| File name: | thhjgjk.exe |
| Full analysis: | https://app.any.run/tasks/226e4ff1-50f5-49f7-aeae-854ea0b901e8 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 06:08:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9D6D30A67013A7853E8055770B9E0CB4 |
| SHA1: | 6A93EA252A6D08D32BA18255D347B9E7BC0F8C43 |
| SHA256: | 6CB18148A9F9B7E810975B1ECCC74AE1E9D1785C80408090706F69E2957AD217 |
| SSDEEP: | 98304:h9U0Sp0651HvOIGbQyGUu2wJuKSfUvOpgZs4Jni:ND82IGUzX2MofTAJni |
MALICIOUS
Application was dropped or rewritten from another process
- nchsetup.exe (PID: 3888)
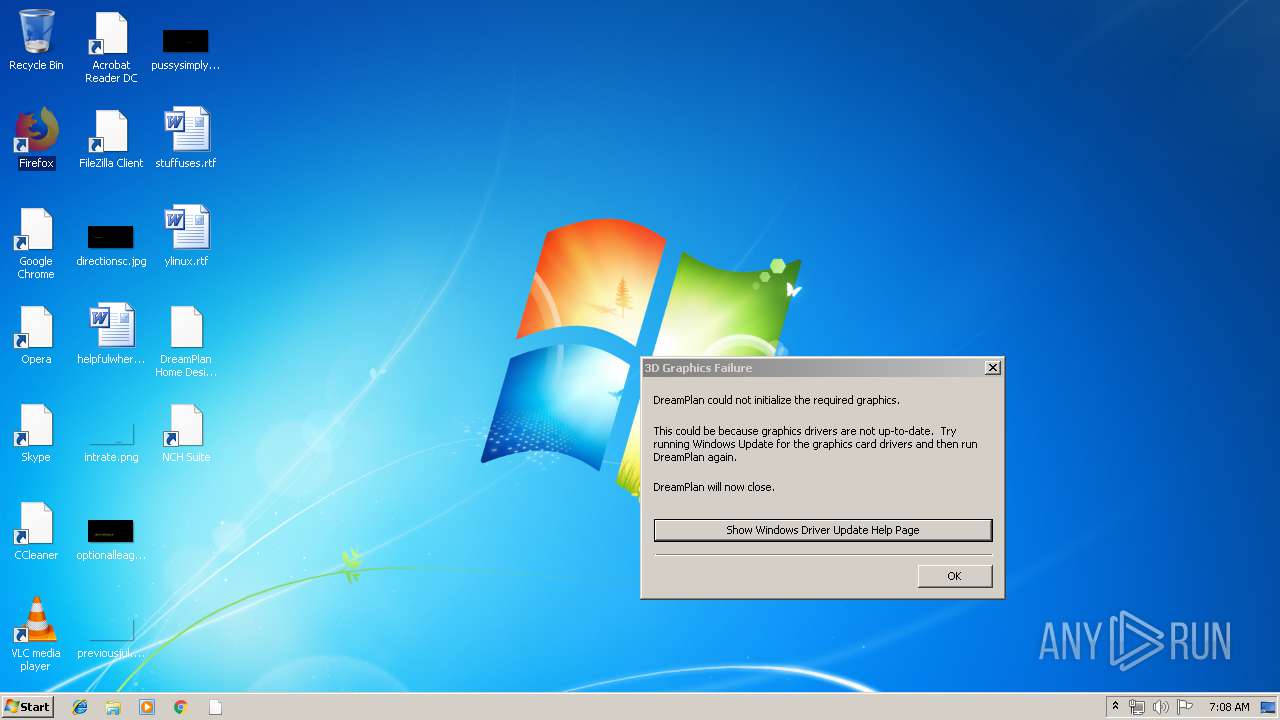
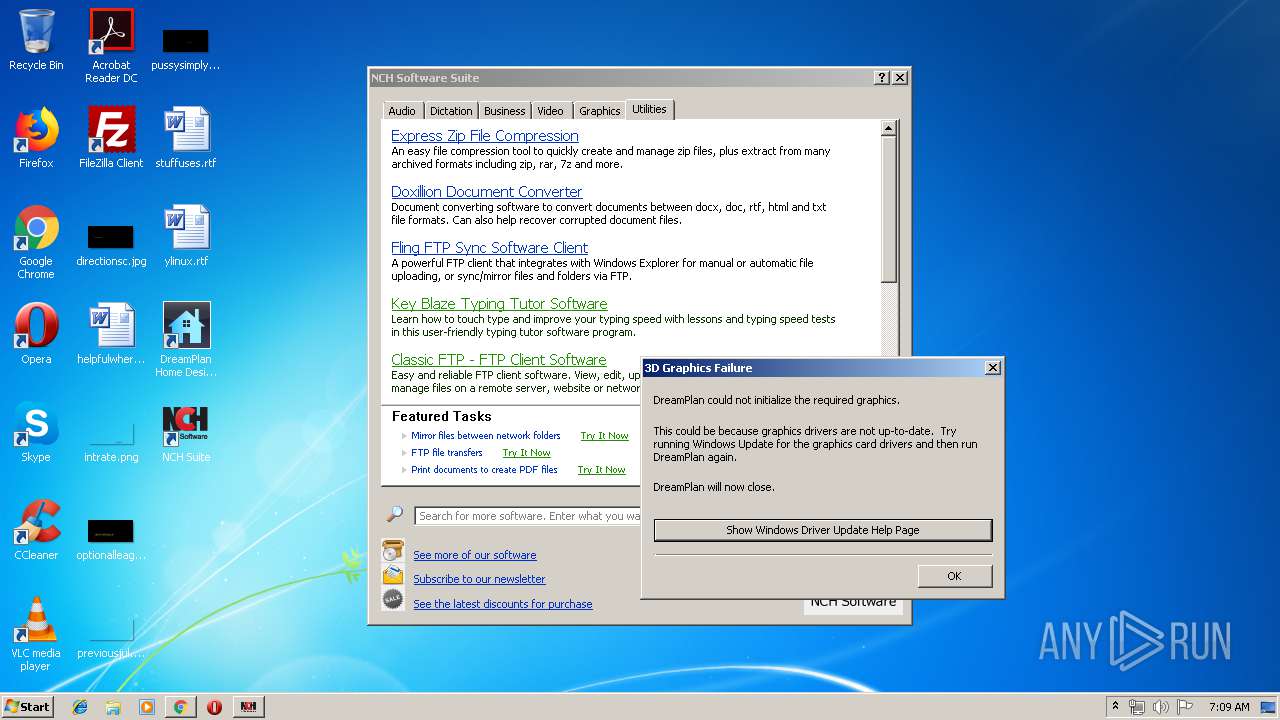
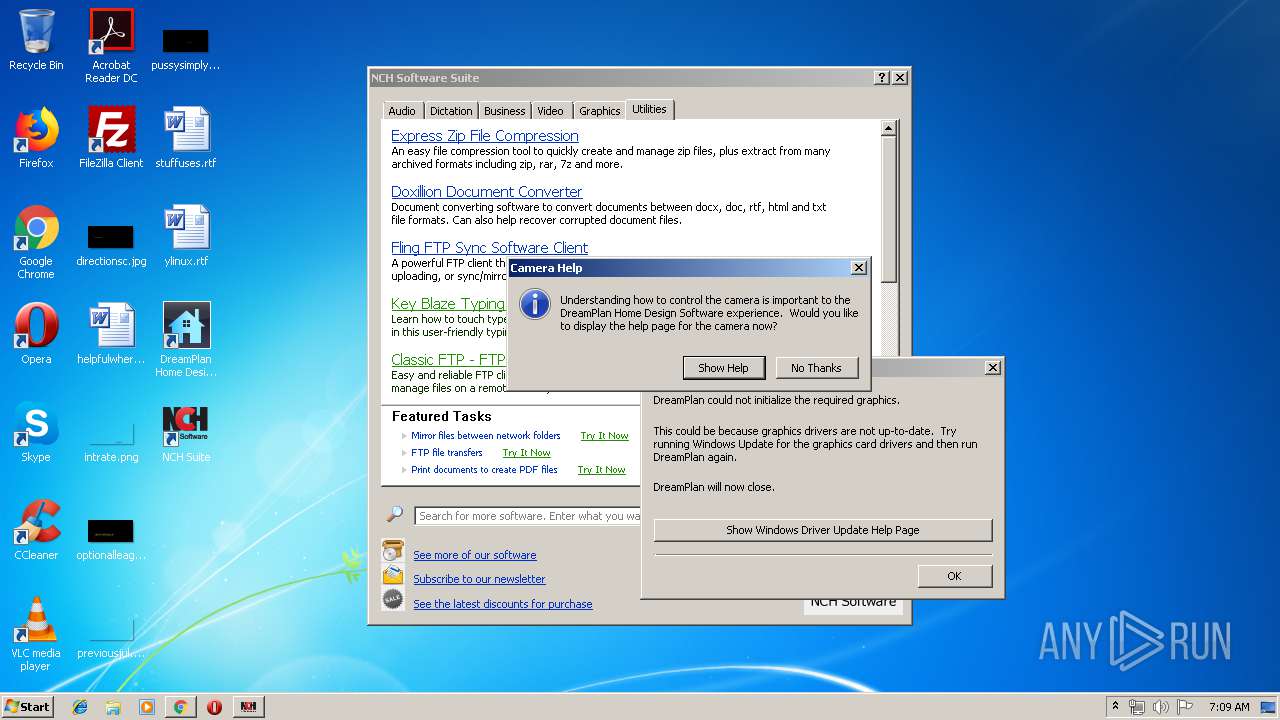
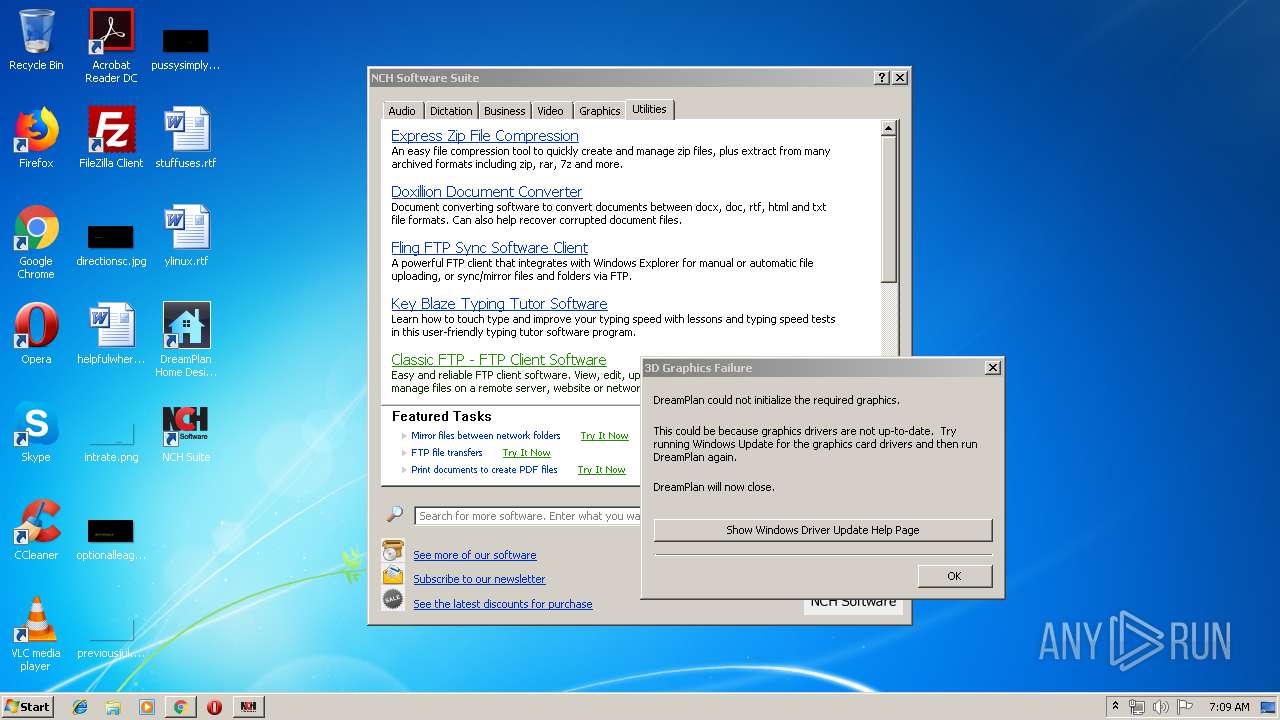
- dreamplan.exe (PID: 2748)
- dreamplan.exe (PID: 4044)
- zlib1.exe (PID: 3420)
- infozip3.exe (PID: 1912)
- dreamplan.exe (PID: 2660)
- dreamplan.exe (PID: 3232)
Loads the Task Scheduler COM API
- nchsetup.exe (PID: 3888)
- dreamplan.exe (PID: 4044)
- dreamplan.exe (PID: 2660)
SUSPICIOUS
Executable content was dropped or overwritten
- thhjgjk.exe (PID: 2412)
- zlib1.exe (PID: 3420)
- infozip3.exe (PID: 1912)
- nchsetup.exe (PID: 3888)
Creates files in the program directory
- zlib1.exe (PID: 3420)
- infozip3.exe (PID: 1912)
- nchsetup.exe (PID: 3888)
Creates a software uninstall entry
- nchsetup.exe (PID: 3888)
Starts itself from another location
- nchsetup.exe (PID: 3888)
Modifies the open verb of a shell class
- nchsetup.exe (PID: 3888)
Creates files in the user directory
- dreamplan.exe (PID: 2748)
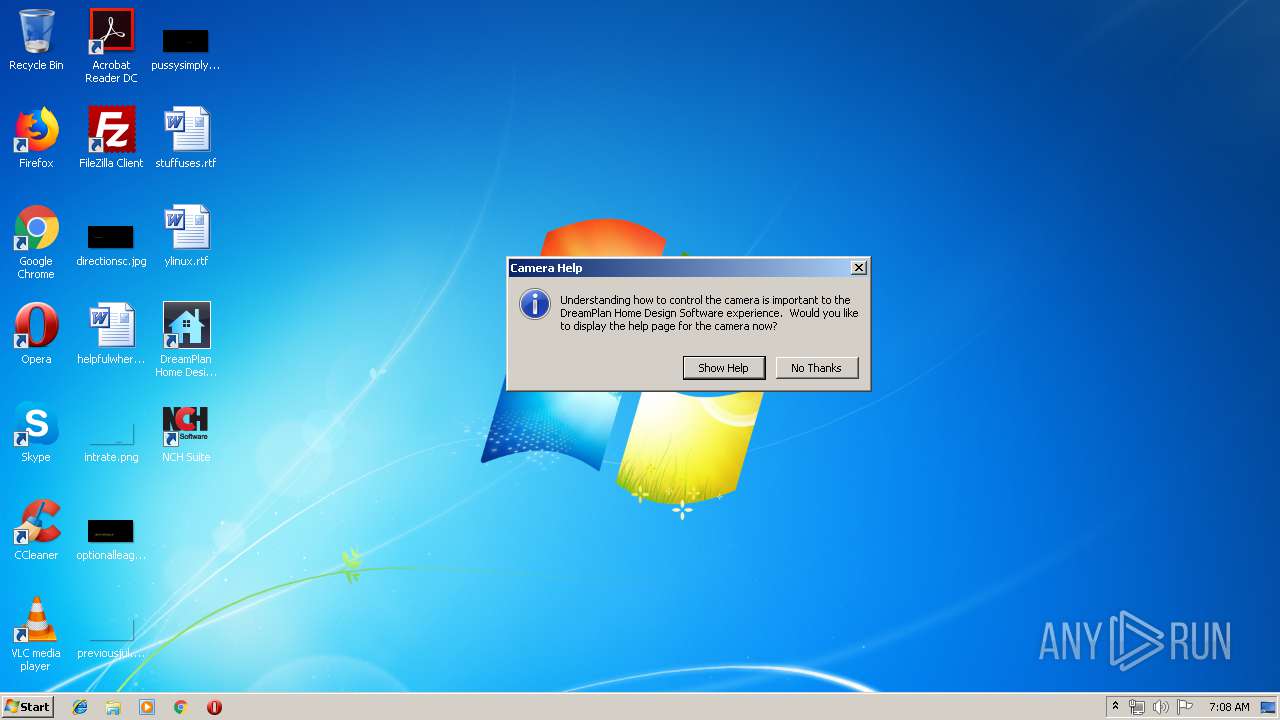
Starts Internet Explorer
- dreamplan.exe (PID: 2748)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2652)
INFO
Application launched itself
- iexplore.exe (PID: 3600)
- chrome.exe (PID: 2652)
Changes internet zones settings
- iexplore.exe (PID: 3600)
Reads settings of System Certificates
- iexplore.exe (PID: 3600)
Creates files in the user directory
- iexplore.exe (PID: 2168)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3680)
Reads internet explorer settings
- iexplore.exe (PID: 2168)
Reads Internet Cache Settings
- iexplore.exe (PID: 2168)
Changes settings of System certificates
- iexplore.exe (PID: 3600)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:12:18 01:47:27+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 1536 |
| InitializedDataSize: | 4144640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11d4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (Australian) |
| CharacterSet: | Unicode |
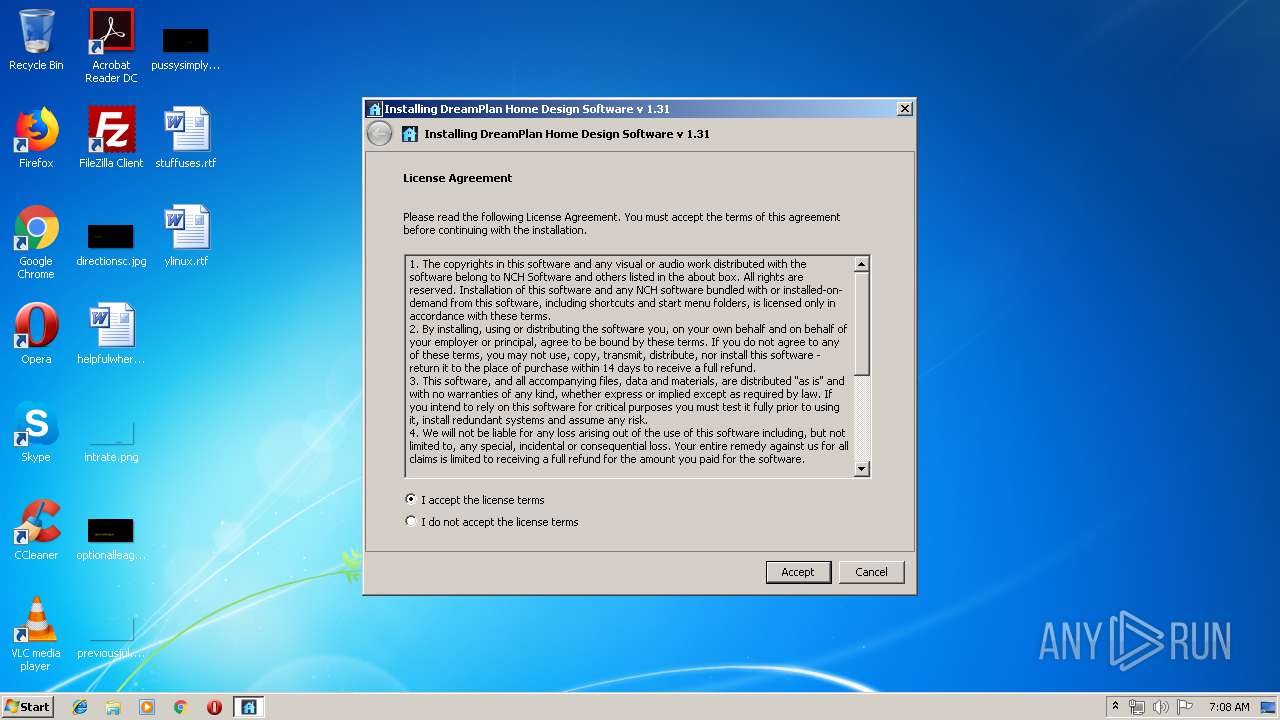
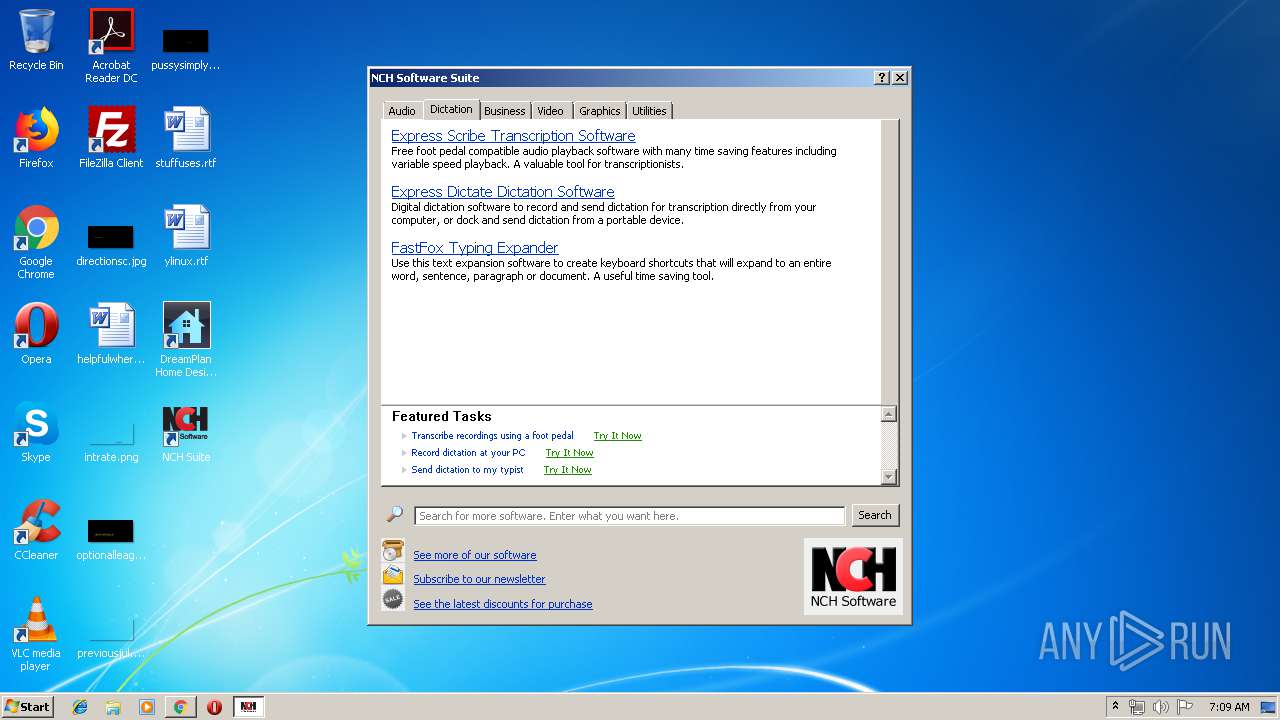
| CompanyName: | NCH Software |
| FileDescription: | DreamPlan Home Design Software |
| FileVersion: | 1.31 |
| ProductVersion: | 1.31 |
| ProductName: | DreamPlan |
| LegalCopyright: | NCH Software |
| InternalName: | DreamPlan |
| OriginalFileName: | DreamPlan.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Dec-2014 00:47:27 |
| Detected languages: |
|
| CompanyName: | NCH Software |
| FileDescription: | DreamPlan Home Design Software |
| FileVersion: | 1.31 |
| ProductVersion: | 1.31 |
| ProductName: | DreamPlan |
| LegalCopyright: | NCH Software |
| InternalName: | DreamPlan |
| OriginalFilename: | DreamPlan.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Dec-2014 00:47:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000058B | 0x00000600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.55311 |
.rdata | 0x00002000 | 0x000008BA | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.86466 |
.data | 0x00003000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0611629 |
.rsrc | 0x00004000 | 0x003F2EC4 | 0x003F3000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99969 |
.reloc | 0x003F7000 | 0x00000124 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.02672 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.0984 | 1050 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.26009 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
95 | 7.99964 | 3667765 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
99 | 7.99943 | 464730 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
Imports
KERNEL32.dll |
SETUPAPI.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
62
Monitored processes
27
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2292 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,10471421602987816216,9195365636733696653,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11726258901282103827 --mojo-platform-channel-handle=3296 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,10471421602987816216,9195365636733696653,131072 --enable-features=PasswordImport --service-pipe-token=18273682474355044070 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18273682474355044070 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2316 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,10471421602987816216,9195365636733696653,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2492864280029478442 --mojo-platform-channel-handle=1520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f390f18,0x6f390f28,0x6f390f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,10471421602987816216,9195365636733696653,131072 --enable-features=PasswordImport --service-pipe-token=14287177073372191272 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14287177073372191272 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\NCH Software\DreamPlan\infozip3.exe" -LQUIET -instby fiDreamPlan | C:\Program Files\NCH Software\DreamPlan\infozip3.exe | nchsetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,10471421602987816216,9195365636733696653,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9818927836897056484 --mojo-platform-channel-handle=3080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3600 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2412 | "C:\Users\admin\AppData\Local\Temp\thhjgjk.exe" | C:\Users\admin\AppData\Local\Temp\thhjgjk.exe | explorer.exe | ||||||||||||
User: admin Company: NCH Software Integrity Level: HIGH Description: DreamPlan Home Design Software Exit code: 0 Version: 1.31 Modules
| |||||||||||||||
Total events
1 442
Read events
1 012
Write events
422
Delete events
8
Modification events
| (PID) Process: | (2412) thhjgjk.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2412) thhjgjk.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3888) nchsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: nchsetup.exe | |||
| (PID) Process: | (3888) nchsetup.exe | Key: | HKEY_CURRENT_USER\Software\NCH Software\DreamPlan\Settings |
| Operation: | write | Name: | InstalledByAdmin |
Value: 1 | |||
| (PID) Process: | (1912) infozip3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\NCH Software\Components\infozip3 |
| Operation: | write | Name: | Path |
Value: C:\Program Files\NCH Software\Components\infozip3\unzip32.dll | |||
| (PID) Process: | (1912) infozip3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\NCH Software\Components\infozip3 |
| Operation: | write | Name: | Version |
Value: 1.01 | |||
| (PID) Process: | (1912) infozip3.exe | Key: | HKEY_CURRENT_USER\Software\NCH Software\Components\infozip3 |
