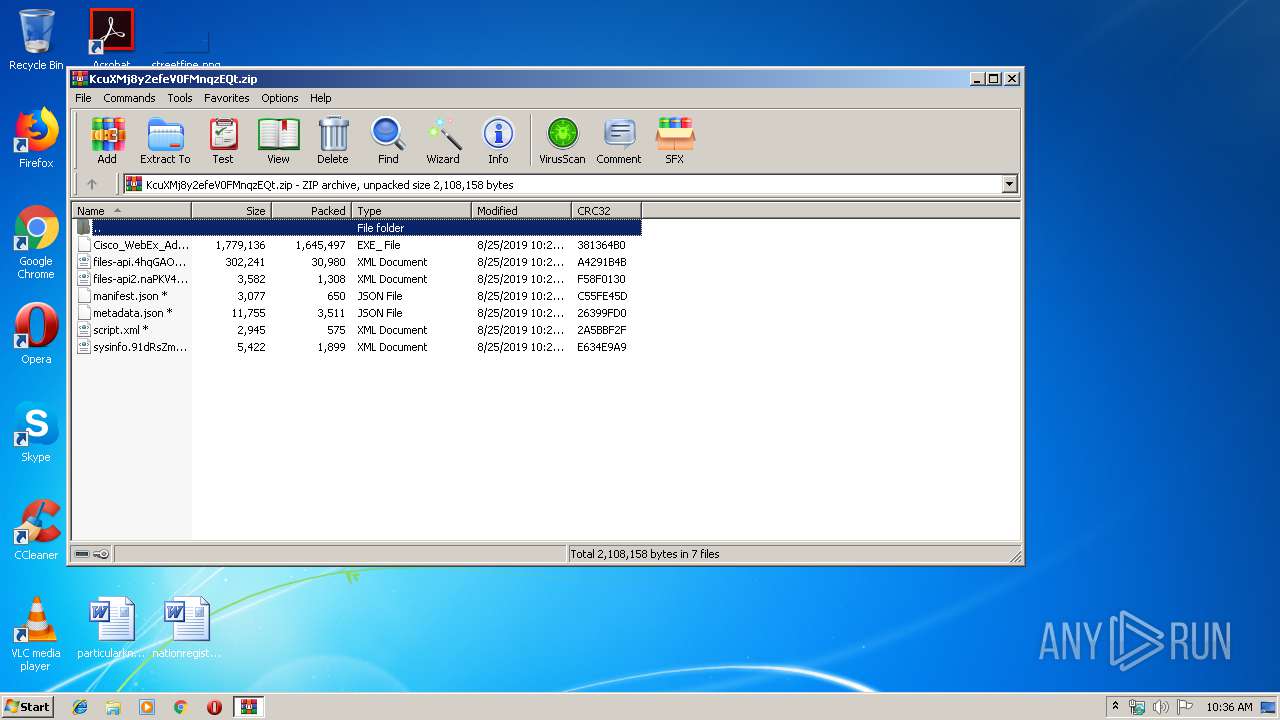
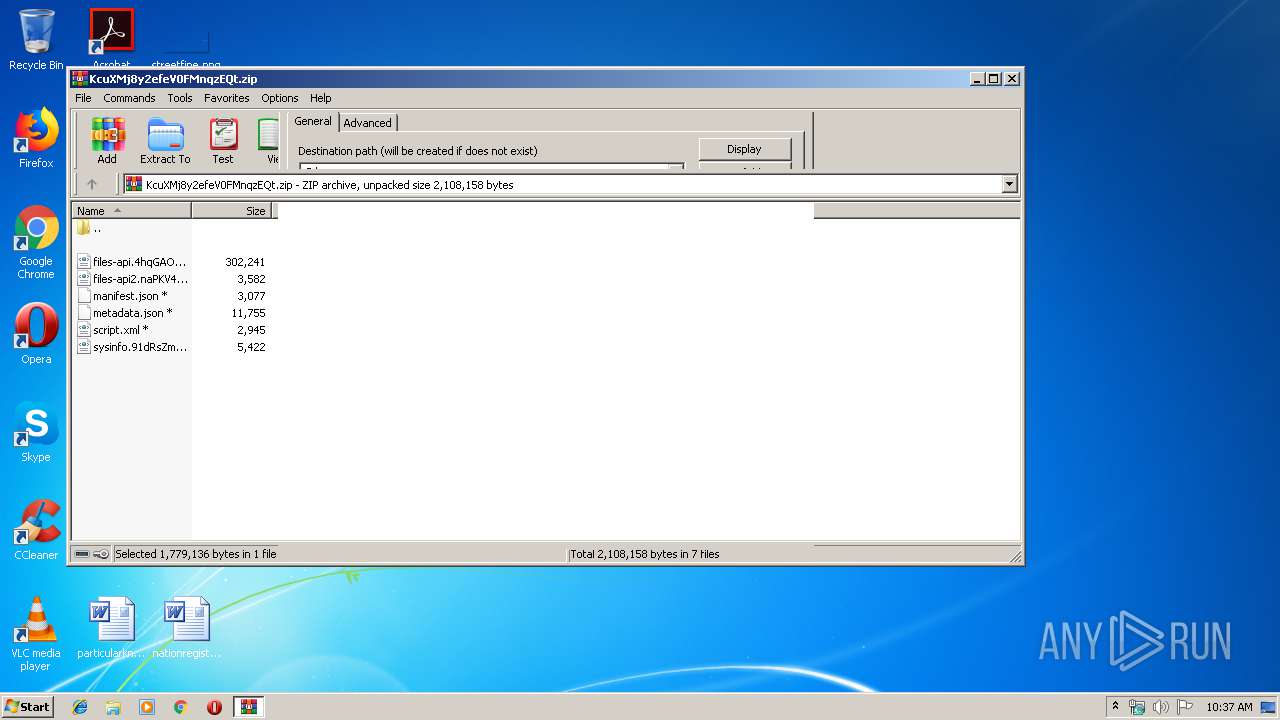
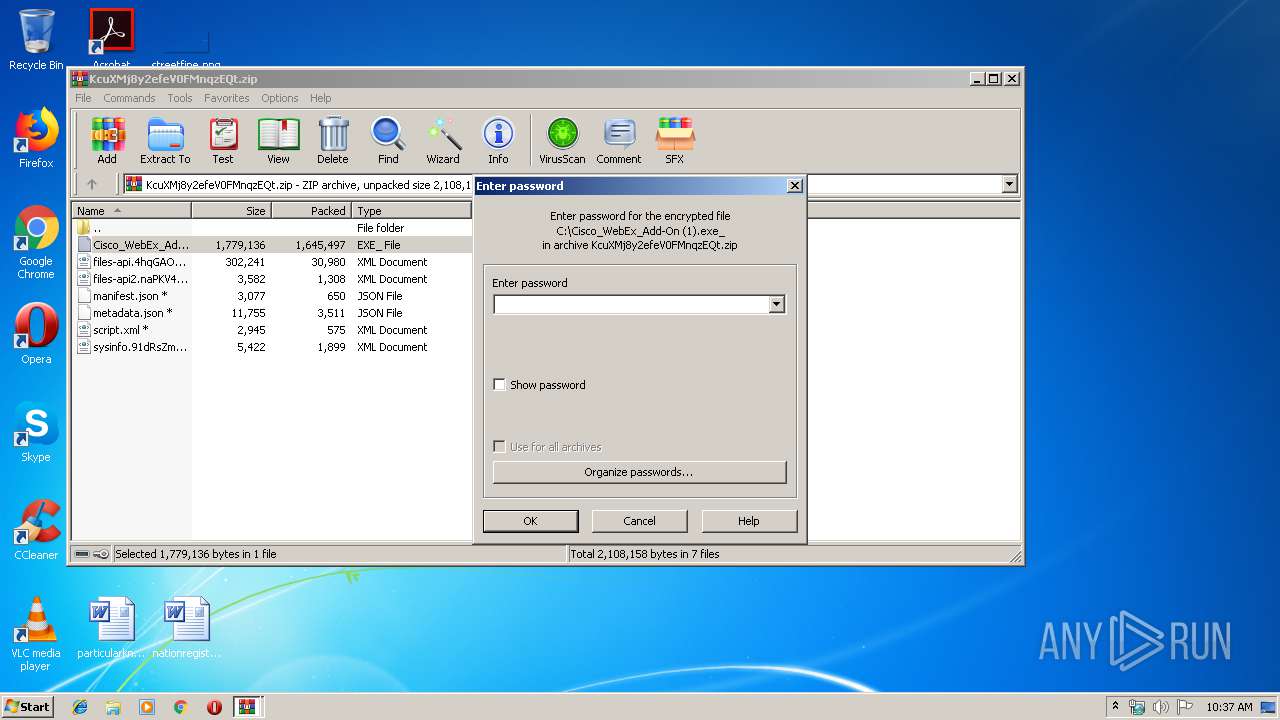
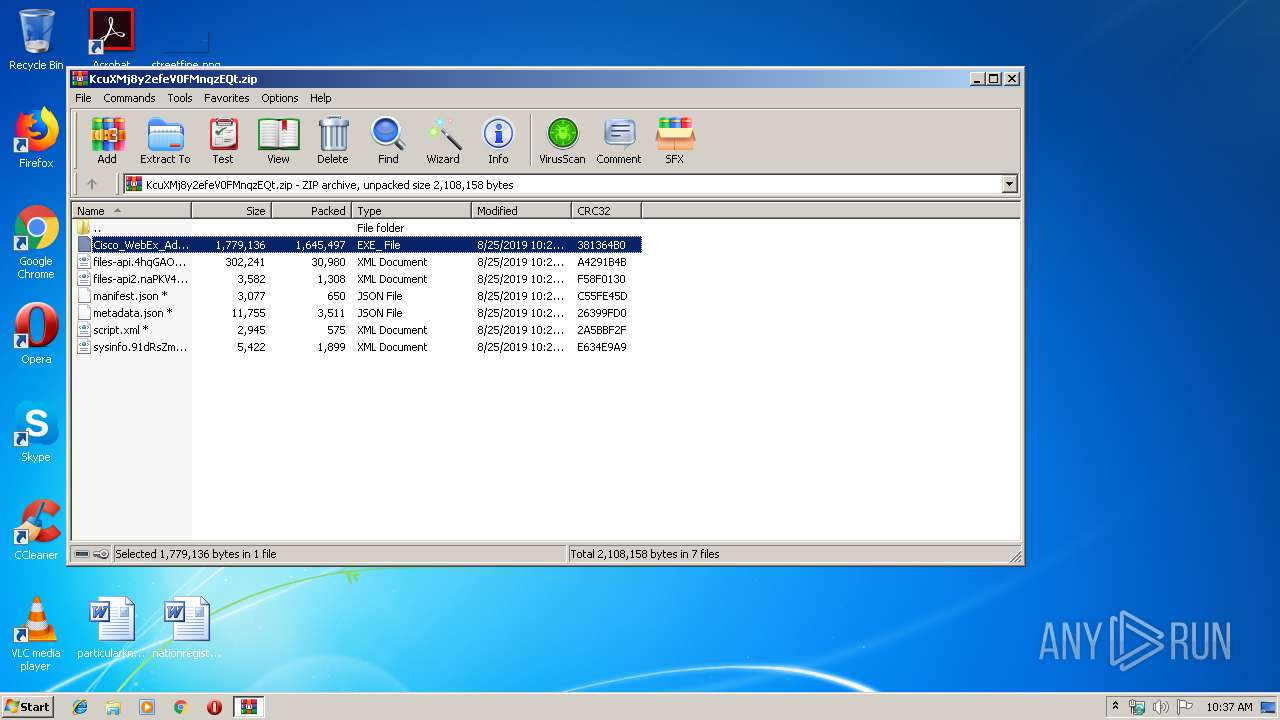
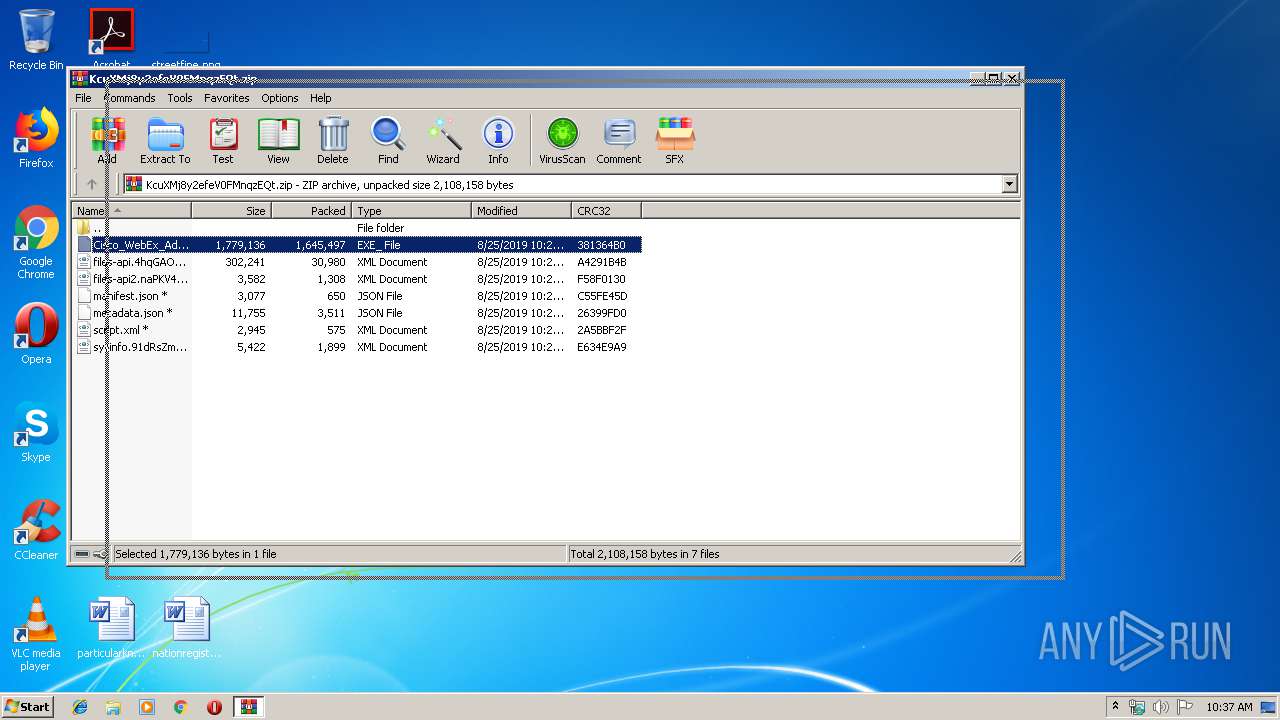
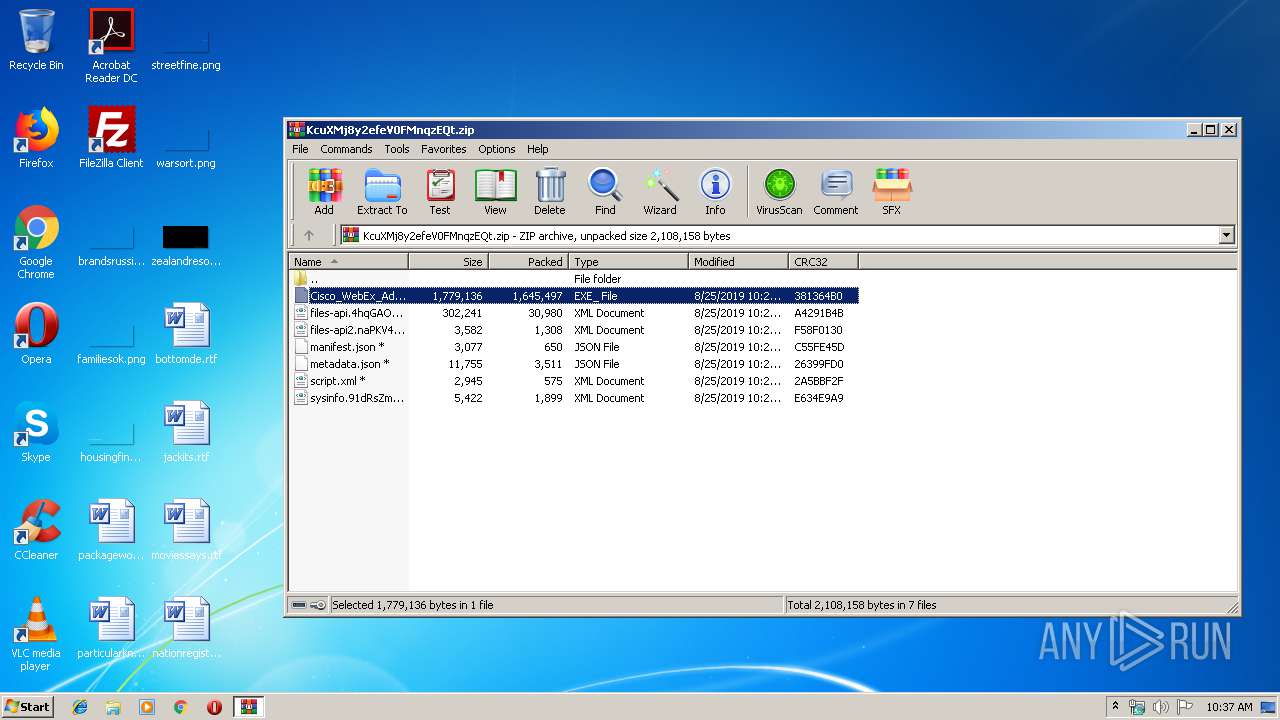
| File name: | KcuXMj8y2efeV0FMnqzEQt.zip |
| Full analysis: | https://app.any.run/tasks/7e5491b0-44cb-4e24-b68d-0d8cf1ad6ef2 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2019, 09:36:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 5215E6DDB8D9CCA3F79E0832131E554A |
| SHA1: | 834B21D0330FAA0738FE7BC5D4FA785E1A0D9CB7 |
| SHA256: | 6C9C632850D3BAE7A1DFA7D65E066CCE5B29FEB29D7C8BE1B5A6891A345E1406 |
| SSDEEP: | 49152:mHYrsV2NUmbIJTfwf8c8WNXjI3hTjenwWY/z:mEsVZmcBfwfTExf4Y7 |
MALICIOUS
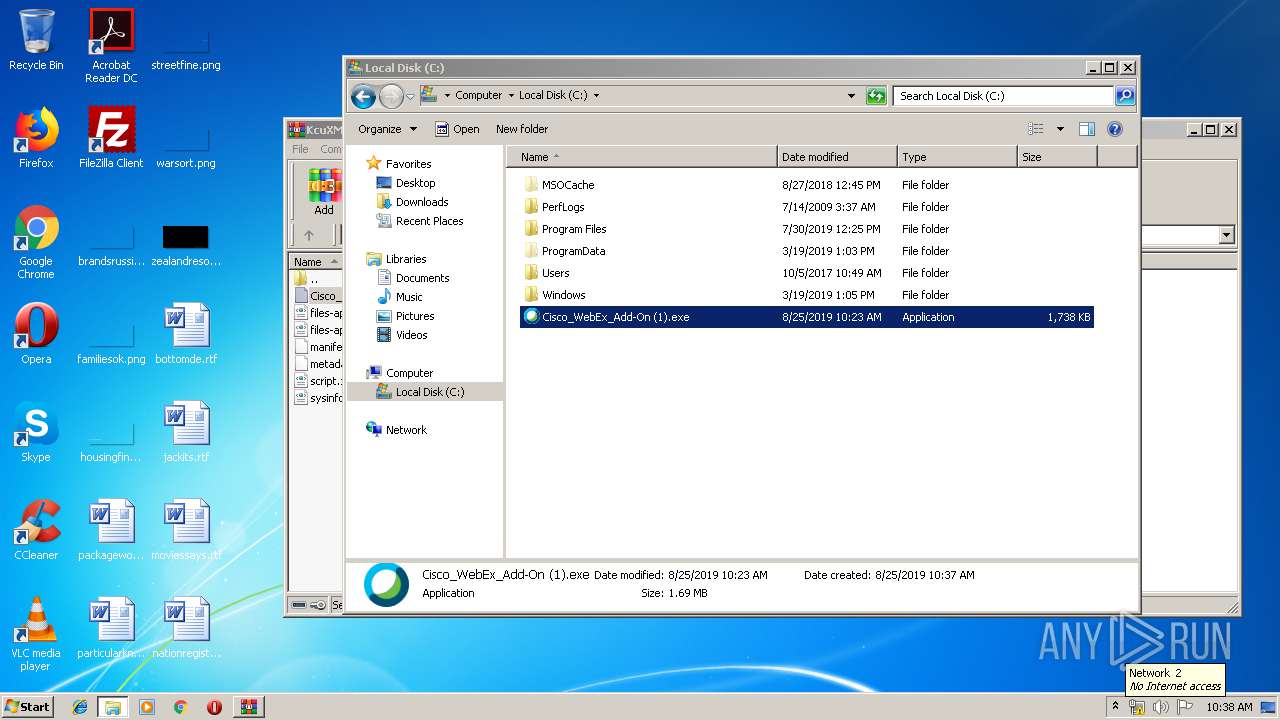
Application was dropped or rewritten from another process
- Cisco_WebEx_Add-On (1).exe (PID: 3788)
- webex.exe (PID: 2340)
- CiscoWebExStart.exe (PID: 2272)
SUSPICIOUS
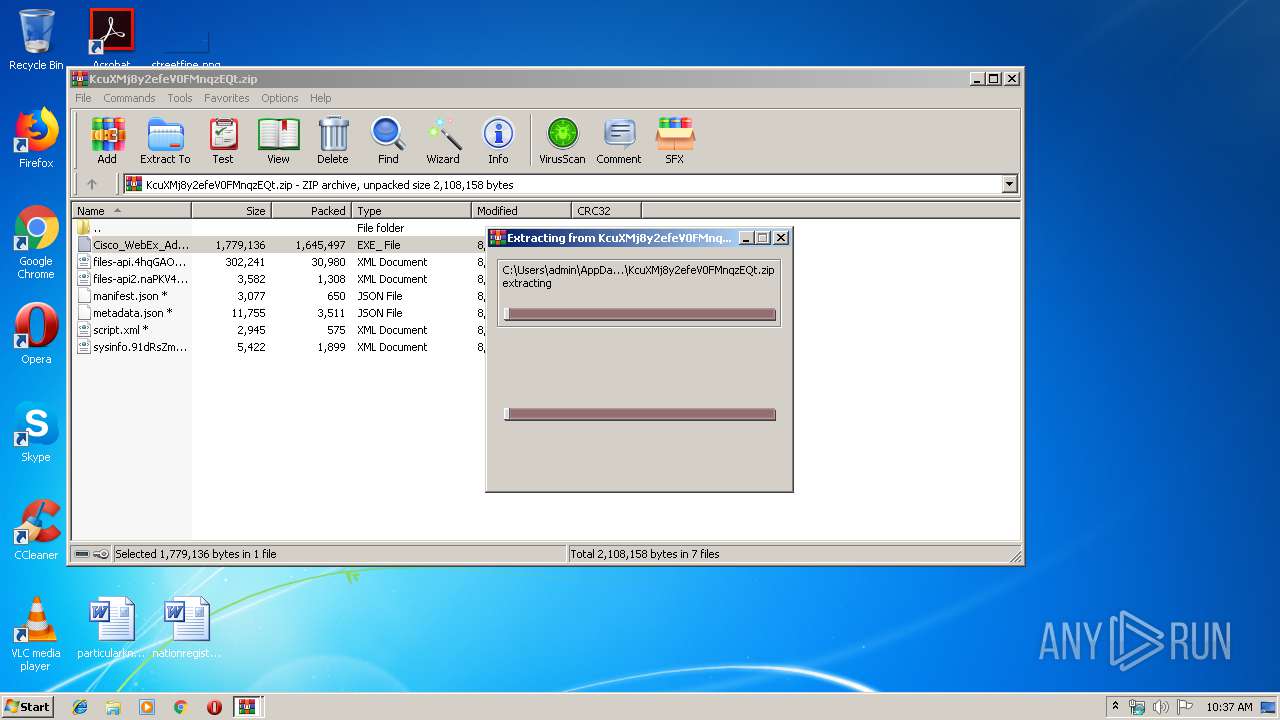
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3964)
- DllHost.exe (PID: 3008)
- Cisco_WebEx_Add-On (1).exe (PID: 3788)
Application launched itself
- WinRAR.exe (PID: 3028)
Executed via COM
- DllHost.exe (PID: 3008)
Creates files in the user directory
- Cisco_WebEx_Add-On (1).exe (PID: 3788)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1100)
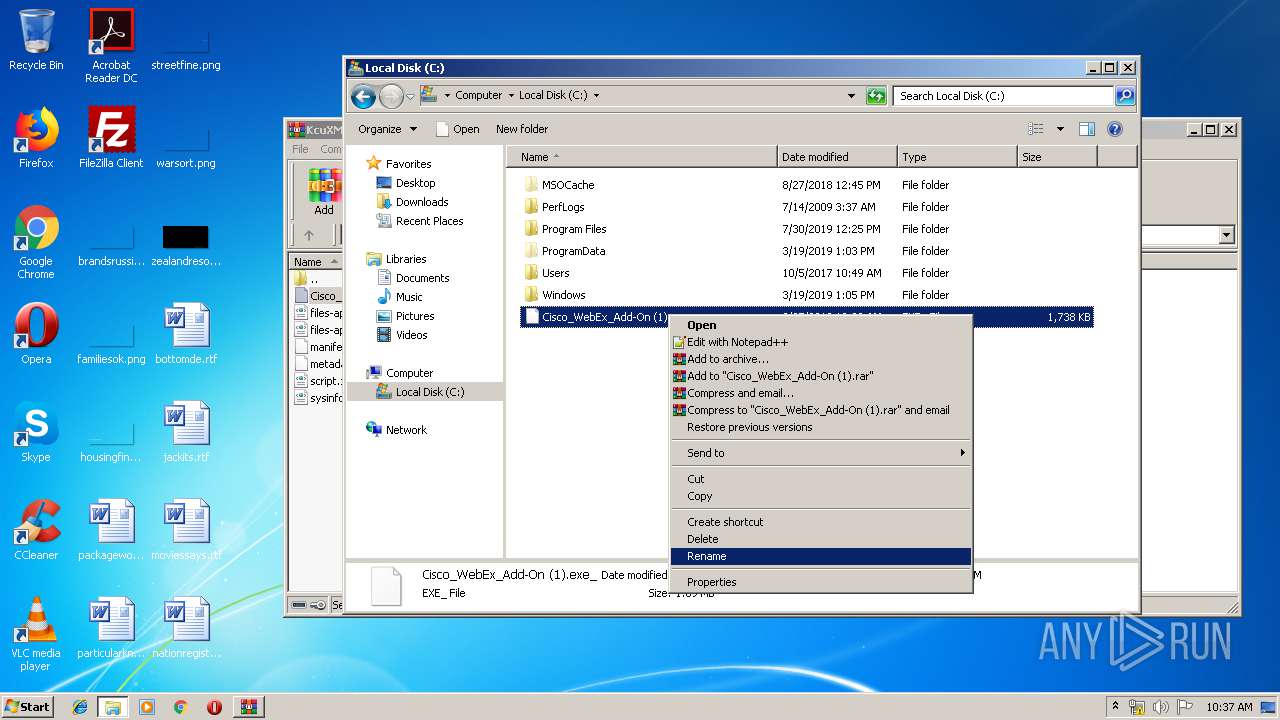
Modifies the open verb of a shell class
- CiscoWebExStart.exe (PID: 2272)
INFO
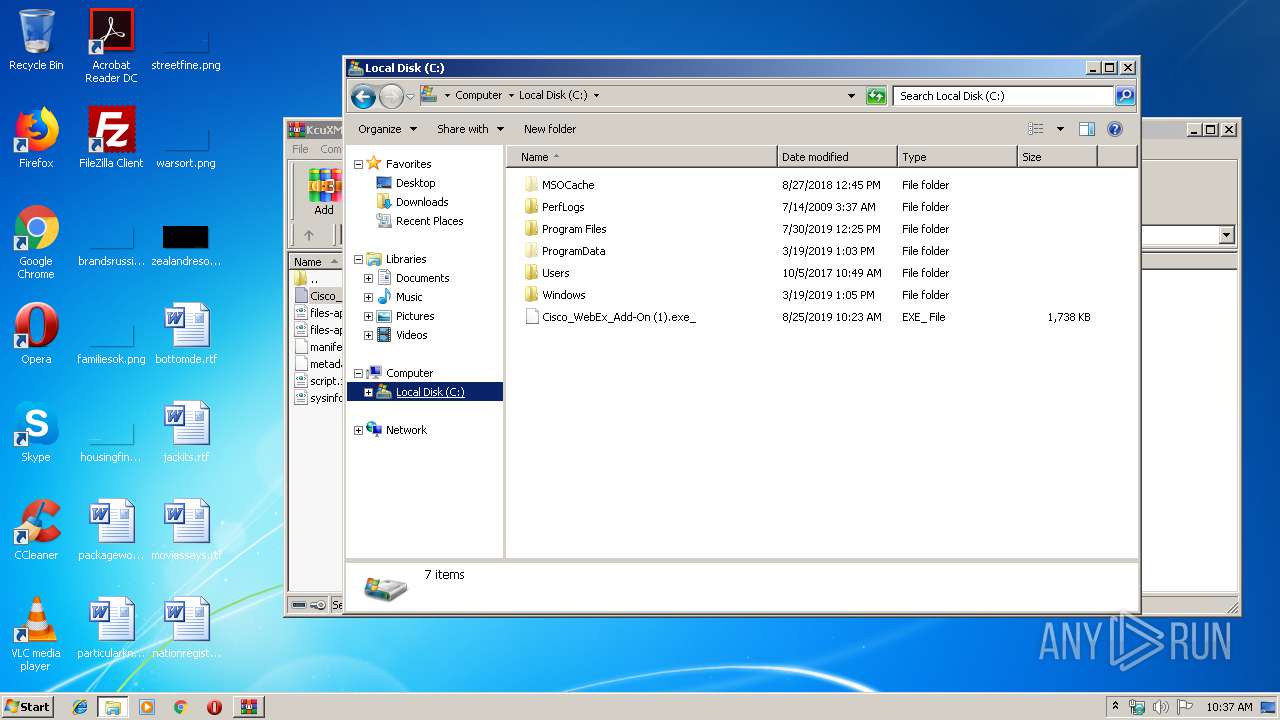
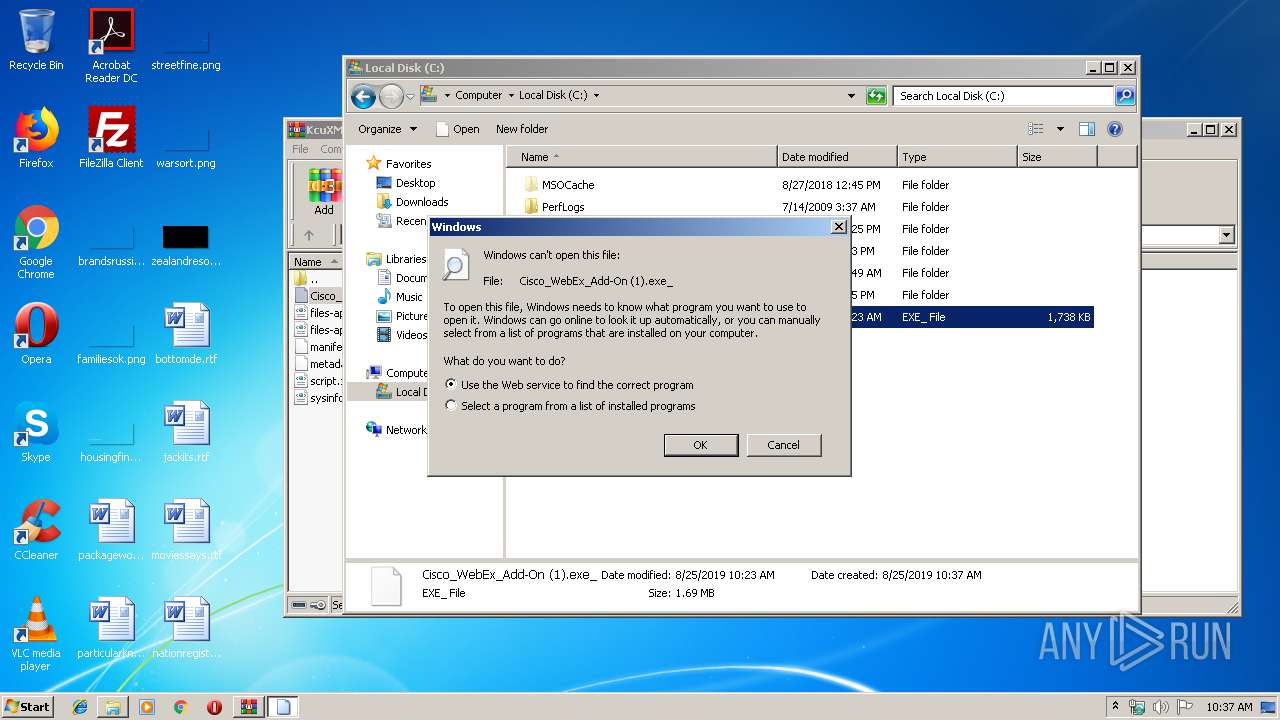
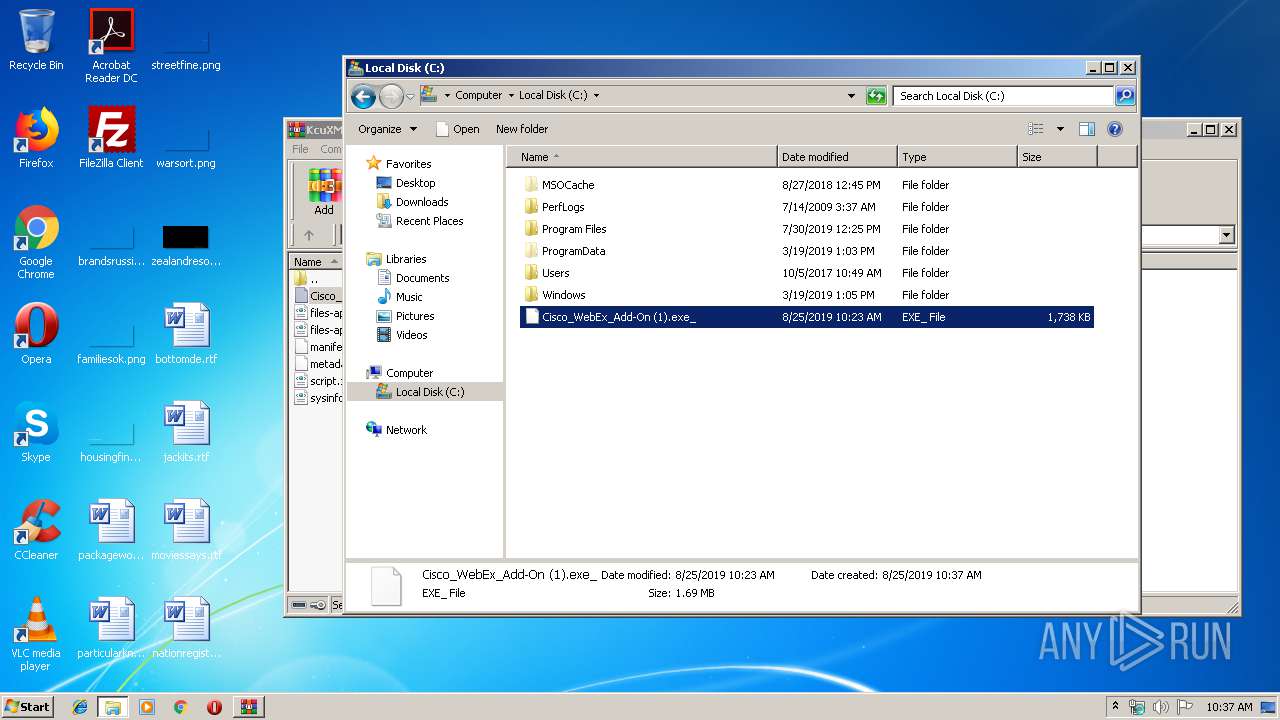
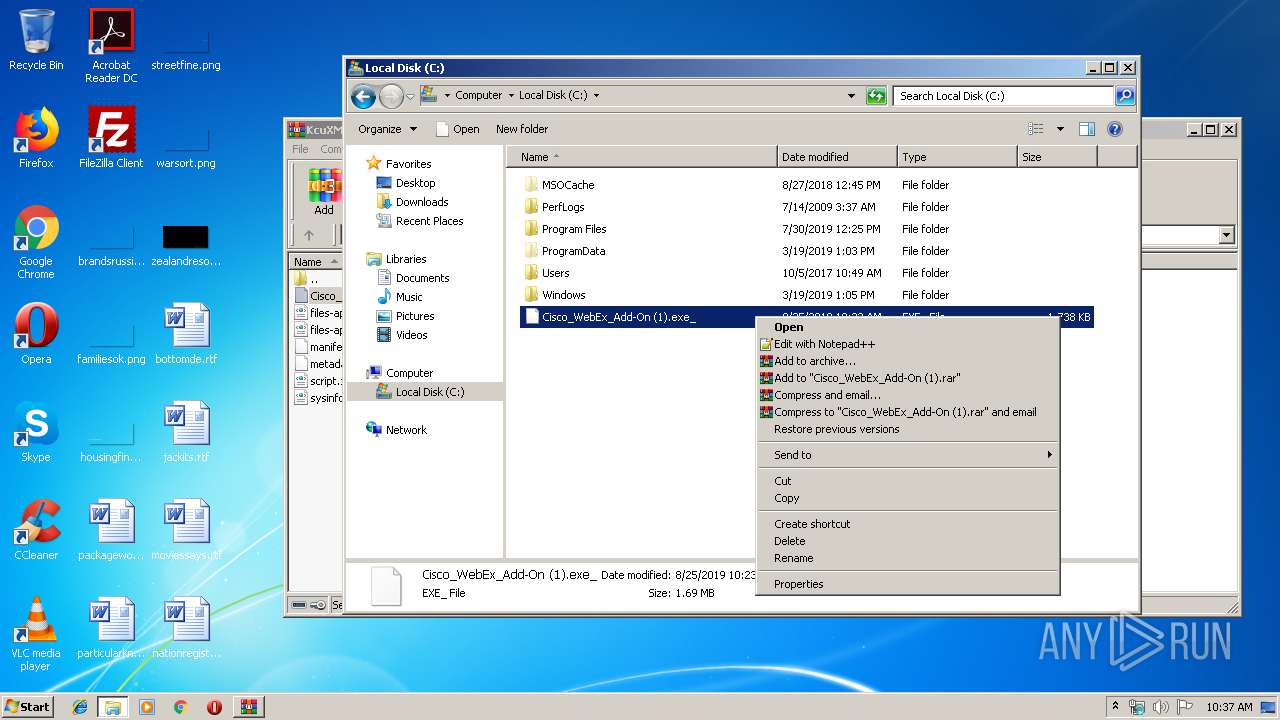
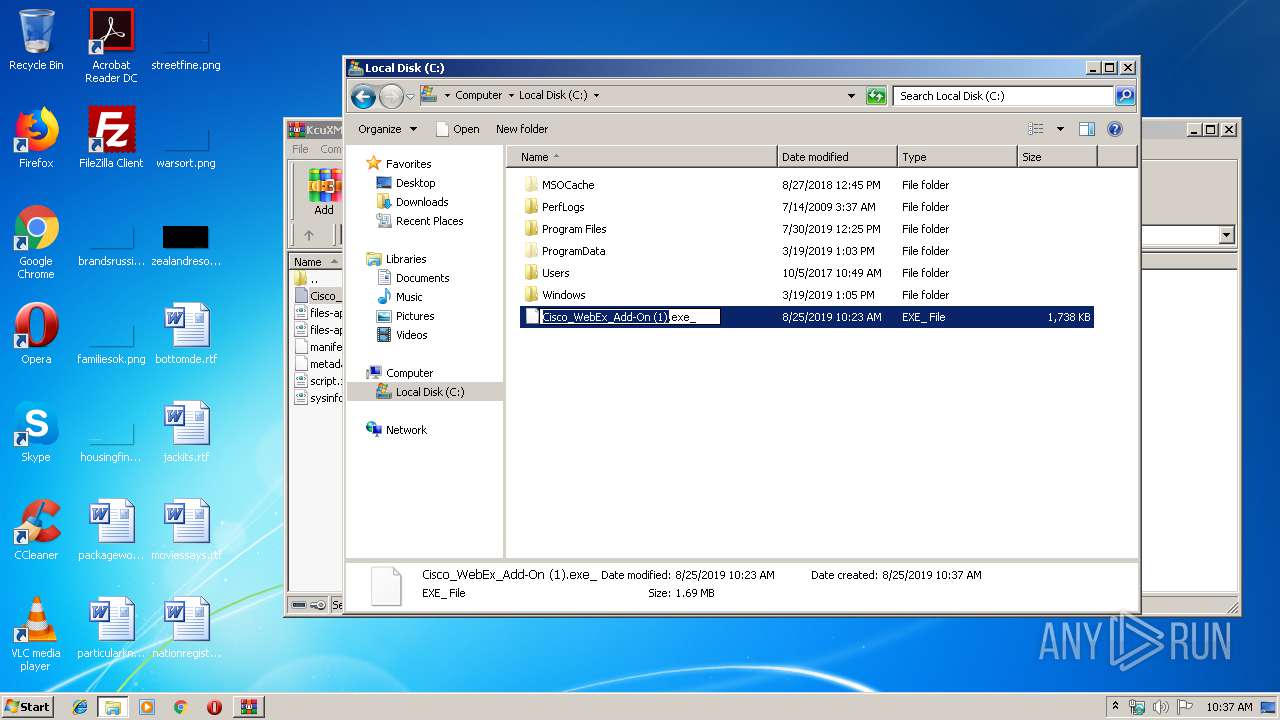
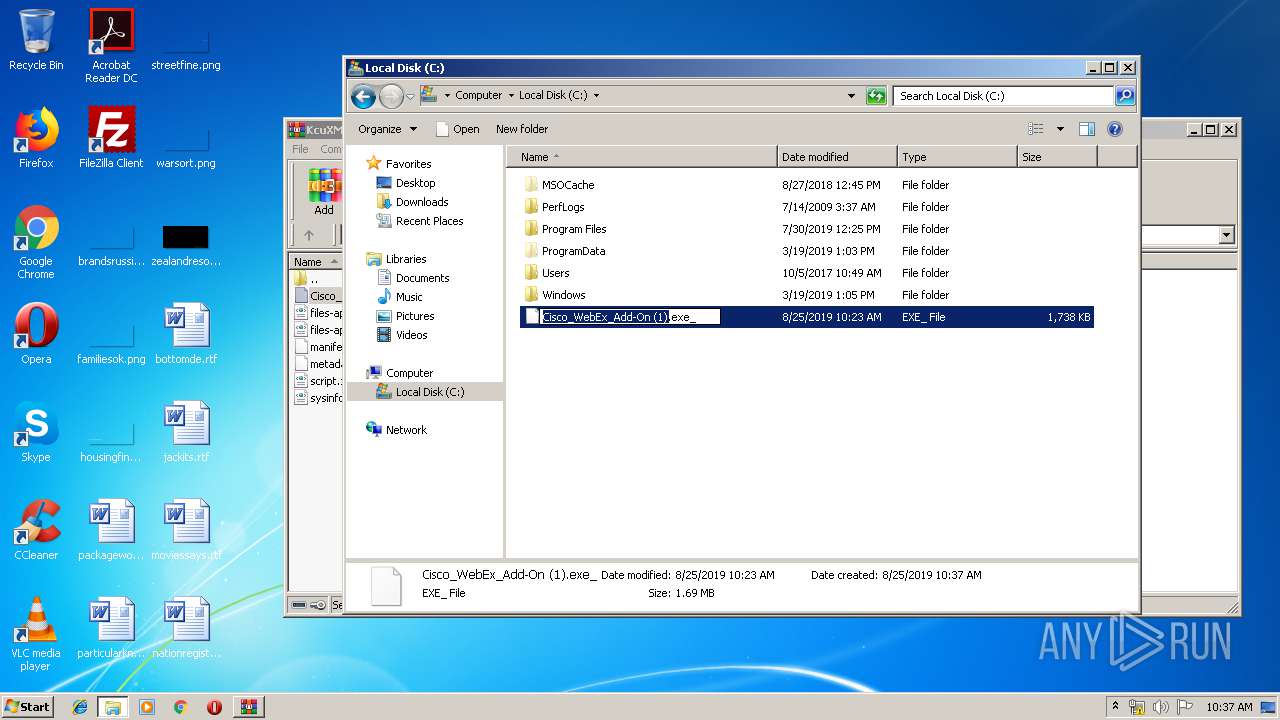
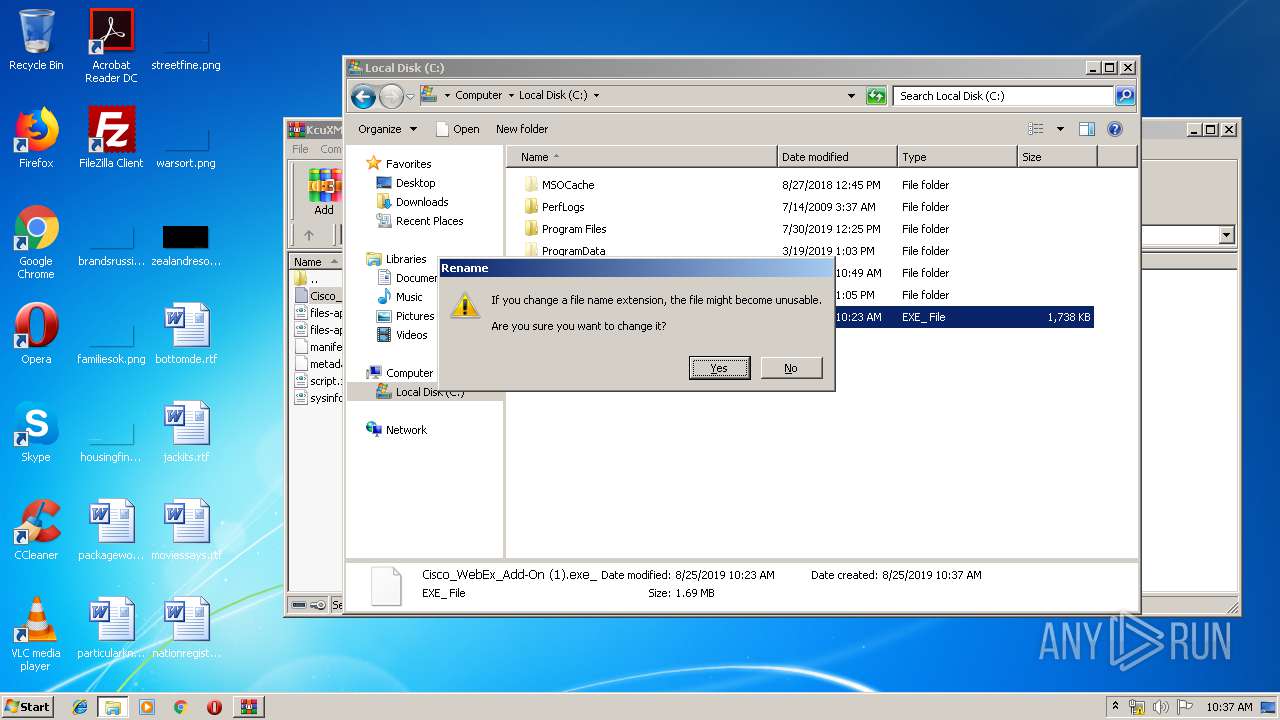
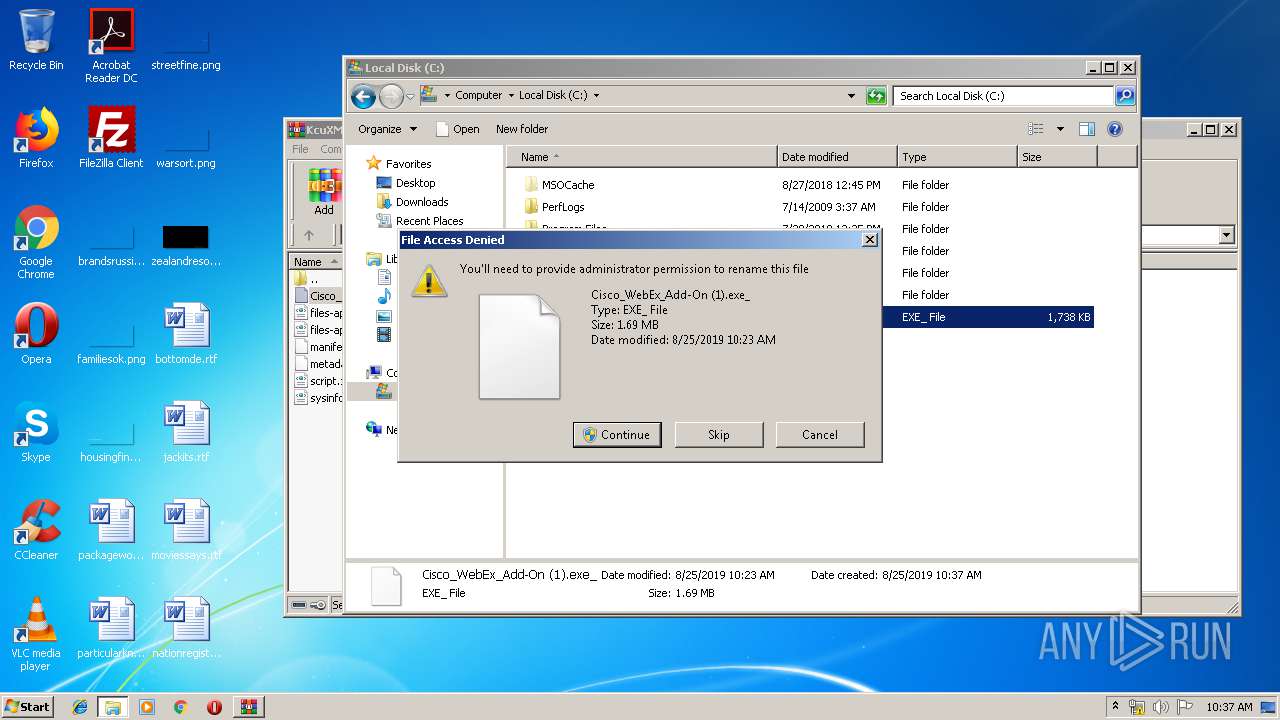
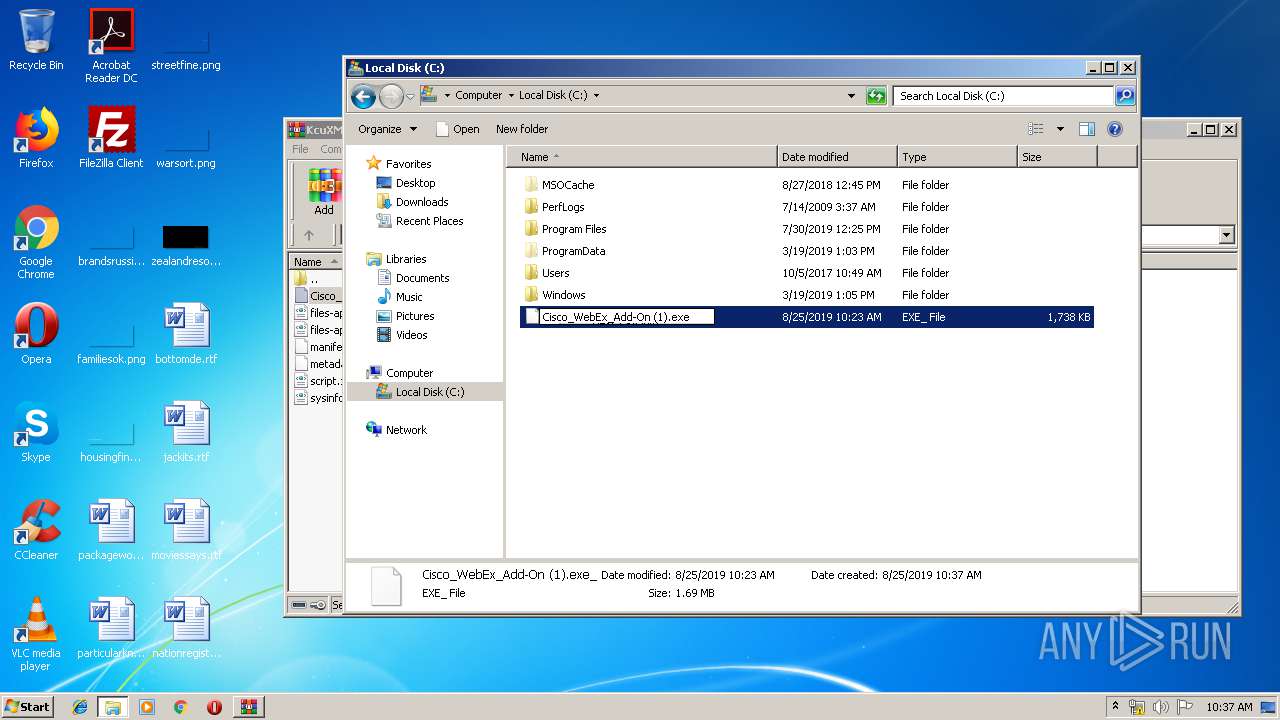
