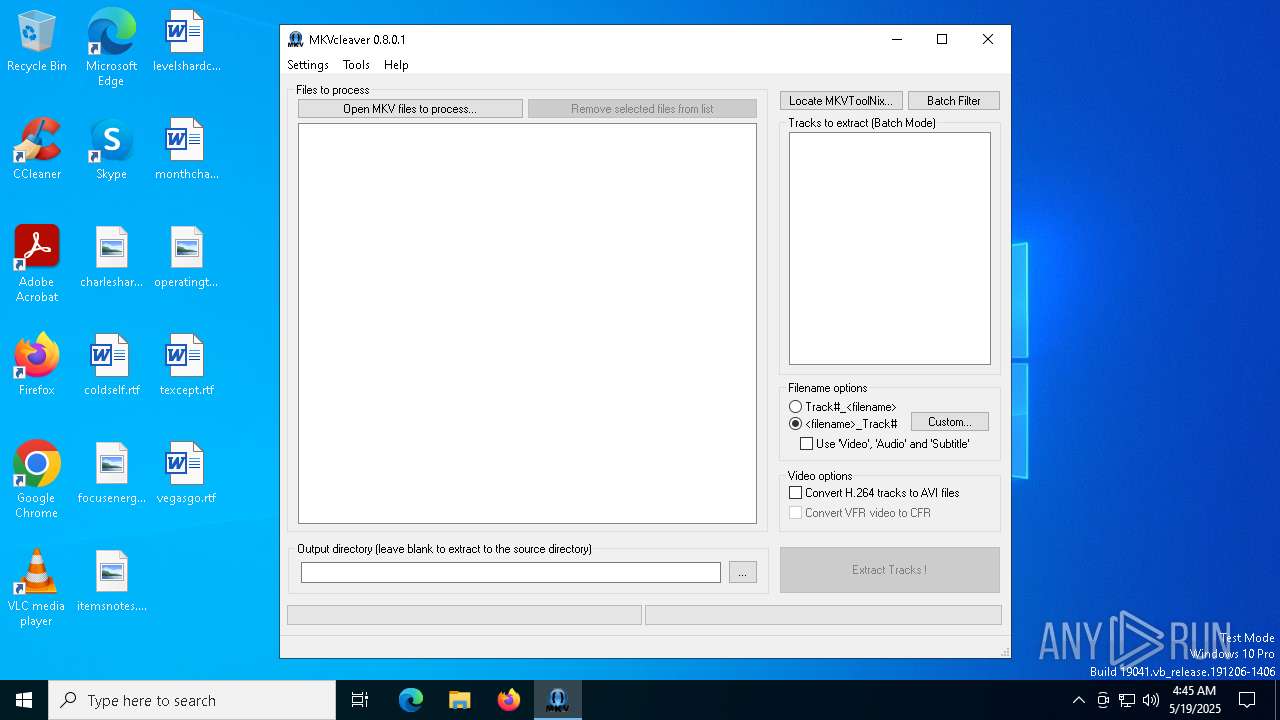
| File name: | MKVCleaver_x64_v0801.exe |
| Full analysis: | https://app.any.run/tasks/5fb6ce34-1191-42af-8f8e-2616feb7a987 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 04:45:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 6F87B8C4E57552C54FD9BD15F1E818D2 |
| SHA1: | 21A18EFB90975D1EF0FFEB8213D385EBE53850BE |
| SHA256: | 6C8212D03B37EF7622958639079ABAA26E06BA828EB88DD6447C06BE4B4E7A04 |
| SSDEEP: | 98304:Y9rem5OidQQNFeEXb5g5zfei7VPGzOHsPeYAdnDcEXFNuRfkFhI3q660KXA9M78U:WvgLnlxSx |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- MKVCleaver_x64_v0801.exe (PID: 2140)
Starts CMD.EXE for commands execution
- MKVCleaver_x64_v0801.exe (PID: 2140)
The executable file from the user directory is run by the CMD process
- LogRotate.exe (PID: 1760)
There is functionality for taking screenshot (YARA)
- MKVCleaver_x64_v0801.exe (PID: 2140)
Reads security settings of Internet Explorer
- MKVCleaver_x64_v0801.exe (PID: 2140)
INFO
Reads mouse settings
- MKVCleaver_x64_v0801.exe (PID: 2140)
- LogRotate.exe (PID: 1760)
Create files in a temporary directory
- MKVCleaver_x64_v0801.exe (PID: 2140)
Checks supported languages
- MKVCleaver_x64_v0801.exe (PID: 2140)
- LogRotate.exe (PID: 1760)
Reads the machine GUID from the registry
- MKVCleaver_x64_v0801.exe (PID: 2140)
Creates files or folders in the user directory
- MKVCleaver_x64_v0801.exe (PID: 2140)
Checks proxy server information
- MKVCleaver_x64_v0801.exe (PID: 2140)
Reads the software policy settings
- MKVCleaver_x64_v0801.exe (PID: 2140)
The process uses AutoIt
- MKVCleaver_x64_v0801.exe (PID: 2140)
The sample compiled with english language support
- MKVCleaver_x64_v0801.exe (PID: 2140)
Reads the computer name
- MKVCleaver_x64_v0801.exe (PID: 2140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:05:03 08:33:12+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 734208 |
| InitializedDataSize: | 7443456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2549c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.8.0.1 |
| ProductVersionNumber: | 0.8.0.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 0.8.0.1 |
| Comments: | This application is freeware. |
| FileDescription: | MKVCleaver can extract all/any tracks from MKV files. |
| ProductName: | MKVCleaver |
| ProductVersion: | 0.8.0.1 |
| CompanyName: | Sapib Corp |
| LegalCopyright: | Ilia Bakhmoutski (sheck) 2010-2024 |
Total processes
133
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1760 | C:\Users\admin\AppData\Local\Temp\LogRotate.exe | C:\Users\admin\AppData\Local\Temp\LogRotate.exe | — | cmd.exe | |||||||||||
User: admin Company: Sapib Corp Integrity Level: MEDIUM Description: LogRotate rotates MKVCleaver log database table. Exit code: 1 Version: 0.8.0.1 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\Temp\MKVCleaver_x64_v0801.exe" | C:\Users\admin\AppData\Local\Temp\MKVCleaver_x64_v0801.exe | explorer.exe | ||||||||||||
User: admin Company: Sapib Corp Integrity Level: MEDIUM Description: MKVCleaver can extract all/any tracks from MKV files. Version: 0.8.0.1 Modules
| |||||||||||||||
| 2148 | C:\WINDOWS\system32\cmd.exe /c "C:\Users\admin\AppData\Local\Temp\LogRotate.exe" | C:\Windows\System32\cmd.exe | — | MKVCleaver_x64_v0801.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5416 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6816 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7152 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
967
Read events
964
Write events
3
Delete events
0
Modification events
| (PID) Process: | (2140) MKVCleaver_x64_v0801.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2140) MKVCleaver_x64_v0801.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2140) MKVCleaver_x64_v0801.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
5
Suspicious files
16
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | MKVCleaver_x64_v0801.exe | C:\Users\admin\AppData\Local\Temp\MKVCleaver_Help.chm | binary | |
MD5:BEEF4307B2D655A574ED19801956C92E | SHA256:283EE9CAEC3F9DC9D39EE1CBF96BF129E303BE2A7E8E01AB096C66177CE0688F | |||
| 2140 | MKVCleaver_x64_v0801.exe | C:\Users\admin\AppData\Local\Temp\LogRotate.exe | executable | |
MD5:92D8EDC8852ED64F1E16438BDECD5A37 | SHA256:C4C4F9A908C0E9BCA3713A1436C79A02CD2DEBCCC5760093FD07E36A8B6FE3A1 | |||
| 2140 | MKVCleaver_x64_v0801.exe | C:\Users\admin\AppData\Local\Temp\autBBB7.tmp | binary | |
MD5:BF685929BAB1214E72A9C42B3728E8E7 | SHA256:FA5A1376BA7758618818BB13F1470A62B68C3CFE05C6DA2254B965ECD78C9EEF | |||
| 2140 | MKVCleaver_x64_v0801.exe | C:\Users\admin\AppData\Local\Temp\tc2cfr.exe | executable | |
MD5:6083B601DFAA94CE01BC6444CEC42D4A | SHA256:9E775BB2FCDB4DFD8B759630D6FDFD8D31FA4B41C2DAF0736FC1437A3F671559 | |||
| 2140 | MKVCleaver_x64_v0801.exe | C:\Users\admin\AppData\Local\Temp\MediaInfo.dll | executable | |
MD5:B6C89ABE90D0F900697E9FC0F0538EFE | SHA256:9D3DA565115E19A195E46A63B27A0B2C2288DB732013640D4FA66D7377F507B3 | |||
| 2140 | MKVCleaver_x64_v0801.exe | C:\Users\admin\AppData\Local\Temp\autBAC8.tmp | binary | |
MD5:BEEF4307B2D655A574ED19801956C92E | SHA256:283EE9CAEC3F9DC9D39EE1CBF96BF129E303BE2A7E8E01AB096C66177CE0688F | |||
| 2140 | MKVCleaver_x64_v0801.exe | C:\Users\admin\AppData\Local\Temp\mediainfo_params.sqlite | binary | |
MD5:0BDEAD323589952828B629C9C264C9CA | SHA256:12B10042D25EDEB88D3D9386C97A101EB87E946FD478F41C9AB618E0A2191718 | |||
| 2140 | MKVCleaver_x64_v0801.exe | C:\Users\admin\AppData\Local\Temp\mkvcleaver_db.sqlite-journal | binary | |
MD5:D2D39626037CFA28589584D7173464E5 | SHA256:8D2F7FF51F5027C762FBED8661C16CD74A415C03C1D853CB2E3BFE05F273D639 | |||
| 2140 | MKVCleaver_x64_v0801.exe | C:\Users\admin\AppData\Local\Temp\autBB47.tmp | binary | |
MD5:A76FF2783FDD9CFB1A569D662462C125 | SHA256:EC80BBE975EEC4BAF3ADDD25EDA3FD9D459F7CE7231B4FD00409C63006280E36 | |||
| 2140 | MKVCleaver_x64_v0801.exe | C:\Users\admin\AppData\Local\Temp\autBB27.tmp | binary | |
MD5:CA9D8E4137A4307140A96289D59106C7 | SHA256:B7D95B49C8A3DE0E2C879241830127EE9DFAF26234B03DB8AF7ADC5BA8AD96F3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
22
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2140 | MKVCleaver_x64_v0801.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2140 | MKVCleaver_x64_v0801.exe | GET | 200 | 184.24.77.56:80 | http://r10.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRpD%2BQVZ%2B1vf7U0RGQGBm8JZwdxcgQUdKR2KRcYVIUxN75n5gZYwLzFBXICEgVV%2B2l8Y1%2FUz%2Bv4Cb9aWCW7Vg%3D%3D | unknown | — | — | whitelisted |
5204 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5204 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2140 | MKVCleaver_x64_v0801.exe | 162.250.191.174:443 | services.sapib.ca | RICAWEBSERVICES | CA | unknown |
2140 | MKVCleaver_x64_v0801.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | whitelisted |
2140 | MKVCleaver_x64_v0801.exe | 184.24.77.56:80 | r10.o.lencr.org | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
sapib.ca |
| unknown |
services.sapib.ca |
| unknown |
x1.c.lencr.org |
| whitelisted |
r10.o.lencr.org |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |