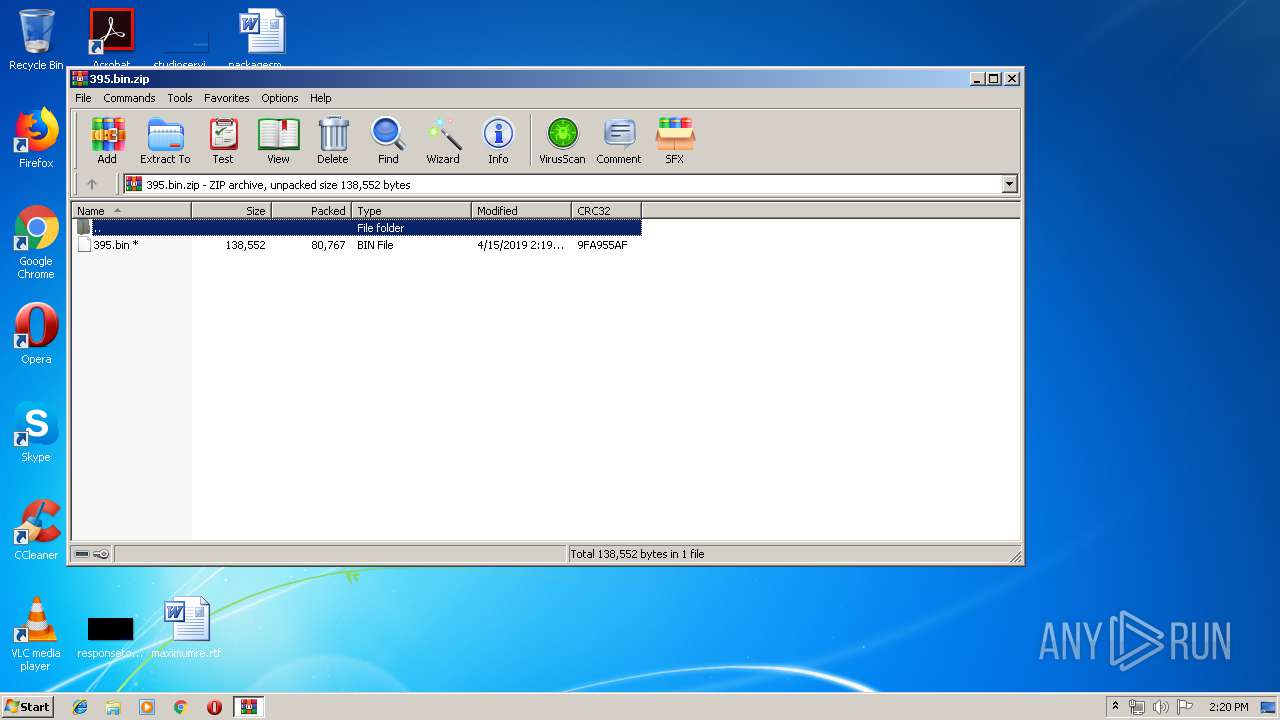
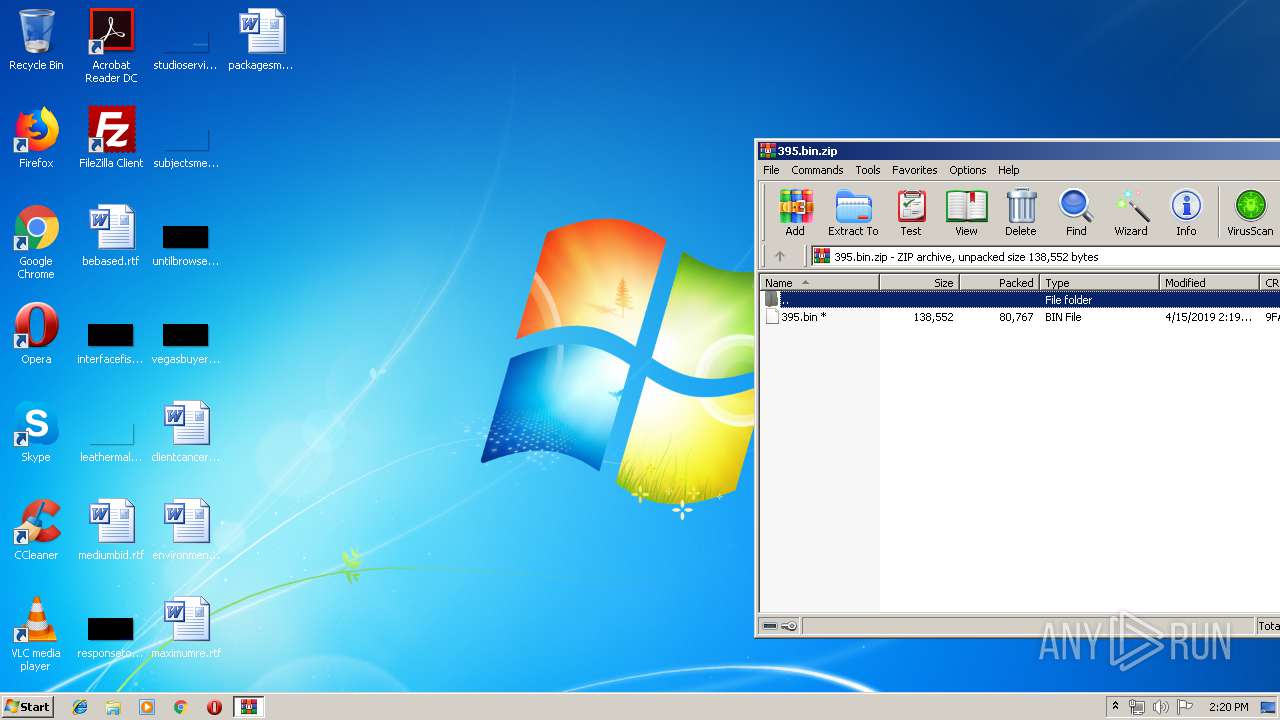
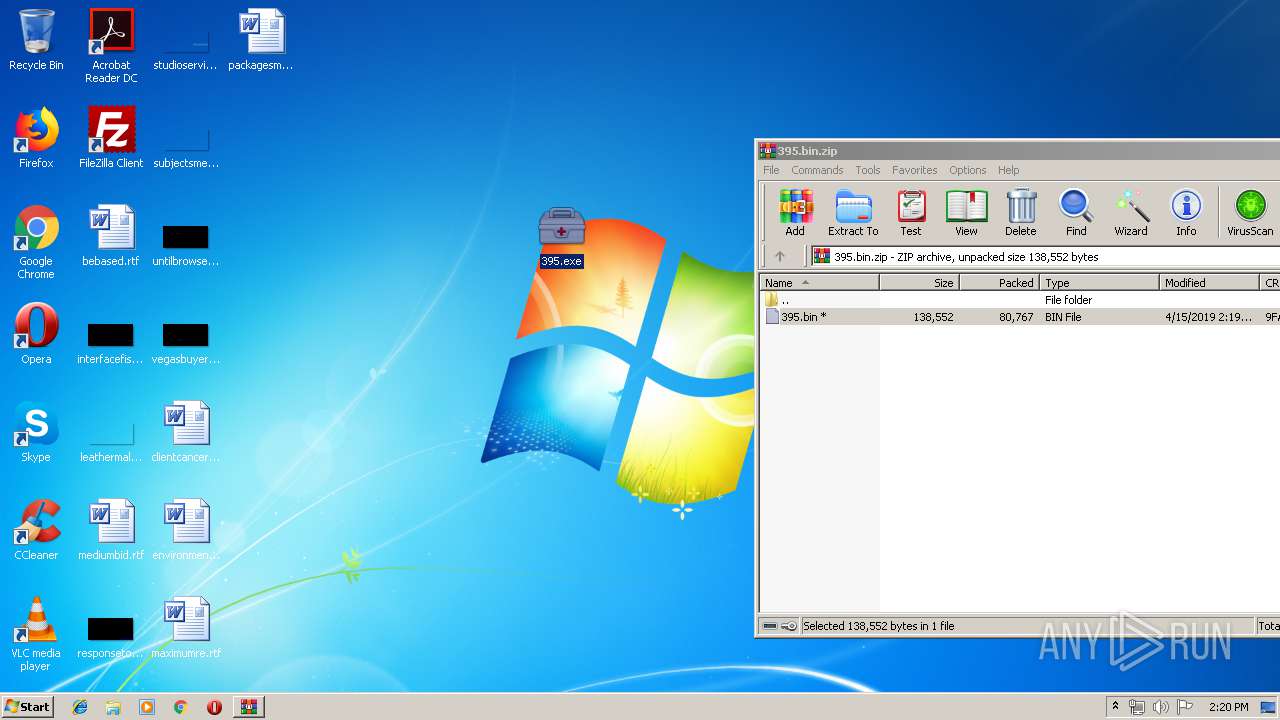
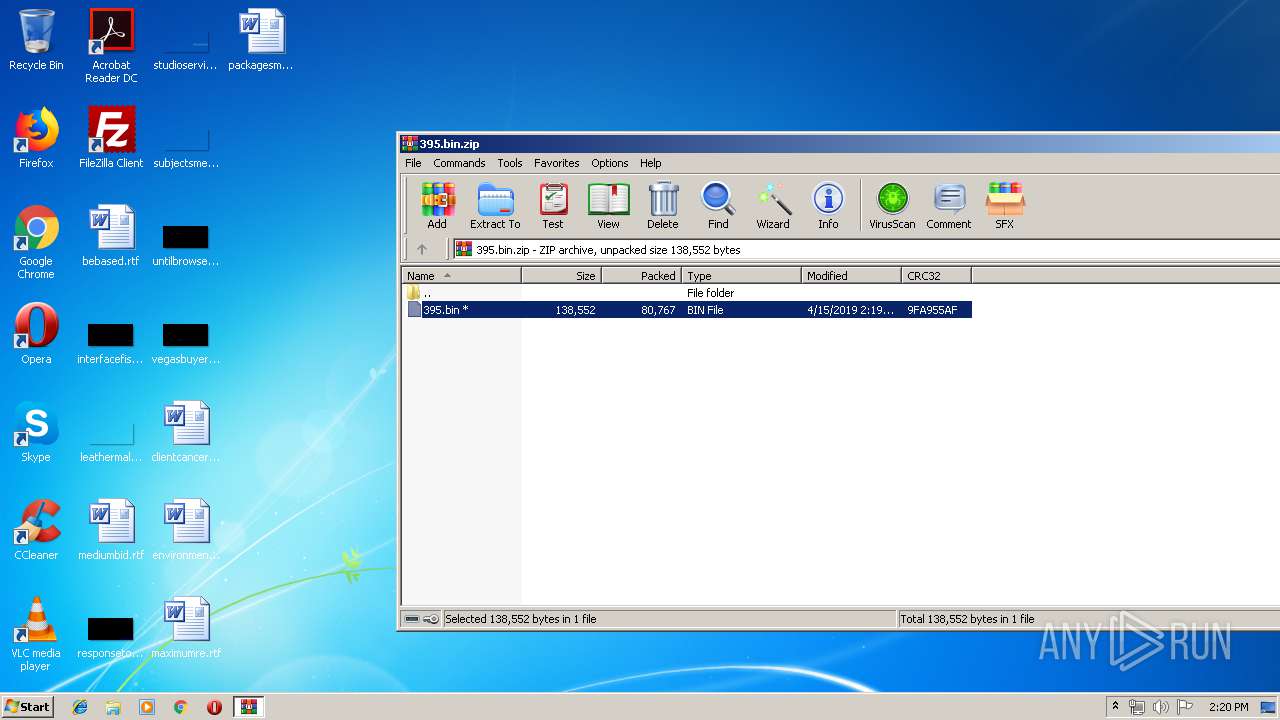
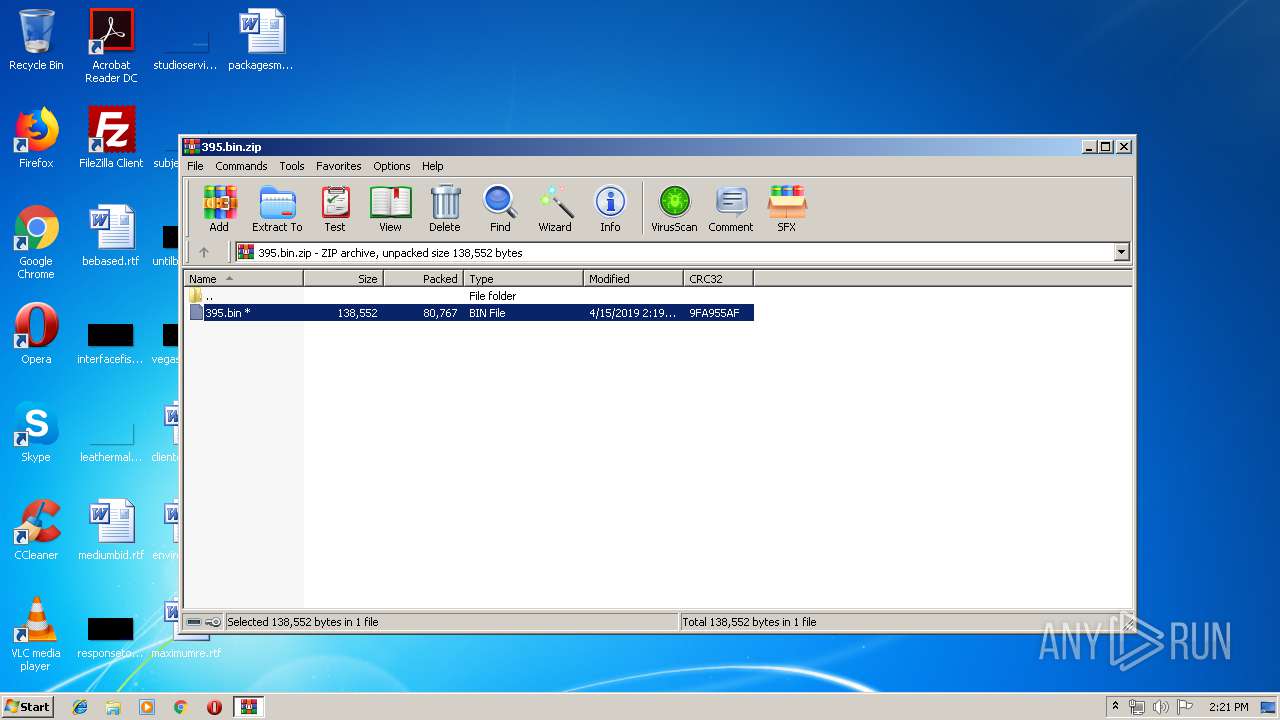
| File name: | 395.bin.zip |
| Full analysis: | https://app.any.run/tasks/6ed9885e-a972-41ac-a5de-2309acb7c164 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 15, 2019, 13:19:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 85AC67BDE682E0B0D2B3E8592C7A2CFD |
| SHA1: | 5B7EF786DAC9A09E48E01D556CA8053D865C7026 |
| SHA256: | 6C7DC997337BEA0BF1FC1731B0CBD35EC7F7E05FD75144E09803CFAC535D22B9 |
| SSDEEP: | 1536:Gj2Z2M6pHmw2uRXDk6hM4nAqFhVn37aYv8zxJof1+rnd988t9jZD:GrM6JmwraAM4Pb8cwndqq/D |
MALICIOUS
Application was dropped or rewritten from another process
- 395.exe (PID: 680)
- 395.exe (PID: 1892)
- soundser.exe (PID: 2652)
- soundser.exe (PID: 3536)
Emotet process was detected
- soundser.exe (PID: 2652)
EMOTET was detected
- soundser.exe (PID: 3536)
Connects to CnC server
- soundser.exe (PID: 3536)
SUSPICIOUS
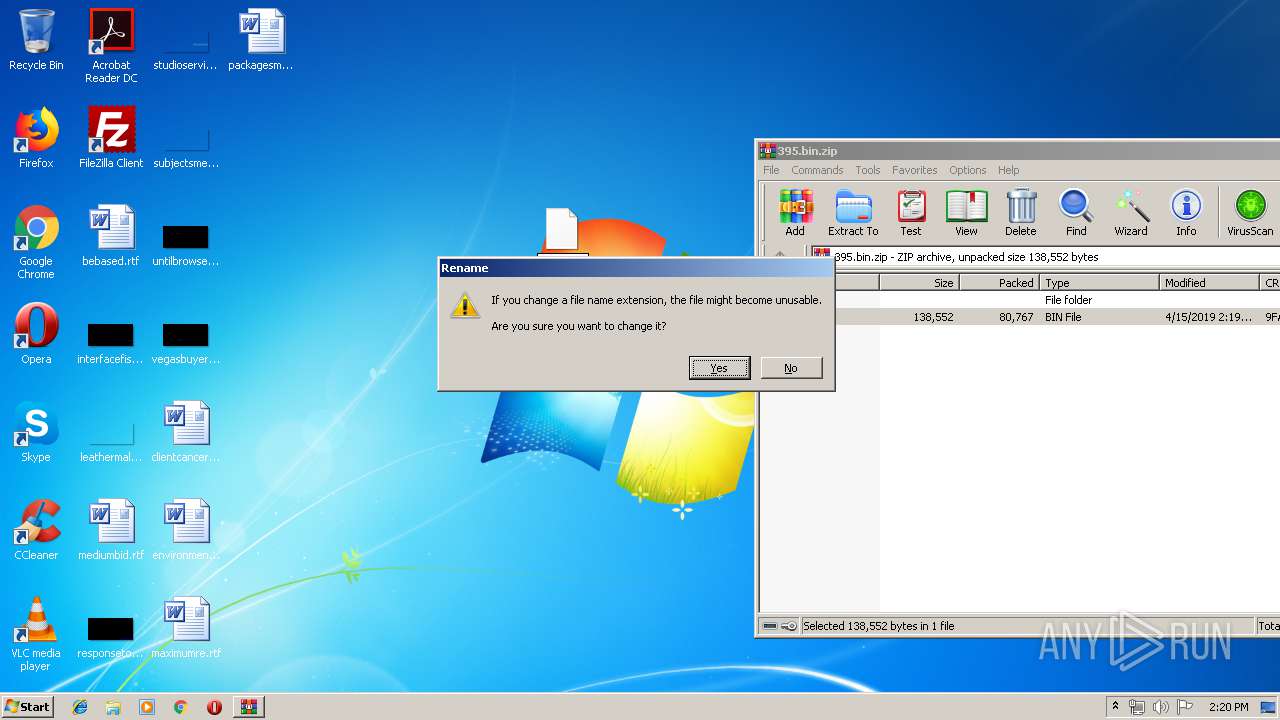
Starts itself from another location
- 395.exe (PID: 1892)
Application launched itself
- soundser.exe (PID: 2652)
- 395.exe (PID: 680)
Executable content was dropped or overwritten
- 395.exe (PID: 1892)
Connects to server without host name
- soundser.exe (PID: 3536)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:15 15:19:13 |
| ZipCRC: | 0x9fa955af |
| ZipCompressedSize: | 80767 |
| ZipUncompressedSize: | 138552 |
| ZipFileName: | 395.bin |
Total processes
37
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Users\admin\Desktop\395.exe" | C:\Users\admin\Desktop\395.exe | — | explorer.exe | |||||||||||
User: admin Company: 360. cn Integrity Level: MEDIUM Description: 360 FirstAid Exit code: 0 Version: 1, 0, 0, 1007 Modules
| |||||||||||||||
| 916 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\395.bin.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1892 | --72c83dad | C:\Users\admin\Desktop\395.exe | 395.exe | ||||||||||||
User: admin Company: 360. cn Integrity Level: MEDIUM Description: 360 FirstAid Exit code: 0 Version: 1, 0, 0, 1007 Modules
| |||||||||||||||
| 2652 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 395.exe | ||||||||||||
User: admin Company: 360. cn Integrity Level: MEDIUM Description: 360 FirstAid Exit code: 0 Version: 1, 0, 0, 1007 Modules
| |||||||||||||||
| 3536 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: 360. cn Integrity Level: MEDIUM Description: 360 FirstAid Exit code: 0 Version: 1, 0, 0, 1007 Modules
| |||||||||||||||
Total events
496
Read events
473
Write events
23
Delete events
0
Modification events
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\395.bin.zip | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (916) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3536) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
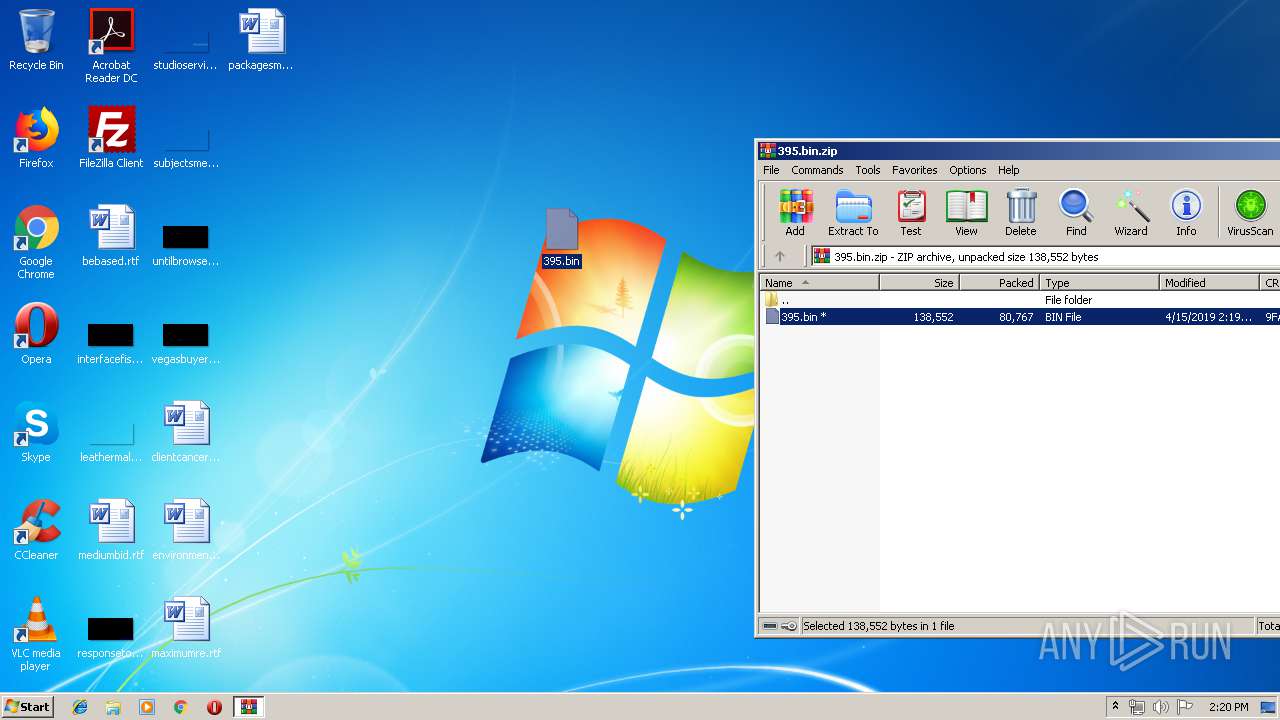
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 916 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb916.42099\395.bin | — | |
MD5:— | SHA256:— | |||
| 1892 | 395.exe | C:\Users\admin\AppData\Local\soundser\soundser.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
51
DNS requests
0
Threats
217
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3536 | soundser.exe | POST | — | 65.49.60.163:443 | http://65.49.60.163:443/health/guids/ringin/merge/ | US | — | — | malicious |
3536 | soundser.exe | POST | — | 138.68.139.199:443 | http://138.68.139.199:443/ringin/ | GB | — | — | malicious |
3536 | soundser.exe | POST | — | 190.117.206.153:443 | http://190.117.206.153:443/window/ | PE | — | — | malicious |
3536 | soundser.exe | POST | 404 | 45.33.35.103:8080 | http://45.33.35.103:8080/xian/symbols/ringin/ | US | xml | 345 b | malicious |
3536 | soundser.exe | POST | 404 | 192.155.90.90:7080 | http://192.155.90.90:7080/publish/ | US | xml | 345 b | malicious |
3536 | soundser.exe | POST | 404 | 210.2.86.72:8080 | http://210.2.86.72:8080/acquire/ | VN | xml | 345 b | malicious |
3536 | soundser.exe | POST | 404 | 187.188.166.192:80 | http://187.188.166.192/jit/between/ringin/ | MX | xml | 345 b | malicious |
3536 | soundser.exe | POST | 404 | 88.97.26.73:50000 | http://88.97.26.73:50000/ringin/ | GB | xml | 345 b | malicious |
3536 | soundser.exe | POST | 404 | 200.90.201.77:80 | http://200.90.201.77/publish/ | CL | xml | 345 b | malicious |
3536 | soundser.exe | POST | 404 | 200.114.142.40:8080 | http://200.114.142.40:8080/window/ | AR | xml | 345 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3536 | soundser.exe | 187.188.166.192:80 | — | TOTAL PLAY TELECOMUNICACIONES SA DE CV | MX | malicious |
3536 | soundser.exe | 88.215.2.29:80 | — | Gamma Telecom Holdings Ltd | GB | malicious |
3536 | soundser.exe | 187.137.162.145:443 | — | Uninet S.A. de C.V. | MX | malicious |
3536 | soundser.exe | 65.49.60.163:443 | — | Linode, LLC | US | malicious |
3536 | soundser.exe | 45.33.35.103:8080 | — | Linode, LLC | US | malicious |
— | — | 190.117.206.153:443 | — | America Movil Peru S.A.C. | PE | malicious |
— | — | 88.97.26.73:50000 | — | Zen Internet Ltd | GB | malicious |
3536 | soundser.exe | 185.86.148.222:8080 | — | Makonix SIA | SE | malicious |
— | — | 187.189.210.143:80 | — | TOTAL PLAY TELECOMUNICACIONES SA DE CV | MX | malicious |
3536 | soundser.exe | 67.241.81.253:8443 | — | Time Warner Cable Internet LLC | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3536 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 8 |
3536 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3536 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 23 |
3536 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3536 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3536 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3536 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
3536 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3536 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3536 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 18 |
144 ETPRO signatures available at the full report