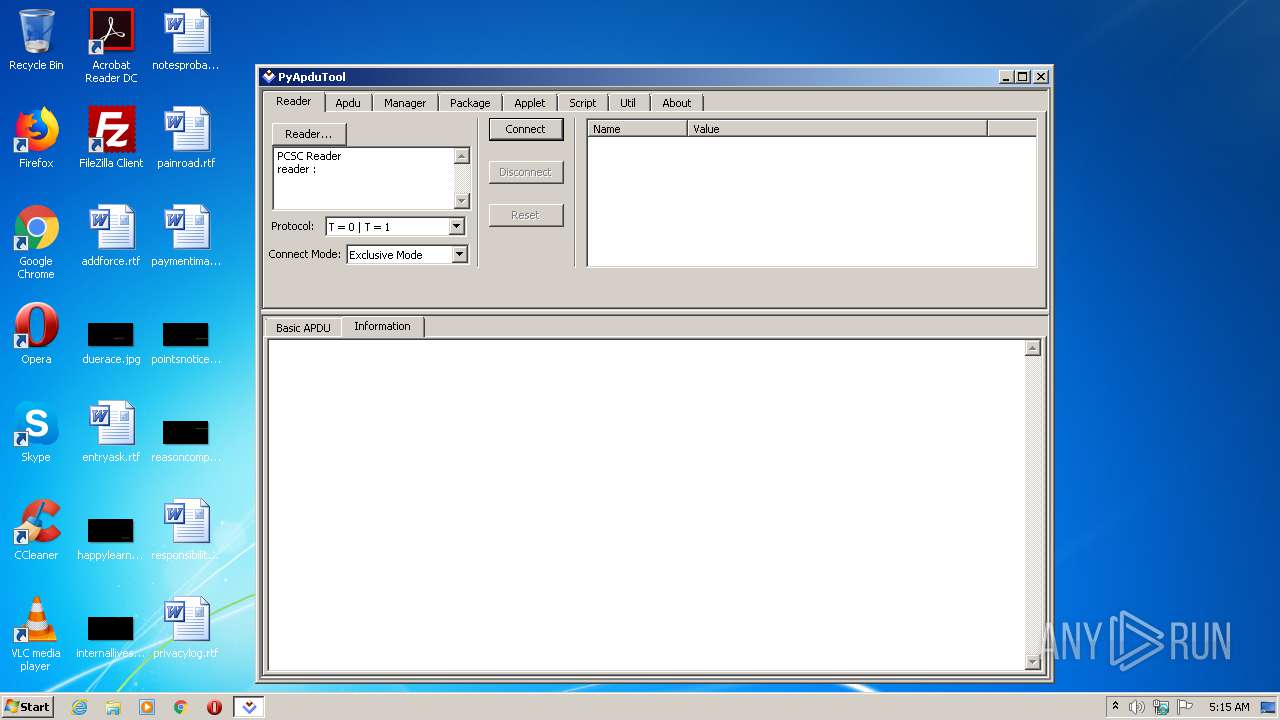
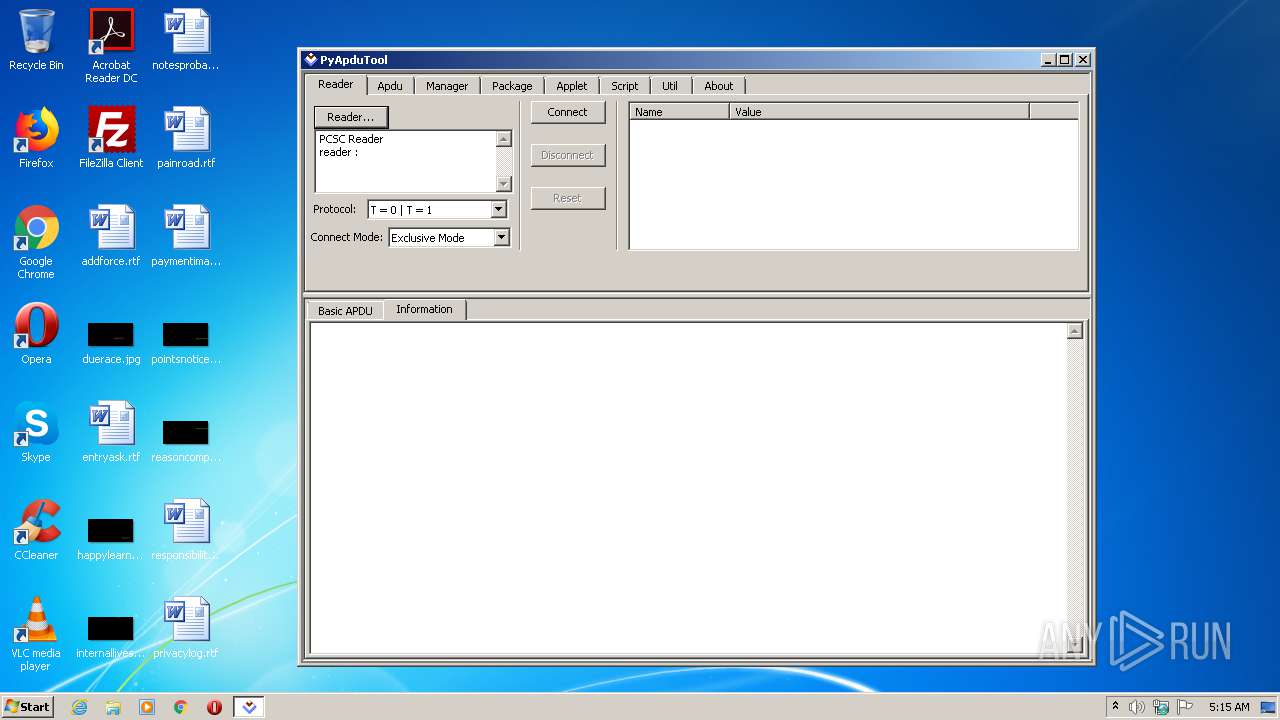
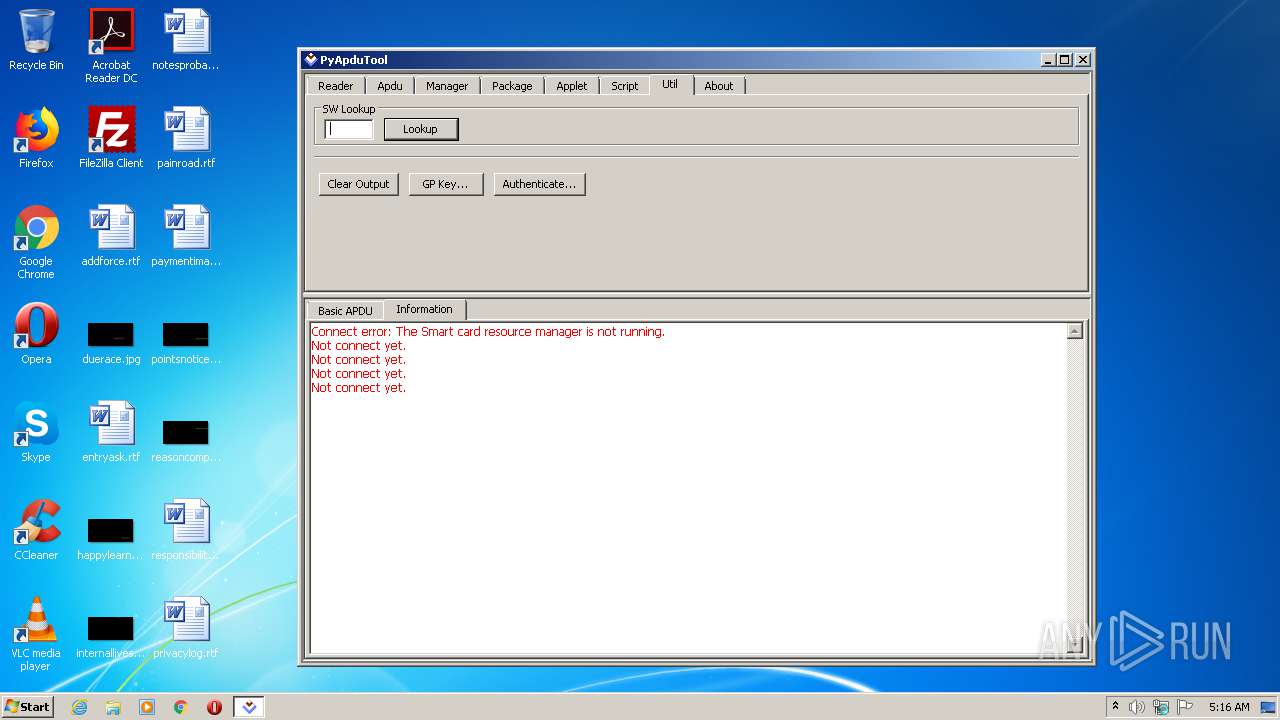
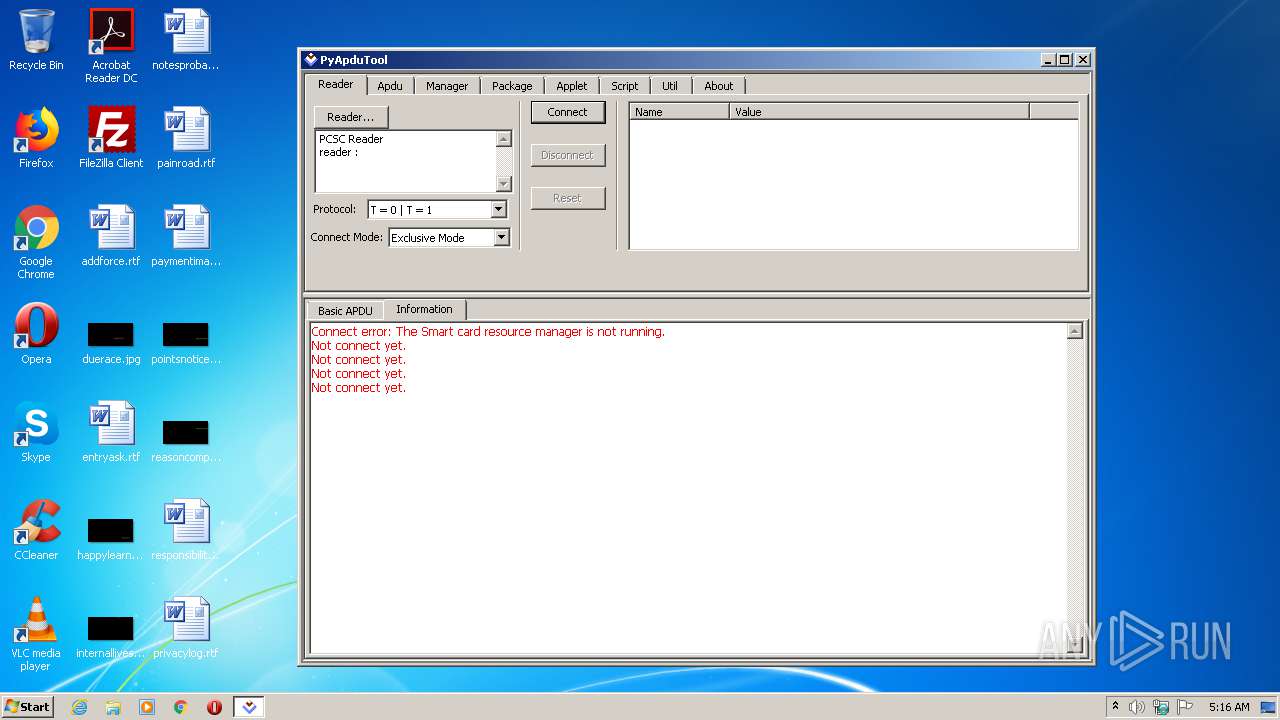
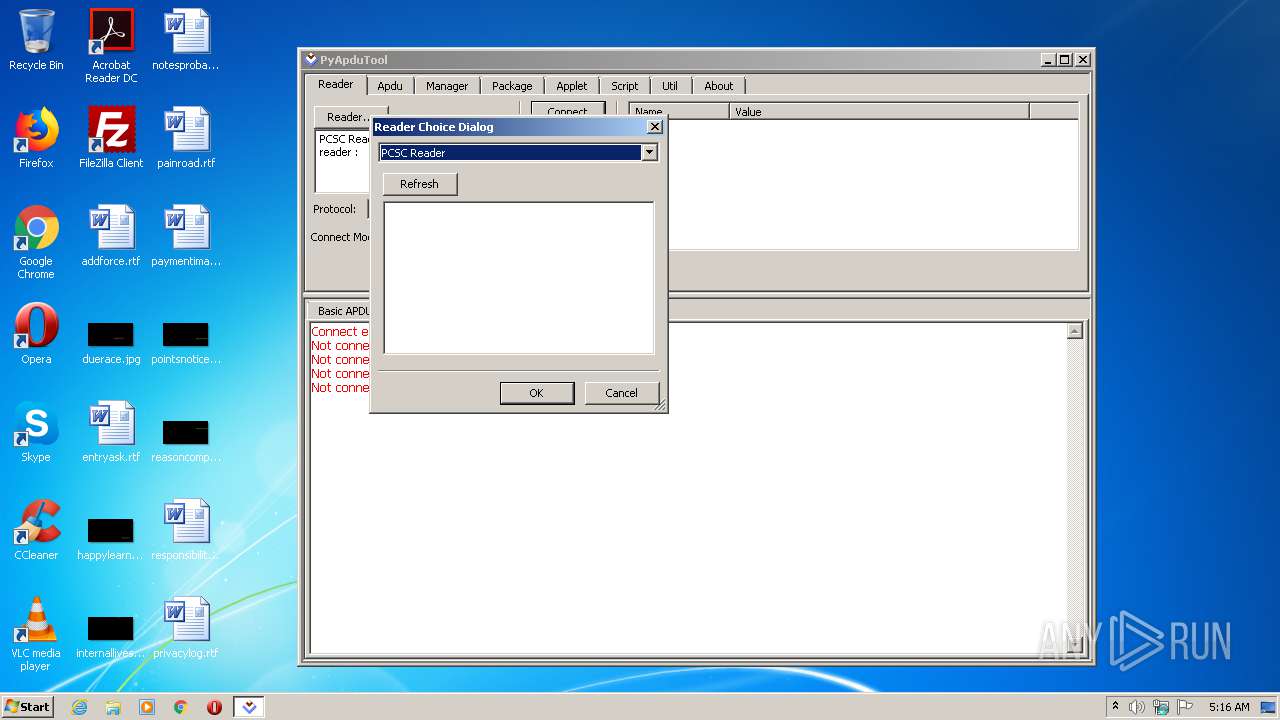
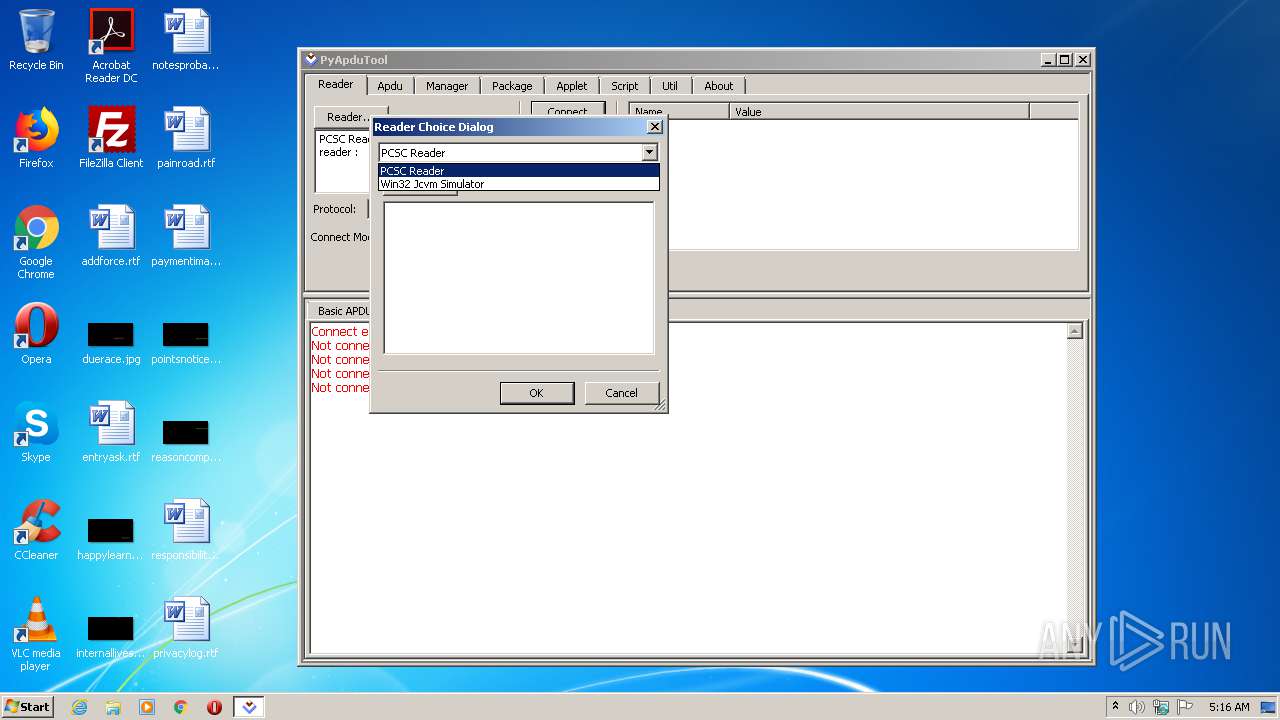
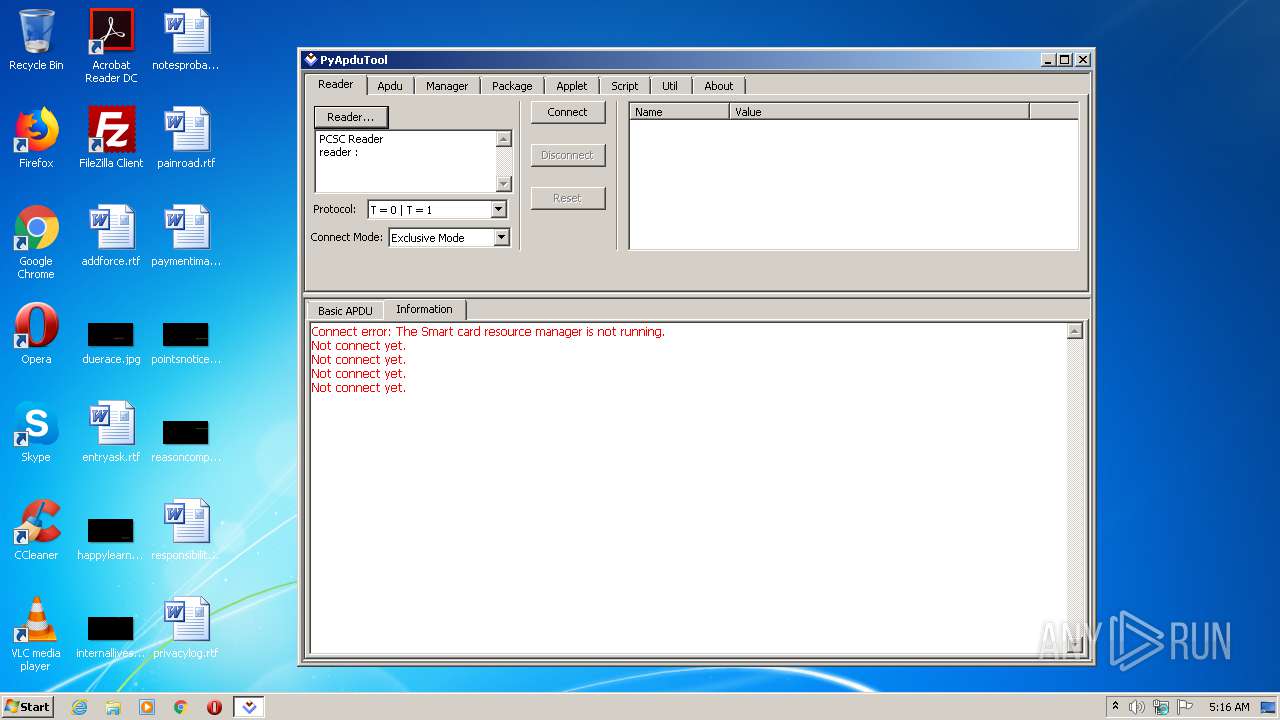
| File name: | pyApduTool.exe |
| Full analysis: | https://app.any.run/tasks/e8d95dd3-3b94-4a60-90ba-81234fd7250b |
| Verdict: | Malicious activity |
| Analysis date: | June 23, 2021, 04:15:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CF6635A3A1693F785518D4A521BE061D |
| SHA1: | EA12811DB1FCE04DE6BA4B3EDA9A24810294BF2A |
| SHA256: | 6D1CDBD0E193144E3B39506C1FE3B50582F58D348912A43D9B060D6E50E4B93D |
| SSDEEP: | 196608:yzQAYqdelA5Pg2oWUpWpkEA9cgav/XSXIkWhnlssx28crIkkWBX0R3XQJFFP3y:qXYSP5PgrWFJA9laDkWLssx28cMk5cgk |
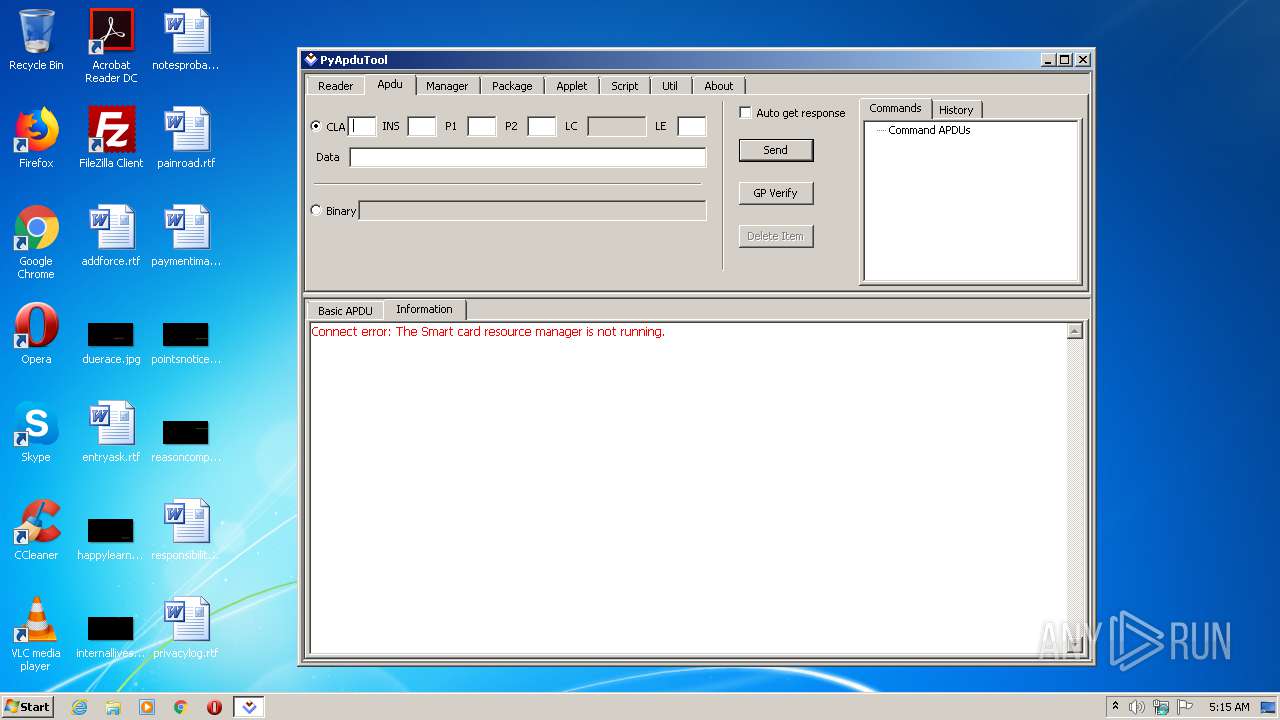
MALICIOUS
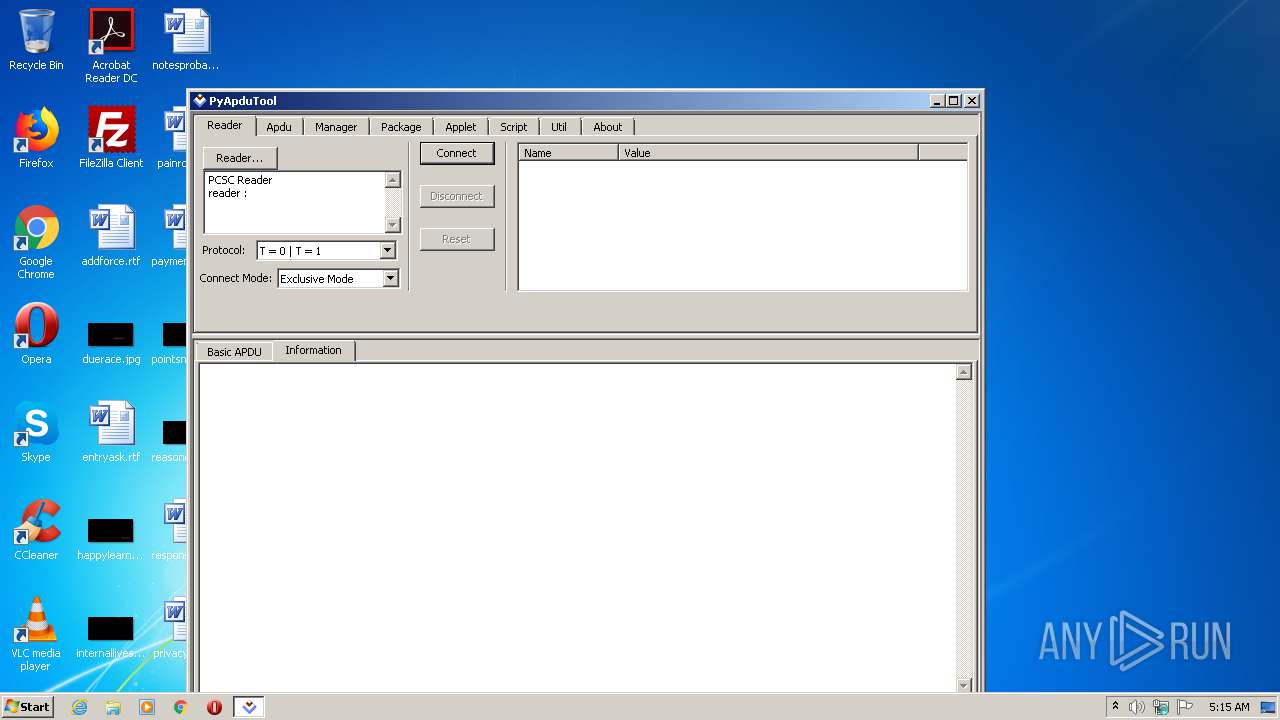
Drops executable file immediately after starts
- pyApduTool.exe (PID: 2660)
Loads dropped or rewritten executable
- pyApduTool.exe (PID: 3124)
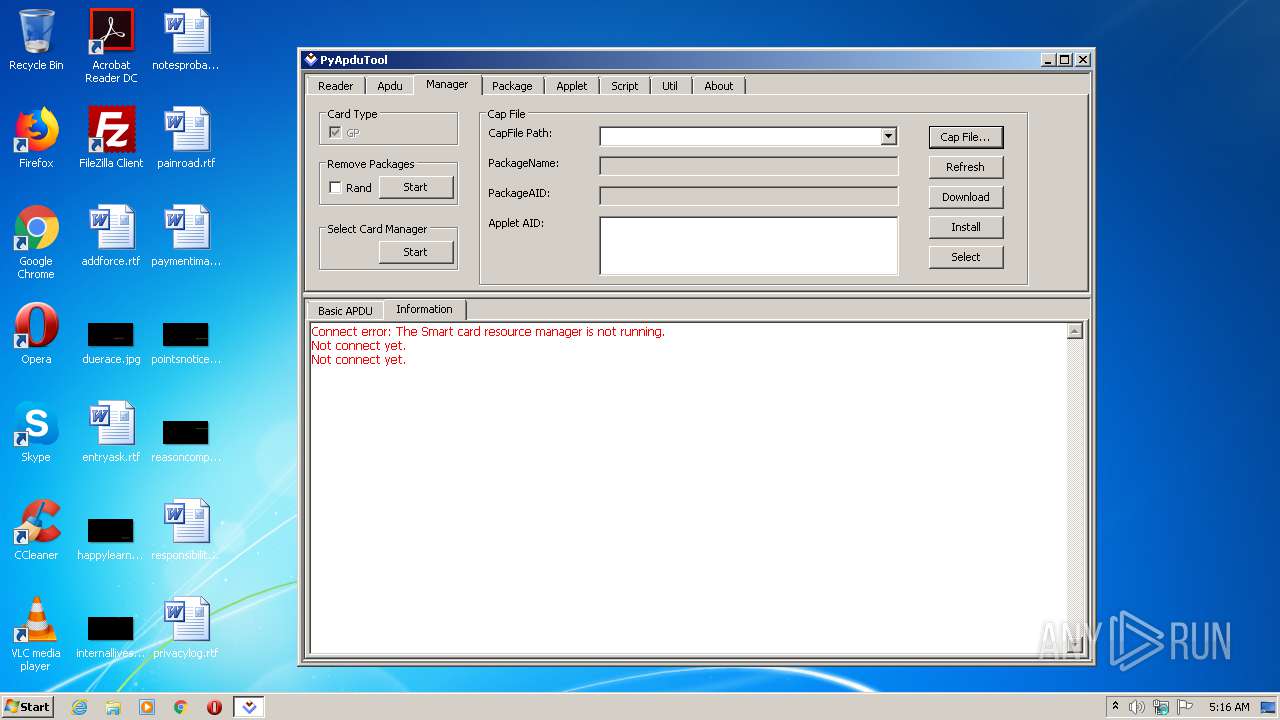
SUSPICIOUS
Drops a file with too old compile date
- pyApduTool.exe (PID: 2660)
Loads Python modules
- pyApduTool.exe (PID: 3124)
Application launched itself
- pyApduTool.exe (PID: 2660)
Executable content was dropped or overwritten
- pyApduTool.exe (PID: 2660)
Drops a file that was compiled in debug mode
- pyApduTool.exe (PID: 2660)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 1.1.0.0 |
|---|---|
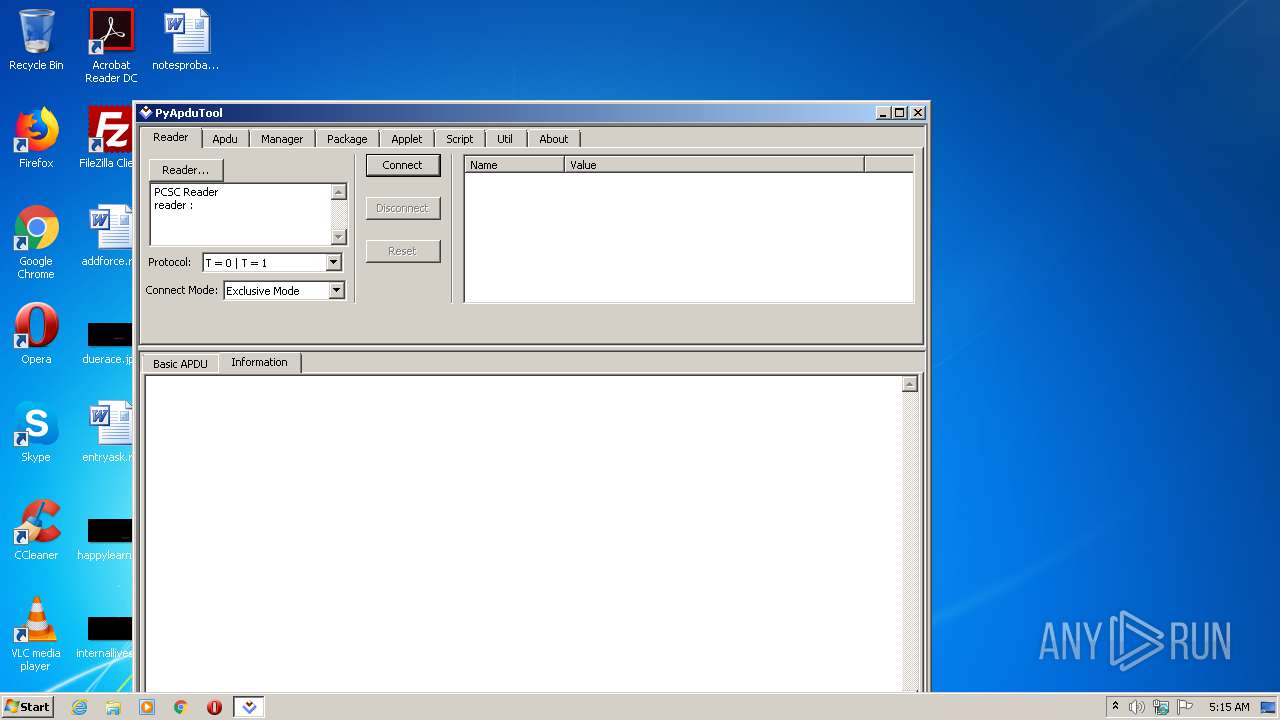
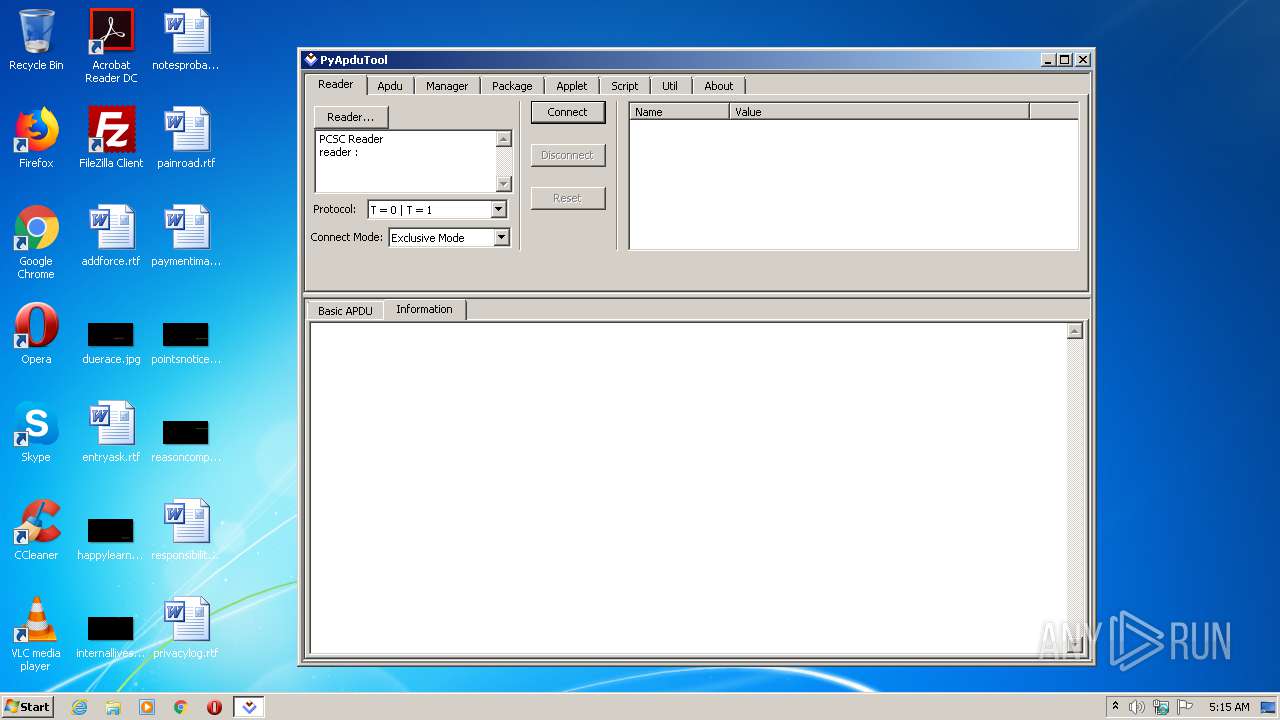
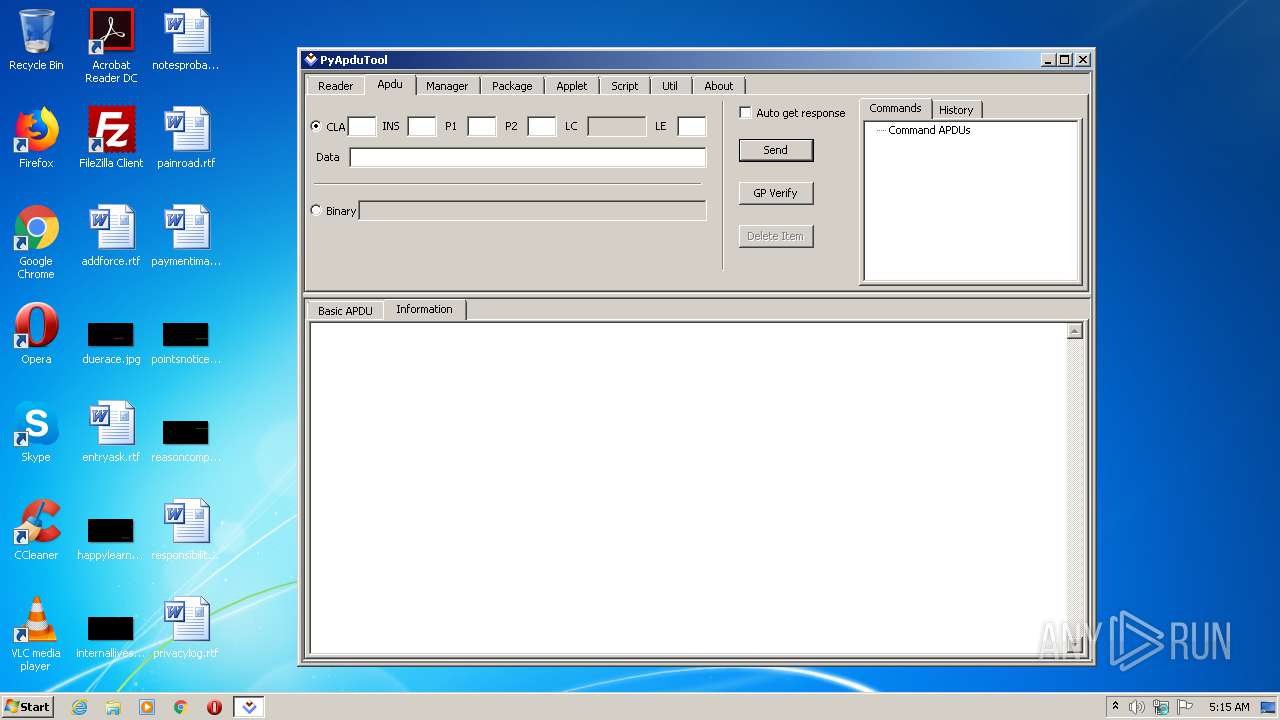
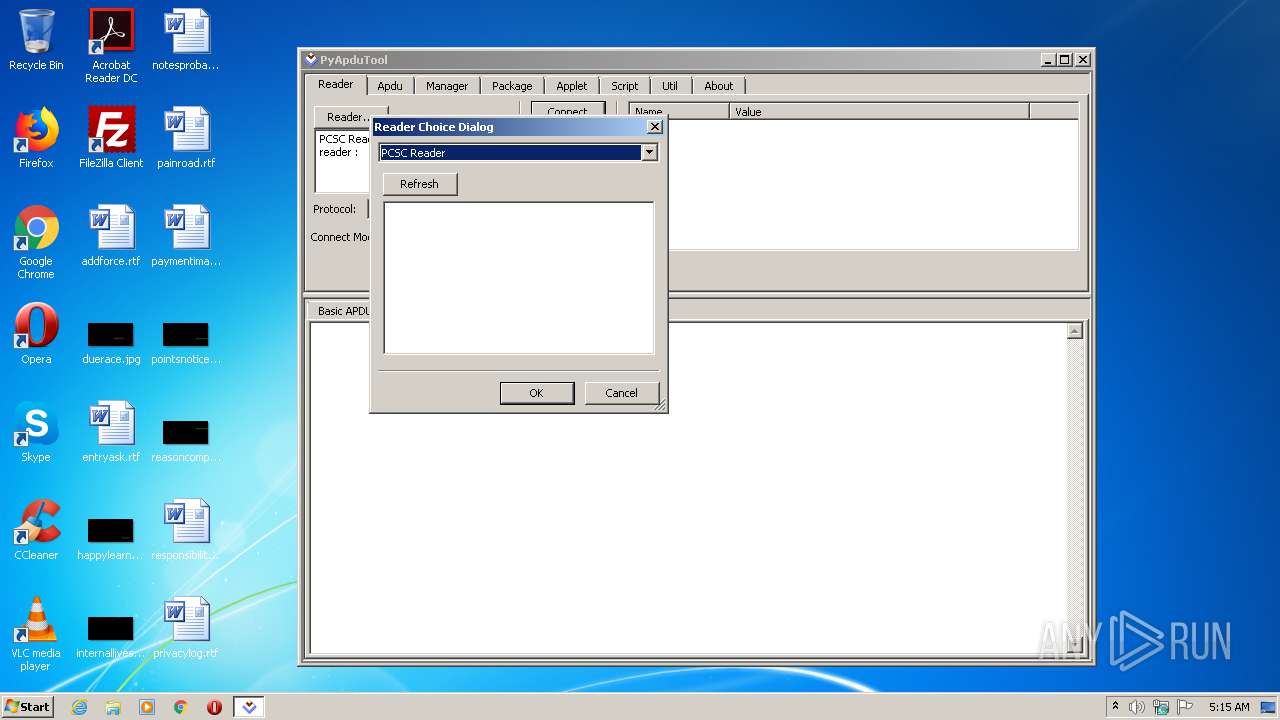
| ProductName: | PyApduTool |
| OriginalFileName: | pyApduTool.exe |
| LegalCopyright: | Copyright (C) 2016 JAVACOS Technologies Co., Ltd. |
| InternalName: | PyApduTool |
| FileVersion: | 1.1.0.0 |
| FileDescription: | PyApduTool |
| CompanyName: | JAVACOS Technologies Co., Ltd. |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.1.0.0 |
| FileVersionNumber: | 1.1.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x8c41 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 193024 |
| CodeSize: | 81408 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2011:07:18 13:56:29+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Jul-2011 11:56:29 |
| Detected languages: |
|
| CompanyName: | JAVACOS Technologies Co., Ltd. |
| FileDescription: | PyApduTool |
| FileVersion: | 1.1.0.0 |
| InternalName: | PyApduTool |
| LegalCopyright: | Copyright (C) 2016 JAVACOS Technologies Co., Ltd. |
| OriginalFilename: | pyApduTool.exe |
| ProductName: | PyApduTool |
| ProductVersion: | 1.1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 18-Jul-2011 11:56:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013CE0 | 0x00013E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63229 |
.rdata | 0x00015000 | 0x00005E16 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.64326 |
.data | 0x0001B000 | 0x00003424 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.00515 |
.rsrc | 0x0001F000 | 0x00027FCC | 0x00028000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.36793 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 3.06388 | 118 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.22308 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.30179 | 21640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.37122 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.51479 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 2.83052 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.15313 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 3.54288 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
COMCTL32.dll |
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
34
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2660 | "C:\Users\admin\AppData\Local\Temp\pyApduTool.exe" | C:\Users\admin\AppData\Local\Temp\pyApduTool.exe | explorer.exe | ||||||||||||
User: admin Company: JAVACOS Technologies Co., Ltd. Integrity Level: MEDIUM Description: PyApduTool Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 3124 | "C:\Users\admin\AppData\Local\Temp\pyApduTool.exe" | C:\Users\admin\AppData\Local\Temp\pyApduTool.exe | — | pyApduTool.exe | |||||||||||
User: admin Company: JAVACOS Technologies Co., Ltd. Integrity Level: MEDIUM Description: PyApduTool Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
Total events
5
Read events
5
Write events
0
Delete events
0
Modification events
Executable files
33
Suspicious files
0
Text files
2
Unknown types
0
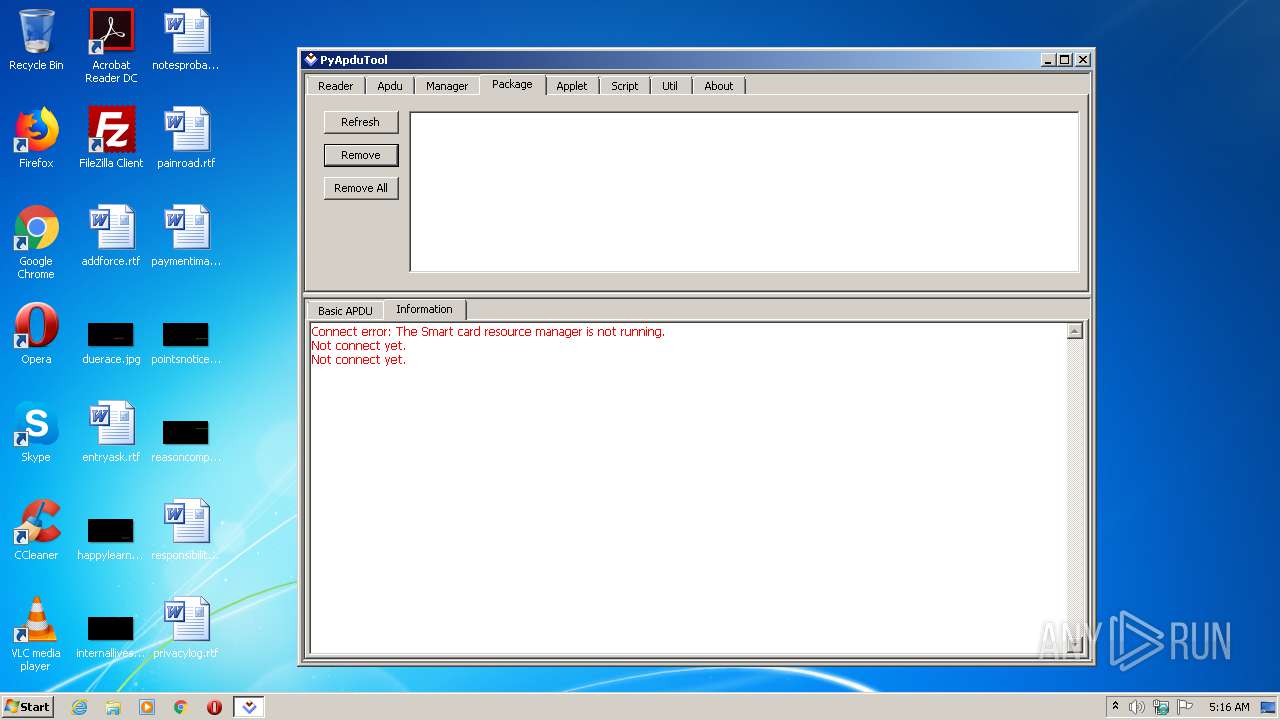
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2660 | pyApduTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI26602\unicodedata.pyd | executable | |
MD5:AB90EBDEB35AFD592DCA1E3D7023DA80 | SHA256:A80049DE708D13C0BB4A5FCA2CD3083524DB164CBC0629D46A3519516AFED889 | |||
| 2660 | pyApduTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI26602\winscard.dll | executable | |
MD5:9419ABF3163B6F0E3AD3DD2B381C879F | SHA256:75029AFDB5F8A8F74A63B6C8165E77110E2FBAEC0021A9613035BFFEC646A54E | |||
| 2660 | pyApduTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI26602\winsound.pyd | executable | |
MD5:2F64F459C3C223FD8826171C24D47EAB | SHA256:C83FF6ACC22A29E221477CC36BBFFAD666C930578C85CCA6CF4D73E92534951C | |||
| 2660 | pyApduTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI26602\_hashlib.pyd | executable | |
MD5:324761CA06EB9E4350307780959D8EBD | SHA256:AFAB75A25CA8F87916D2A639D384B8CFF9BF3050354594E9564C27FE62EF3E4E | |||
| 2660 | pyApduTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI26602\ftutils.authclient.pyd | executable | |
MD5:71769A4E8875347C141C94EF2853BB21 | SHA256:1D7BA4204006CEED70796A2939EA715F7380A86D94D60F408F9140FCFAE7A860 | |||
| 2660 | pyApduTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI26602\_ssl.pyd | executable | |
MD5:6BA1564CD78DDB62900FF3327C18587C | SHA256:6D9ABE468B51B13E220D042F160E617E896EDDECF7031A14CAC2407ED65C7EAF | |||
| 2660 | pyApduTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI26602\_ctypes.pyd | executable | |
MD5:C5422DB93C5FD74E09DB36DDF975DA9E | SHA256:96846A901D0D793FB77FF0B6488A904DC675A8D5273A442888D41D9A32BB845B | |||
| 2660 | pyApduTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI26602\select.pyd | executable | |
MD5:5602701B02F8F8CAC446AD4E4E05C317 | SHA256:D50E9E695C69F54A42FFA043029D12BB228FC1ED199C919749731C15348A6460 | |||
| 2660 | pyApduTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI26602\wx._misc_.pyd | executable | |
MD5:DEE9EF954B8D012874DC09C818508291 | SHA256:DEC81371BAFA11602E11FCA17420BE0E2A89D523BA54A605F6FF858557FB0483 | |||
| 2660 | pyApduTool.exe | C:\Users\admin\AppData\Local\Temp\_MEI26602\bz2.pyd | executable | |
MD5:3478581DB4EB3865282562C277F28B0A | SHA256:2F65A93A7E9B5D8CD618B7AD893A8E094942016DFB165E0638E57C1E9BDB4507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report