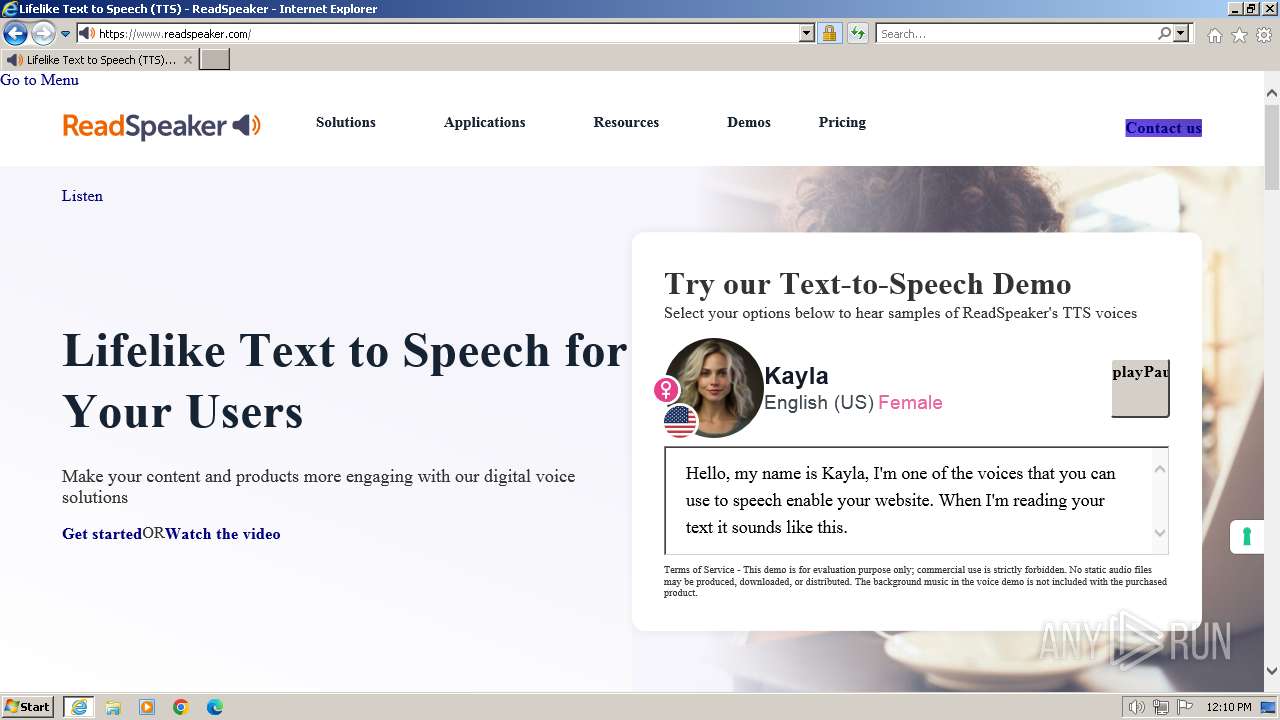
| URL: | https://cdn-as.readspeaker.com |
| Full analysis: | https://app.any.run/tasks/7f5c4825-f2b6-4343-8f7e-09d58bc1b7e7 |
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2023, 12:10:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B28FCCE0588529198CD3CC2360014E64 |
| SHA1: | 1F34B893C48E893E6D701B338C724FCB5DB64D17 |
| SHA256: | 6C6B8CC6E53C19A0D99B71EB09559B0BF635ED62BFE19F3C74142AC8F39CF380 |
| SSDEEP: | 3:N8cVWCGX:2cVW3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1432 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1492 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://cdn-as.readspeaker.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
20 723
Read events
20 636
Write events
79
Delete events
8
Modification events
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
57
Text files
249
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:D2F6DC4CF84B8592E5D60C2AE04BD12C | SHA256:F9B3061FD118A32084E374B131022C1A2F5C24BD1CAB3452B50FBFDBE4E89662 | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:6FC375C3BD65356CC6B7E22F976B5013 | SHA256:1D50BF5D49D1F8B5D5C2BA20151DE510D08C2A7063830C86087EEED46CFAEDAB | |||
| 1432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFC91.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFC92.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 1432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:546DDBCCA99A0D6D1D47356BE380F0CC | SHA256:44495E2BC43E329EE0C1206755C552913F232C6167403285949726F9990D96B9 | |||
| 1432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:A52427920BC96680DA81F8D2B988159D | SHA256:2457686D0A2B4FA59C25A52511BCAD7D08138EF42EB762BD29C59E0225B0AC42 | |||
| 1432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:6F5D413200C535136F01734ABD968982 | SHA256:D4E45D7D68BC5275FE72298A51DFA7C9FAB2628FD0511CF9053C3BA1A0B7DB09 | |||
| 1432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFCA2.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:D3A1221F214D3DACEC9F20DBAC57BEAA | SHA256:B65A46C4EE783907ADC7BB4476F95109A69AE87E86A7221607EB09E0AC4F5FBF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
79
DNS requests
40
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1432 | iexplore.exe | GET | 200 | 23.216.77.72:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?08963e2848236aa7 | unknown | compressed | 4.66 Kb | unknown |
1432 | iexplore.exe | GET | 200 | 23.216.77.72:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?16e53a13f7f2d96f | unknown | compressed | 4.66 Kb | unknown |
1432 | iexplore.exe | GET | 200 | 23.216.77.72:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7a9d8baceff24343 | unknown | compressed | 65.2 Kb | unknown |
1432 | iexplore.exe | GET | 200 | 23.216.77.72:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?608cb4ab6d3f68d3 | unknown | compressed | 65.2 Kb | unknown |
1432 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
1492 | iexplore.exe | GET | 304 | 23.216.77.72:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?67308e0939100114 | unknown | — | — | unknown |
1492 | iexplore.exe | GET | 304 | 23.216.77.72:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ce83dcf70518f919 | unknown | — | — | unknown |
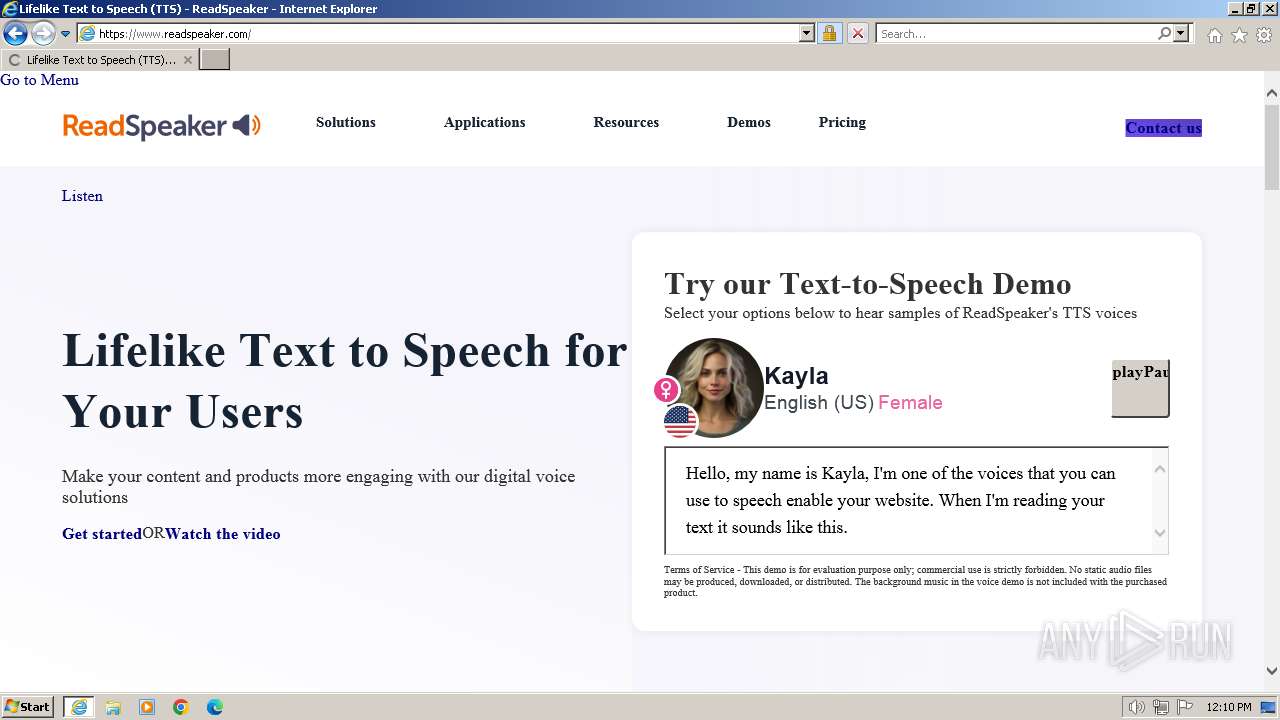
1432 | iexplore.exe | GET | 301 | 104.199.47.213:80 | http://www.readspeaker.com/ | unknown | html | 162 b | unknown |
1432 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | binary | 1.42 Kb | unknown |
1432 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1432 | iexplore.exe | 156.146.52.20:443 | cdn-as.readspeaker.com | Datacamp Limited | TR | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1432 | iexplore.exe | 23.216.77.72:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1432 | iexplore.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
1492 | iexplore.exe | 156.146.52.20:443 | cdn-as.readspeaker.com | Datacamp Limited | TR | unknown |
1492 | iexplore.exe | 23.216.77.72:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1432 | iexplore.exe | 104.199.47.213:80 | www.readspeaker.com | GOOGLE-CLOUD-PLATFORM | BE | unknown |
1432 | iexplore.exe | 104.199.47.213:443 | www.readspeaker.com | GOOGLE-CLOUD-PLATFORM | BE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn-as.readspeaker.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
www.readspeaker.com |
| unknown |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
cdn-eu.readspeaker.com |
| unknown |
cdn.iubenda.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1432 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
1432 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
1432 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code.jquery .com) |