| File name: | booter.bin |
| Full analysis: | https://app.any.run/tasks/1a2a06fb-ecde-4e31-8abe-bcf95199f613 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2024, 22:25:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 36D4E51484C9BC7E0C18696B19DAFB0A |
| SHA1: | 8090D1B8896A0FC9277E2180EA9E47A3E499C2AC |
| SHA256: | 6C969E2CC64A88DABBA6348A7C4BB864EBD76E67A02730394BD572030BF3AA9C |
| SSDEEP: | 49152:hoa7MZ7WttcZB9j6dnT5+5Zoa7MZ7WttcZB9j6dnT5+5F7eUM:hoaYWtmjj45+LoaYWtmjj45+OUM |
MALICIOUS
Drops the executable file immediately after the start
- booter.bin.exe (PID: 3980)
SUSPICIOUS
Reads security settings of Internet Explorer
- booter.bin.exe (PID: 3980)
Reads Microsoft Outlook installation path
- booter.bin.exe (PID: 3980)
Reads the Internet Settings
- booter.bin.exe (PID: 3980)
Reads Internet Explorer settings
- booter.bin.exe (PID: 3980)
INFO
Checks supported languages
- booter.bin.exe (PID: 3980)
Reads the computer name
- booter.bin.exe (PID: 3980)
Reads the machine GUID from the registry
- booter.bin.exe (PID: 3980)
Checks proxy server information
