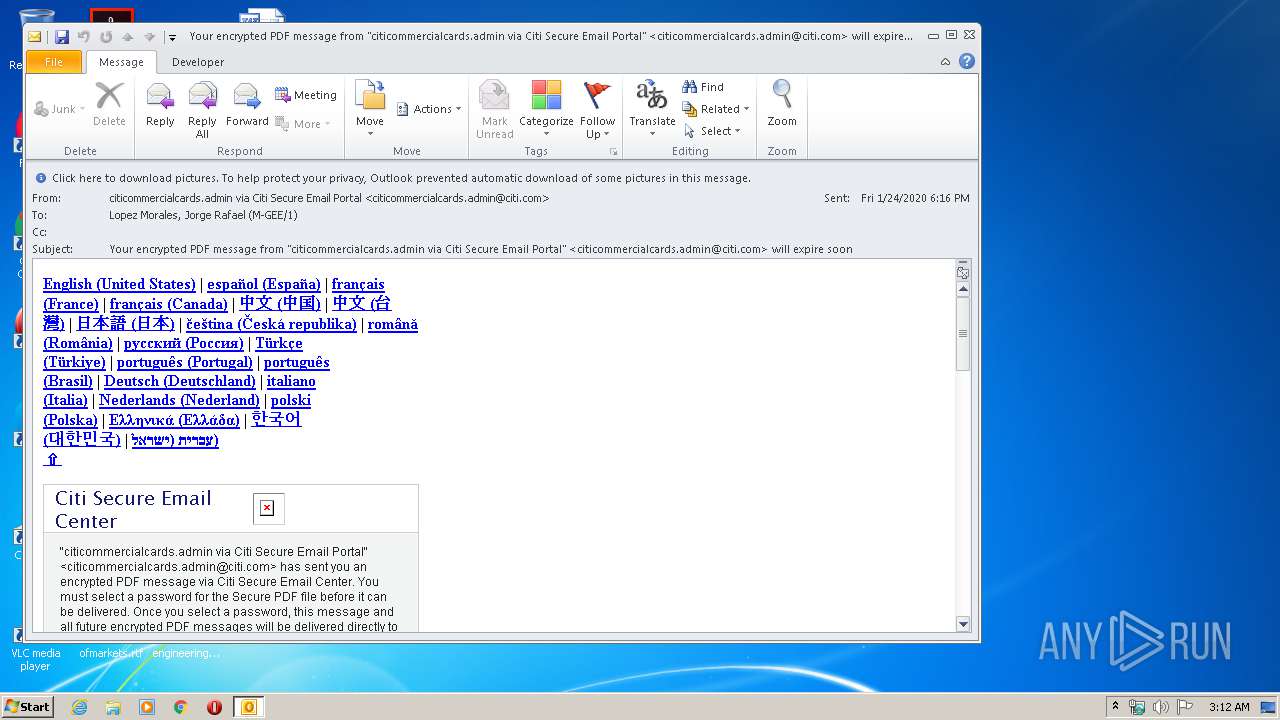
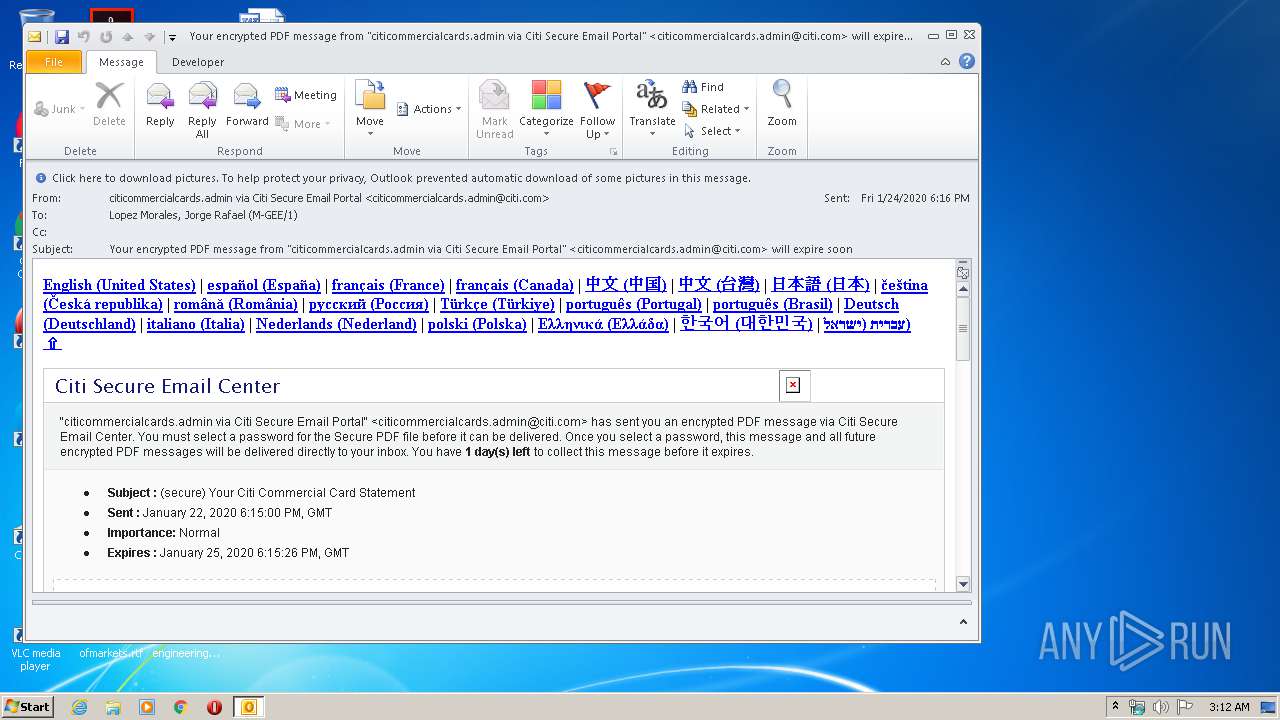
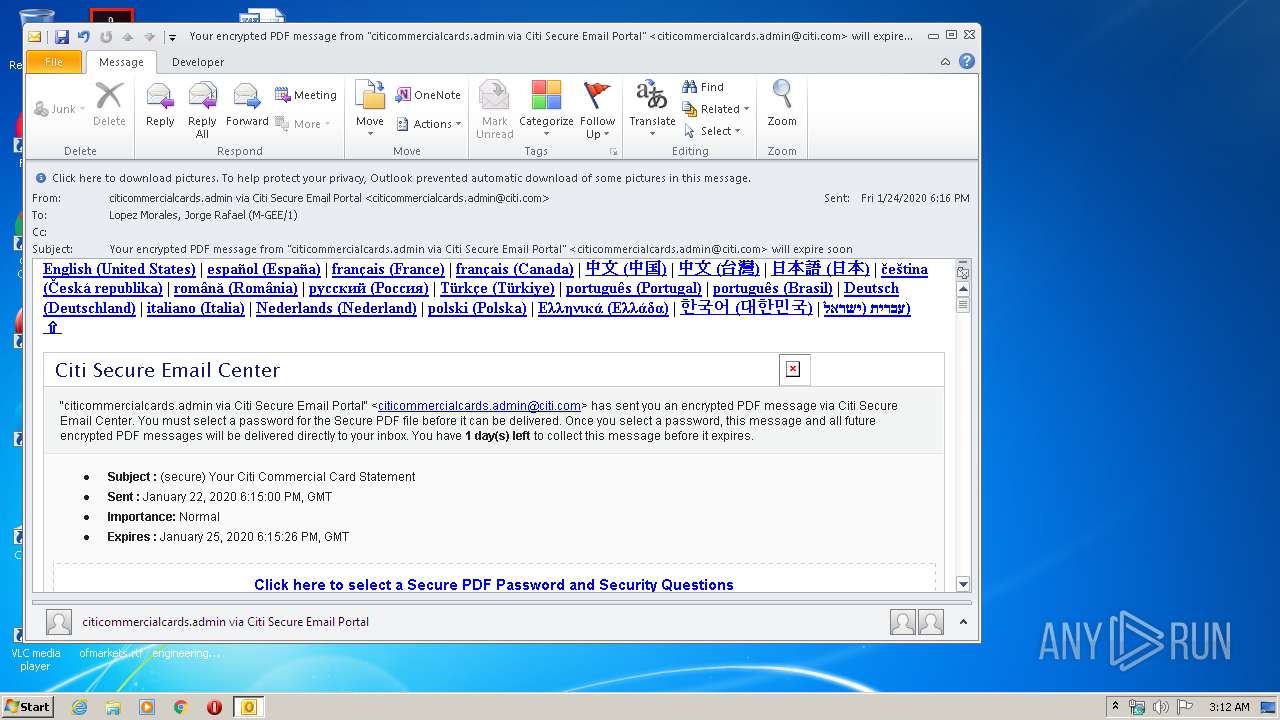
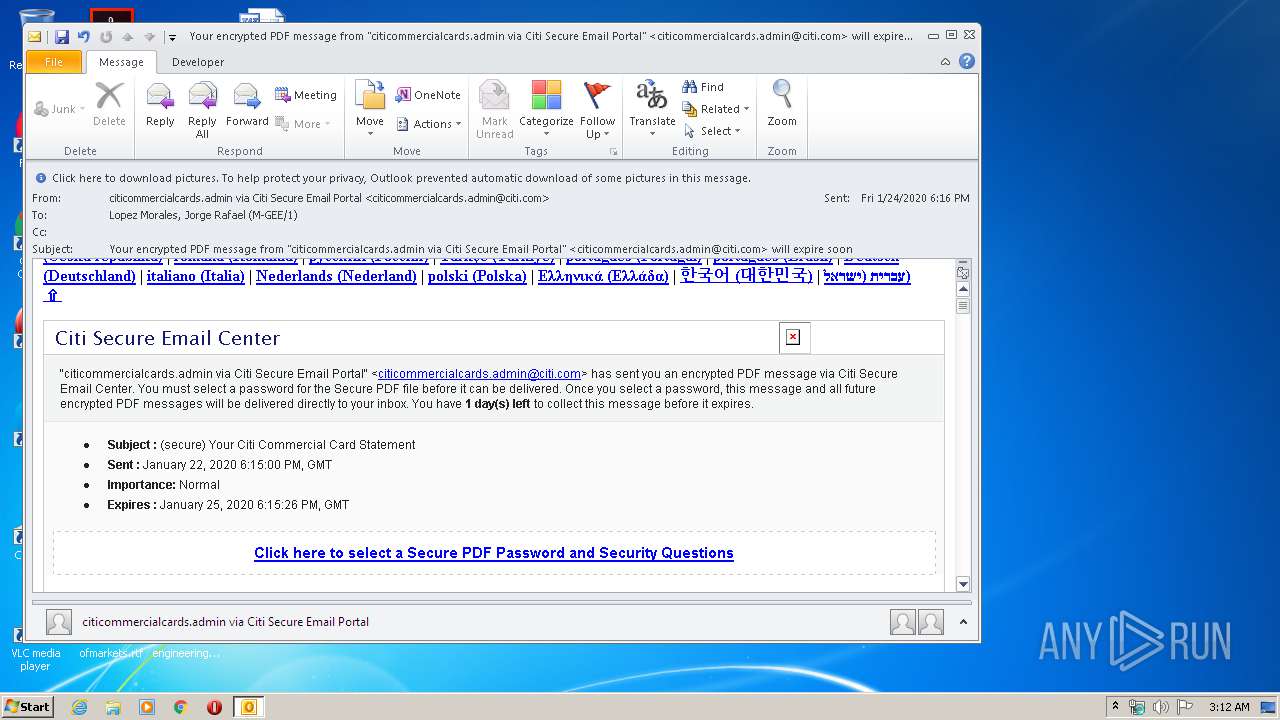
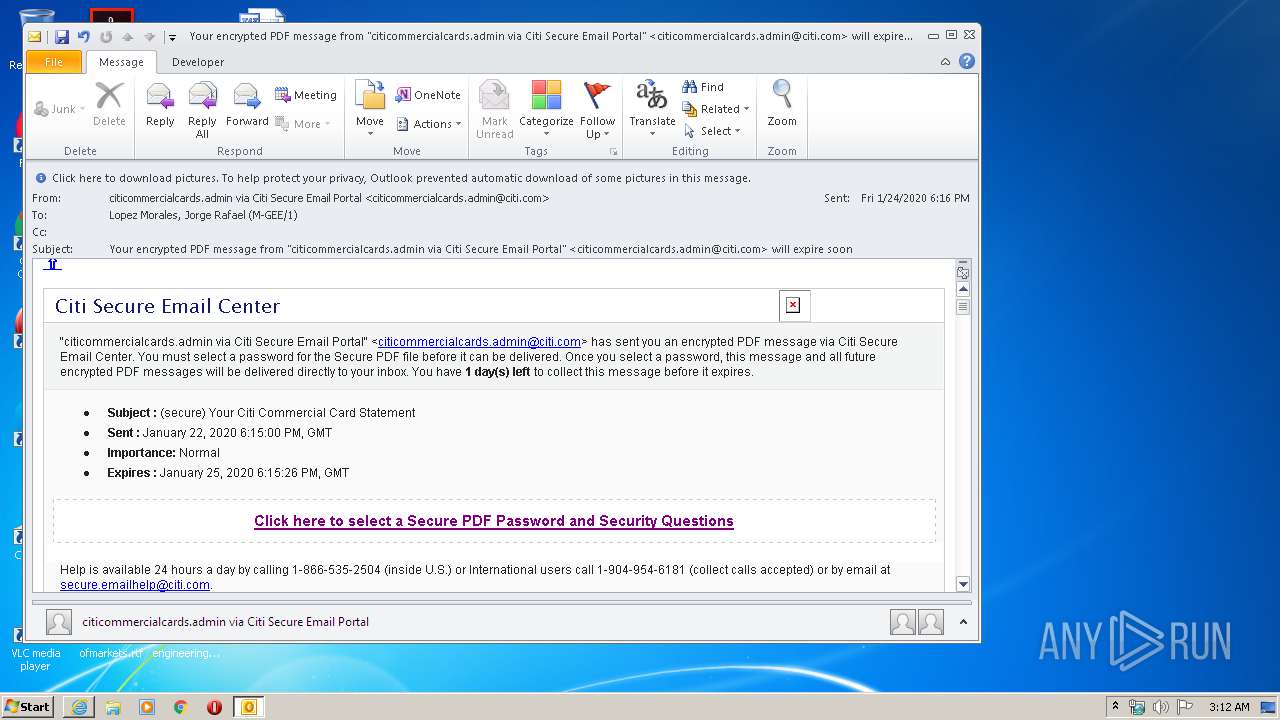
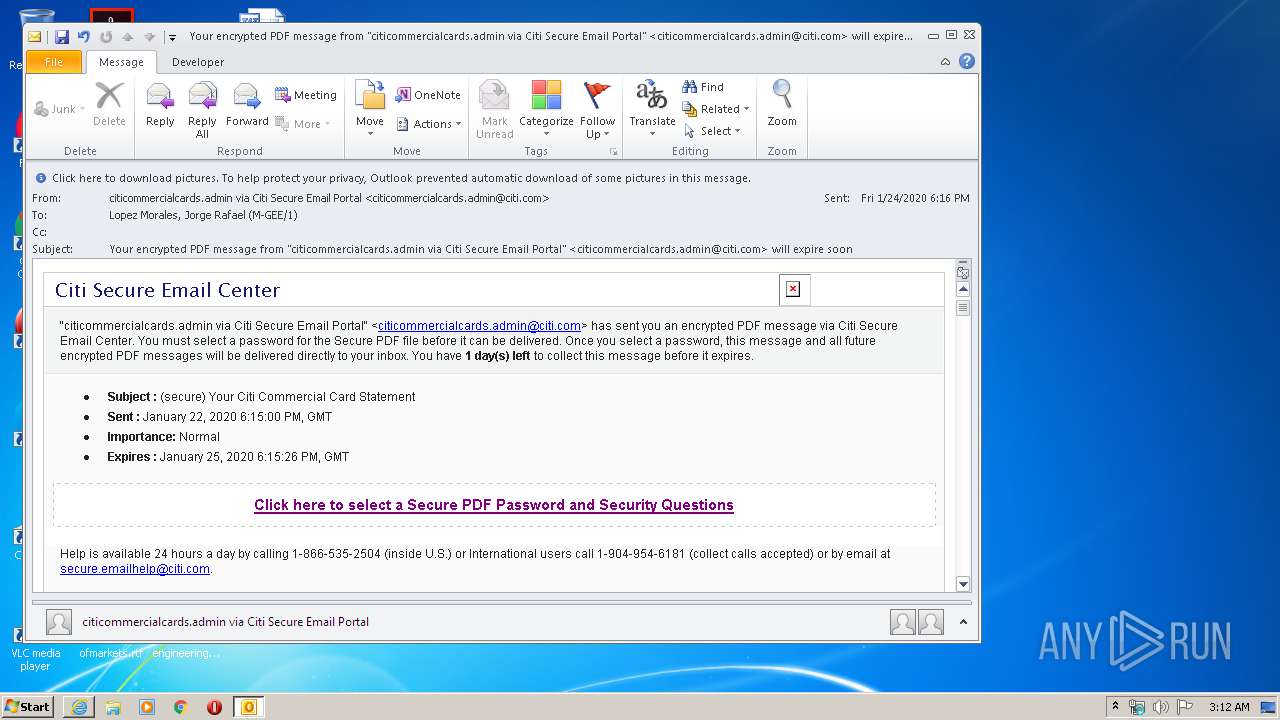
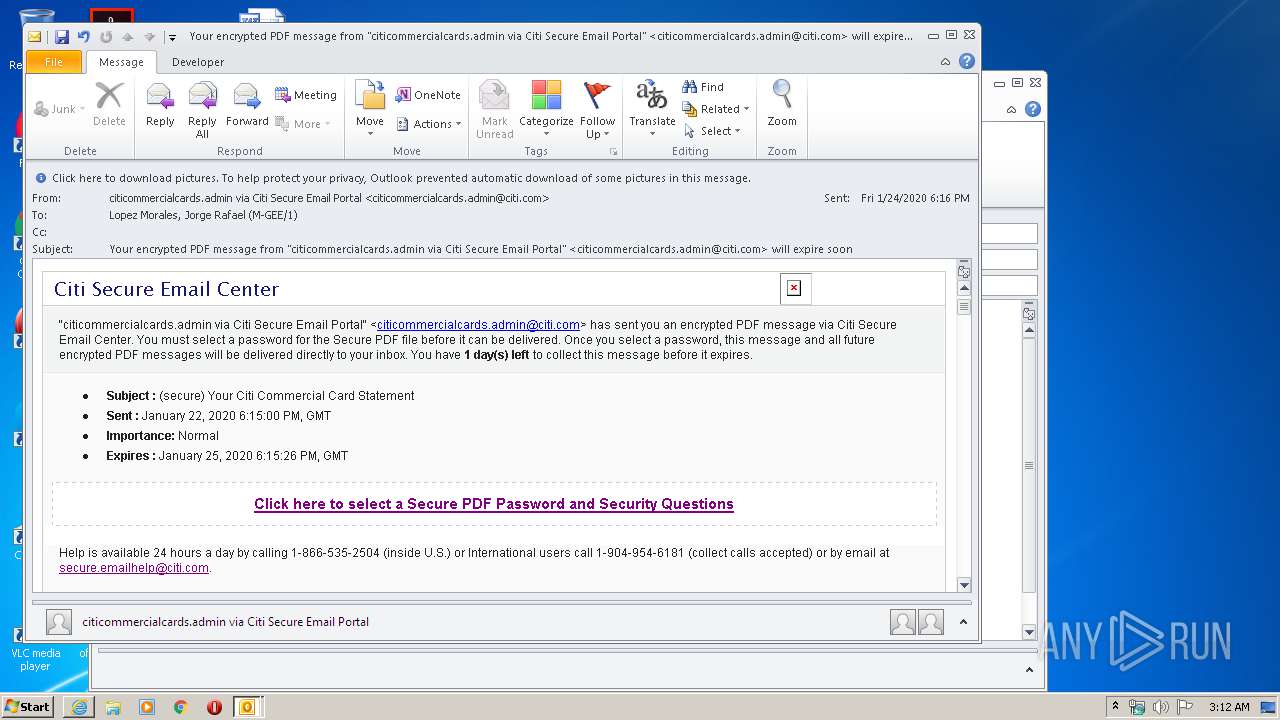
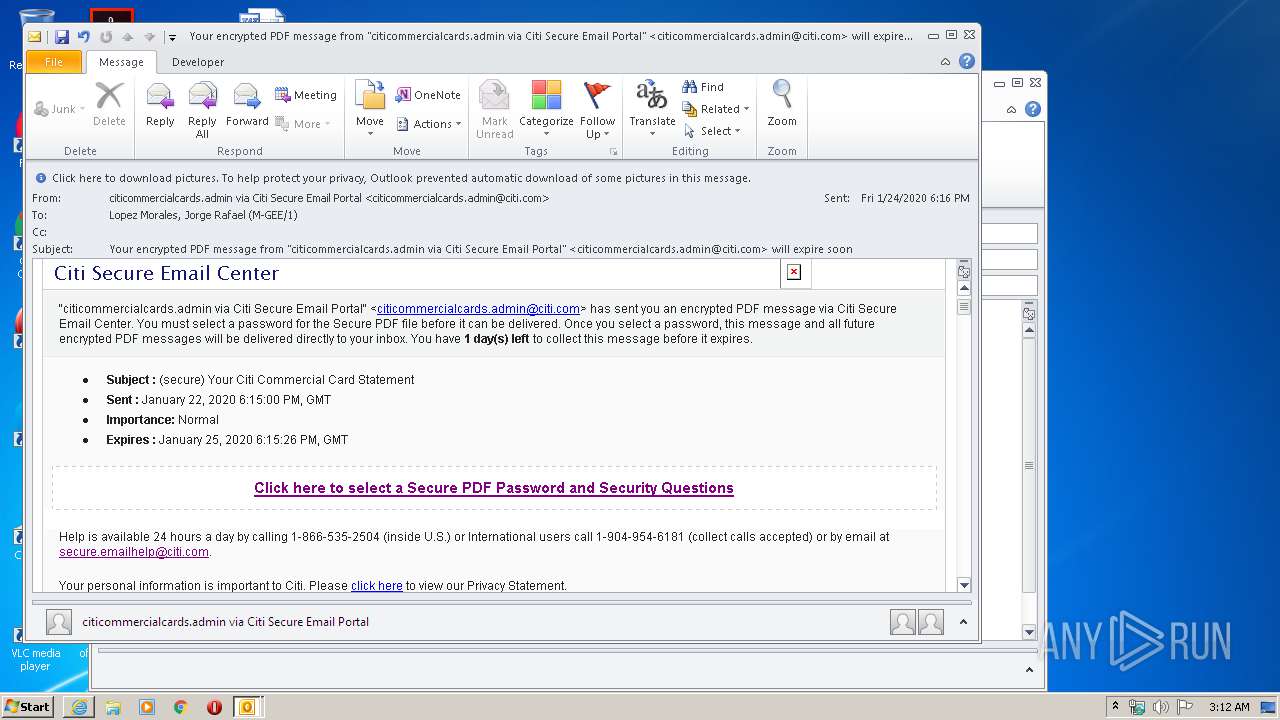
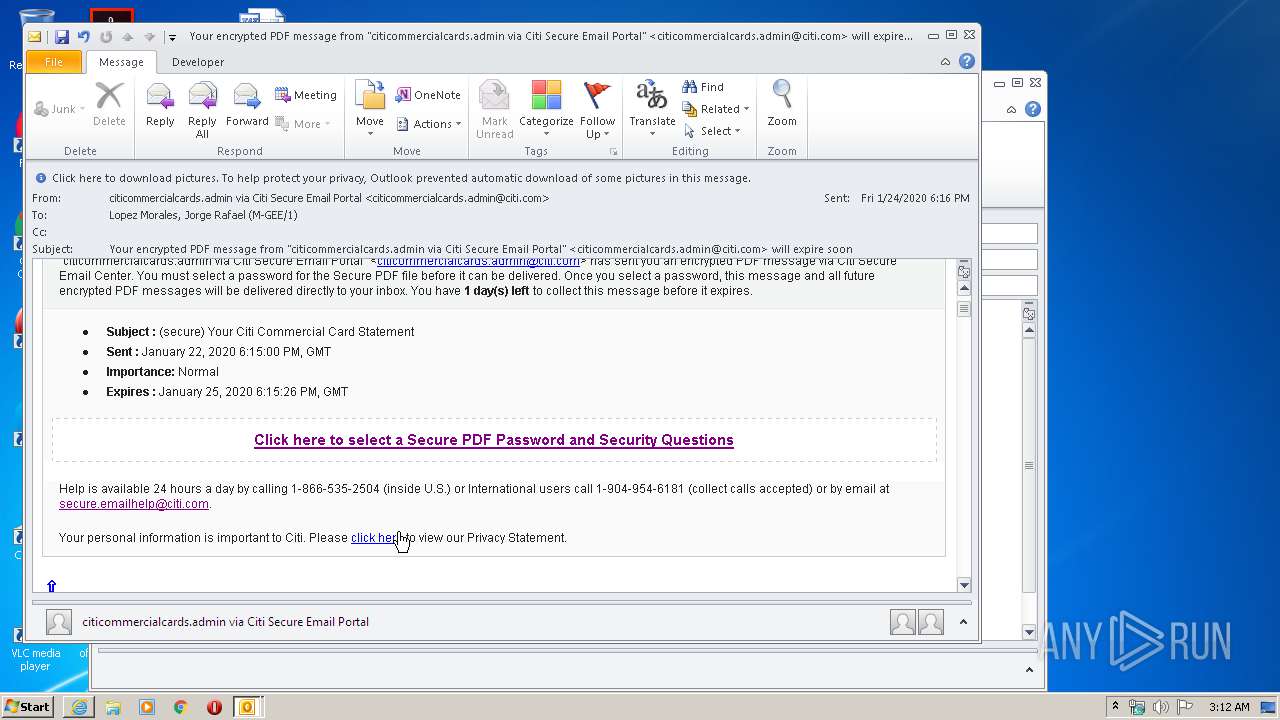
| File name: | Your encrypted PDF message from citicommercialcards.admin via Citi Secure Email Portal citicommercialcards.admin@citi.com will expire soon.msg |
| Full analysis: | https://app.any.run/tasks/2641939d-c45d-44e2-b969-60400947736d |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2020, 03:12:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 05D874030FC008719F2D4C47B8FC5BD9 |
| SHA1: | 98C784DAD8EE89B1681A7BBB5B0E318A3C728E4F |
| SHA256: | 6D1AA349B03020CC208C4D2AA77F354DB807FE3EF2A786AF651FCD4CA955F79C |
| SSDEEP: | 3072:nc1741nryDiH29wZIImzZCE2HI9aUoNCGpc1N/HVkoikH9rs10AT81gE4nV64UoD:cD1ZHVkoFu10ATegE4nV64Uo3OiOLk |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2420)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2420)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2420)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2420)
Starts itself from another location
- OUTLOOK.EXE (PID: 2420)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 2388)
- iexplore.exe (PID: 1248)
Changes internet zones settings
- iexplore.exe (PID: 956)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2952)
- OUTLOOK.EXE (PID: 2420)
Creates files in the user directory
- iexplore.exe (PID: 2388)
- iexplore.exe (PID: 1248)
- iexplore.exe (PID: 956)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2388)
Application launched itself
- iexplore.exe (PID: 956)
Reads internet explorer settings
- iexplore.exe (PID: 2388)
- iexplore.exe (PID: 1248)
Reads settings of System Certificates
- iexplore.exe (PID: 2388)
- iexplore.exe (PID: 956)
- iexplore.exe (PID: 1248)
Adds / modifies Windows certificates
- iexplore.exe (PID: 956)
Changes settings of System certificates
- iexplore.exe (PID: 956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
40
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
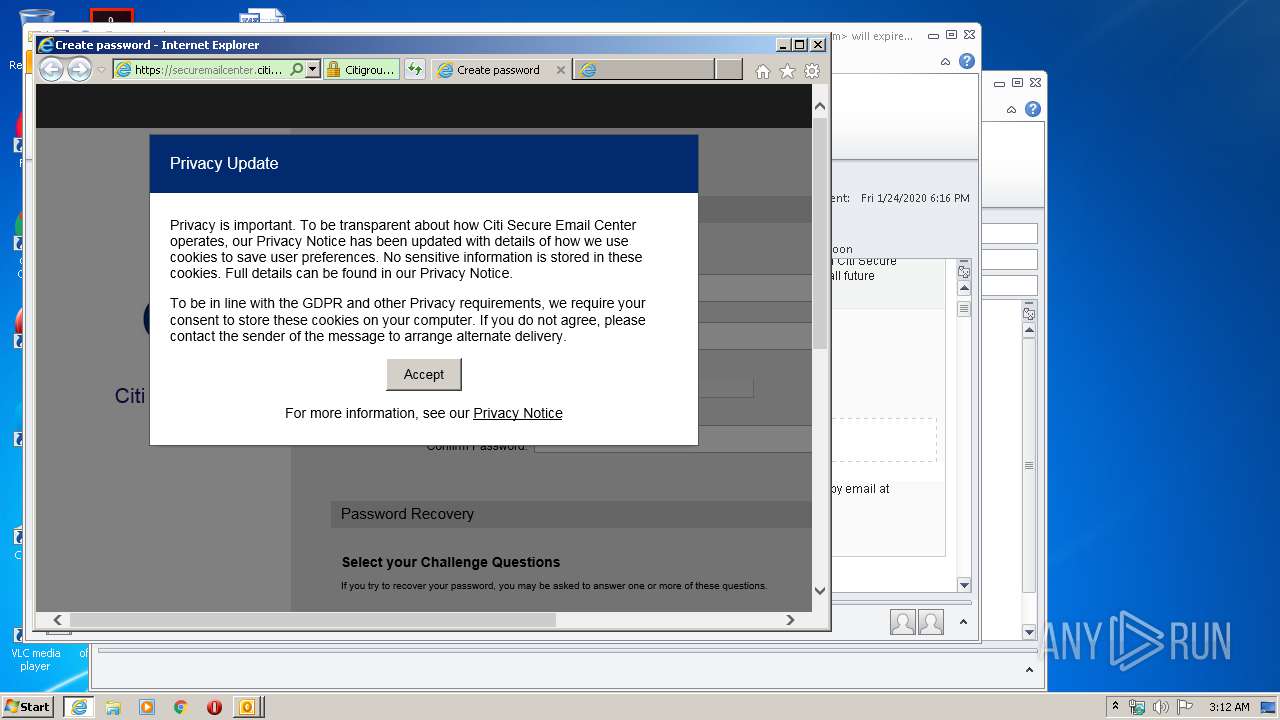
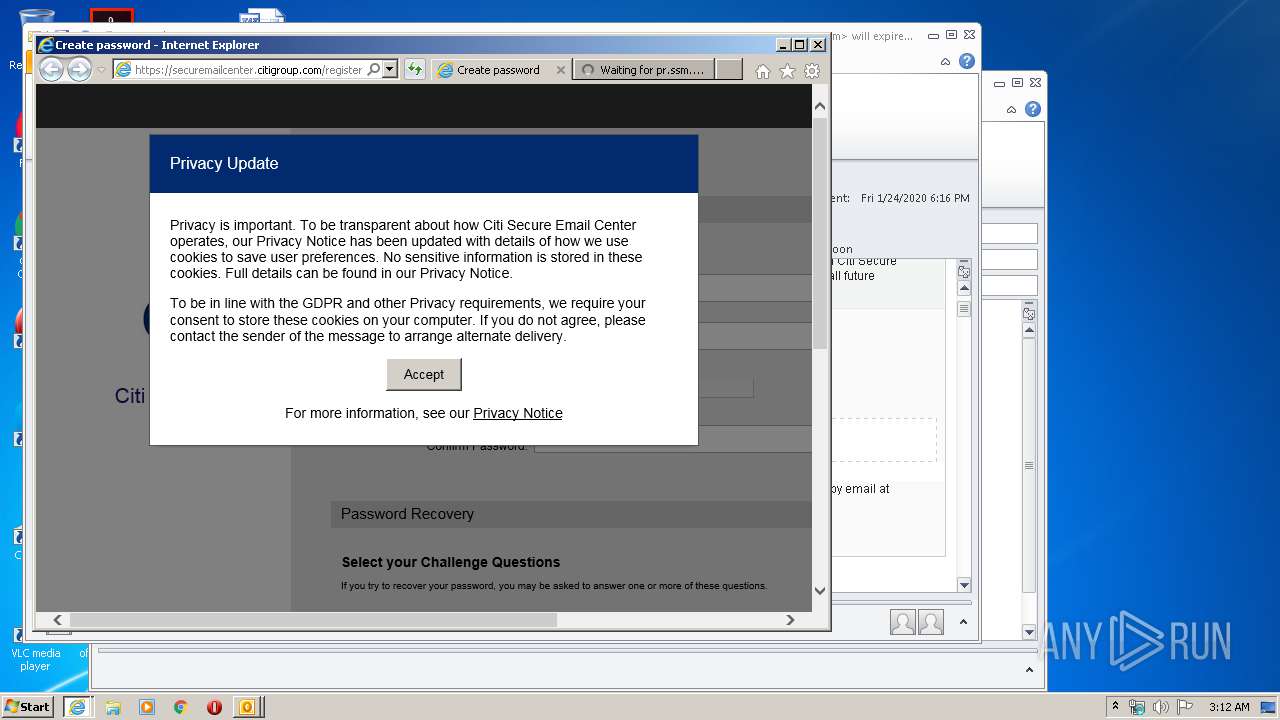
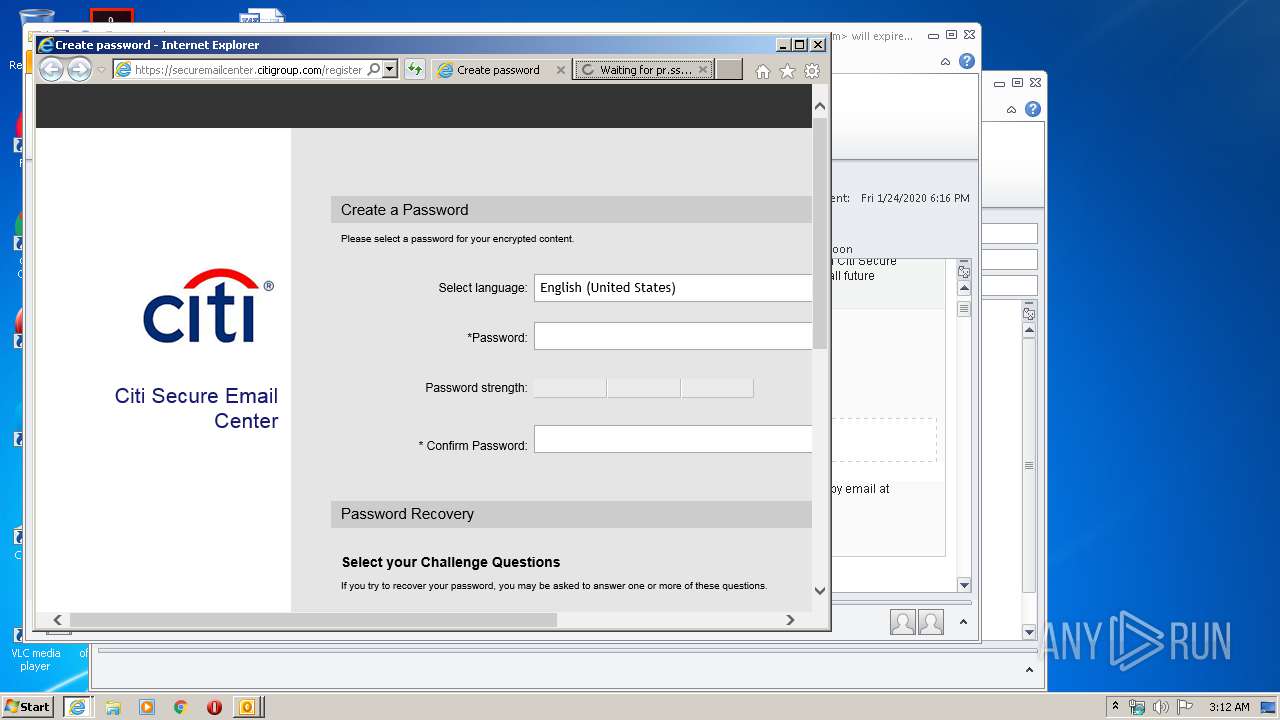
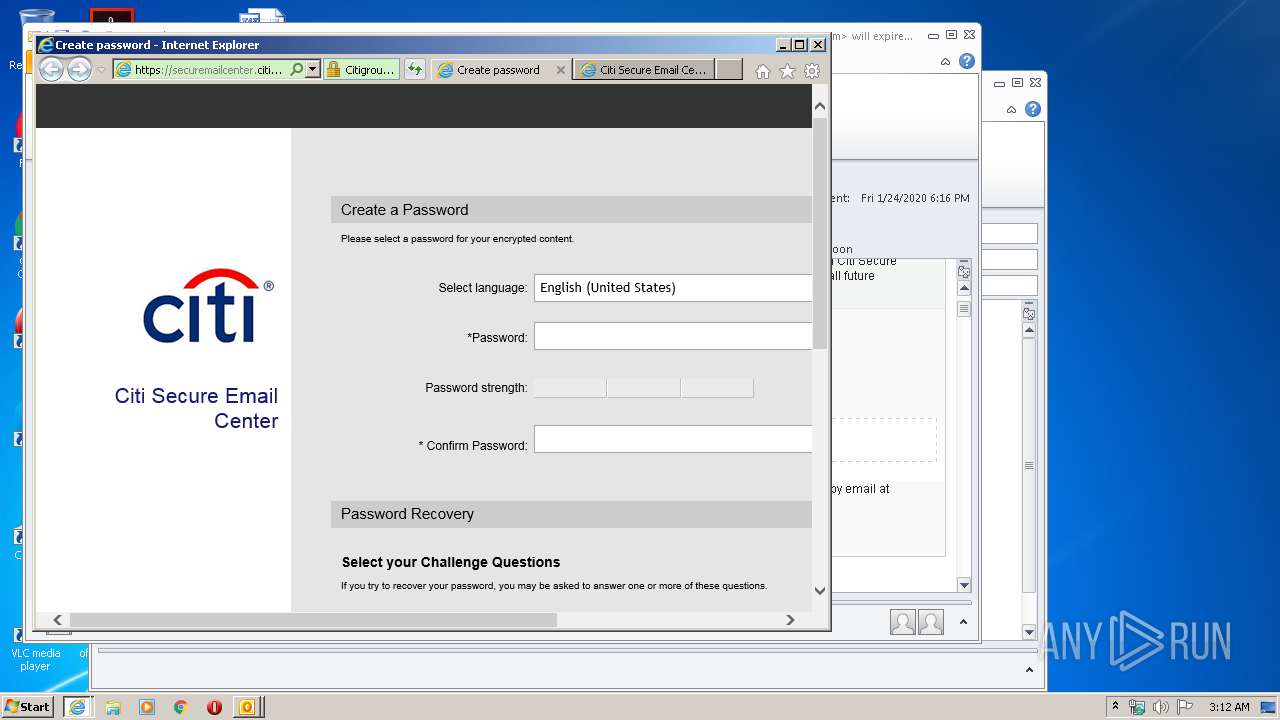
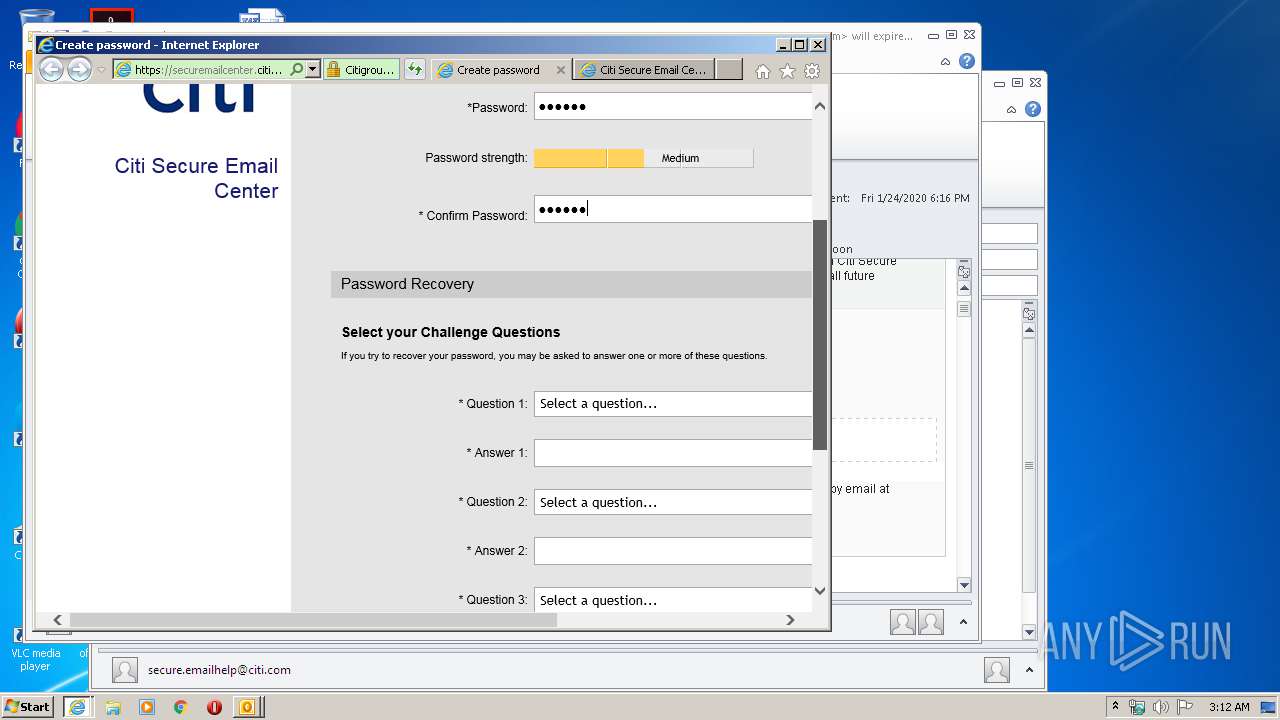
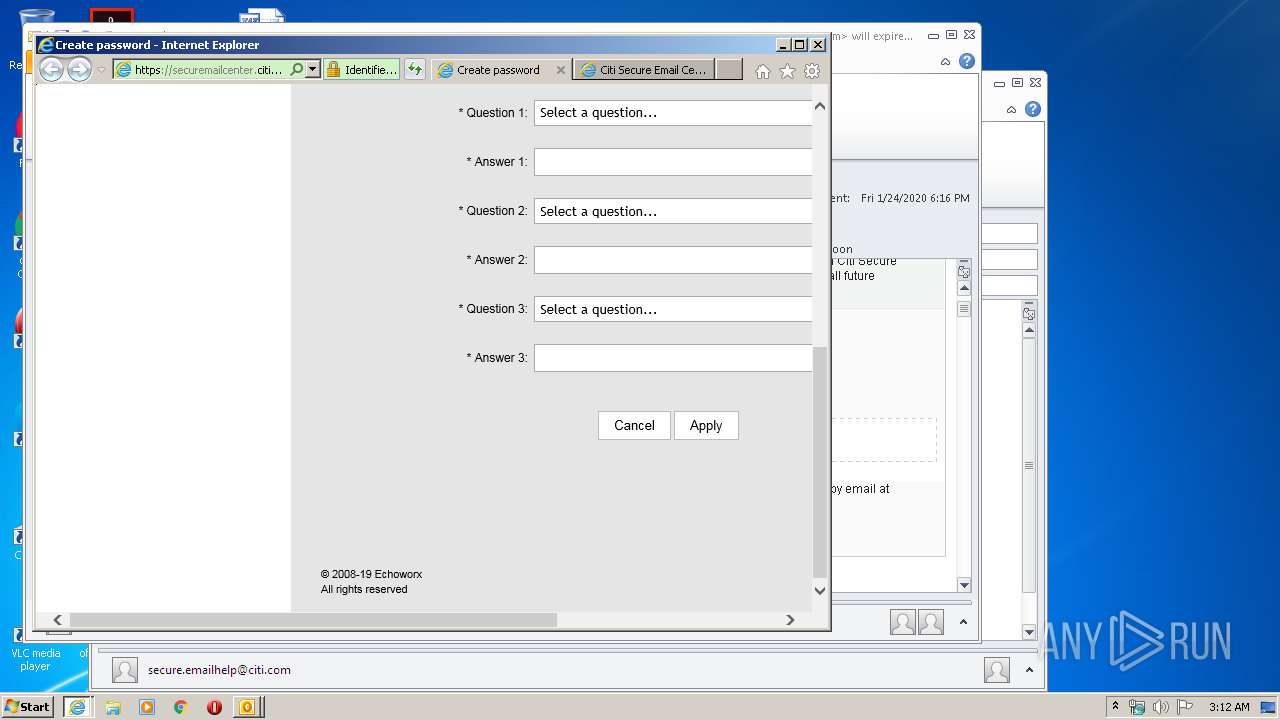
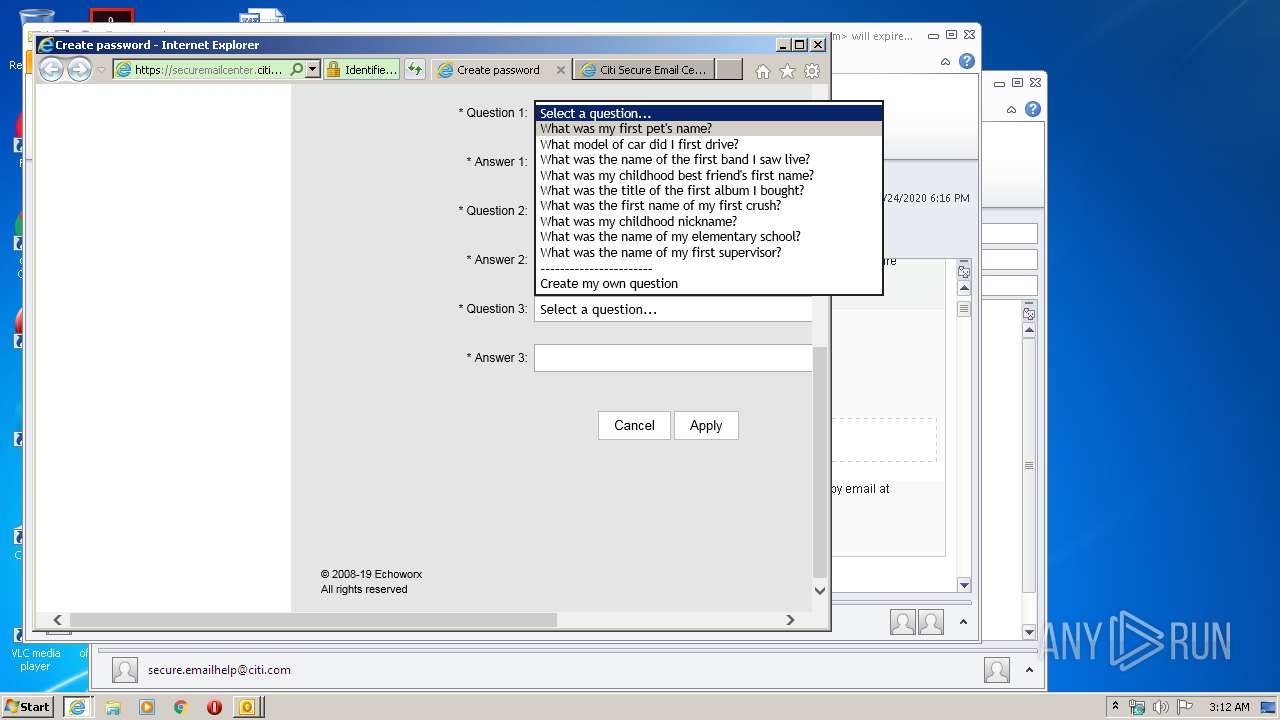
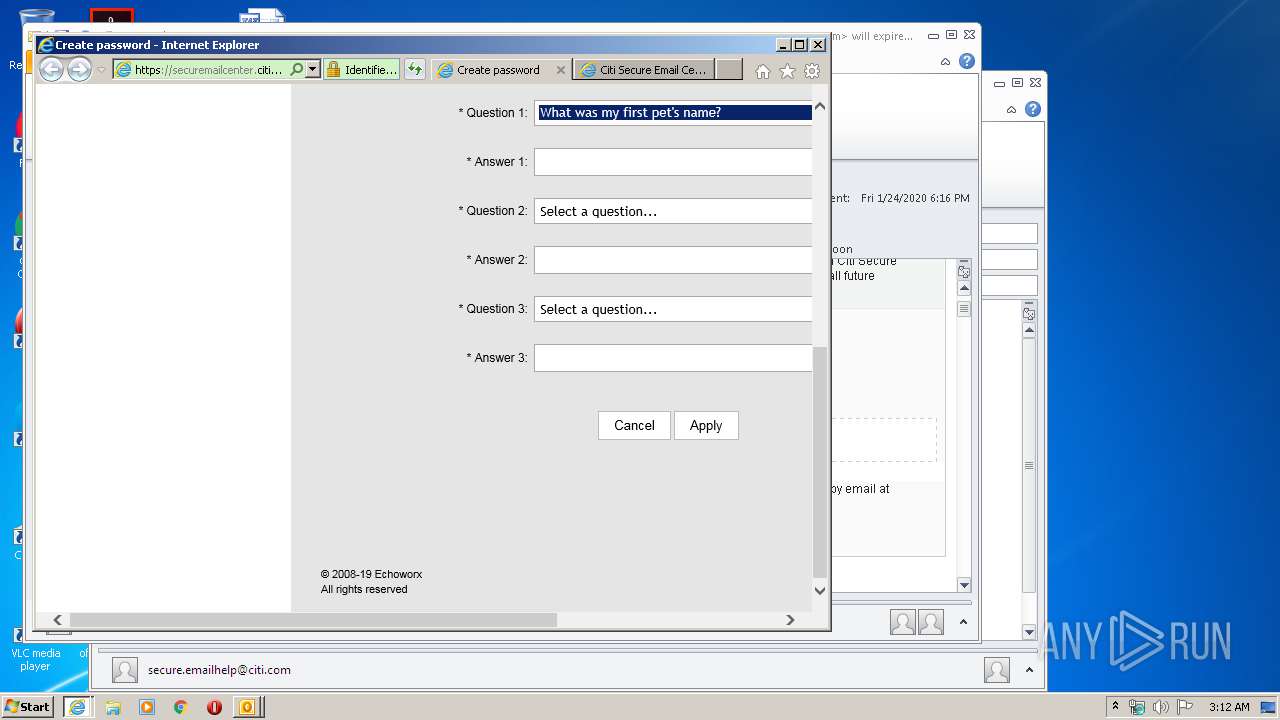
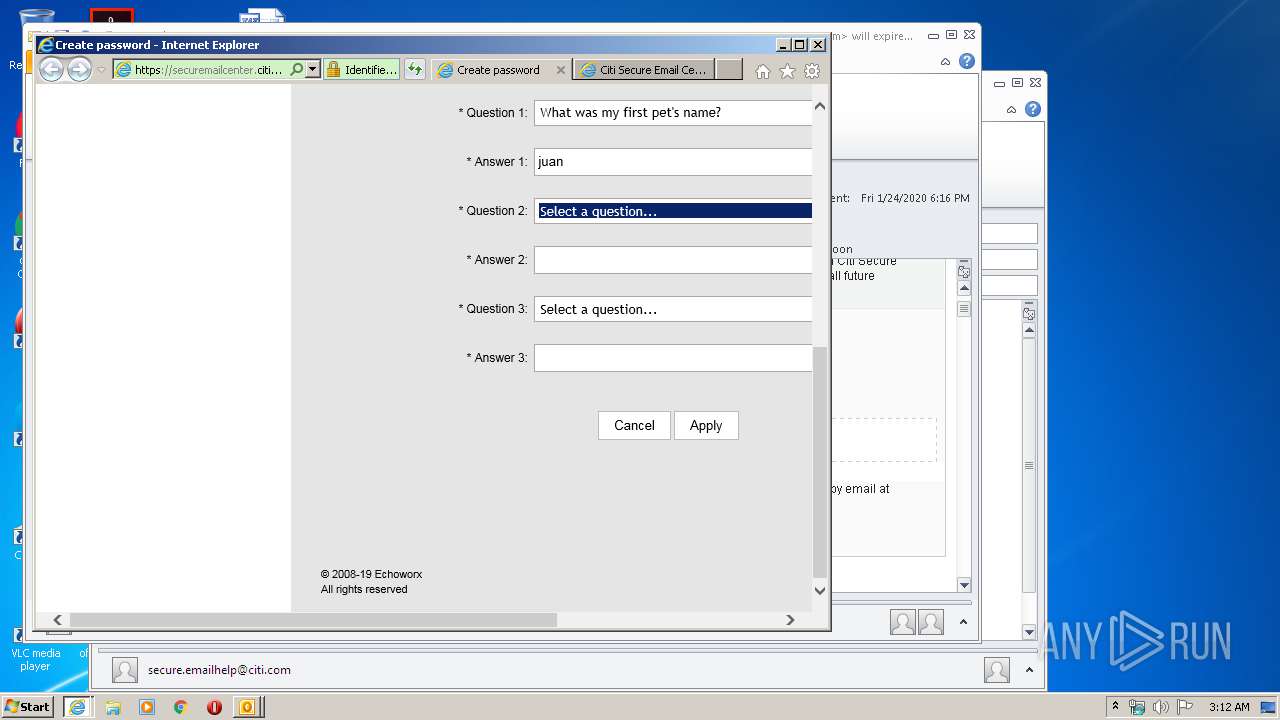
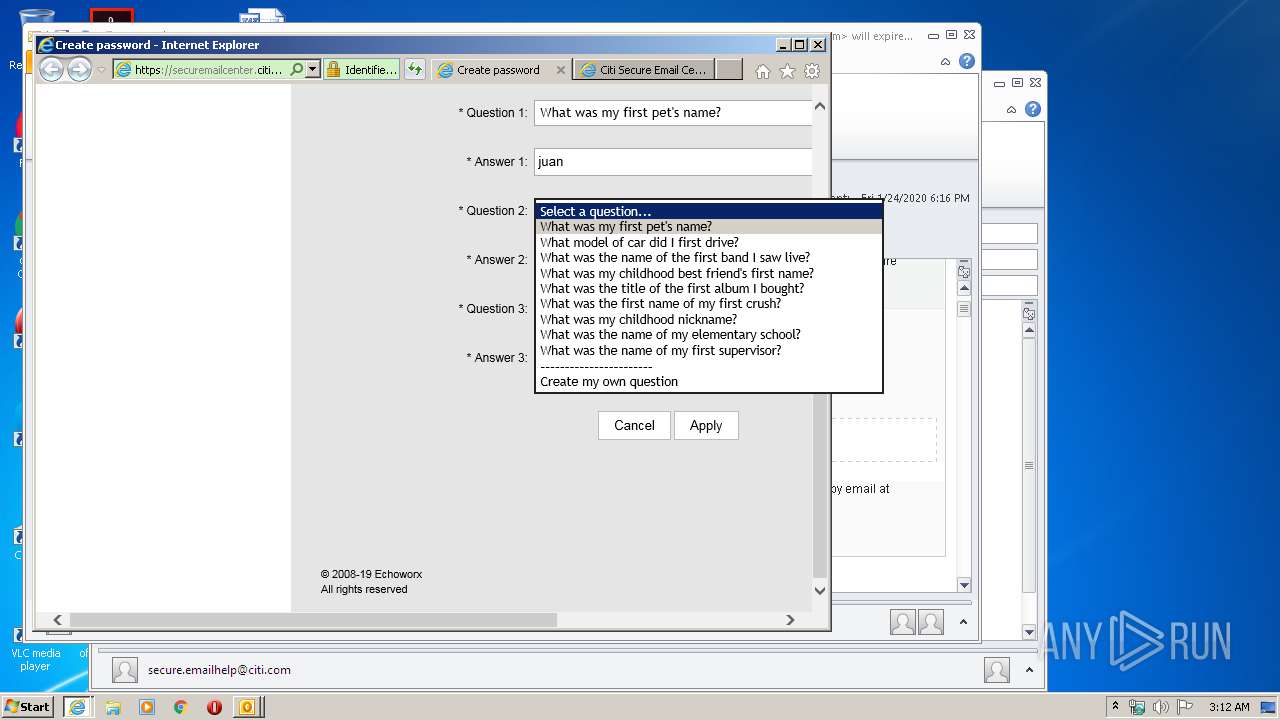
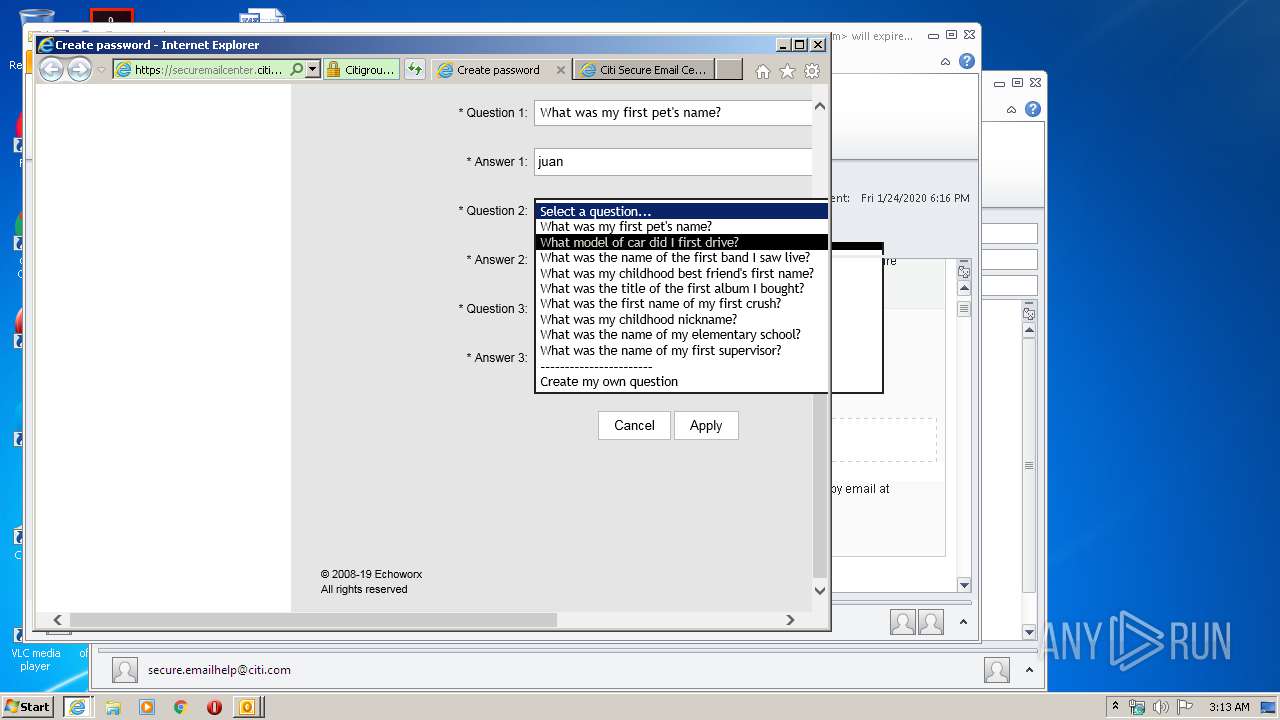
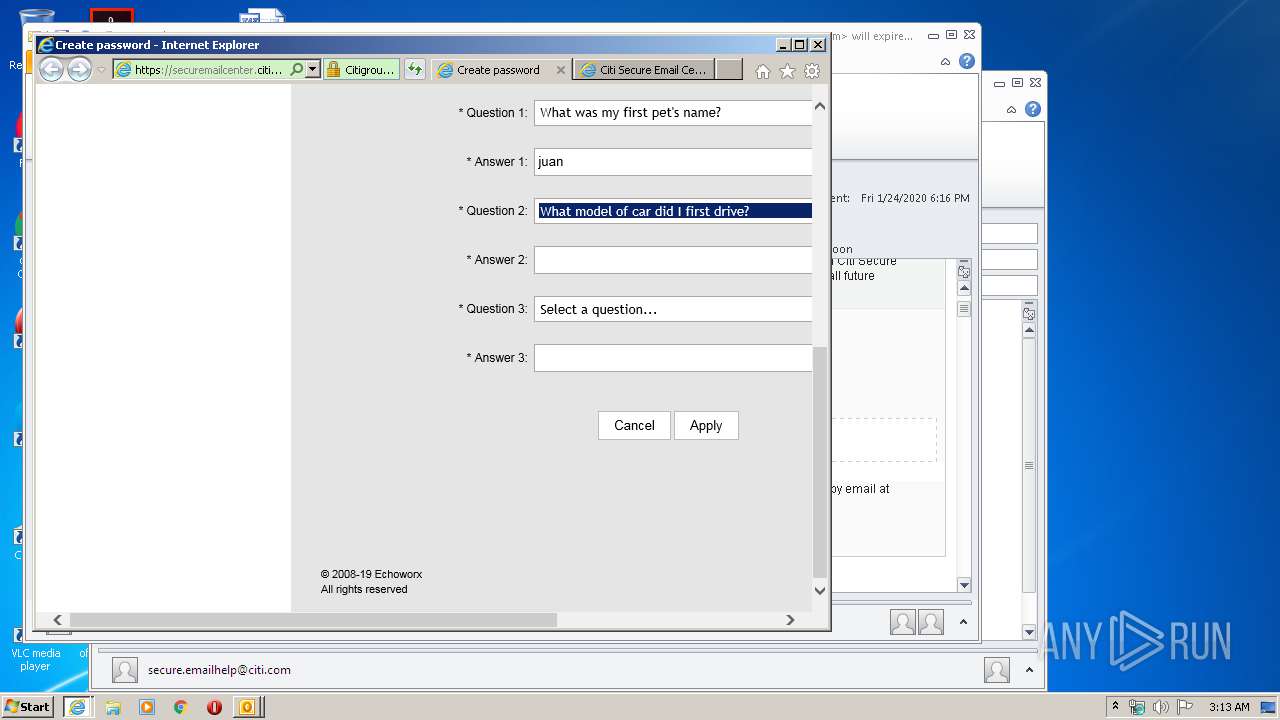
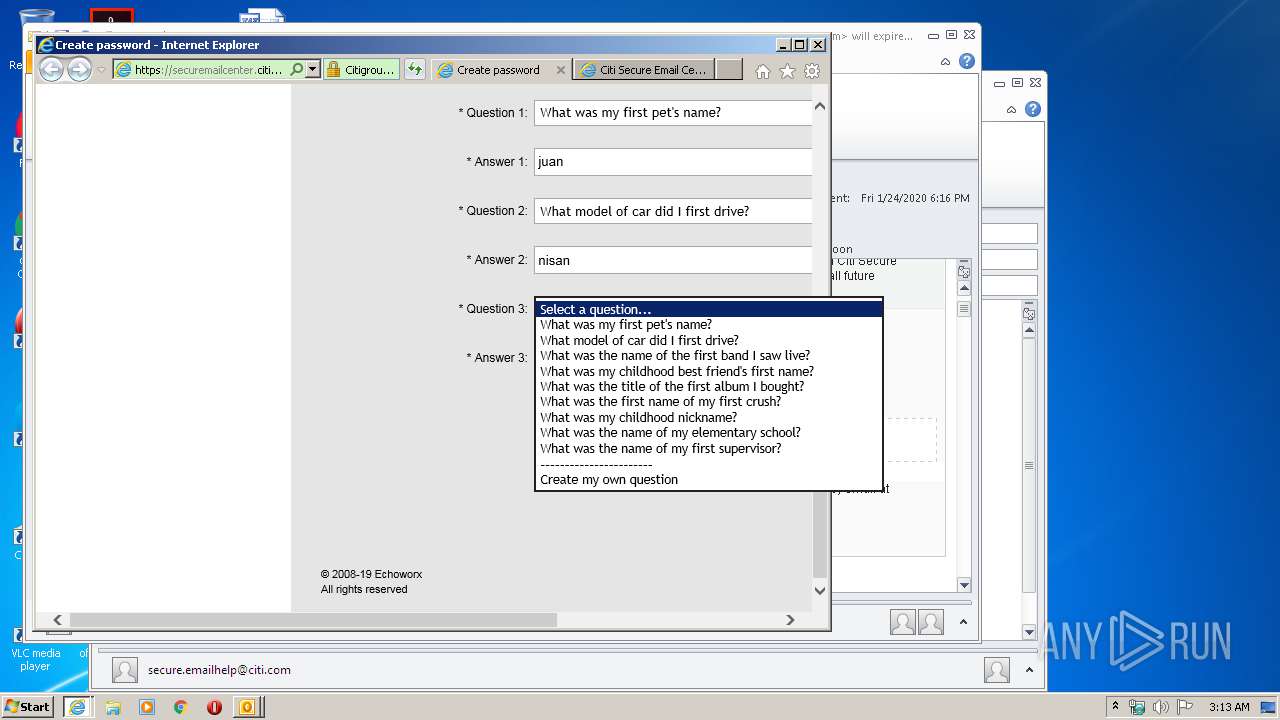
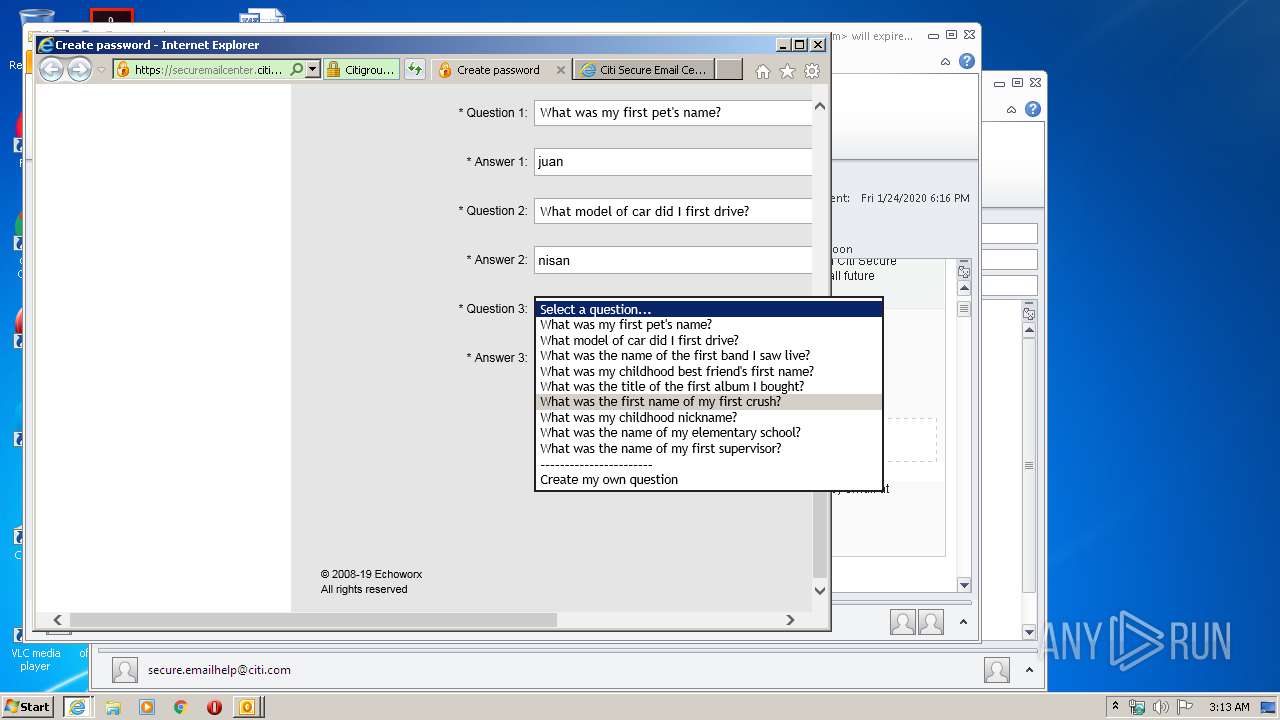
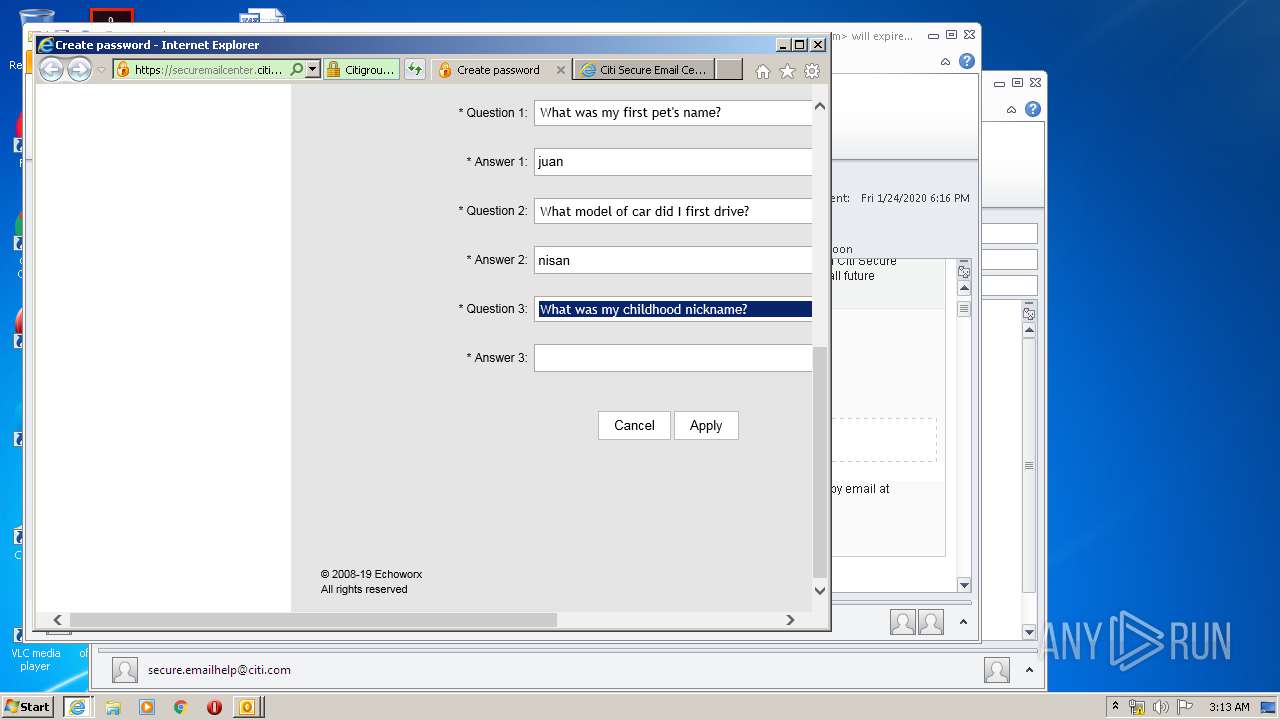
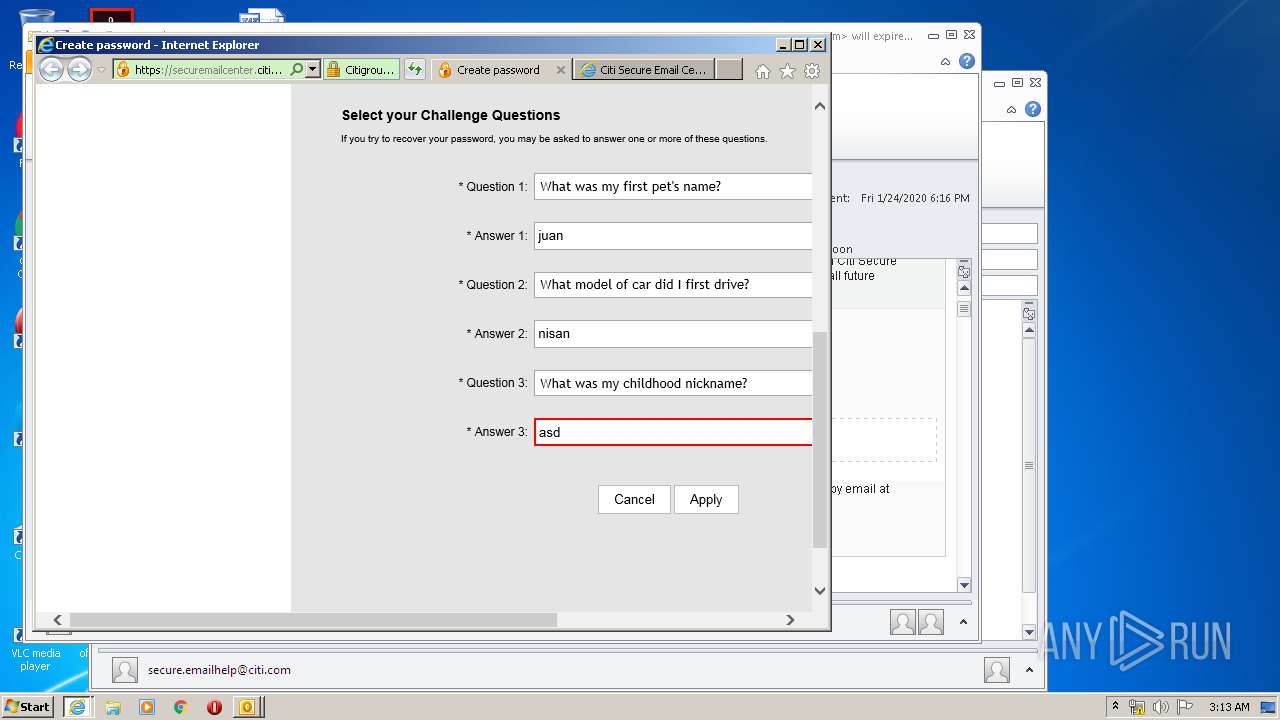
| 956 | "C:\Program Files\Internet Explorer\iexplore.exe" https://securemailcenter.citigroup.com/login.html?questionId=1c4136501d5201c0&locale=en_US | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
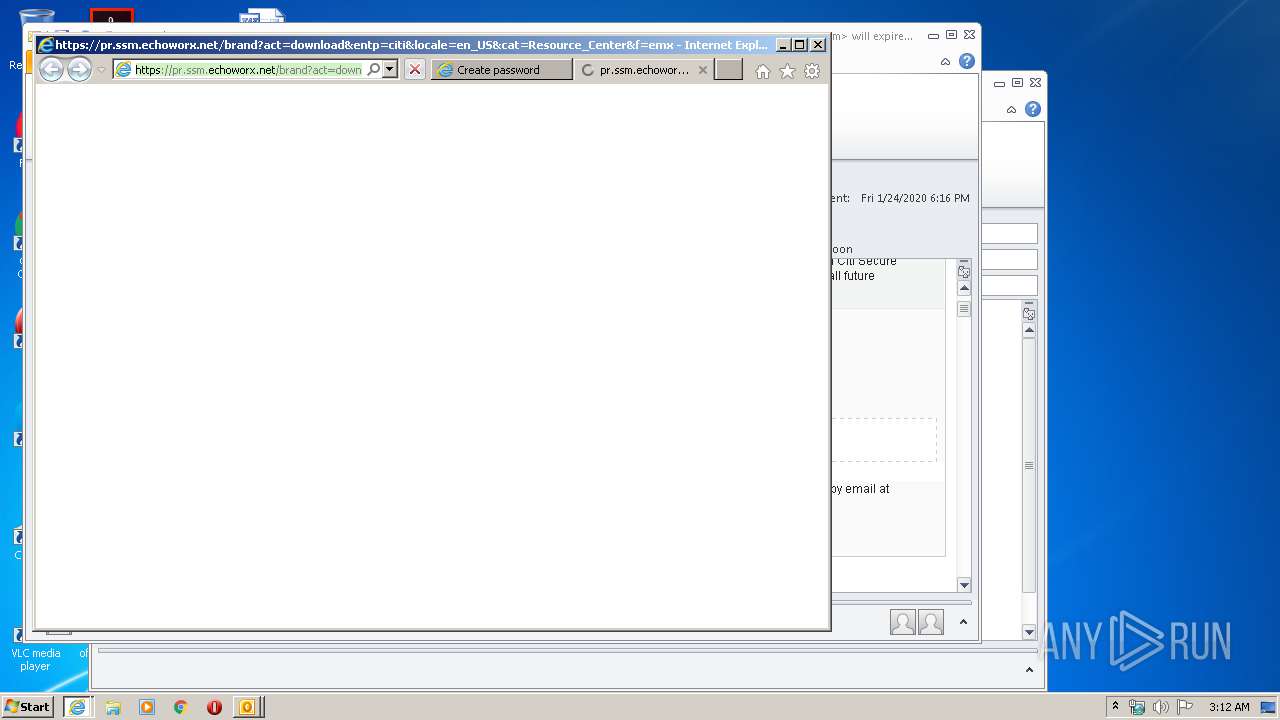
| 1248 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:956 CREDAT:2495749 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:956 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\402db1c1-ef8a-482f-ab97-1d8e6038dcd9.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2952 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" -c IPM.Note /m "mailto:secure.emailhelp@citi.com" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
10 675
Read events
2 768
Write events
5 458
Delete events
2 449
Modification events
| (PID) Process: | (2420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
25
Text files
62
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6A5B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2420 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\mso6F5D.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR963D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2388 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabA214.tmp | — | |
MD5:— | SHA256:— | |||
| 2388 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarA215.tmp | — | |
MD5:— | SHA256:— | |||
| 2388 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EAII6FQU.txt | — | |
MD5:— | SHA256:— | |||
| 2388 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\QLQ1XMVL.txt | — | |
MD5:— | SHA256:— | |||
| 2388 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C31B2498754E340573F1336DE607D619 | der | |
MD5:— | SHA256:— | |||
| 2388 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\TDRFTPJ1.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
29
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2420 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1248 | iexplore.exe | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
1248 | iexplore.exe | GET | 200 | 2.21.242.245:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgQO%2BHjn3OdoYWjlKCUFcO9CMg%3D%3D | NL | der | 527 b | whitelisted |
1248 | iexplore.exe | GET | 200 | 2.21.242.245:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgQO%2BHjn3OdoYWjlKCUFcO9CMg%3D%3D | NL | der | 527 b | whitelisted |
956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
956 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2388 | iexplore.exe | GET | 200 | 104.18.11.39:80 | http://cacerts.digicert.com/DigiCertSHA2ExtendedValidationServerCA.crt | US | der | 1.18 Kb | whitelisted |
2388 | iexplore.exe | GET | 200 | 104.18.11.39:80 | http://cacerts.digicert.com/DigiCertSHA2ExtendedValidationServerCA.crt | US | der | 1.18 Kb | whitelisted |
956 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1248 | iexplore.exe | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2420 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2388 | iexplore.exe | 104.18.11.39:80 | cacerts.digicert.com | Cloudflare Inc | US | shared |
2388 | iexplore.exe | 192.193.154.4:443 | securemailcenter.citigroup.com | Citigroup | US | suspicious |
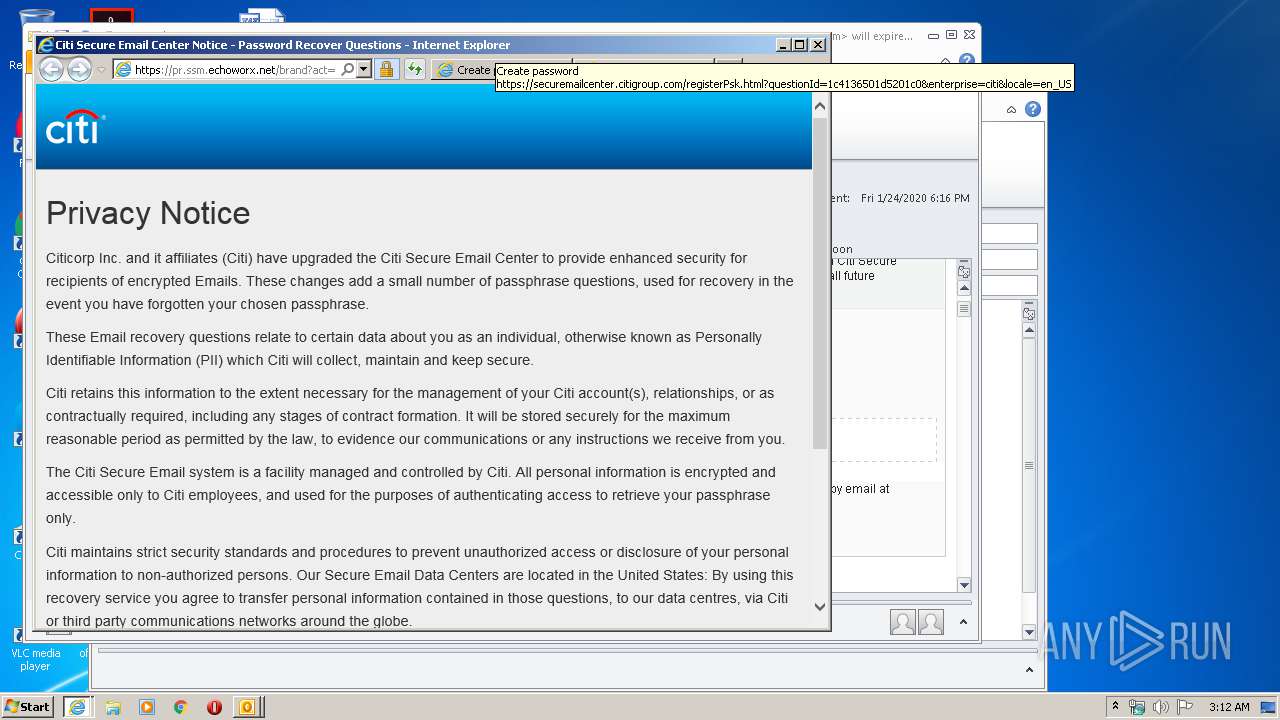
1248 | iexplore.exe | 3.133.239.31:443 | pr.ssm.echoworx.net | — | US | unknown |
1248 | iexplore.exe | 2.21.242.187:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
956 | iexplore.exe | 3.133.239.31:443 | pr.ssm.echoworx.net | — | US | unknown |
956 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
956 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 192.193.154.4:443 | securemailcenter.citigroup.com | Citigroup | US | suspicious |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
securemailcenter.citigroup.com |
| suspicious |
cacerts.digicert.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
pr.ssm.echoworx.net |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |