| File name: | ADZP 20 Complex.exe |
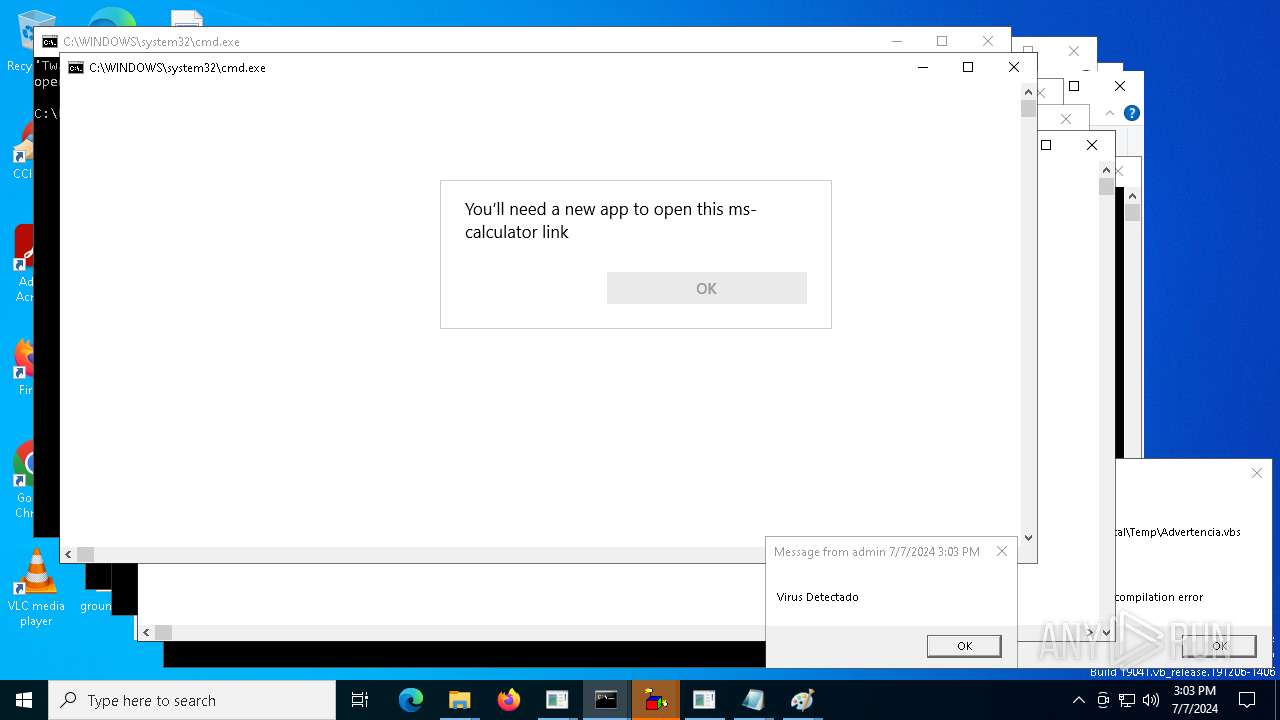
| Full analysis: | https://app.any.run/tasks/d4a338d0-193b-4113-acee-4c6f95685ba7 |
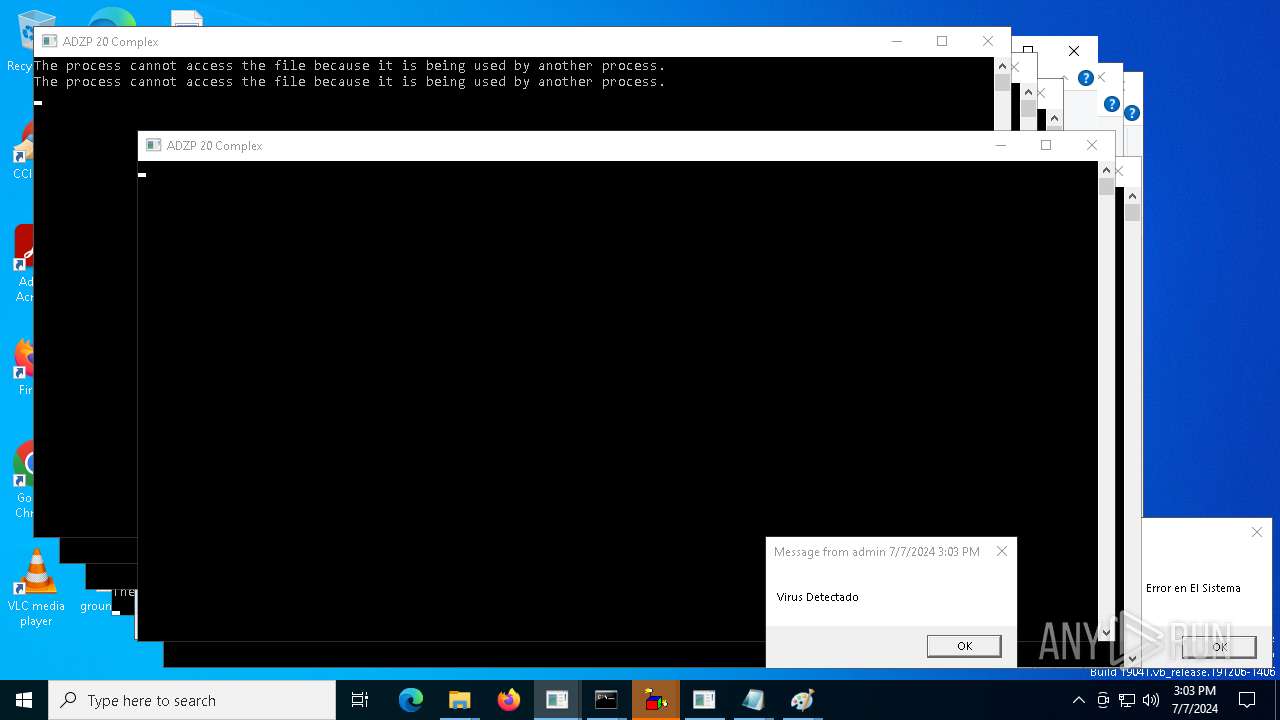
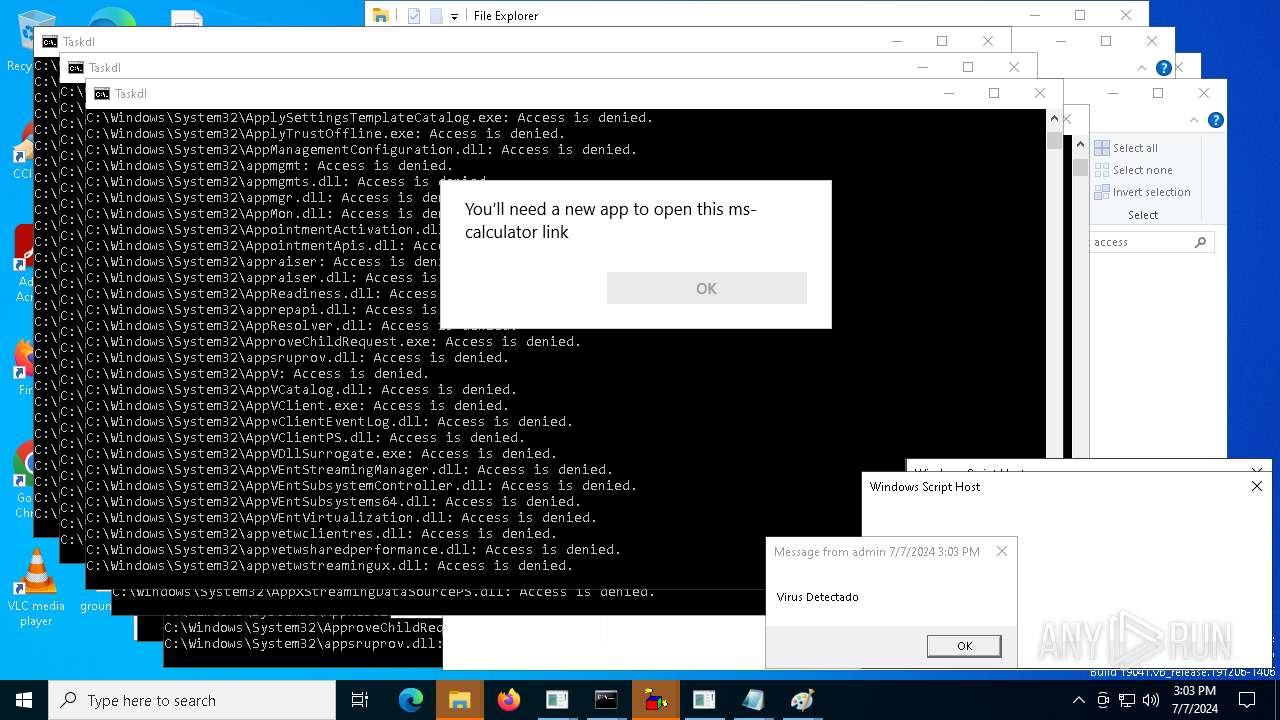
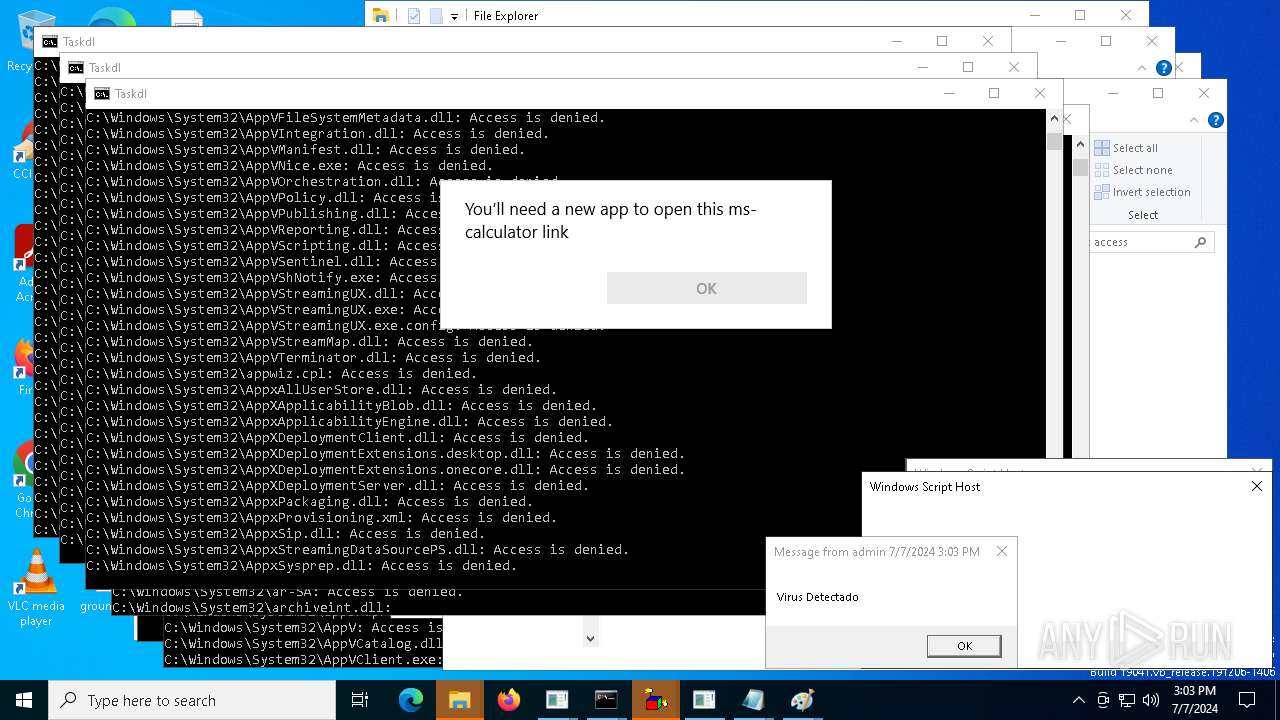
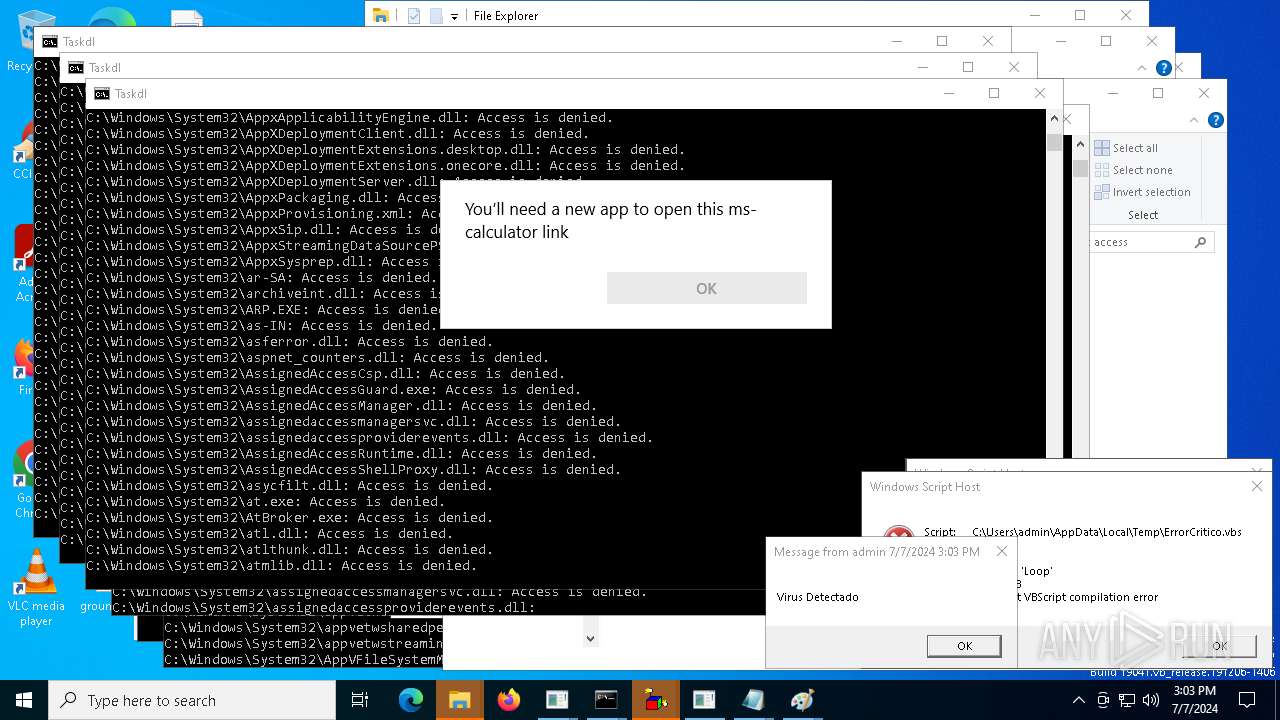
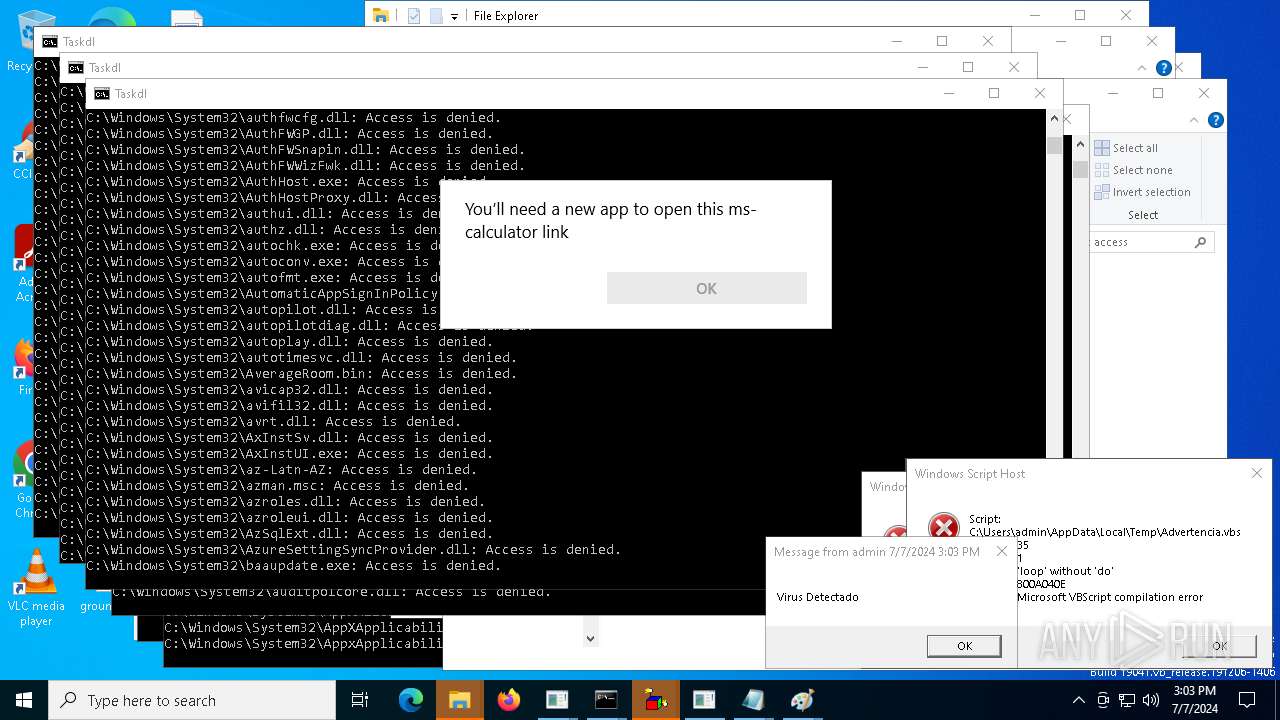
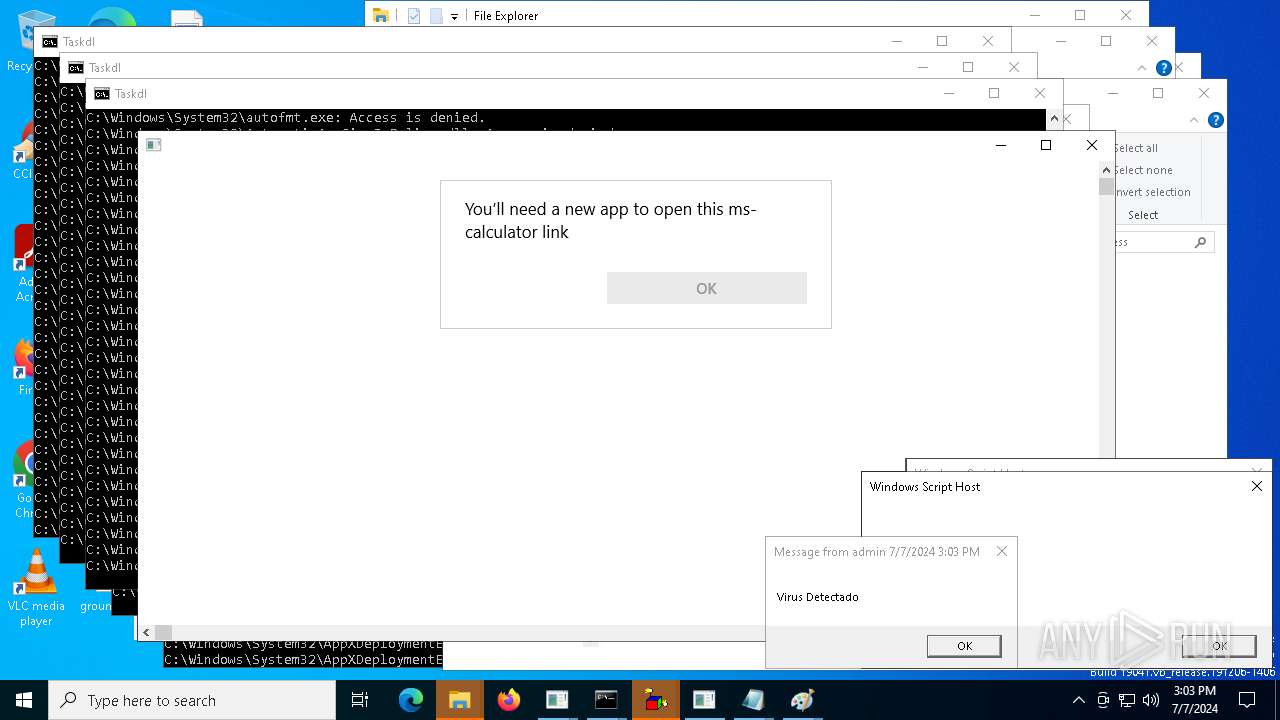
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2024, 15:03:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 8B6A377F9A67D5482A8EBA5708F45BB2 |
| SHA1: | 7197436525E568606850EE5E033C43AEA1C3BC91 |
| SHA256: | 6CA11C8B6442DB97C02F3B0F73DB61F58C96D52E8A880E33ABEE5B10807D993F |
| SSDEEP: | 3072:v7DhdC6kzWypvaQ0FxyNTBfqMXERseQF8:vBlkZvaF4NTBSAesPF8 |
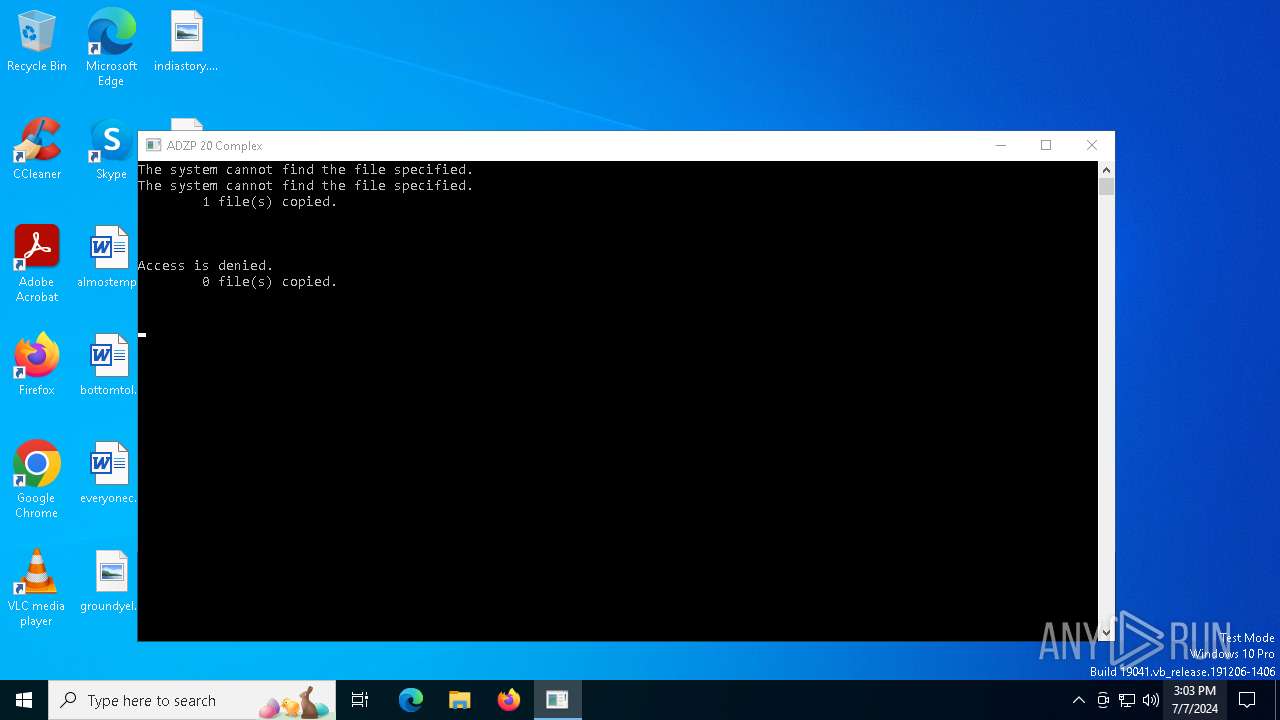
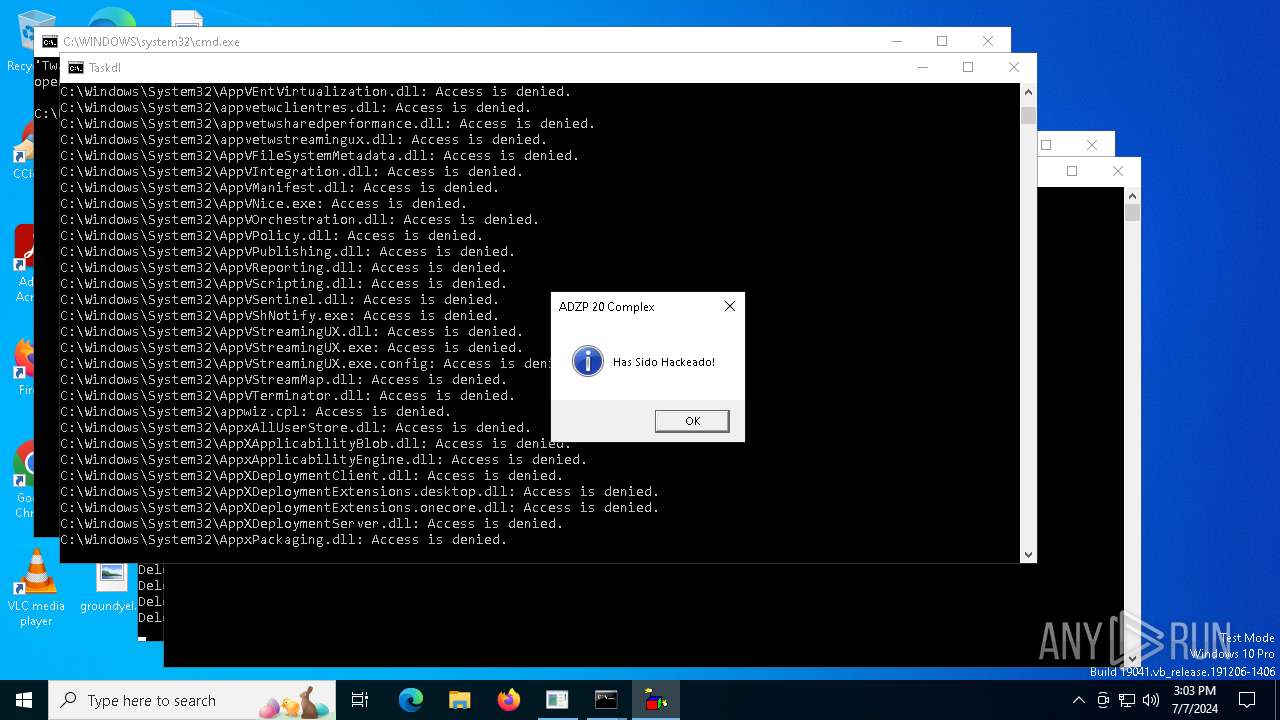
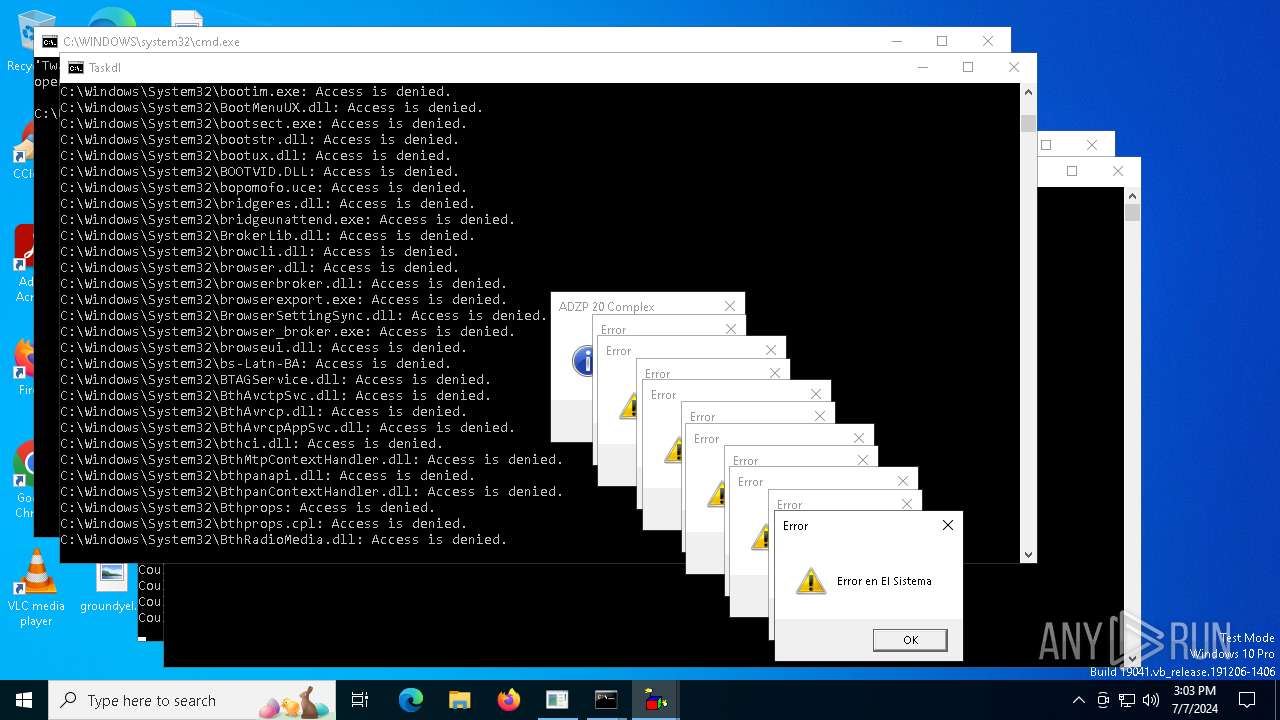
MALICIOUS
Drops the executable file immediately after the start
- ADZP 20 Complex.exe (PID: 5252)
Changes the autorun value in the registry
- reg.exe (PID: 648)
Actions looks like stealing of personal data
- cmd.exe (PID: 3104)
- cmd.exe (PID: 7564)
SUSPICIOUS
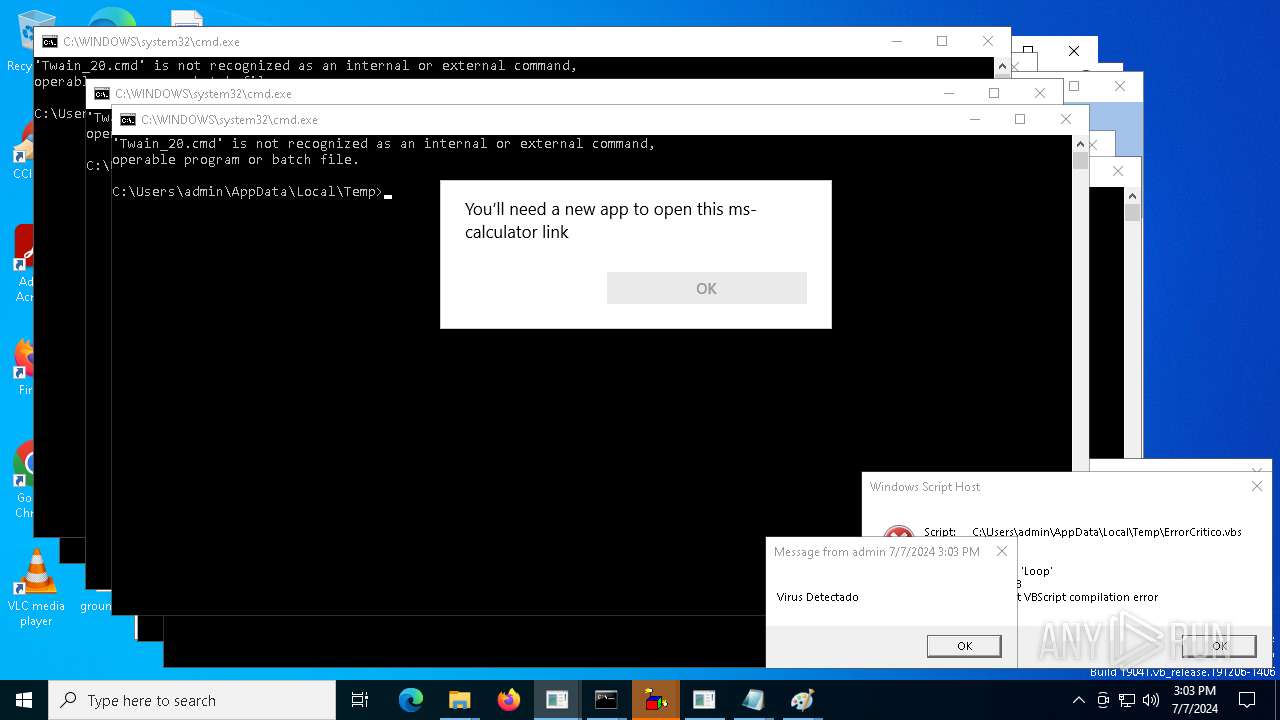
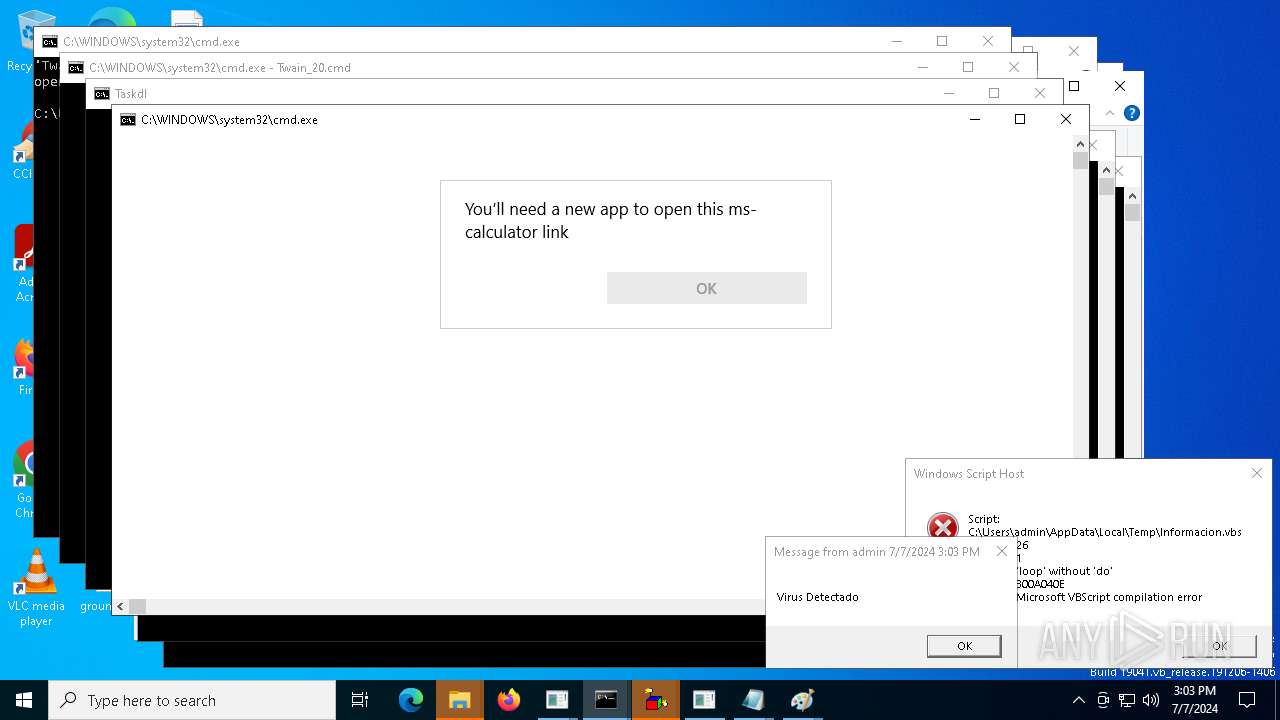
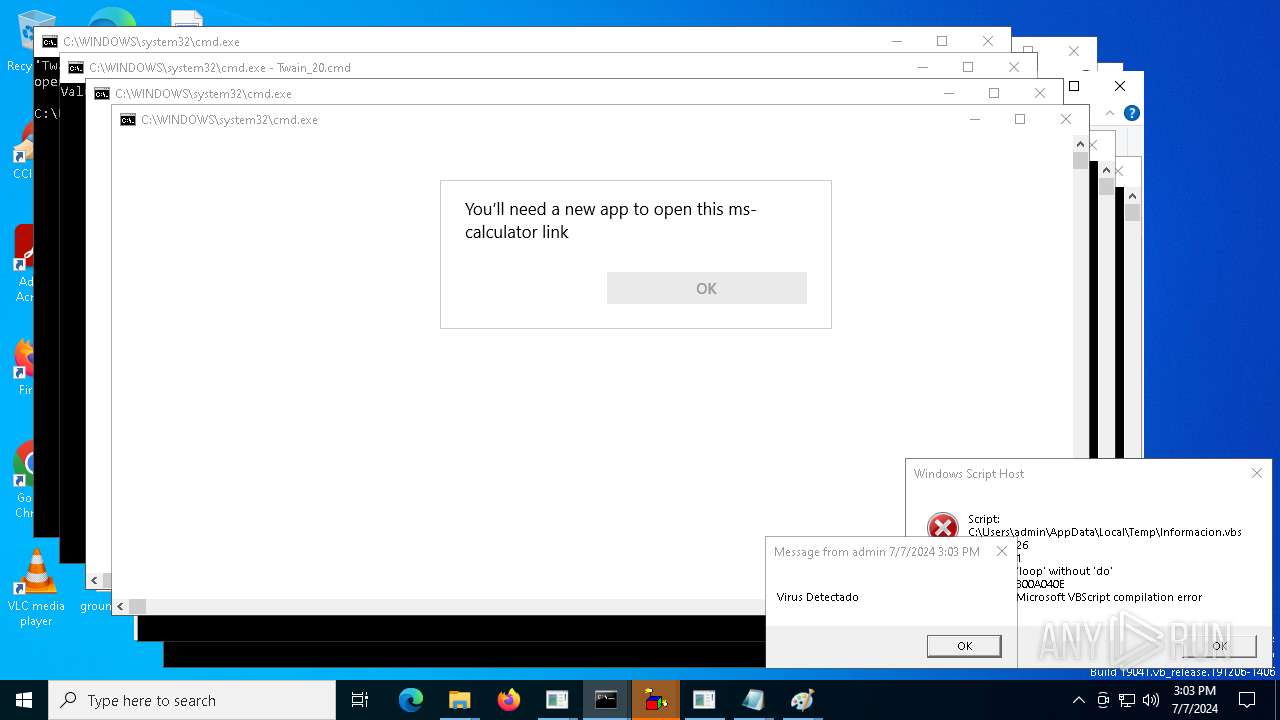
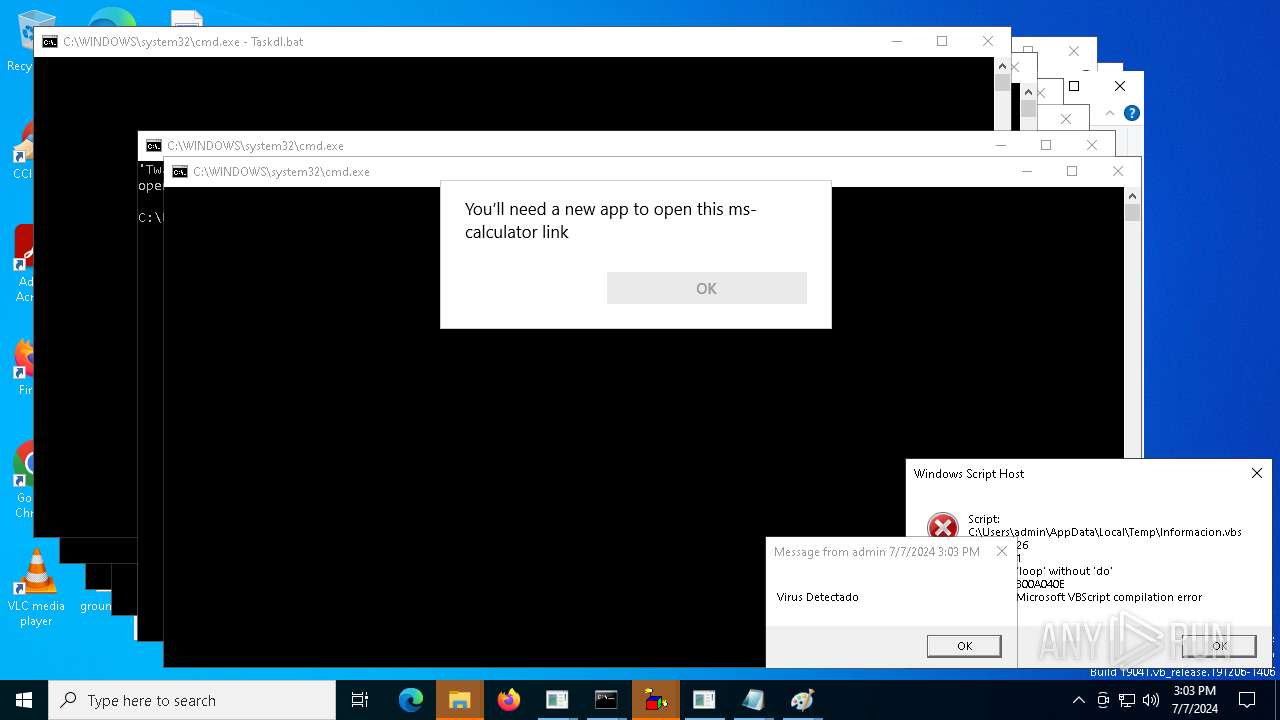
Executing commands from a ".bat" file
- ADZP 20 Complex.exe (PID: 5252)
- ADZP 20 Complex.exe (PID: 6304)
- cmd.exe (PID: 3104)
- ADZP 20 Complex.exe (PID: 7176)
- ADZP 20 Complex.exe (PID: 3156)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 7564)
- ADZP 20 Complex.exe (PID: 7728)
- ADZP 20 Complex.exe (PID: 8816)
- ADZP 20 Complex.exe (PID: 7772)
- ADZP 20 Complex.exe (PID: 10108)
- ADZP 20 Complex.exe (PID: 9944)
- ADZP 20 Complex.exe (PID: 10000)
- ADZP 20 Complex.exe (PID: 10312)
- ADZP 20 Complex.exe (PID: 9912)
- ADZP 20 Complex.exe (PID: 10872)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 9612)
- cmd.exe (PID: 10572)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 11308)
- cmd.exe (PID: 10984)
- cmd.exe (PID: 9908)
- ADZP 20 Complex.exe (PID: 15324)
- ADZP 20 Complex.exe (PID: 15708)
- ADZP 20 Complex.exe (PID: 6704)
Starts CMD.EXE for commands execution
- ADZP 20 Complex.exe (PID: 5252)
- cmd.exe (PID: 3104)
- ADZP 20 Complex.exe (PID: 3156)
- cmd.exe (PID: 7564)
- ADZP 20 Complex.exe (PID: 7176)
- cmd.exe (PID: 7460)
- ADZP 20 Complex.exe (PID: 6304)
- cmd.exe (PID: 7640)
- ADZP 20 Complex.exe (PID: 7728)
- ADZP 20 Complex.exe (PID: 8816)
- ADZP 20 Complex.exe (PID: 7772)
- ADZP 20 Complex.exe (PID: 10108)
- ADZP 20 Complex.exe (PID: 9944)
- ADZP 20 Complex.exe (PID: 10000)
- ADZP 20 Complex.exe (PID: 10312)
- ADZP 20 Complex.exe (PID: 9912)
- cmd.exe (PID: 10596)
- ADZP 20 Complex.exe (PID: 10872)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 10572)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 10984)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 9908)
- cmd.exe (PID: 9612)
- cmd.exe (PID: 11308)
- ADZP 20 Complex.exe (PID: 15324)
- ADZP 20 Complex.exe (PID: 15708)
- ADZP 20 Complex.exe (PID: 6704)
Executable content was dropped or overwritten
- cmd.exe (PID: 3104)
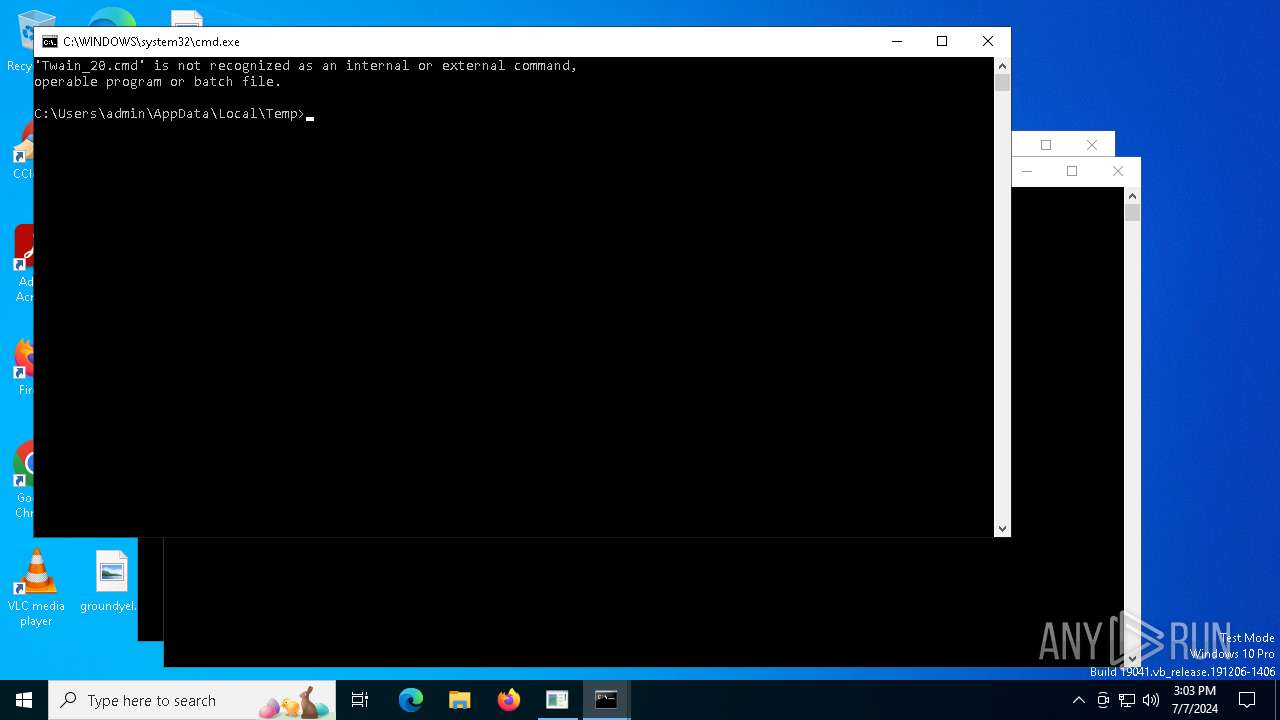
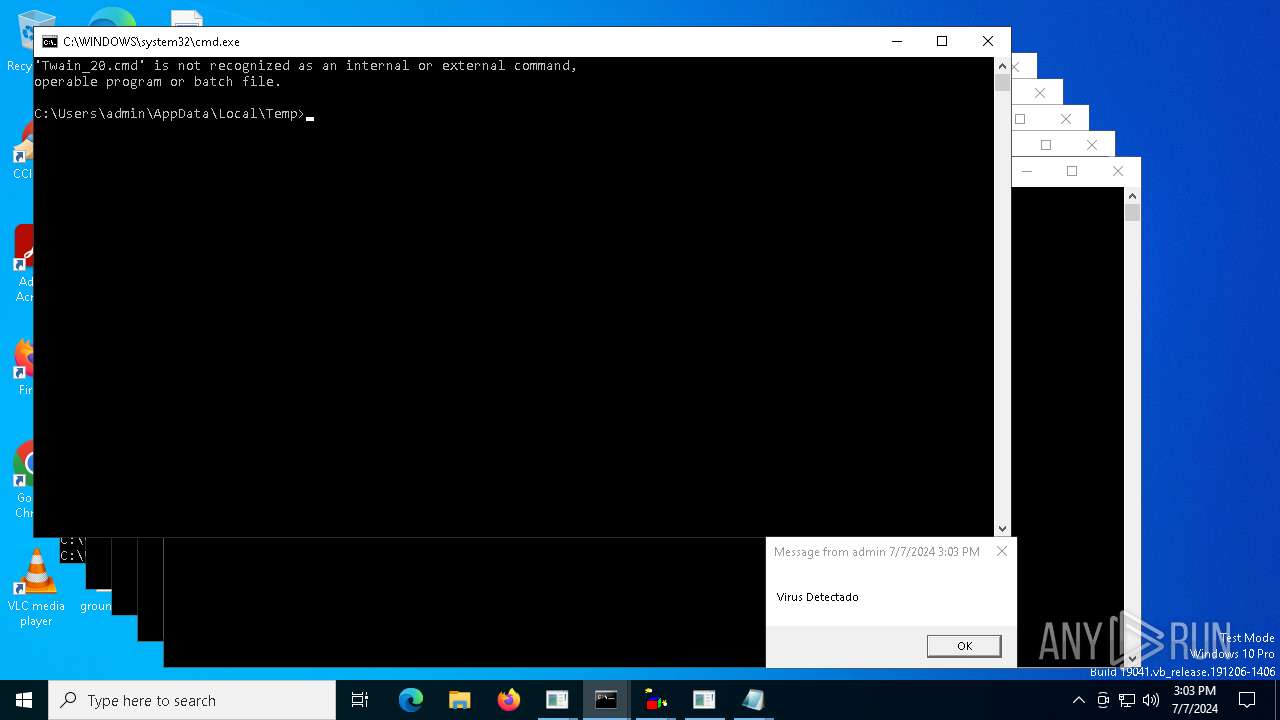
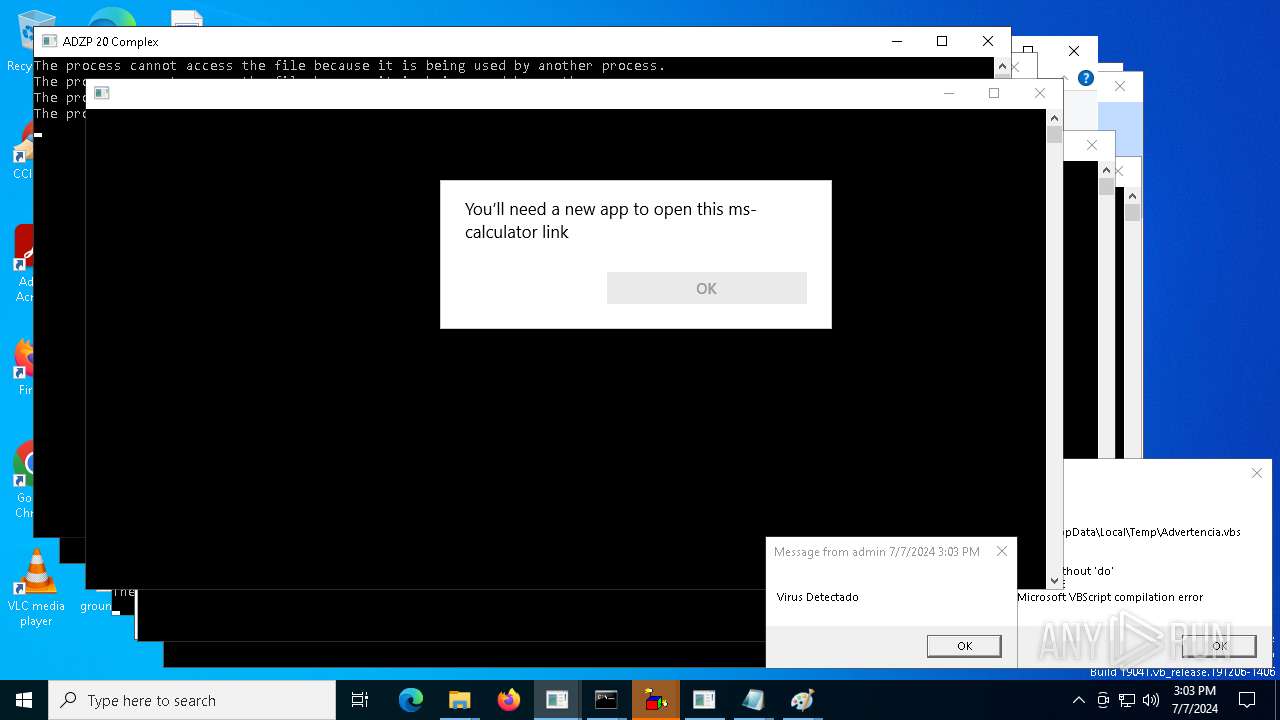
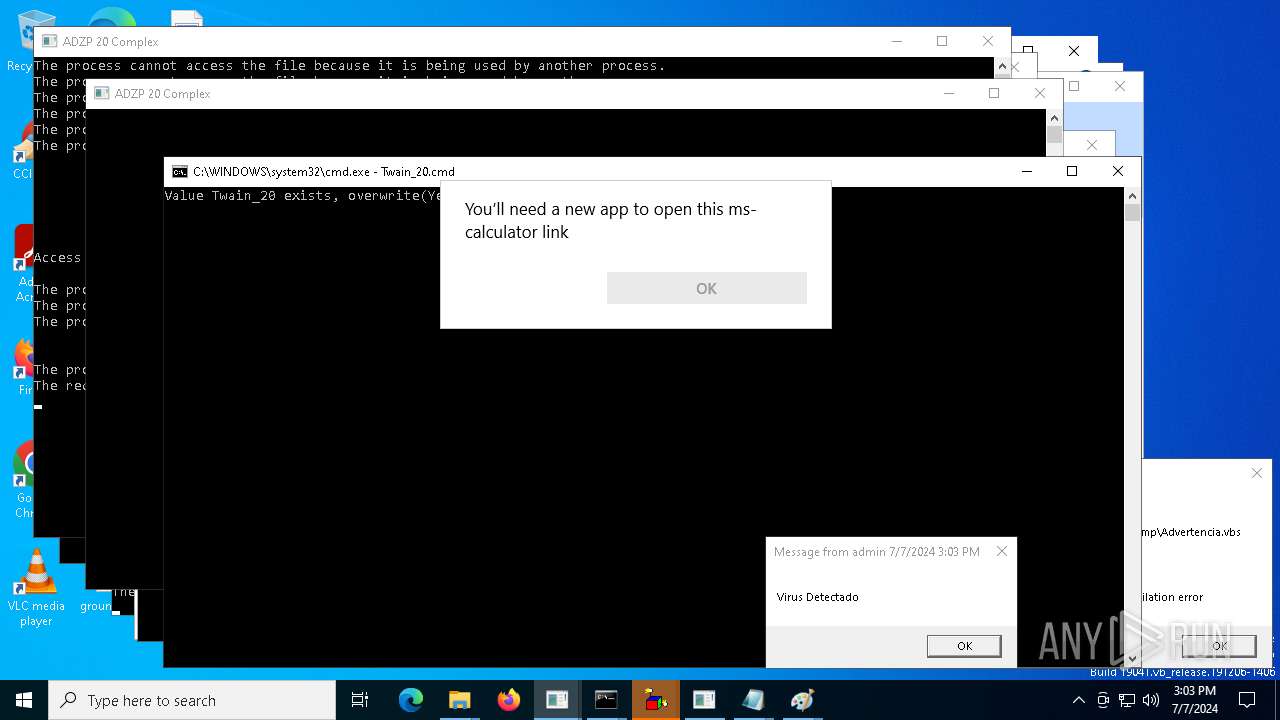
Executing commands from ".cmd" file
- cmd.exe (PID: 3104)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 10572)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 10984)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 9612)
- cmd.exe (PID: 11308)
- cmd.exe (PID: 9908)
Application launched itself
- cmd.exe (PID: 3104)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 10572)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 9612)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 10984)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 9908)
- cmd.exe (PID: 11308)
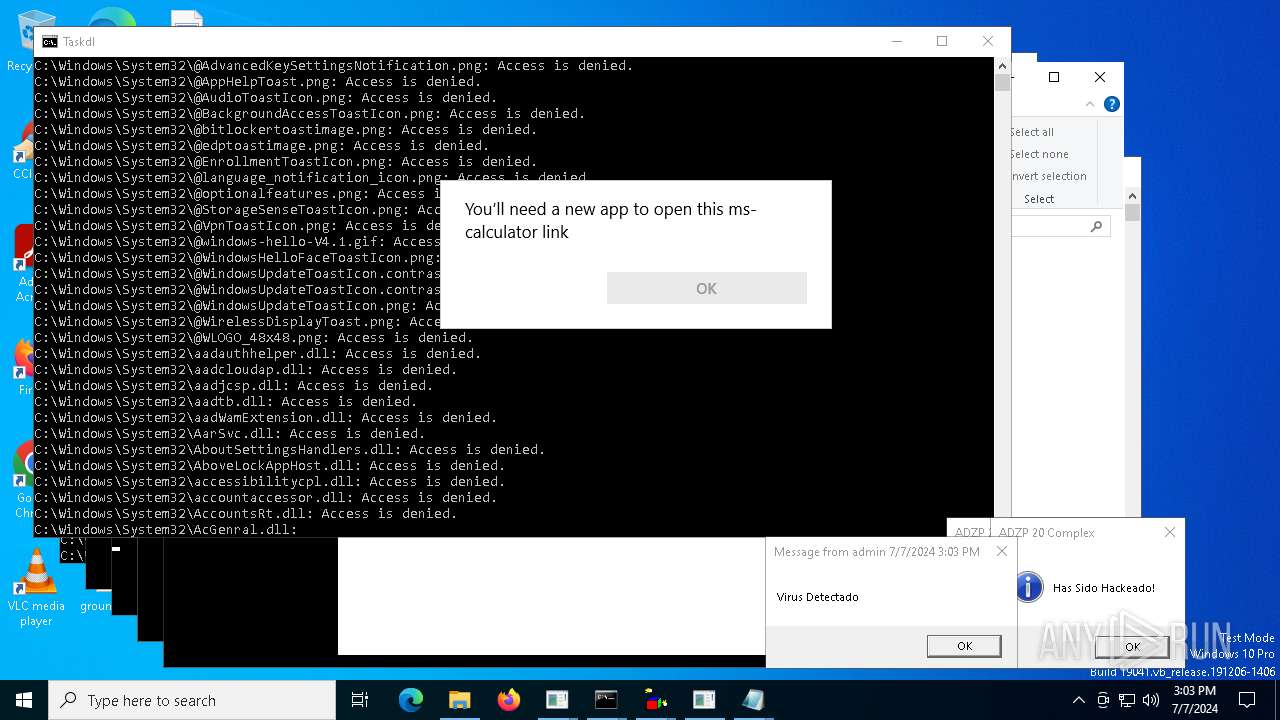
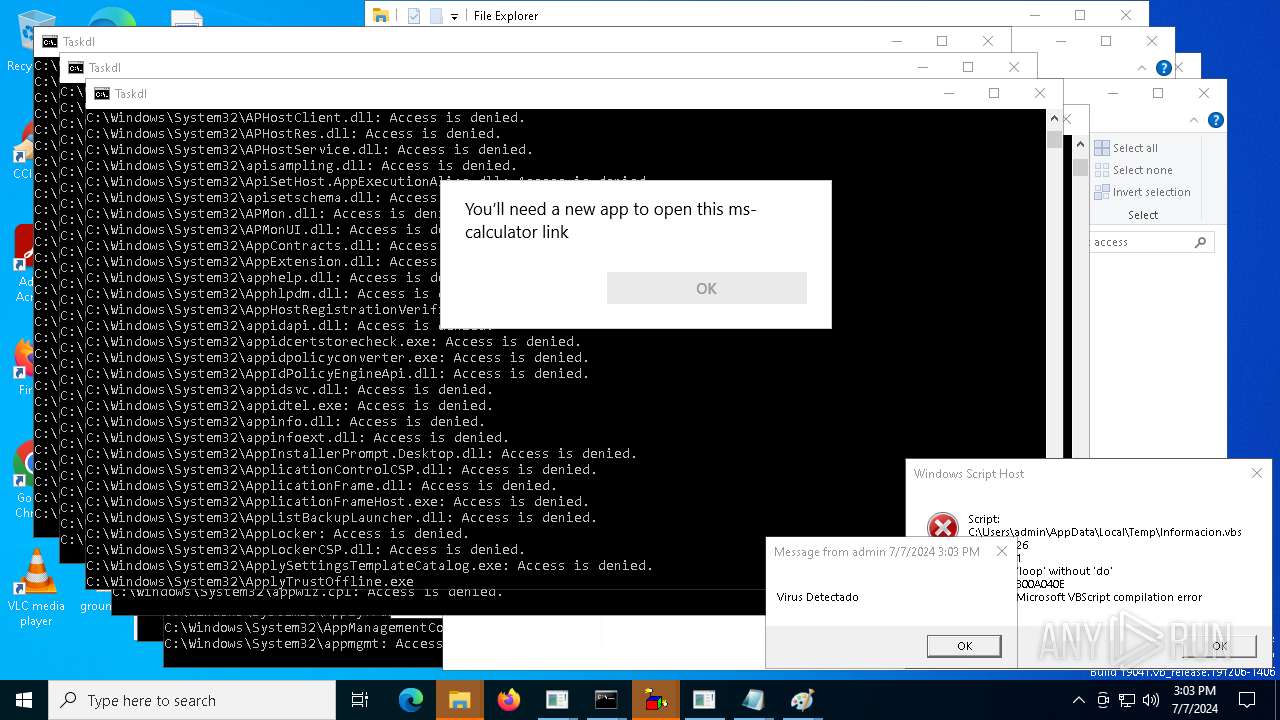
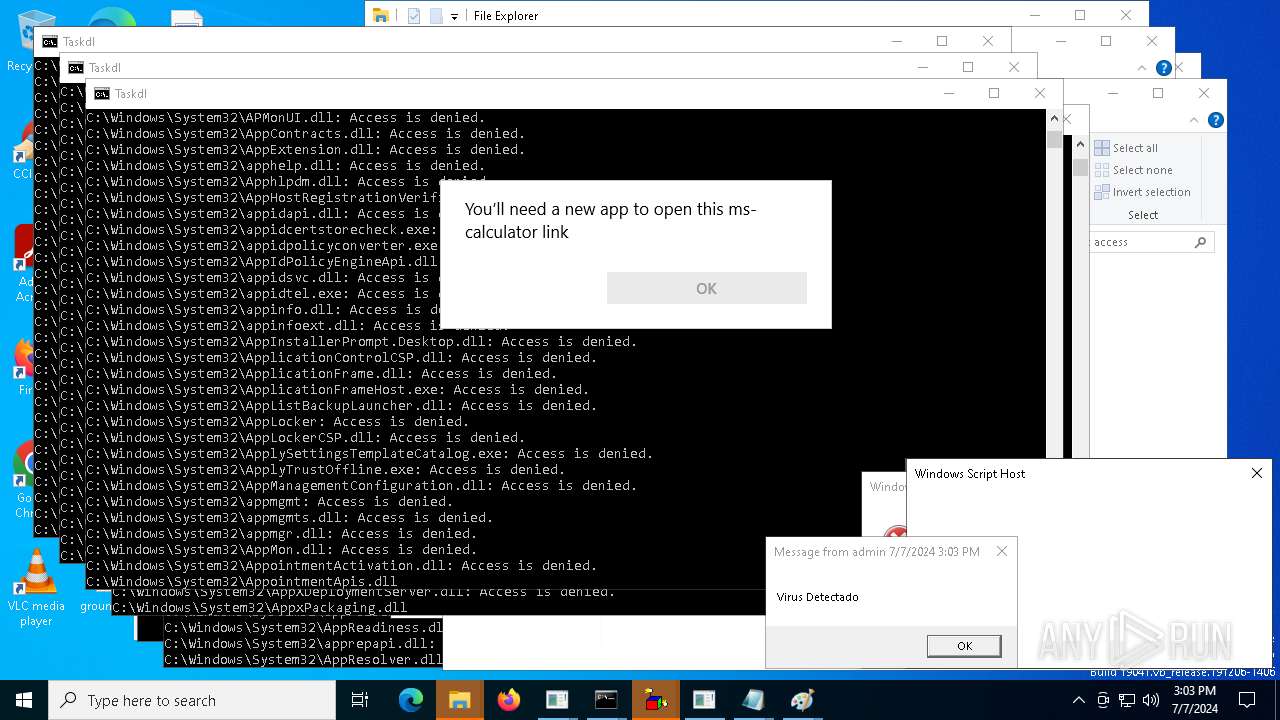
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 3104)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 10572)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 9612)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 10984)
- cmd.exe (PID: 9908)
- cmd.exe (PID: 11308)
- cmd.exe (PID: 10968)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1228)
- cmd.exe (PID: 3104)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 8060)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 11164)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 12164)
- cmd.exe (PID: 10572)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 9612)
- cmd.exe (PID: 11692)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 10984)
- cmd.exe (PID: 11308)
- cmd.exe (PID: 9908)
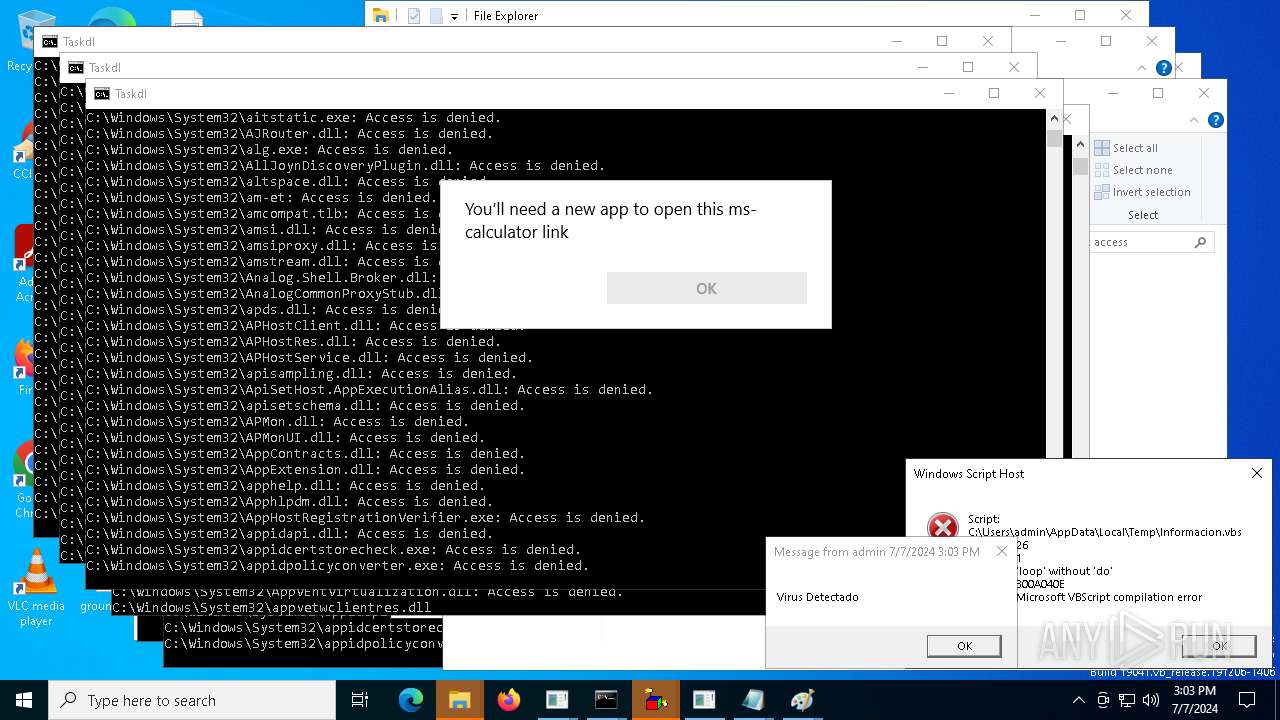
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3104)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 10572)
- cmd.exe (PID: 9612)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 10984)
- cmd.exe (PID: 11308)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 9908)
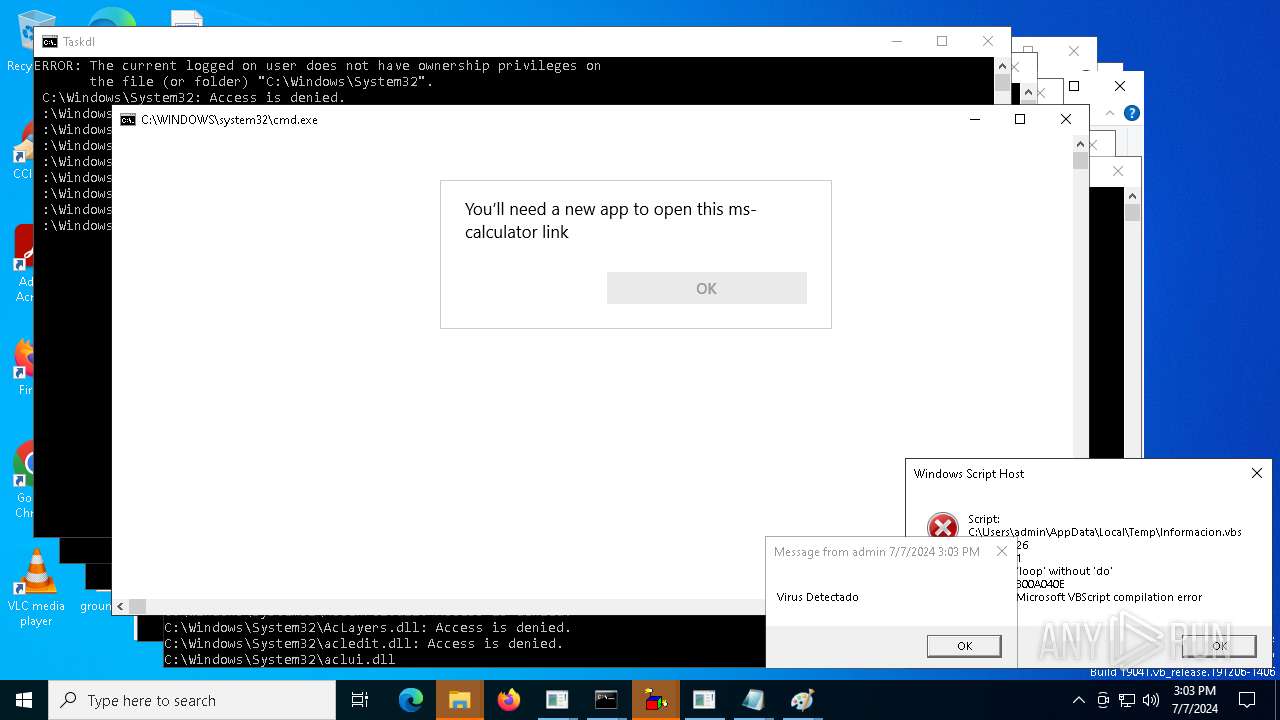
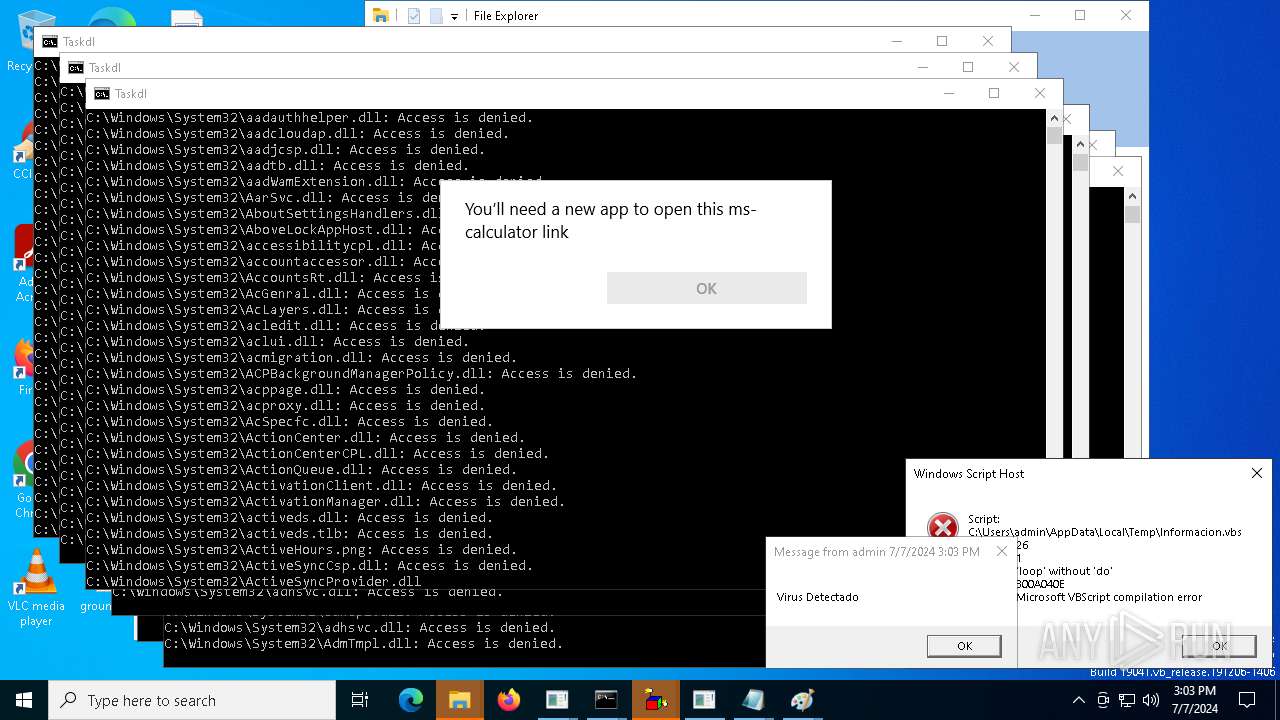
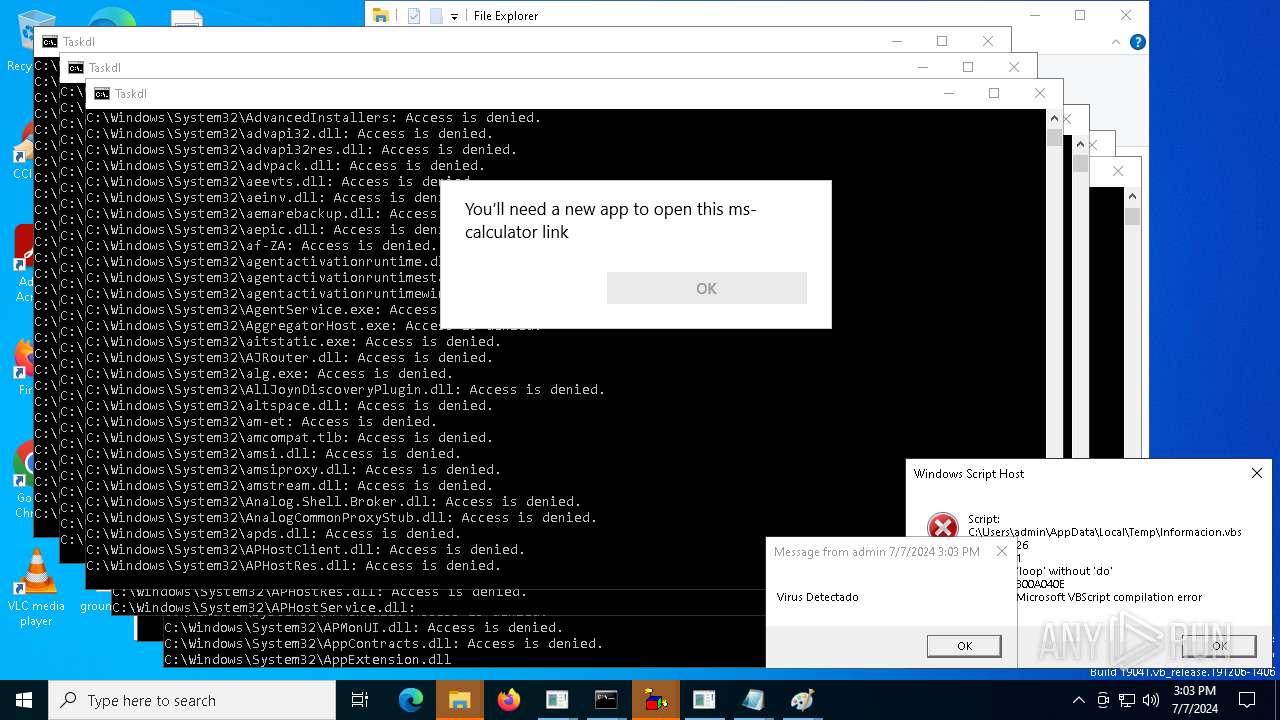
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 1740)
- cmd.exe (PID: 8548)
- cmd.exe (PID: 8872)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 12280)
- cmd.exe (PID: 12292)
- cmd.exe (PID: 12336)
- cmd.exe (PID: 10732)
- cmd.exe (PID: 13004)
- cmd.exe (PID: 12936)
- cmd.exe (PID: 12304)
- cmd.exe (PID: 13228)
- cmd.exe (PID: 13120)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3104)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 10984)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 9908)
- cmd.exe (PID: 11308)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 10572)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 9612)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 1740)
- cmd.exe (PID: 8548)
- cmd.exe (PID: 8872)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 12280)
- cmd.exe (PID: 12292)
- cmd.exe (PID: 12336)
- cmd.exe (PID: 10732)
- cmd.exe (PID: 12936)
- cmd.exe (PID: 12304)
- cmd.exe (PID: 13004)
- cmd.exe (PID: 13228)
- cmd.exe (PID: 13120)
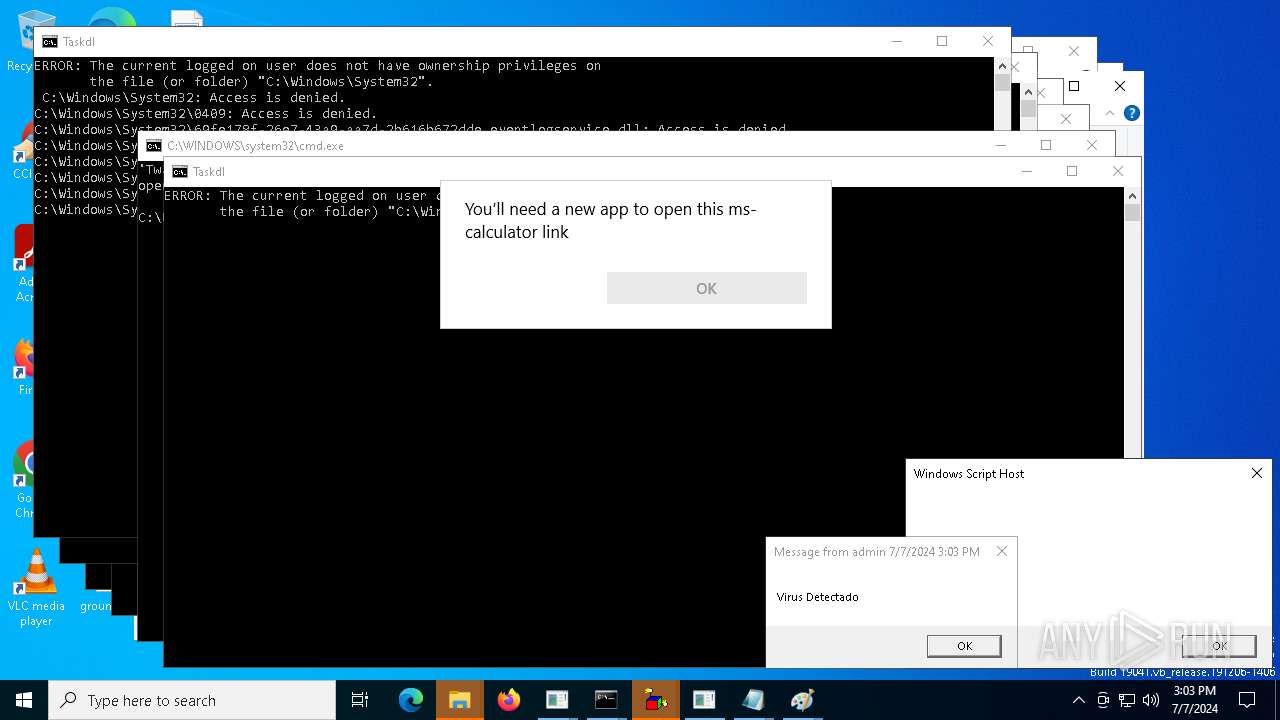
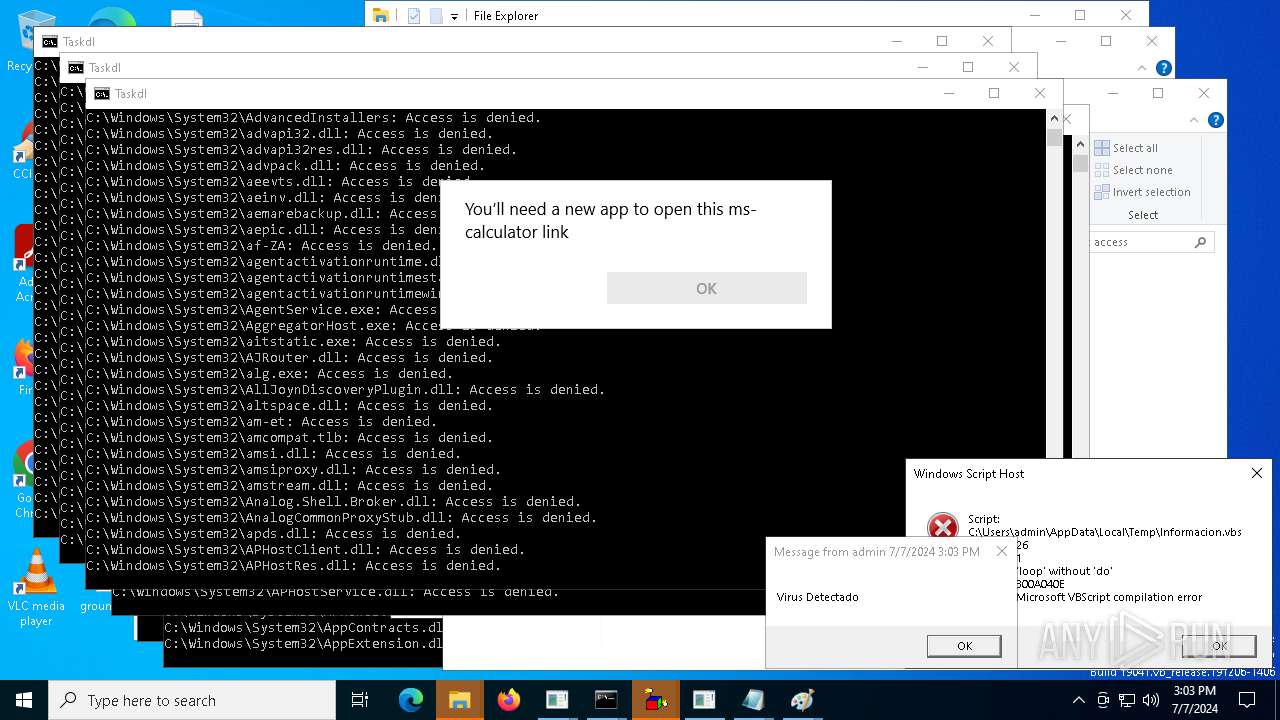
The process executes VB scripts
- cmd.exe (PID: 3104)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 9612)
- cmd.exe (PID: 10572)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 10984)
- cmd.exe (PID: 11308)
- cmd.exe (PID: 10968)
- cmd.exe (PID: 9908)
Process uses IPCONFIG to discard the IP address configuration
- cmd.exe (PID: 3104)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 9612)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 10572)
- cmd.exe (PID: 9908)
- cmd.exe (PID: 11308)
- cmd.exe (PID: 10984)
- cmd.exe (PID: 10968)
INFO
Create files in a temporary directory
- ADZP 20 Complex.exe (PID: 5252)
- cmd.exe (PID: 3104)
- ADZP 20 Complex.exe (PID: 6304)
- ADZP 20 Complex.exe (PID: 7176)
- cmd.exe (PID: 7640)
- ADZP 20 Complex.exe (PID: 3156)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7564)
- ADZP 20 Complex.exe (PID: 7728)
- ADZP 20 Complex.exe (PID: 8816)
- ADZP 20 Complex.exe (PID: 7772)
- ADZP 20 Complex.exe (PID: 10312)
- ADZP 20 Complex.exe (PID: 10108)
- ADZP 20 Complex.exe (PID: 9944)
- ADZP 20 Complex.exe (PID: 10000)
- cmd.exe (PID: 10596)
- ADZP 20 Complex.exe (PID: 9912)
- ADZP 20 Complex.exe (PID: 10872)
Checks supported languages
- ADZP 20 Complex.exe (PID: 5252)
- ADZP 20 Complex.exe (PID: 6304)
- ADZP 20 Complex.exe (PID: 7176)
- ADZP 20 Complex.exe (PID: 3156)
- ADZP 20 Complex.exe (PID: 7772)
- ADZP 20 Complex.exe (PID: 8816)
- ADZP 20 Complex.exe (PID: 7728)
- ADZP 20 Complex.exe (PID: 10108)
- ADZP 20 Complex.exe (PID: 9944)
- ADZP 20 Complex.exe (PID: 10000)
- ADZP 20 Complex.exe (PID: 10312)
- ADZP 20 Complex.exe (PID: 9912)
- ADZP 20 Complex.exe (PID: 10872)
Drops the executable file immediately after the start
- cmd.exe (PID: 3104)
Reads Microsoft Office registry keys
- cmd.exe (PID: 3104)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7640)
Reads security settings of Internet Explorer
- cmd.exe (PID: 3104)
- calc.exe (PID: 6332)
- calc.exe (PID: 6256)
- calc.exe (PID: 7204)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7460)
- OpenWith.exe (PID: 7772)
- OpenWith.exe (PID: 7280)
- OpenWith.exe (PID: 8264)
- cmd.exe (PID: 7640)
- calc.exe (PID: 5224)
- calc.exe (PID: 7496)
- calc.exe (PID: 7724)
- calc.exe (PID: 9960)
- calc.exe (PID: 9608)
- calc.exe (PID: 10152)
- calc.exe (PID: 10708)
- calc.exe (PID: 10464)
- OpenWith.exe (PID: 9748)
- OpenWith.exe (PID: 9900)
- calc.exe (PID: 11008)
- OpenWith.exe (PID: 10336)
- OpenWith.exe (PID: 10488)
- OpenWith.exe (PID: 10548)
- OpenWith.exe (PID: 9836)
- OpenWith.exe (PID: 11252)
- OpenWith.exe (PID: 11096)
- OpenWith.exe (PID: 9288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:30 08:52:45+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 70656 |
| InitializedDataSize: | 36864 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Total processes
638
Monitored processes
511
Malicious processes
26
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
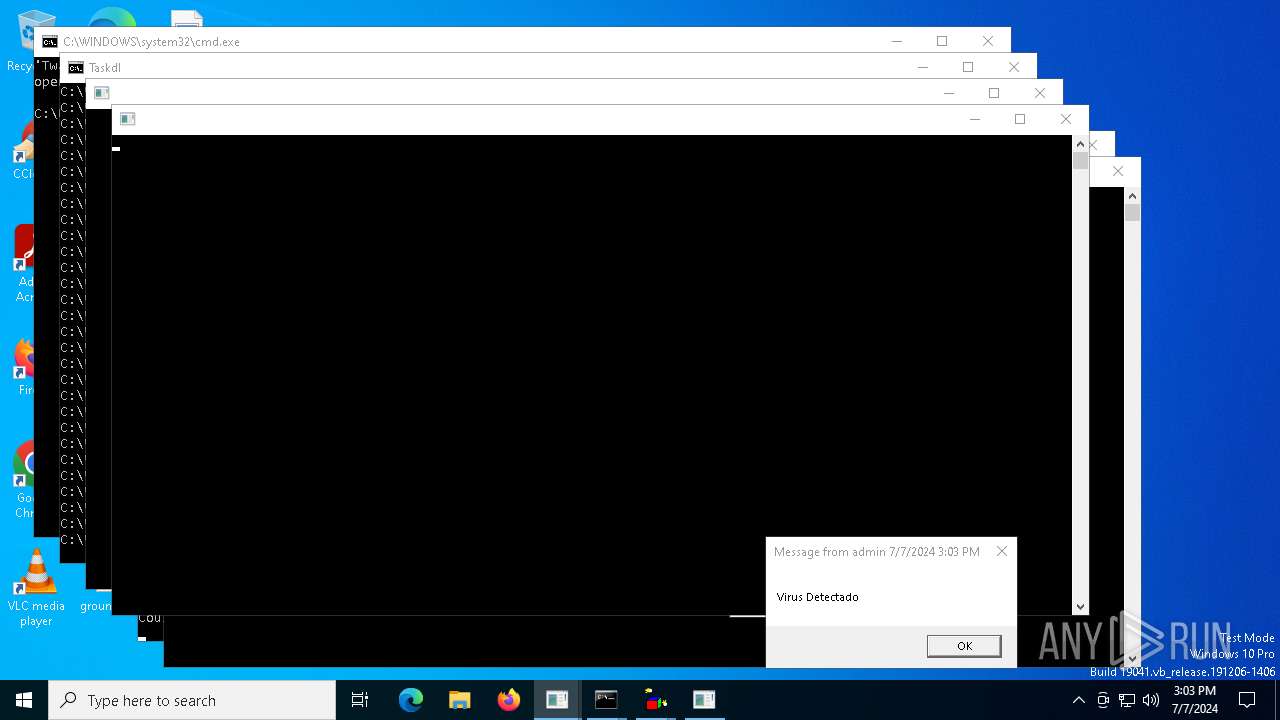
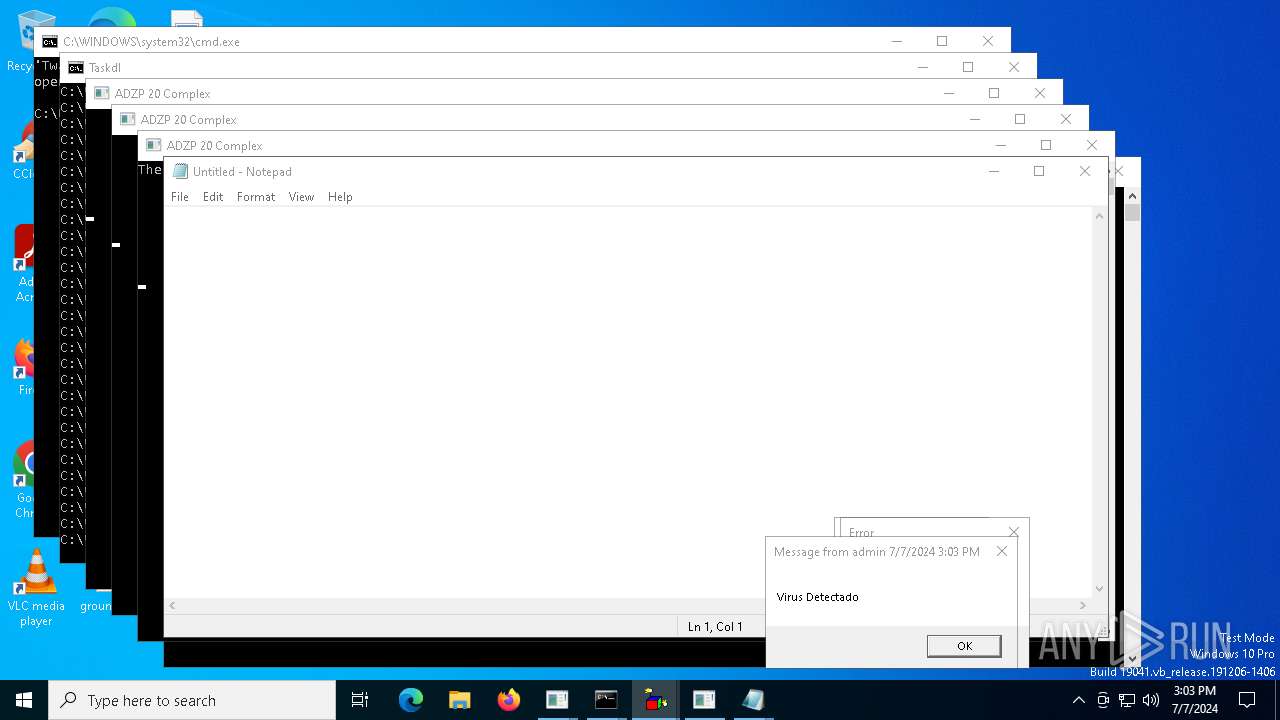
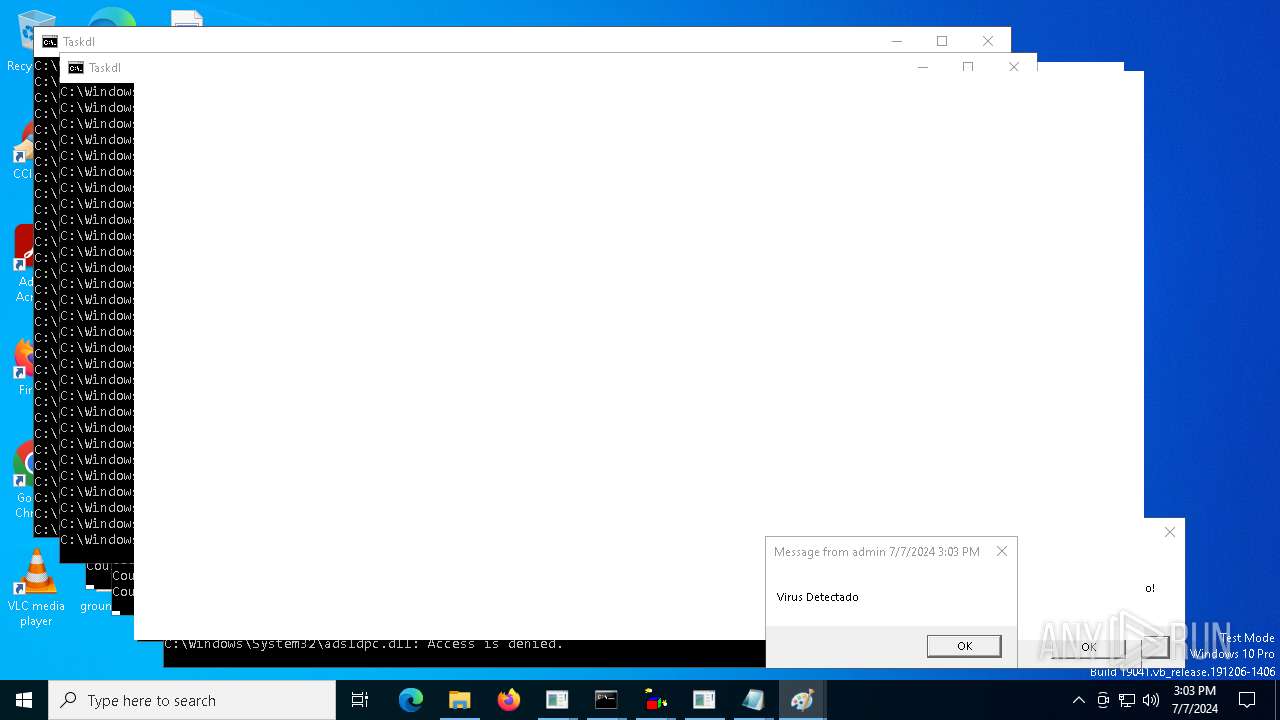
| 240 | msg * Virus Detectado | C:\Windows\System32\msg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Message Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 648 | REG ADD HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v Twain_20 /t REG_SZ /d "C:\Users\admin\AppData\Local\Temp\Twain_20.cmd" | C:\Windows\System32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
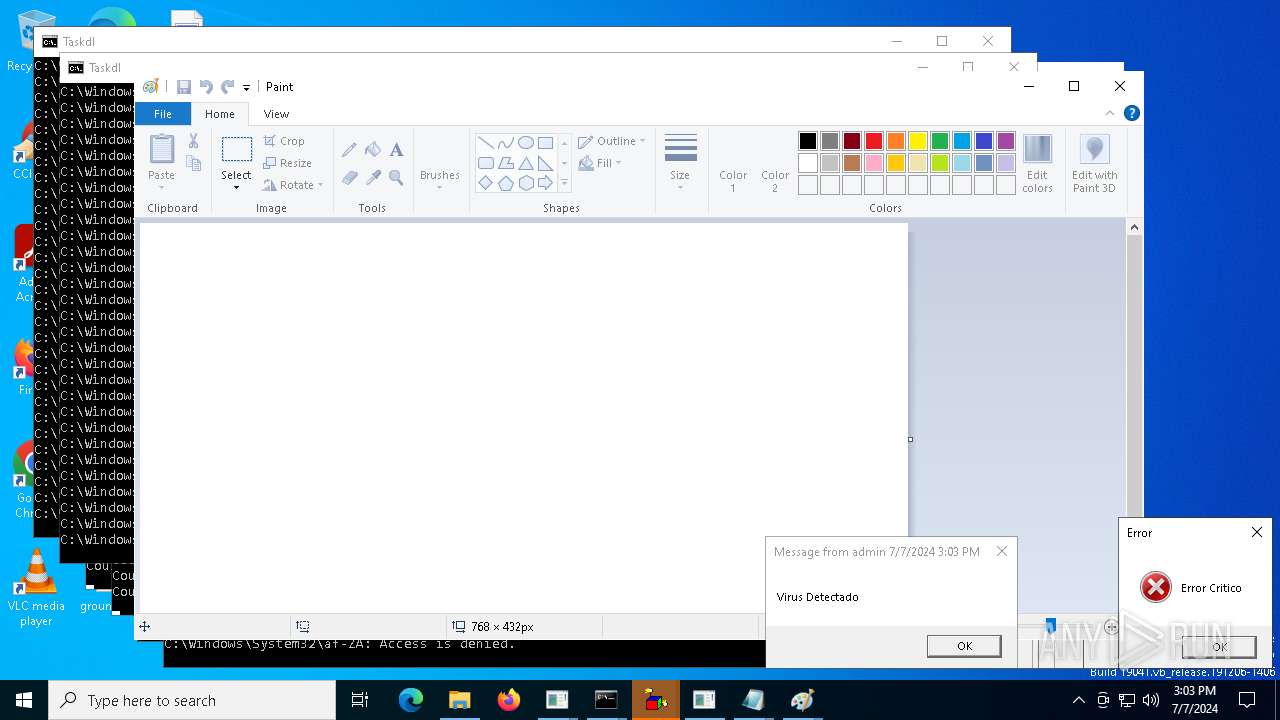
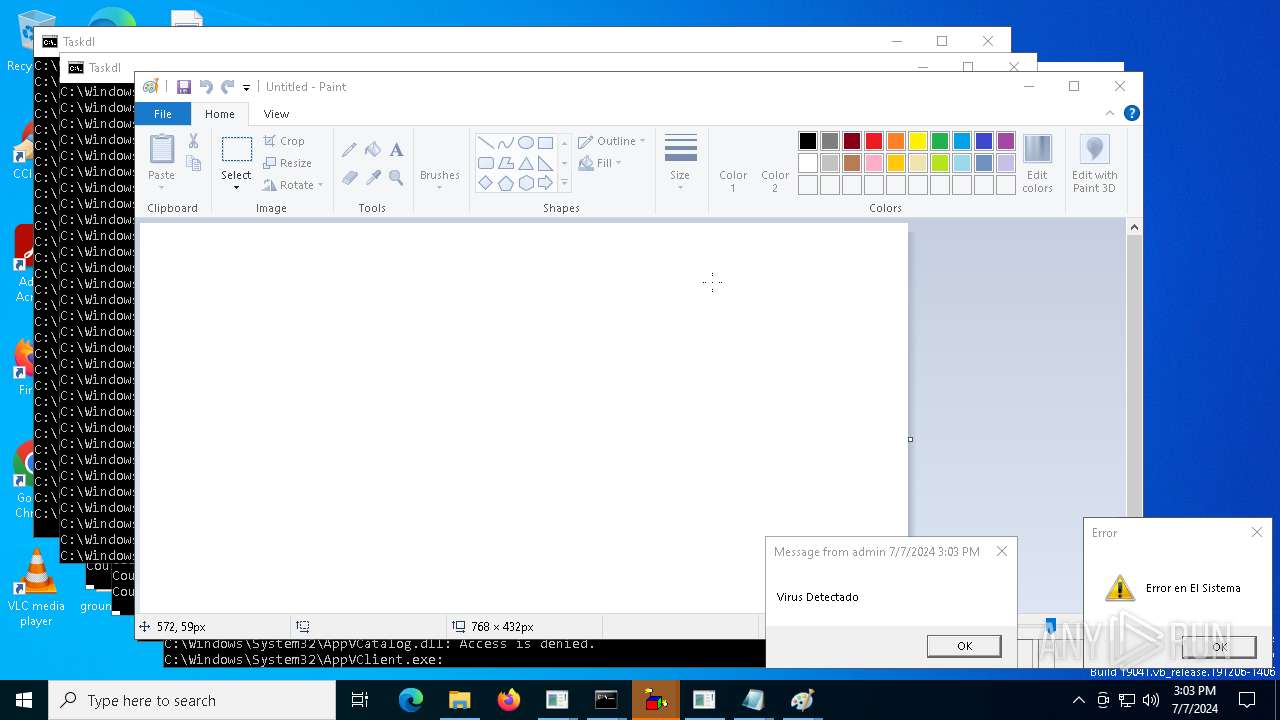
| 780 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\ErrorCritico.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 900 | notepad | C:\Windows\System32\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1120 | notepad | C:\Windows\System32\notepad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\system32\cmd.exe /K Twain_20.cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1740 | netsh advfirewall set publicprofile state off | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
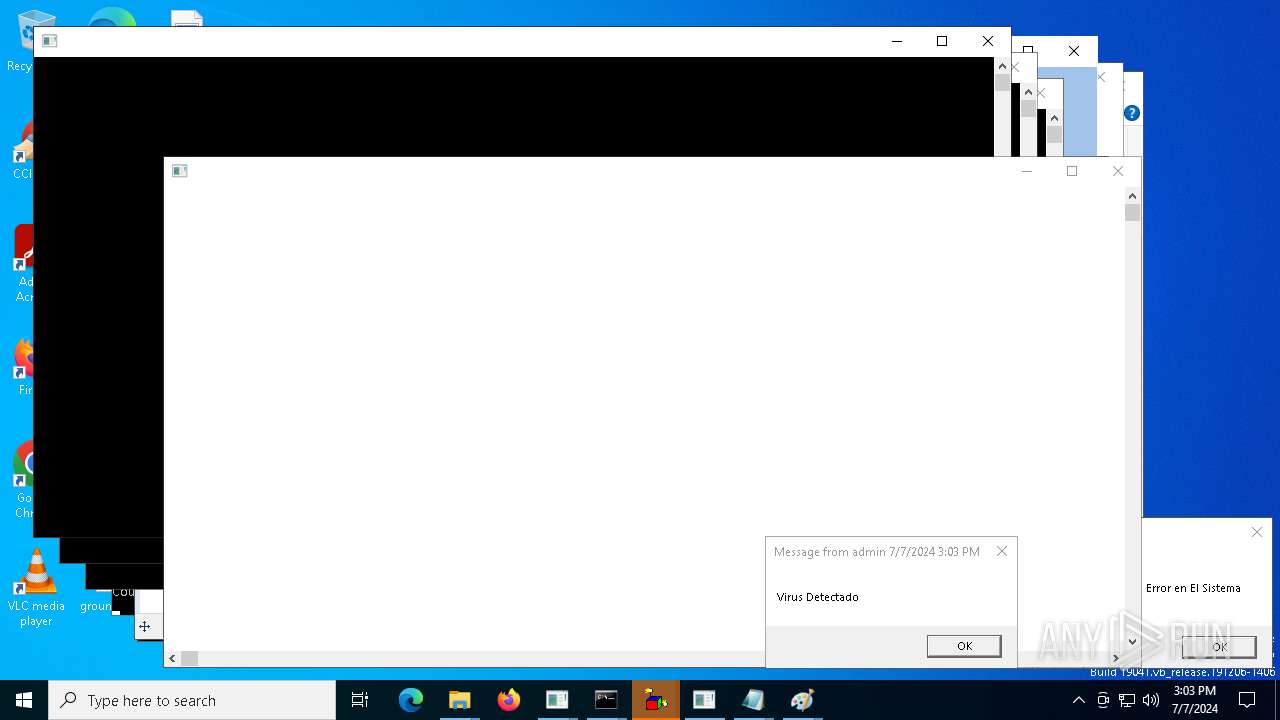
| 1740 | C:\WINDOWS\system32\cmd.exe /K Taskdl.bat | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1776 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Advertencia.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 | |||||||||||||||
Total events
93 892
Read events
93 690
Write events
202
Delete events
0
Modification events
| (PID) Process: | (3104) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (3104) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3104) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3104) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3104) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (648) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Twain_20 |
Value: C:\Users\admin\AppData\Local\Temp\Twain_20.cmd | |||
| (PID) Process: | (6332) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6332) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6332) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6332) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
0
Text files
28
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5252 | ADZP 20 Complex.exe | C:\Users\admin\AppData\Local\Temp\EA96.tmp\EA97.tmp\EA98.bat | text | |
MD5:190E7CFA7D6DE532BA4498CA3D38B47D | SHA256:FAEE2B0AC2218435A6973B87277B29010C988EFEFDCD7FE0E107808C2CC0F282 | |||
| 3104 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Taskdl.bat | text | |
MD5:9905E5A33C6EDD8EB5F59780AFBF74DE | SHA256:C134B2F85415BA5CFCE3E3FE4745688335745A9BB22152AC8F5C77F190D8AEE3 | |||
| 3104 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Twain_20.dll | executable | |
MD5:8B6A377F9A67D5482A8EBA5708F45BB2 | SHA256:6CA11C8B6442DB97C02F3B0F73DB61F58C96D52E8A880E33ABEE5B10807D993F | |||
| 3104 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Informacion.vbs | text | |
MD5:08121EA7E3B2EB7EDFC85252B937AAEB | SHA256:31CD4463ECC62DC846DBAEE0A5446D4BF11100BEFF1B01AE88E234B6C29329C2 | |||
| 3104 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Autorun.inf | ini | |
MD5:9A9FED65AE5AECB2E2723DCCF0F0B34E | SHA256:B9EB9A01994285B8A10189321D0CF6055AD92AE659D6603F7D1FE835F39CA1D2 | |||
| 3104 | cmd.exe | C:\Users\admin\AppData\Local\Temp\windowswimn32.bat | text | |
MD5:9905E5A33C6EDD8EB5F59780AFBF74DE | SHA256:C134B2F85415BA5CFCE3E3FE4745688335745A9BB22152AC8F5C77F190D8AEE3 | |||
| 3104 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Taskse.exe | text | |
MD5:B161DA0A6D1AA5263AA79E92FED50518 | SHA256:7F93DD640672F35E089E1E97A7E73910E7EBD794A87C72AE4EC5B089C2F68B30 | |||
| 6304 | ADZP 20 Complex.exe | C:\Users\admin\AppData\Local\Temp\FA65.tmp\FA66.tmp\FA67.bat | text | |
MD5:190E7CFA7D6DE532BA4498CA3D38B47D | SHA256:FAEE2B0AC2218435A6973B87277B29010C988EFEFDCD7FE0E107808C2CC0F282 | |||
| 10000 | ADZP 20 Complex.exe | C:\Users\admin\AppData\Local\Temp\1995.tmp\1996.tmp\1997.bat | text | |
MD5:190E7CFA7D6DE532BA4498CA3D38B47D | SHA256:FAEE2B0AC2218435A6973B87277B29010C988EFEFDCD7FE0E107808C2CC0F282 | |||
| 7772 | ADZP 20 Complex.exe | C:\Users\admin\AppData\Local\Temp\1772.tmp\1773.tmp\1784.bat | text | |
MD5:190E7CFA7D6DE532BA4498CA3D38B47D | SHA256:FAEE2B0AC2218435A6973B87277B29010C988EFEFDCD7FE0E107808C2CC0F282 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
31
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
3652 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2072 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3828 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4656 | SearchApp.exe | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3652 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3652 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1060 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
3040 | OfficeClickToRun.exe | 52.111.227.14:443 | nexusrules.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |