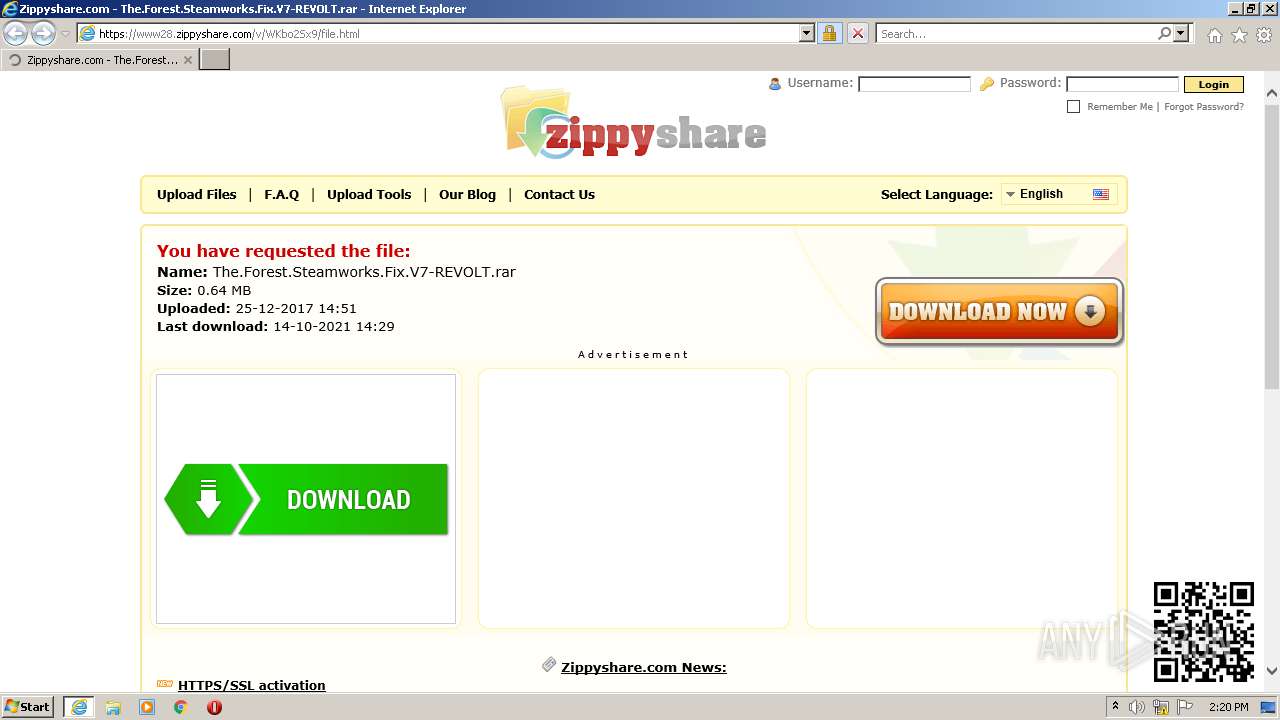
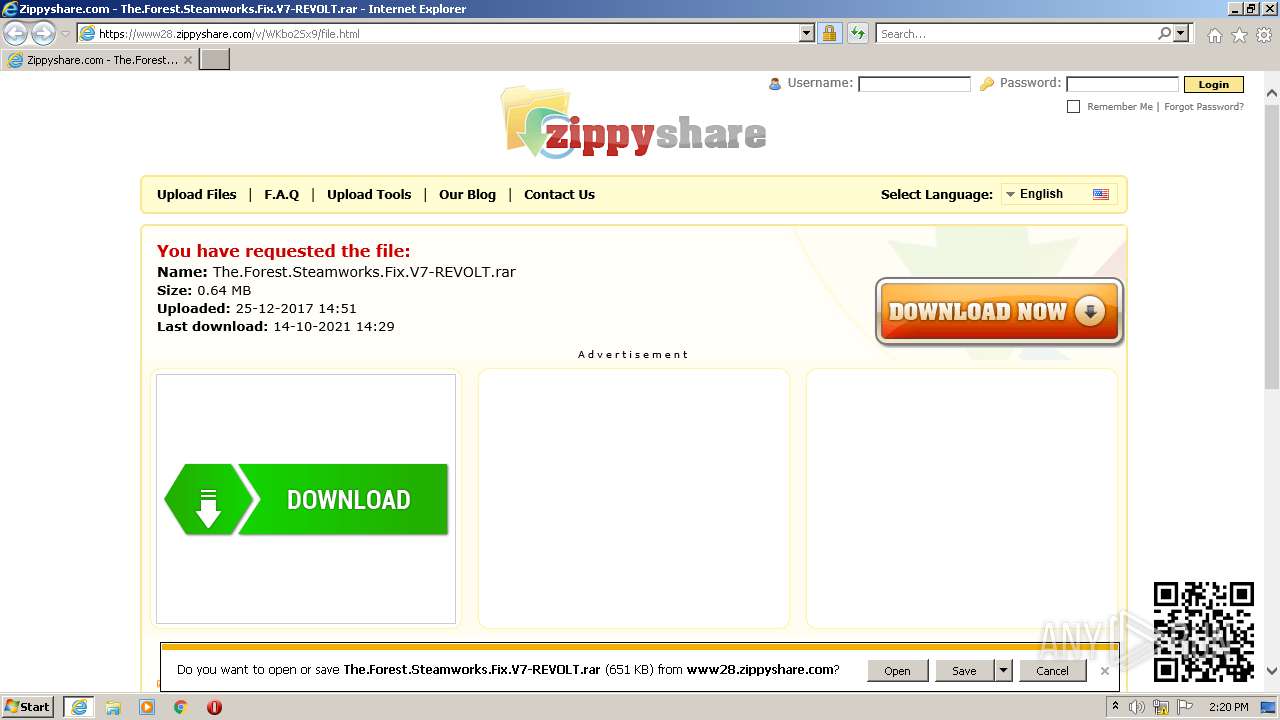
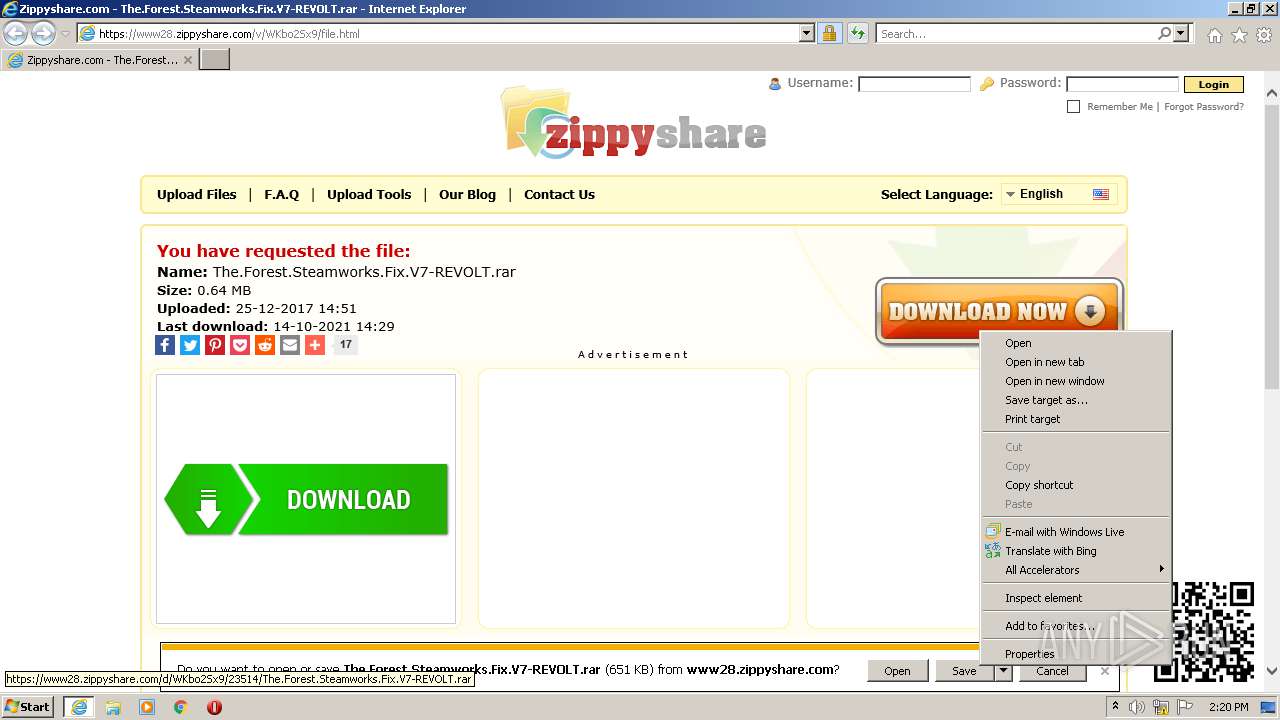
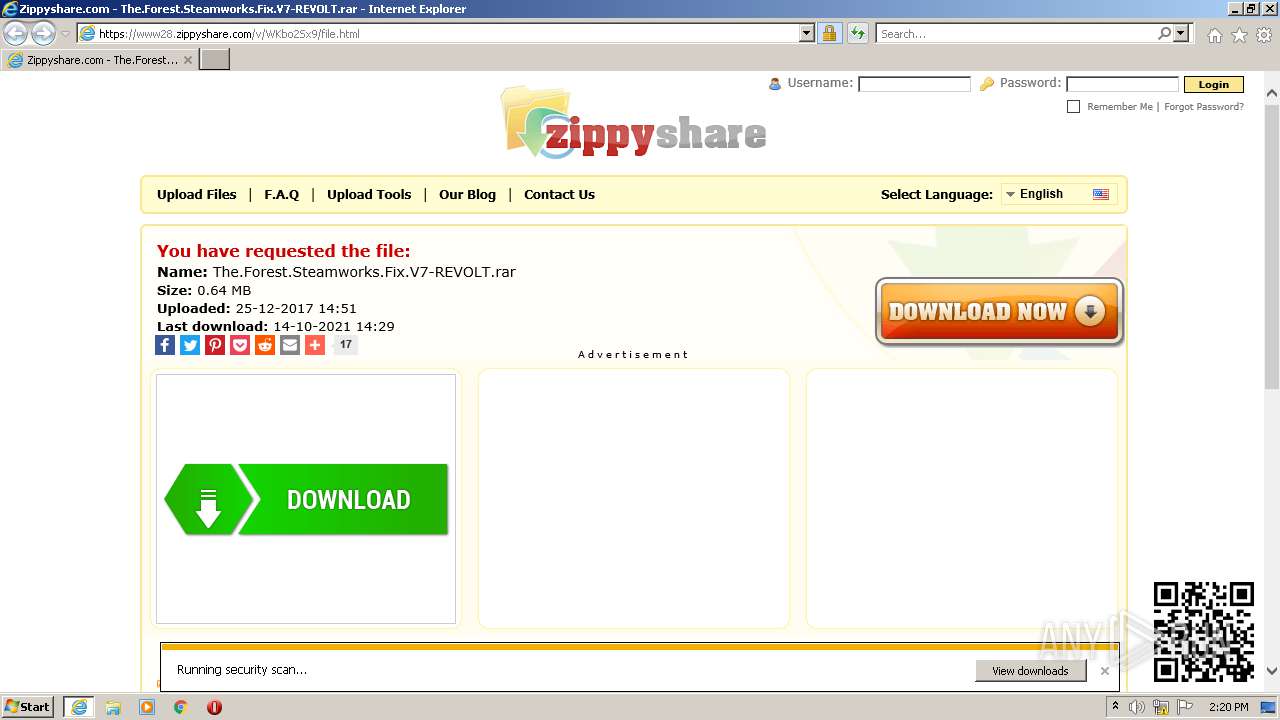
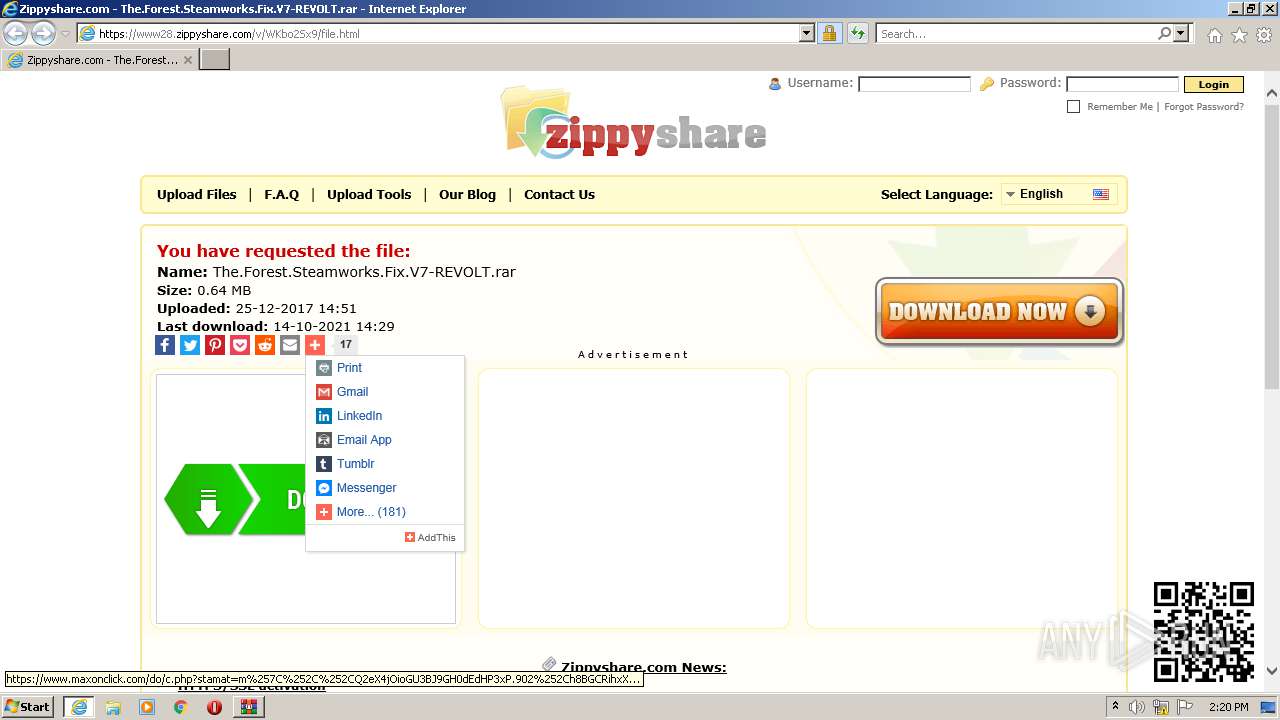
| URL: | https://www28.zippyshare.com/v/WKbo2Sx9/file.html |
| Full analysis: | https://app.any.run/tasks/78630c21-ed0c-4e76-9798-8e80bafcb9ff |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2021, 13:20:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DE12137B5A4670C0D15597AE7C223901 |
| SHA1: | 13A32AE951BB24FEEC858BE54CA8540222F2A0A8 |
| SHA256: | 6CA41ADB34420FD86B9988B39C0B4C9DCAA500FA2B25C69E32A94BD244D19954 |
| SSDEEP: | 3:N8DSXqZGKjK9qX6cKDMJAwJ:2OXmGj9s6cYMFJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 632)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3816)
- WinRAR.exe (PID: 2992)
Checks supported languages
- WinRAR.exe (PID: 2992)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3816)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3816)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3816)
INFO
Reads the computer name
- iexplore.exe (PID: 1372)
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 632)
Checks supported languages
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 1372)
- iexplore.exe (PID: 632)
Changes internet zones settings
- iexplore.exe (PID: 1372)
Application launched itself
- iexplore.exe (PID: 1372)
Reads settings of System Certificates
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 1372)
- iexplore.exe (PID: 632)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1372)
Checks Windows Trust Settings
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 1372)
- iexplore.exe (PID: 632)
Reads CPU info
- iexplore.exe (PID: 3644)
Reads internet explorer settings
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 632)
Creates files in the user directory
- iexplore.exe (PID: 3644)
- iexplore.exe (PID: 632)
Changes settings of System certificates
- iexplore.exe (PID: 1372)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1372 CREDAT:2692396 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1372 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www28.zippyshare.com/v/WKbo2Sx9/file.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
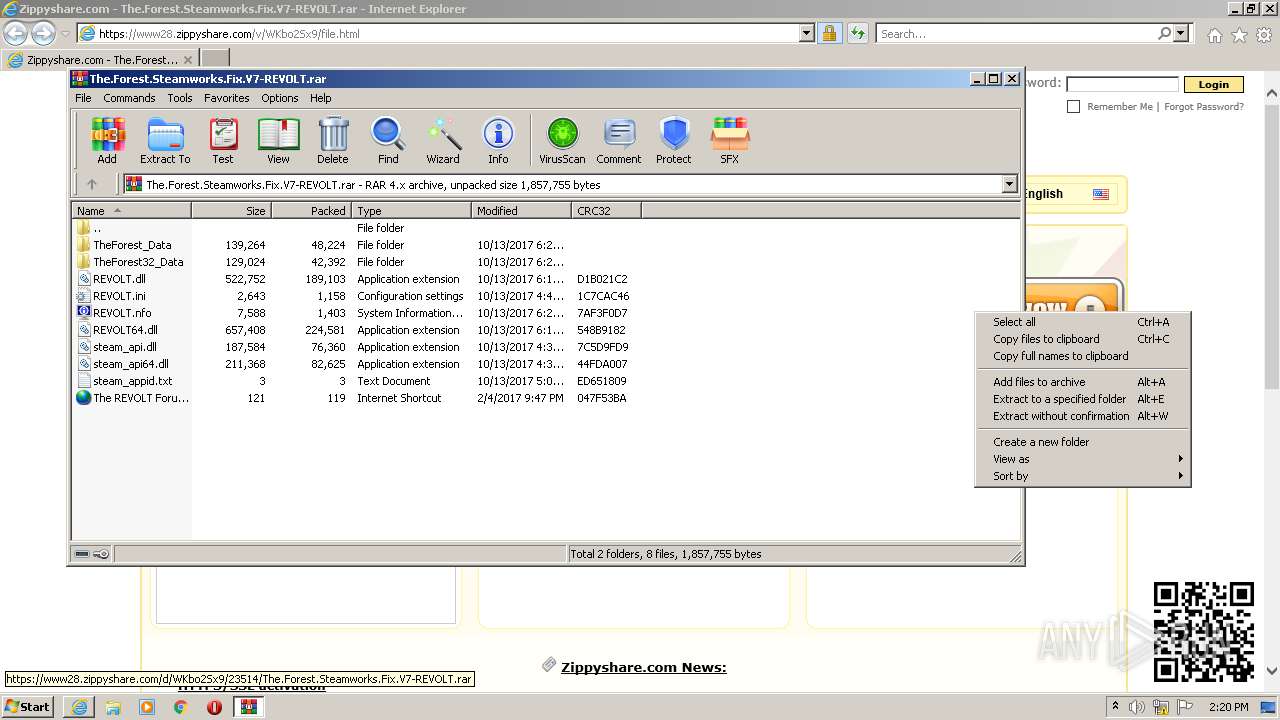
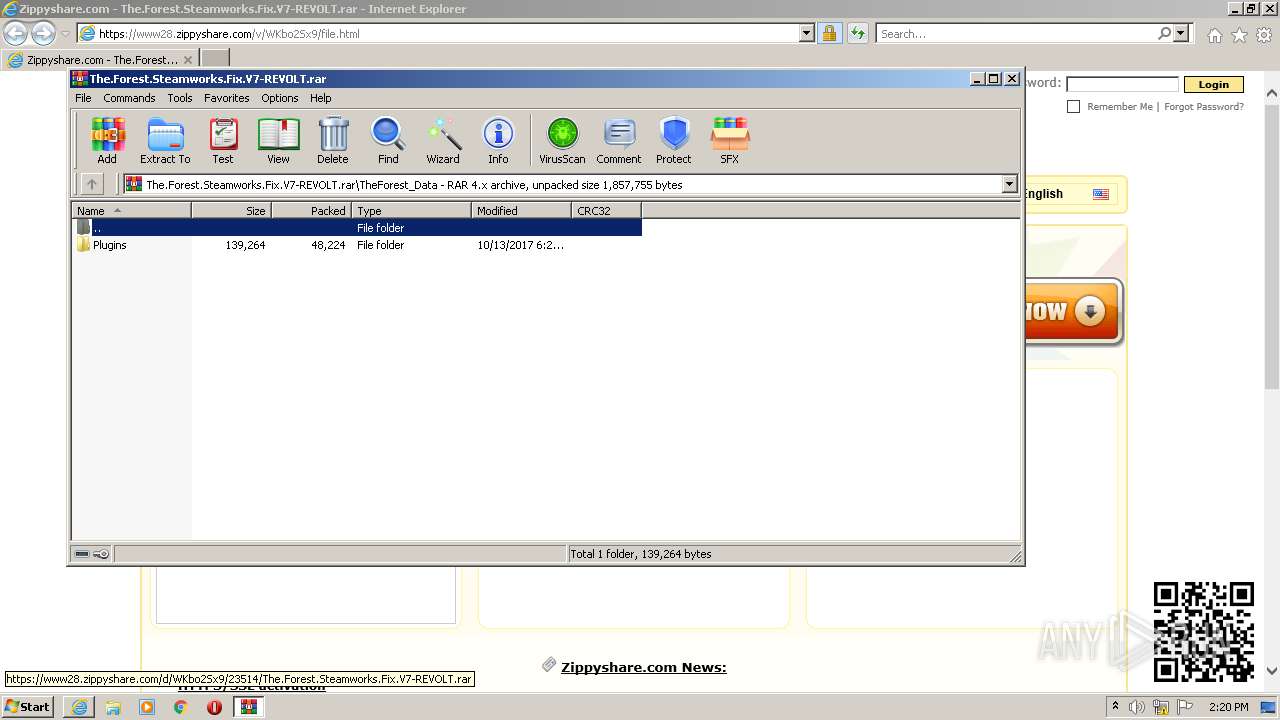
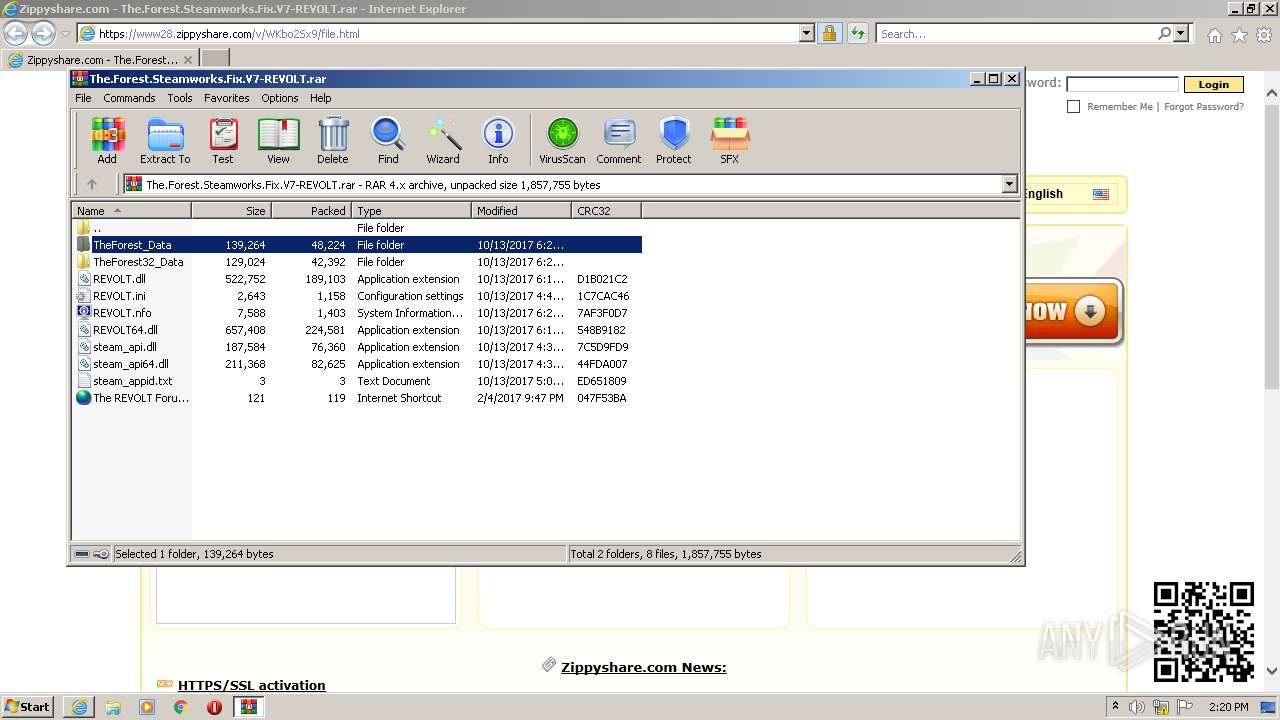
| 2992 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\The.Forest.Steamworks.Fix.V7-REVOLT.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3644 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1372 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3816 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
Total events
28 652
Read events
28 444
Write events
204
Delete events
4
Modification events
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 889774848 | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30916862 | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30916862 | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
37
Text files
65
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\viewjs-9c29d4e653e865831dc028fdac7e7dfff3be049e[1].css | text | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BC570EC0DE58335AFAF92FDC8E3AA330_D21CA3FA19E2494154CA1B3726B54309 | binary | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ads[1].js | text | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\sw[1].js | text | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\file[1].htm | html | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6Q7FYZHO.txt | text | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
| 3644 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BC570EC0DE58335AFAF92FDC8E3AA330_D21CA3FA19E2494154CA1B3726B54309 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
111
DNS requests
47
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3644 | iexplore.exe | GET | 200 | 143.204.101.124:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3644 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3644 | iexplore.exe | GET | 200 | 143.204.101.123:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3644 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://crl2.alphassl.com/gs/gsalphasha2g2.crl | US | binary | 84.6 Kb | whitelisted |
3644 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3644 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?fa5f2d4034c8b617 | US | compressed | 59.7 Kb | whitelisted |
1372 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3644 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEHv7D3dUMlEM88feQf6bkF0%3D | US | der | 471 b | whitelisted |
3644 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQDp%2F66kAKXv9Yd3%2F%2B3h9usU | US | der | 472 b | whitelisted |
3644 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECRXdf7EU7SwCgAAAAD%2FZgs%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3644 | iexplore.exe | 46.166.139.185:443 | www28.zippyshare.com | NForce Entertainment B.V. | NL | unknown |
3644 | iexplore.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
3644 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1372 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 46.166.139.185:443 | www28.zippyshare.com | NForce Entertainment B.V. | NL | unknown |
1372 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1372 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 143.204.101.149:443 | ds88pc0kw6cvc.cloudfront.net | — | US | unknown |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | Microsoft Corporation | GB | whitelisted |
— | — | 35.190.68.123:443 | www.maxonclick.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www28.zippyshare.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
crl.globalsign.net |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
crl2.alphassl.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |