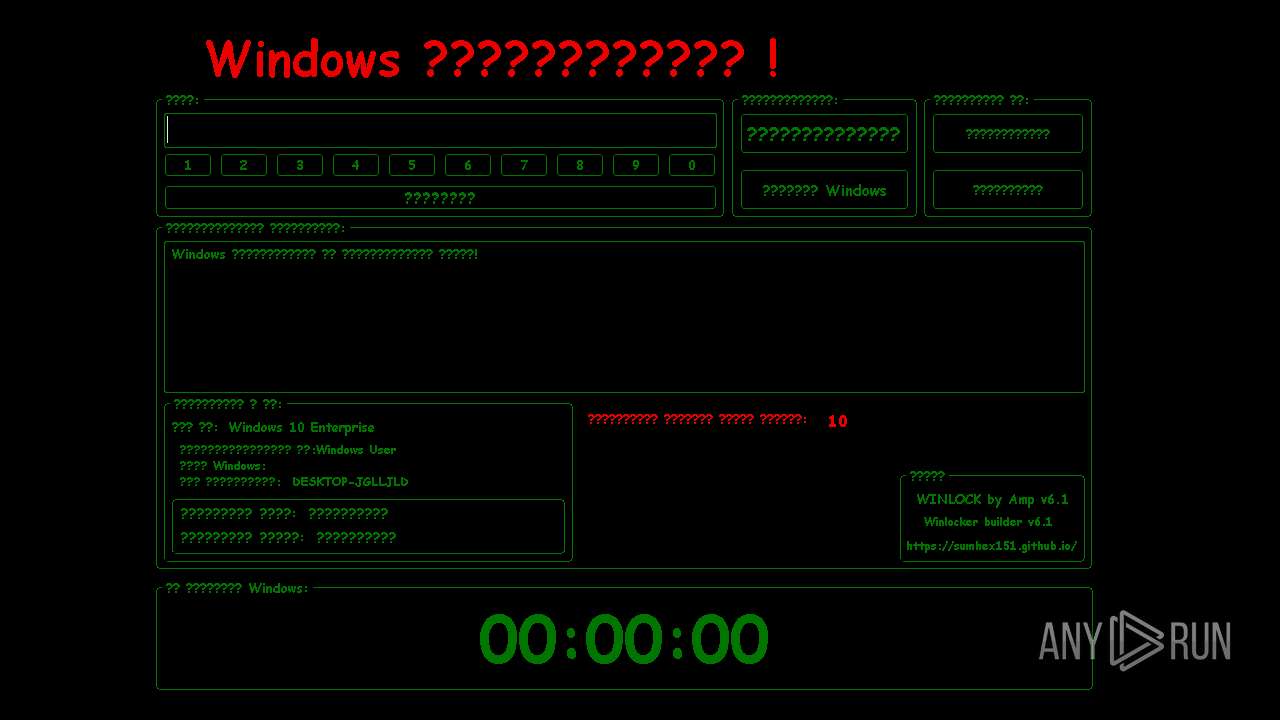
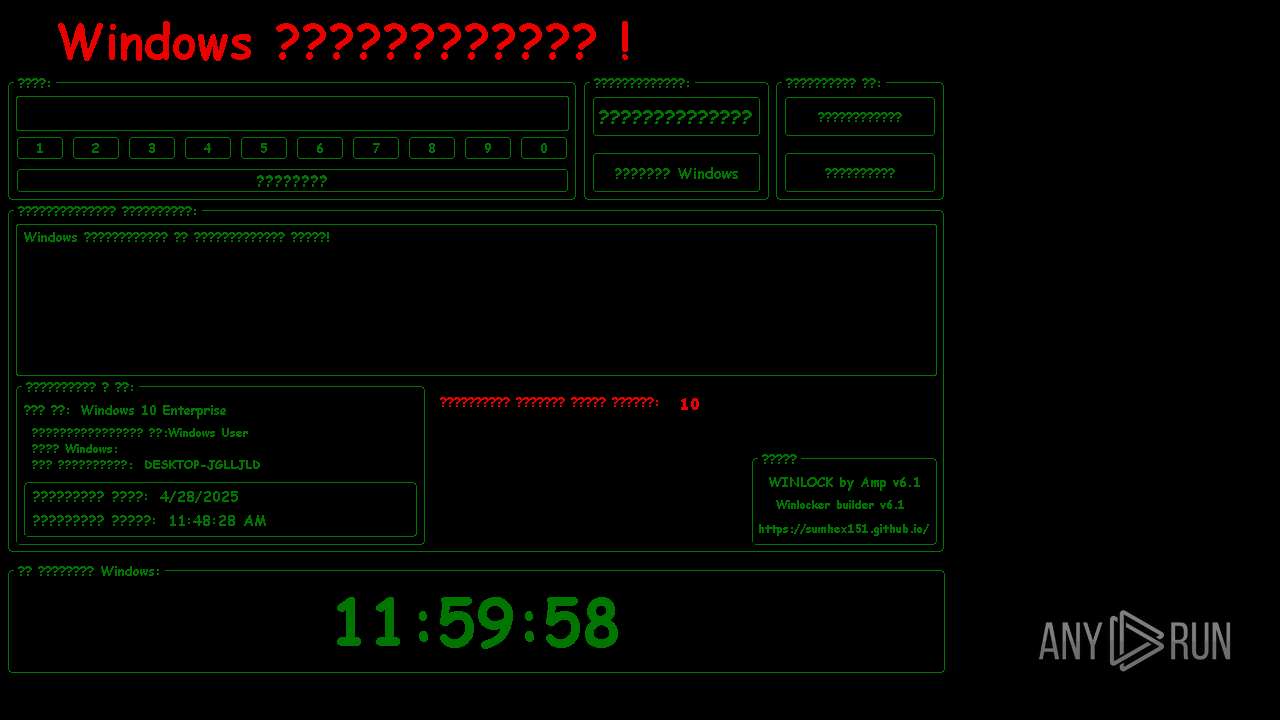
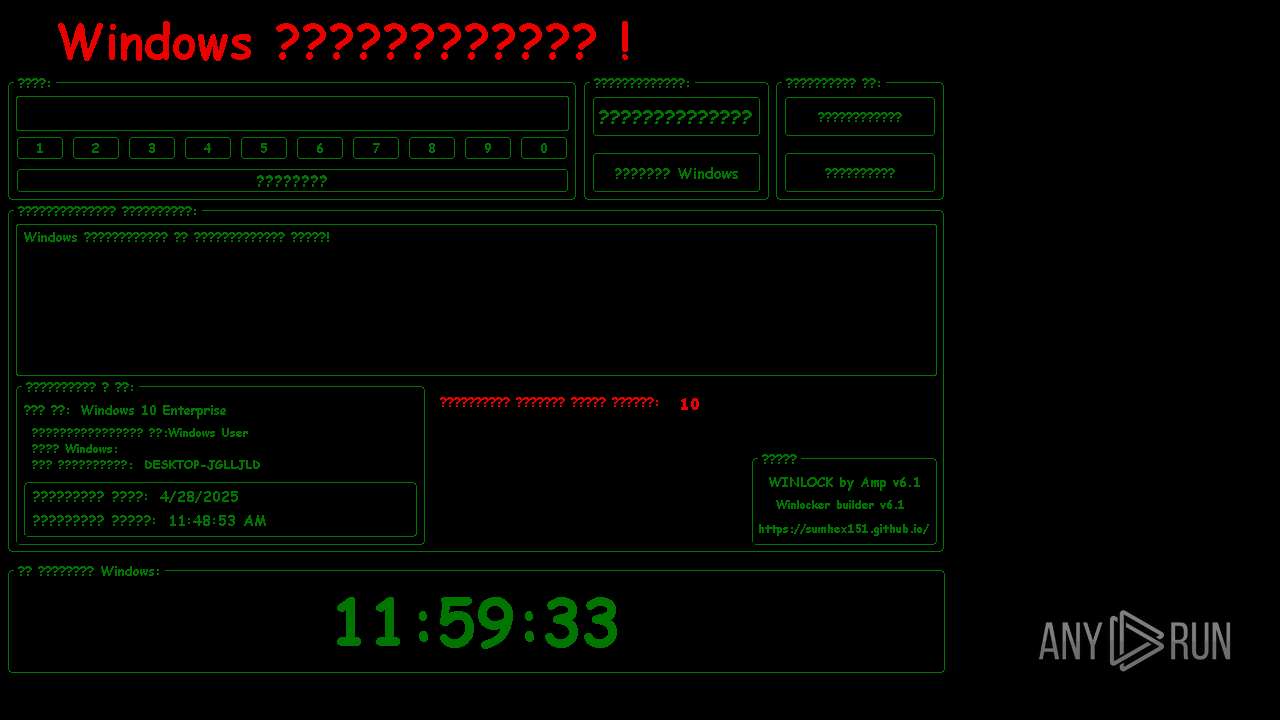
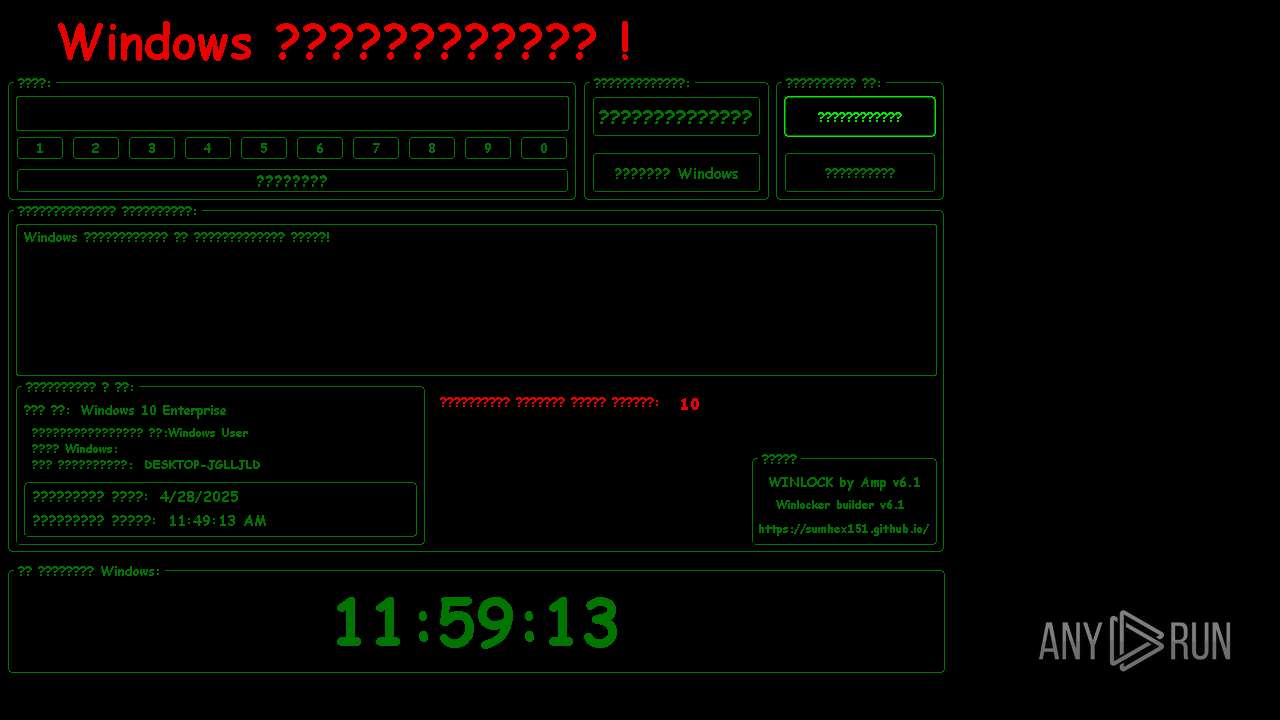
WINLOCKER mutex has been found
- WinLocker.exe (PID: 6584)
Changes image file execution options
- WinLocker.exe (PID: 6584)
Disables the LogOff the Start menu
- WinLocker.exe (PID: 6584)
Disables the Find the Start menu
- WinLocker.exe (PID: 6584)
UAC/LUA settings modification
- WinLocker.exe (PID: 6584)
Disables the Shutdown in the Start menu
- WinLocker.exe (PID: 6584)
WINLOCKER has been detected (YARA)
- WinLocker.exe (PID: 6584)
Disables the Run the Start menu
- WinLocker.exe (PID: 6584)
SUSPICIOUS
Executable content was dropped or overwritten
- Master.bat.exe (PID: 6048)
- webCrt.exe (PID: 6108)
- wininit.exe (PID: 4188)
Executing commands from a ".bat" file
- wscript.exe (PID: 6132)
- webCrt.exe (PID: 6108)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6132)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 6132)
- webCrt.exe (PID: 6108)
Reads security settings of Internet Explorer
- Master.bat.exe (PID: 6048)
- webCrt.exe (PID: 6108)
- wininit.exe (PID: 4188)
The executable file from the user directory is run by the CMD process
- webCrt.exe (PID: 6108)
Executed via WMI
- schtasks.exe (PID: 5260)
- schtasks.exe (PID: 6592)
- schtasks.exe (PID: 2236)
- schtasks.exe (PID: 1280)
- schtasks.exe (PID: 720)
- schtasks.exe (PID: 6824)
- schtasks.exe (PID: 1452)
- schtasks.exe (PID: 1240)
- schtasks.exe (PID: 7152)
- schtasks.exe (PID: 7036)
- schtasks.exe (PID: 5720)
- schtasks.exe (PID: 4172)
- schtasks.exe (PID: 1056)
- schtasks.exe (PID: 5508)
- schtasks.exe (PID: 920)
- schtasks.exe (PID: 6272)
- schtasks.exe (PID: 6516)
- schtasks.exe (PID: 2040)
