| File name: | bluescreenview_setup.exe |
| Full analysis: | https://app.any.run/tasks/24bd4965-b590-4f50-ba22-c9a0a85ba7ab |
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2018, 20:22:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 974C32F8EC24194EAE13E4628FD3B933 |
| SHA1: | 9731C8E834972DF9FC88A89868974DC11C440CEE |
| SHA256: | 6CA883A660C318AEFB0CC67D6B5767443A24590D50800902181BA83F845DDB41 |
| SSDEEP: | 3072:fd/vyWmJe4501GPs7b/8D12/q2bVuzVNx8nE852WrjoXu:fXp7GPGL8DkyDfiEzWnoX |
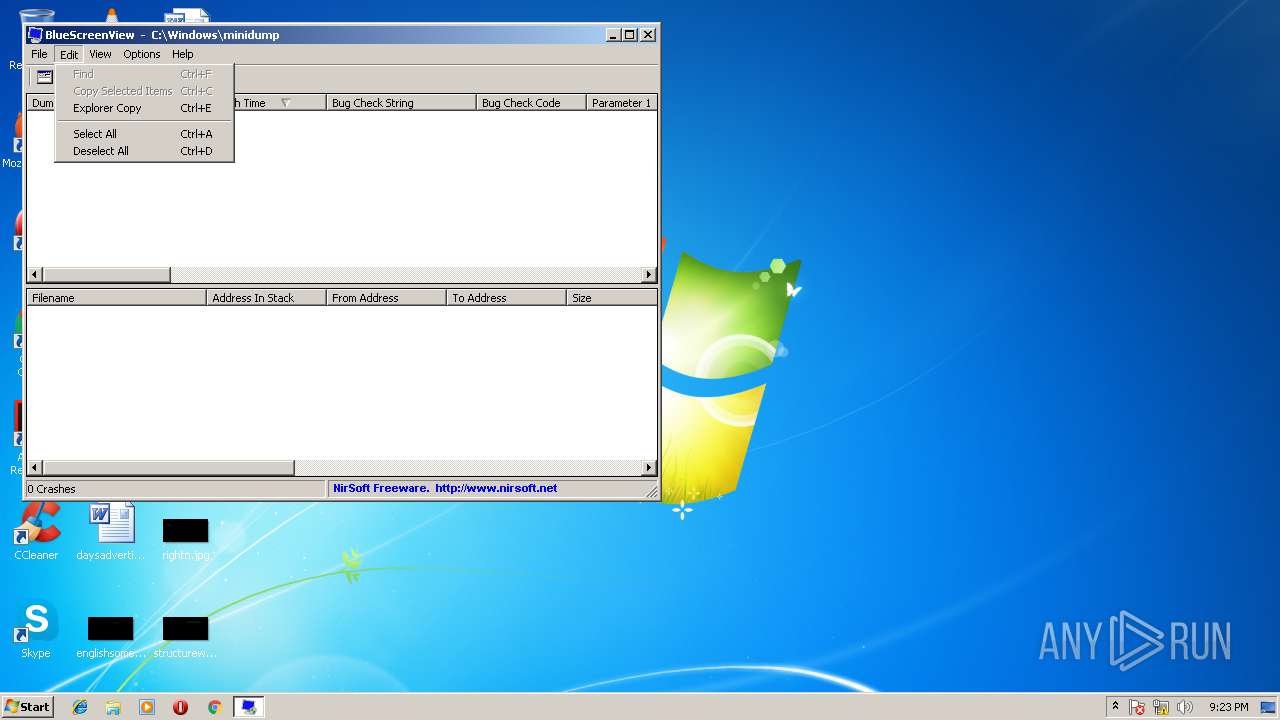
MALICIOUS
Loads dropped or rewritten executable
- bluescreenview_setup.exe (PID: 1440)
Application was dropped or rewritten from another process
- BlueScreenView.exe (PID: 2608)
SUSPICIOUS
Creates a software uninstall entry
- bluescreenview_setup.exe (PID: 1440)
Creates files in the user directory
- bluescreenview_setup.exe (PID: 1440)
Executable content was dropped or overwritten
- bluescreenview_setup.exe (PID: 1440)
Creates files in the program directory
- bluescreenview_setup.exe (PID: 1440)
INFO
Dropped object may contain URL's
- bluescreenview_setup.exe (PID: 1440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:05:03 16:08:42+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23040 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3225 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-May-2008 14:08:42 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-May-2008 14:08:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005934 | 0x00005A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45687 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17797 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.7025 |
.ndata | 0x00024000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002D000 | 0x000041E0 | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.93495 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08937 | 733 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
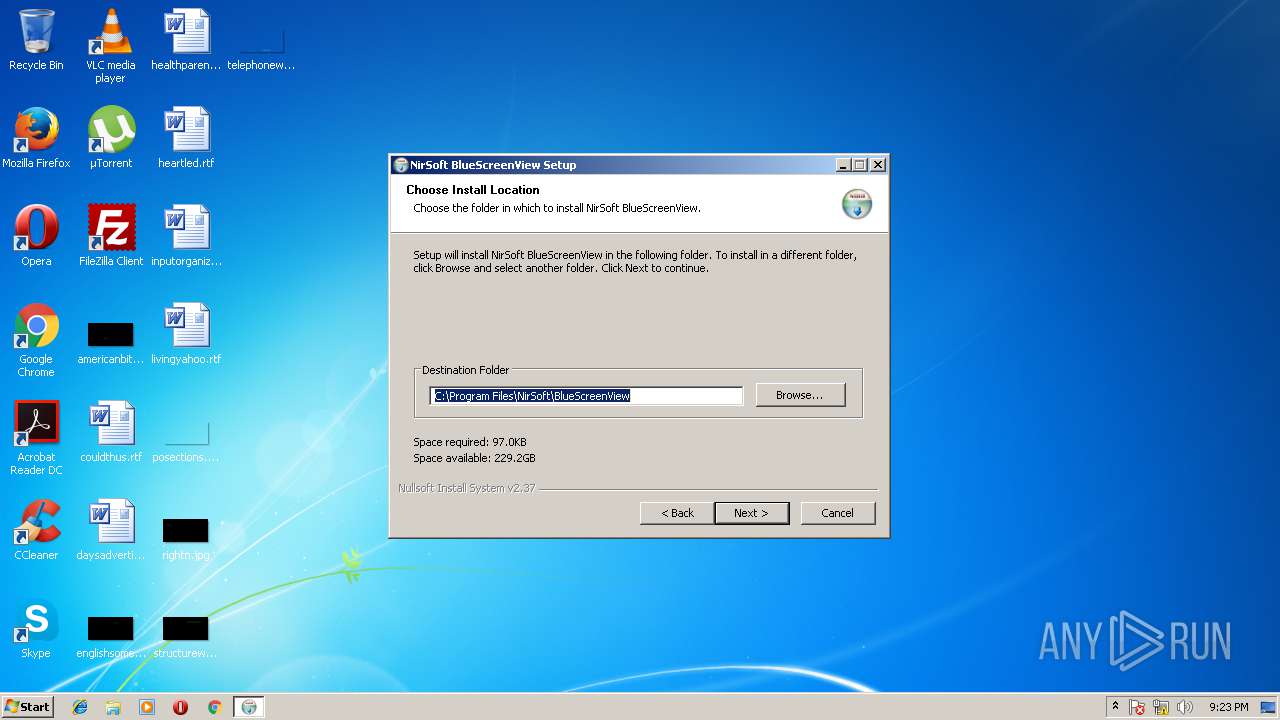
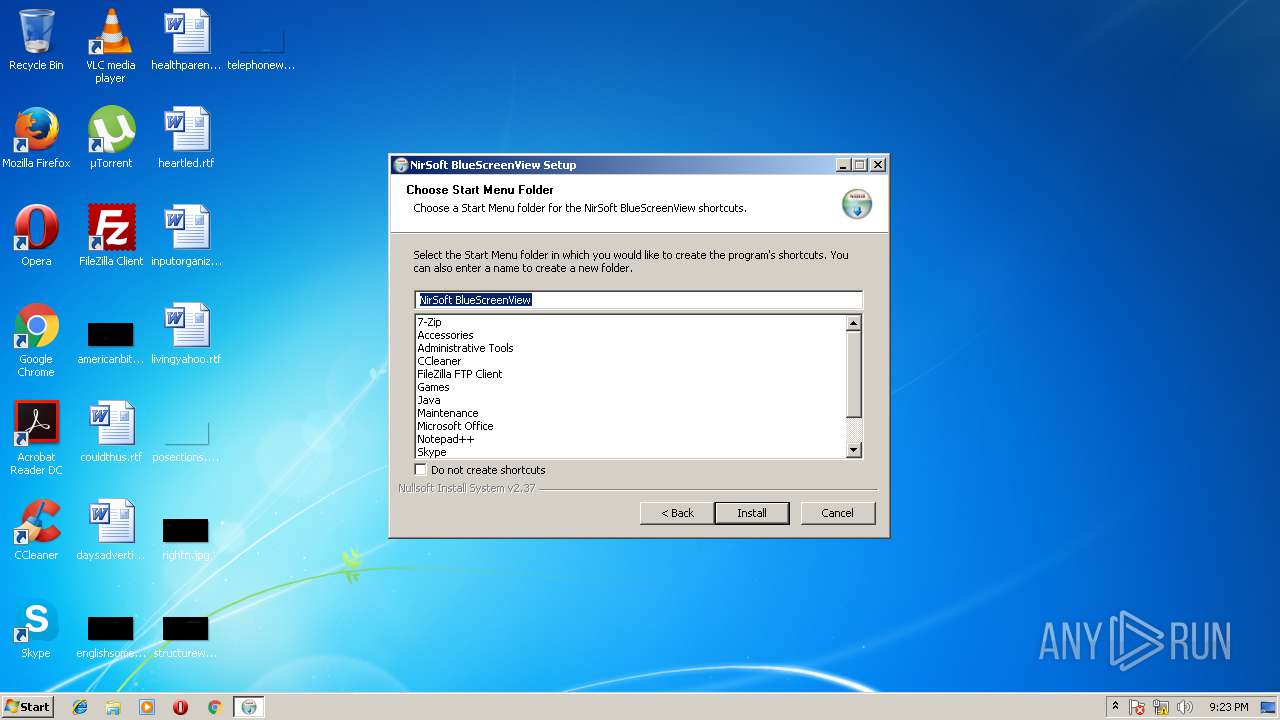
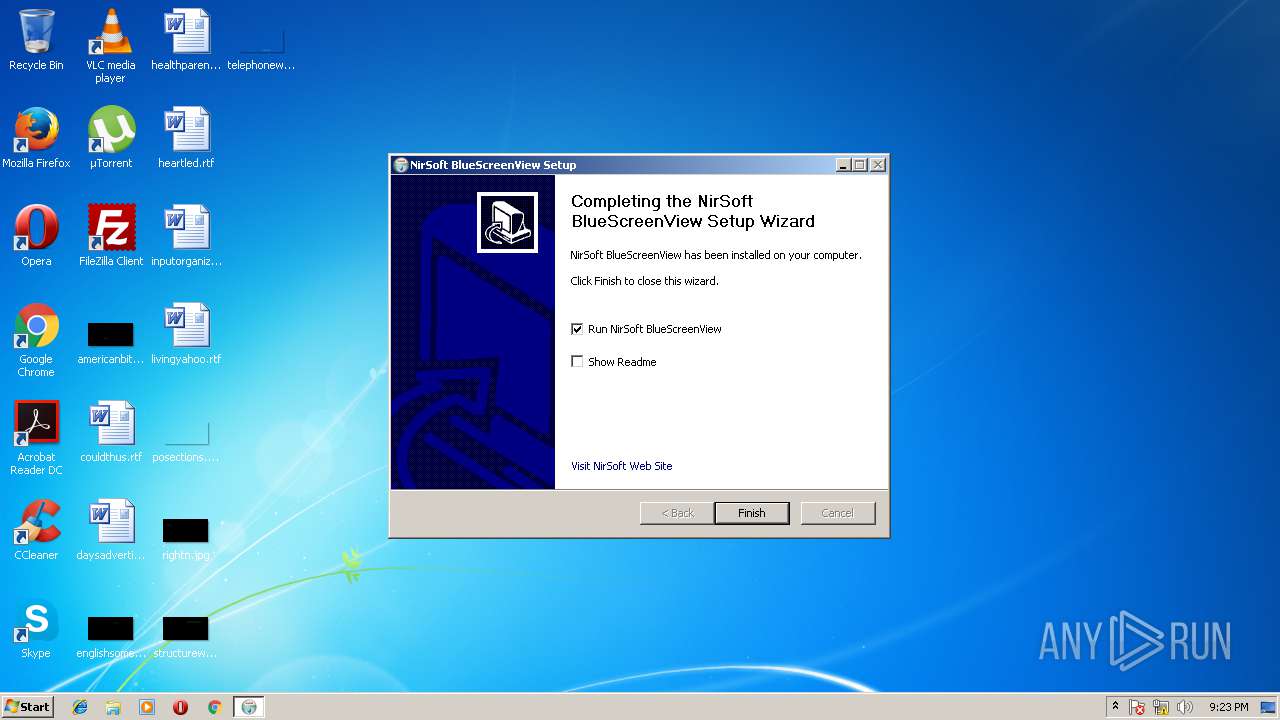
| 1440 | "C:\Users\admin\AppData\Local\Temp\bluescreenview_setup.exe" | C:\Users\admin\AppData\Local\Temp\bluescreenview_setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
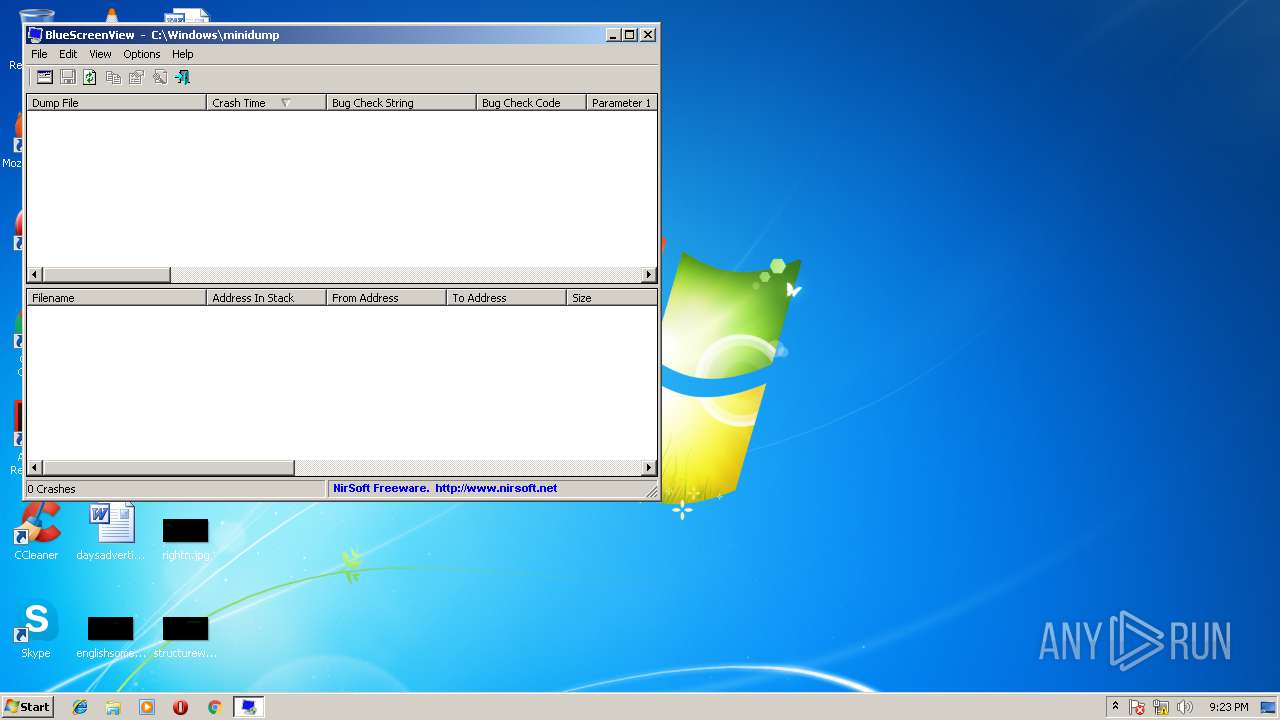
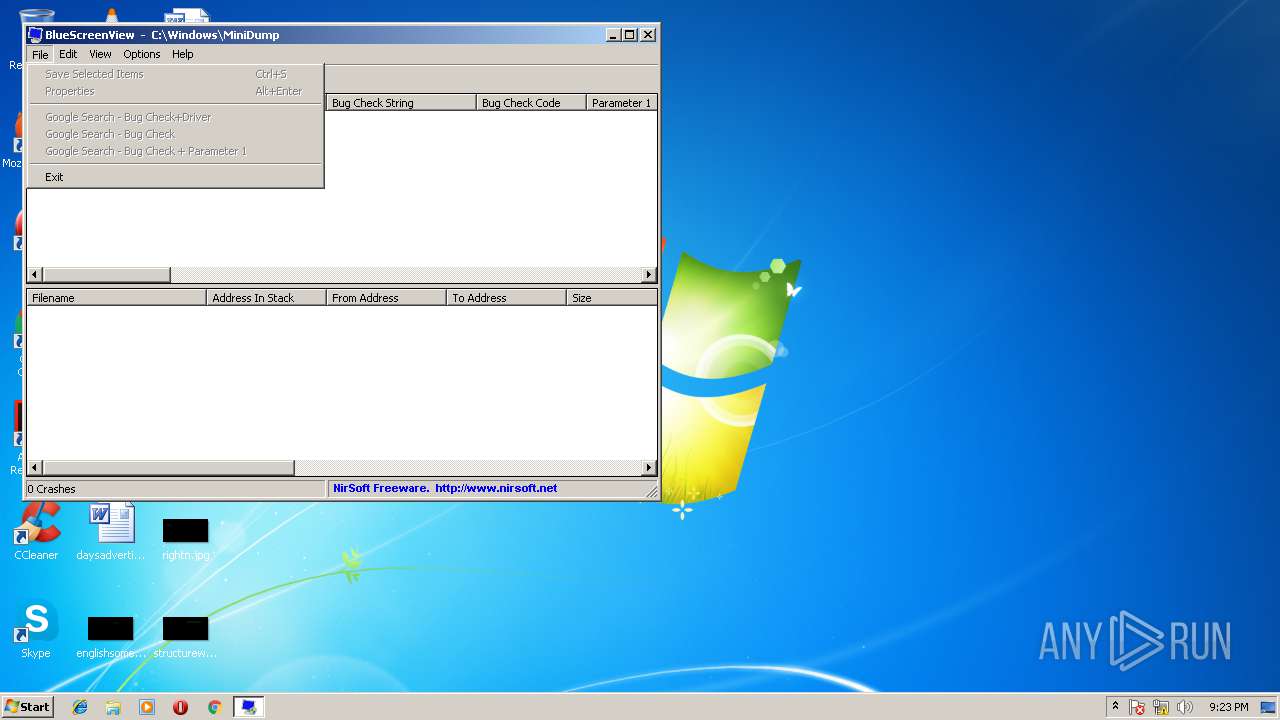
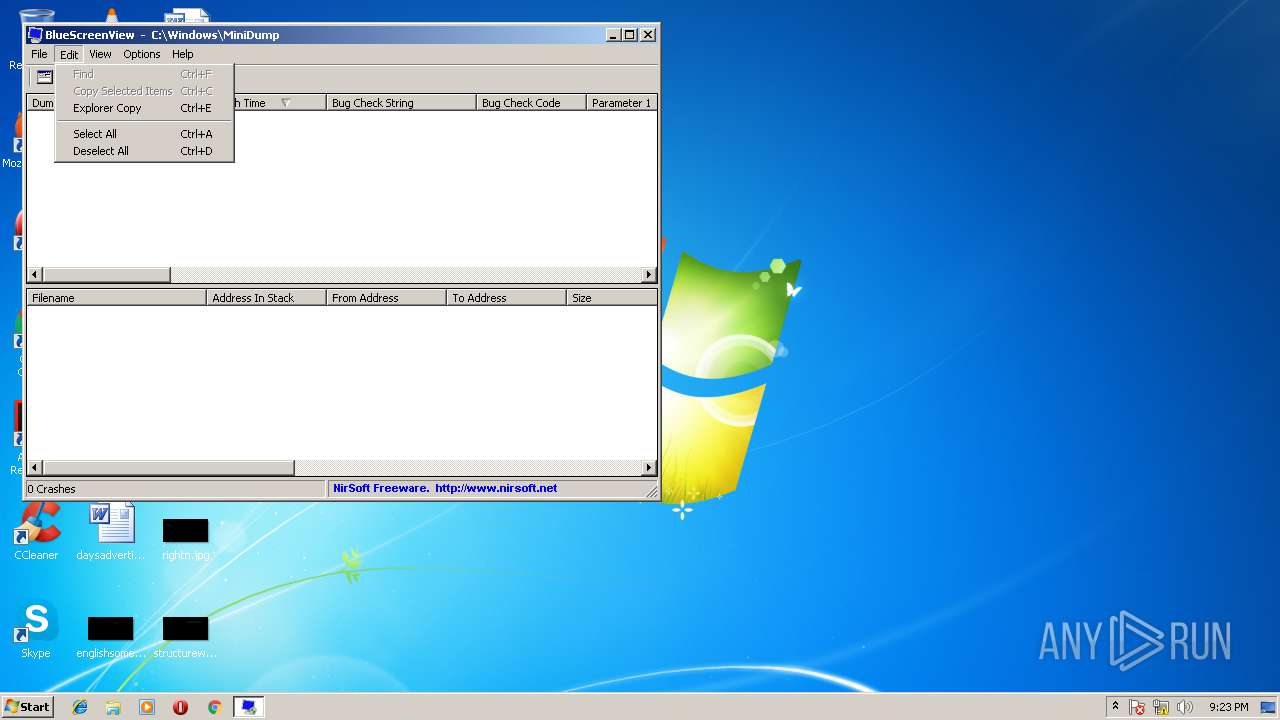
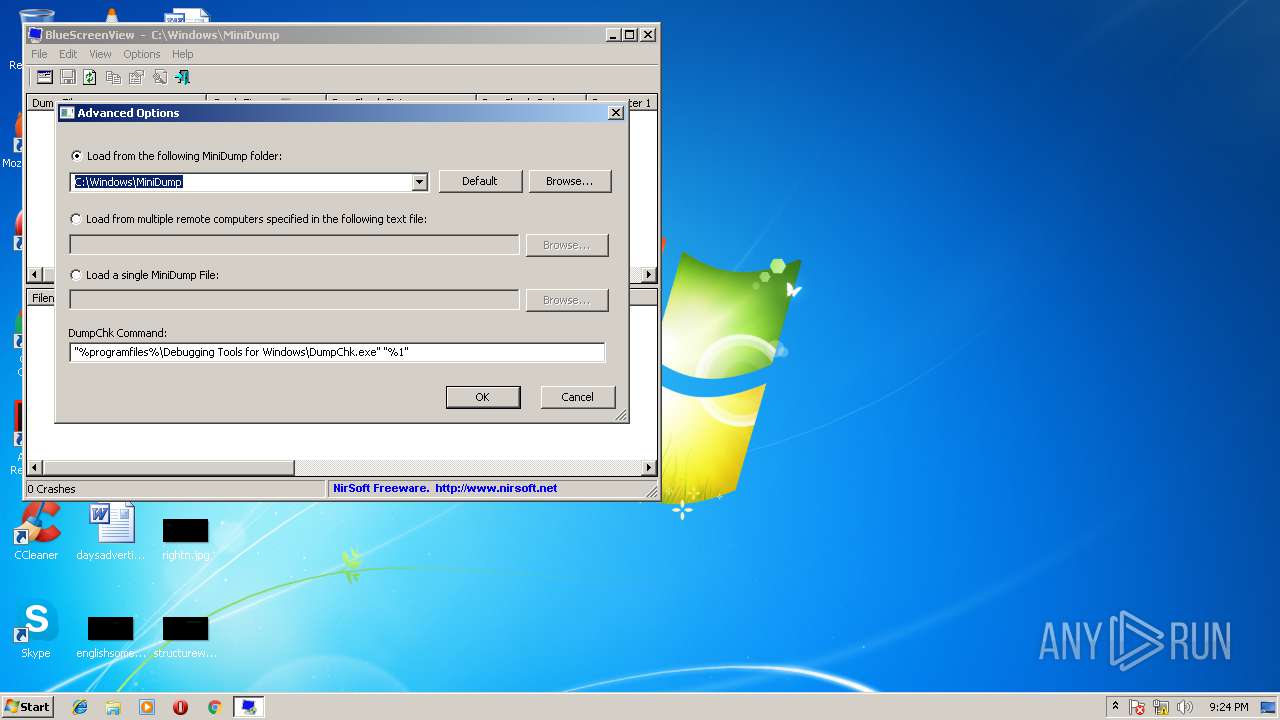
| 2608 | "C:\Program Files\NirSoft\BlueScreenView\BlueScreenView.exe" | C:\Program Files\NirSoft\BlueScreenView\BlueScreenView.exe | — | bluescreenview_setup.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: BlueScreenView Exit code: 0 Version: 1.55 Modules
| |||||||||||||||
| 3676 | "C:\Users\admin\AppData\Local\Temp\bluescreenview_setup.exe" | C:\Users\admin\AppData\Local\Temp\bluescreenview_setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
339
Read events
336
Write events
3
Delete events
0
Modification events
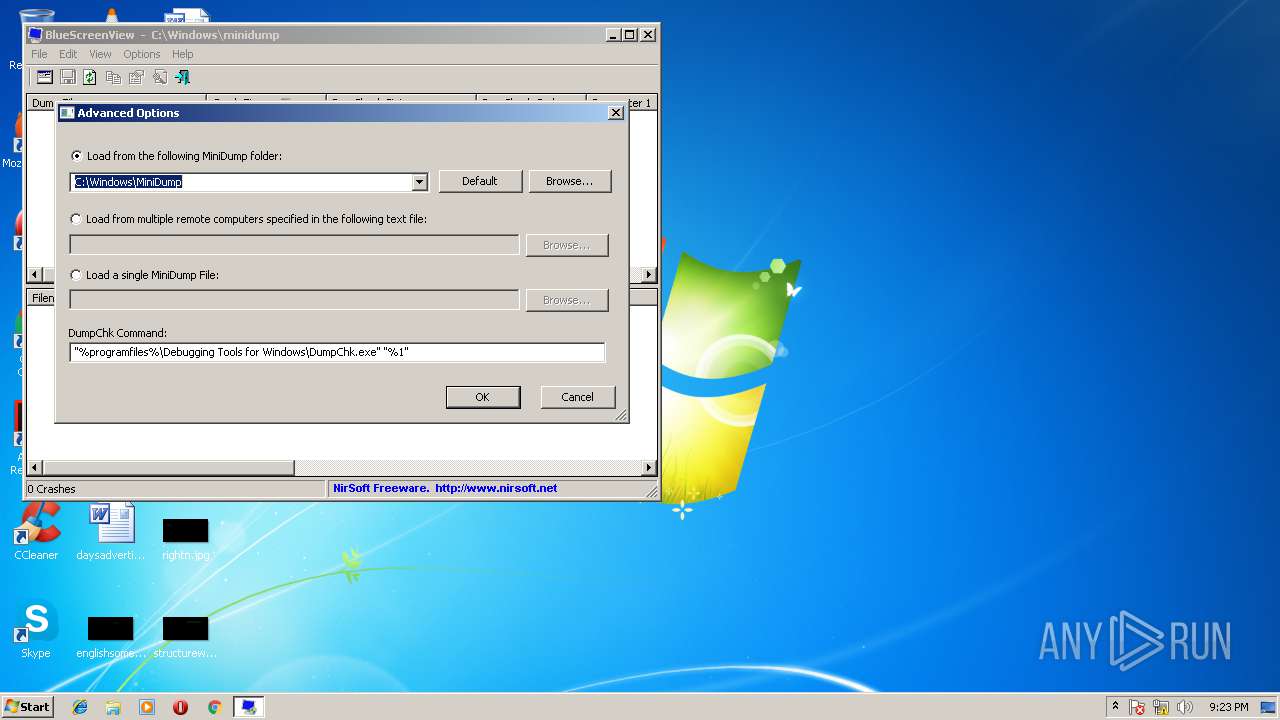
| (PID) Process: | (1440) bluescreenview_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NirSoft BlueScreenView |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\NirSoft\BlueScreenView\uninst.exe" | |||
| (PID) Process: | (1440) bluescreenview_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NirSoft BlueScreenView |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\NirSoft\BlueScreenView | |||
| (PID) Process: | (1440) bluescreenview_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NirSoft BlueScreenView |
| Operation: | write | Name: | DisplayName |
Value: NirSoft BlueScreenView | |||
Executable files
4
Suspicious files
0
Text files
51
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1440 | bluescreenview_setup.exe | C:\Users\admin\AppData\Local\Temp\nsj5CC.tmp | — | |
MD5:— | SHA256:— | |||
| 1440 | bluescreenview_setup.exe | C:\Users\admin\AppData\Local\Temp\nsj5CD.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 1440 | bluescreenview_setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\NirSoft BlueScreenView\BlueScreenView.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1440 | bluescreenview_setup.exe | C:\Program Files\NirSoft\BlueScreenView\BlueScreenView.chm | chi | |
MD5:D130E5001531448871BB8EF10C106B25 | SHA256:3B9D7F203E282C0AAA522F706308E2215786A2FB95E9FFB86E97168FFFFE3009 | |||
| 1440 | bluescreenview_setup.exe | C:\Program Files\NirSoft\BlueScreenView\readme.txt | text | |
MD5:ACECB7D7AF592DA7A843EF44B4500818 | SHA256:92BFF76A8CBD014A8445F6F522924DB7F29B2ADF5BDC344AC727D1C12B10E285 | |||
| 1440 | bluescreenview_setup.exe | C:\Program Files\NirSoft\BlueScreenView\BlueScreenView.exe | executable | |
MD5:6126F1221D29712C069EE28EF4186E24 | SHA256:F5F52EC9C38E7123507FE362BA0A0CD0E3AC17B820813EC3BF435FA3A8135ED0 | |||
| 1440 | bluescreenview_setup.exe | C:\Users\admin\AppData\Local\Temp\nsj5CD.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 1440 | bluescreenview_setup.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\NirSoft BlueScreenView\BlueScreenView Help.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1440 | bluescreenview_setup.exe | C:\Users\admin\AppData\Local\Temp\nsj5CD.tmp\InstallOptions.dll | executable | |
MD5:3809B1424D53CCB427C88CABAB8B5F94 | SHA256:426EFD56DA4014F12EC8EE2E268F86B848BBCA776333D55482CB3EB71C744088 | |||
| 1440 | bluescreenview_setup.exe | C:\Users\admin\AppData\Local\Temp\nsj5CD.tmp\StartMenu.dll | executable | |
MD5:8262FBC2A172FF04146E7587649D7091 | SHA256:AC53840D019B746AB5DABAA40D7720C9A4487C861B155926454BF8B10BD0963D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report