| File name: | LoveLetter.vbs |
| Full analysis: | https://app.any.run/tasks/1ef83f39-9684-40f6-87f1-e12fff8f1825 |
| Verdict: | Malicious activity |
| Analysis date: | June 02, 2024, 09:17:30 |
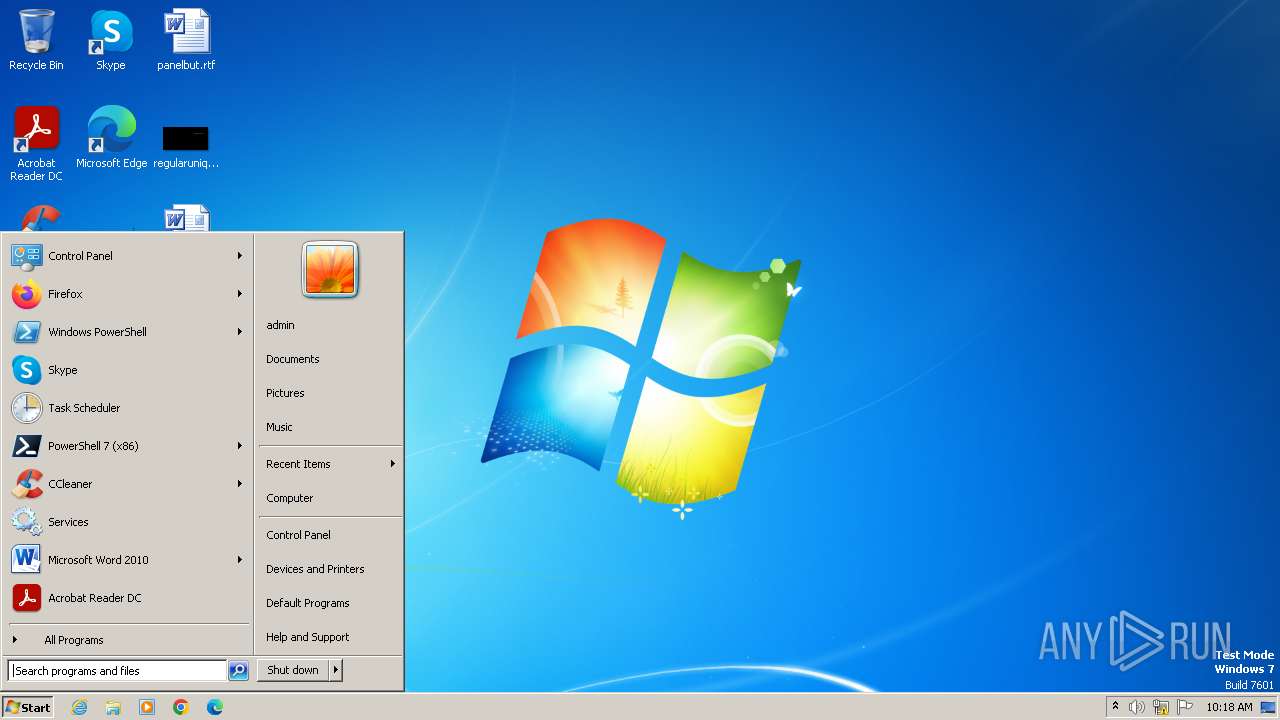
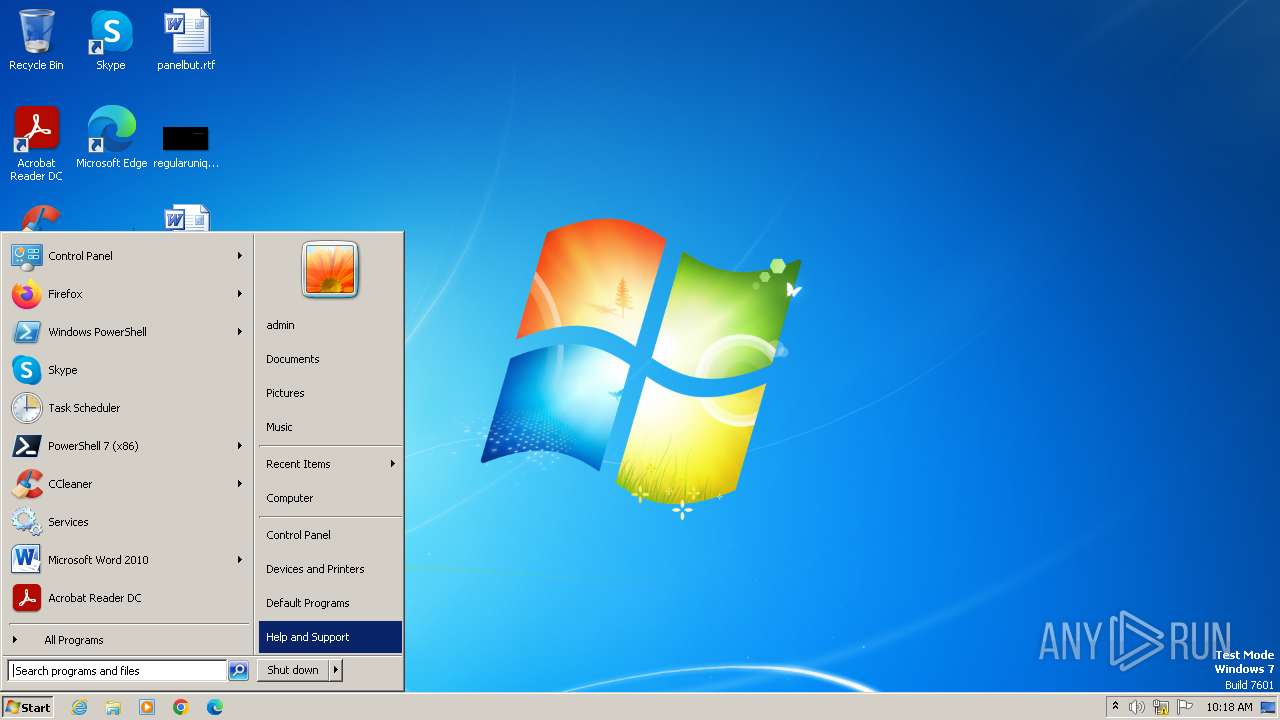
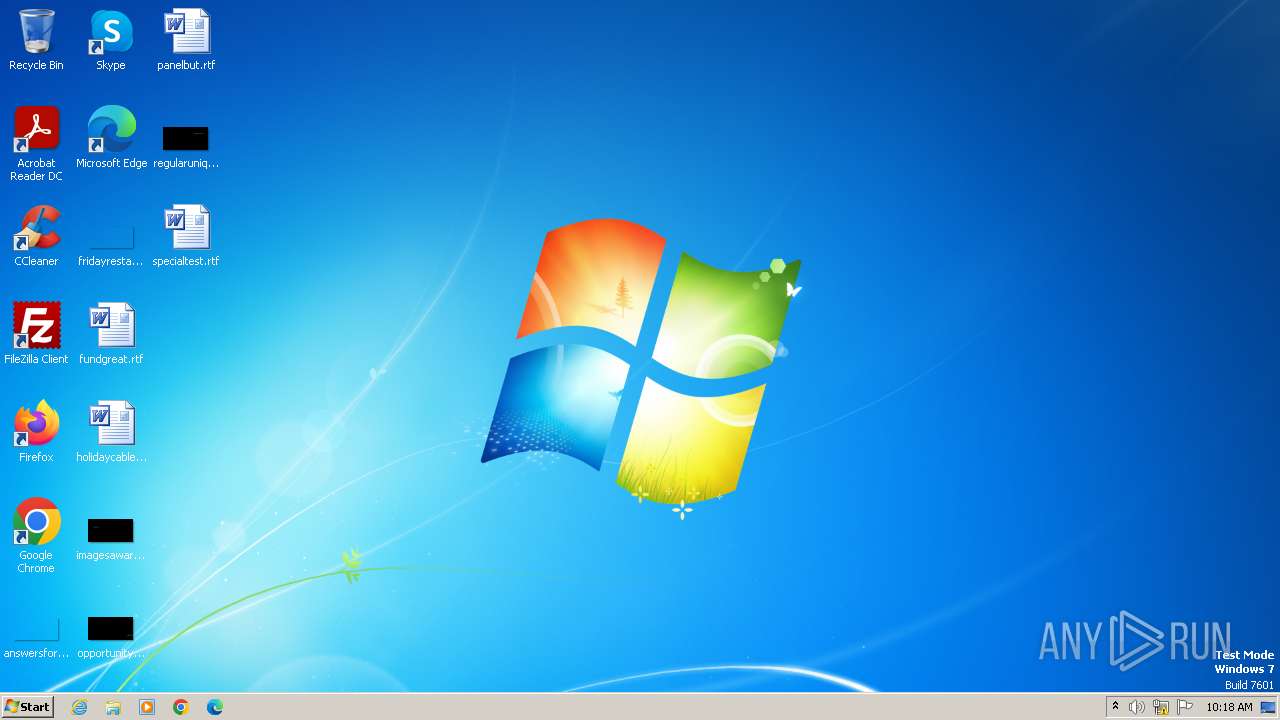
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-c |
| File info: | C source, ASCII text, with CRLF line terminators |
| MD5: | 0163E220B01604D4F085498F233195B5 |
| SHA1: | EB23E6239ACA35E64D478589630A4387C8314A1E |
| SHA256: | 6C65FEEF8C7FD68585E3B91CD4180211889D75C47776057D996717A7F0699D23 |
| SSDEEP: | 192:OoYL5Z+tEHPFKm/zMGMQMQMNMmMuMFMmMwMUMhAMPjlJ02A5iToEcHs3jSe8cBEW:OhNk6HPFKm/zPl18xX0xZxiAwjzlYiT7 |
MALICIOUS
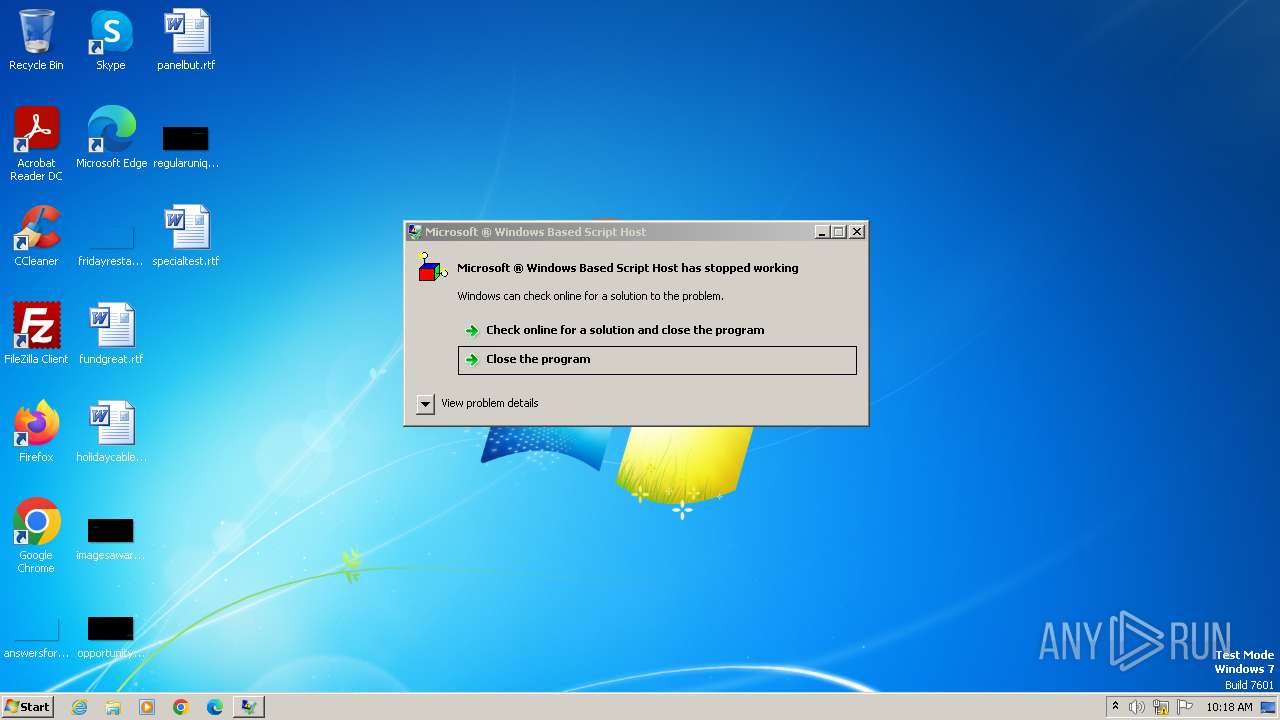
Opens a text file (SCRIPT)
- wscript.exe (PID: 3984)
Creates a writable file in the system directory
- wscript.exe (PID: 3984)
Modifies registry startup key (SCRIPT)
- wscript.exe (PID: 3984)
Deletes a file (SCRIPT)