The process creates files with name similar to system file names
- webCrt.exe (PID: 6108)
Likely accesses (executes) a file from the Public directory
- schtasks.exe (PID: 5260)
- schtasks.exe (PID: 6592)
- schtasks.exe (PID: 2040)
- schtasks.exe (PID: 2236)
- schtasks.exe (PID: 720)
- schtasks.exe (PID: 1280)
- fontdrvhost.exe (PID: 4380)
Process drops legitimate windows executable
- webCrt.exe (PID: 6108)
Reads the date of Windows installation
- webCrt.exe (PID: 6108)
- wininit.exe (PID: 4188)
Starts application with an unusual extension
- cmd.exe (PID: 2096)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 2096)
There is functionality for taking screenshot (YARA)
- wininit.exe (PID: 4188)
- WinLocker.exe (PID: 6584)
The process executes via Task Scheduler
- webCrt.exe (PID: 968)
- fontdrvhost.exe (PID: 4380)
INFO
Reads the computer name
- Master.bat.exe (PID: 6048)
- webCrt.exe (PID: 6108)
- wininit.exe (PID: 4188)
- WinLocker.exe (PID: 6584)
- webCrt.exe (PID: 968)
- fontdrvhost.exe (PID: 4380)
Drops encrypted VBS script (Microsoft Script Encoder)
- Master.bat.exe (PID: 6048)
Process checks computer location settings
- Master.bat.exe (PID: 6048)
- webCrt.exe (PID: 6108)
- wininit.exe (PID: 4188)
Checks supported languages
- webCrt.exe (PID: 6108)
- csc.exe (PID: 5892)
- cvtres.exe (PID: 3240)
- Master.bat.exe (PID: 6048)
- chcp.com (PID: 1096)
- WinLocker.exe (PID: 6584)
- webCrt.exe (PID: 968)
- wininit.exe (PID: 4188)
- fontdrvhost.exe (PID: 4380)
Reads the machine GUID from the registry
- webCrt.exe (PID: 6108)
- csc.exe (PID: 5892)
- wininit.exe (PID: 4188)
- fontdrvhost.exe (PID: 4380)
- webCrt.exe (PID: 968)
Creates files in the program directory
- webCrt.exe (PID: 6108)
Reads Environment values
- webCrt.exe (PID: 6108)
- wininit.exe (PID: 4188)
- webCrt.exe (PID: 968)
- fontdrvhost.exe (PID: 4380)
Failed to create an executable file in Windows directory
- webCrt.exe (PID: 6108)
Creates files or folders in the user directory
- Master.bat.exe (PID: 6048)
- webCrt.exe (PID: 6108)
- csc.exe (PID: 5892)
Create files in a temporary directory
- webCrt.exe (PID: 6108)
- cvtres.exe (PID: 3240)
The sample compiled with english language support
- webCrt.exe (PID: 6108)
Changes the display of characters in the console
- cmd.exe (PID: 2096)
.NET Reactor protector has been detected
- wininit.exe (PID: 4188)
Disables trace logs
- wininit.exe (PID: 4188)
Found Base64 encoded reference to WMI classes (YARA)
- wininit.exe (PID: 4188)
Found Base64 encoded reference to AntiVirus WMI classes (YARA)
- wininit.exe (PID: 4188)
Potential library load (Base64 Encoded 'LoadLibrary')
- wininit.exe (PID: 4188)
Checks proxy server information
- slui.exe (PID: 1388)
- wininit.exe (PID: 4188)
Reads the software policy settings
- slui.exe (PID: 5972)
- slui.exe (PID: 1388)
Compiled with Borland Delphi (YARA)
- WinLocker.exe (PID: 6584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DcRat
(PID) Process(4188) wininit.exe
C2 (1)http://mreblan148.temp.swtest.ru/index
Options
Version5.0.1
Plugins (10)TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDANzW72QAAAAAAAAAAOAAAiELAQgAAH4AAAAGAAAAAAAAbpwAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAA9UcBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAAbY72QAAAAAAAAAAOAAAiELAQgAALwAAAAGAAAAAAAA/tkAAAAgAAAA4AAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAgAQAAAgAA32UBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAPze72QAAAAAAAAAAOAAAiELAQgAAJQAAAAGAAAAAAAAPrIAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAA5AwBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAHbb72QAAAAAAAAAAOAAAiELAQgAAIAAAAAGAAAAAAAAvp4AAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAAzVsBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMIE8GQAAAAAAAAAAOAAAiELAQgAAHwAAAAGAAAAAAAArpoAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAAqtoAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAOjQ72QAAAAAAAAAAOAAAiELAQgAAHYAAAAGAAAAAAAAbpQAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAACOMAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAG7c72QAAAAAAAAAAOAAAiELAQgAAJQAAAAGAAAAAAAA7rIAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAAEroAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAGve72QAAAAAAAAAAOAAAiELAQgAAHoAAAAGAAAAAAAAvpkAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAA3OEAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAPHb72QAAAAAAAAAAOAAAiELAQgAAJoAAAAGAAAAAAAAzrgAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAA794AAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMvY72QAAAAAAAAAAOAAAiELAQgAAIYAAAAGAAAAAAAAHqUAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAAhvEAAAMAQIUA...
C2 (1)http://mreblan148.temp.swtest.ru/index
Options
Version5.0.1
Plugins (13)TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDANzW72QAAAAAAAAAAOAAAiELAQgAAH4AAAAGAAAAAAAAbpwAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAA9UcBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAAbY72QAAAAAAAAAAOAAAiELAQgAALwAAAAGAAAAAAAA/tkAAAAgAAAA4AAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAgAQAAAgAA32UBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAPze72QAAAAAAAAAAOAAAiELAQgAAJQAAAAGAAAAAAAAPrIAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAA5AwBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAAKX/2QAAAAAAAAAAOAAIiALAQgAAEYBAAAGAAAAAAAA7mUBAAAgAAAAgAEAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADAAQAAAgAAm0ACAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAHbb72QAAAAAAAAAAOAAAiELAQgAAIAAAAAGAAAAAAAAvp4AAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAAzVsBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMIE8GQAAAAAAAAAAOAAAiELAQgAAHwAAAAGAAAAAAAArpoAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAAqtoAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDALI7+mQAAAAAAAAAAOAAIiALAQgAAAgBAAAGAAAAAAAAricBAAAgAAAAQAEAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAACAAQAAAgAArNABAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAOjQ72QAAAAAAAAAAOAAAiELAQgAAHYAAAAGAAAAAAAAbpQAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAACOMAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAG7c72QAAAAAAAAAAOAAAiELAQgAAJQAAAAGAAAAAAAA7rIAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAAEroAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAGve72QAAAAAAAAAAOAAAiELAQgAAHoAAAAGAAAAAAAAvpkAAAAgAAAAoAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADgAAAAAgAA3OEAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMzf72QAAAAAAAAAAOAAIiALAQgAAAoBAAAGAAAAAAAALikBAAAgAAAAQAEAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAACAAQAAAgAAOPMBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAPHb72QAAAAAAAAAAOAAAiELAQgAAJoAAAAGAAAAAAAAzrgAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAA794AAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMvY72QAAAAAAAAAAOAAAiELAQgAAIYAAAAGAAAAAAAAHqUAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAAhvEAAAMAQIUA...
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 203776 |
| InitializedDataSize: | 261632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f530 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
172
Monitored processes
40
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | schtasks.exe /create /tn "fontdrvhostf" /sc MINUTE /mo 11 /tr "'C:\Users\Public\Downloads\fontdrvhost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | schtasks.exe /create /tn "wininit" /sc ONLOGON /tr "'C:\Users\All Users\Application Data\wininit.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | "C:\Users\admin\AppData\Roaming\chainportsurrogatecomponentcrt\webCrt.exe" | C:\Users\admin\AppData\Roaming\chainportsurrogatecomponentcrt\webCrt.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 1056 | schtasks.exe /create /tn "cmdc" /sc MINUTE /mo 9 /tr "'C:\Users\admin\Local Settings\cmd.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | schtasks.exe /create /tn "wininitw" /sc MINUTE /mo 8 /tr "'C:\Users\All Users\Application Data\wininit.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | schtasks.exe /create /tn "fontdrvhost" /sc ONLOGON /tr "'C:\Users\Public\Downloads\fontdrvhost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | schtasks.exe /create /tn "sluis" /sc MINUTE /mo 10 /tr "'C:\Windows\Temp\slui.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 357
Read events
7 306
Write events
51
Delete events
0
Modification events
| (PID) Process: | (6048) Master.bat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbe\OpenWithProgids |
| Operation: | write | Name: | VBEFile |
Value: | |||
| (PID) Process: | (6108) webCrt.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\7fbaaeade1e6e0af740b579149a60325b922aa58 |
| Operation: | write | Name: | 1648b1415af1ecc35ce5f08f13921c64460ad9f7 |
Value: H4sIAAAAAAAEAHWOwWoCQQyGX2XxXHyA3sp6tFSs4sF4iDPZNXQ2GWYyro/fFCkUrOSQ8OXP/+e46F8B9pVKBdi0c+IA8N7qT/sYBg7UO/ra6bbJkm60ePnvYKWzJMXoaFCxWK4XrfZHf2CJOvt6R1MGqKnxoxvGiQVgrQFT90lmLKPjMMVH7VtK3e+Ysz+BxirdCg0BZhYve5rgF3fhVtHB6BkXZMlarLZSdESjoFNWIbFQzB3p3Je74ekbb8PkwzMBAAA= | |||
| (PID) Process: | (6108) webCrt.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | OfficeClickToRun |
Value: "C:\Users\Public\Music\OfficeClickToRun.exe" | |||
| (PID) Process: | (6108) webCrt.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | fontdrvhost |
Value: "C:\Users\Public\Downloads\fontdrvhost.exe" | |||
| (PID) Process: | (6108) webCrt.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | slui |
Value: "C:\Windows\Temp\slui.exe" | |||
| (PID) Process: | (6108) webCrt.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | wininit |
Value: "C:\Users\All Users\Application Data\wininit.exe" | |||
| (PID) Process: | (6108) webCrt.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | webCrt |
Value: "C:\Users\admin\AppData\Roaming\chainportsurrogatecomponentcrt\webCrt.exe" | |||
| (PID) Process: | (6108) webCrt.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | cmd |
Value: "C:\Users\admin\Local Settings\cmd.exe" | |||
| (PID) Process: | (4188) wininit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wininit_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4188) wininit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wininit_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
38
Suspicious files
3
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6108 | webCrt.exe | C:\Users\admin\Desktop\MkfDGTaf.log | executable | |
MD5:F4B38D0F95B7E844DD288B441EBC9AAF | SHA256:AAB95596475CA74CEDE5BA50F642D92FA029F6F74F6FAEAE82A9A07285A5FB97 | |||
| 6048 | Master.bat.exe | C:\Users\admin\AppData\Roaming\chainportsurrogatecomponentcrt\webCrt.exe | executable | |
MD5:0D018401DF43D1A448FF5E157F827CDA | SHA256:3E3B6564B8F3F9BD8155480CAE1743164ACCA6E8EA8F3559E6A1D714BCFDE9D3 | |||
| 6108 | webCrt.exe | C:\Users\admin\Desktop\ewGIZpvu.log | executable | |
MD5:D8BF2A0481C0A17A634D066A711C12E9 | SHA256:2B93377EA087225820A9F8E4F331005A0C600D557242366F06E0C1EAE003D669 | |||
| 6108 | webCrt.exe | C:\Users\admin\Desktop\uGwfXcLO.log | executable | |
MD5:16B480082780CC1D8C23FB05468F64E7 | SHA256:7A080D8BD178EC02C7F39F7F941479074C450C4FDD8E963C993D2FB5537C7708 | |||
| 6048 | Master.bat.exe | C:\Users\admin\AppData\Roaming\chainportsurrogatecomponentcrt\212LUqDPPDeNJ.bat | text | |
MD5:F2FFA18C41C8362EE537C46C99414F4F | SHA256:E1A9FE9BC3AF4224BD13750A5A55098A6C3D2E8037B8D64F88248E93645E4CE3 | |||
| 6048 | Master.bat.exe | C:\Users\admin\AppData\Roaming\chainportsurrogatecomponentcrt\VhEqLNONk3HPr1s98E0HrxGHOviiq2kQ6ZtuiO57.vbe | binary | |
MD5:FE6AA22A0C09C2ECFE5EA22901B57FBB | SHA256:070760AAD8D71B8309677A02B36DD5C3EB46759FAE1FDD6E1019CE448269027D | |||
| 6108 | webCrt.exe | C:\Users\admin\Desktop\VTyTpwfN.log | executable | |
MD5:E9CE850DB4350471A62CC24ACB83E859 | SHA256:7C95D3B38114E7E4126CB63AADAF80085ED5461AB0868D2365DD6A18C946EA3A | |||
| 6108 | webCrt.exe | C:\Users\admin\Desktop\kpjiCVAj.log | executable | |
MD5:94DA5073CCC14DCF4766DF6781485937 | SHA256:B81B9FA9B7017BE34F62D30CB16BAAB33757F04CC94EF4D6459C9D3BC768FD18 | |||
| 6108 | webCrt.exe | C:\Users\admin\Desktop\DHWOWaKy.log | executable | |
MD5:9B25959D6CD6097C0EF36D2496876249 | SHA256:4DBA0293B2BA9478EC0738BAD92F0E56CB7CF800B0CA4FDA8261EE2C0C91E217 | |||
| 6108 | webCrt.exe | C:\Users\admin\Desktop\sTsXmOPQ.log | executable | |
MD5:2E116FC64103D0F0CF47890FD571561E | SHA256:25EEEA99DCA05BF7651264FA0C07E0E91D89E0DA401C387284E9BE9AFDF79625 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
307
TCP/UDP connections
33
DNS requests
18
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4188 | wininit.exe | POST | 200 | 77.222.61.179:80 | http://mreblan148.temp.swtest.ru/index.php | unknown | — | — | malicious |
6228 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4188 | wininit.exe | POST | 200 | 77.222.61.179:80 | http://mreblan148.temp.swtest.ru/index.php | unknown | — | — | malicious |
4188 | wininit.exe | POST | 200 | 77.222.61.179:80 | http://mreblan148.temp.swtest.ru/index.php | unknown | — | — | malicious |
6228 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4188 | wininit.exe | POST | 200 | 77.222.61.179:80 | http://mreblan148.temp.swtest.ru/index.php | unknown | — | — | malicious |
4188 | wininit.exe | POST | 200 | 77.222.61.179:80 | http://mreblan148.temp.swtest.ru/index.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.32.238.112:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
mreblan148.temp.swtest.ru |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET TA_ABUSED_SERVICES Commonly Abused Domain Service Domain in DNS Lookup (temp .swtest .ru) |
4188 | wininit.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
4188 | wininit.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |