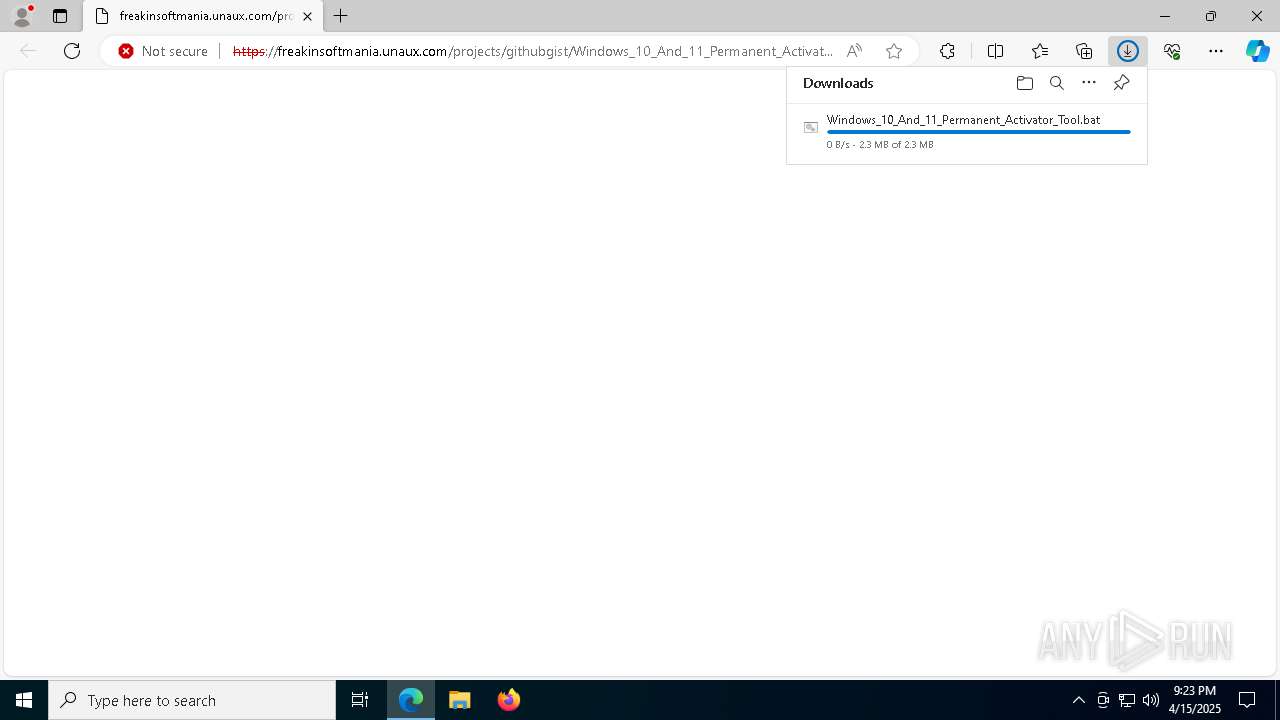
| URL: | https://freakinsoftmania.unaux.com/projects/githubgist/Windows_10_And_11_Permanent_Activator_Tool.bat |
| Full analysis: | https://app.any.run/tasks/b00884cd-916c-4853-9956-c542e6eedd71 |
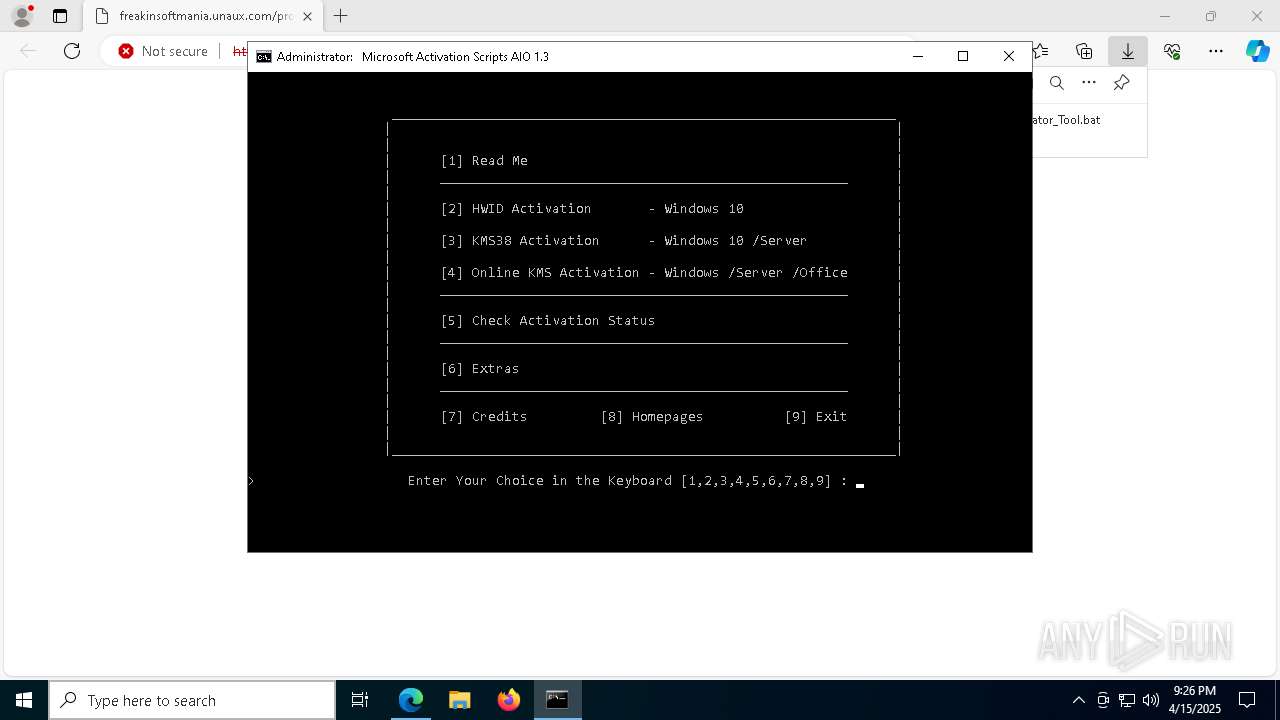
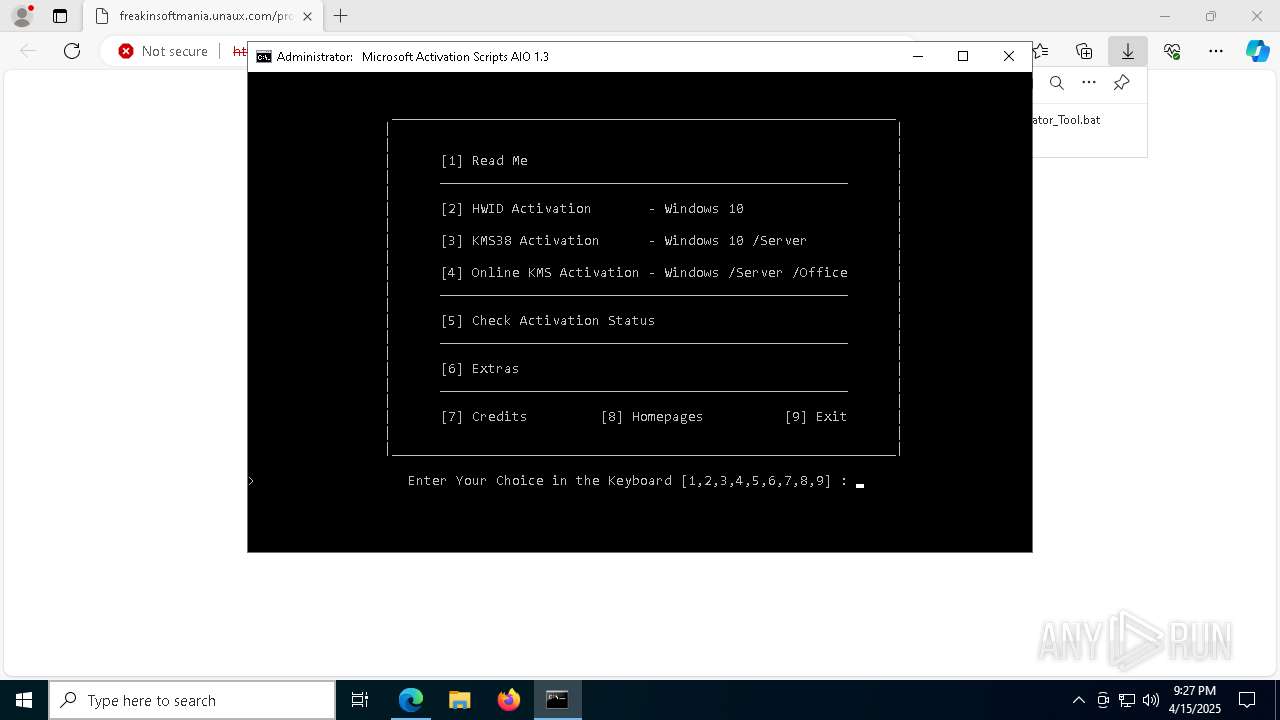
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2025, 21:23:19 |
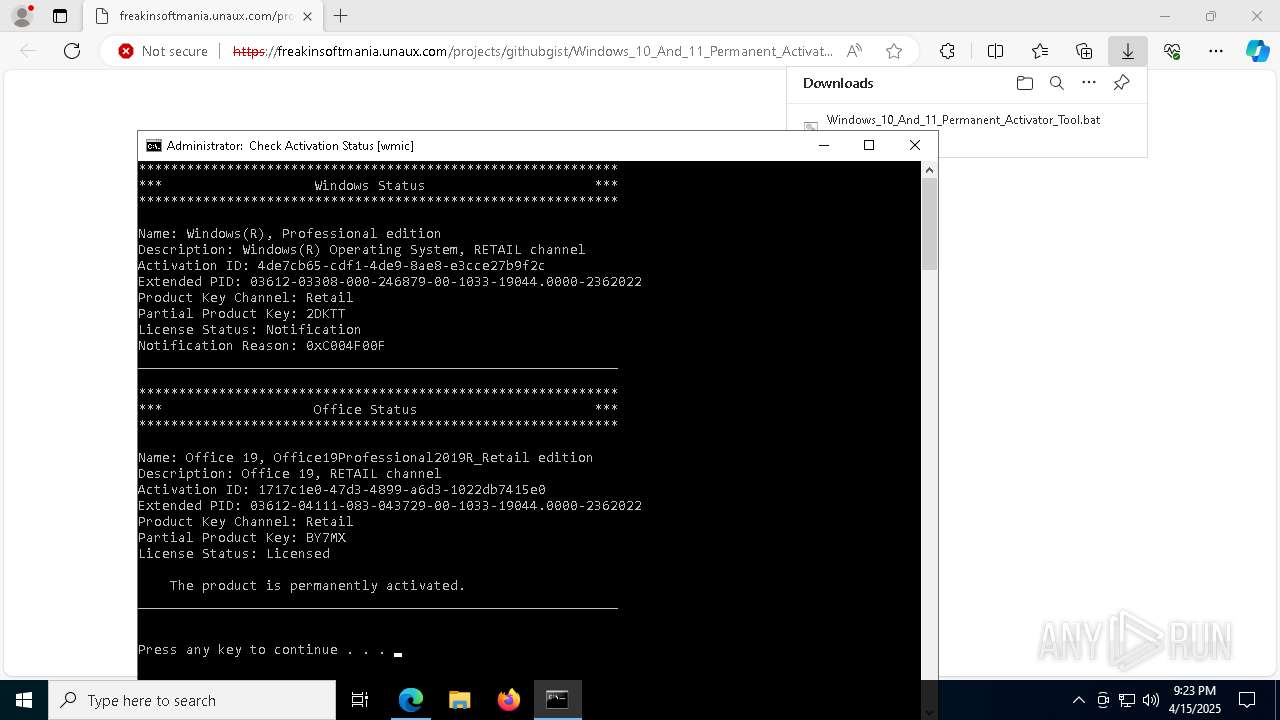
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | A5CE2E527FAEE4F9F2E7B4548CB3174E |
| SHA1: | 2FCF1B29248543ED9C983A436D31C6D863DDD88B |
| SHA256: | 6D0541EFAAB530972D56E30B379E794919C8A3F2C76CF3A48B978B47B0CE5A8C |
| SSDEEP: | 3:N82KWKNIvELb5KVXUtVDcJ2Q2gL+o7xkn:22NKZKqtcJ2QlZ7xk |
MALICIOUS
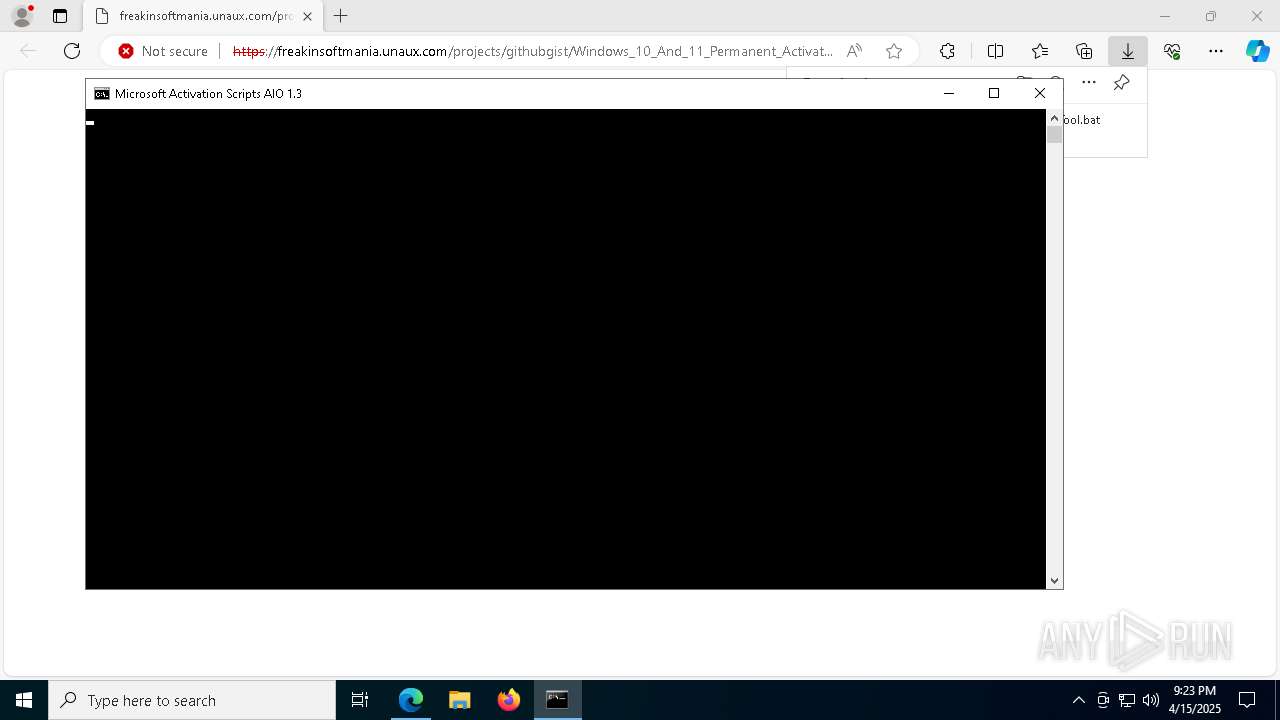
Starts CMD.EXE for commands execution
- msedge.exe (PID: 4428)
Bypass execution policy to execute commands
- powershell.exe (PID: 5800)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 7736)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 4408)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 2088)
- powershell.exe (PID: 6828)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 7848)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 732)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 7928)
- powershell.exe (PID: 4376)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 4008)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 2772)
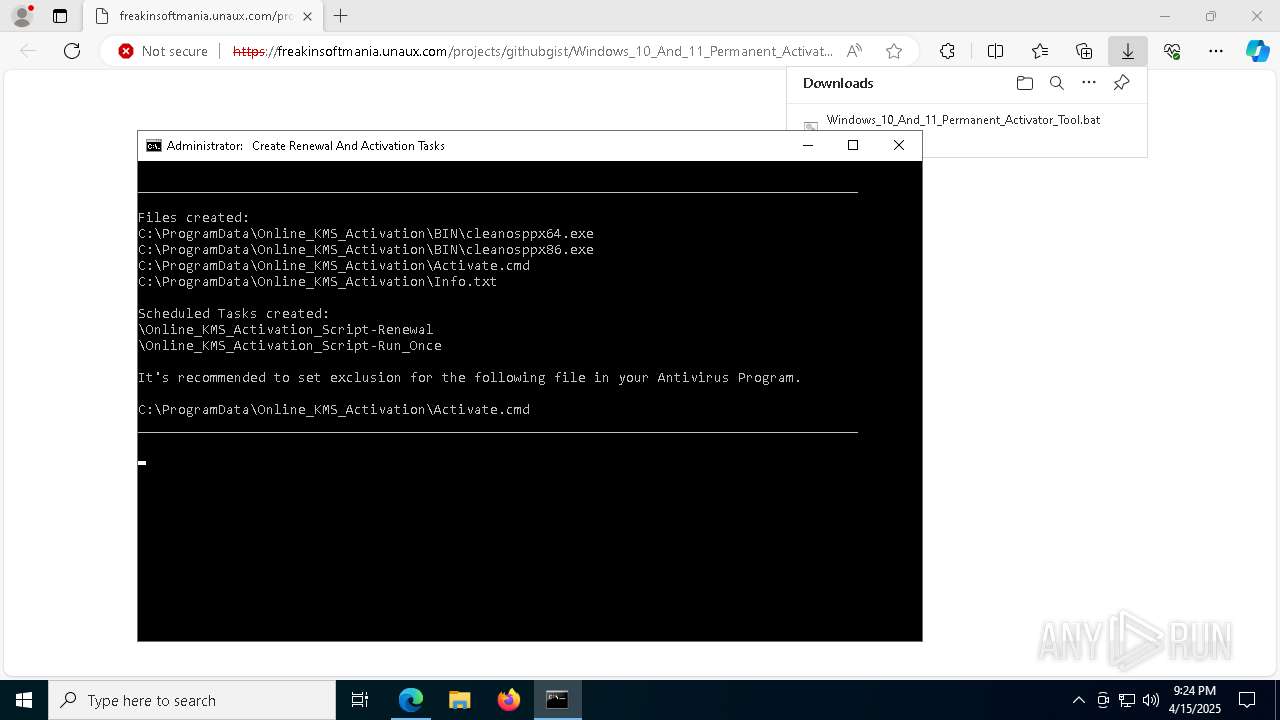
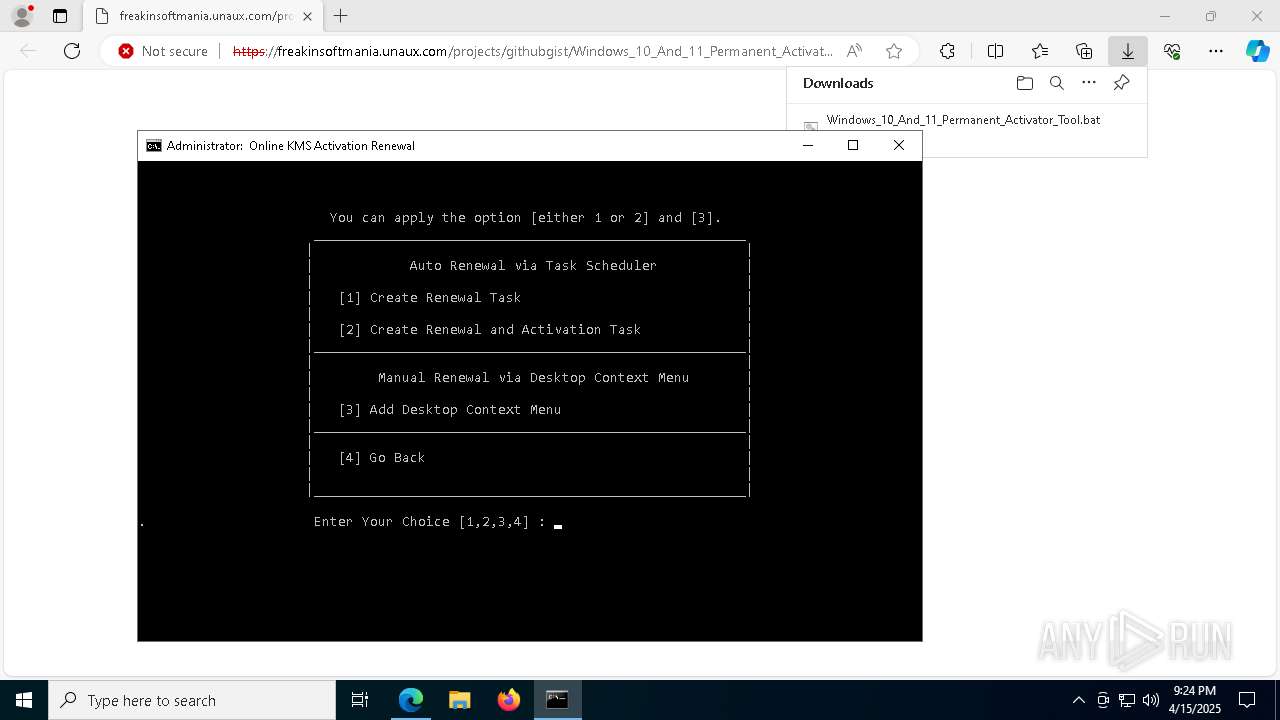
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4008)
Starts NET.EXE for service management
- cmd.exe (PID: 8140)
- net.exe (PID: 5528)
- net.exe (PID: 7864)
SUSPICIOUS
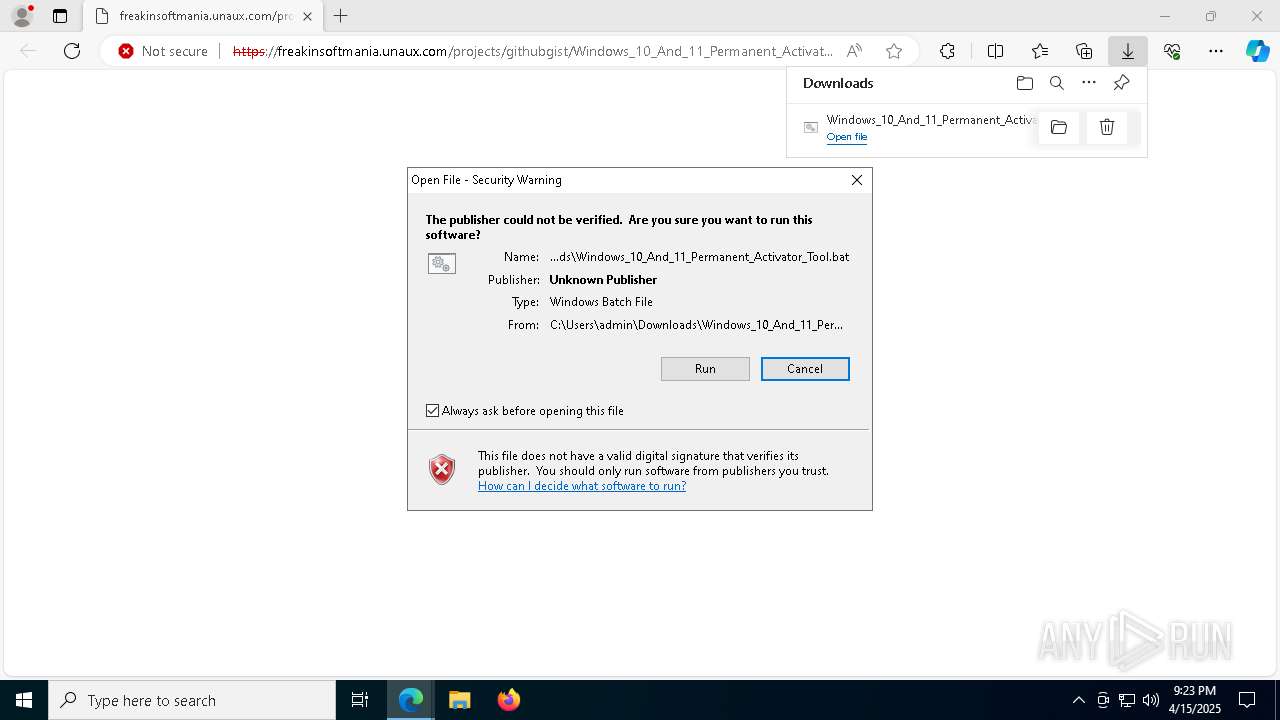
Executing commands from a ".bat" file
- msedge.exe (PID: 4428)
- cscript.exe (PID: 1168)
Application launched itself
- cmd.exe (PID: 8044)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 4008)
- cmd.exe (PID: 8140)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8044)
- cscript.exe (PID: 1168)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 4008)
- cmd.exe (PID: 8140)
The process executes VB scripts
- cmd.exe (PID: 8044)
- cmd.exe (PID: 8140)
Uses RUNDLL32.EXE to load library
- cscript.exe (PID: 1168)
Runs shell command (SCRIPT)
- cscript.exe (PID: 1168)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6516)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 1180)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 1348)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 3032)
- cmd.exe (PID: 6740)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5720)
- cmd.exe (PID: 4008)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 2772)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5720)
- cmd.exe (PID: 4008)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 2772)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5720)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 7792)
- cmd.exe (PID: 6740)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 5720)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 732)
- cmd.exe (PID: 7792)
Executes script without checking the security policy
- powershell.exe (PID: 5800)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 7736)
- powershell.exe (PID: 4408)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 2088)
- powershell.exe (PID: 6828)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 7848)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 732)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 7928)
- powershell.exe (PID: 4376)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 5720)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 5720)
- cmd.exe (PID: 4008)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 7736)
- powershell.exe (PID: 4408)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 2088)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 7848)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6108)
- csc.exe (PID: 5036)
Executable content was dropped or overwritten
- csc.exe (PID: 6108)
- expand.exe (PID: 2344)
- cmd.exe (PID: 4008)
- expand.exe (PID: 7824)
- csc.exe (PID: 5036)
Unpacks CAB file
- expand.exe (PID: 2344)
- expand.exe (PID: 7824)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 4408)
- powershell.exe (PID: 7736)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 2088)
- powershell.exe (PID: 7848)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4008)
- cmd.exe (PID: 8140)
Executing commands from ".cmd" file
- cmd.exe (PID: 5720)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5720)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 5544)
Potential TCP-based PowerShell reverse shell connection
- cmd.exe (PID: 8140)
Windows service management via SC.EXE
- sc.exe (PID: 4304)
- sc.exe (PID: 4008)
- sc.exe (PID: 5588)
- sc.exe (PID: 240)
- sc.exe (PID: 7896)
- sc.exe (PID: 7836)
- sc.exe (PID: 5344)
- sc.exe (PID: 8152)
Starts SC.EXE for service management
- cmd.exe (PID: 8140)
Connects to unusual port
- powershell.exe (PID: 6760)
- SppExtComObj.Exe (PID: 5332)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 8140)
Hides command output
- cmd.exe (PID: 7928)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 7104)
- cmd.exe (PID: 4304)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 1764)
- cmd.exe (PID: 872)
- cmd.exe (PID: 900)
- cmd.exe (PID: 4172)
- cmd.exe (PID: 5364)
- cmd.exe (PID: 1004)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 4212)
- cmd.exe (PID: 6424)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 812)
- cmd.exe (PID: 7584)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 7712)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 7712)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 812)
INFO
Application launched itself
- msedge.exe (PID: 4428)
Reads the computer name
- identity_helper.exe (PID: 4608)
Checks supported languages
- identity_helper.exe (PID: 4608)
- mode.com (PID: 4464)
- mode.com (PID: 1324)
- mode.com (PID: 7992)
- mode.com (PID: 2772)
- csc.exe (PID: 6108)
- cvtres.exe (PID: 1568)
- expand.exe (PID: 2344)
- mode.com (PID: 4488)
- mode.com (PID: 7084)
- mode.com (PID: 5332)
- csc.exe (PID: 5036)
- cvtres.exe (PID: 3364)
- expand.exe (PID: 7824)
- mode.com (PID: 5984)
- mode.com (PID: 3032)
- mode.com (PID: 5136)
- mode.com (PID: 8168)
- mode.com (PID: 1616)
- mode.com (PID: 4304)
- mode.com (PID: 7888)
- mode.com (PID: 4980)
- mode.com (PID: 3396)
- mode.com (PID: 5204)
- mode.com (PID: 7752)
Checks operating system version
- cmd.exe (PID: 8044)
- cmd.exe (PID: 5720)
- cmd.exe (PID: 4008)
- cmd.exe (PID: 8140)
Reads Environment values
- identity_helper.exe (PID: 4608)
Reads security settings of Internet Explorer
- cscript.exe (PID: 1168)
- WMIC.exe (PID: 5964)
- WMIC.exe (PID: 5504)
- WMIC.exe (PID: 780)
- WMIC.exe (PID: 3100)
- WMIC.exe (PID: 1272)
- WMIC.exe (PID: 5608)
- WMIC.exe (PID: 6668)
- WMIC.exe (PID: 780)
- WMIC.exe (PID: 6252)
- WMIC.exe (PID: 7252)
- WMIC.exe (PID: 3156)
- WMIC.exe (PID: 7104)
- WMIC.exe (PID: 5260)
- WMIC.exe (PID: 7792)
- WMIC.exe (PID: 6132)
- WMIC.exe (PID: 6852)
- WMIC.exe (PID: 3396)
- WMIC.exe (PID: 7696)
- WMIC.exe (PID: 7828)
- WMIC.exe (PID: 7852)
- WMIC.exe (PID: 7928)
- WMIC.exe (PID: 7880)
- WMIC.exe (PID: 8188)
- WMIC.exe (PID: 924)
- WMIC.exe (PID: 2064)
- WMIC.exe (PID: 4740)
- WMIC.exe (PID: 6252)
- WMIC.exe (PID: 5188)
- cscript.exe (PID: 7712)
- WMIC.exe (PID: 7420)
- WMIC.exe (PID: 4692)
- WMIC.exe (PID: 7104)
- WMIC.exe (PID: 4408)
- WMIC.exe (PID: 2656)
- WMIC.exe (PID: 2516)
- WMIC.exe (PID: 7696)
- WMIC.exe (PID: 7860)
- WMIC.exe (PID: 5812)
- WMIC.exe (PID: 7632)
- WMIC.exe (PID: 1912)
- WMIC.exe (PID: 2108)
- WMIC.exe (PID: 4696)
- WMIC.exe (PID: 6252)
- WMIC.exe (PID: 6136)
- WMIC.exe (PID: 7604)
- WMIC.exe (PID: 5892)
- WMIC.exe (PID: 516)
- WMIC.exe (PID: 8072)
- WMIC.exe (PID: 7020)
- WMIC.exe (PID: 4572)
- WMIC.exe (PID: 2420)
- WMIC.exe (PID: 7732)
- WMIC.exe (PID: 6576)
- WMIC.exe (PID: 3028)
- WMIC.exe (PID: 456)
- WMIC.exe (PID: 2420)
- WMIC.exe (PID: 8064)
- WMIC.exe (PID: 5556)
- WMIC.exe (PID: 2236)
- WMIC.exe (PID: 7880)
- WMIC.exe (PID: 1912)
- WMIC.exe (PID: 4224)
- WMIC.exe (PID: 7732)
- WMIC.exe (PID: 8160)
Starts MODE.COM to configure console settings
- mode.com (PID: 4464)
- mode.com (PID: 1324)
- mode.com (PID: 2772)
- mode.com (PID: 7992)
- mode.com (PID: 4488)
- mode.com (PID: 7084)
- mode.com (PID: 5332)
- mode.com (PID: 5984)
- mode.com (PID: 3032)
- mode.com (PID: 5136)
- mode.com (PID: 8168)
- mode.com (PID: 1616)
- mode.com (PID: 7888)
- mode.com (PID: 4304)
- mode.com (PID: 4980)
- mode.com (PID: 3396)
- mode.com (PID: 5204)
- mode.com (PID: 7752)
Reads the machine GUID from the registry
- csc.exe (PID: 6108)
- expand.exe (PID: 2344)
- csc.exe (PID: 5036)
- expand.exe (PID: 7824)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 7736)
- powershell.exe (PID: 4408)
- powershell.exe (PID: 5556)
- powershell.exe (PID: 2088)
- powershell.exe (PID: 8160)
- powershell.exe (PID: 7848)
Create files in a temporary directory
- csc.exe (PID: 6108)
- cvtres.exe (PID: 1568)
- csc.exe (PID: 5036)
- cvtres.exe (PID: 3364)
Creates files in the program directory
- cmd.exe (PID: 4008)
- powershell.exe (PID: 2088)
Reads the software policy settings
- slui.exe (PID: 7908)
Reads Microsoft Office registry keys
- reg.exe (PID: 1096)
- reg.exe (PID: 7732)
- reg.exe (PID: 7796)
- reg.exe (PID: 6576)
- reg.exe (PID: 7704)
- reg.exe (PID: 968)
- reg.exe (PID: 616)
The sample compiled with english language support
- msedge.exe (PID: 7420)
Executable content was dropped or overwritten
- msedge.exe (PID: 7420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
697
Monitored processes
558
Malicious processes
14
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\WINDOWS\system32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | findstr /I /C:"StandardRetail" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | findstr /I /C:"O365EduCloudRetail" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
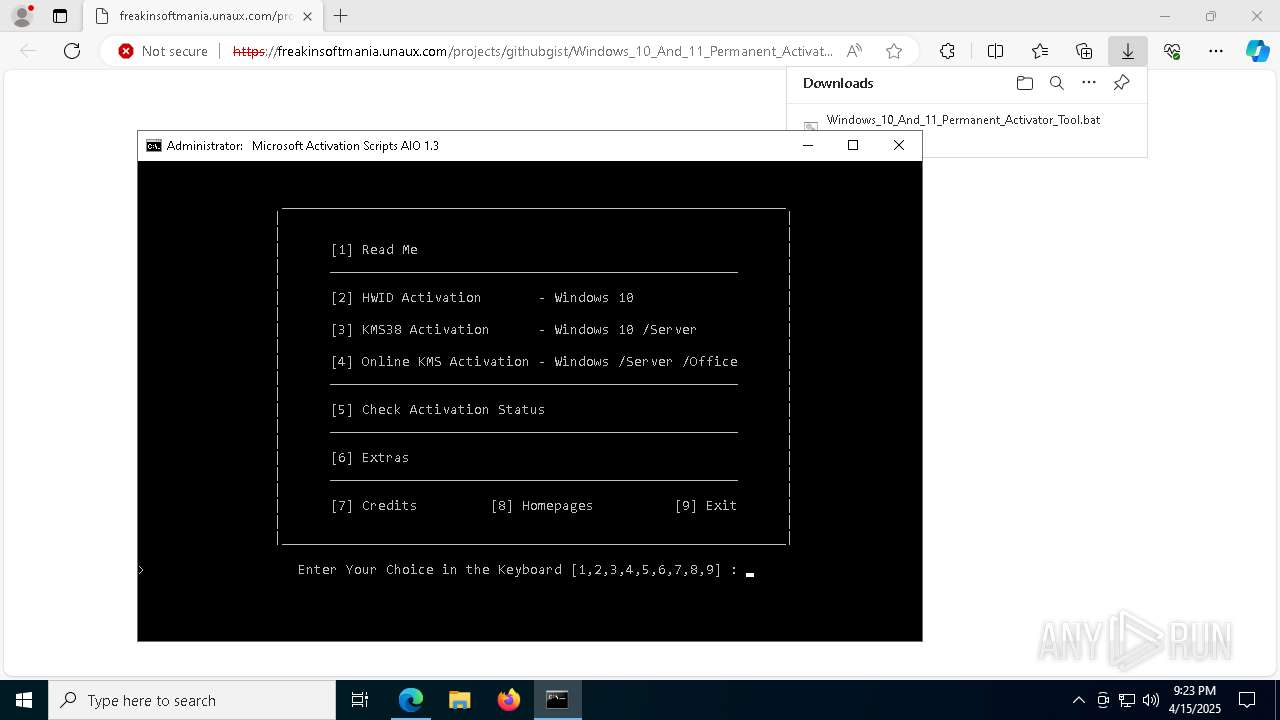
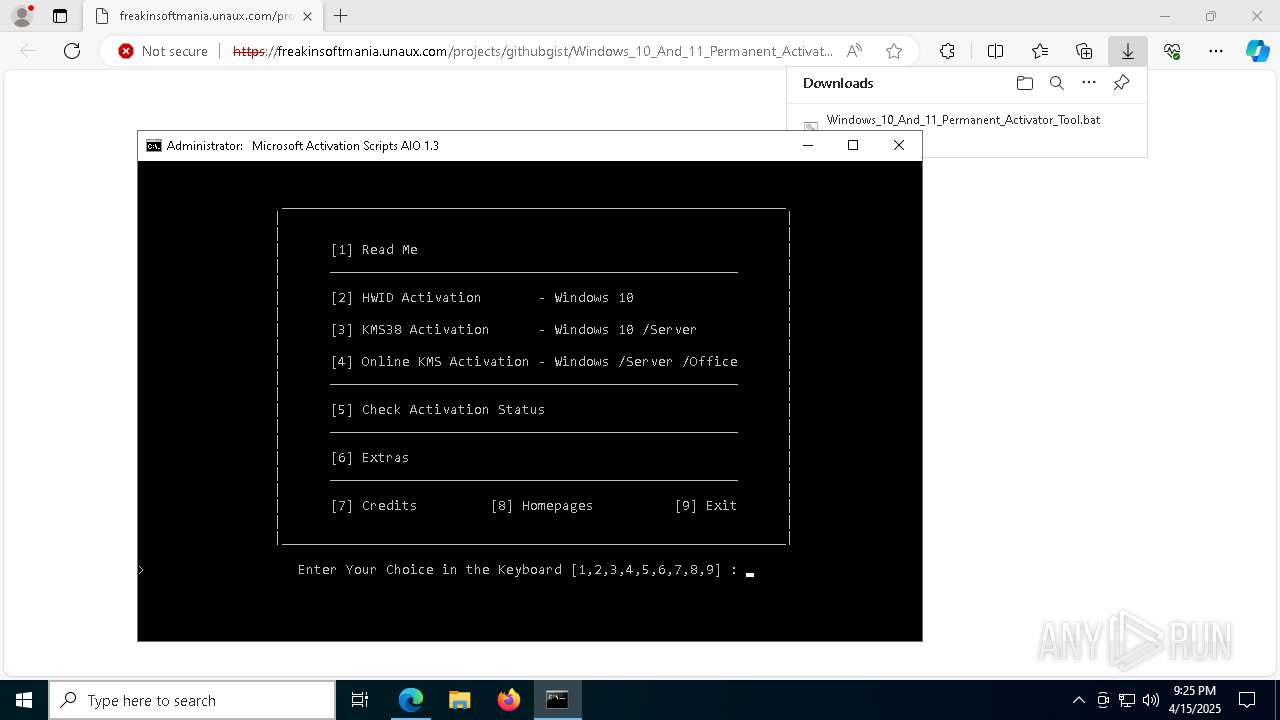
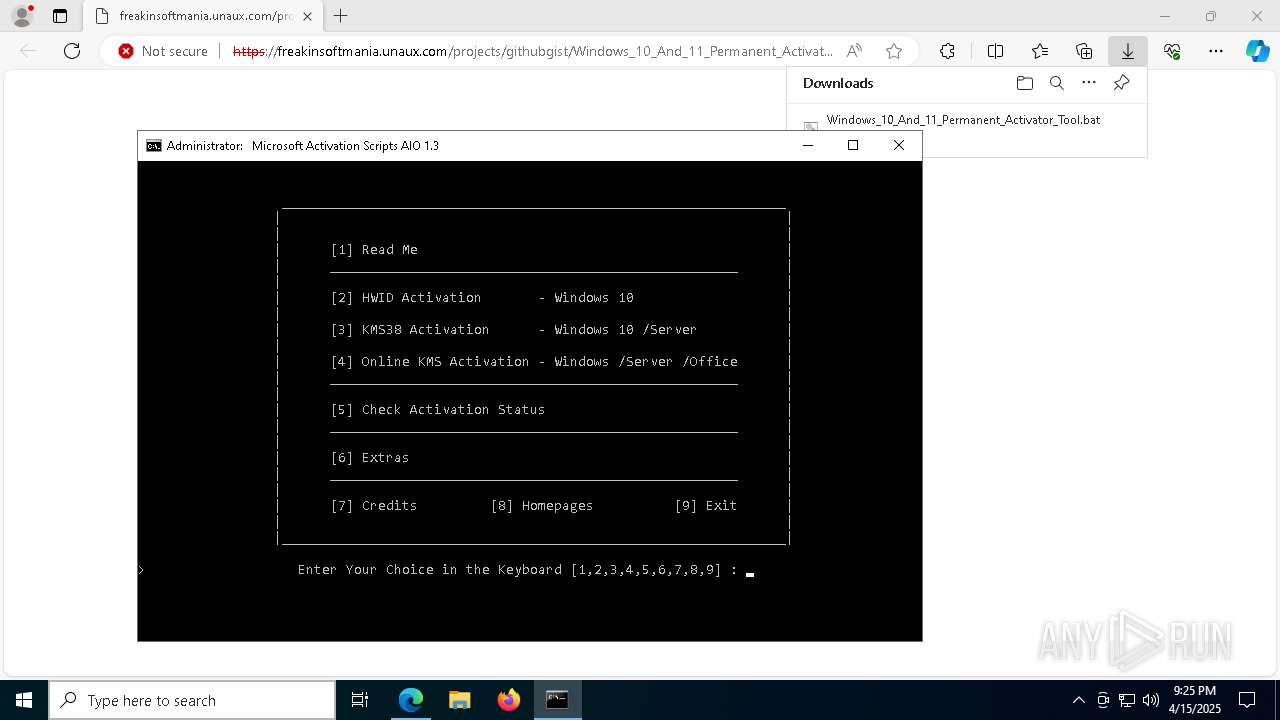
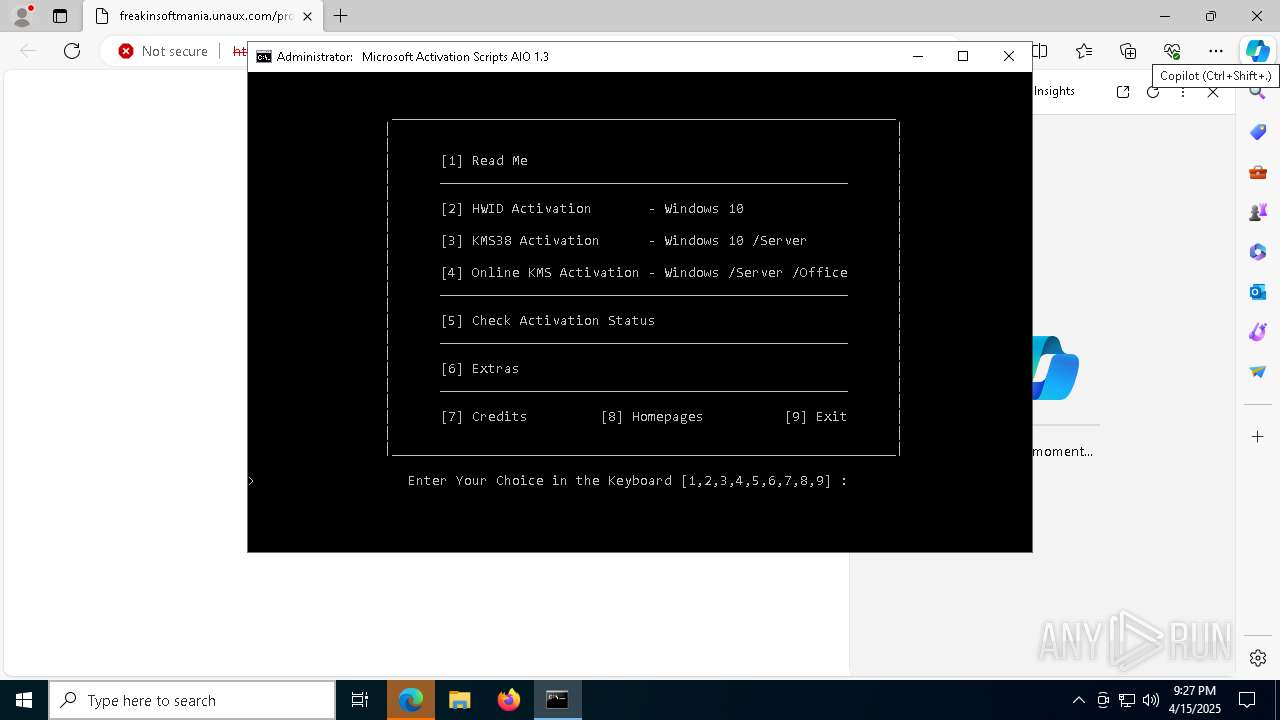
| 236 | choice /C:123456789 /N /M "> Enter Your Choice in the Keyboard [1,2,3,4,5,6,7,8,9] : " | C:\Windows\System32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | findstr /I /C:"ProjectStdVolume" "C:\WINDOWS\Temp\c2rchk.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | sc query OfficeSvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | reg query HKLM\SOFTWARE\Microsoft\Office\ClickToRun\ProductReleaseIDs\5B9936B4-3789-47CD-A7E1-A479148E7D7F\ProPlusRetail.16 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | wmic path SoftwareLicensingProduct where (ApplicationID='55c92734-d682-4d71-983e-d6ec3f16059f' and PartialProductKey is not null) get ID /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7424 --field-trial-handle=2324,i,12895035488758504940,6215035513937471896,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7028 --field-trial-handle=2324,i,12895035488758504940,6215035513937471896,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
115 258
Read events
115 236
Write events
22
Delete events
0
Modification events
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6D2CE30F6E912F00 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FF7BF60F6E912F00 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7C8BC0B9-E95A-4162-91A5-19B1D504F379} | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C7EBCDD2-FC24-4E91-8AE0-6323CDD33838} | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C6952B48-FA1A-45CB-AB88-D5C596E380E3} | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {67D509BD-FA73-4F9B-9128-A1ACC37306C9} | |||
Executable files
25
Suspicious files
544
Text files
159
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b43e.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b43e.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b44e.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b45e.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b45e.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
68
DNS requests
89
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7336 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://zerossl.crt.sectigo.com/ZeroSSLRSADomainSecureSiteCA.crt | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.169:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7336 | msedge.exe | GET | 204 | 150.171.73.11:80 | http://edge-http.microsoft.com/captiveportal/generate_204 | unknown | — | — | whitelisted |
7336 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | unknown | — | — | whitelisted |
6516 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7036 | svchost.exe | HEAD | 200 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745355046&P2=404&P3=2&P4=FoC7Q%2ftcT6cHqJ0HJ3azsMUmwWoWesVnuuBKZtGK8geumZ2rWw5QD87i2g1DuyZOww5hxe9aVmb8LwEvKc%2fMWQ%3d%3d | unknown | — | — | whitelisted |
6516 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7036 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745355046&P2=404&P3=2&P4=FoC7Q%2ftcT6cHqJ0HJ3azsMUmwWoWesVnuuBKZtGK8geumZ2rWw5QD87i2g1DuyZOww5hxe9aVmb8LwEvKc%2fMWQ%3d%3d | unknown | — | — | whitelisted |
7036 | svchost.exe | GET | 206 | 208.89.74.17:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745355046&P2=404&P3=2&P4=FoC7Q%2ftcT6cHqJ0HJ3azsMUmwWoWesVnuuBKZtGK8geumZ2rWw5QD87i2g1DuyZOww5hxe9aVmb8LwEvKc%2fMWQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 23.48.23.169:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4428 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7336 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7336 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7336 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7336 | msedge.exe | 185.27.134.221:443 | freakinsoftmania.unaux.com | Wildcard UK Limited | GB | whitelisted |
7336 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
freakinsoftmania.unaux.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
zerossl.crt.sectigo.com |
| whitelisted |
crt.usertrust.com |
| whitelisted |