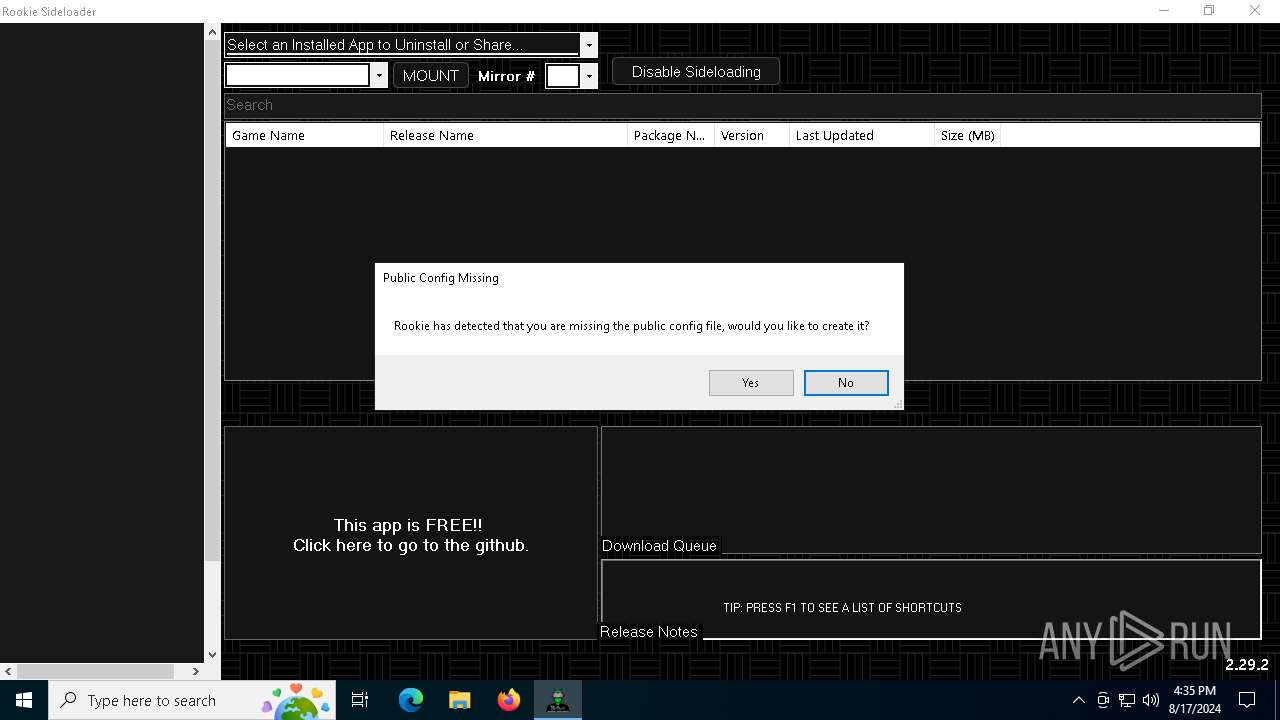
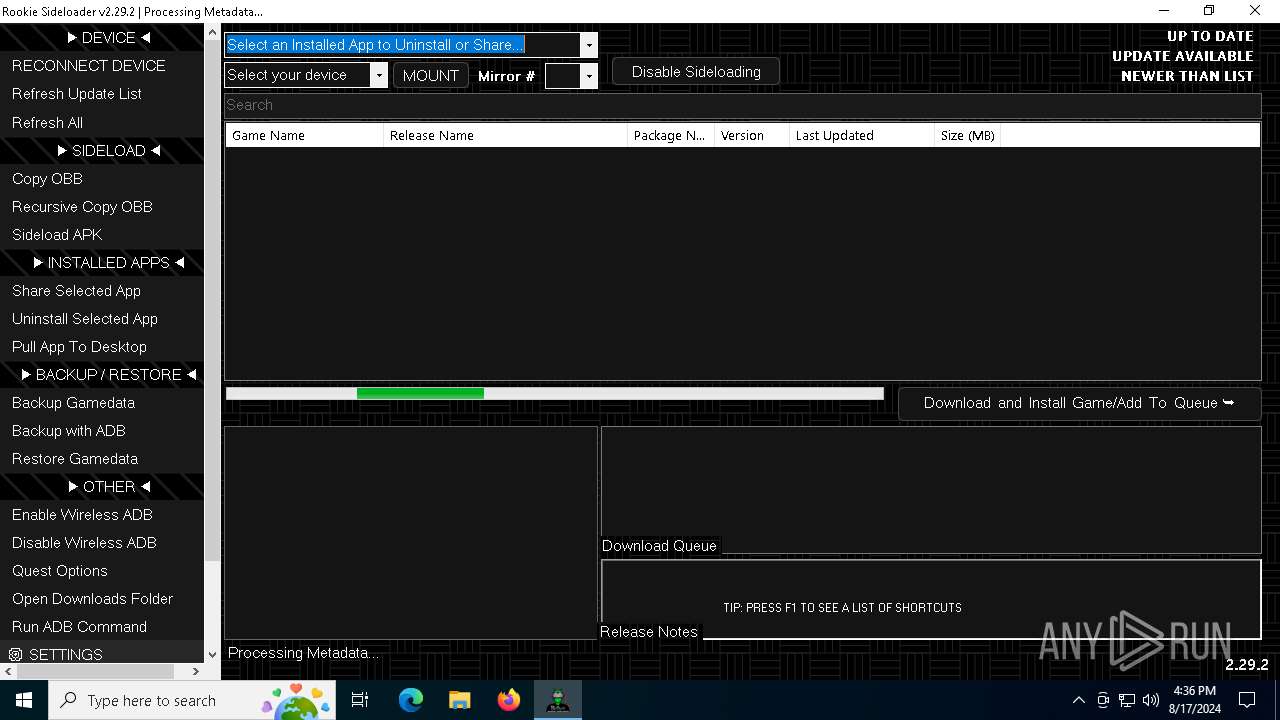
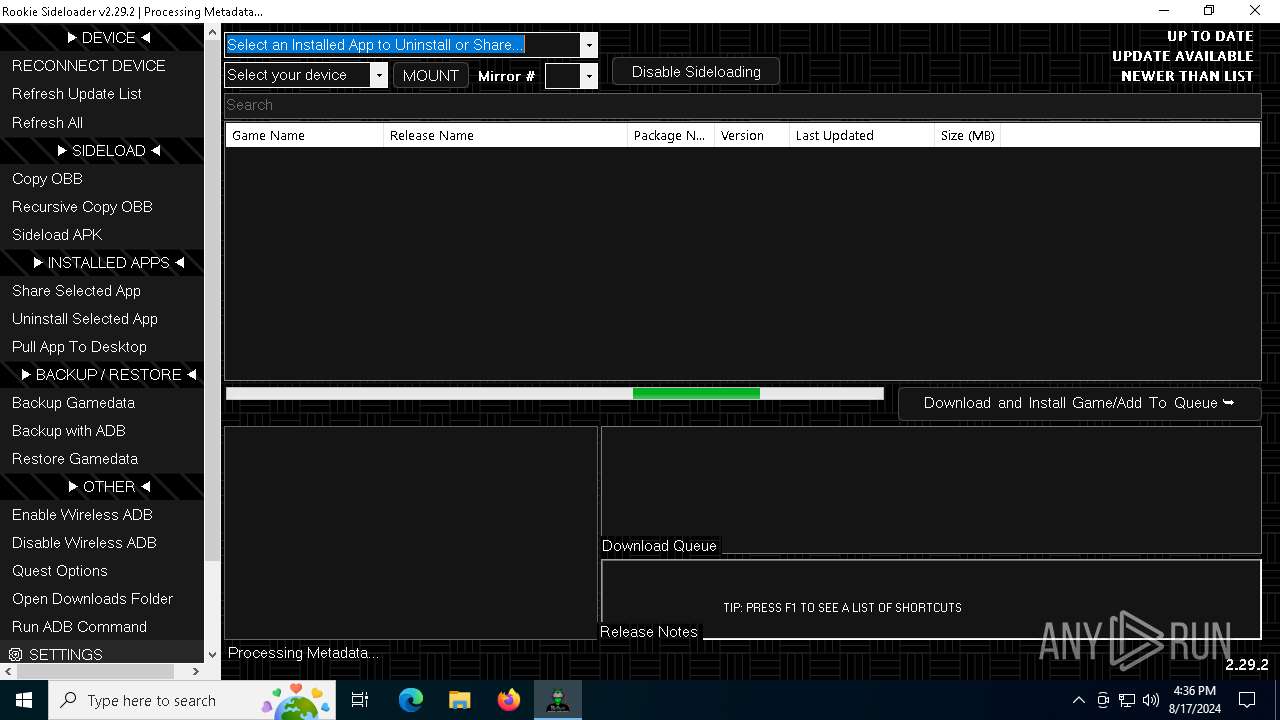
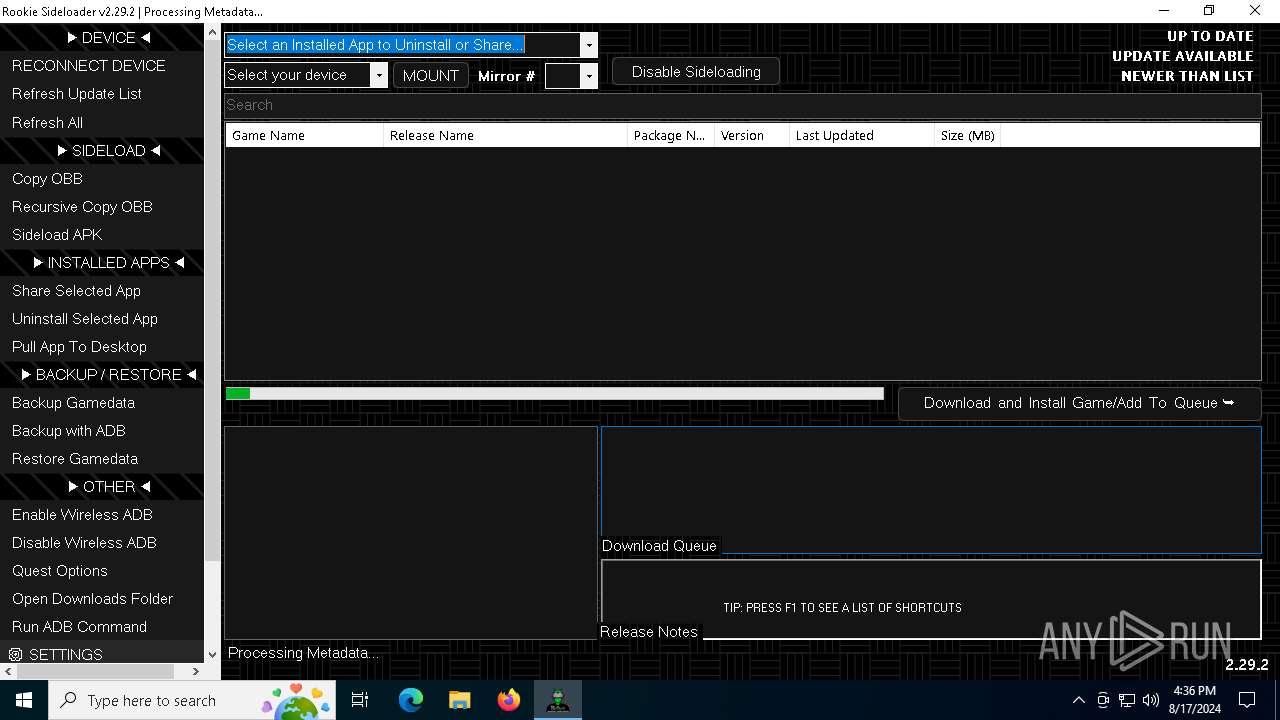
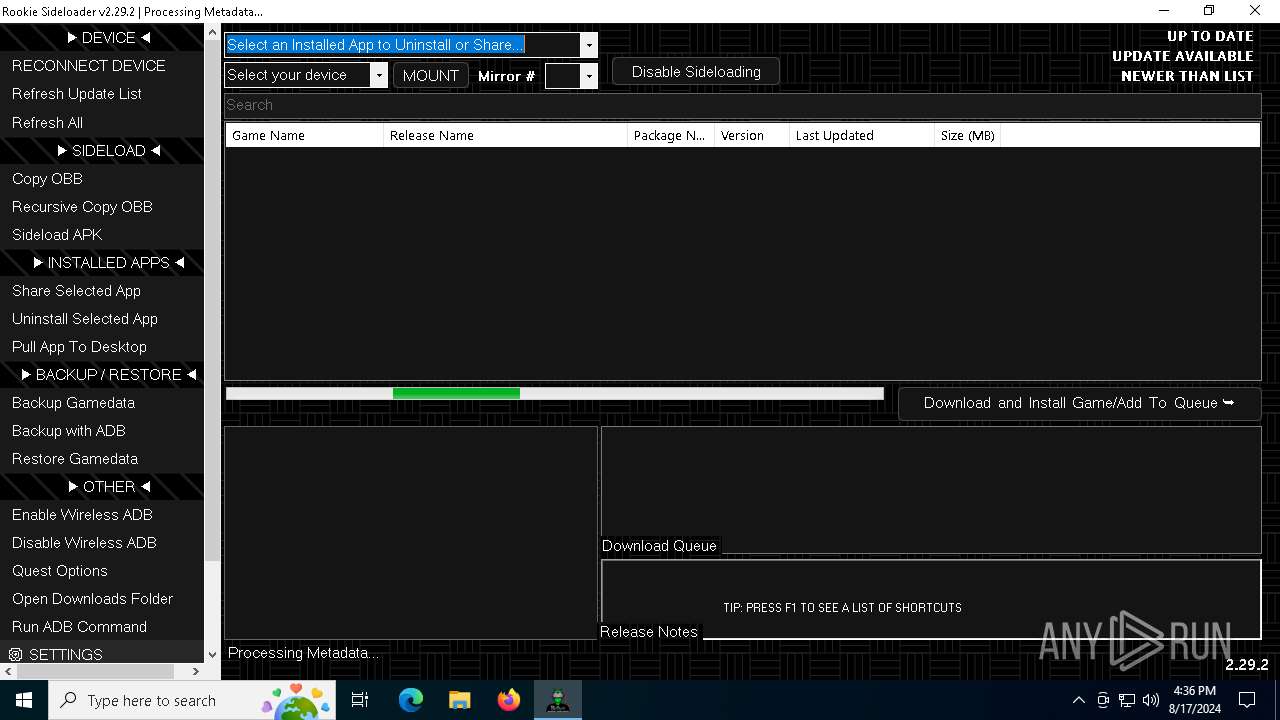
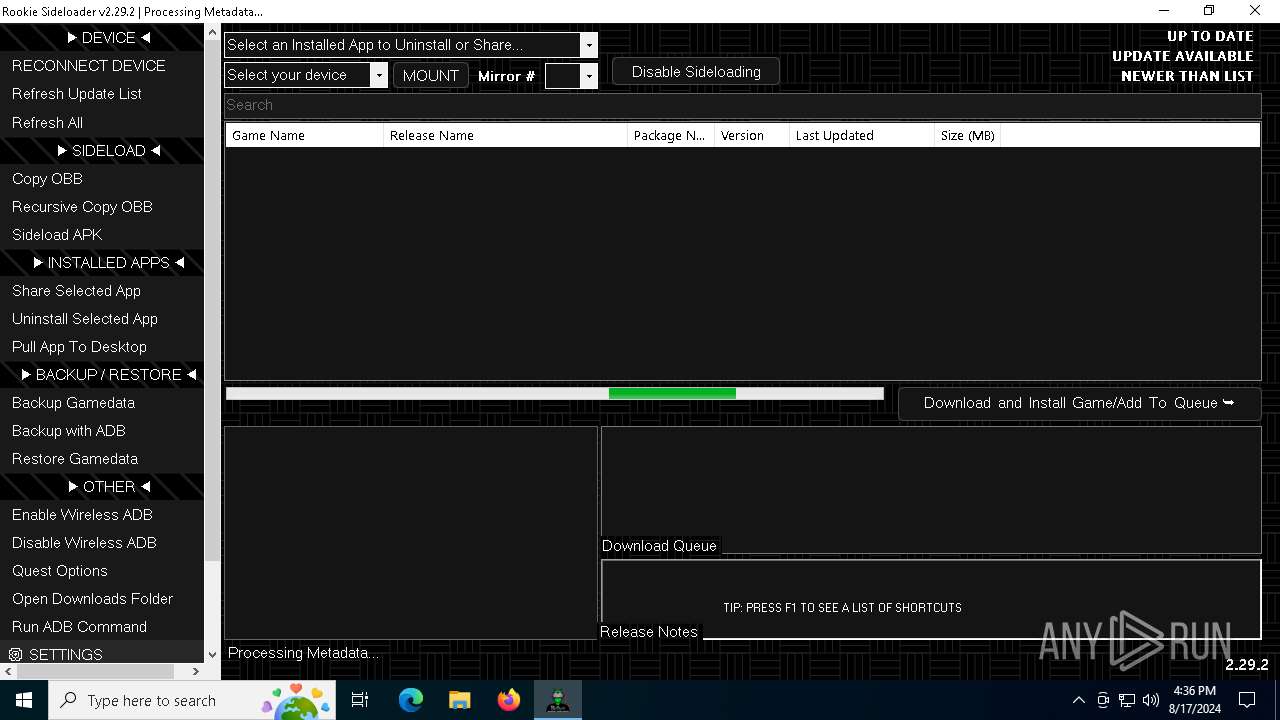
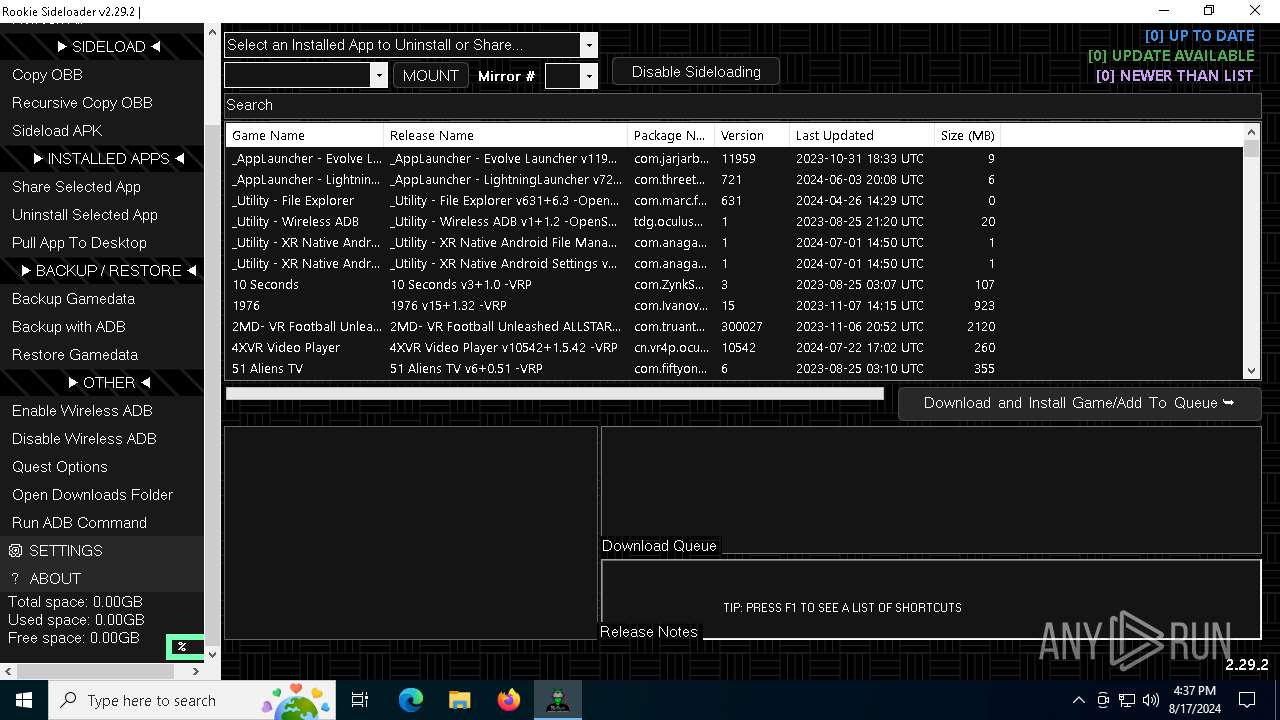
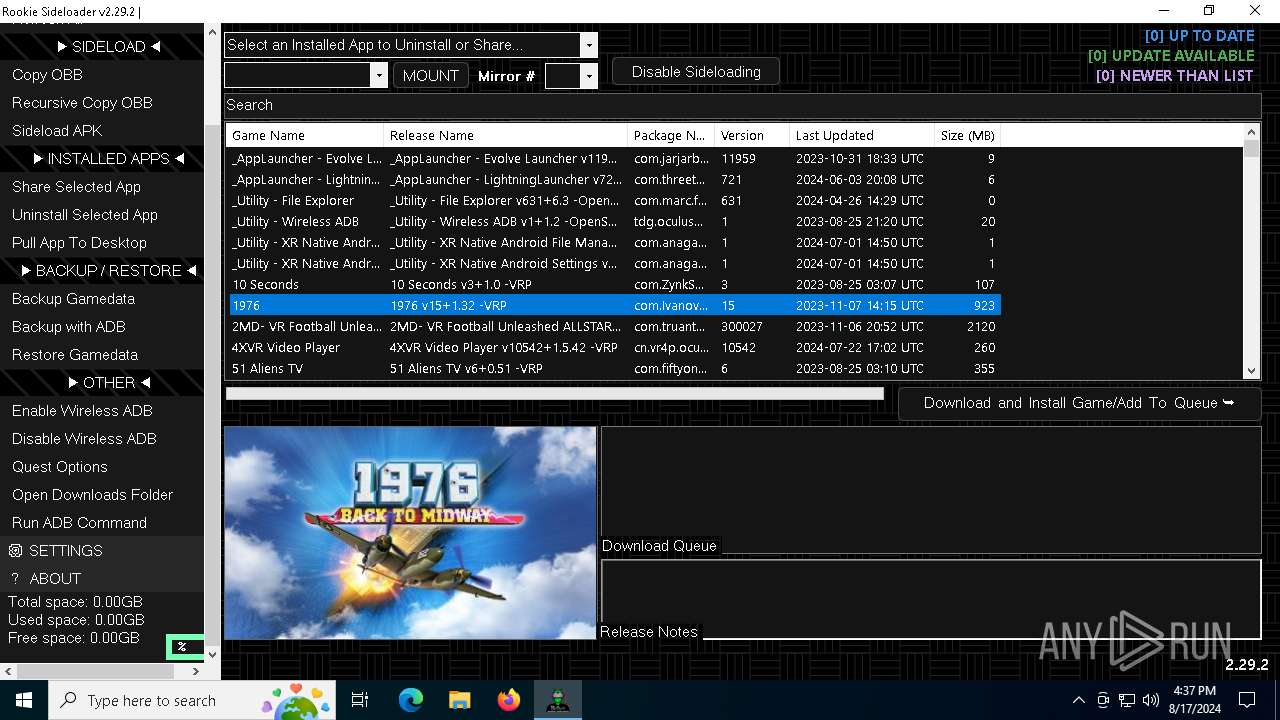
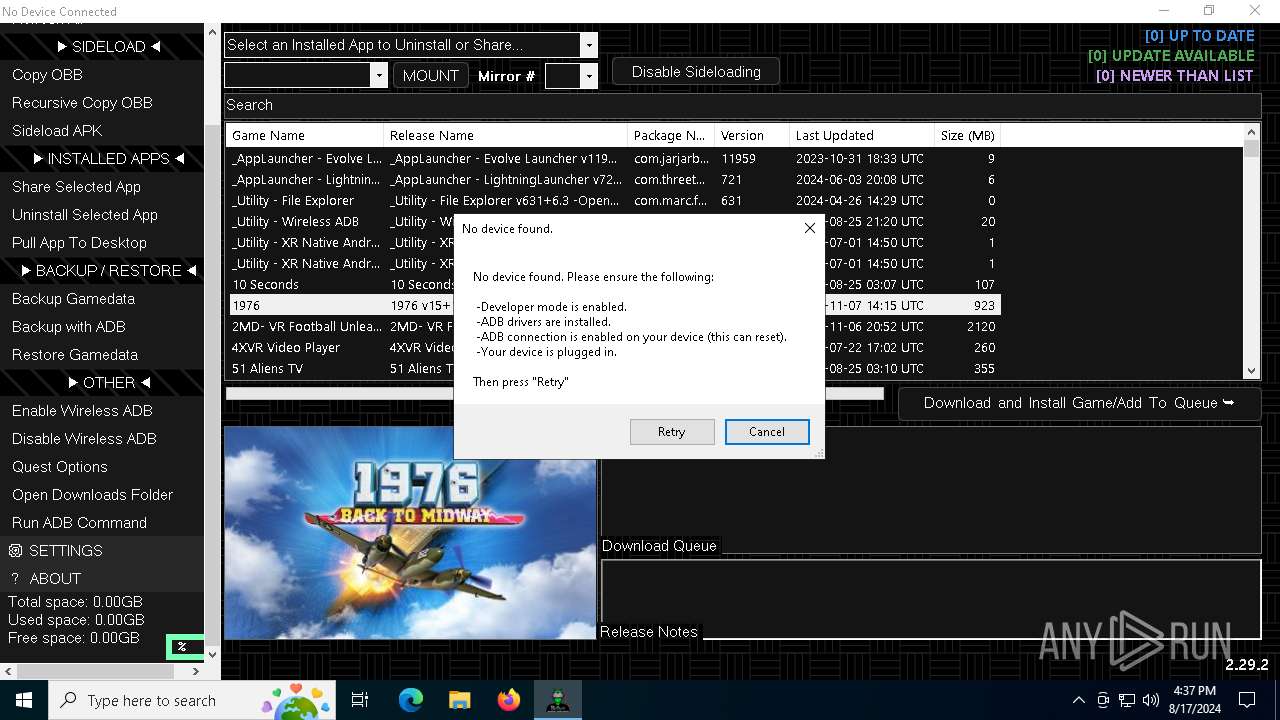
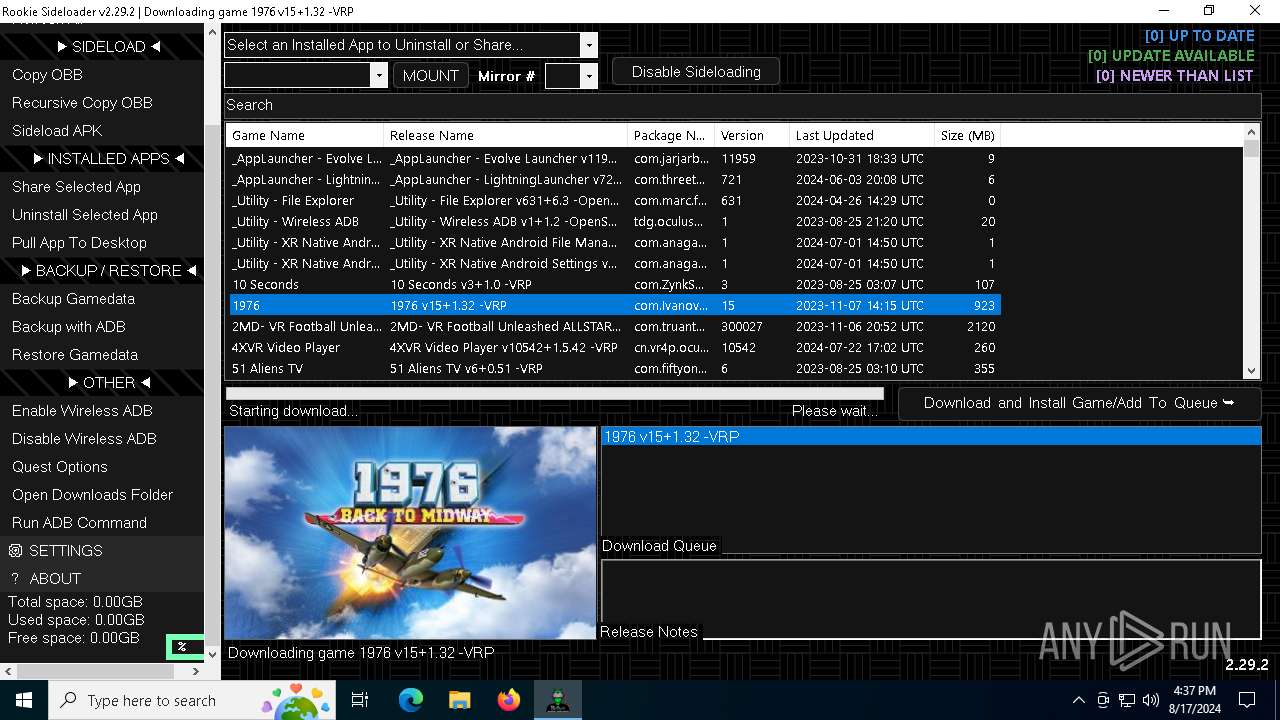
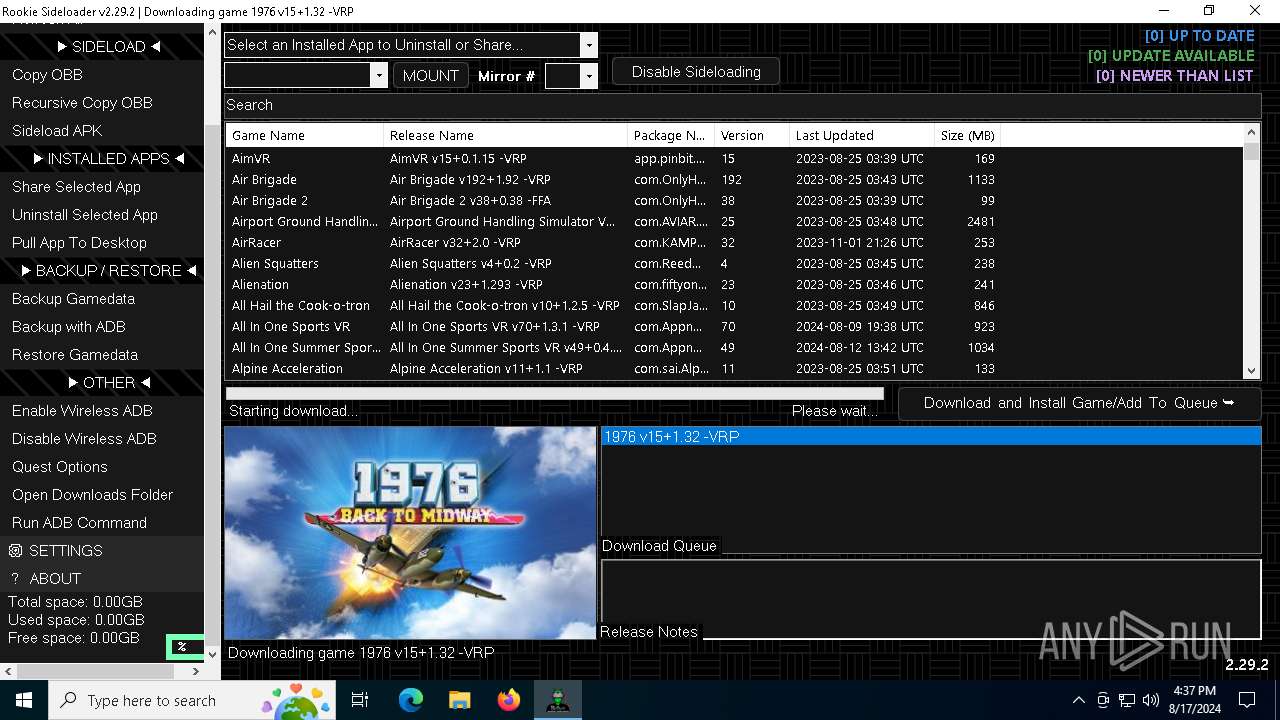
| File name: | AndroidSideloader v2.29.2.exe |
| Full analysis: | https://app.any.run/tasks/4c28007a-c7fb-4bac-a580-583baefb1db9 |
| Verdict: | Malicious activity |
| Analysis date: | August 17, 2024, 16:34:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | B7FA8A83DD1C92D93679C58D06691369 |
| SHA1: | 0CFF7BB71FF43EE92172F30566D8EE1B043129FC |
| SHA256: | 6CF2BCDB1A463FC69EDDB125EBA8CC12854EE23EFFCD7C65B968667C668A7F0B |
| SSDEEP: | 49152:yJ0dT5efJ0dT5hJ0dT5hJ0dT5x0MJ0dT56J0dT5hJ0dT5M9nWQv8+OqVM5hwCnJe:hcEQQMDXQ+9nWuWqVM5XflB2bz14ZPU |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops the executable file immediately after the start
- AndroidSideloader v2.29.2.exe (PID: 6444)
- 7z.exe (PID: 7072)
Reads security settings of Internet Explorer
- AndroidSideloader v2.29.2.exe (PID: 6444)
Executable content was dropped or overwritten
- AndroidSideloader v2.29.2.exe (PID: 6444)
- 7z.exe (PID: 7072)
Drops 7-zip archiver for unpacking
- AndroidSideloader v2.29.2.exe (PID: 6444)
Application launched itself
- adb.exe (PID: 3140)
There is functionality for VM detection (antiVM strings)
- rclone.exe (PID: 6232)
- rclone.exe (PID: 4364)
INFO
Creates files or folders in the user directory
- AndroidSideloader v2.29.2.exe (PID: 6444)
Checks supported languages
- AndroidSideloader v2.29.2.exe (PID: 6444)
- 7z.exe (PID: 7072)
- 7z.exe (PID: 1680)
- adb.exe (PID: 208)
- adb.exe (PID: 3140)
- adb.exe (PID: 4316)
- rclone.exe (PID: 6220)
- rclone.exe (PID: 6232)
- 7z.exe (PID: 6436)
- adb.exe (PID: 2088)
- adb.exe (PID: 6152)
- adb.exe (PID: 3268)
- adb.exe (PID: 7072)
- adb.exe (PID: 7100)
- adb.exe (PID: 6644)
- adb.exe (PID: 4560)
- adb.exe (PID: 6080)
- adb.exe (PID: 6244)
- adb.exe (PID: 6352)
- rclone.exe (PID: 4364)
- adb.exe (PID: 6456)
- adb.exe (PID: 2424)
- adb.exe (PID: 6672)
- adb.exe (PID: 3548)
- adb.exe (PID: 6324)
- adb.exe (PID: 3648)
- adb.exe (PID: 6920)
- adb.exe (PID: 4020)
- adb.exe (PID: 4276)
- adb.exe (PID: 6124)
- adb.exe (PID: 6972)
- rclone.exe (PID: 5388)
- adb.exe (PID: 208)
- adb.exe (PID: 5940)
- adb.exe (PID: 7140)
- adb.exe (PID: 7136)
- adb.exe (PID: 1140)
- adb.exe (PID: 7060)
- adb.exe (PID: 2468)
- 7z.exe (PID: 5924)
- adb.exe (PID: 6188)
- adb.exe (PID: 644)
- adb.exe (PID: 6244)
Reads the computer name
- AndroidSideloader v2.29.2.exe (PID: 6444)
- 7z.exe (PID: 7072)
- 7z.exe (PID: 1680)
- adb.exe (PID: 4316)
- rclone.exe (PID: 6220)
- rclone.exe (PID: 6232)
- 7z.exe (PID: 6436)
- rclone.exe (PID: 4364)
- rclone.exe (PID: 5388)
- 7z.exe (PID: 5924)
Create files in a temporary directory
- AndroidSideloader v2.29.2.exe (PID: 6444)
- 7z.exe (PID: 1680)
- adb.exe (PID: 4316)
- rclone.exe (PID: 6232)
- 7z.exe (PID: 6436)
- rclone.exe (PID: 4364)
- rclone.exe (PID: 5388)
- 7z.exe (PID: 5924)
Reads Environment values
- AndroidSideloader v2.29.2.exe (PID: 6444)
Reads the machine GUID from the registry
- AndroidSideloader v2.29.2.exe (PID: 6444)
- rclone.exe (PID: 6232)
- rclone.exe (PID: 4364)
- rclone.exe (PID: 5388)
Disables trace logs
- AndroidSideloader v2.29.2.exe (PID: 6444)
Checks proxy server information
- AndroidSideloader v2.29.2.exe (PID: 6444)
Reads the software policy settings
- AndroidSideloader v2.29.2.exe (PID: 6444)
- rclone.exe (PID: 6232)
- rclone.exe (PID: 4364)
- rclone.exe (PID: 5388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2078:05:26 10:58:37+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 3898880 |
| InitializedDataSize: | 413184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3b9d5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Rookie Sideloader |
| CompanyName: | Rookie.AndroidSideloader |
| FileDescription: | AndroidSideloader |
| FileVersion: | 2.0.0.0 |
| InternalName: | AndroidSideloader.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | AndroidSideloader.exe |
| ProductName: | AndroidSideloader |
| ProductVersion: | 2.0.0.0 |
| AssemblyVersion: | 2.0.0.0 |
Total processes
212
Monitored processes
84
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\RSL\platform-tools\adb.exe" kill-server | C:\RSL\platform-tools\adb.exe | — | AndroidSideloader v2.29.2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 208 | "C:\RSL\platform-tools\adb.exe" shell df | C:\RSL\platform-tools\adb.exe | — | AndroidSideloader v2.29.2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 644 | "C:\RSL\platform-tools\adb.exe" shell df | C:\RSL\platform-tools\adb.exe | — | AndroidSideloader v2.29.2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1140 | "C:\RSL\platform-tools\adb.exe" shell dumpsys battery | C:\RSL\platform-tools\adb.exe | — | AndroidSideloader v2.29.2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1448 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | adb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1492 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | adb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1636 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | adb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1680 | "7z.exe" x "C:\Users\admin\AppData\Local\Temp\rclone.zip" -y -o"C:\Users\admin\AppData\Local\Temp" -bsp1 | C:\Users\admin\AppData\Local\Temp\7z.exe | — | AndroidSideloader v2.29.2.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 23.01 Modules
| |||||||||||||||
| 2088 | "C:\RSL\platform-tools\adb.exe" devices | C:\RSL\platform-tools\adb.exe | — | AndroidSideloader v2.29.2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2424 | "C:\RSL\platform-tools\adb.exe" shell dumpsys battery | C:\RSL\platform-tools\adb.exe | — | AndroidSideloader v2.29.2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
33 535
Read events
33 266
Write events
269
Delete events
0
Modification events
| (PID) Process: | (6444) AndroidSideloader v2.29.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6444) AndroidSideloader v2.29.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6444) AndroidSideloader v2.29.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6444) AndroidSideloader v2.29.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6444) AndroidSideloader v2.29.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6444) AndroidSideloader v2.29.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6444) AndroidSideloader v2.29.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6444) AndroidSideloader v2.29.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6444) AndroidSideloader v2.29.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6444) AndroidSideloader v2.29.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
16
Suspicious files
3
Text files
1 688
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6444 | AndroidSideloader v2.29.2.exe | C:\Users\admin\AppData\Local\Temp\dependencies.7z | — | |
MD5:— | SHA256:— | |||
| 6444 | AndroidSideloader v2.29.2.exe | C:\Users\admin\AppData\Local\Rookie.AndroidSideloader\AndroidSideloader_v2.29.2_Url_yoqfpljawlmuvev2xykf0ju0t0p31uqo\2.0.0.0\a2lbrbkw.newcfg | xml | |
MD5:6DC22626C68E39D1F7A92BC247D064FA | SHA256:5B1CFB327E8E4F605CDB650526AB442CC846CE97CFDC51D1DA23DFECB3ABDF60 | |||
| 6444 | AndroidSideloader v2.29.2.exe | C:\Users\admin\AppData\Local\Rookie.AndroidSideloader\AndroidSideloader_v2.29.2_Url_yoqfpljawlmuvev2xykf0ju0t0p31uqo\2.0.0.0\user.config | xml | |
MD5:6DC22626C68E39D1F7A92BC247D064FA | SHA256:5B1CFB327E8E4F605CDB650526AB442CC846CE97CFDC51D1DA23DFECB3ABDF60 | |||
| 6444 | AndroidSideloader v2.29.2.exe | C:\Users\admin\AppData\Local\Rookie.AndroidSideloader\AndroidSideloader_v2.29.2_Url_yoqfpljawlmuvev2xykf0ju0t0p31uqo\2.0.0.0\ij0ouqow.newcfg | xml | |
MD5:FD7EDBD5217360247B35D3EA8919A84F | SHA256:F1BAE05CD263E2B84C1DA6BBF023BEE2E45763087A548F1A6B0CE2F590280634 | |||
| 6444 | AndroidSideloader v2.29.2.exe | C:\Users\admin\AppData\Local\Rookie.AndroidSideloader\AndroidSideloader_v2.29.2_Url_yoqfpljawlmuvev2xykf0ju0t0p31uqo\2.0.0.0\s3fuzwud.newcfg | xml | |
MD5:924C15BEB31603B39E9C754A48E93734 | SHA256:1A46012F74705AA359E3D6747CB3F017D292C4232152210CF56B97EE651C7ECC | |||
| 6444 | AndroidSideloader v2.29.2.exe | C:\Users\admin\AppData\Local\Temp\Sideloader Launcher.exe | executable | |
MD5:A53A5E70248EB3DA58DEFA74B0554704 | SHA256:98BC8CF1C6A59EF70D6431E1E92887984E5B21C8FBC85B4AD23CCC70589C4B1F | |||
| 6444 | AndroidSideloader v2.29.2.exe | C:\Users\admin\AppData\Local\Temp\Rookie Offline.cmd | text | |
MD5:513248E44025E42FD2B8F9280501A8BB | SHA256:7DD245A6267A6D9500EE6B13A29FBDD80CEF9A020162C0E24A228558C58FA092 | |||
| 6444 | AndroidSideloader v2.29.2.exe | C:\Users\admin\AppData\Local\Temp\7z.exe | executable | |
MD5:1A7EAA1DAB7867E15D7800AE0B5AF5E3 | SHA256:356BEA8B6E9EB84DFA0DD8674E7C03428C641A47789DF605C5BEA0730DE4AED2 | |||
| 6444 | AndroidSideloader v2.29.2.exe | C:\Users\admin\AppData\Local\Temp\7z.dll | executable | |
MD5:71EBAC040D32560BB9D76A552A7CB986 | SHA256:1AA51AA9BB50B26BB652D9C442208DB76546286B0DB169C8882DE97D1117029D | |||
| 7072 | 7z.exe | C:\RSL\platform-tools\mke2fs.conf | text | |
MD5:699098CA95F87BA48BB94A3E848549B3 | SHA256:AD58A58DCDD24D85055814CA9CAC67DB89D4E67C434E96774BDCE0D0A007D067 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
38
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5900 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2208 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6668 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2680 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2388 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6444 | AndroidSideloader v2.29.2.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
6444 | AndroidSideloader v2.29.2.exe | 185.199.111.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
2680 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2208 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2208 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
raw.githubusercontent.com |
| shared |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
downloads.rclone.org |
| unknown |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6444 | AndroidSideloader v2.29.2.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |