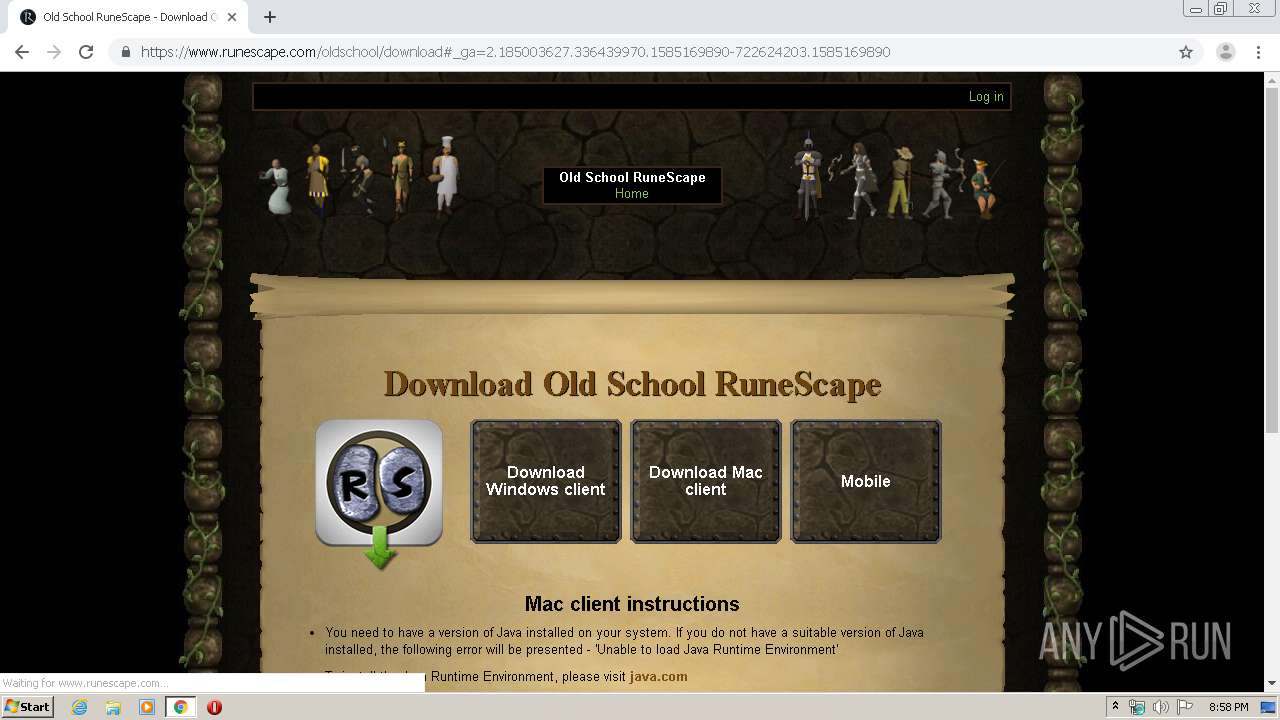
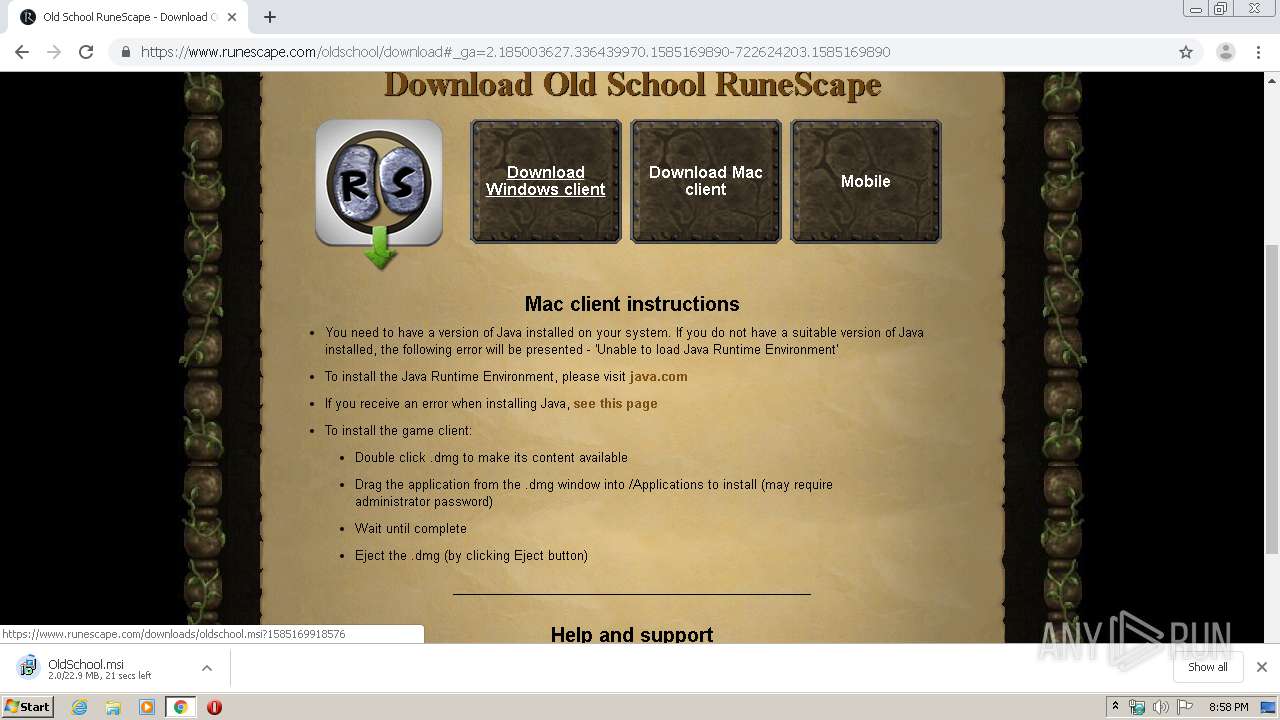
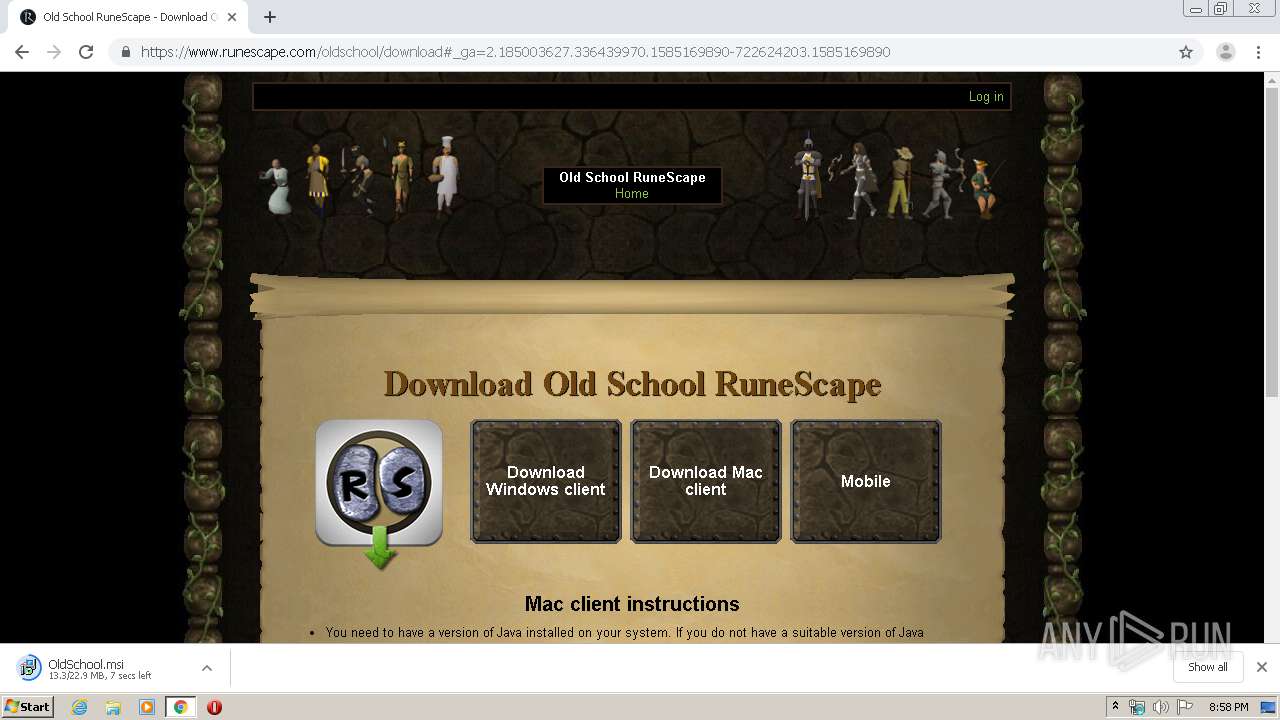
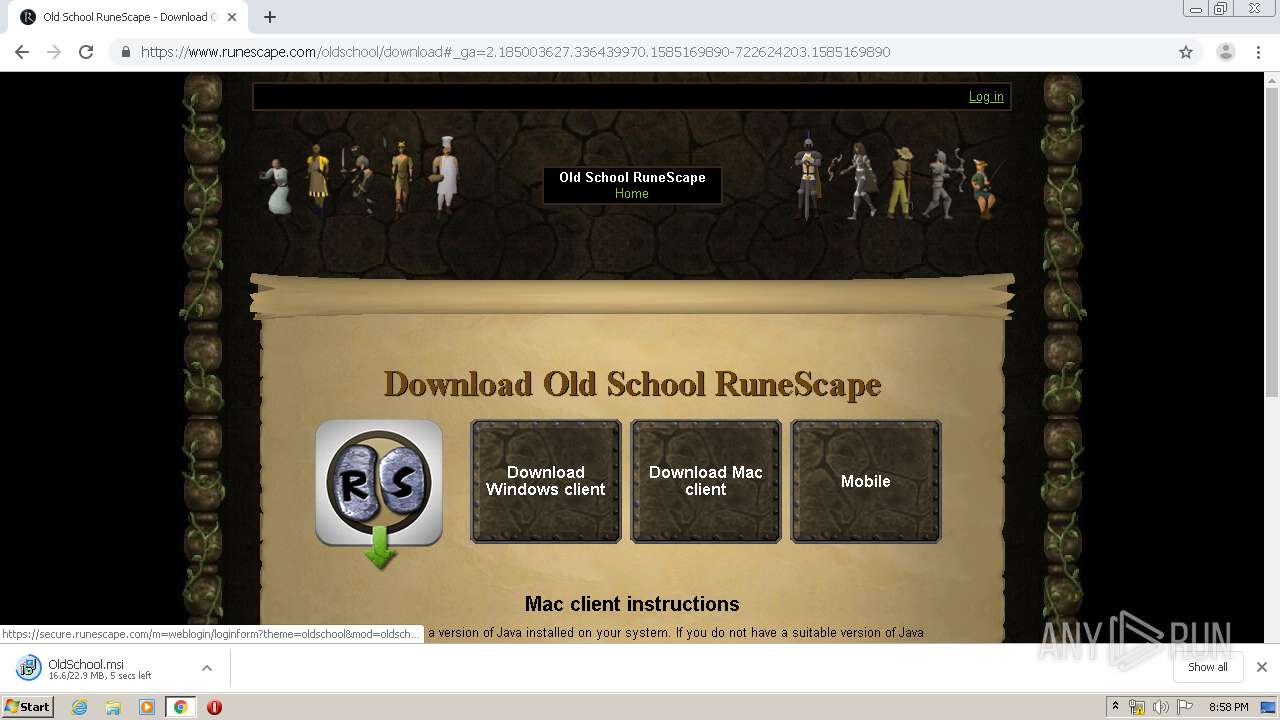
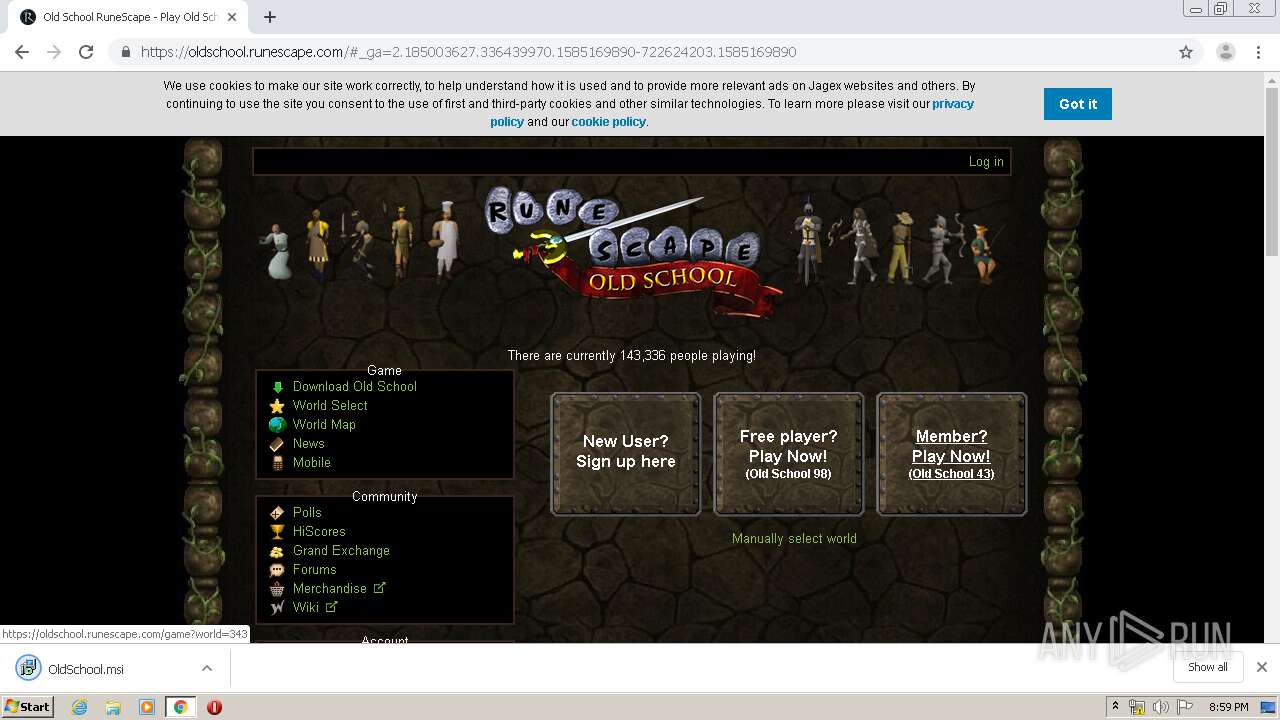
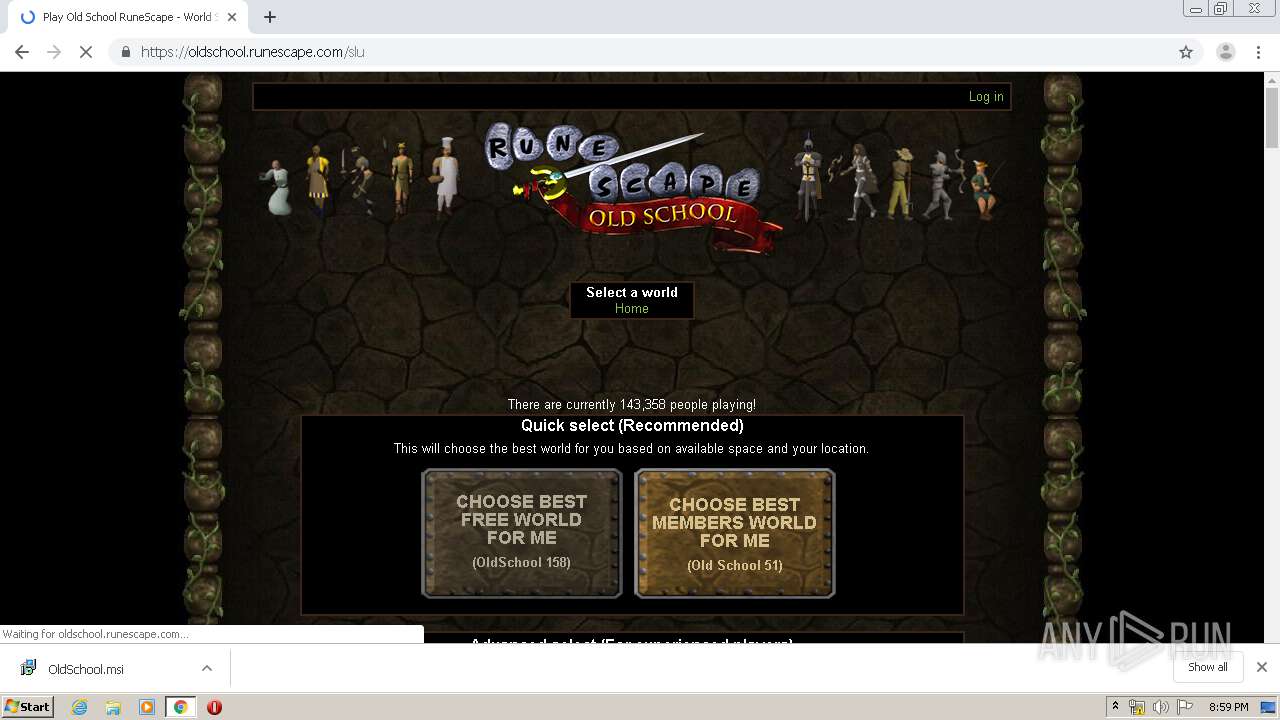
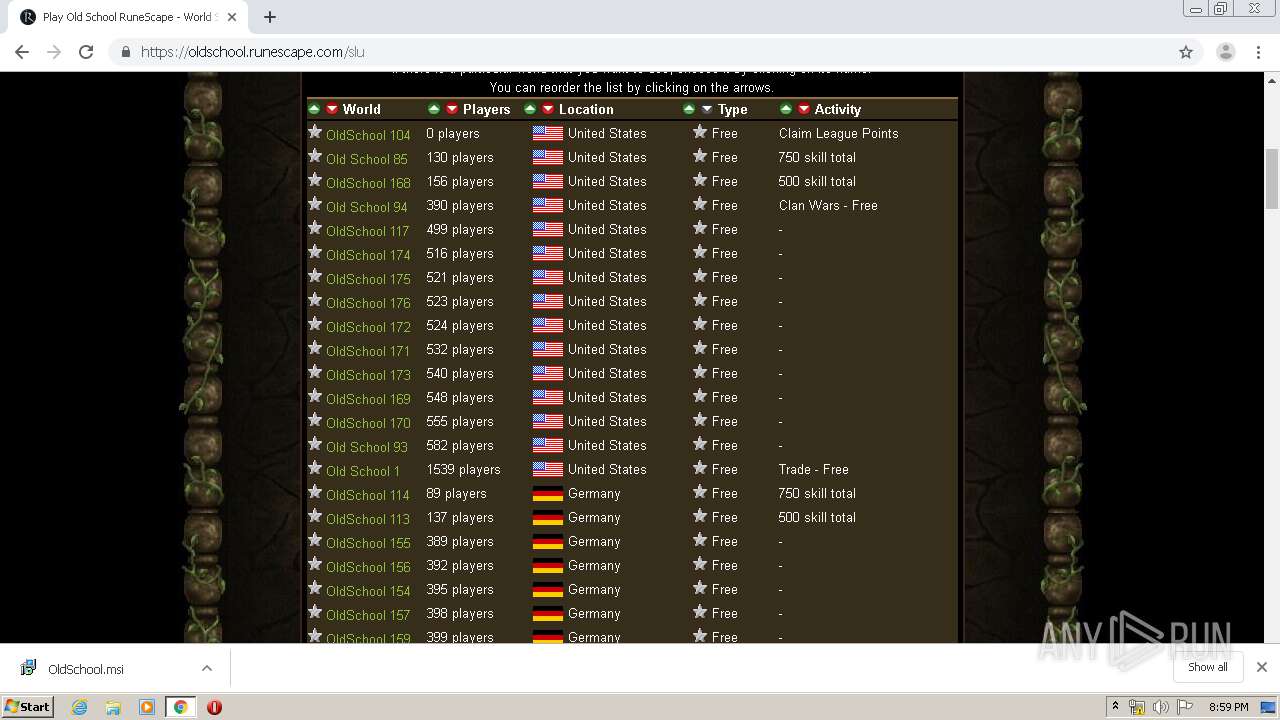
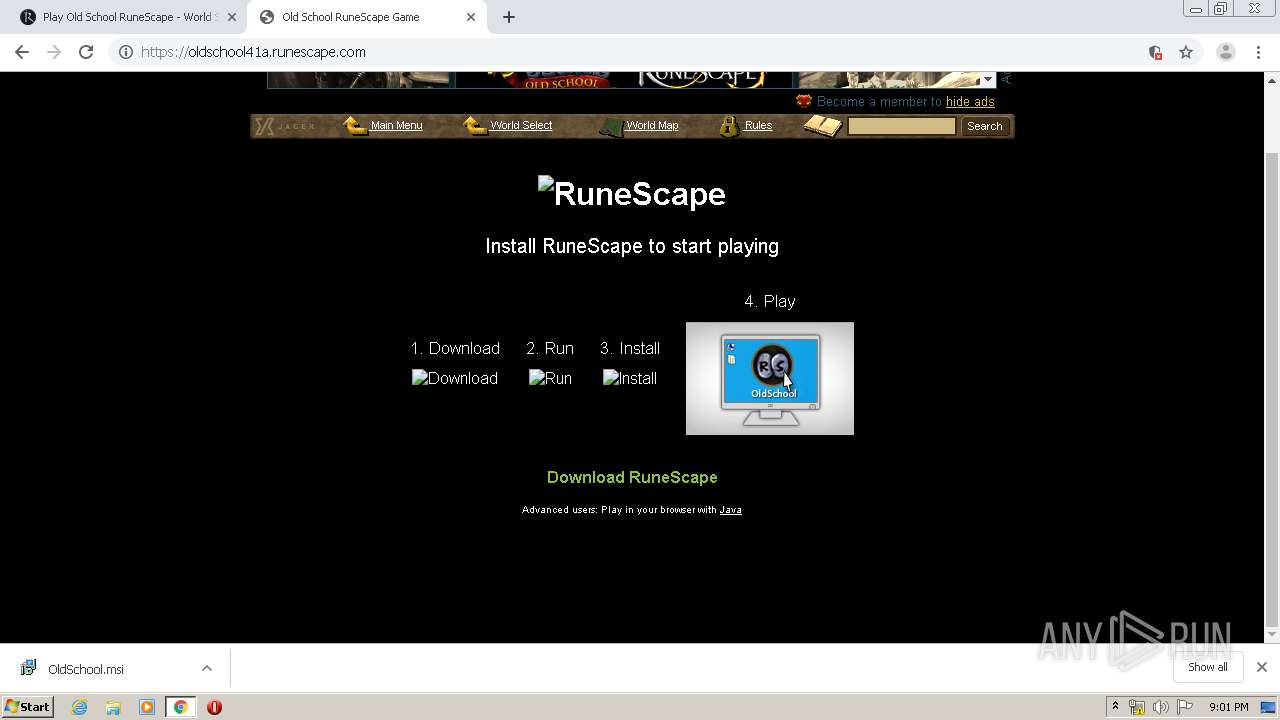
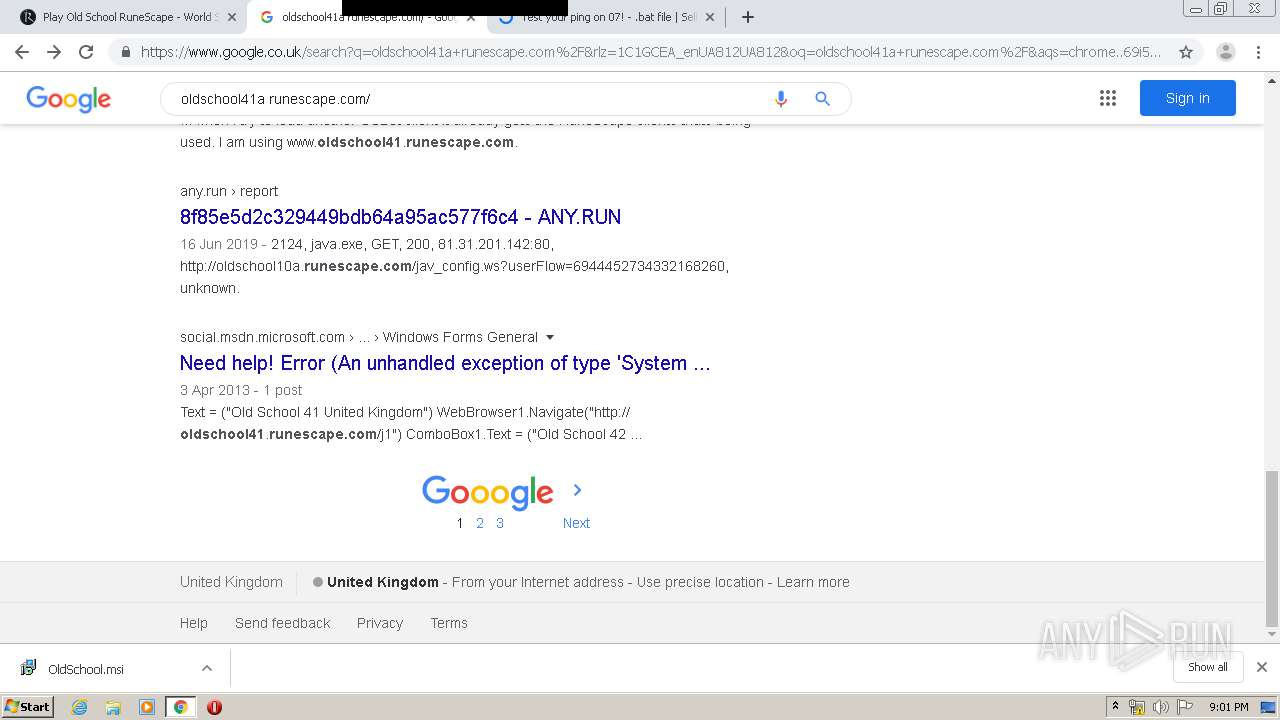
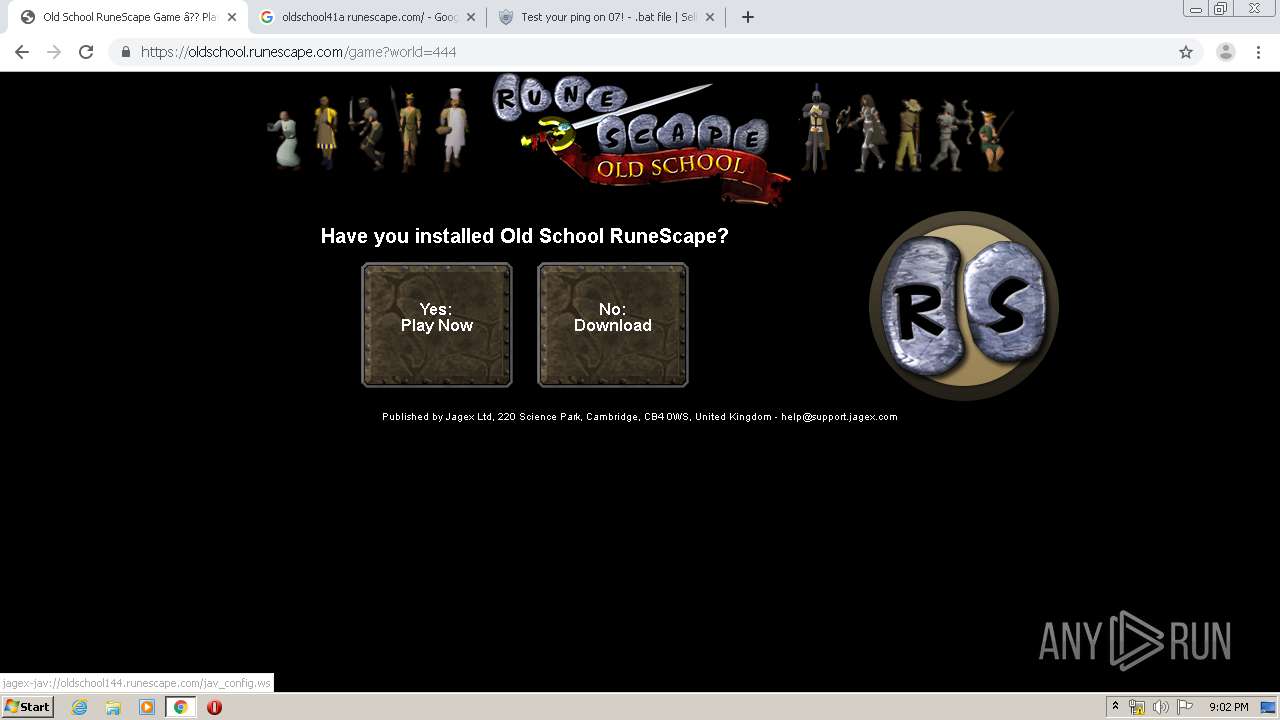
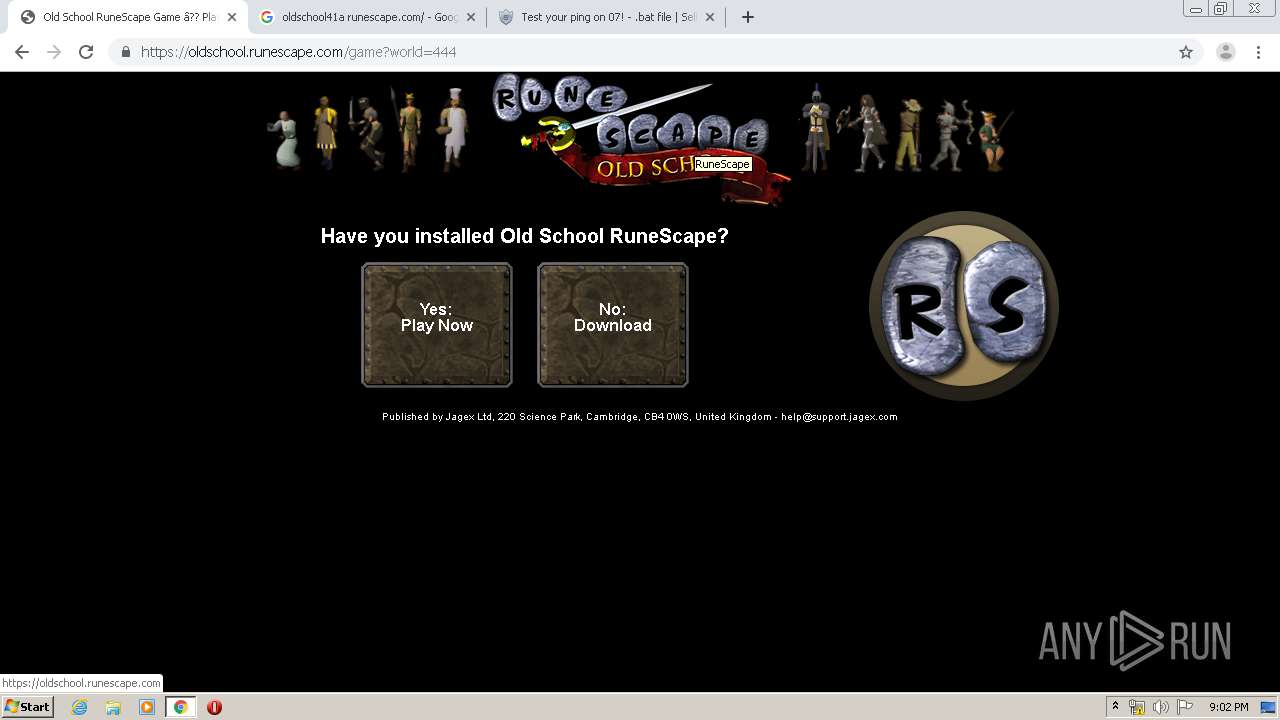
| URL: | http://runescape.com |
| Full analysis: | https://app.any.run/tasks/d50d3c14-e80e-439d-a995-6dcf8c58e1b4 |
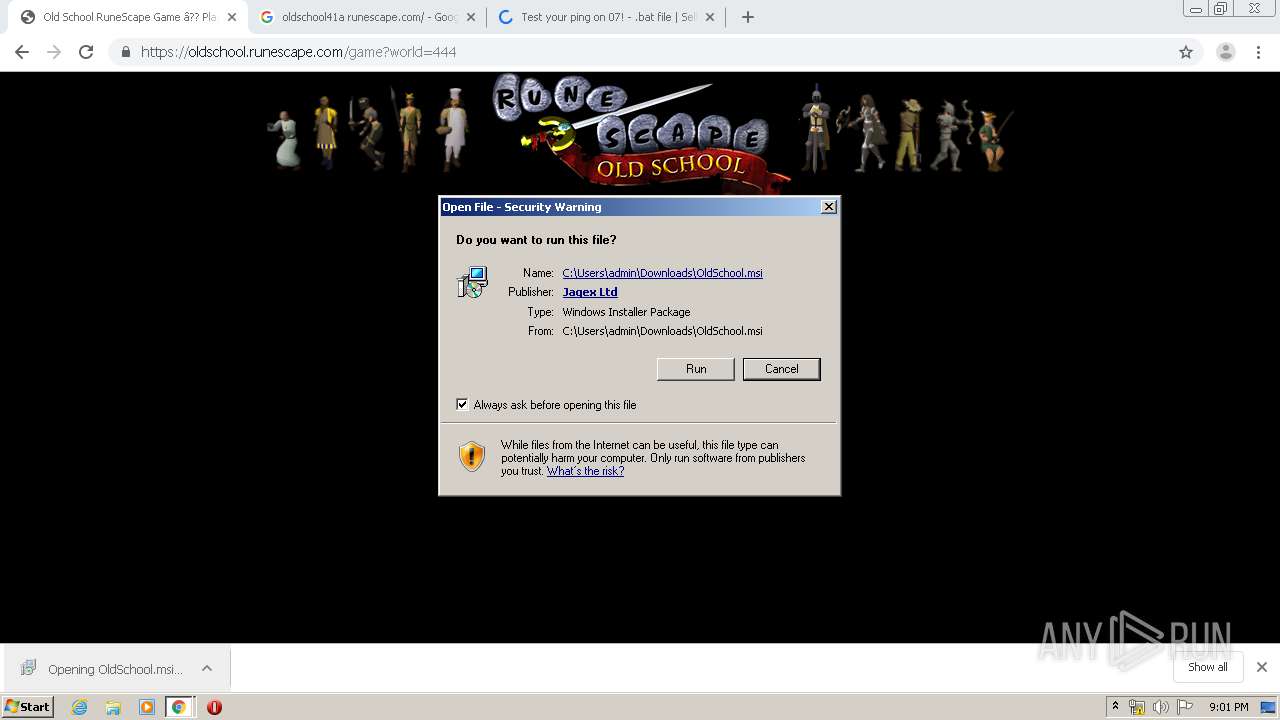
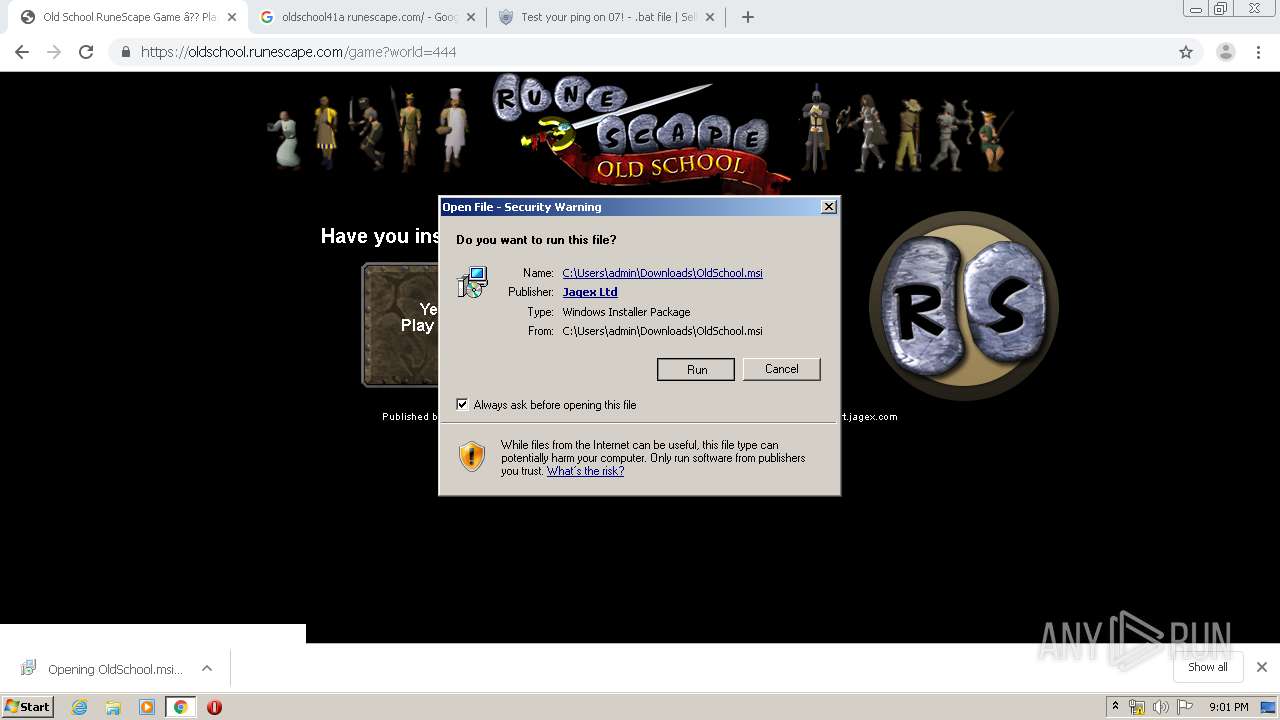
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2020, 20:57:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C26FD82BDE2FA55BABD518C850DE4AA2 |
| SHA1: | CDB1CA24852DE30565B2F5CAA1A6D13BC51F9F51 |
| SHA256: | 6CB15724C51656D8C741BD8FA370A6B69258215D81062AD204B4D5EF535C7B3B |
| SSDEEP: | 3:N1KMfywK:CMjK |
MALICIOUS
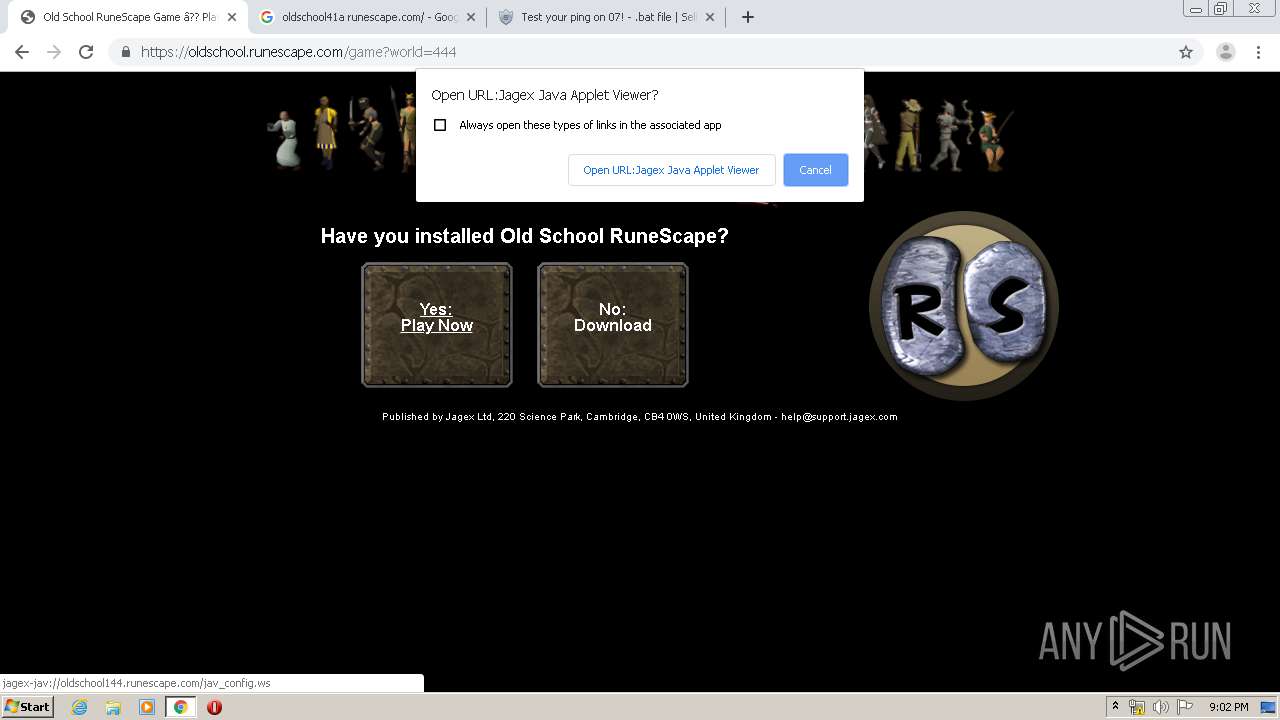
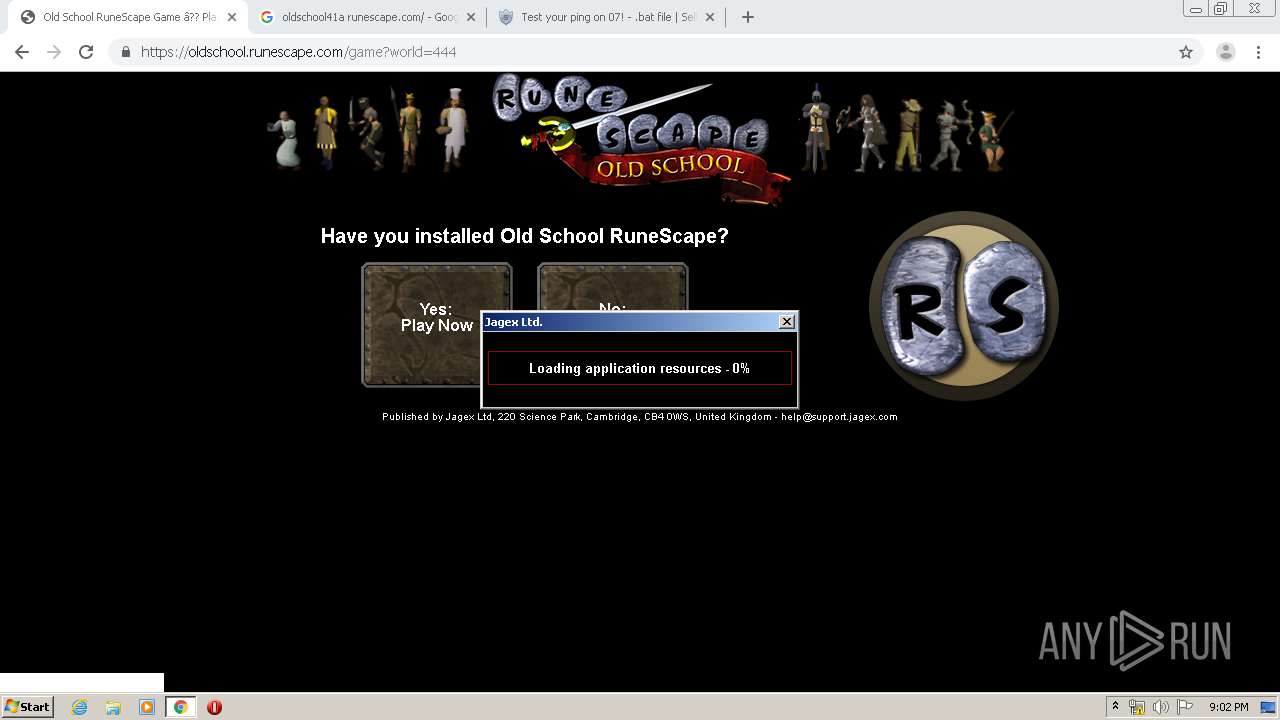
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3024)
- JagexLauncher.exe (PID: 1728)
Application was dropped or rewritten from another process
- JagexLauncher.exe (PID: 1728)
SUSPICIOUS
Creates files in the user directory
- msiexec.exe (PID: 4012)
Changes IE settings (feature browser emulation)
- msiexec.exe (PID: 4012)
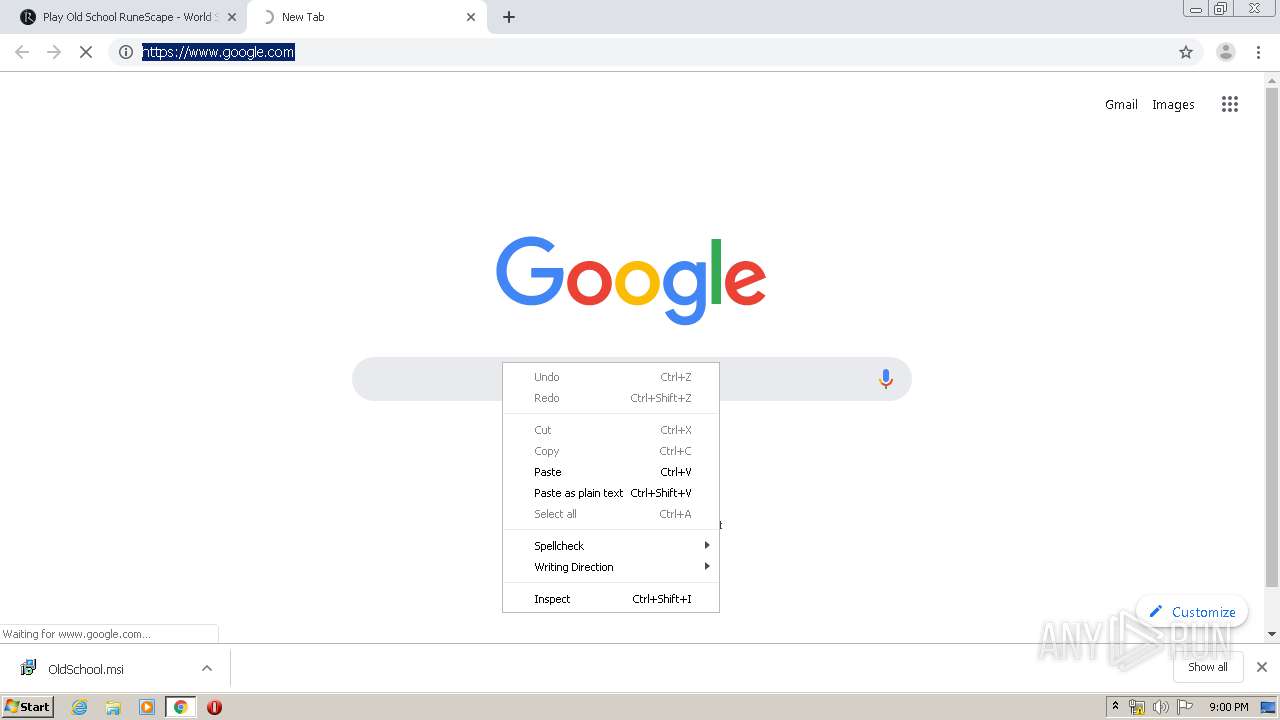
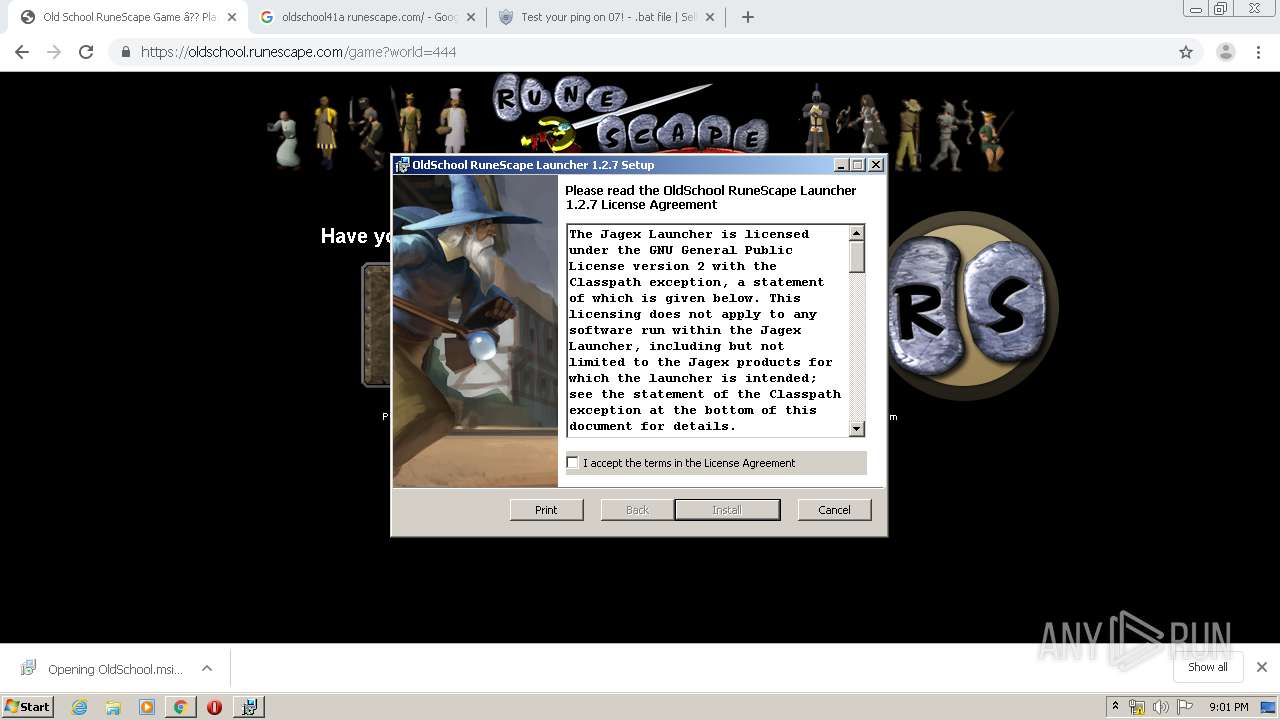
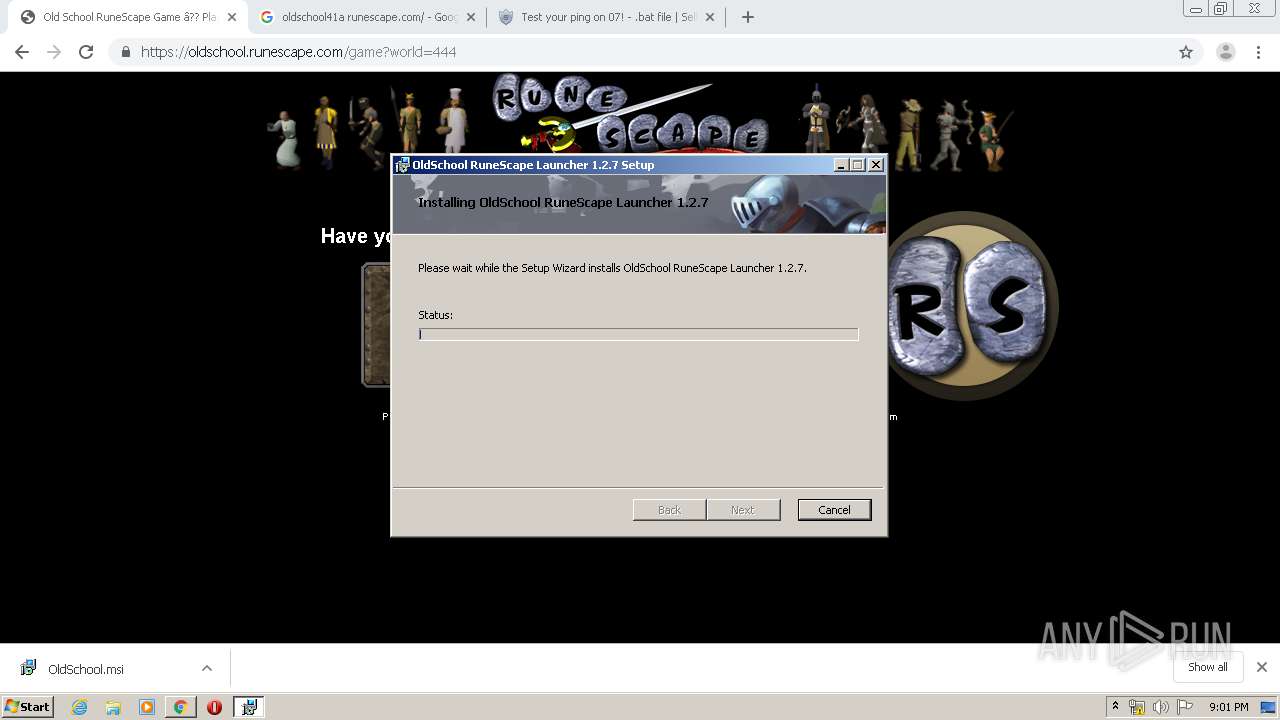
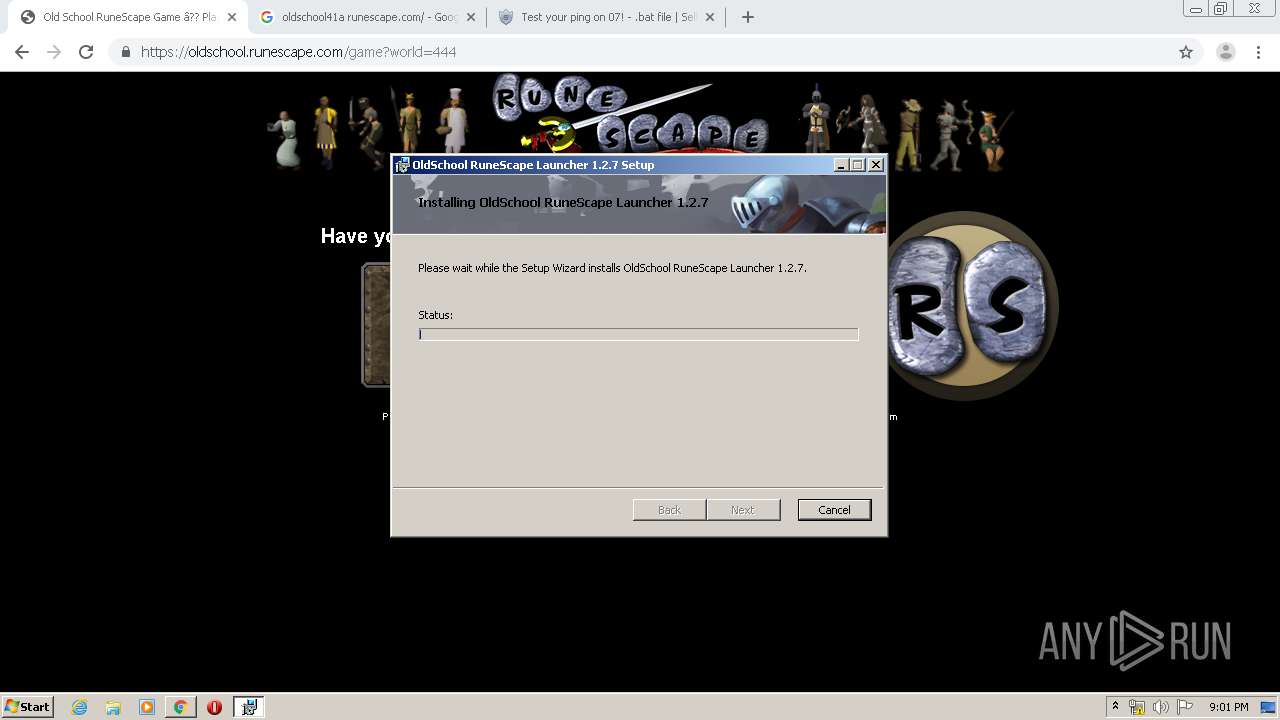
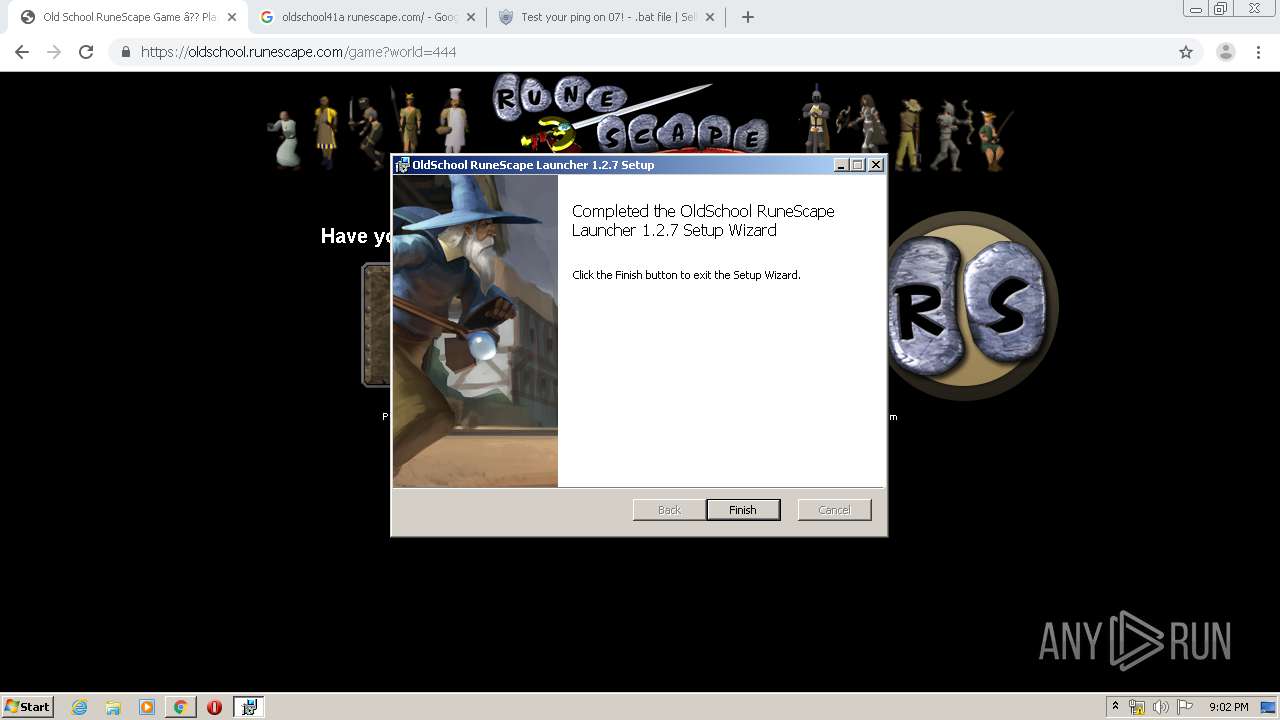
Starts Microsoft Installer
- chrome.exe (PID: 3020)
Modifies the open verb of a shell class
- msiexec.exe (PID: 4012)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3020)
Executed as Windows Service
- vssvc.exe (PID: 1228)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4012)
- JagexLauncher.exe (PID: 1728)
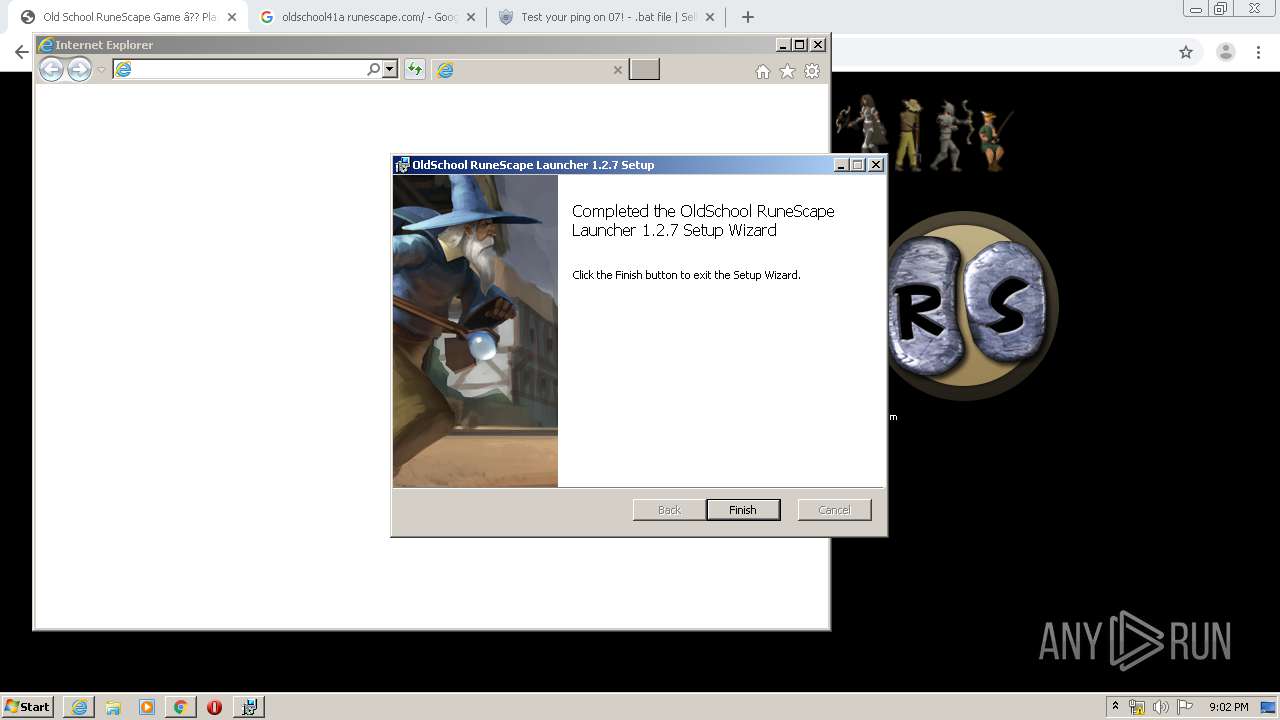
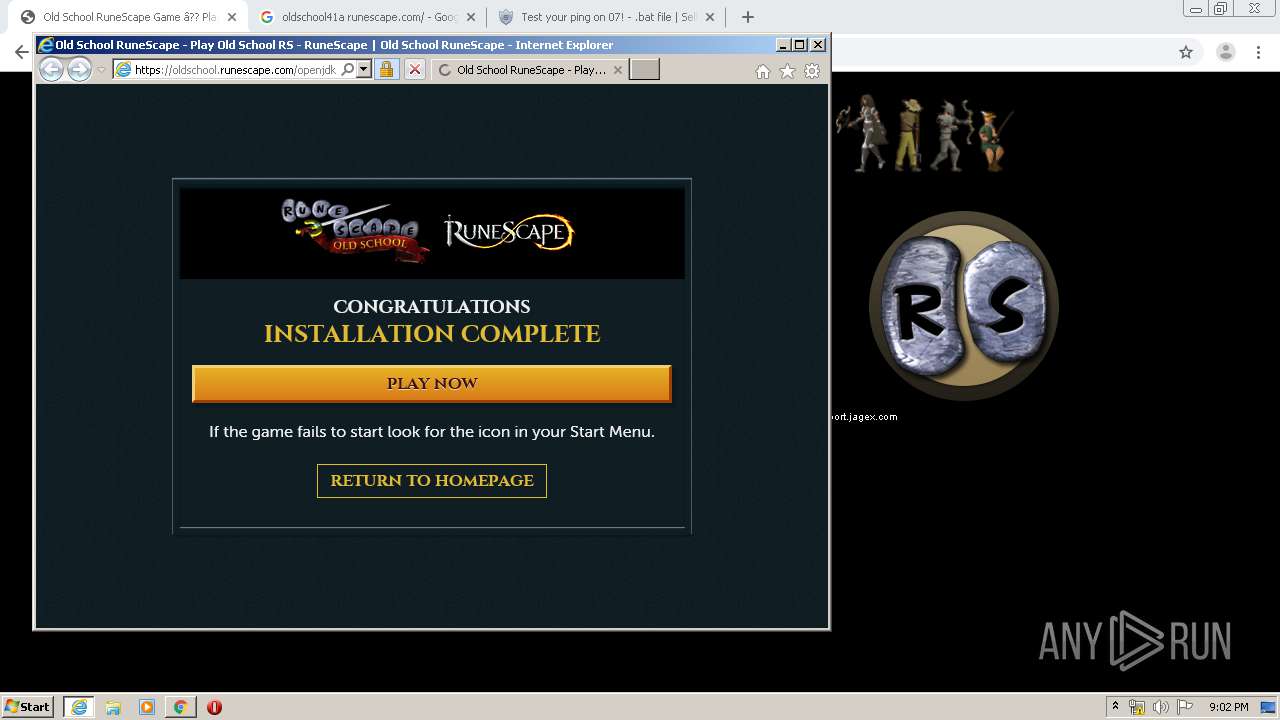
Starts Internet Explorer
- MsiExec.exe (PID: 1332)
Connects to unusual port
- JagexLauncher.exe (PID: 1728)
INFO
Reads the hosts file
- chrome.exe (PID: 3020)
- chrome.exe (PID: 3248)
Reads Internet Cache Settings
- chrome.exe (PID: 3020)
- iexplore.exe (PID: 1024)
- iexplore.exe (PID: 772)
Application launched itself
- msiexec.exe (PID: 4012)
- chrome.exe (PID: 3020)
- iexplore.exe (PID: 1024)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1332)
Reads settings of System Certificates
- chrome.exe (PID: 3020)
- iexplore.exe (PID: 1024)
Searches for installed software
- msiexec.exe (PID: 4012)
Creates a software uninstall entry
- msiexec.exe (PID: 4012)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1228)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 4012)
Changes internet zones settings
- iexplore.exe (PID: 1024)
Creates files in the user directory
- iexplore.exe (PID: 772)
Reads internet explorer settings
- iexplore.exe (PID: 772)
Changes settings of System certificates
- iexplore.exe (PID: 1024)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
92
Monitored processes
52
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4462244359067420756,13169150180599068469,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13944095051195601905 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1656 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4462244359067420756,13169150180599068469,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11481294840516292925 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4462244359067420756,13169150180599068469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5689702247258875046 --mojo-platform-channel-handle=4324 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4462244359067420756,13169150180599068469,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13334821889664963713 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3820 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1024 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4462244359067420756,13169150180599068469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4931921612350623342 --mojo-platform-channel-handle=3544 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4462244359067420756,13169150180599068469,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11853173003949444041 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4462244359067420756,13169150180599068469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12972704107872449230 --mojo-platform-channel-handle=4380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
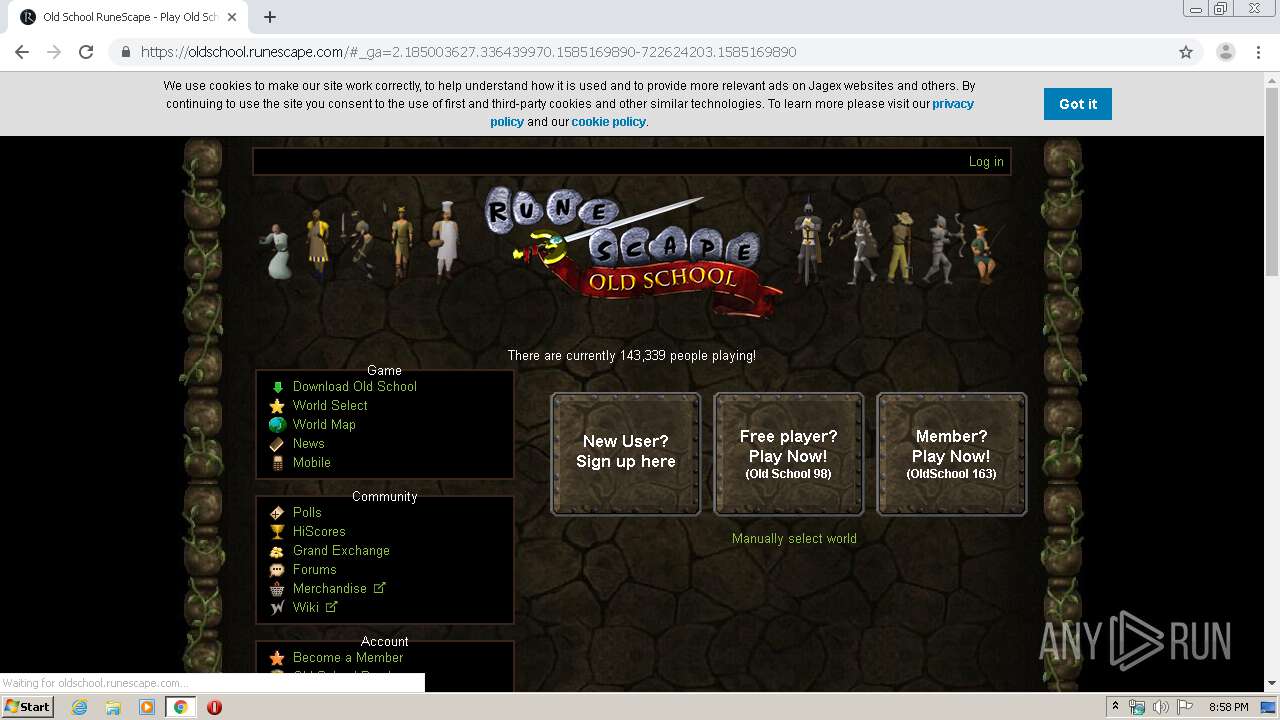
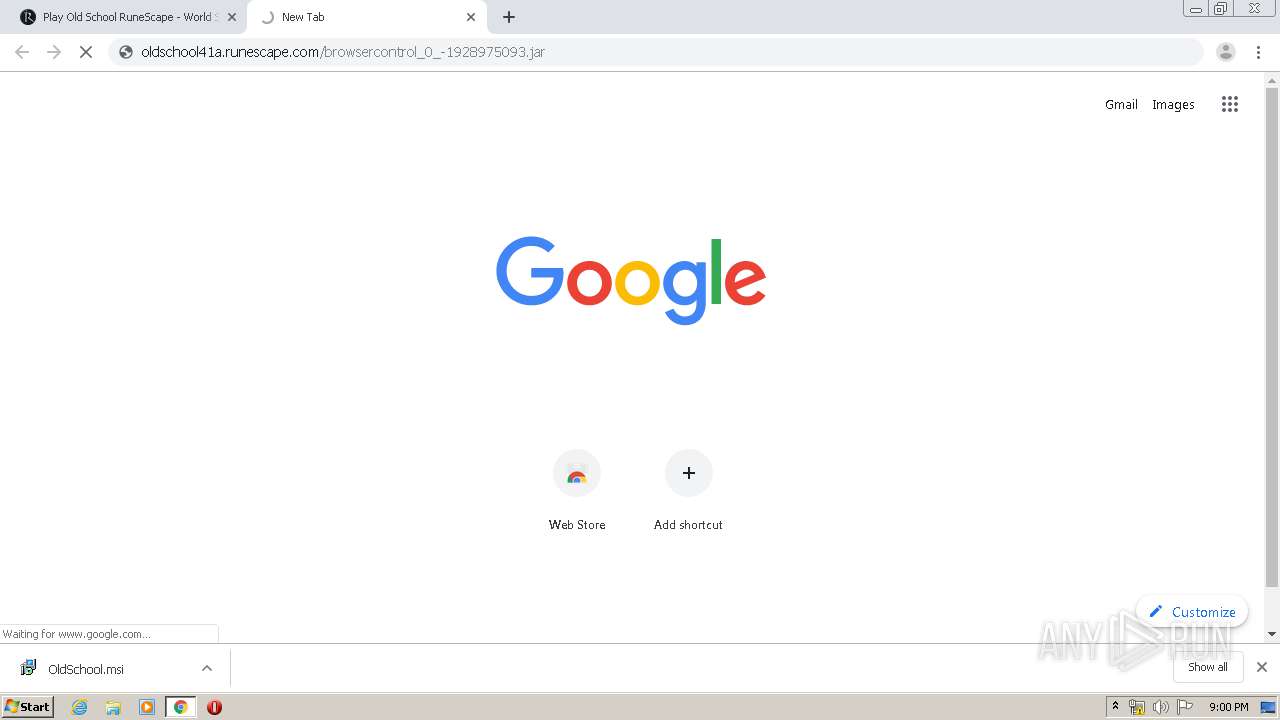
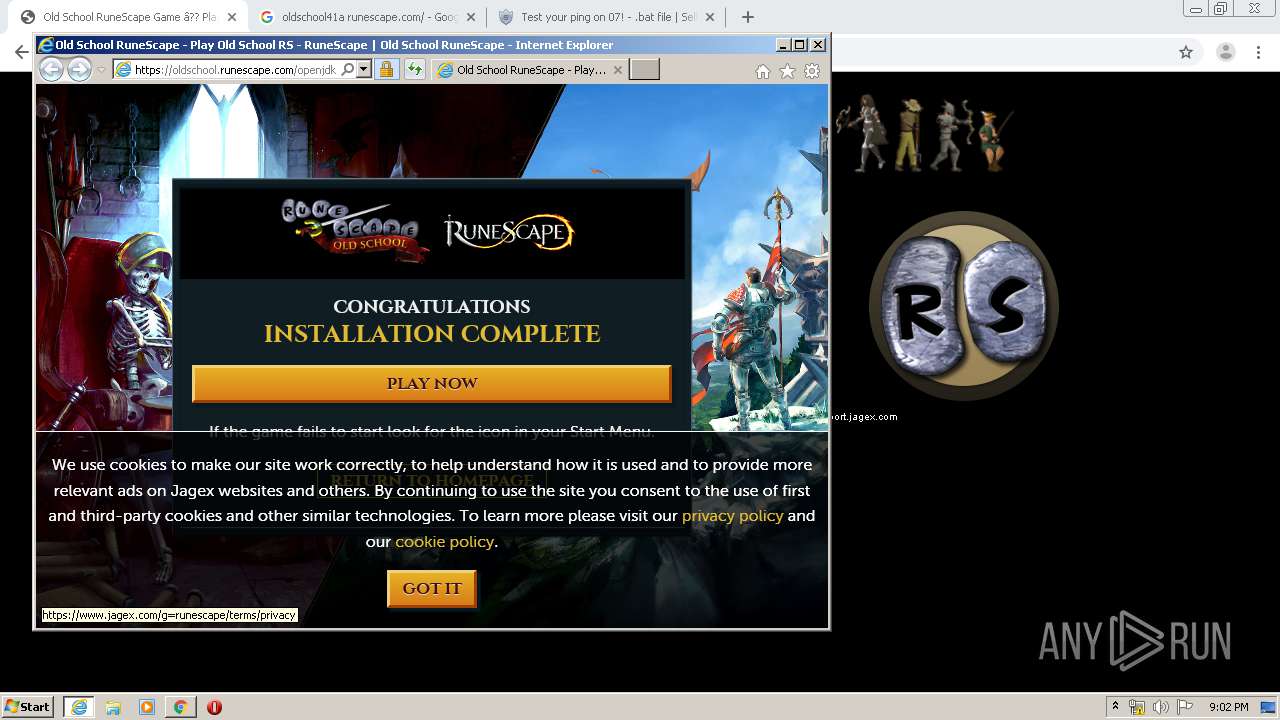
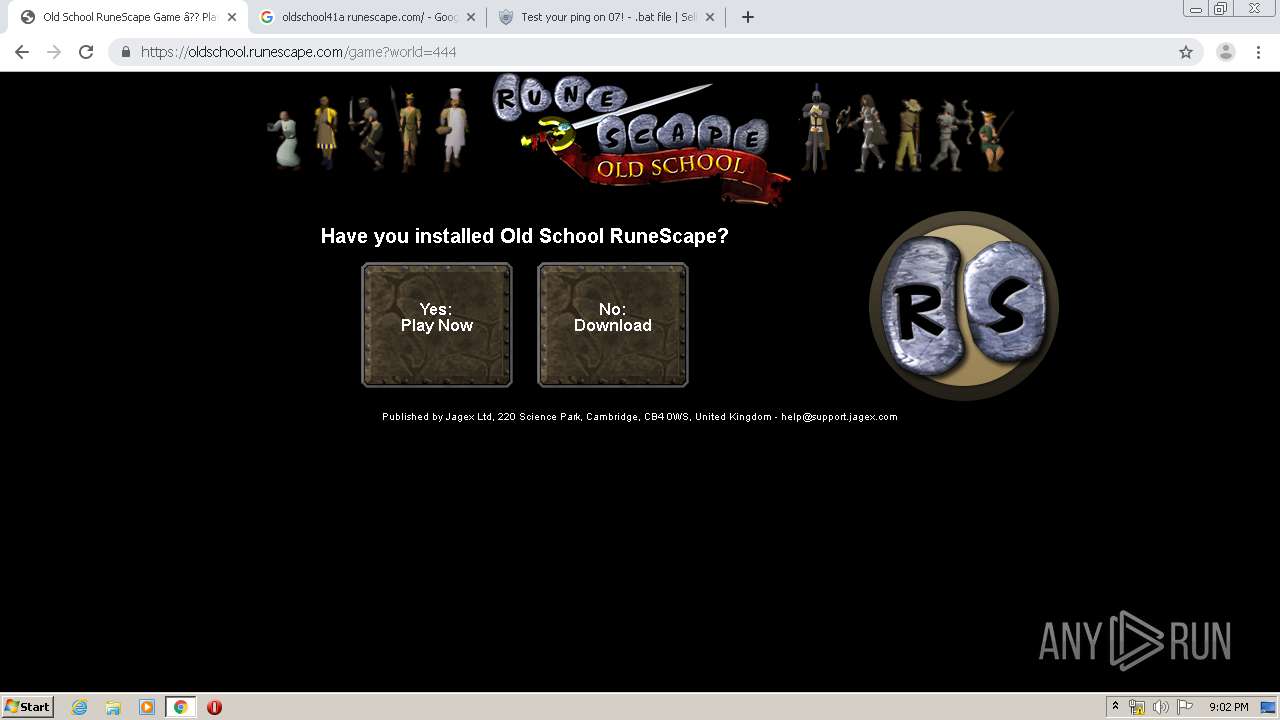
| 1024 | "C:\Program Files\Internet Explorer\iexplore.exe" http://oldschool.runescape.com/openjdk_install.ws | C:\Program Files\Internet Explorer\iexplore.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
8 771
Read events
2 658
Write events
4 375
Delete events
1 738
Modification events
| (PID) Process: | (660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3020-13229643478109000 |
Value: 259 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3020-13229643478109000 |
Value: 259 | |||
Executable files
23
Suspicious files
671
Text files
467
Unknown types
69
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E7BC5D6-BCC.pma | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3ca463e9-34e6-48b6-a369-ae7ab60e01a4.tmp | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66c01.TMP | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFa66cdb.TMP | text | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66d68.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
207
DNS requests
125
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
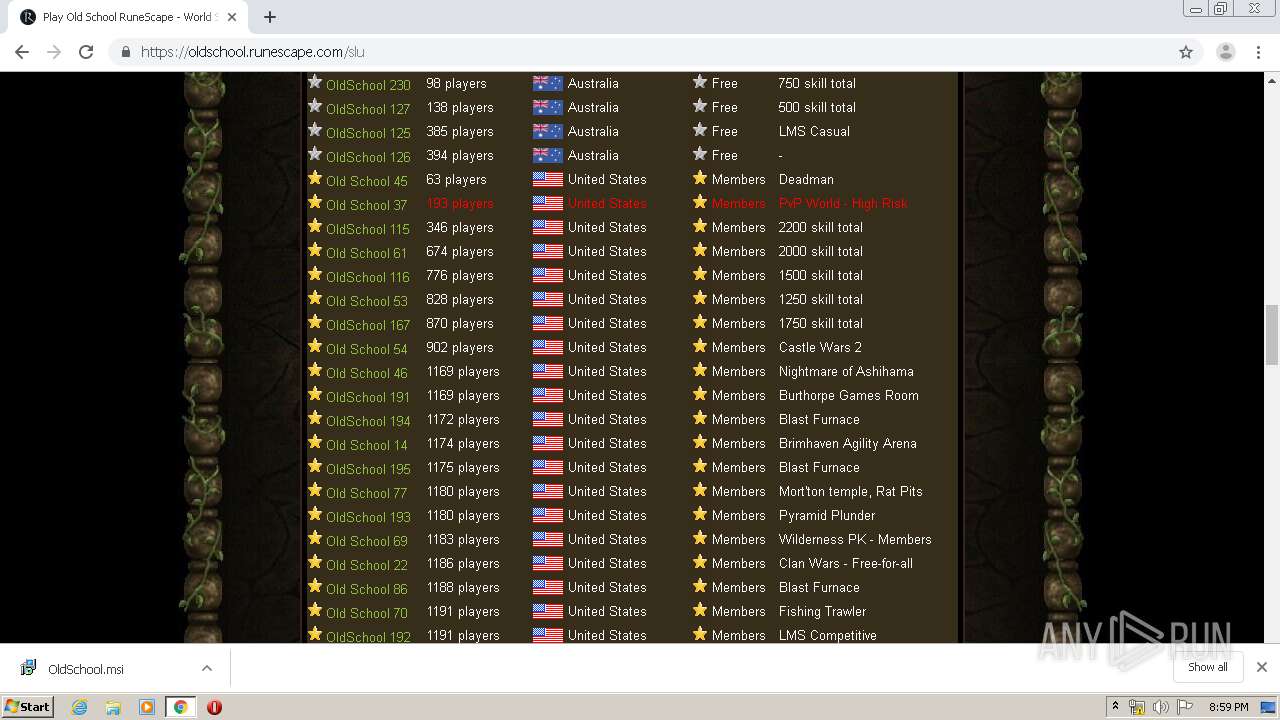
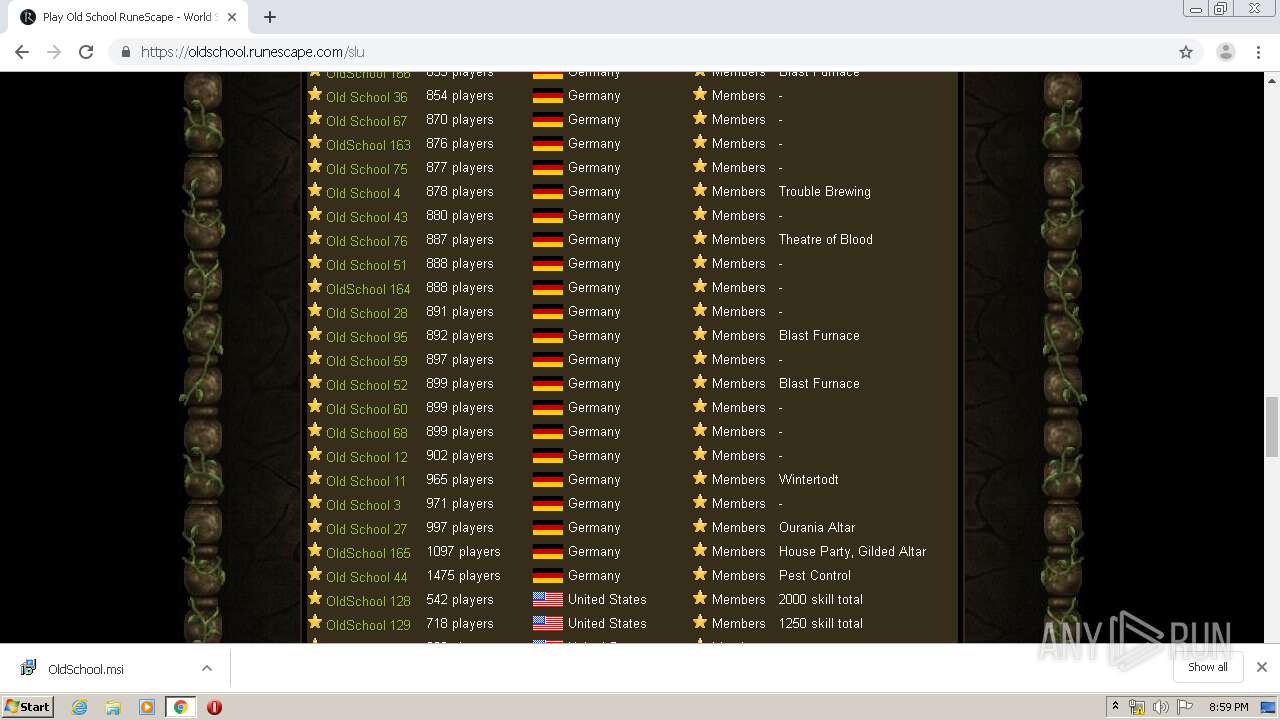
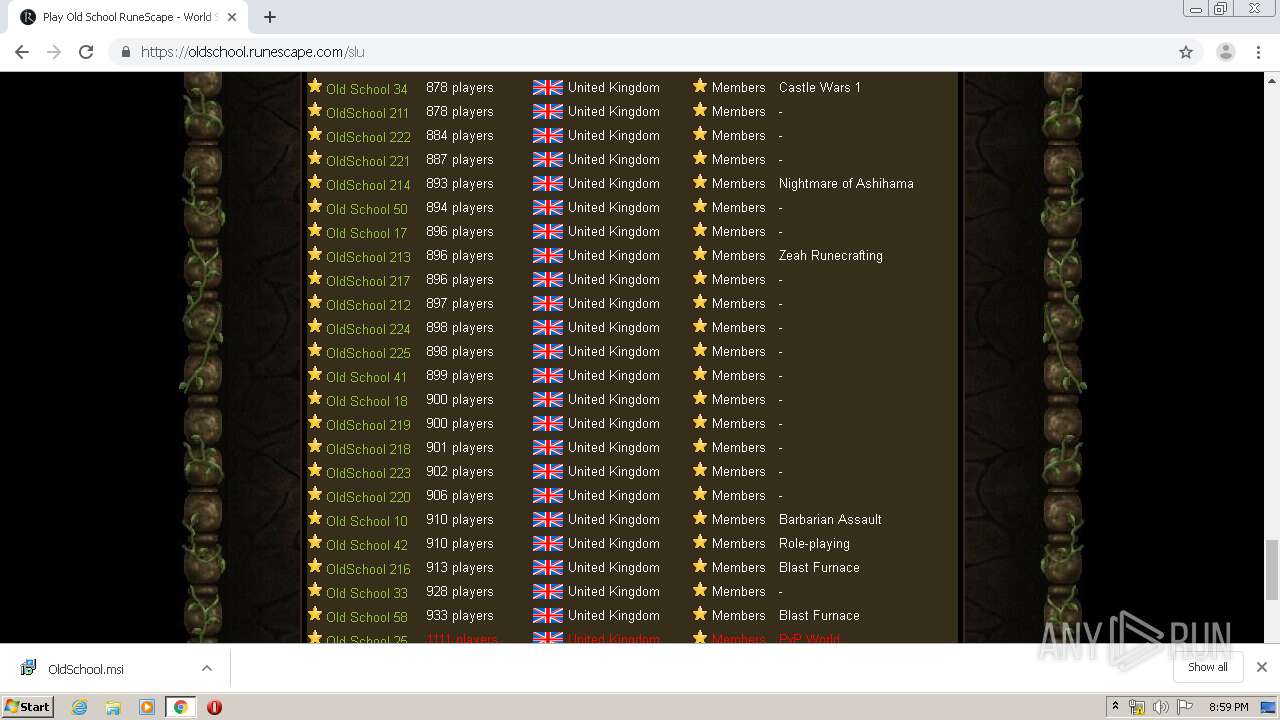
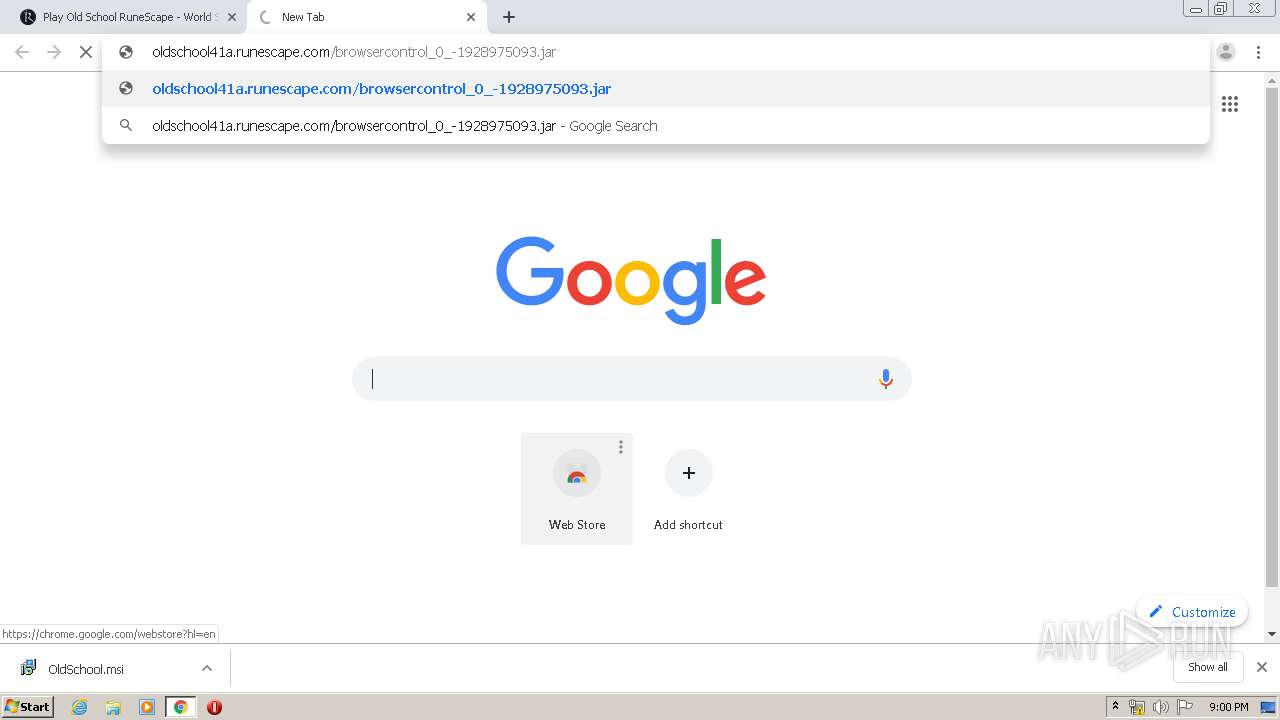
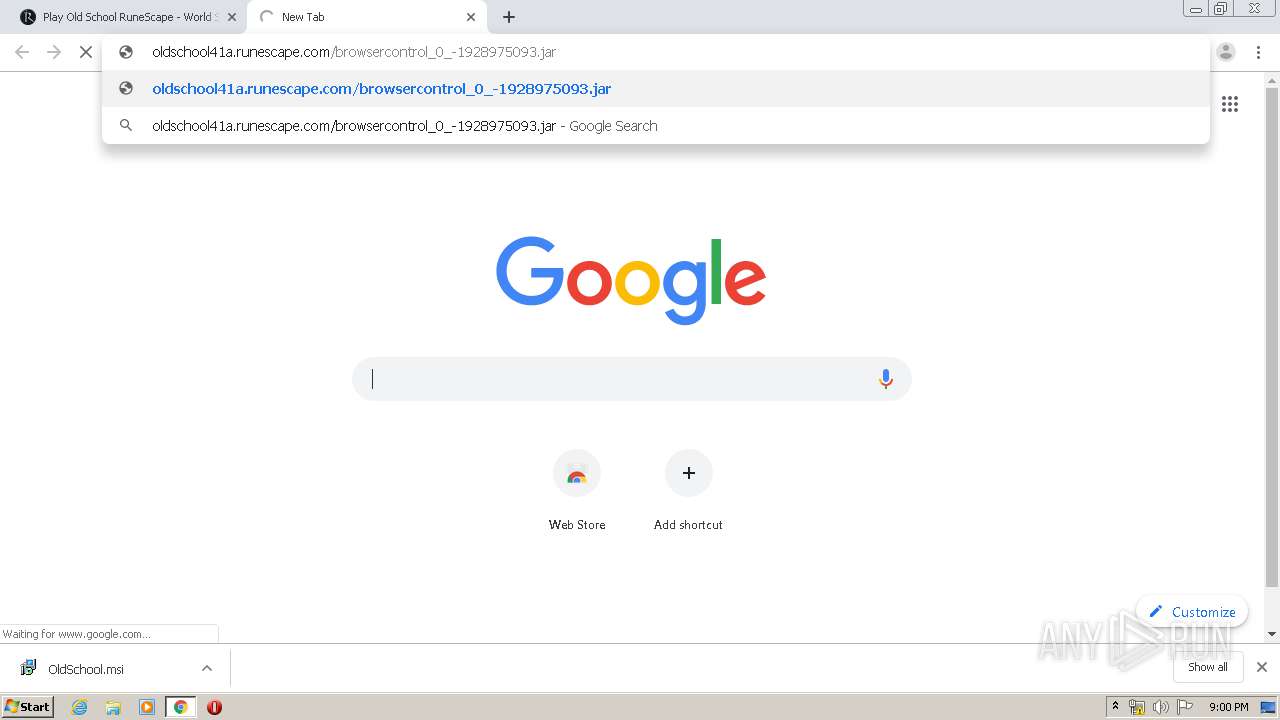
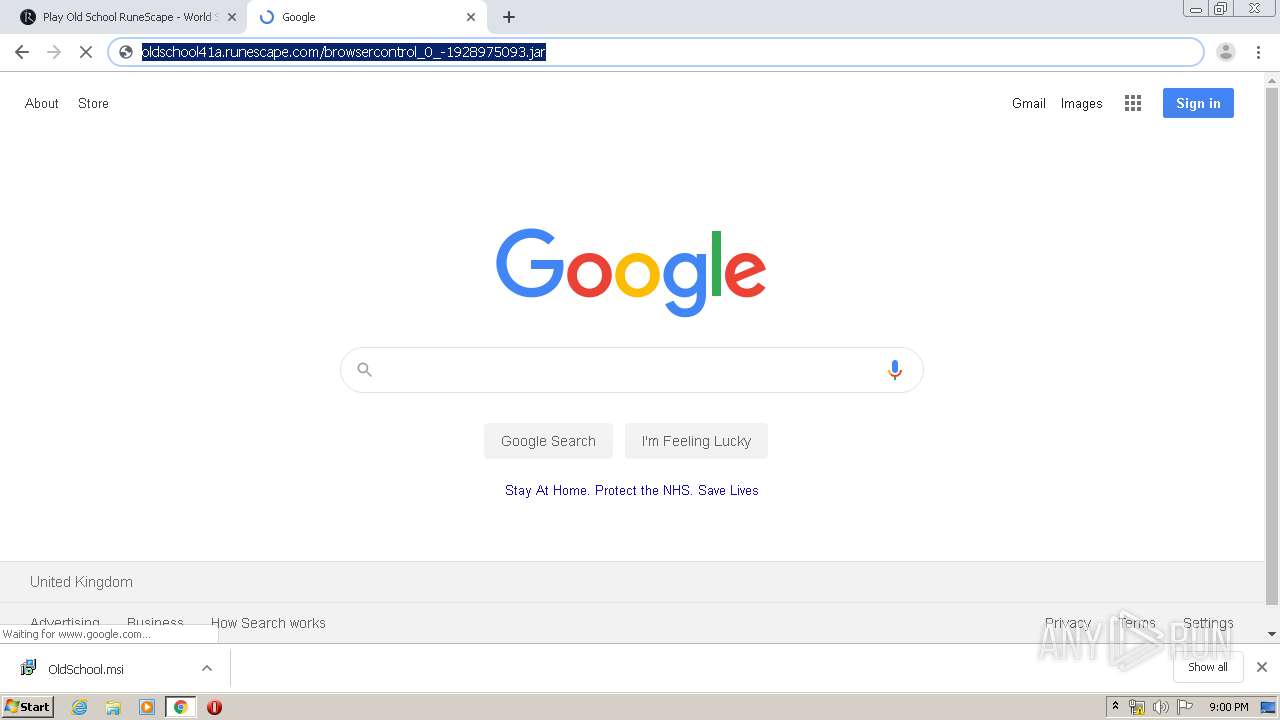
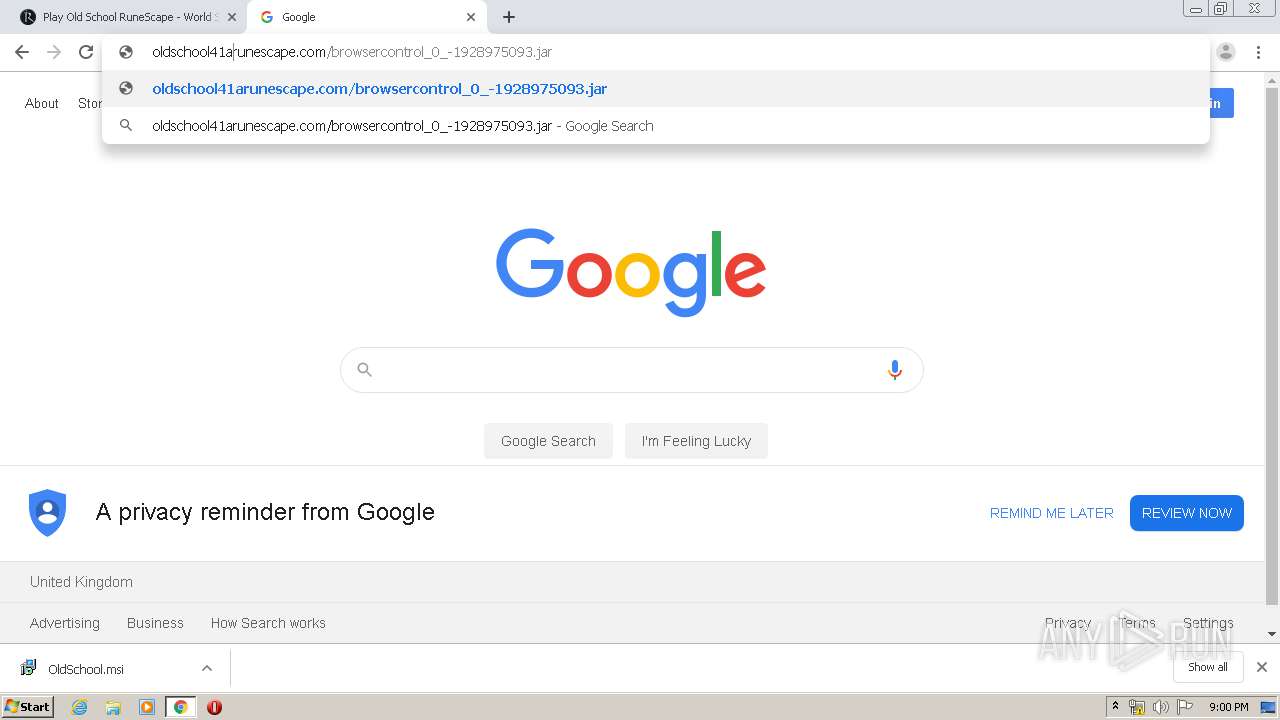
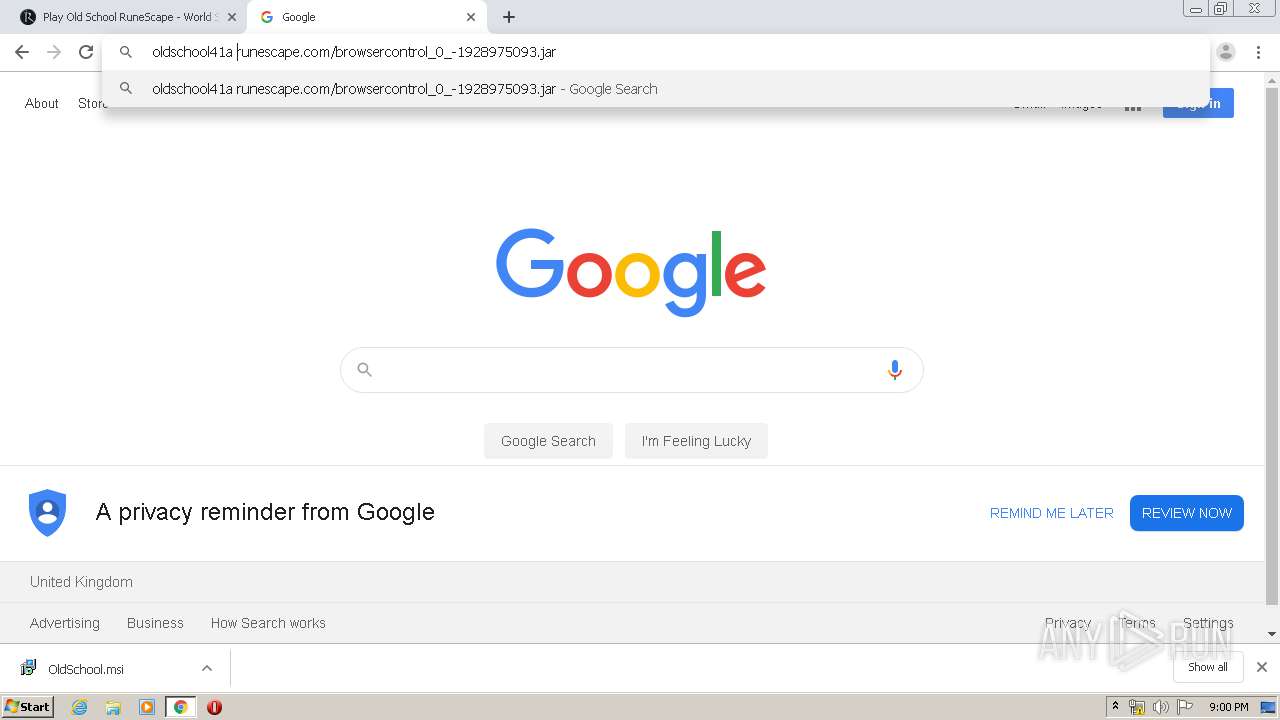
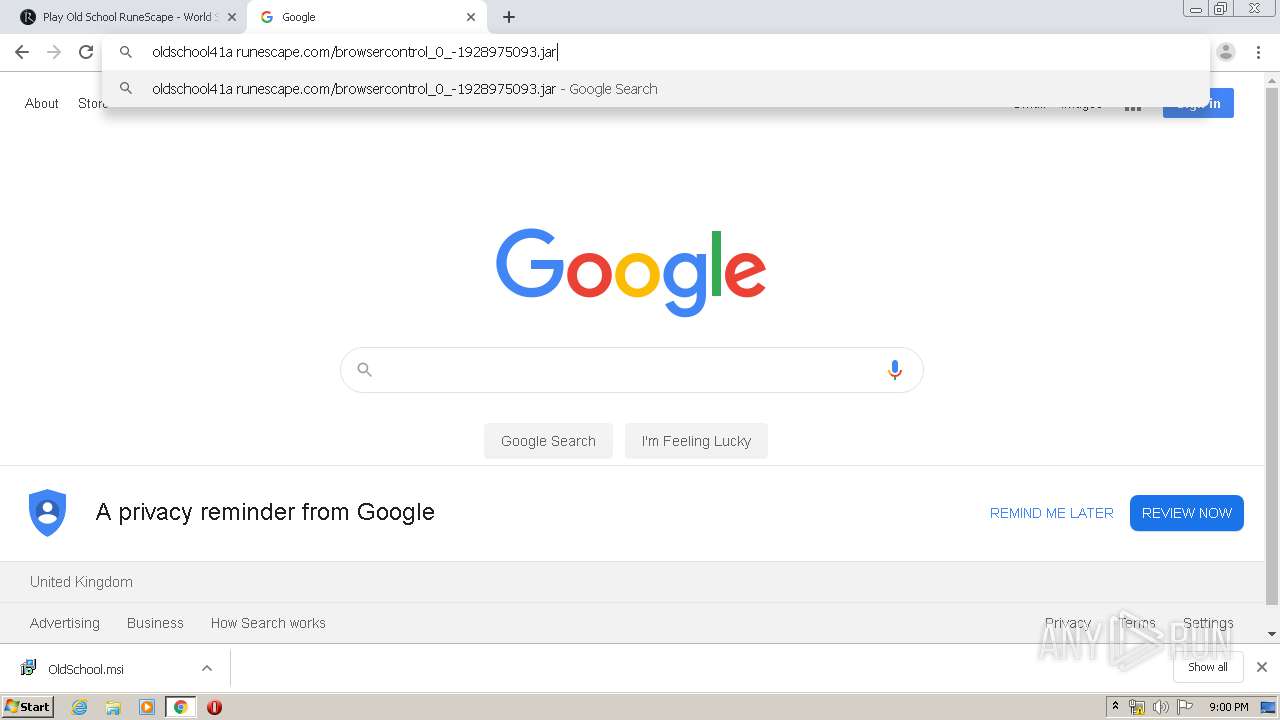
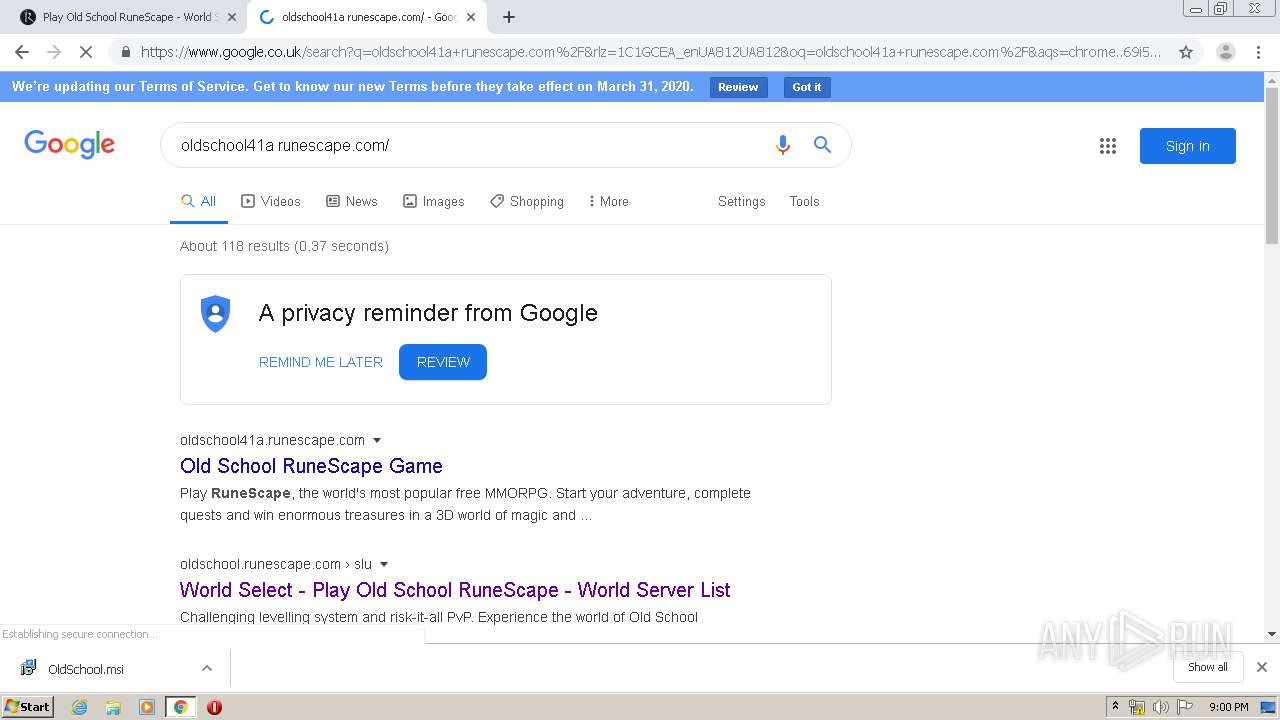
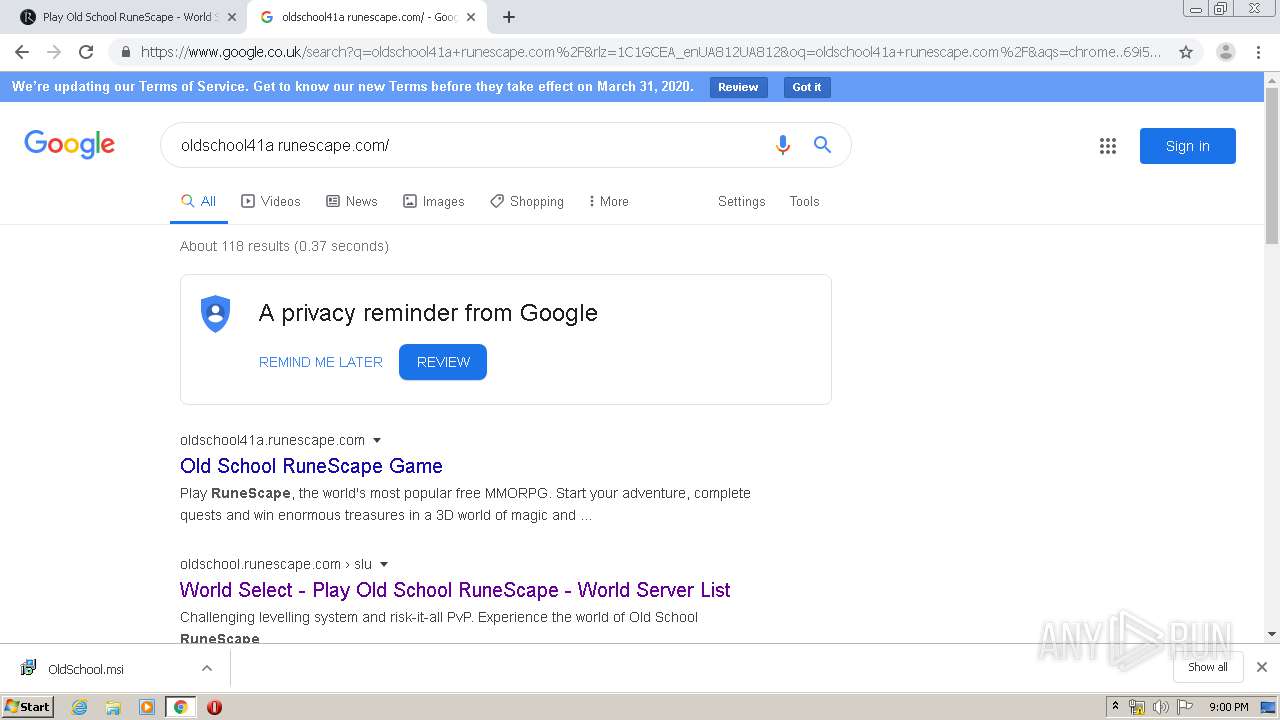
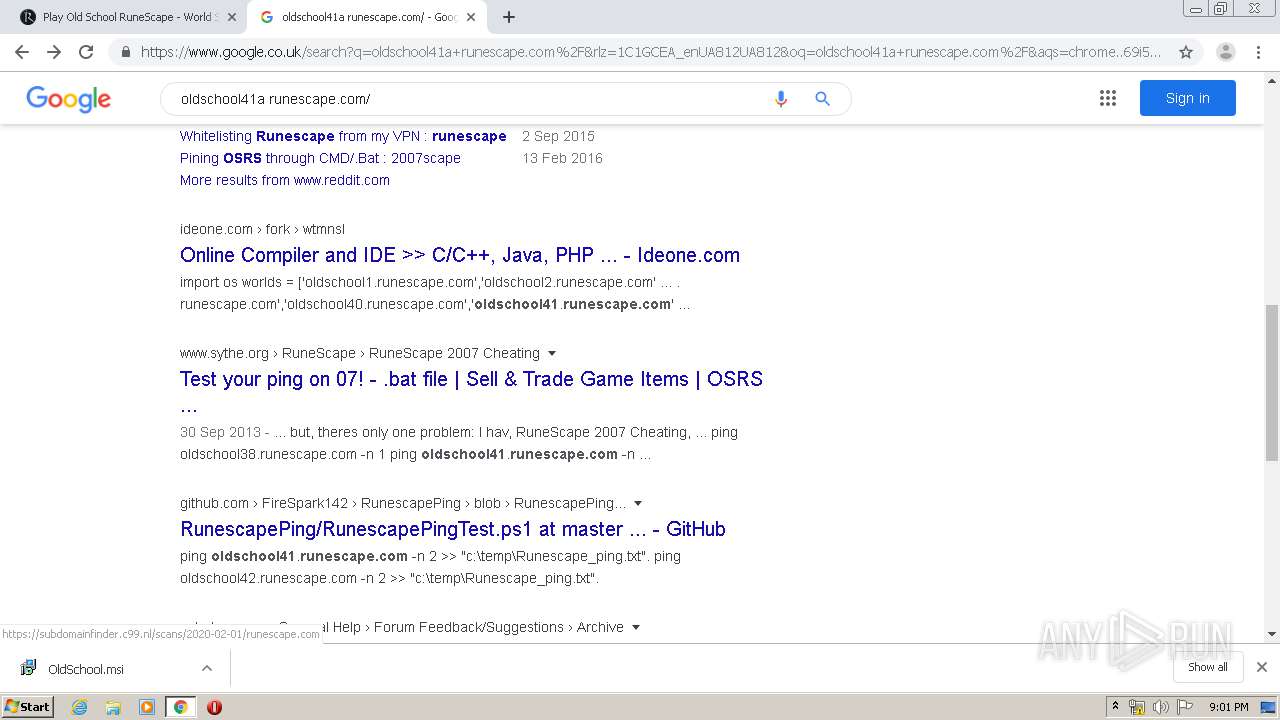
3248 | chrome.exe | GET | 302 | 91.235.140.148:80 | http://www.runescape.com/g=oldscape/img/rsp777/nojava/step3.jpg | GB | — | — | suspicious |
3248 | chrome.exe | GET | 302 | 91.235.140.148:80 | http://www.runescape.com/g=oldscape/img/rsp777/nojava/step1.jpg | GB | — | — | suspicious |
3248 | chrome.exe | GET | 302 | 91.235.140.148:80 | http://www.runescape.com/g=oldscape/img/rsp777/nojava/step2.jpg | GB | — | — | suspicious |
3248 | chrome.exe | GET | 302 | 91.235.140.148:80 | http://www.runescape.com/g=oldscape/img/rsp777/title2/rslogo3.png | GB | — | — | suspicious |
3248 | chrome.exe | GET | 302 | 91.235.140.148:80 | http://www.runescape.com/g=oldscape/img/rsp777/nojava/step4.jpg | GB | — | — | suspicious |
772 | iexplore.exe | GET | 302 | 91.235.140.148:80 | http://oldschool.runescape.com/openjdk_install.ws | GB | — | — | suspicious |
3248 | chrome.exe | GET | 302 | 91.235.140.148:80 | http://www.runescape.com/img/rsp777/jagex-logo-landscape.svg | GB | — | — | suspicious |
3248 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
3248 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
772 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
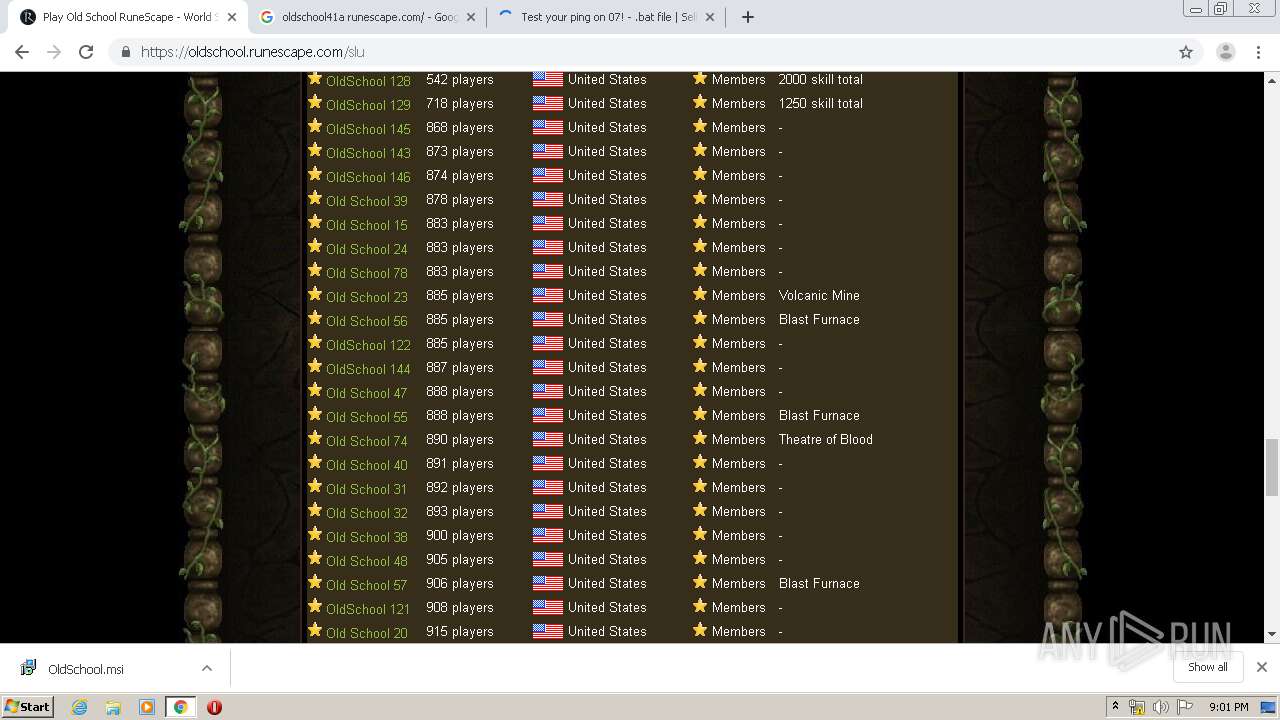
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3248 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3248 | chrome.exe | 104.244.42.131:443 | analytics.twitter.com | Twitter Inc. | US | suspicious |
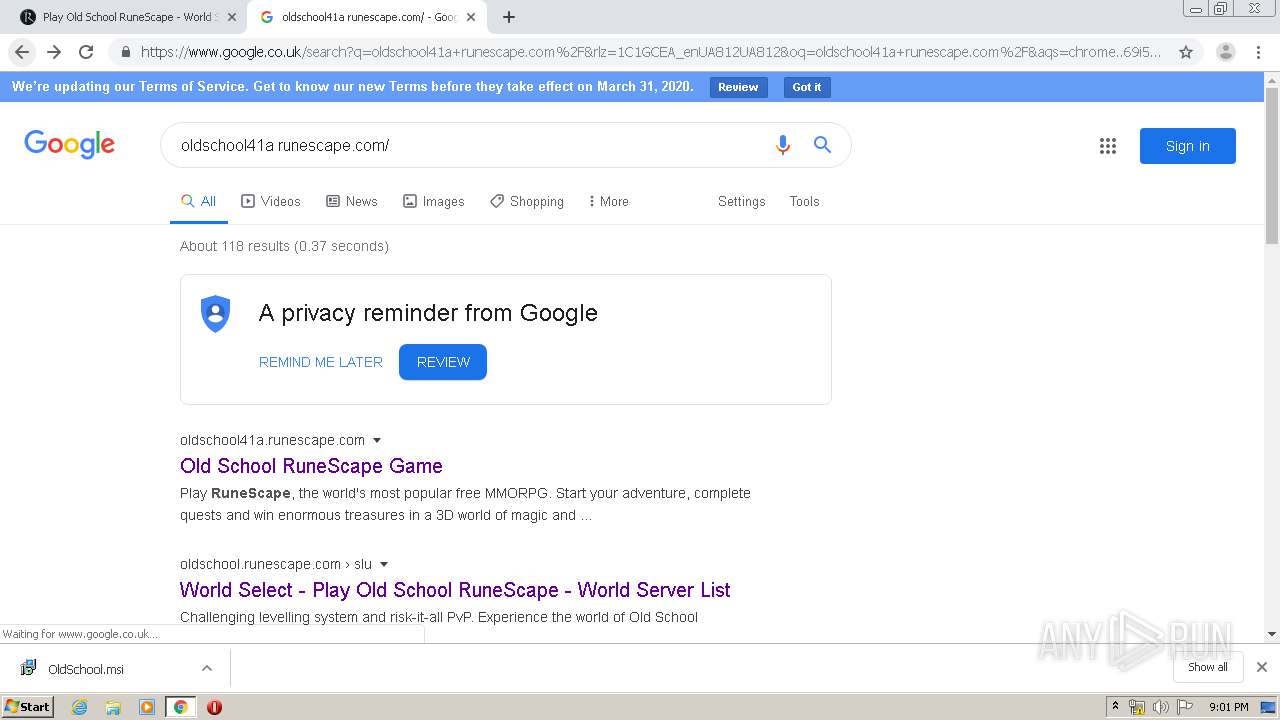
3248 | chrome.exe | 91.235.140.148:80 | runescape.com | Level 3 Communications, Inc. | GB | suspicious |
3248 | chrome.exe | 37.252.173.62:443 | secure.adnxs.com | AppNexus, Inc | — | unknown |
3248 | chrome.exe | 91.235.140.148:443 | runescape.com | Level 3 Communications, Inc. | GB | suspicious |
3248 | chrome.exe | 157.240.20.19:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
3248 | chrome.exe | 151.101.2.2:443 | cdn.taboola.com | Fastly | US | shared |
3248 | chrome.exe | 151.101.1.44:443 | trc.taboola.com | Fastly | US | suspicious |
3248 | chrome.exe | 151.101.1.140:443 | www.redditstatic.com | Fastly | US | suspicious |
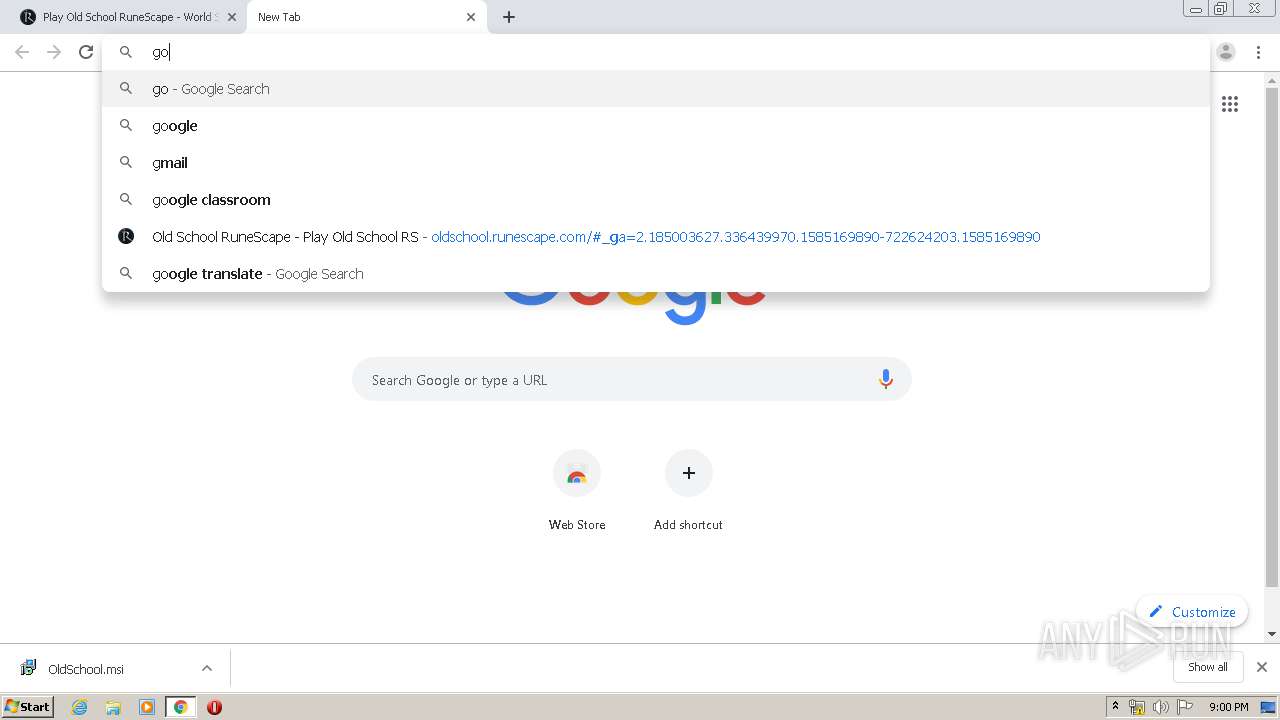
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
runescape.com |
| suspicious |
accounts.google.com |
| shared |
www.runescape.com |
| suspicious |
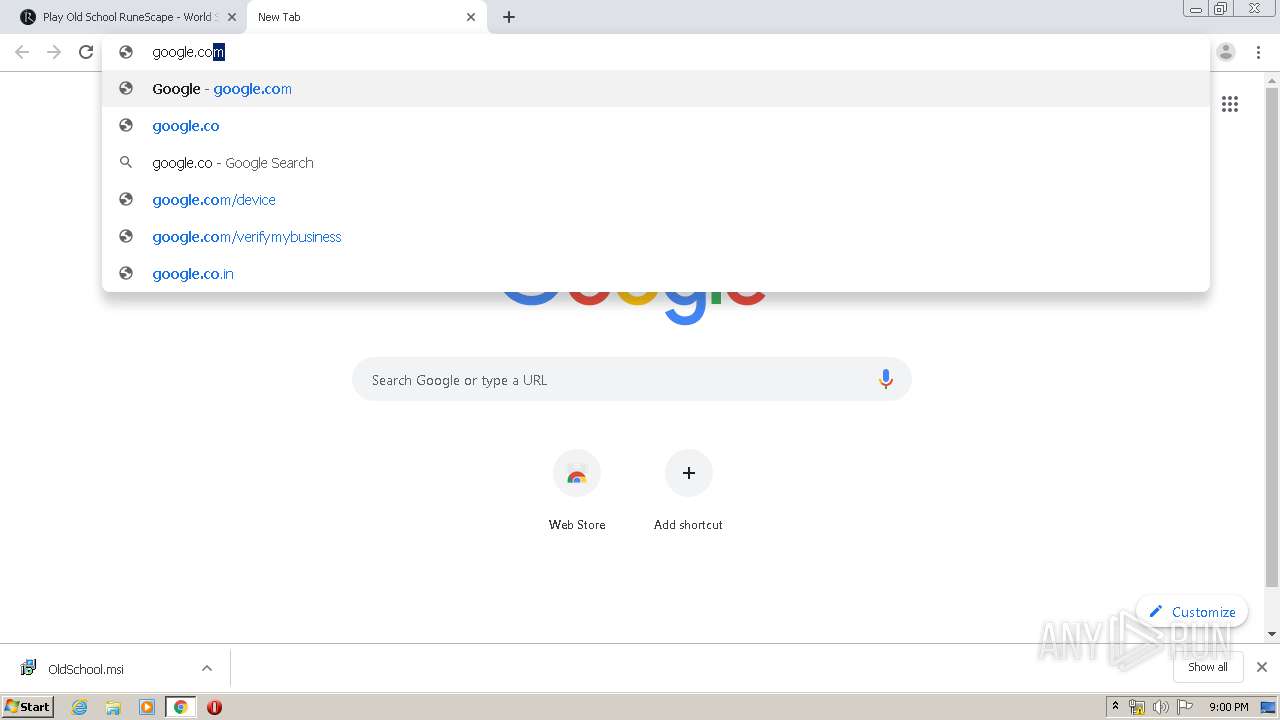
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1728 | JagexLauncher.exe | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |
1728 | JagexLauncher.exe | A Network Trojan was detected | ET INFO suspicious - uncompressed pack200-ed JAR |