- wscript.exe (PID: 3984)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 3984)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 3984)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 3984)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 3984)
SUSPICIOUS
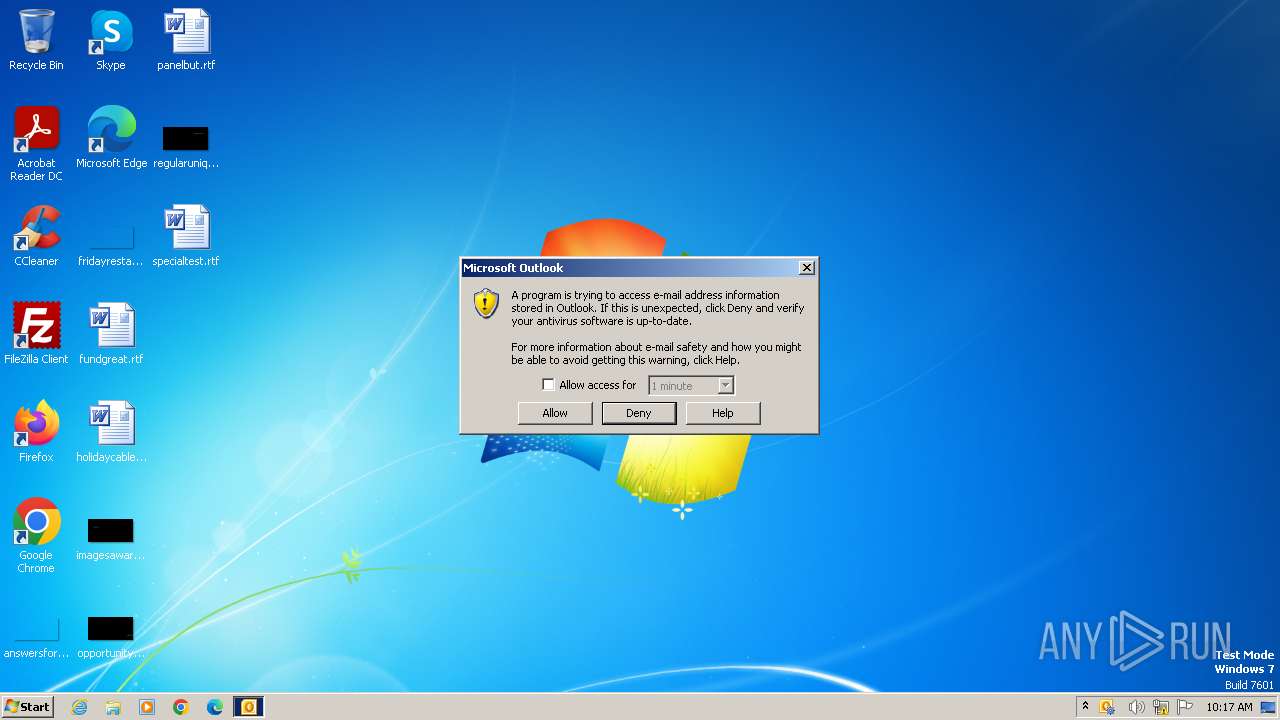
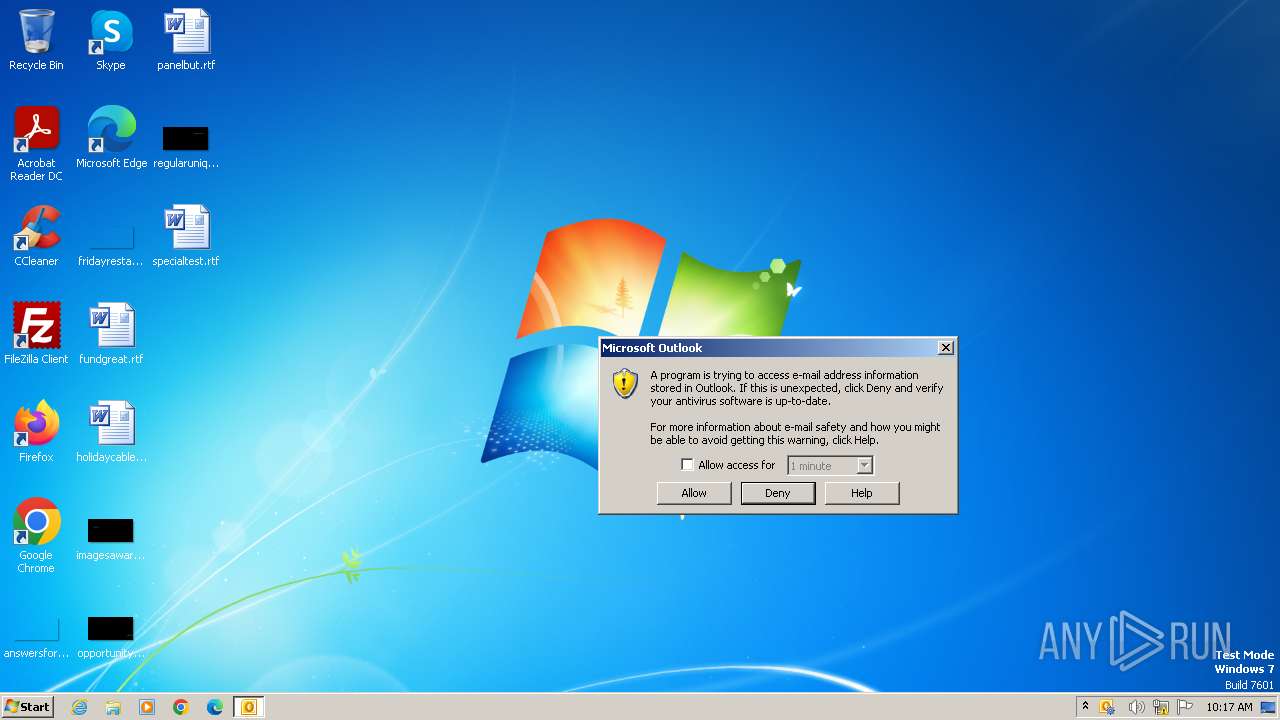
Changes the title of the Internet Explorer window
- wscript.exe (PID: 3984)
Gets a collection of all available drive names (SCRIPT)
- wscript.exe (PID: 3984)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 3984)
Gets the drive type (SCRIPT)
- wscript.exe (PID: 3984)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 3984)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3984)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 3984)
Changes the Home page of Internet Explorer
- wscript.exe (PID: 3984)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 3984)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3984 | "C:\Windows\System32\WScript.exe" C:\Users\admin\AppData\Local\Temp\LoveLetter.vbs | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 3221225477 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 4028 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
5 455
Read events
5 347
Write events
87
Delete events
21
Modification events
| (PID) Process: | (3984) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MSKernel32 |
Value: C:\Windows\System32\MSKernel32.vbs | |||
| (PID) Process: | (3984) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | Start Page |
Value: http://www.skyinet.net/~young1s/HJKhjnwerhjkxcvytwertnMTFwetrdsfmhPnjw6587345gvsdf7679njbvYT/WIN-BUGSFIX.exe | |||
| (PID) Process: | (4028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (4028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (4028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (4028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (4028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (4028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (4028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (4028) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
Executable files
0
Suspicious files
1
Text files
96
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4028 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR3644.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4028 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 4028 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 3984 | wscript.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Reader\WebResources\Resource1\static\js\plugins\activity-badge\images\avatar.jpg | text | |
MD5:0163E220B01604D4F085498F233195B5 | SHA256:6C65FEEF8C7FD68585E3B91CD4180211889D75C47776057D996717A7F0699D23 | |||
| 3984 | wscript.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Reader\Tracker\main.css | text | |
MD5:0163E220B01604D4F085498F233195B5 | SHA256:6C65FEEF8C7FD68585E3B91CD4180211889D75C47776057D996717A7F0699D23 | |||
| 3984 | wscript.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Reader\WebResources\Resource1\static\css\main-cef-win8.css | text | |
MD5:0163E220B01604D4F085498F233195B5 | SHA256:6C65FEEF8C7FD68585E3B91CD4180211889D75C47776057D996717A7F0699D23 | |||
| 3984 | wscript.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Reader\WebResources\Resource1\static\css\main-cef-mac.css | text | |
MD5:0163E220B01604D4F085498F233195B5 | SHA256:6C65FEEF8C7FD68585E3B91CD4180211889D75C47776057D996717A7F0699D23 | |||
| 4028 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{8EC3D004-FC63-45B9-927D-6B9B692BB3AE}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 3984 | wscript.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Reader\WebResources\Resource1\static\css\main-cef-ui-theme.css | text | |
MD5:0163E220B01604D4F085498F233195B5 | SHA256:6C65FEEF8C7FD68585E3B91CD4180211889D75C47776057D996717A7F0699D23 | |||
| 3984 | wscript.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Reader\WebResources\Resource1\static\css\main-cef.css | text | |
MD5:0163E220B01604D4F085498F233195B5 | SHA256:6C65FEEF8C7FD68585E3B91CD4180211889D75C47776057D996717A7F0699D23 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4028 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
dns.msftncsi.com |
| shared |