| File name: | Crypter.exe |
| Full analysis: | https://app.any.run/tasks/a6006b45-23c4-4d07-8fb1-620425844429 |
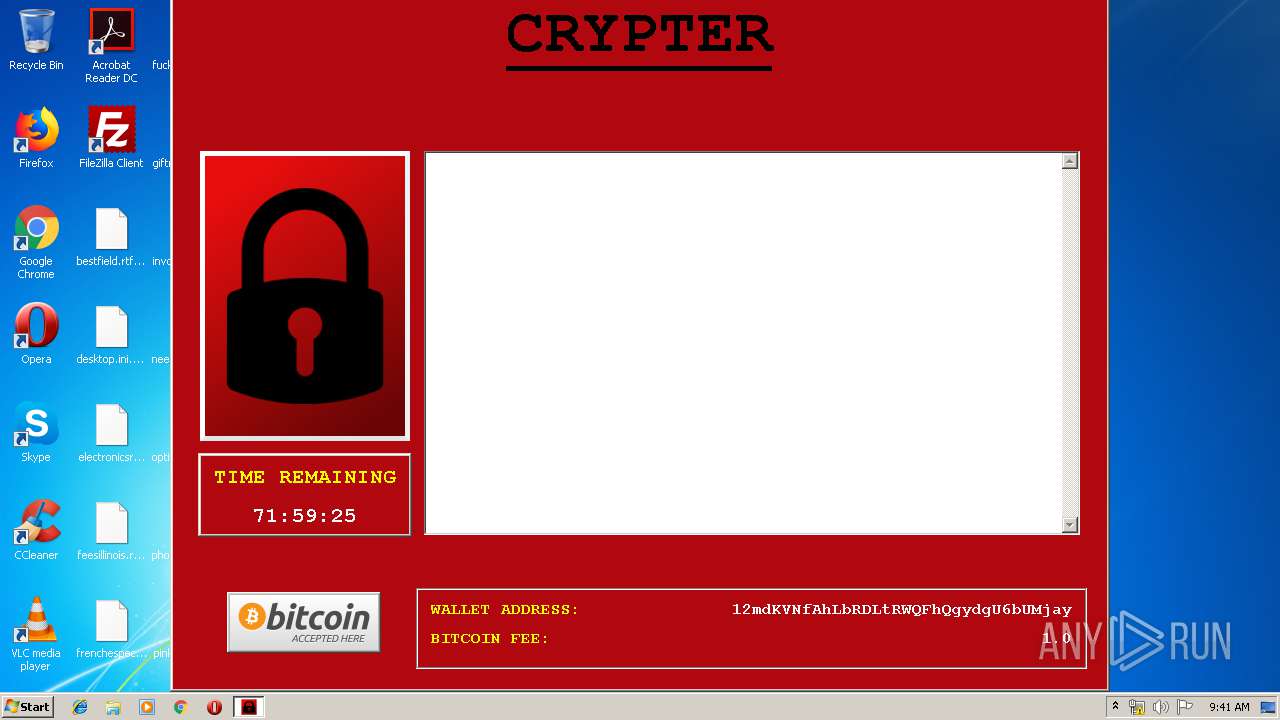
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 08:39:52 |
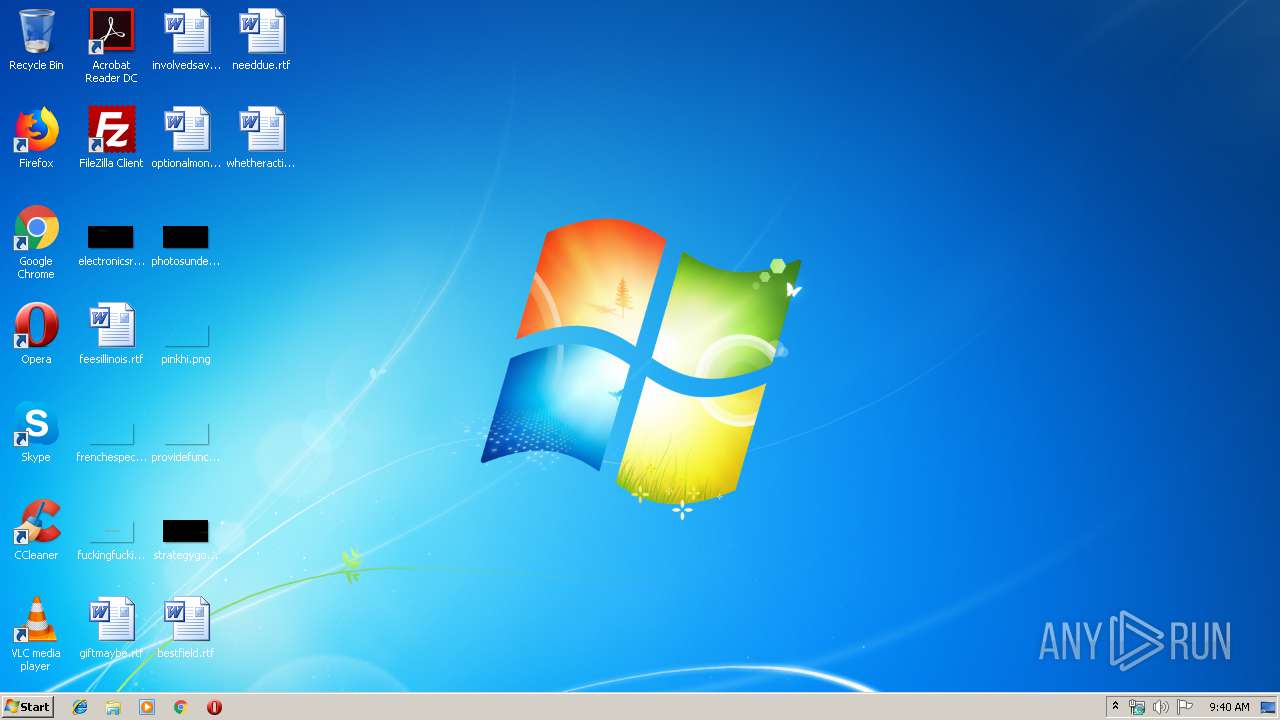
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 4C71A5BDB0CB6FD98FD06C59D304B8F5 |
| SHA1: | CCE6DAE9F79BDE5F8E54D86EB4C1AD4563E483FE |
| SHA256: | 6CCB58450F13CAF7D6A6AA28B65B5ABCFAF1317A0846CA0E4632D7E154146A7E |
| SSDEEP: | 196608:XtlX+aFFuPRYVkmmCIw+5j3dpXr7e6ficueojSsmzRITWs7i7:XtlrFFCYSpwYTDvIjNoRhs7S |
MALICIOUS
Loads dropped or rewritten executable
- Crypter.exe (PID: 2440)
Changes the autorun value in the registry
- Crypter.exe (PID: 2440)
Writes to a start menu file
- Crypter.exe (PID: 2440)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2548)
- cmd.exe (PID: 2168)
- cmd.exe (PID: 3360)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3024)
- schtasks.exe (PID: 2736)
- schtasks.exe (PID: 3852)
Actions looks like stealing of personal data
- Crypter.exe (PID: 2440)
Modifies files in Chrome extension folder
- Crypter.exe (PID: 2440)
SUSPICIOUS
Executable content was dropped or overwritten
- Crypter.exe (PID: 3964)
Loads Python modules
- Crypter.exe (PID: 2440)
Starts CMD.EXE for commands execution
- Crypter.exe (PID: 2440)
Creates files in the user directory
- Crypter.exe (PID: 2440)
INFO
Dropped object may contain Bitcoin addresses
- Crypter.exe (PID: 3964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.24 |
| CodeSize: | 39936 |
| InitializedDataSize: | 87040 |
| UninitializedDataSize: | 51200 |
| EntryPoint: | 0x14d0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| TLS Callbacks: | 2 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00009A60 | 0x00009C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.09665 |
.data | 0x0000B000 | 0x00000038 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.665052 |
.rdata | 0x0000C000 | 0x00005008 | 0x00005200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.9414 |
.bss | 0x00012000 | 0x0000C698 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001F000 | 0x00000BD4 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.16699 |
.CRT | 0x00020000 | 0x00000034 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.267208 |
.tls | 0x00021000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.190489 |
.rsrc | 0x00022000 | 0x0000EEC4 | 0x0000F000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.51703 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 6.15653 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.44895 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.77742 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95095 | 38188 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 6.0521 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 6.15081 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 6.39466 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
msvcrt.dll |
Total processes
43
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2168 | C:\Windows\system32\cmd.exe /c "schtasks /run /i /tn updater47" | C:\Windows\system32\cmd.exe | — | Crypter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\Temp\Crypter.exe" | C:\Users\admin\AppData\Local\Temp\Crypter.exe | Crypter.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2548 | C:\Windows\system32\cmd.exe /c "schtasks /create /tn updater47 /sc once /sd 01/01/1901 /tr "vssadmin Delete Shadows /All /Quiet" /st 00:00 /rl highest /ru SYSTEM /f" | C:\Windows\system32\cmd.exe | — | Crypter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2736 | schtasks /run /i /tn updater47 | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3024 | schtasks /create /tn updater47 /sc once /sd 01/01/1901 /tr "vssadmin Delete Shadows /All /Quiet" /st 00:00 /rl highest /ru SYSTEM /f | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3360 | C:\Windows\system32\cmd.exe /c "schtasks /delete /tn updater47 /f" | C:\Windows\system32\cmd.exe | — | Crypter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3852 | schtasks /delete /tn updater47 /f | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | "C:\Users\admin\AppData\Local\Temp\Crypter.exe" | C:\Users\admin\AppData\Local\Temp\Crypter.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
20
Read events
18
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2440) Crypter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Crypter |
Value: C:\Users\admin\AppData\Local\Temp\Crypter.exe | |||
| (PID) Process: | (2440) Crypter.exe | Key: | HKEY_CURRENT_USER\Software\Crypter |
| Operation: | write | Name: | |
Value: 1568191235 | |||
Executable files
35
Suspicious files
1 145
Text files
14
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI39642\Crypto.Cipher._AES.pyd | executable | |
MD5:DD3DB5480EB52E8F69D47F3B725E6BFB | SHA256:51054F4D28782B6698B1B6510317650E797E11F87FA29FCEAF8559B6BCBF4DFE | |||
| 3964 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI39642\Main.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 3964 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI39642\bz2.pyd | executable | |
MD5:58C57A662CDE57FEA311444CC8DADC24 | SHA256:69B4EC17DE1368A9EA62313954629E1ACE3F414A7EAEDCEDBFC79B110CADBAAC | |||
| 3964 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI39642\pyexpat.pyd | executable | |
MD5:C79A904C852347565950E437335BE107 | SHA256:5FB1D9F49A61BF1641EB097298B635E42A9AEF9755C9F22CA09B812B94614AEF | |||
| 3964 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI39642\_hashlib.pyd | executable | |
MD5:B1DBD52E5DA083E5B5613A2B4C17A4EF | SHA256:FA57BF3173F2D636984305401C06F1618B8119FEA2C311D1173566EA236FA0C6 | |||
| 3964 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI39642\_ssl.pyd | executable | |
MD5:9B59BE1FA8427368C4E0E763F578D74C | SHA256:4BA198E7F53A37B3A825FF2CE4D3E6CA00AD96E62852F0127A46C57A9A4A3026 | |||
| 3964 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI39642\Crypto.Hash._SHA256.pyd | executable | |
MD5:FD7BA0D28B7809D0DC15AEF9D7EAF62B | SHA256:36314665FA2A6EFFBE7A4280B2D420A438D02C40BD7B6A690A588490A2E8E4D0 | |||
| 3964 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI39642\python27.dll | executable | |
MD5:C8C4685509F1375666B03206457D4E9F | SHA256:42343C316E7AAC408E6066BA93BCBDDDB00940BDF901D9AED28111CA5D96279E | |||
| 3964 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI39642\pywintypes27.dll | executable | |
MD5:51D5CD3A71EA75D4AF9535E27DD09E61 | SHA256:893E9DFEBE8D69A80AB884B3028CB2C5A898E431012EC652DAE803DB01F222F1 | |||
| 3964 | Crypter.exe | C:\Users\admin\AppData\Local\Temp\_MEI39642\Crypto.Random.OSRNG.winrandom.pyd | executable | |
MD5:0A3EC8FFF372A800326EB8365DE81F38 | SHA256:17FBE1DD26AC0B49B7764D5F667FD12B9929B7FA9FA60395847CF80F653A0FDB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report