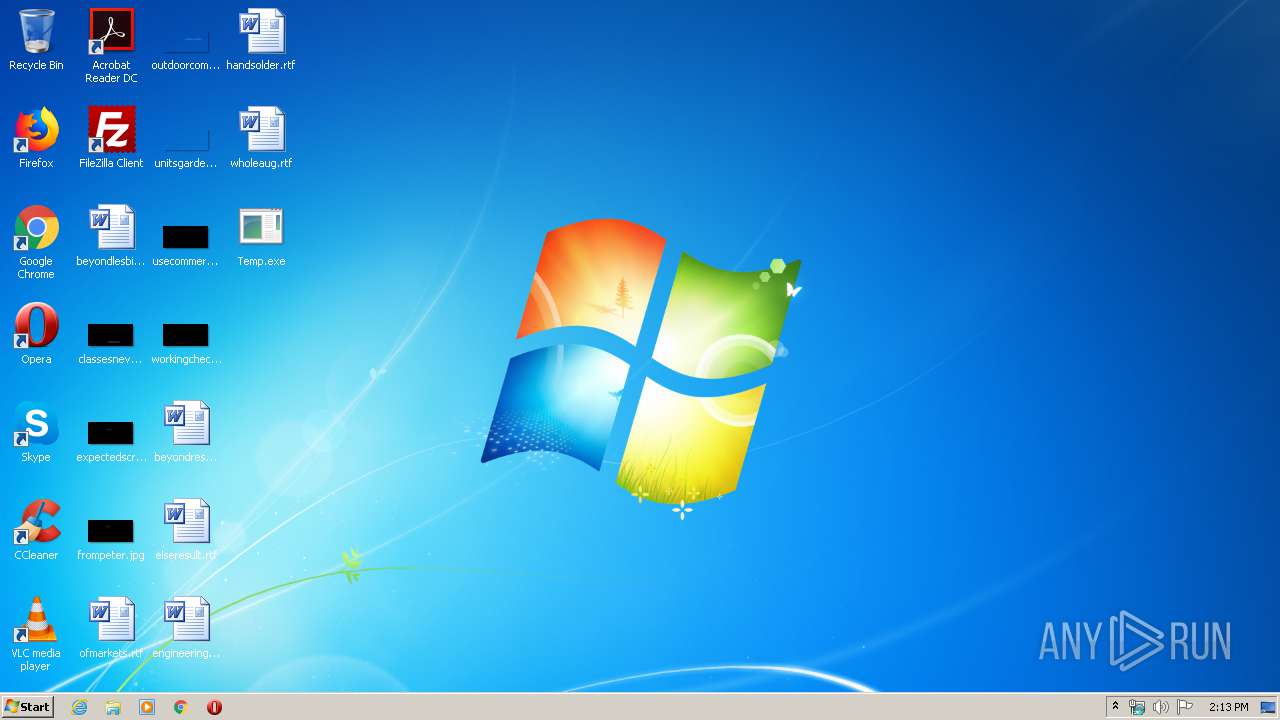
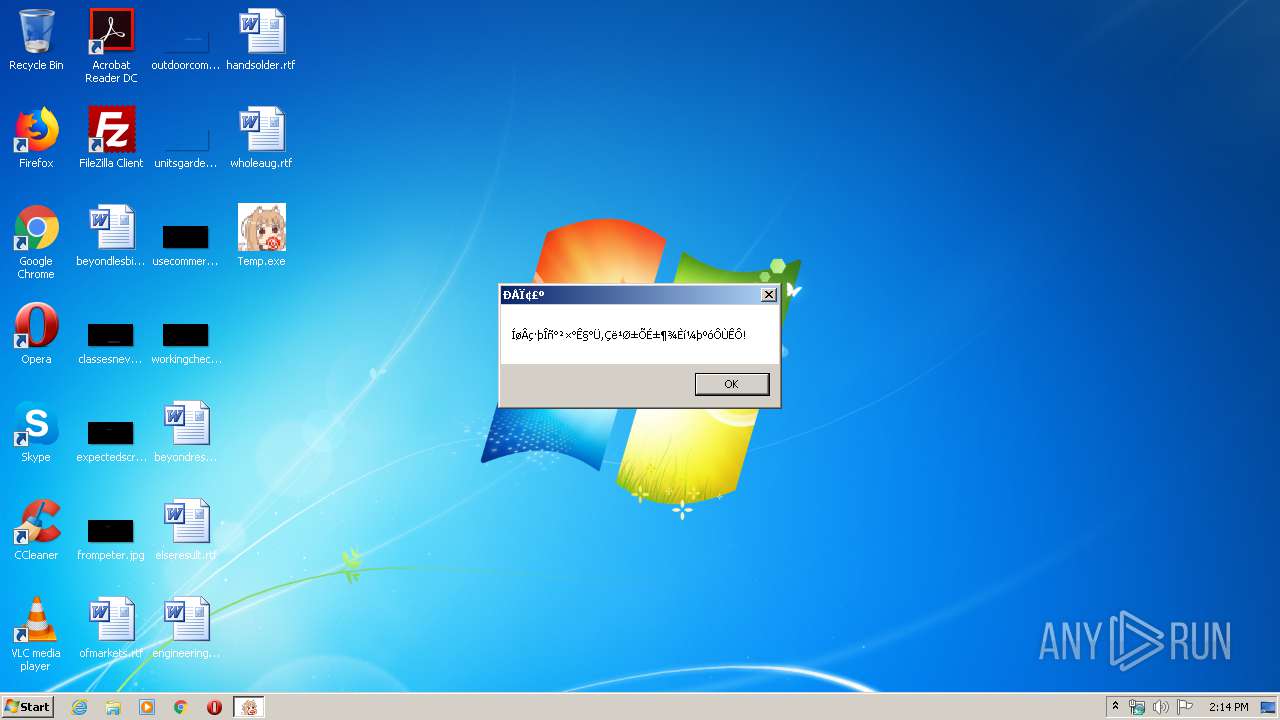
| File name: | Temp.exe |
| Full analysis: | https://app.any.run/tasks/cf7bfa0c-acdd-46c2-bfd8-e33b7a2f188c |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2020, 14:13:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 04C31D3670C6B684591FEB8018216AF4 |
| SHA1: | 4361297B3140C8E970BCC572253E31440774DD44 |
| SHA256: | 6CB652A00AFDF35A60B8BD9042DE793BCBDEDDA045AF684E560571788F1625F8 |
| SSDEEP: | 196608:QI5L2HGsOLJvzmcX5FnqMKBMDi8vWvyu0F:QI5KmsOxmuzKBOl7R |
MALICIOUS
Loads dropped or rewritten executable
- Temp.exe (PID: 304)
Application was dropped or rewritten from another process
- AndroidEmulator.exe (PID: 2904)
- ±ùºÛ.exe (PID: 1380)
SUSPICIOUS
Creates files in the Windows directory
- Temp.exe (PID: 304)
Starts CMD.EXE for commands execution
- Temp.exe (PID: 304)
Executable content was dropped or overwritten
- Temp.exe (PID: 304)
INFO
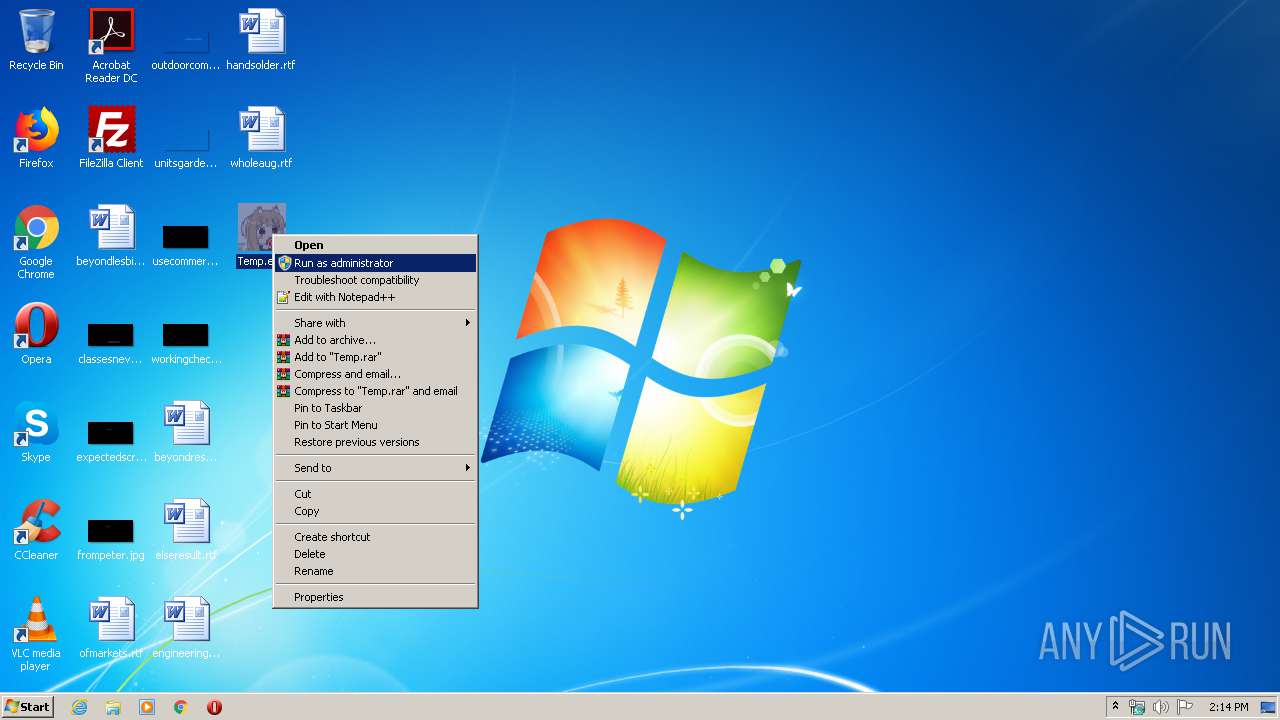
Manual execution by user
- Temp.exe (PID: 304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (72.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (11.7) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
| .exe | | | DOS Executable Generic (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:21 10:00:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 618496 |
| InitializedDataSize: | 11739136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x10306bc |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| FileDescription: | 金龙 |
| ProductName: | 金龙 |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | 作者版权所有 请尊重并使用正版 |
| Comments: | 金龙 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Feb-2020 09:00:36 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| FileDescription: | 金龙 |
| ProductName: | 金龙 |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | 作者版权所有 请尊重并使用正版 |
| Comments: | 金龙 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 21-Feb-2020 09:00:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000967BA | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.rdata | 0x00098000 | 0x00B14EF2 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.data | 0x00BAD000 | 0x000538CA | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.vmp0 | 0x00C01000 | 0x00337D03 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.vmp1 | 0x00F39000 | 0x008FE3C0 | 0x008FF000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.98285 |
.rsrc | 0x01838000 | 0x00001AC9 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.6919 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.10342 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
1151 | 2.16096 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
1152 | 2.02322 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
DEFAULT_ICON | 1.94375 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WINMM.dll |
WINSPOOL.DRV |
WS2_32.dll |
Total processes
45
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Users\admin\Desktop\Temp.exe" | C:\Users\admin\Desktop\Temp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 金龙 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1380 | C:\Users\admin\AppData\Local\Temp\±ùºÛ.exe | C:\Users\admin\AppData\Local\Temp\±ùºÛ.exe | Temp.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 2904 | \AndroidEmulator.exe | C:\AndroidEmulator.exe | — | Temp.exe | |||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: Tencent Gaming Buddy Exit code: 3221225781 Version: 2.0.11646.123 Modules
| |||||||||||||||
| 3424 | "C:\Users\admin\Desktop\Temp.exe" | C:\Users\admin\Desktop\Temp.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 金龙 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3620 | cmd /c ""C:\connect.bat" " | C:\Windows\system32\cmd.exe | — | Temp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
127
Read events
106
Write events
20
Delete events
1
Modification events
| (PID) Process: | (304) Temp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\ESPI11 |
| Operation: | write | Name: | 1001 |
Value: 2553797374656D526F6F74255C73797374656D33325C6D7377736F636B2E646C6C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000006600020000000000000000000000000008000000A01A0FE78BABCF118CA300805F48A192E90300000100000000000000000000000000000000000000000000000000000000000000020000000200000010000000100000000100000006000000000000000000000000000000000000000000000040002500530079007300740065006D0052006F006F00740025005C00530079007300740065006D00330032005C00770073006800740063007000690070002E0064006C006C002C002D00360030003100300030000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (304) Temp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\Protocol_Catalog9\Catalog_Entries\000000000001 |
| Operation: | write | Name: | PackedCatalogItem |
Value: 433A5C57696E646F77735C73797374656D33325C4553504931312E646C6C006C6C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000006600020000000000000000000000000008000000A01A0FE78BABCF118CA300805F48A192E90300000100000000000000000000000000000000000000000000000000000000000000020000000200000010000000100000000100000006000000000000000000000000000000000000000000000040002500530079007300740065006D0052006F006F00740025005C00530079007300740065006D00330032005C00770073006800740063007000690070002E0064006C006C002C002D00360030003100300030000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (304) Temp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\ESPI11 |
| Operation: | write | Name: | 1002 |
Value: 2553797374656D526F6F74255C73797374656D33325C6D7377736F636B2E646C6C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000906020000000000000000000000000008000000A01A0FE78BABCF118CA300805F48A192EA0300000100000000000000000000000000000000000000000000000000000000000000020000000200000010000000100000000200000011000000000000000000000000000000F7FF00000000000040002500530079007300740065006D0052006F006F00740025005C00530079007300740065006D00330032005C00770073006800740063007000690070002E0064006C006C002C002D00360030003100300031000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (304) Temp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\Protocol_Catalog9\Catalog_Entries\000000000002 |
| Operation: | write | Name: | PackedCatalogItem |
Value: 433A5C57696E646F77735C73797374656D33325C4553504931312E646C6C006C6C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000906020000000000000000000000000008000000A01A0FE78BABCF118CA300805F48A192EA0300000100000000000000000000000000000000000000000000000000000000000000020000000200000010000000100000000200000011000000000000000000000000000000F7FF00000000000040002500530079007300740065006D0052006F006F00740025005C00530079007300740065006D00330032005C00770073006800740063007000690070002E0064006C006C002C002D00360030003100300031000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (304) Temp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\ESPI11 |
| Operation: | write | Name: | 1003 |
Value: 2553797374656D526F6F74255C73797374656D33325C6D7377736F636B2E646C6C0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000090602000000000000000000000000000C000000A01A0FE78BABCF118CA300805F48A192EB0300000100000000000000000000000000000000000000000000000000000000000000020000000200000010000000100000000300000000000000FF0000000000000000000000008000000000000040002500530079007300740065006D0052006F006F00740025005C00530079007300740065006D00330032005C00770073006800740063007000690070002E0064006C006C002C002D00360030003100300032000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (304) Temp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\Protocol_Catalog9\Catalog_Entries\000000000003 |
| Operation: | write | Name: | PackedCatalogItem |
Value: 433A5C57696E646F77735C73797374656D33325C4553504931312E646C6C006C6C0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000090602000000000000000000000000000C000000A01A0FE78BABCF118CA300805F48A192EB0300000100000000000000000000000000000000000000000000000000000000000000020000000200000010000000100000000300000000000000FF0000000000000000000000008000000000000040002500530079007300740065006D0052006F006F00740025005C00530079007300740065006D00330032005C00770073006800740063007000690070002E0064006C006C002C002D00360030003100300032000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (304) Temp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\ESPI11 |
| Operation: | write | Name: | 1012 |
Value: 2553797374656D526F6F74255C73797374656D33325C6D7377736F636B2E646C6C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000006620020000000000000000000000000008000000E0A9609D7A33D011BD880000C082E69AF40300000100000000000000000000000000000000000000000000000000000000000000020000000200000010000000100000000100000006000000000000000000000000000000000000000000000040002500530079007300740065006D0052006F006F00740025005C00530079007300740065006D00330032005C0077007300680071006F0073002E0064006C006C002C002D0031003000310000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (304) Temp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\Protocol_Catalog9\Catalog_Entries\000000000008 |
| Operation: | write | Name: | PackedCatalogItem |
Value: 433A5C57696E646F77735C73797374656D33325C4553504931312E646C6C006C6C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000006620020000000000000000000000000008000000E0A9609D7A33D011BD880000C082E69AF40300000100000000000000000000000000000000000000000000000000000000000000020000000200000010000000100000000100000006000000000000000000000000000000000000000000000040002500530079007300740065006D0052006F006F00740025005C00530079007300740065006D00330032005C0077007300680071006F0073002E0064006C006C002C002D0031003000310000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (304) Temp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\ESPI11 |
| Operation: | write | Name: | 1014 |
Value: 2553797374656D526F6F74255C73797374656D33325C6D7377736F636B2E646C6C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000926020000000000000000000000000008000000E0A9609D7A33D011BD880000C082E69AF60300000100000000000000000000000000000000000000000000000000000000000000020000000200000010000000100000000200000011000000000000000000000000000000F7FF00000000000040002500530079007300740065006D0052006F006F00740025005C00530079007300740065006D00330032005C0077007300680071006F0073002E0064006C006C002C002D0031003000330000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (304) Temp.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\Protocol_Catalog9\Catalog_Entries\000000000010 |
| Operation: | write | Name: | PackedCatalogItem |
Value: 433A5C57696E646F77735C73797374656D33325C4553504931312E646C6C006C6C00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000926020000000000000000000000000008000000E0A9609D7A33D011BD880000C082E69AF60300000100000000000000000000000000000000000000000000000000000000000000020000000200000010000000100000000200000011000000000000000000000000000000F7FF00000000000040002500530079007300740065006D0052006F006F00740025005C00530079007300740065006D00330032005C0077007300680071006F0073002E0064006C006C002C002D0031003000330000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
9
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 304 | Temp.exe | C:\connect.bat | — | |
MD5:— | SHA256:— | |||
| 304 | Temp.exe | C:\aow_exe.exe | executable | |
MD5:— | SHA256:— | |||
| 304 | Temp.exe | C:\AOW_DRV_X64.SYS | executable | |
MD5:— | SHA256:— | |||
| 304 | Temp.exe | C:\libaow.dll | executable | |
MD5:— | SHA256:— | |||
| 304 | Temp.exe | C:\AOW_DRV_X64_EV.SYS | executable | |
MD5:— | SHA256:— | |||
| 304 | Temp.exe | C:\1.dll | o | |
MD5:— | SHA256:— | |||
| 304 | Temp.exe | C:\AEngineUtil.dll | executable | |
MD5:— | SHA256:— | |||
| 304 | Temp.exe | C:\Users\admin\AppData\Local\Temp\±ùºÛ.exe | executable | |
MD5:— | SHA256:— | |||
| 304 | Temp.exe | C:\AndroidEmulator.exe | executable | |
MD5:— | SHA256:— | |||
| 304 | Temp.exe | C:\Windows\system32\ESPI11.dll | executable | |
MD5:B4C2CAAA15D4E505AD2858AB15EAFB58 | SHA256:93E03EADD330242F2394C15CD32857194E5B80F6300835EF77F8558CA70A2EF1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report