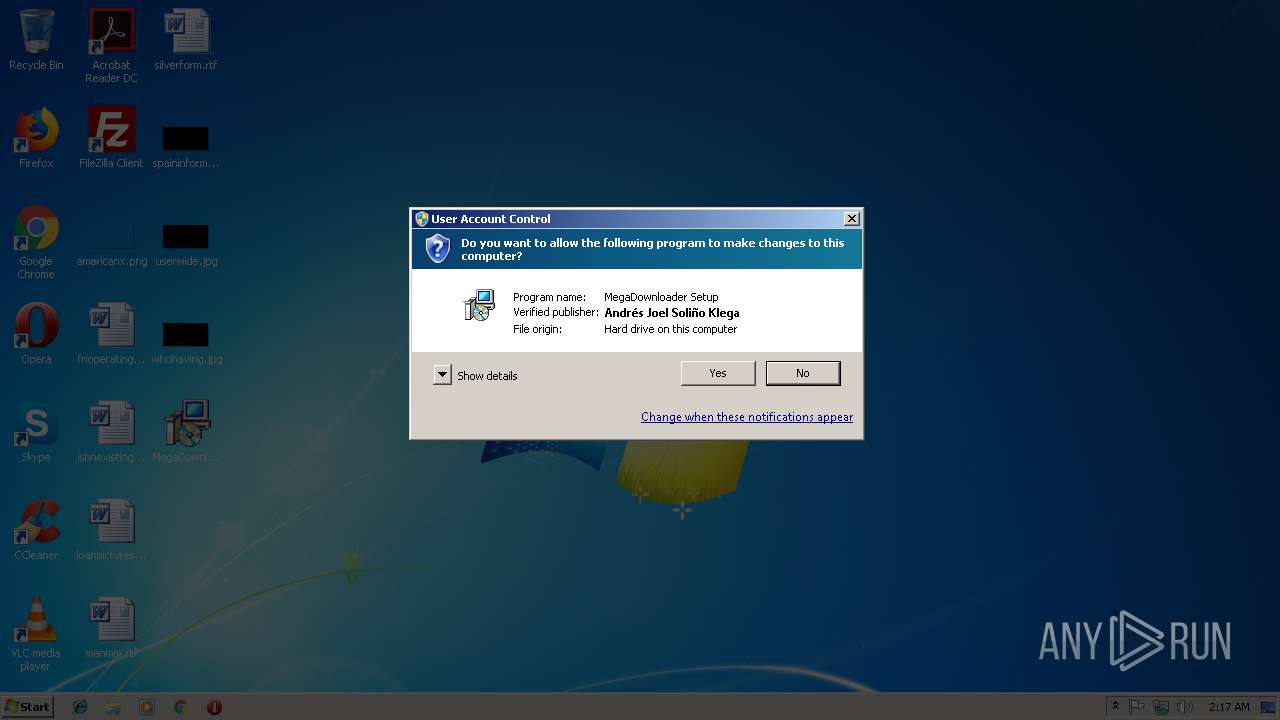
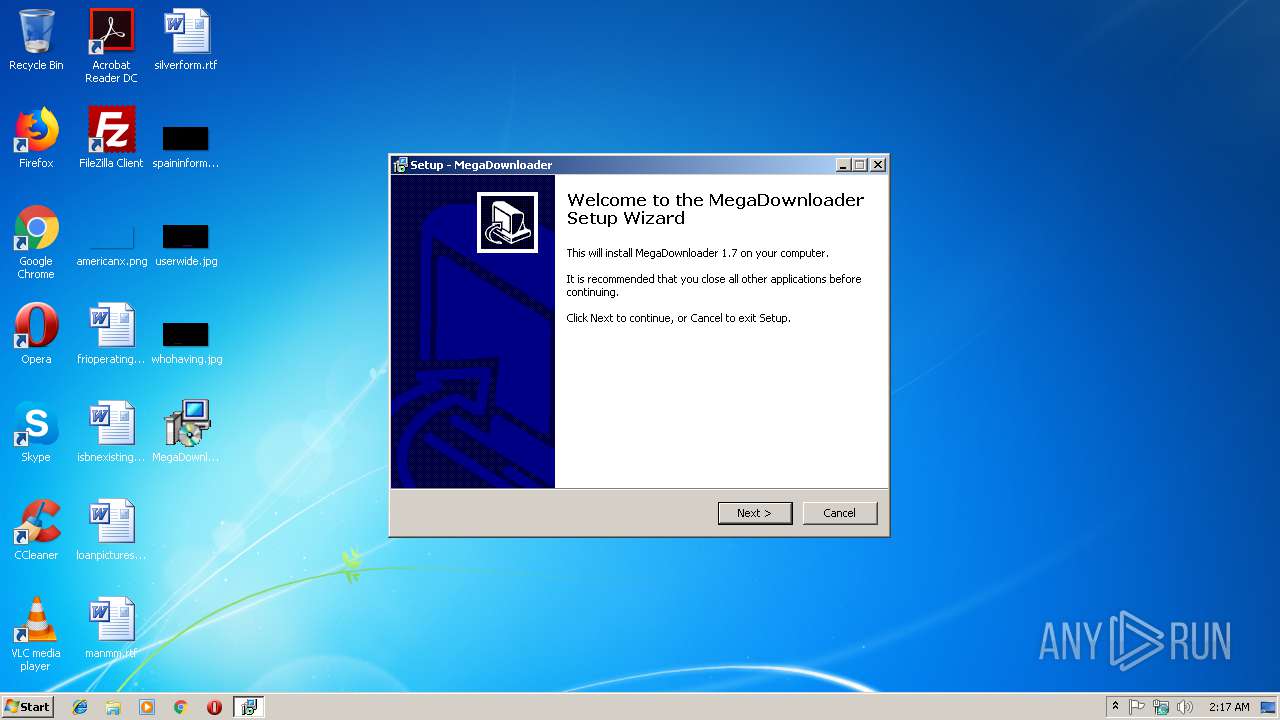
| File name: | MegaDownloader_v1.7.exe |
| Full analysis: | https://app.any.run/tasks/7b0f93c1-ef28-4a12-8f92-f564058eba02 |
| Verdict: | No threats detected |
| Analysis date: | November 24, 2018, 02:17:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E3C5EA31E0E5291CFEEA503CF3C4E56F |
| SHA1: | 84FED36A4D63BDE37EE41421EE7A8265DC56D855 |
| SHA256: | 6CC2F7037E6B314FA72DCD9549CF4114F4B0A4EC102DF734C167A28E53CEB633 |
| SSDEEP: | 49152:g9rBNMEze67tlThUghHWMYpgecNOUtU4Eax/O+6aabtJ/hl7Gpfa:qwmZU82zmec5tUXan6nr/HGa |
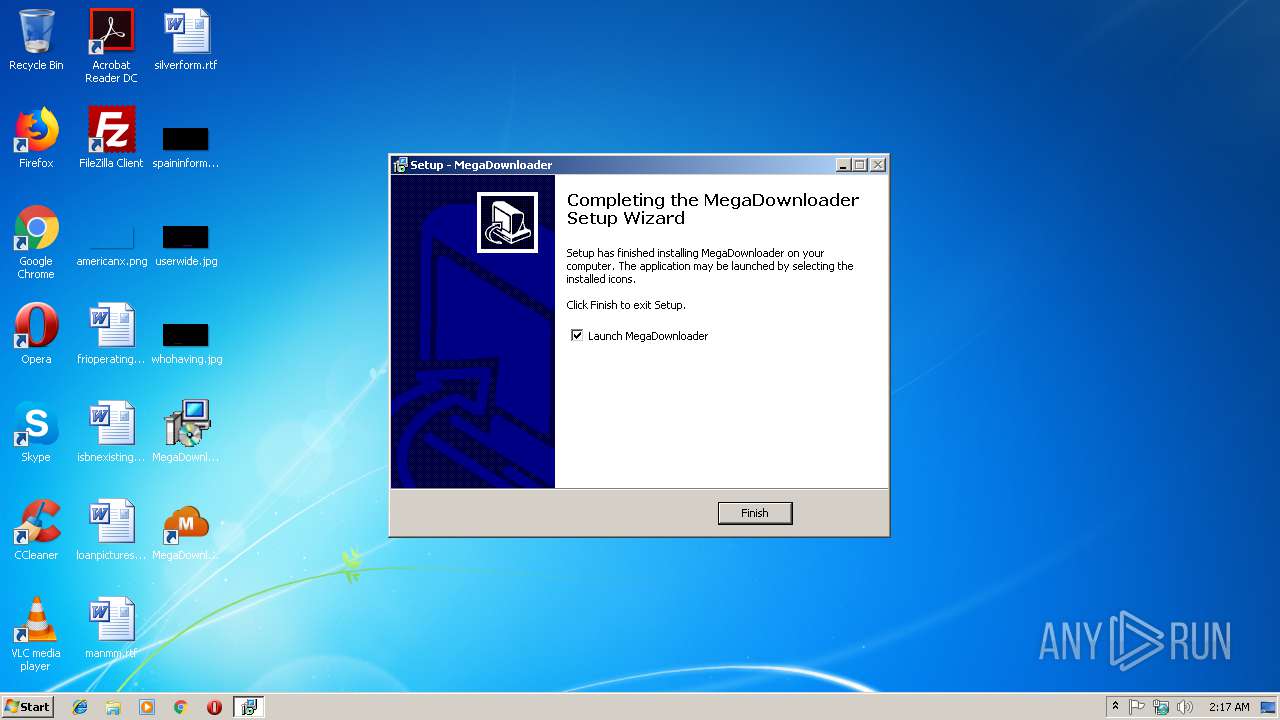
MALICIOUS
Application was dropped or rewritten from another process
- MegaDownloader.exe (PID: 3140)
SUSPICIOUS
Reads Environment values
- MegaDownloader.exe (PID: 3140)
Executable content was dropped or overwritten
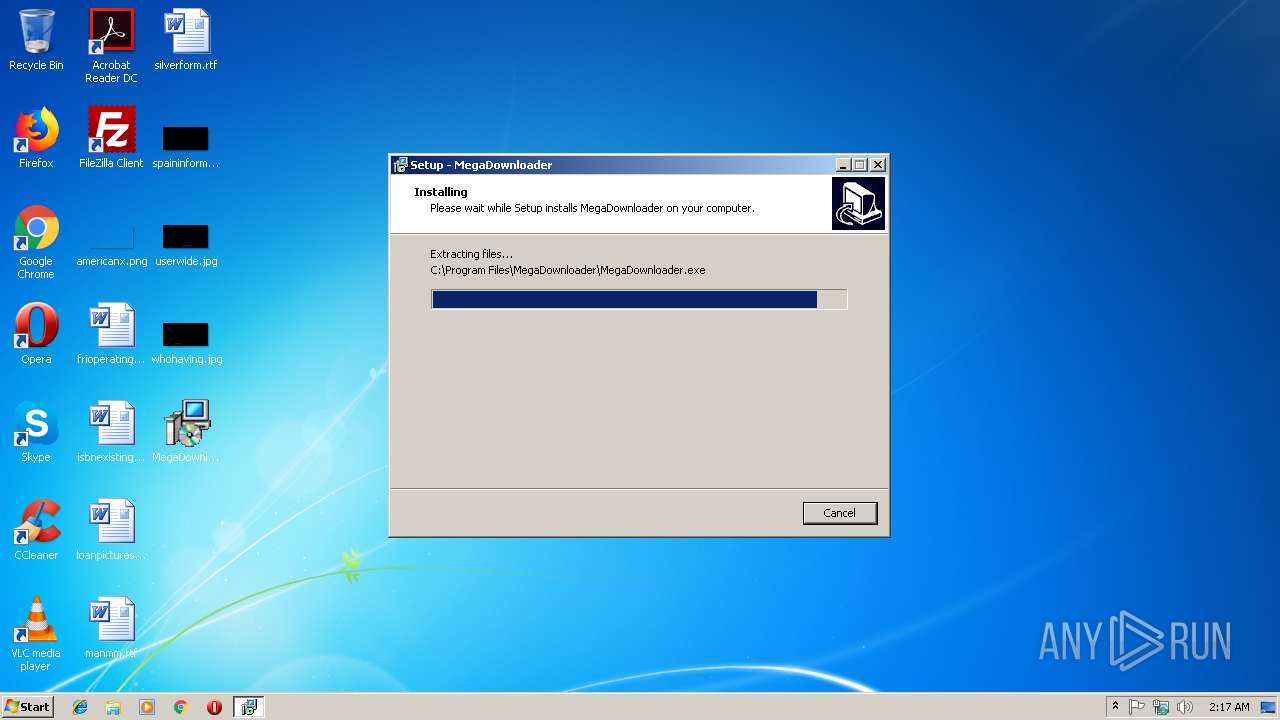
- MegaDownloader_v1.7.tmp (PID: 3112)
- MegaDownloader_v1.7.exe (PID: 2360)
- MegaDownloader_v1.7.exe (PID: 2732)
Reads internet explorer settings
- MegaDownloader.exe (PID: 3140)
Modifies the open verb of a shell class
- MegaDownloader_v1.7.tmp (PID: 3112)
INFO
Application was dropped or rewritten from another process
- MegaDownloader_v1.7.tmp (PID: 3428)
- MegaDownloader_v1.7.tmp (PID: 3112)
Loads dropped or rewritten executable
- MegaDownloader_v1.7.tmp (PID: 3112)
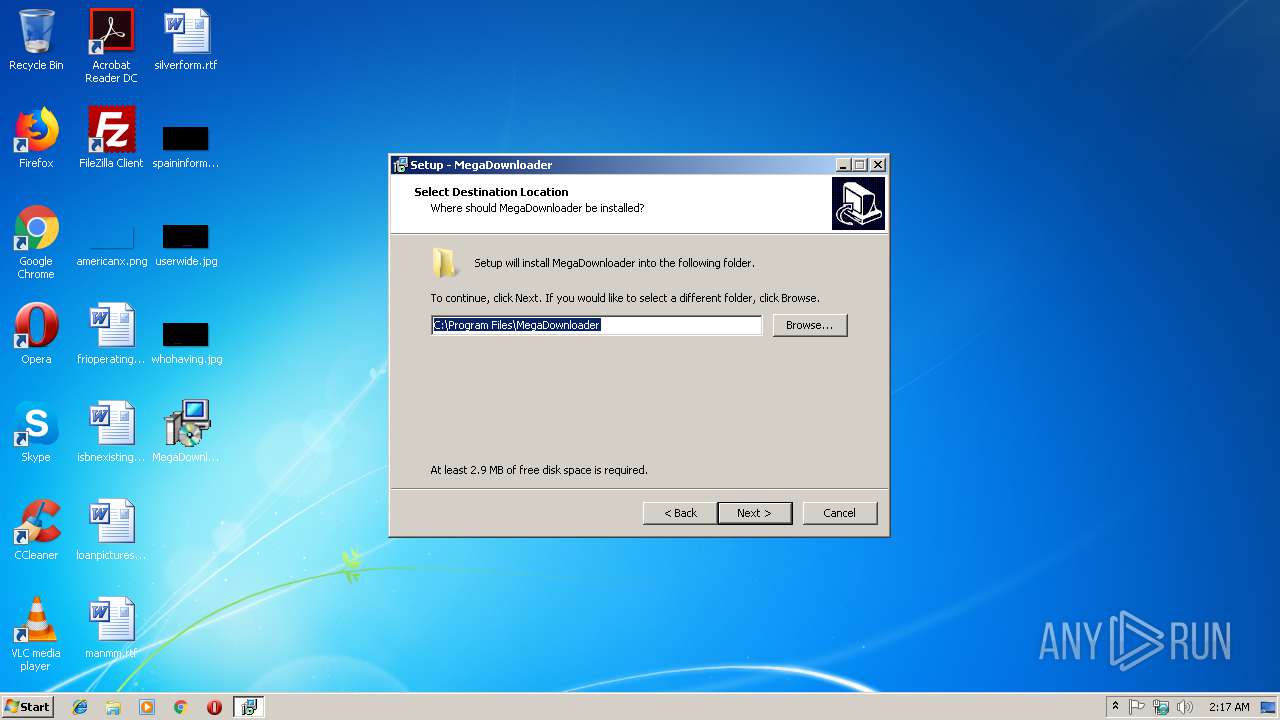
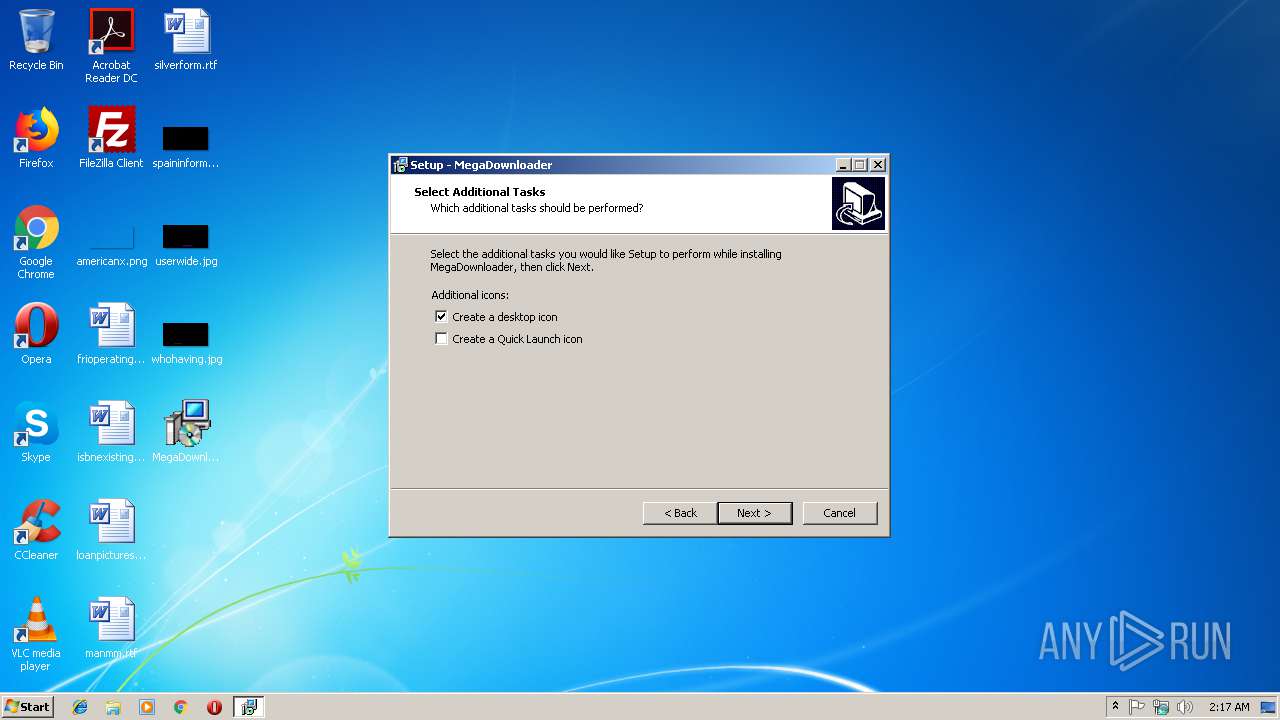
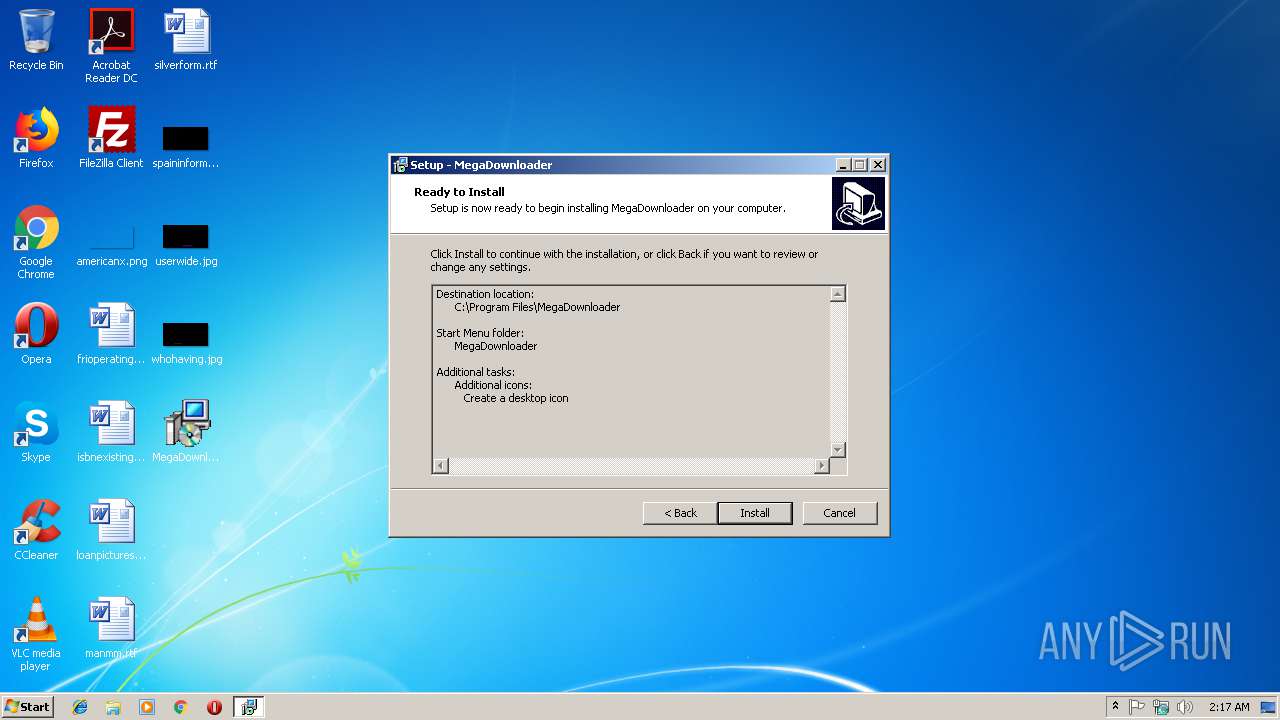
Creates files in the program directory
- MegaDownloader_v1.7.tmp (PID: 3112)
Creates a software uninstall entry
- MegaDownloader_v1.7.tmp (PID: 3112)
Reads settings of System Certificates
- MegaDownloader.exe (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (71.1) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (9.1) |
| .scr | | | Windows screen saver (8.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.2) |
| .exe | | | Win32 Executable (generic) (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40448 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa5f8 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.7.0.0 |
| ProductVersionNumber: | 1.7.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | AppsForMega.info |
| FileDescription: | MegaDownloader Setup |
| FileVersion: | 1.7 |
| LegalCopyright: | Copyright © 2015 |
| ProductName: | MegaDownloader |
| ProductVersion: | 1.7 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | AppsForMega.info |
| FileDescription: | MegaDownloader Setup |
| FileVersion: | 1.7 |
| LegalCopyright: | Copyright © 2015 |
| ProductName: | MegaDownloader |
| ProductVersion: | 1.7 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009D30 | 0x00009E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63177 |
DATA | 0x0000B000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75182 |
BSS | 0x0000C000 | 0x00000E8C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008C4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.54823 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11919 | 1512 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
41
Monitored processes
5
Malicious processes
0
Suspicious processes
0
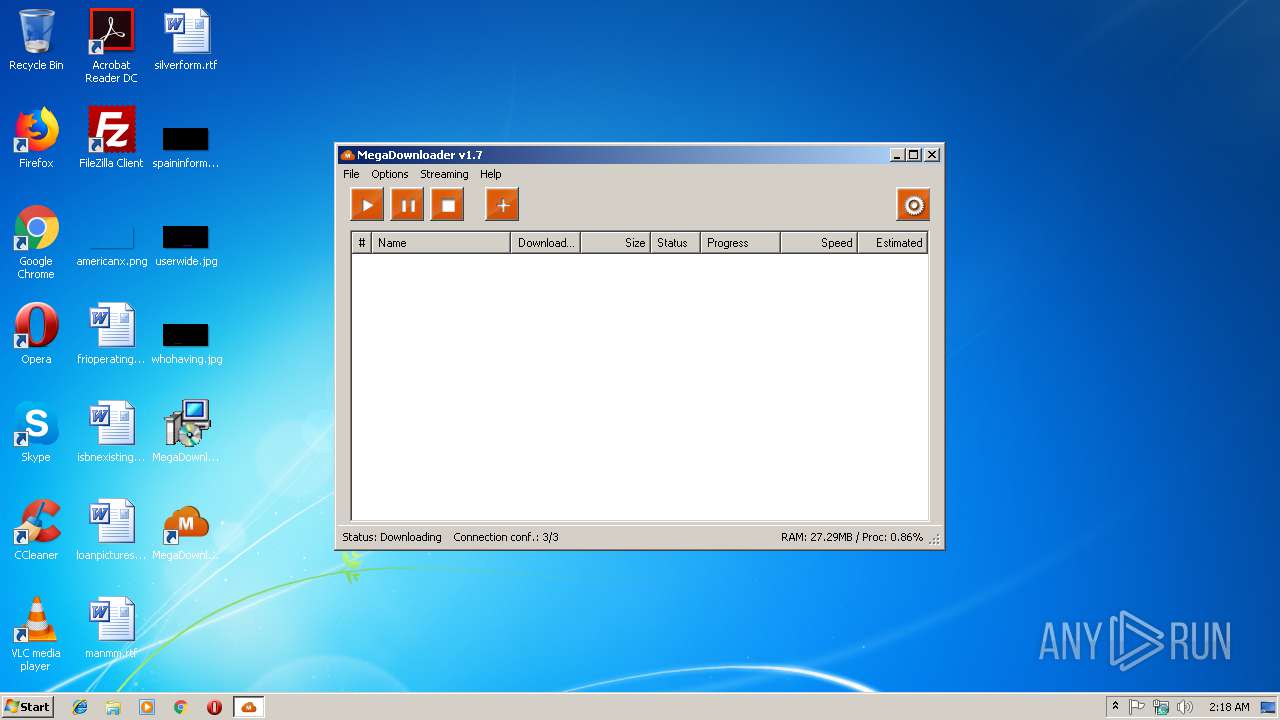
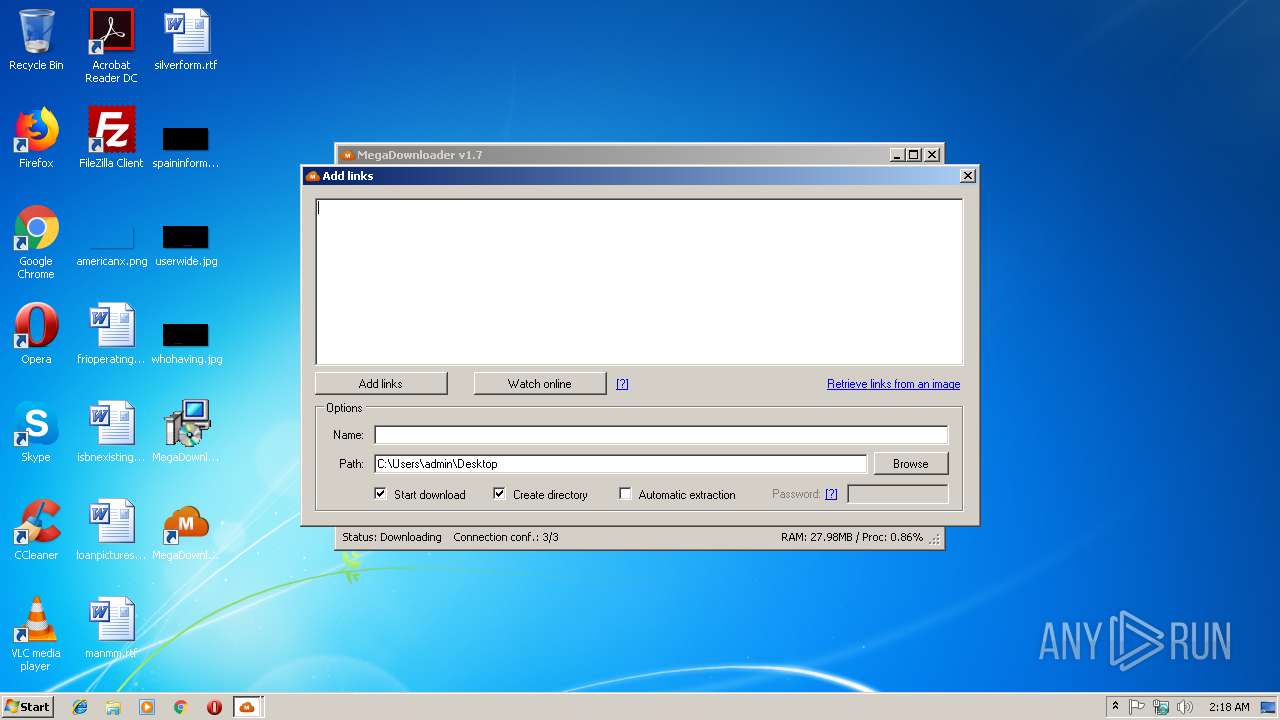
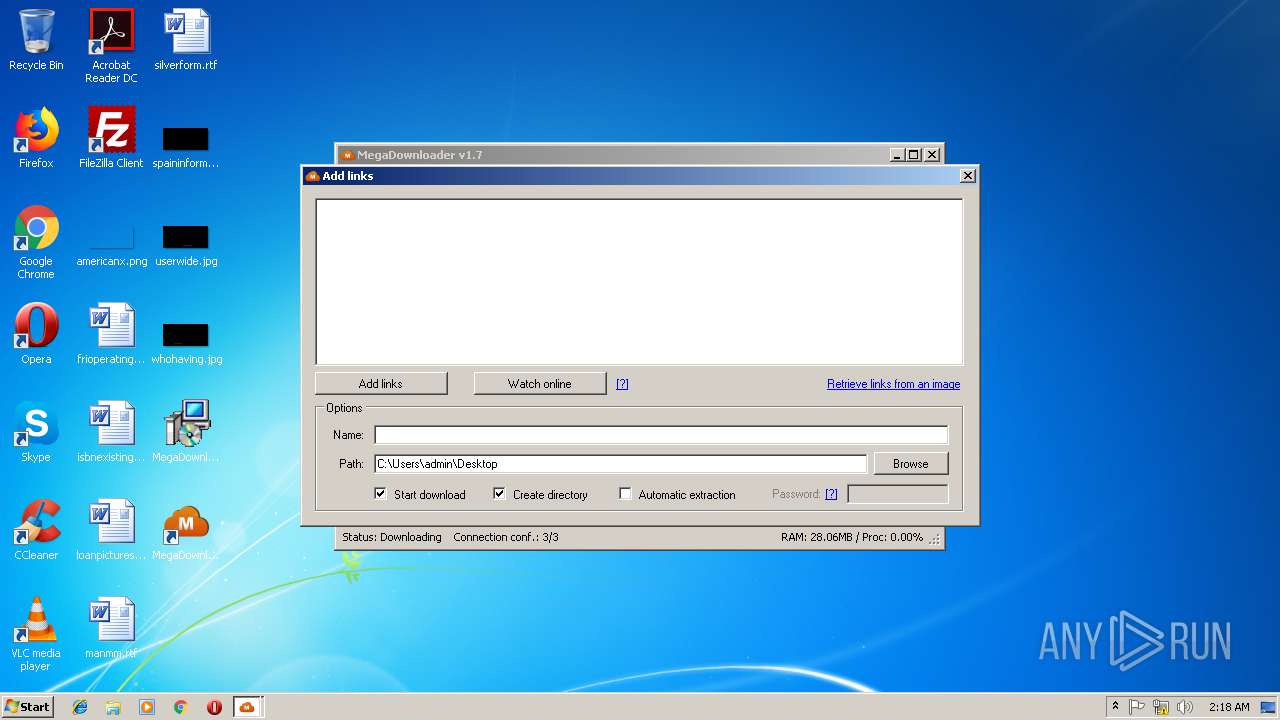
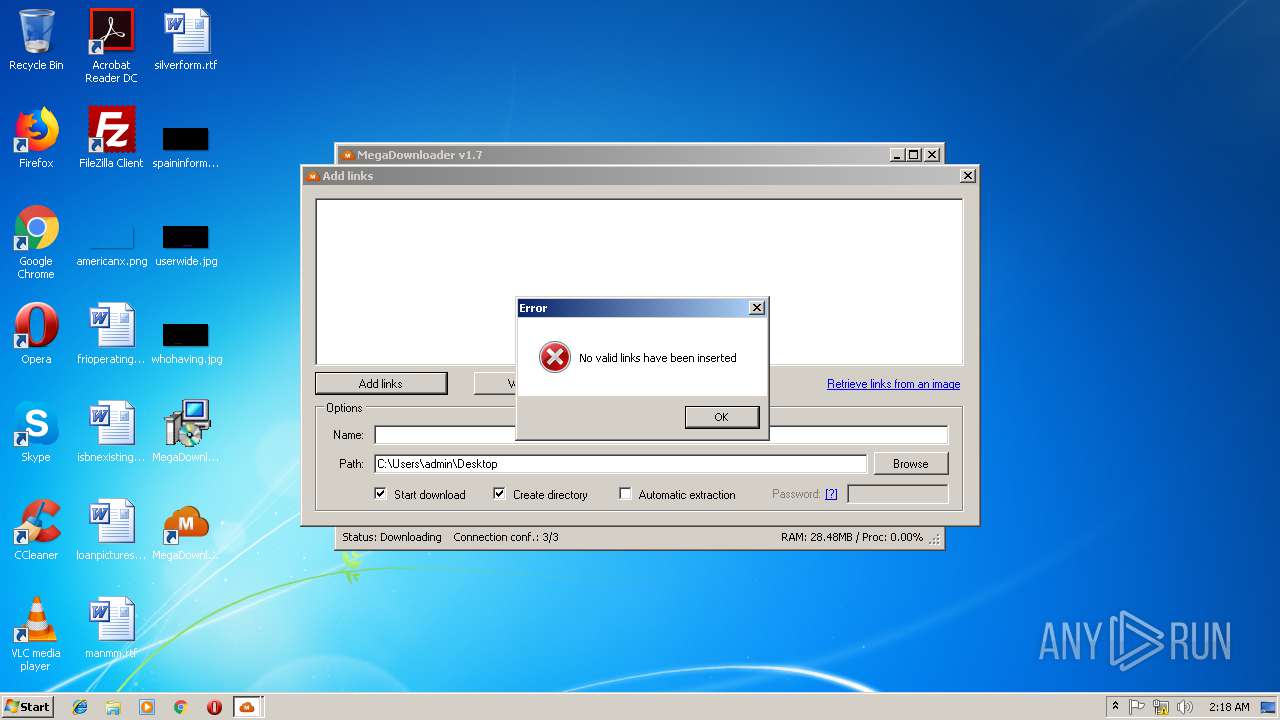
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2360 | "C:\Users\admin\Desktop\MegaDownloader_v1.7.exe" | C:\Users\admin\Desktop\MegaDownloader_v1.7.exe | explorer.exe | ||||||||||||
User: admin Company: AppsForMega.info Integrity Level: MEDIUM Description: MegaDownloader Setup Exit code: 0 Version: 1.7 Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\Desktop\MegaDownloader_v1.7.exe" /SPAWNWND=$20116 /NOTIFYWND=$20110 | C:\Users\admin\Desktop\MegaDownloader_v1.7.exe | MegaDownloader_v1.7.tmp | ||||||||||||
User: admin Company: AppsForMega.info Integrity Level: HIGH Description: MegaDownloader Setup Exit code: 0 Version: 1.7 Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\AppData\Local\Temp\is-QQLEB.tmp\MegaDownloader_v1.7.tmp" /SL5="$3011E,1831344,56832,C:\Users\admin\Desktop\MegaDownloader_v1.7.exe" /SPAWNWND=$20116 /NOTIFYWND=$20110 | C:\Users\admin\AppData\Local\Temp\is-QQLEB.tmp\MegaDownloader_v1.7.tmp | MegaDownloader_v1.7.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
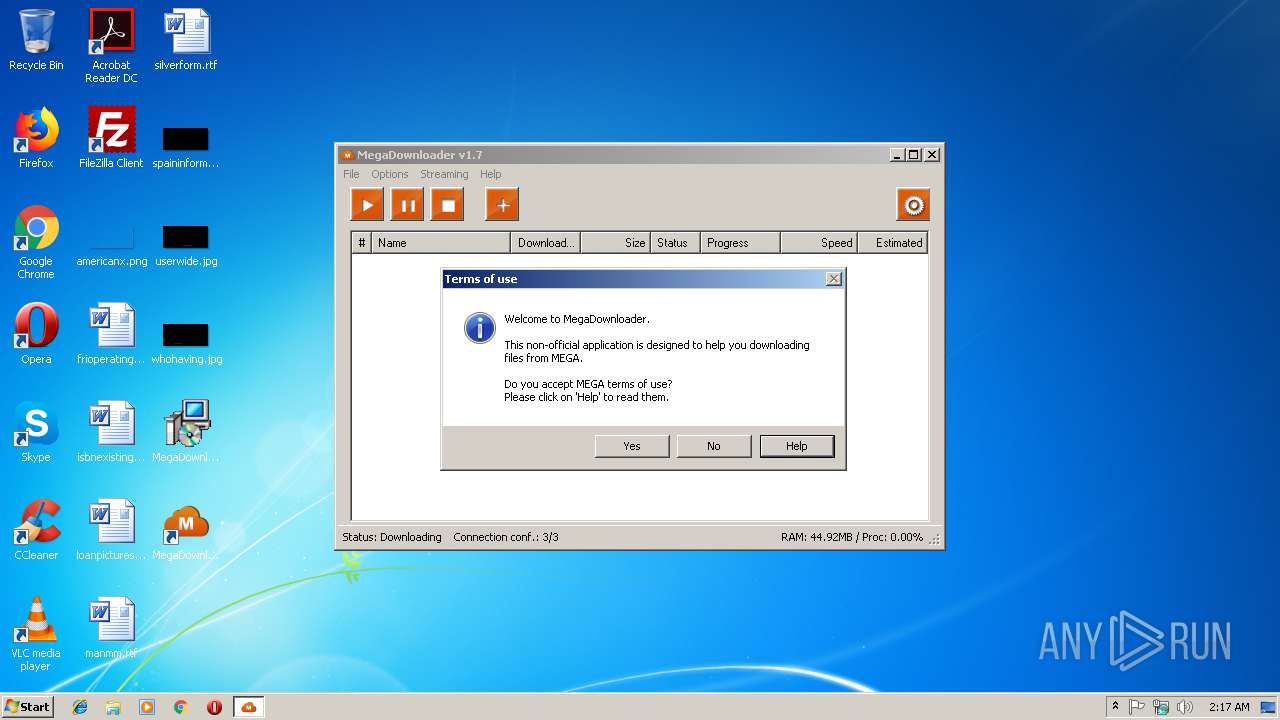
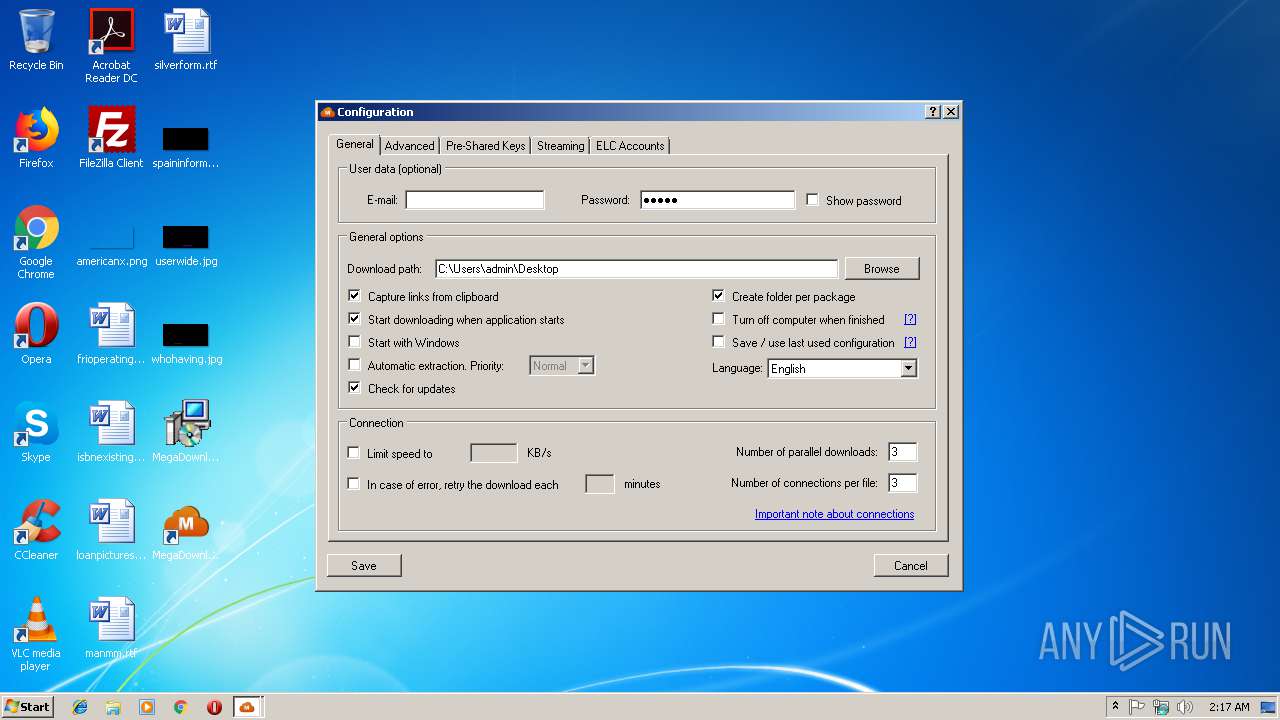
| 3140 | "C:\Program Files\MegaDownloader\MegaDownloader.exe" | C:\Program Files\MegaDownloader\MegaDownloader.exe | MegaDownloader_v1.7.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MegaDownloader Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3428 | "C:\Users\admin\AppData\Local\Temp\is-PABLA.tmp\MegaDownloader_v1.7.tmp" /SL5="$20110,1831344,56832,C:\Users\admin\Desktop\MegaDownloader_v1.7.exe" | C:\Users\admin\AppData\Local\Temp\is-PABLA.tmp\MegaDownloader_v1.7.tmp | — | MegaDownloader_v1.7.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
457
Read events
398
Write events
53
Delete events
6
Modification events
| (PID) Process: | (3112) MegaDownloader_v1.7.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 280C0000DD35A9DC9B83D401 | |||
| (PID) Process: | (3112) MegaDownloader_v1.7.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 09F401D79FC810692CA78BFB8FC0BE1AD96C4A68DD8E0570BDA8EBE5DCA7B256 | |||
| (PID) Process: | (3112) MegaDownloader_v1.7.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3112) MegaDownloader_v1.7.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\MegaDownloader\MegaDownloader.exe | |||
| (PID) Process: | (3112) MegaDownloader_v1.7.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 27132C84DECFFAD2C5C9F9926AFADAFE34B2DB6EAAA71FD018E57EBCA5600DB0 | |||
| (PID) Process: | (3112) MegaDownloader_v1.7.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\mega |
| Operation: | write | Name: | |
Value: URL: mega Protocol | |||
| (PID) Process: | (3112) MegaDownloader_v1.7.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\mega |
| Operation: | write | Name: | URL protocol |
Value: | |||
| (PID) Process: | (3112) MegaDownloader_v1.7.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\mega\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Program Files\MegaDownloader\MegaDownloader.exe" %1 | |||
| (PID) Process: | (3112) MegaDownloader_v1.7.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MegaDownloader |
| Operation: | write | Name: | Installer |
Value: 1 | |||
| (PID) Process: | (3112) MegaDownloader_v1.7.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{C12C2297-65A4-4E64-9AE1-29F0D947FDA0}}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.5 (a) | |||
Executable files
6
Suspicious files
0
Text files
16
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3112 | MegaDownloader_v1.7.tmp | C:\Program Files\MegaDownloader\is-67TB4.tmp | — | |
MD5:— | SHA256:— | |||
| 3112 | MegaDownloader_v1.7.tmp | C:\Program Files\MegaDownloader\is-CCESA.tmp | — | |
MD5:— | SHA256:— | |||
| 3112 | MegaDownloader_v1.7.tmp | C:\Users\Public\Desktop\MegaDownloader.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3112 | MegaDownloader_v1.7.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\MegaDownloader\Uninstall MegaDownloader.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3112 | MegaDownloader_v1.7.tmp | C:\Program Files\MegaDownloader\unins000.dat | dat | |
MD5:— | SHA256:— | |||
| 2732 | MegaDownloader_v1.7.exe | C:\Users\admin\AppData\Local\Temp\is-QQLEB.tmp\MegaDownloader_v1.7.tmp | executable | |
MD5:9303156631EE2436DB23827E27337BE4 | SHA256:BAE22F27C12BCE1FAEB64B6EB733302AFF5867BAA8EED832397A7CE284A86FF4 | |||
| 3112 | MegaDownloader_v1.7.tmp | C:\Program Files\MegaDownloader\MegaDownloader.exe | executable | |
MD5:02D50582F3216D59744F80B407BA0B70 | SHA256:DD2E64E27B2A982FD08365C37A26953C28FD386EC075C47CC05101C2B2660D2B | |||
| 3112 | MegaDownloader_v1.7.tmp | C:\Program Files\MegaDownloader\unins000.exe | executable | |
MD5:0E8C37CB9EA9BA5F197BF1366ADC05ED | SHA256:9480E40E1D70858D766628697F476B18A728D88361B58D41BF1B04BE48C56BA3 | |||
| 3112 | MegaDownloader_v1.7.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\MegaDownloader\MegaDownloader.lnk | lnk | |
MD5:8D14ED7C8832FDF60115A7D20E2C2F02 | SHA256:F4A02FD4DC231A4D5363BCF1060BBF5D864C814FFAAA28C21CD82E0FAE99C64F | |||
| 3140 | MegaDownloader.exe | C:\Users\admin\AppData\Local\MegaDownloader\Language\ro-RO.xml | xml | |
MD5:54867276EDBC9AA48628494AE3D565CF | SHA256:BFDD3DCBE42E7E9B8EC25D710F0418189870ABC99786E96799211939B83EB2C9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3140 | MegaDownloader.exe | GET | 200 | 87.98.231.40:80 | http://www.checkforupdates.ovh/megadownloader.xml?d=2018112402 | ES | text | 82 b | whitelisted |
3140 | MegaDownloader.exe | GET | 301 | 172.217.168.14:80 | http://goo.gl/UfSSNF | US | html | 233 b | shared |
3140 | MegaDownloader.exe | GET | 200 | 188.165.7.40:80 | http://megadownloader.appsformega.info/new_user.xml | IE | text | 65 b | malicious |
3140 | MegaDownloader.exe | GET | 200 | 188.165.7.40:80 | http://megadownloader.appsformega.info/new_version.xml?v=1.7 | IE | text | 65 b | malicious |
3140 | MegaDownloader.exe | GET | 301 | 172.217.168.14:80 | http://goo.gl/z47iWJ | US | html | 242 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3140 | MegaDownloader.exe | 31.216.147.130:443 | www.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
3140 | MegaDownloader.exe | 87.98.231.40:80 | www.checkforupdates.ovh | OVH SAS | ES | malicious |
3140 | MegaDownloader.exe | 188.165.7.40:80 | megadownloader.appsformega.info | OVH SAS | IE | suspicious |
3140 | MegaDownloader.exe | 172.217.168.14:80 | goo.gl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mega.co.nz |
| shared |
www.checkforupdates.ovh |
| whitelisted |
mega.co.nz |
| shared |
goo.gl |
| shared |
megadownloader.appsformega.info |
| malicious |