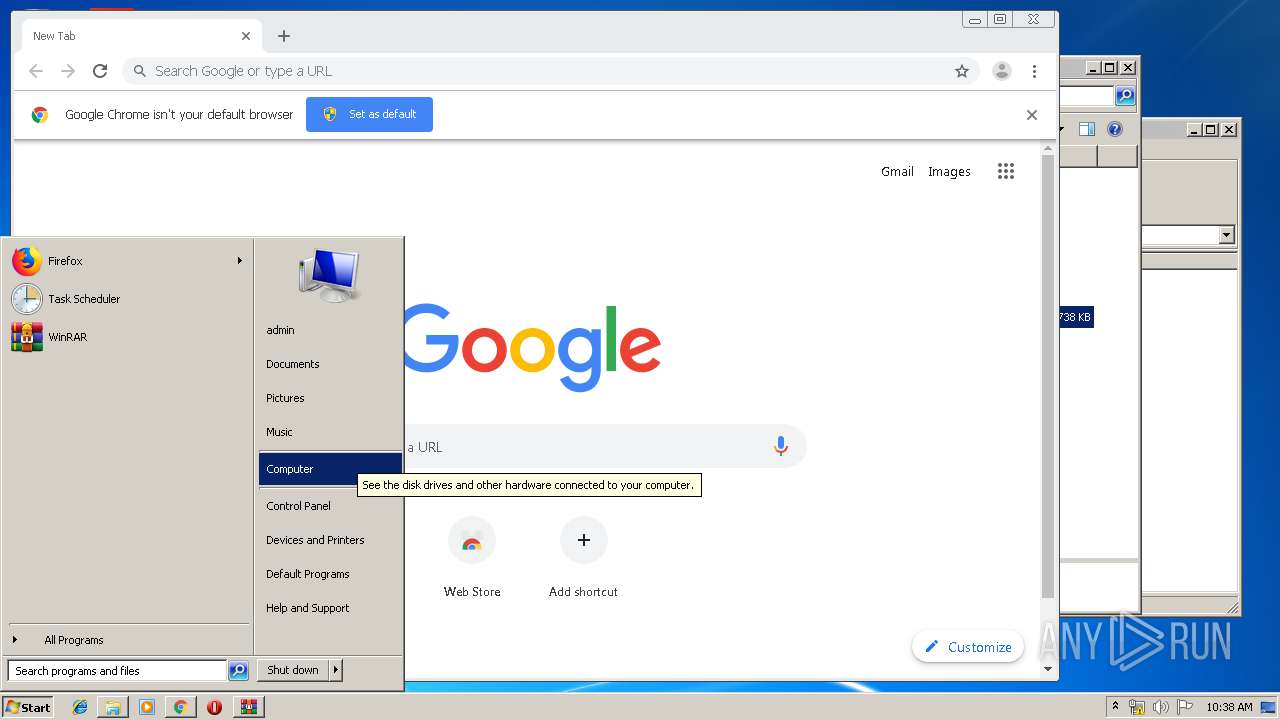
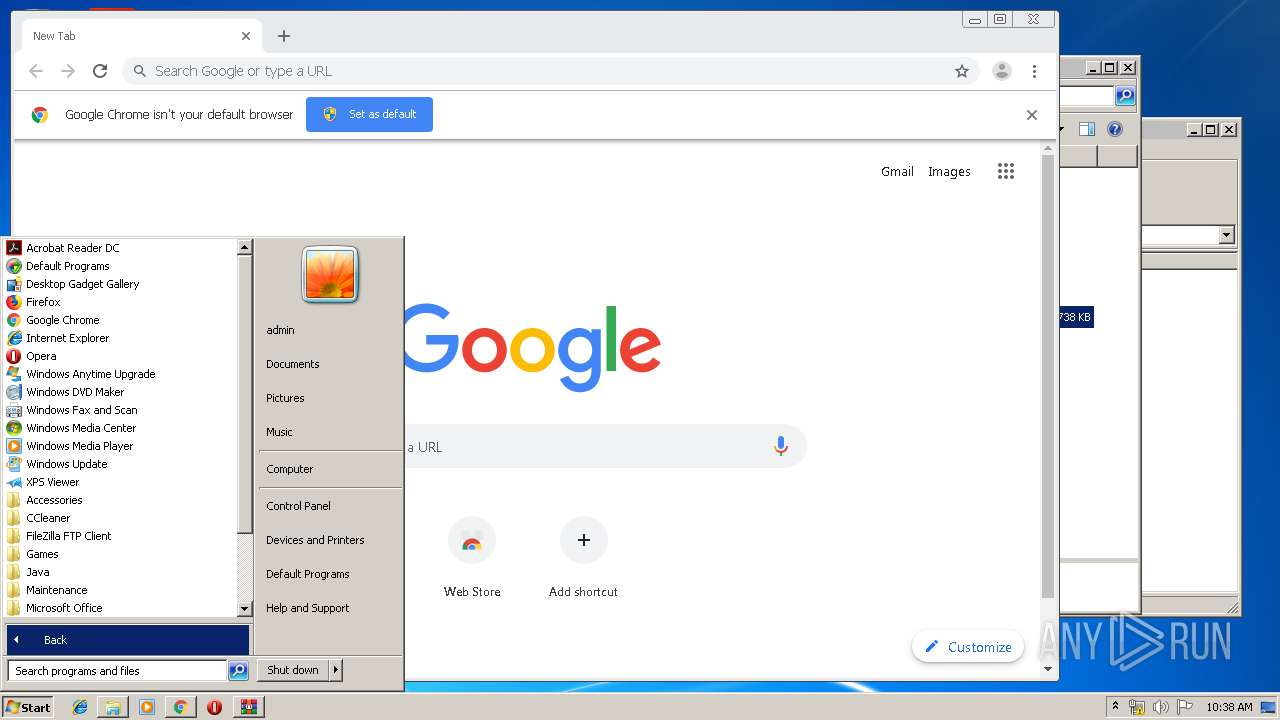
Manual execution by user
- explorer.exe (PID: 3052)
- rundll32.exe (PID: 1008)
- Cisco_WebEx_Add-On (1).exe (PID: 3788)
- chrome.exe (PID: 1100)
Application launched itself
- chrome.exe (PID: 1100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:08:25 09:23:27 |
| ZipCRC: | 0x381364b0 |
| ZipCompressedSize: | 1645497 |
| ZipUncompressedSize: | 1779136 |
| ZipFileName: | Cisco_WebEx_Add-On (1).exe_ |
Total processes
72
Monitored processes
31
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,3845578171518282960,16447775794077319941,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17517031014402441058 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,3845578171518282960,16447775794077319941,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2195081507545390899 --mojo-platform-channel-handle=3348 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Cisco_WebEx_Add-On (1).exe_ | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3845578171518282960,16447775794077319941,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10768541254278245434 --mojo-platform-channel-handle=3344 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3845578171518282960,16447775794077319941,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6947762044699777272 --mojo-platform-channel-handle=3680 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3845578171518282960,16447775794077319941,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9693710485836506625 --mojo-platform-channel-handle=3940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3845578171518282960,16447775794077319941,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7886703493472753438 --mojo-platform-channel-handle=3600 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2272 | /r | C:\Users\admin\AppData\Local\WebEx\CiscoWebExStart.exe | Cisco_WebEx_Add-On (1).exe | ||||||||||||
User: admin Company: Cisco Webex LLC Integrity Level: MEDIUM Description: Cisco Webex Meeting Exit code: 1 Version: 10039,1,2019,0111 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,3845578171518282960,16447775794077319941,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10178463017135385744 --mojo-platform-channel-handle=3488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
812
Read events
694
Write events
114
Delete events
4
Modification events
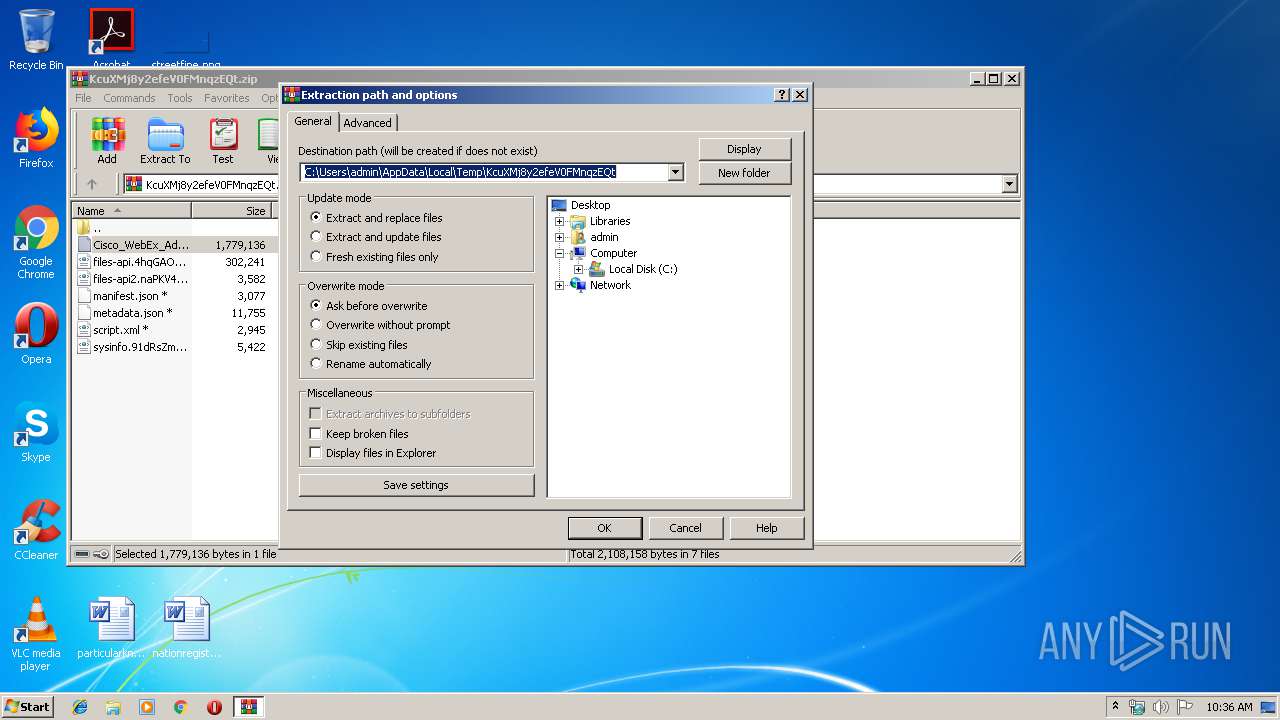
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KcuXMj8y2efeV0FMnqzEQt.zip | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\ | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
6
Suspicious files
21
Text files
174
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3788 | Cisco_WebEx_Add-On (1).exe | C:\Users\admin\AppData\Local\Temp\PreBA58.tmp | — | |
MD5:— | SHA256:— | |||
| 3788 | Cisco_WebEx_Add-On (1).exe | C:\Users\admin\AppData\Local\Temp\wbxBA57.tmp | binary | |
MD5:— | SHA256:— | |||
| 3788 | Cisco_WebEx_Add-On (1).exe | C:\Users\admin\AppData\Local\WebEx\ciscowebexstart.exe | executable | |
MD5:— | SHA256:— | |||
| 3788 | Cisco_WebEx_Add-On (1).exe | C:\Users\admin\AppData\Roaming\Mozilla\plugins\npatgpc.dll | executable | |
MD5:— | SHA256:— | |||
| 3788 | Cisco_WebEx_Add-On (1).exe | C:\Users\admin\AppData\Local\WebEx\webex.exe | executable | |
MD5:— | SHA256:— | |||
| 3788 | Cisco_WebEx_Add-On (1).exe | C:\Users\admin\AppData\Local\Temp\wbxtra_08252019_103802.wbt | binary | |
MD5:— | SHA256:— | |||
| 2272 | CiscoWebExStart.exe | C:\Users\admin\AppData\Local\WebEx\chrome.json | text | |
MD5:— | SHA256:— | |||
| 3788 | Cisco_WebEx_Add-On (1).exe | C:\Users\admin\AppData\Local\WebEx\chrome.json | text | |
MD5:— | SHA256:— | |||
| 2272 | CiscoWebExStart.exe | C:\Users\admin\AppData\Local\WebEx\firefox.json | text | |
MD5:— | SHA256:— | |||
| 1100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c6850f20-0735-4326-8cc5-d7dfefb4f210.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
18
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3856 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
3856 | chrome.exe | GET | 200 | 173.194.5.216:80 | http://r2---sn-aigl6n7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.217.117.157&mm=28&mn=sn-aigl6n7d&ms=nvh&mt=1566725835&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3856 | chrome.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 216.58.210.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
— | — | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.21.238:443 | apis.google.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3856 | chrome.exe | 172.217.22.110:443 | ogs.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Cisco_WebEx_Add-On (1).exe | WbxMapViewOfFile szMapFileName=WBX_TRACE_MAPVIEW_MAP_NAME_PRE_3788
|
Cisco_WebEx_Add-On (1).exe | WbxMapViewOfFile szMapFileName=WBX_TRACE_MAPVIEW_MAP_NAME_PRE_3788
|
Cisco_WebEx_Add-On (1).exe | WbxMapViewOfFile new lpBaseAddress=21757952
|
Cisco_WebEx_Add-On (1).exe | wbxtra_lib_clean start
|
Cisco_WebEx_Add-On (1).exe | wbxtra_lib_clean start
|
Cisco_WebEx_Add-On (1).exe | WbxUnmapViewOfFile lpBaseAddress=2175795l |
Cisco_WebEx_Add-On (1).exe | WbxUnmapViewOfFile lpBaseAddress=21757952
|
Cisco_WebEx_Add-On (1).exe | WbxMapViewOfFile AddMapFileRef=0 lpBaseAddress=21757952
|
Cisco_WebEx_Add-On (1).exe | WbxMapViewOfFile AddMapFileRef data.dwRefCount=0
|
Cisco_WebEx_Add-On (1).exe | wbxtra_lib_clean end
|