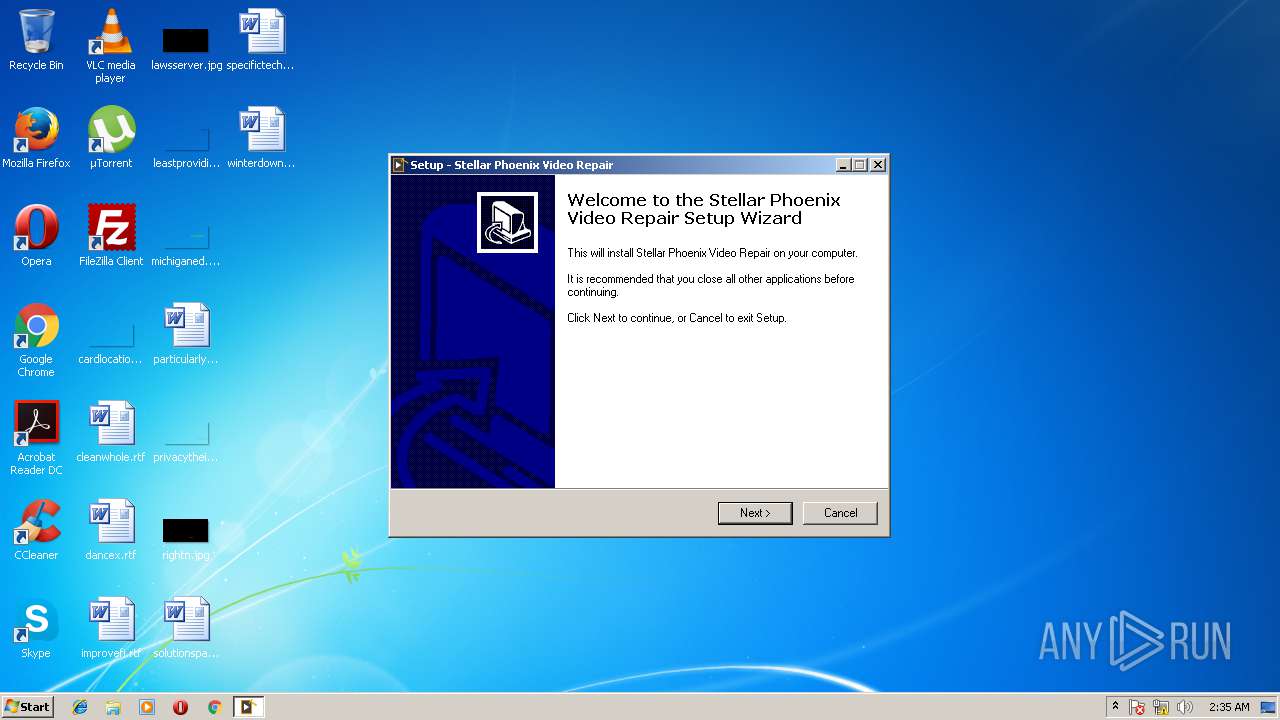
| download: | StellarPhoenixVideoRepair.exe |
| Full analysis: | https://app.any.run/tasks/69259975-c07e-456f-86c5-663b23d73bca |
| Verdict: | No threats detected |
| Analysis date: | June 07, 2018, 01:34:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8EB2F8F180E729819A5F1DE8FBD96B5F |
| SHA1: | 28913BDB673E9C657F5FB975B5716D79181EE118 |
| SHA256: | 6CFE07A744AAAB6F0F5D8504F46F35EA57A87AC075349FE436D25ABC1448F0E0 |
| SSDEEP: | 393216:UEm0zFFje2+SwiKFfb6uqEoAeVzv9fpJ6qgco/6rBg8j01QSYDZEZK0:UEmUte9SW7viz6co/6rBzj0jYa5 |
MALICIOUS
Loads dropped or rewritten executable
- spvr.exe (PID: 3076)
Application was dropped or rewritten from another process
- EKAG20NT.EXE (PID: 3720)
- spvr.exe (PID: 3900)
- spvr.exe (PID: 3076)
SUSPICIOUS
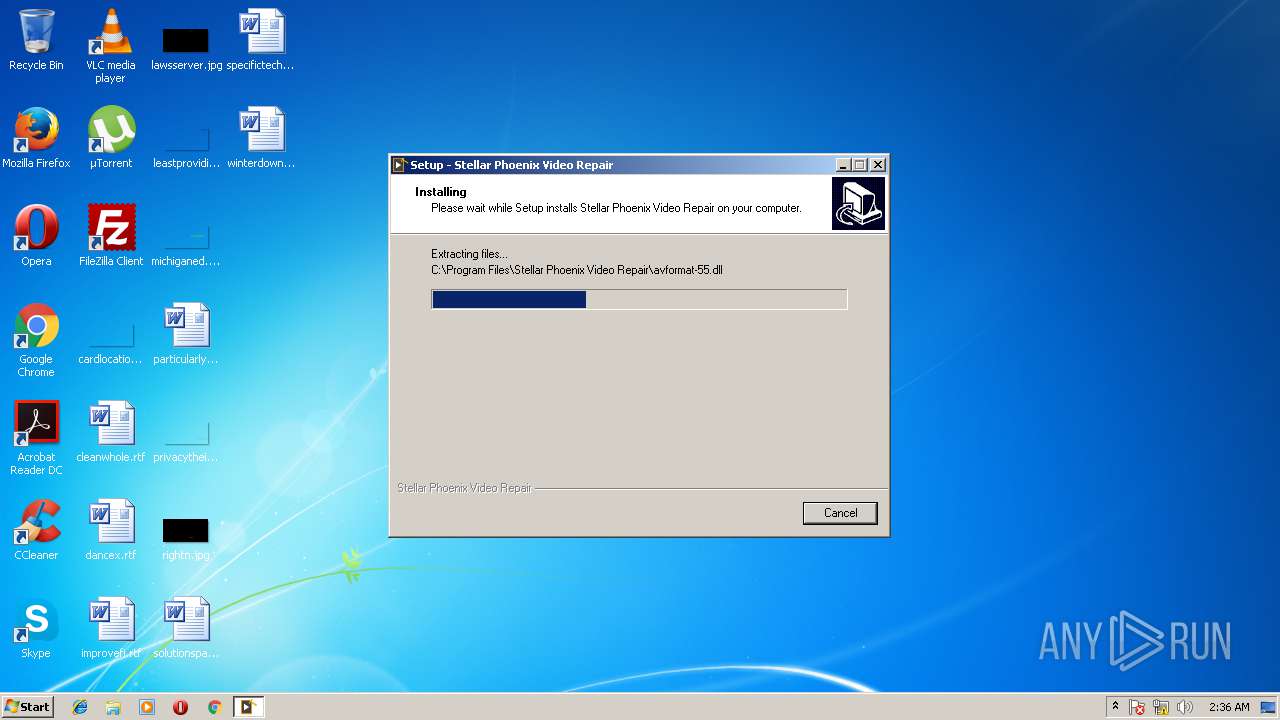
Executable content was dropped or overwritten
- StellarPhoenixVideoRepair.tmp (PID: 3468)
- StellarPhoenixVideoRepair.exe (PID: 2092)
- StellarPhoenixVideoRepair.exe (PID: 4024)
Creates files in the program directory
- EKAG20NT.EXE (PID: 3720)
INFO
Dropped object may contain URL's
- StellarPhoenixVideoRepair.exe (PID: 2092)
- StellarPhoenixVideoRepair.exe (PID: 4024)
- StellarPhoenixVideoRepair.tmp (PID: 3468)
Application was dropped or rewritten from another process
- StellarPhoenixVideoRepair.tmp (PID: 2668)
- StellarPhoenixVideoRepair.tmp (PID: 3468)
Loads dropped or rewritten executable
- StellarPhoenixVideoRepair.tmp (PID: 3468)
Creates files in the program directory
- StellarPhoenixVideoRepair.tmp (PID: 3468)
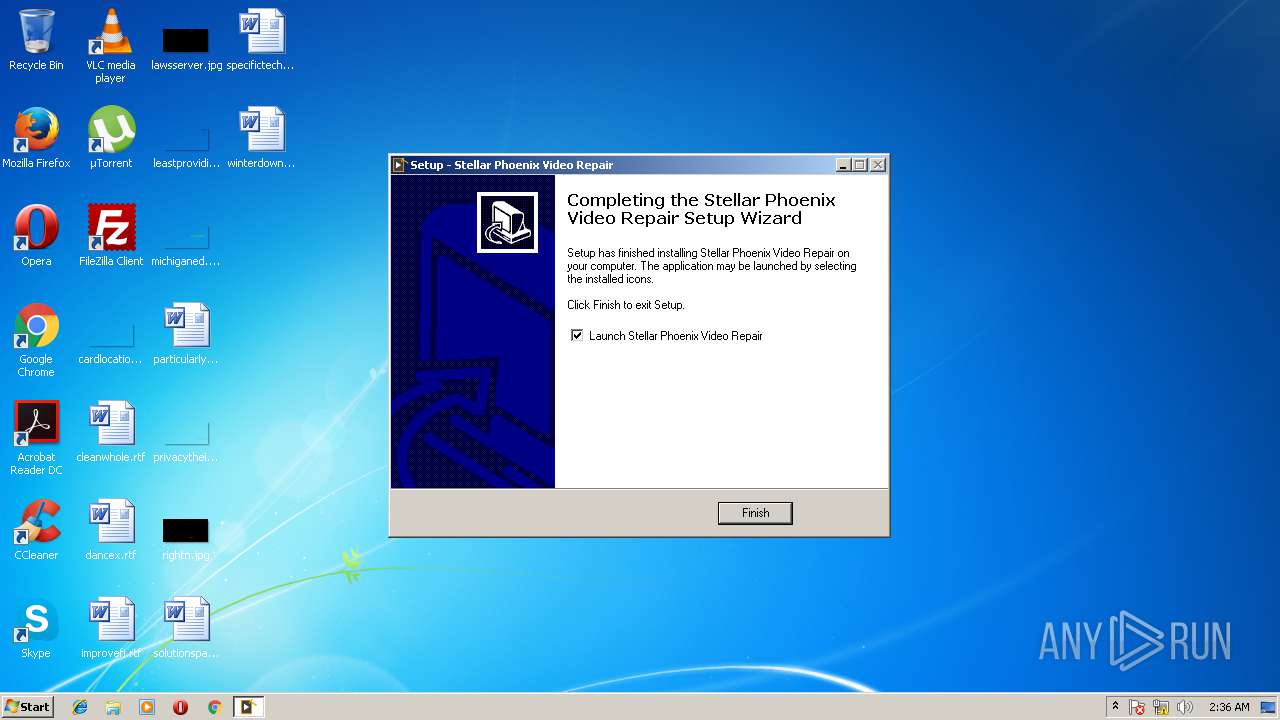
Creates a software uninstall entry
- StellarPhoenixVideoRepair.tmp (PID: 3468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (91.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (3.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 134656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b24 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.0.0 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
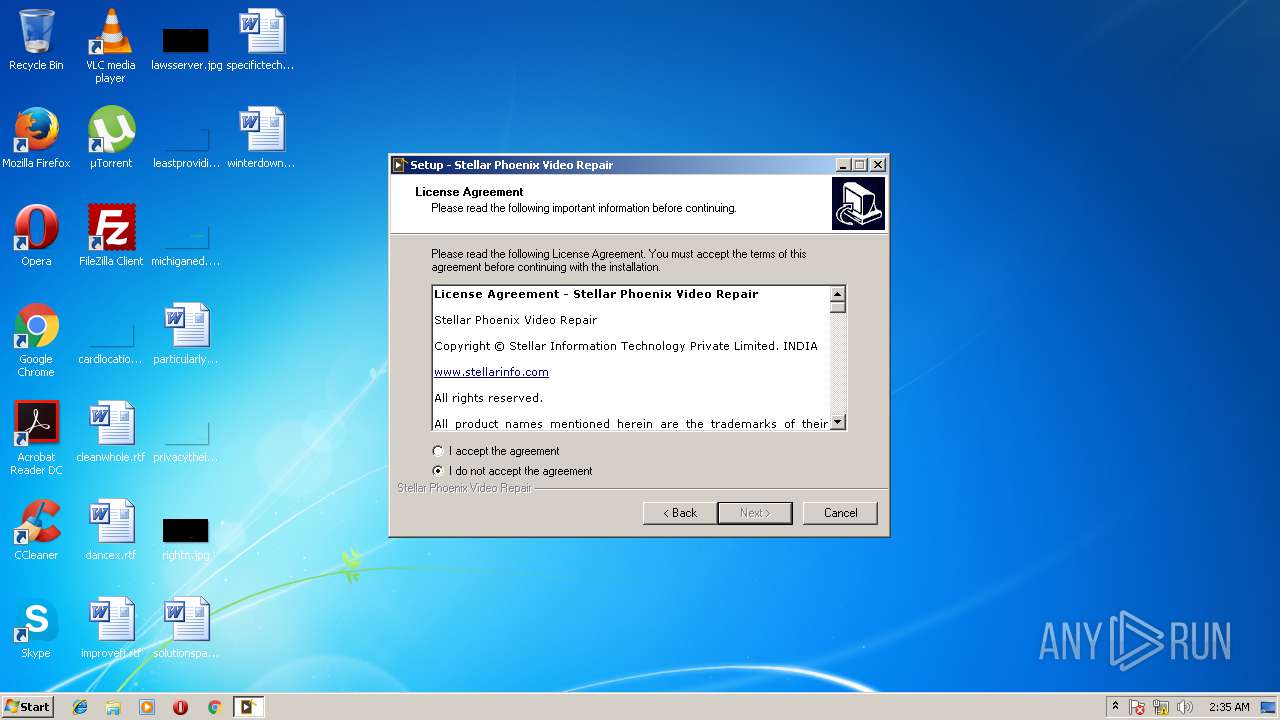
| CompanyName: | Stellar Information Technology Pvt Ltd |
| FileDescription: | Stellar Information Technology Pvt Ltd. |
| FileVersion: | 3.0.0.0 |
| LegalCopyright: | Stellar Information Technology Pvt Ltd. |
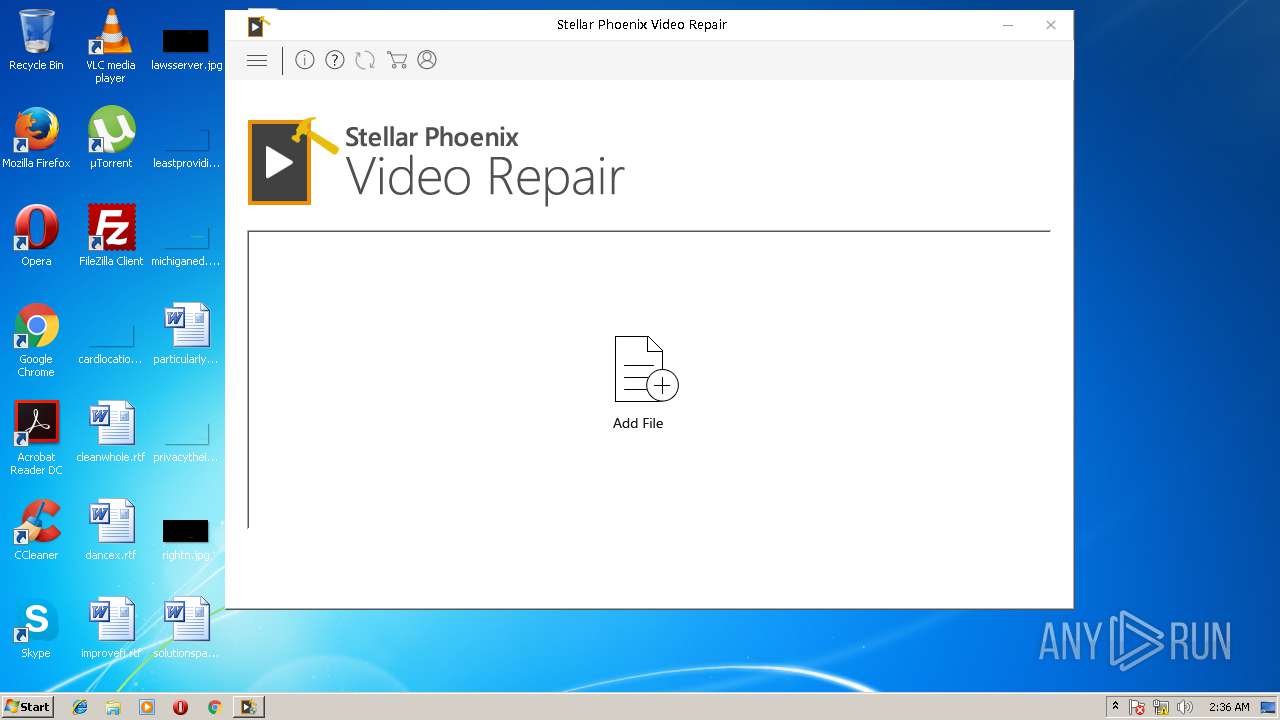
| ProductName: | Stellar Phoenix Video Repair |
| ProductVersion: | 3.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Stellar Information Technology Pvt Ltd |
| FileDescription: | Stellar Information Technology Pvt Ltd. |
| FileVersion: | 3.0.0.0 |
| LegalCopyright: | Stellar Information Technology Pvt Ltd. |
| ProductName: | Stellar Phoenix Video Repair |
| ProductVersion: | 3.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009244 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52973 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.7347 |
BSS | 0x0000C000 | 0x00000E48 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x0001FC44 | 0x0001FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.49735 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.37612 | 21640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.2352 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.79746 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.81249 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.42341 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.18132 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
46
Monitored processes
7
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2092 | "C:\Users\admin\AppData\Local\Temp\StellarPhoenixVideoRepair.exe" | C:\Users\admin\AppData\Local\Temp\StellarPhoenixVideoRepair.exe | explorer.exe | ||||||||||||
User: admin Company: Stellar Information Technology Pvt Ltd Integrity Level: MEDIUM Description: Stellar Information Technology Pvt Ltd. Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 2668 | "C:\Users\admin\AppData\Local\Temp\is-GUOA8.tmp\StellarPhoenixVideoRepair.tmp" /SL5="$B0226,20926547,173568,C:\Users\admin\AppData\Local\Temp\StellarPhoenixVideoRepair.exe" | C:\Users\admin\AppData\Local\Temp\is-GUOA8.tmp\StellarPhoenixVideoRepair.tmp | — | StellarPhoenixVideoRepair.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 3076 | "C:\Program Files\Stellar Phoenix Video Repair\spvr.exe" | C:\Program Files\Stellar Phoenix Video Repair\spvr.exe | StellarPhoenixVideoRepair.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3468 | "C:\Users\admin\AppData\Local\Temp\is-16LMF.tmp\StellarPhoenixVideoRepair.tmp" /SL5="$90146,20926547,173568,C:\Users\admin\AppData\Local\Temp\StellarPhoenixVideoRepair.exe" /SPAWNWND=$901A4 /NOTIFYWND=$B0226 | C:\Users\admin\AppData\Local\Temp\is-16LMF.tmp\StellarPhoenixVideoRepair.tmp | StellarPhoenixVideoRepair.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 3720 | "C:\Program Files\Stellar Phoenix Video Repair\EKAG20NT.EXE" 0200906578FD5A5A 0 | C:\Program Files\Stellar Phoenix Video Repair\EKAG20NT.EXE | — | spvr.exe | |||||||||||
User: admin Company: Software Security System Integrity Level: HIGH Description: EK Agent (Interface version SRV 2.01) Exit code: 0 Version: 2.0.8.40 Modules
| |||||||||||||||
| 3900 | "C:\Program Files\Stellar Phoenix Video Repair\spvr.exe" | C:\Program Files\Stellar Phoenix Video Repair\spvr.exe | — | StellarPhoenixVideoRepair.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4024 | "C:\Users\admin\AppData\Local\Temp\StellarPhoenixVideoRepair.exe" /SPAWNWND=$901A4 /NOTIFYWND=$B0226 | C:\Users\admin\AppData\Local\Temp\StellarPhoenixVideoRepair.exe | StellarPhoenixVideoRepair.tmp | ||||||||||||
User: admin Company: Stellar Information Technology Pvt Ltd Integrity Level: HIGH Description: Stellar Information Technology Pvt Ltd. Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
Total events
1 477
Read events
1 303
Write events
174
Delete events
0
Modification events
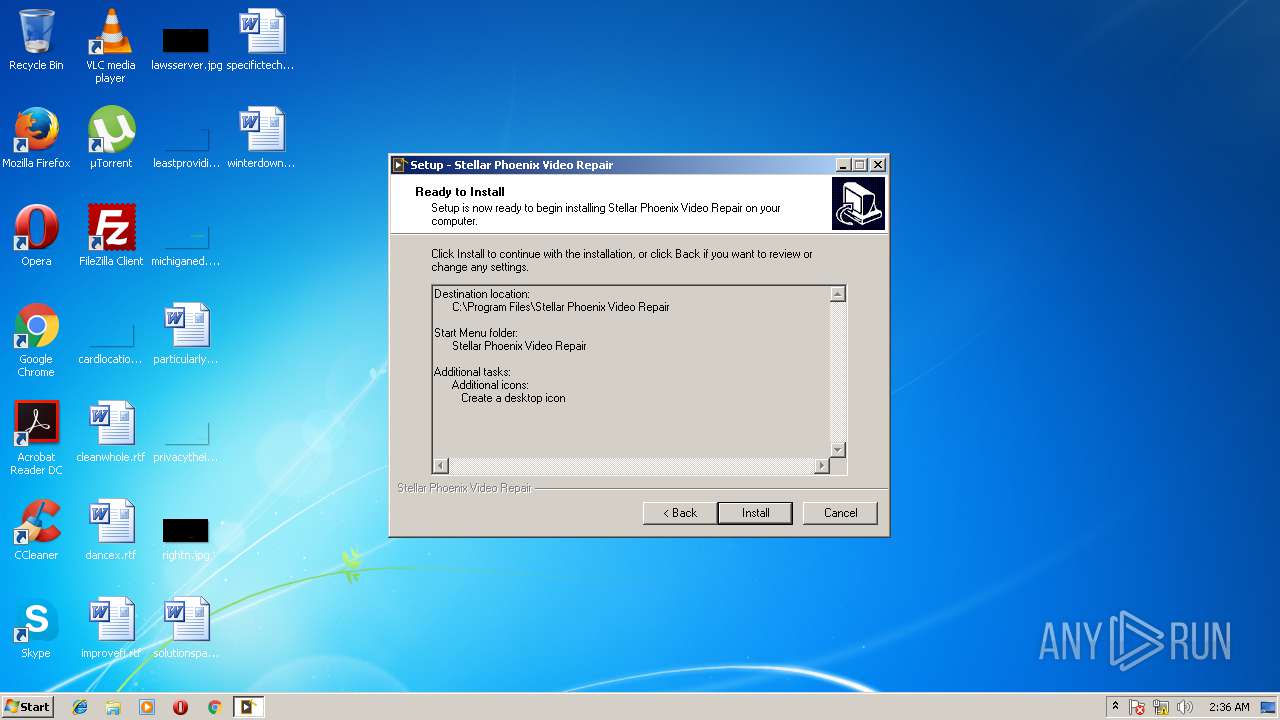
| (PID) Process: | (3468) StellarPhoenixVideoRepair.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Stellar Data Recovery\Stellar Phoenix Video Repair |
| Operation: | write | Name: | Path |
Value: C:\Program Files\Stellar Phoenix Video Repair | |||
| (PID) Process: | (3468) StellarPhoenixVideoRepair.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Stellar Data Recovery\Stellar Phoenix Video Repair |
| Operation: | write | Name: | Version |
Value: 3.0.0.0 | |||
| (PID) Process: | (3468) StellarPhoenixVideoRepair.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Stellar Data Recovery\Stellar Phoenix Video Repair |
| Operation: | write | Name: | ExeName |
Value: spvr | |||
| (PID) Process: | (3468) StellarPhoenixVideoRepair.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Program Files\Stellar Phoenix Video Repair\spvr.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (3468) StellarPhoenixVideoRepair.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Stellar Data Recovery\Stellar Phoenix Video Repair |
| Operation: | write | Name: | Sales |
Value: mailto:orders@stellarinfo.com?subject=Stellar Phoenix Video Repair - purchase request | |||
| (PID) Process: | (3468) StellarPhoenixVideoRepair.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Stellar Data Recovery\Stellar Phoenix Video Repair |
| Operation: | write | Name: | Dollar |
Value: https://www.stellarinfo.com/disk-recovery/video-repair/buy-now.php | |||
| (PID) Process: | (3468) StellarPhoenixVideoRepair.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Stellar Data Recovery\Stellar Phoenix Video Repair |
| Operation: | write | Name: | SalesText |
Value: Contact Sales | |||
| (PID) Process: | (3468) StellarPhoenixVideoRepair.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Stellar Data Recovery\Stellar Phoenix Video Repair |
| Operation: | write | Name: | DollarText |
Value: Buy Now | |||
| (PID) Process: | (3468) StellarPhoenixVideoRepair.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Stellar Data Recovery\Stellar Phoenix Video Repair |
| Operation: | write | Name: | EmailSupText |
Value: Contact Support | |||
| (PID) Process: | (3468) StellarPhoenixVideoRepair.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Stellar Data Recovery\Stellar Phoenix Video Repair |
| Operation: | write | Name: | EmailSup |
Value: support@stellarinfo.com | |||
Executable files
28
Suspicious files
7
Text files
6
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | StellarPhoenixVideoRepair.tmp | C:\Program Files\Stellar Phoenix Video Repair\is-F1IPB.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | StellarPhoenixVideoRepair.tmp | C:\Program Files\Stellar Phoenix Video Repair\is-9JBLT.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | StellarPhoenixVideoRepair.tmp | C:\Program Files\Stellar Phoenix Video Repair\is-1PB9U.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | StellarPhoenixVideoRepair.tmp | C:\Program Files\Stellar Phoenix Video Repair\is-O618E.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | StellarPhoenixVideoRepair.tmp | C:\Program Files\Stellar Phoenix Video Repair\is-HHE46.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | StellarPhoenixVideoRepair.tmp | C:\Program Files\Stellar Phoenix Video Repair\is-LHHV2.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | StellarPhoenixVideoRepair.tmp | C:\Program Files\Stellar Phoenix Video Repair\is-RDUMN.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | StellarPhoenixVideoRepair.tmp | C:\Program Files\Stellar Phoenix Video Repair\is-H063B.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | StellarPhoenixVideoRepair.tmp | C:\Program Files\Stellar Phoenix Video Repair\is-NEPHJ.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | StellarPhoenixVideoRepair.tmp | C:\Program Files\Stellar Phoenix Video Repair\is-EGB53.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
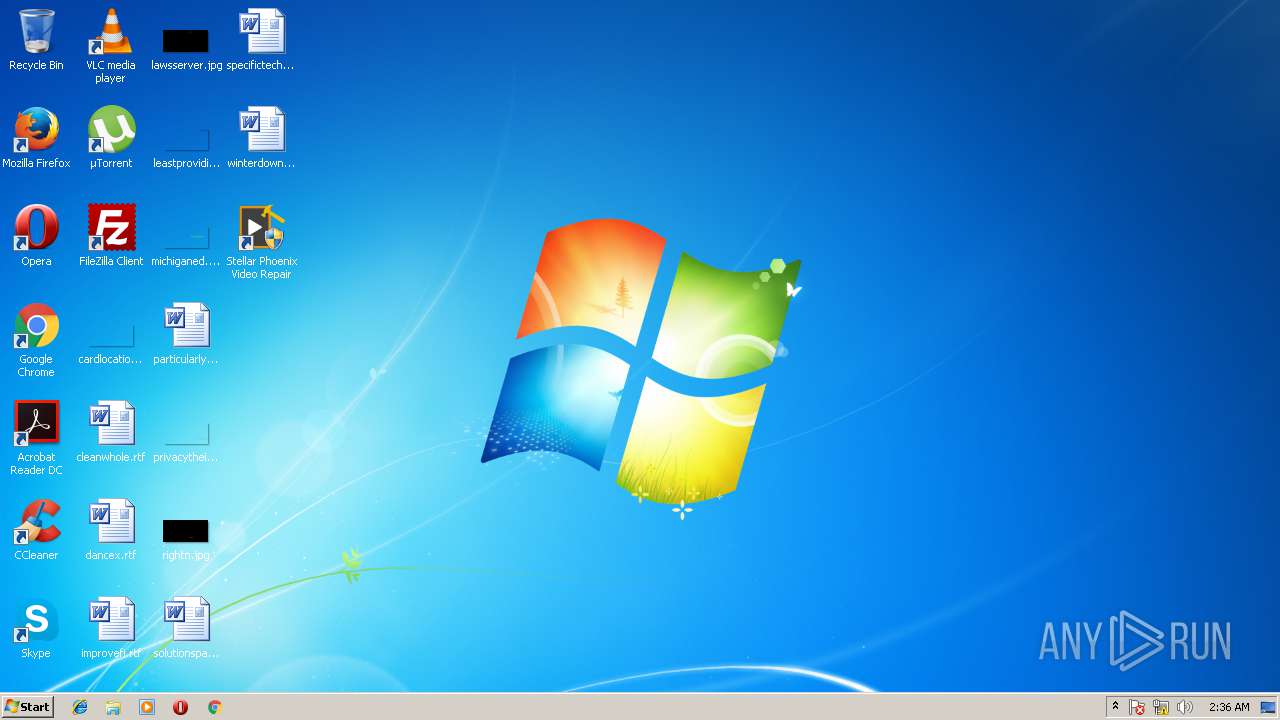
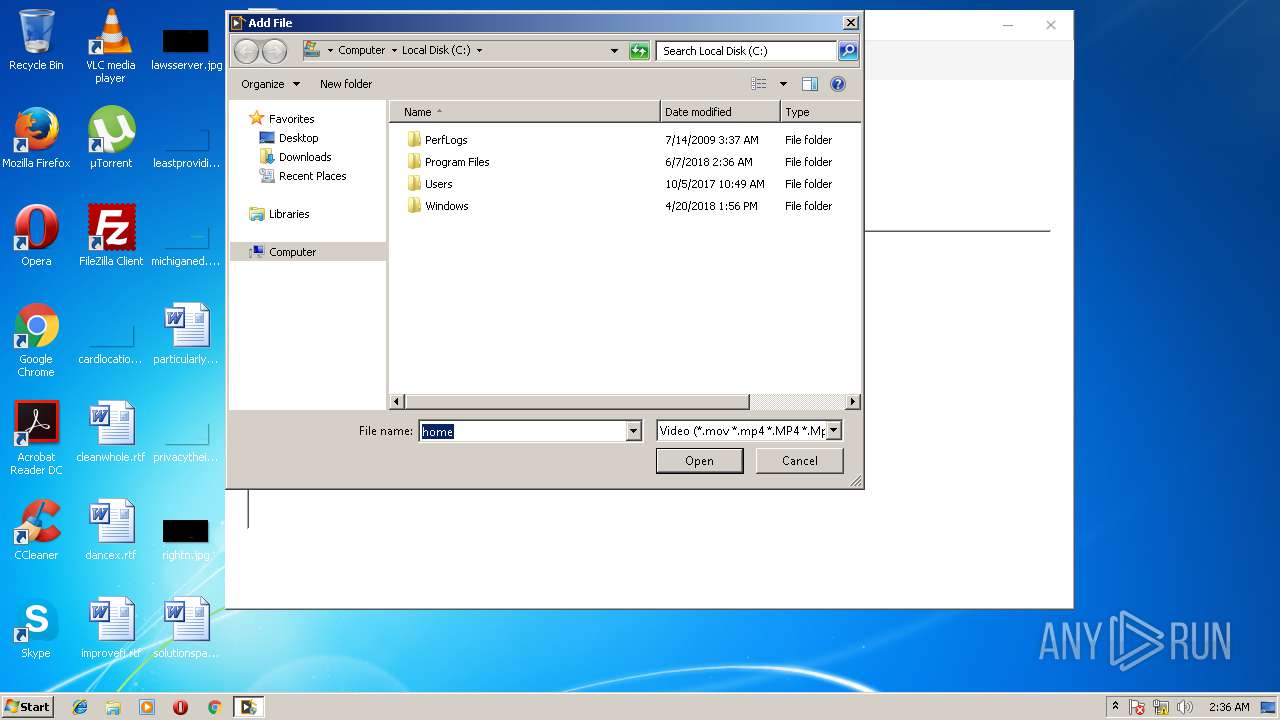
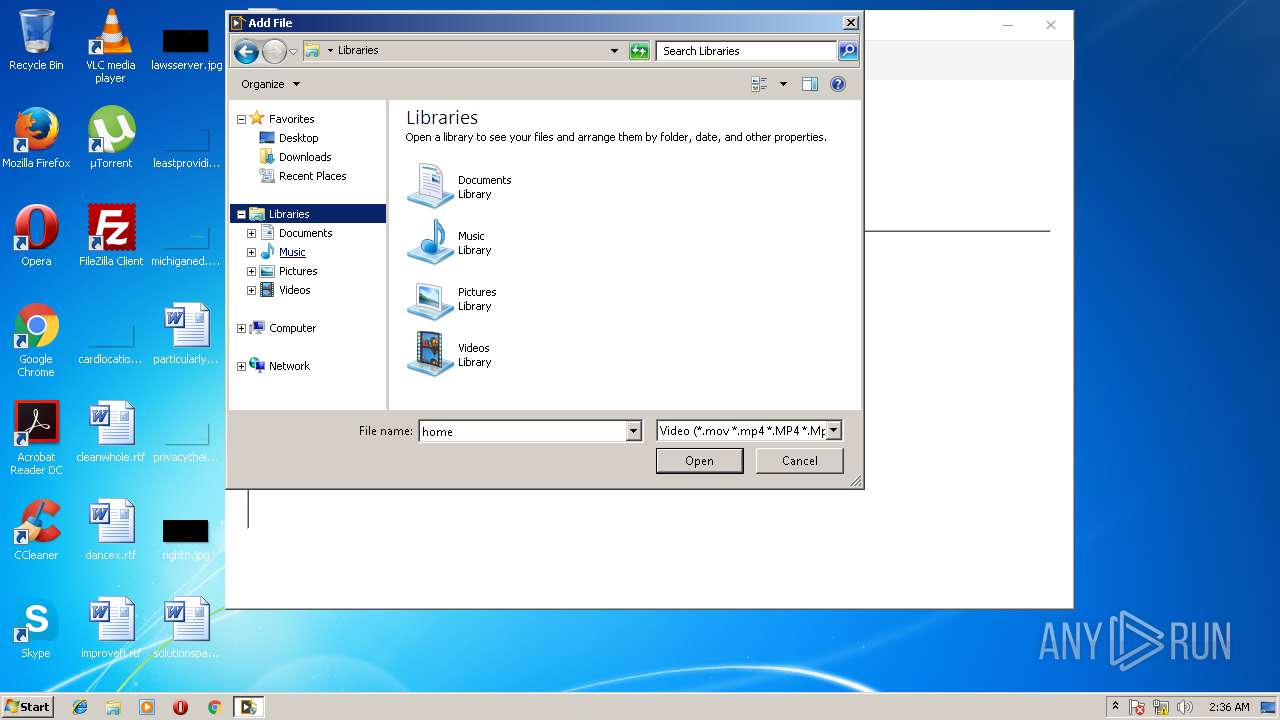
spvr.exe | Application started successfully.
|
spvr.exe | libpng warning: iCCP: known incorrect sRGB profile
|
spvr.exe | libpng warning: iCCP: known incorrect sRGB profile
|
spvr.exe | libpng warning: iCCP: known incorrect sRGB profile
|
spvr.exe | libpng warning: iCCP: known incorrect sRGB profile
|
spvr.exe | libpng warning: iCCP: known incorrect sRGB profile
|
spvr.exe | libpng warning: iCCP: known incorrect sRGB profile
|
spvr.exe | libpng warning: iCCP: known incorrect sRGB profile
|
spvr.exe | libpng warning: iCCP: known incorrect sRGB profile
|
spvr.exe | libpng warning: iCCP: known incorrect sRGB profile
|