| Operation: | write | Name: | Path |
Value: C:\Program Files\NCH Software\Components\infozip3\unzip32.dll | |||
| (PID) Process: | (1912) infozip3.exe | Key: | HKEY_CURRENT_USER\Software\NCH Software\Components\infozip3 |
| Operation: | write | Name: | Version |
Value: 1.01 | |||
| (PID) Process: | (1912) infozip3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\NCH Swift Sound\Components\infozip3 |
| Operation: | write | Name: | Path |
Value: C:\Program Files\NCH Software\Components\infozip3\unzip32.dll | |||
| (PID) Process: | (1912) infozip3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\NCH Swift Sound\Components\infozip3 |
| Operation: | write | Name: | Version |
Value: 1.01 | |||
Executable files
8
Suspicious files
115
Text files
284
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2412 | thhjgjk.exe | C:\Users\admin\AppData\Local\Temp\n1s\nchsetup.cab | — | |
MD5:— | SHA256:— | |||
| 2412 | thhjgjk.exe | C:\Users\admin\AppData\Local\Temp\n1s\nchdata.cab | — | |
MD5:— | SHA256:— | |||
| 2412 | thhjgjk.exe | C:\Users\admin\AppData\Local\Temp\n1s\nchdata.dat | — | |
MD5:— | SHA256:— | |||
| 3888 | nchsetup.exe | C:\Program Files\NCH Software\DreamPlan\dreamplan.exe | executable | |
MD5:— | SHA256:— | |||
| 3888 | nchsetup.exe | C:\ProgramData\NCH Software\DreamPlan\engine\skydome-cloud-few-early.jpg | image | |
MD5:— | SHA256:— | |||
| 3888 | nchsetup.exe | C:\ProgramData\NCH Software\DreamPlan\engine\camera-controls-bkg.png | image | |
MD5:— | SHA256:— | |||
| 2412 | thhjgjk.exe | C:\Users\admin\AppData\Local\Temp\n1s\nchsetup.exe | executable | |
MD5:— | SHA256:— | |||
| 3888 | nchsetup.exe | C:\ProgramData\NCH Software\DreamPlan\engine\down_active.png | image | |
MD5:— | SHA256:— | |||
| 3888 | nchsetup.exe | C:\ProgramData\NCH Software\DreamPlan\engine\elevation-down.png | image | |
MD5:— | SHA256:— | |||
| 3888 | nchsetup.exe | C:\ProgramData\NCH Software\DreamPlan\engine\SkyDome2.3dn | binary | |
MD5:75B9B6AD4EF8783F040C88F5B9B3ACD8 | SHA256:3B622AFDDF3DD817102E8FBB5D24EE10B3548B2CC5E19F724DD89B150F24B901 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
65
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
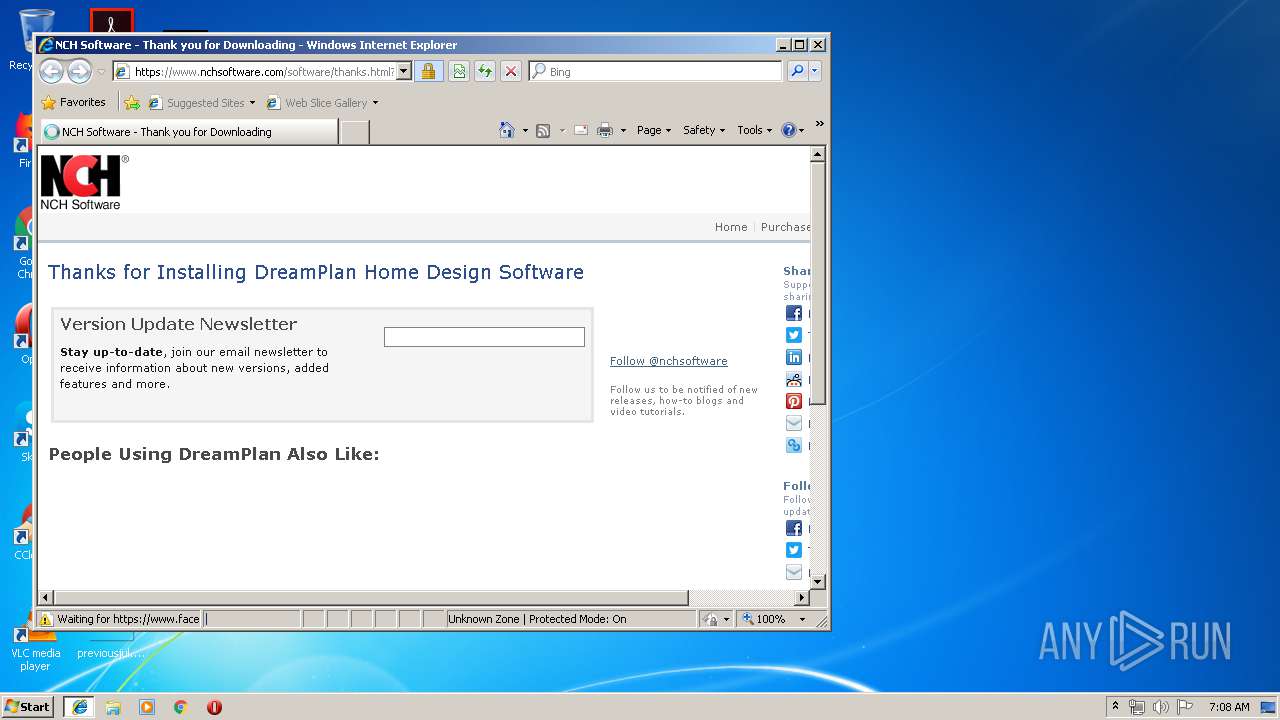
2168 | iexplore.exe | GET | 301 | 66.117.15.144:80 | http://www.nchsoftware.com/software/thanks.html?software=DreamPlan&appname=DreamPlan%20Home%20Design%20Software&version=1.31&base=design&domain=nchsoftware&svar=LLIBShowSuiteButtonOff&usage=046103&antivirus=expired&instby=dl | US | html | 471 b | malicious |
2168 | iexplore.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
3600 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1528 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
1528 | chrome.exe | GET | 200 | 217.146.165.206:80 | http://r3---sn-oun-1gie.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=136.0.0.156&mm=28&mn=sn-oun-1gie&ms=nvh&mt=1555308048&mv=u&pl=25&shardbypass=yes | CH | crx | 842 Kb | whitelisted |
2168 | iexplore.exe | GET | 200 | 52.222.146.197:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3600 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2168 | iexplore.exe | 66.117.15.144:80 | www.nchsoftware.com | InMotion Hosting, Inc. | US | suspicious |
2168 | iexplore.exe | 66.117.15.144:443 | www.nchsoftware.com | InMotion Hosting, Inc. | US | suspicious |
2168 | iexplore.exe | 172.217.23.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2168 | iexplore.exe | 31.13.90.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
2168 | iexplore.exe | 172.217.23.130:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
2168 | iexplore.exe | 151.101.2.2:443 | trc.taboola.com | Fastly | US | shared |
2168 | iexplore.exe | 34.248.190.7:443 | trends.revcontent.com | Amazon.com, Inc. | IE | unknown |
2168 | iexplore.exe | 192.249.118.22:443 | secure.nch.com.au | InMotion Hosting, Inc. | US | suspicious |
2168 | iexplore.exe | 185.60.216.19:443 | static.xx.fbcdn.net | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.nchsoftware.com |
| malicious |
www.facebook.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
secure.nch.com.au |
| suspicious |
bat.bing.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
trc.taboola.com |
| whitelisted |
q.quora.com |
| whitelisted |