- booter.bin.exe (PID: 3980)
Creates files or folders in the user directory
- booter.bin.exe (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2040:11:13 11:12:34+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 1439744 |
| InitializedDataSize: | 272896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x161702 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | discord.gg/MTdUp2G |
| CompanyName: | Nigmode Incorporated |
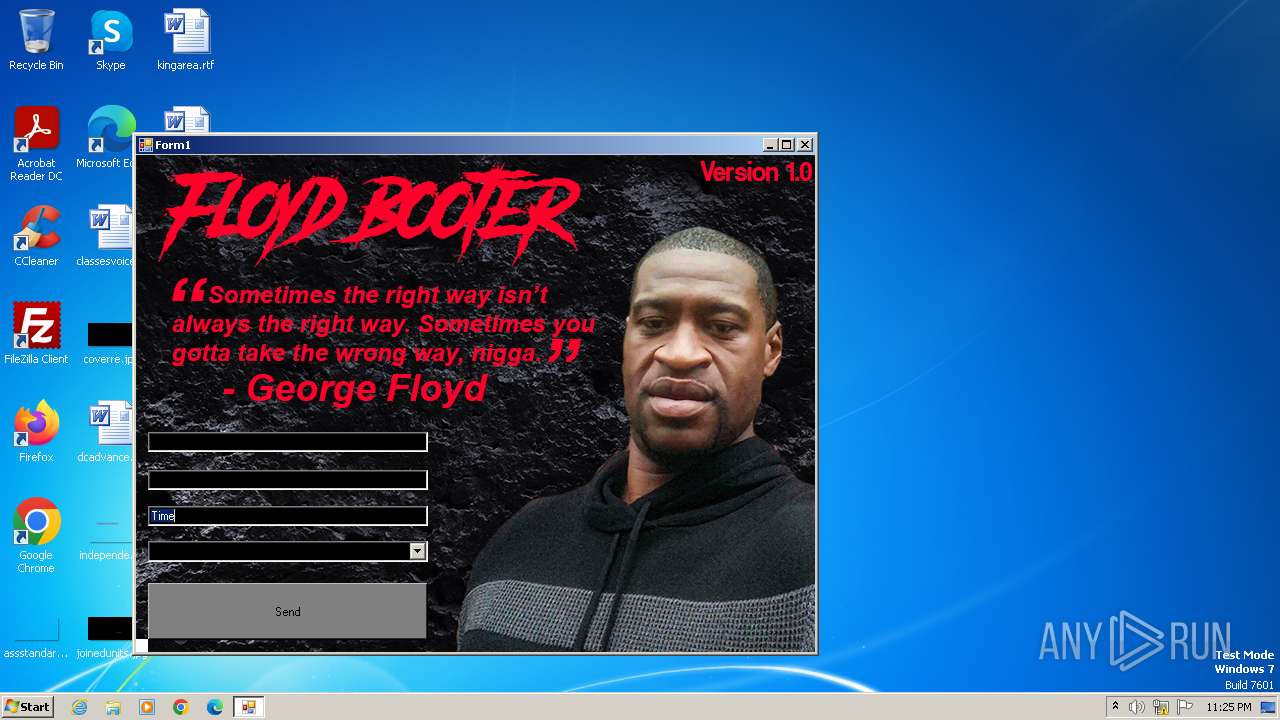
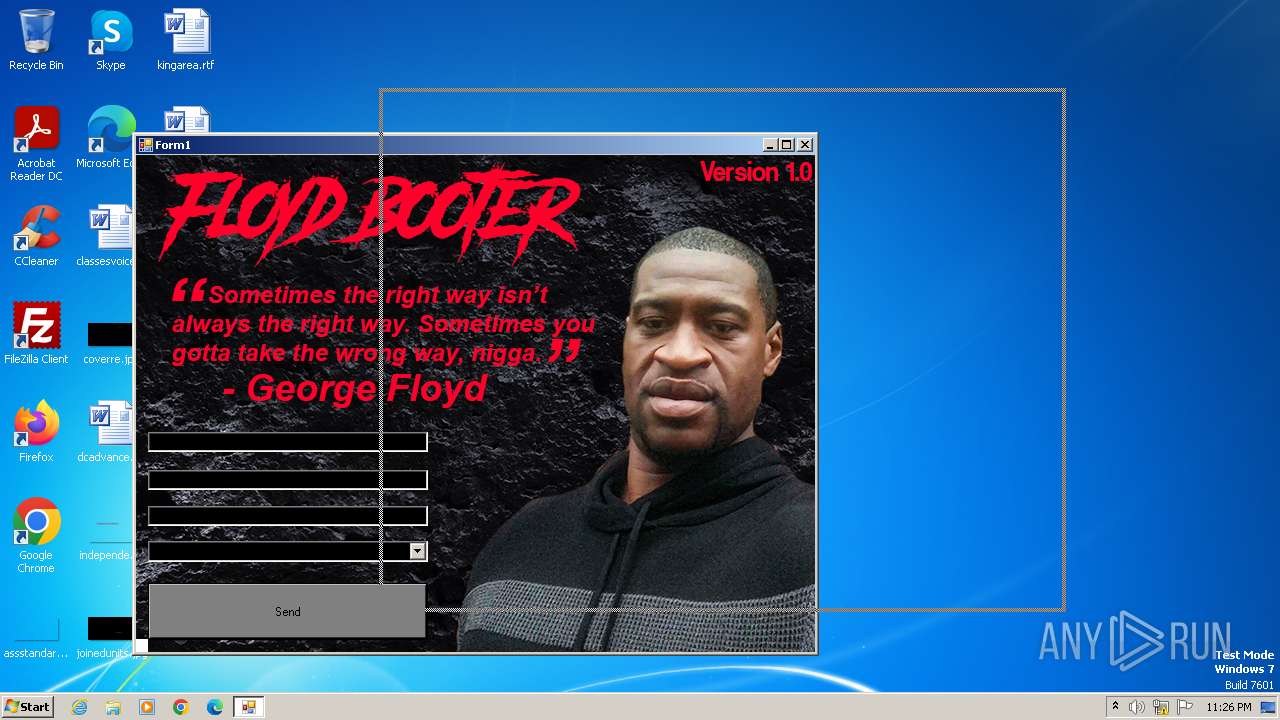
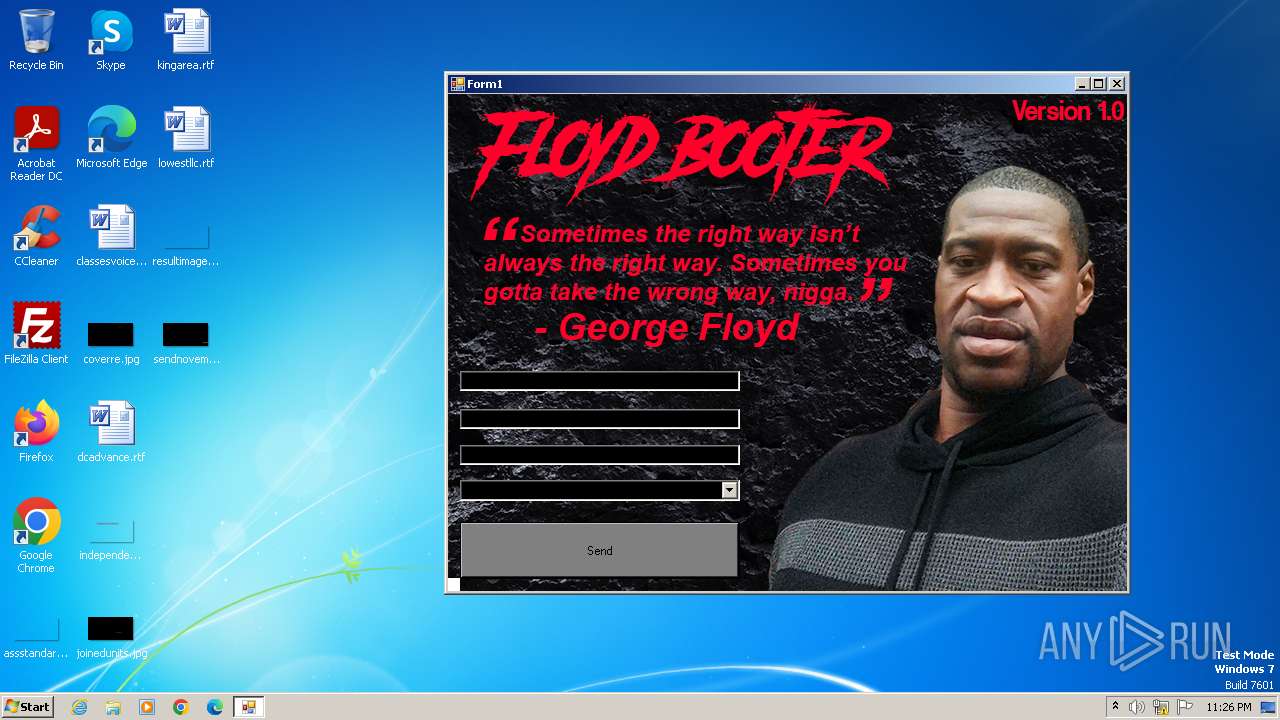
| FileDescription: | Floyd Booter v1.0 |
| FileVersion: | 1.0.0.0 |
| InternalName: | Floyd Booter v1.0.exe |
| LegalCopyright: | ©2020 Nigmode Incorporated |
| LegalTrademarks: | - |
| OriginalFileName: | Floyd Booter v1.0.exe |
| ProductName: | Floyd Booter |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
34
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
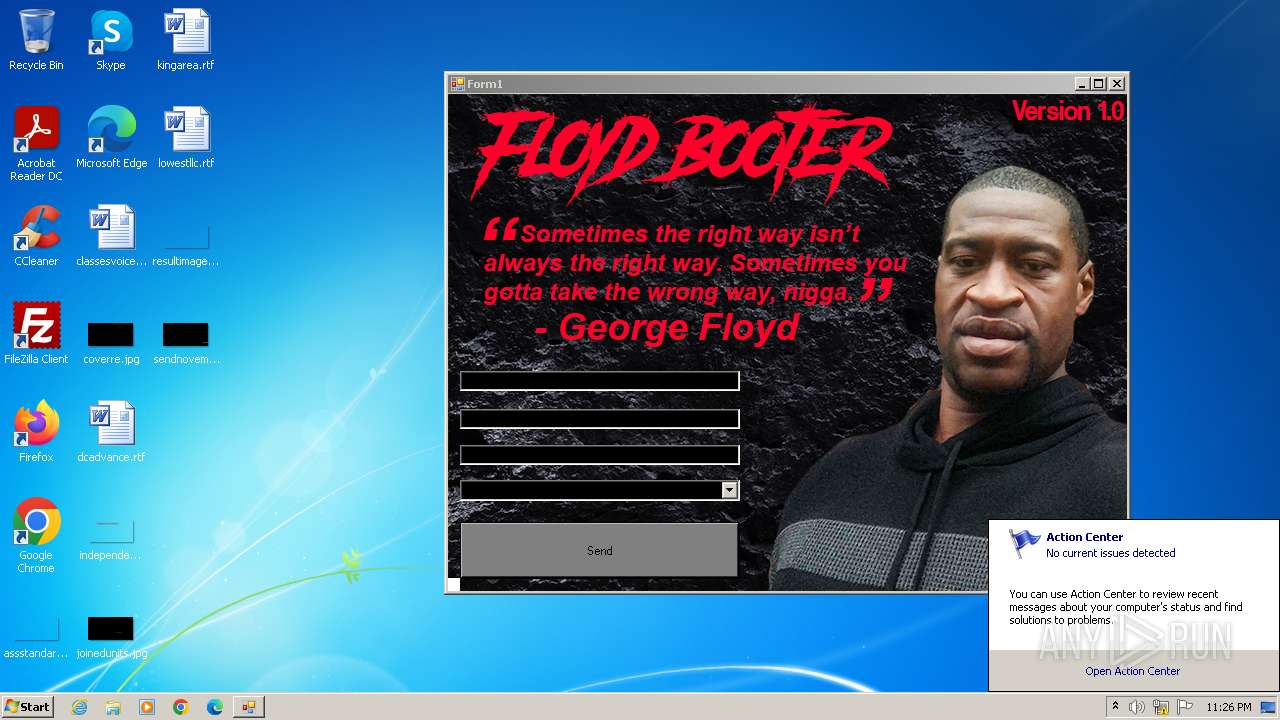
| 3980 | "C:\Users\admin\AppData\Local\Temp\booter.bin.exe" | C:\Users\admin\AppData\Local\Temp\booter.bin.exe | explorer.exe | ||||||||||||
User: admin Company: Nigmode Incorporated Integrity Level: MEDIUM Description: Floyd Booter v1.0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 680
Read events
1 552
Write events
104
Delete events
24
Modification events
| (PID) Process: | (3980) booter.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3980) booter.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3980) booter.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3980) booter.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3980) booter.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3980) booter.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3980) booter.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3980) booter.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3980) booter.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (3980) booter.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
26
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3980 | booter.bin.exe | 66.42.116.204:80 | — | AS-CHOOPA | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |