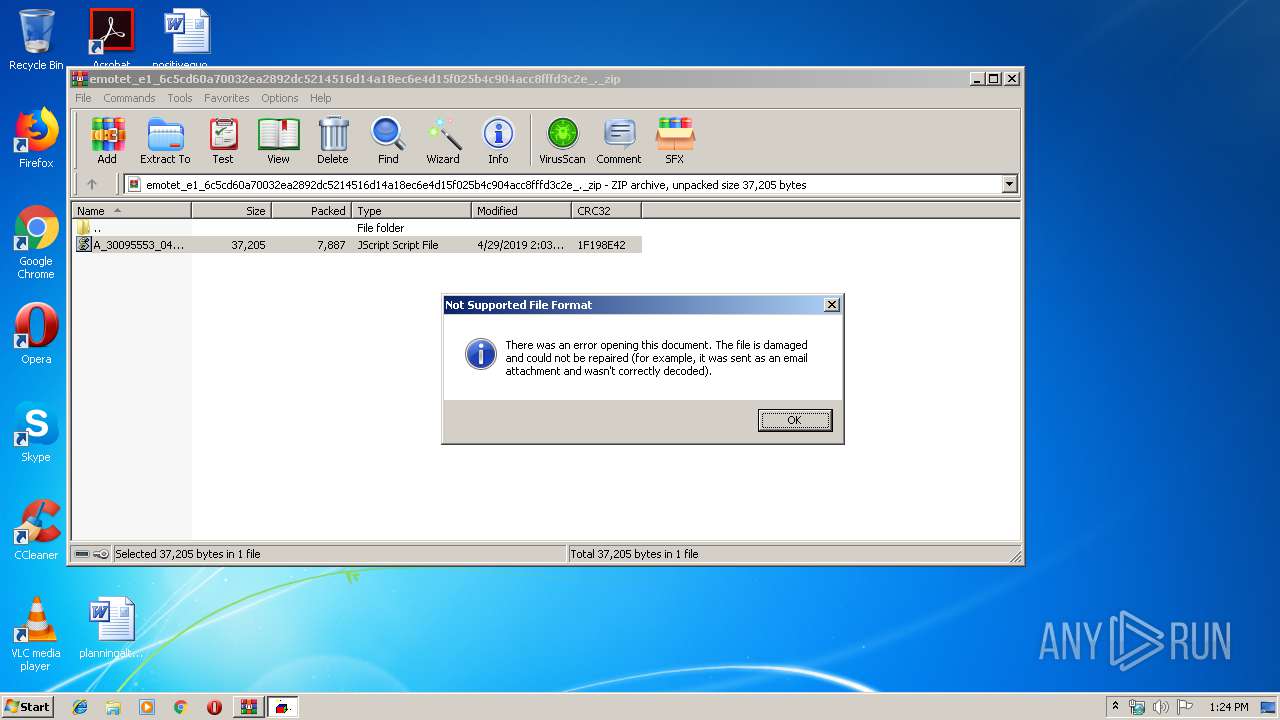
| File name: | emotet_e1_6c5cd60a70032ea2892dc5214516d14a18ec6e4d15f025b4c904acc8fffd3c2e_._zip |
| Full analysis: | https://app.any.run/tasks/bf07be94-1e62-4eab-ac2a-e22eb0bcc6d0 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 12:23:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 86682ACD72BDF8F2618F340CC1243215 |
| SHA1: | DB7BA045B3B99E0B543D148A849BAA7B0D605C5A |
| SHA256: | 6C5CD60A70032EA2892DC5214516D14A18EC6E4D15F025B4C904ACC8FFFD3C2E |
| SSDEEP: | 192:aaQ2fNH700tel5ucRtJU3iCuU6RsW65OWPGSIMrn:9Q2ftluRUyChW65OYIen |
MALICIOUS
Changes settings of System certificates
- WScript.exe (PID: 3220)
SUSPICIOUS
Executes scripts
- WinRAR.exe (PID: 3848)
Adds / modifies Windows certificates
- WScript.exe (PID: 3220)
INFO
Modifies the open verb of a shell class
- rundll32.exe (PID: 2940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
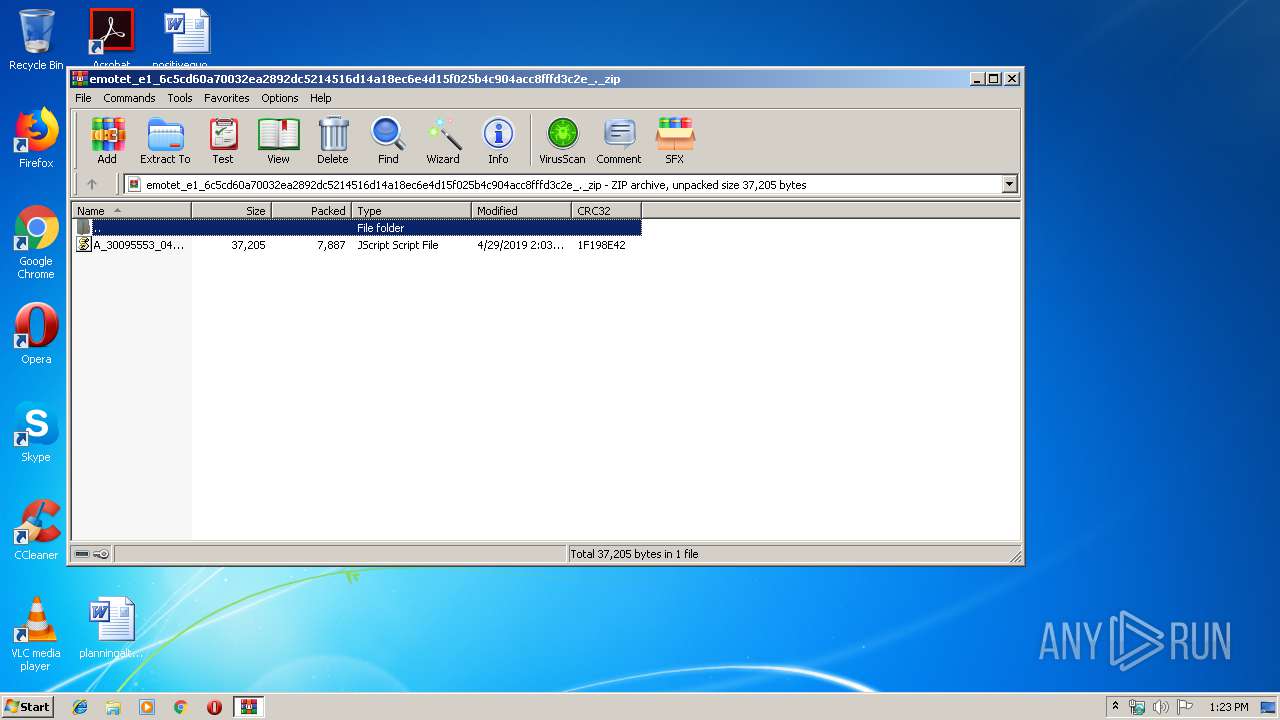
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:29 02:03:00 |
| ZipCRC: | 0x1f198e42 |
| ZipCompressedSize: | 7887 |
| ZipUncompressedSize: | 37205 |
| ZipFileName: | A_30095553_04292019.js |
Total processes
35
Monitored processes
3
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
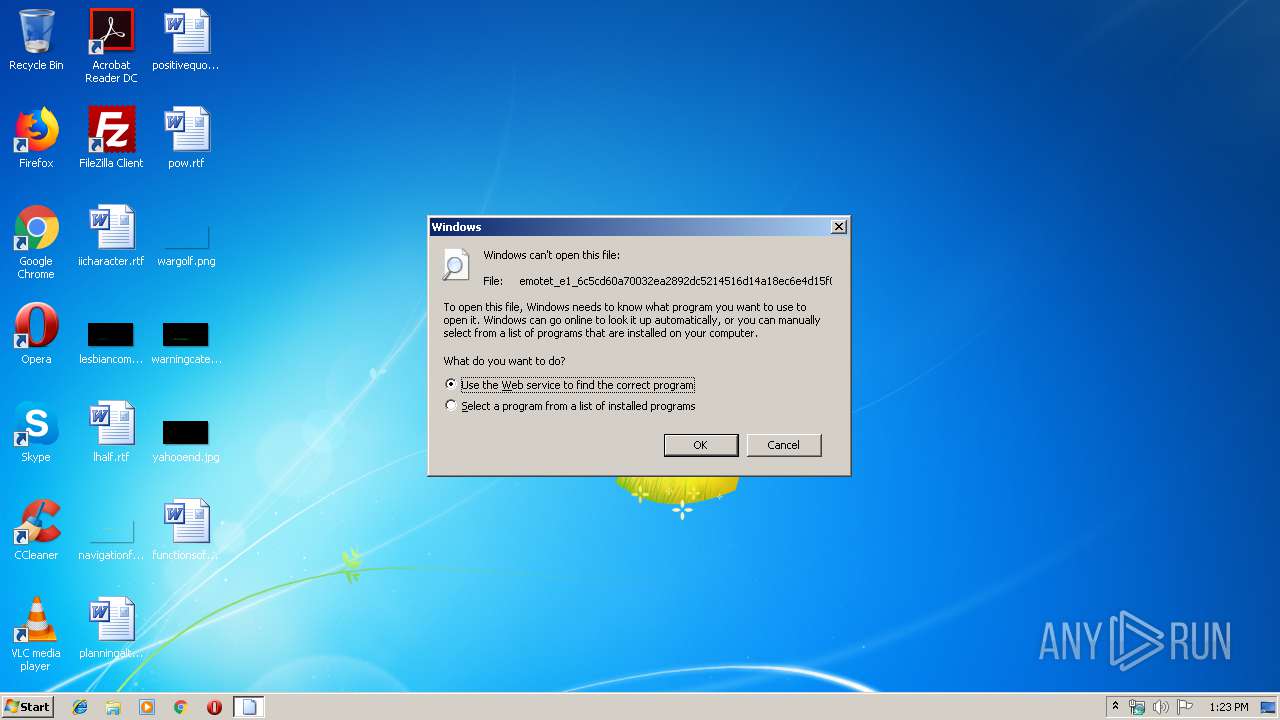
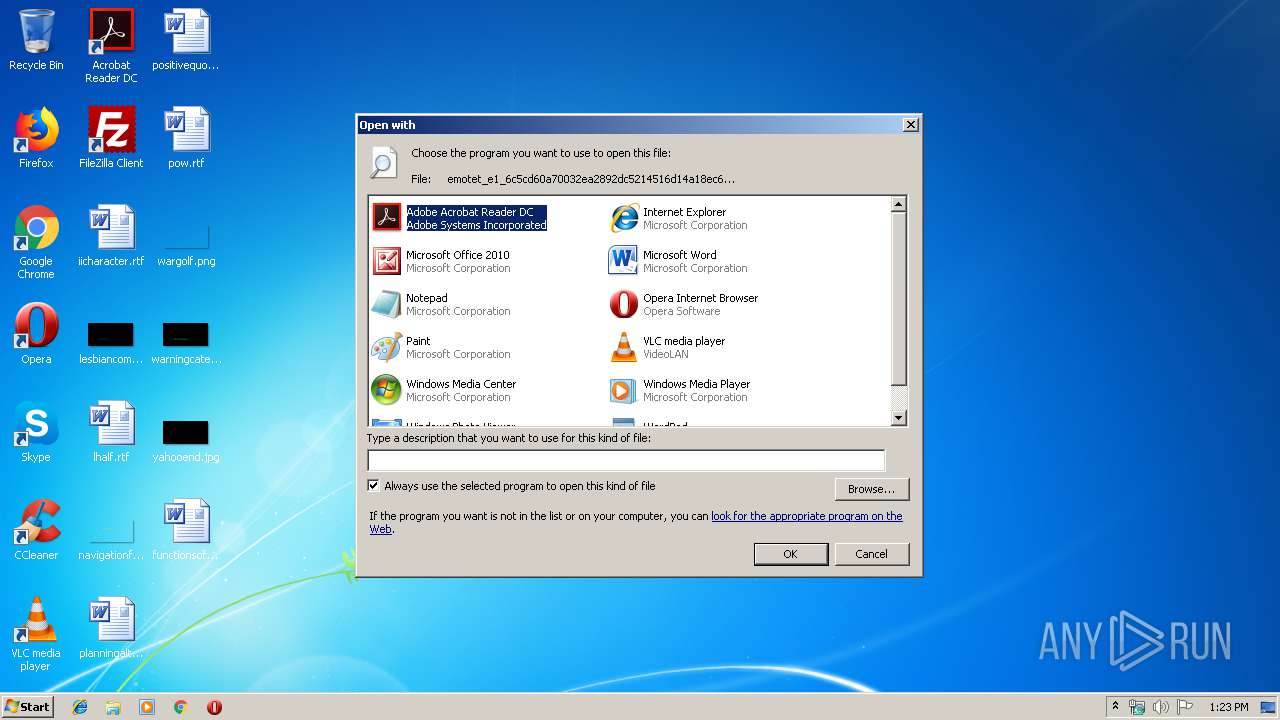
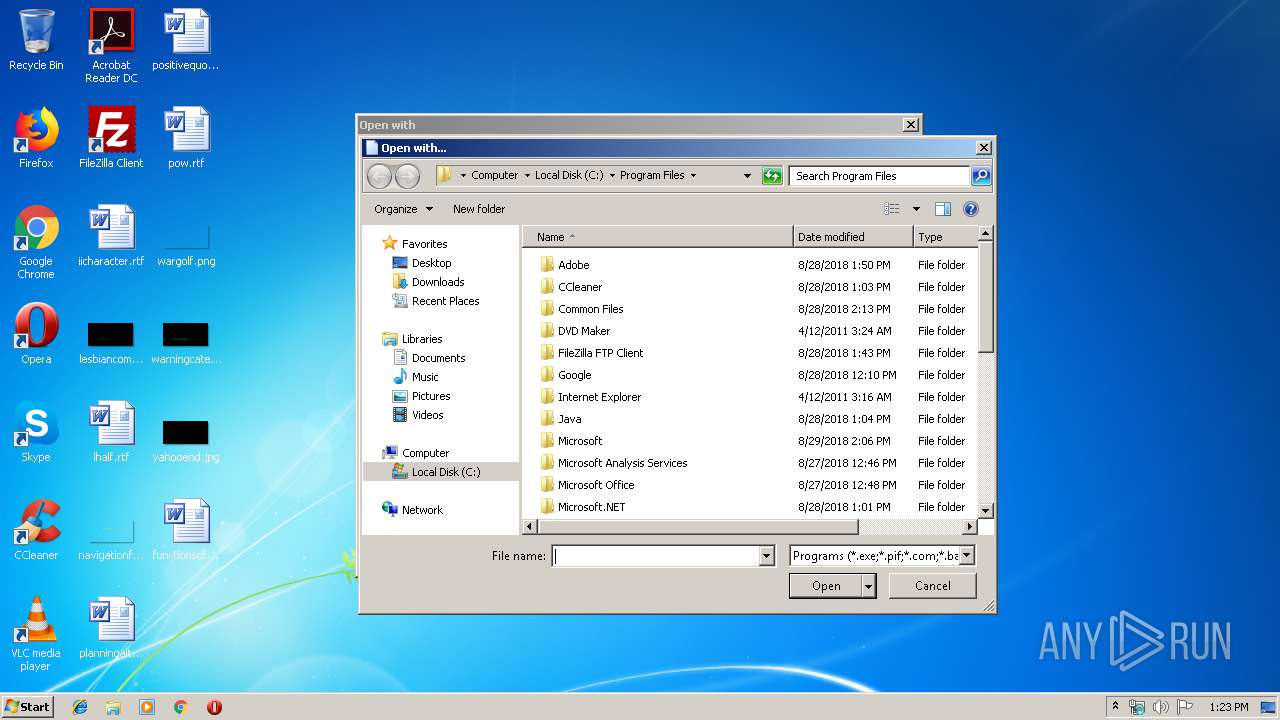
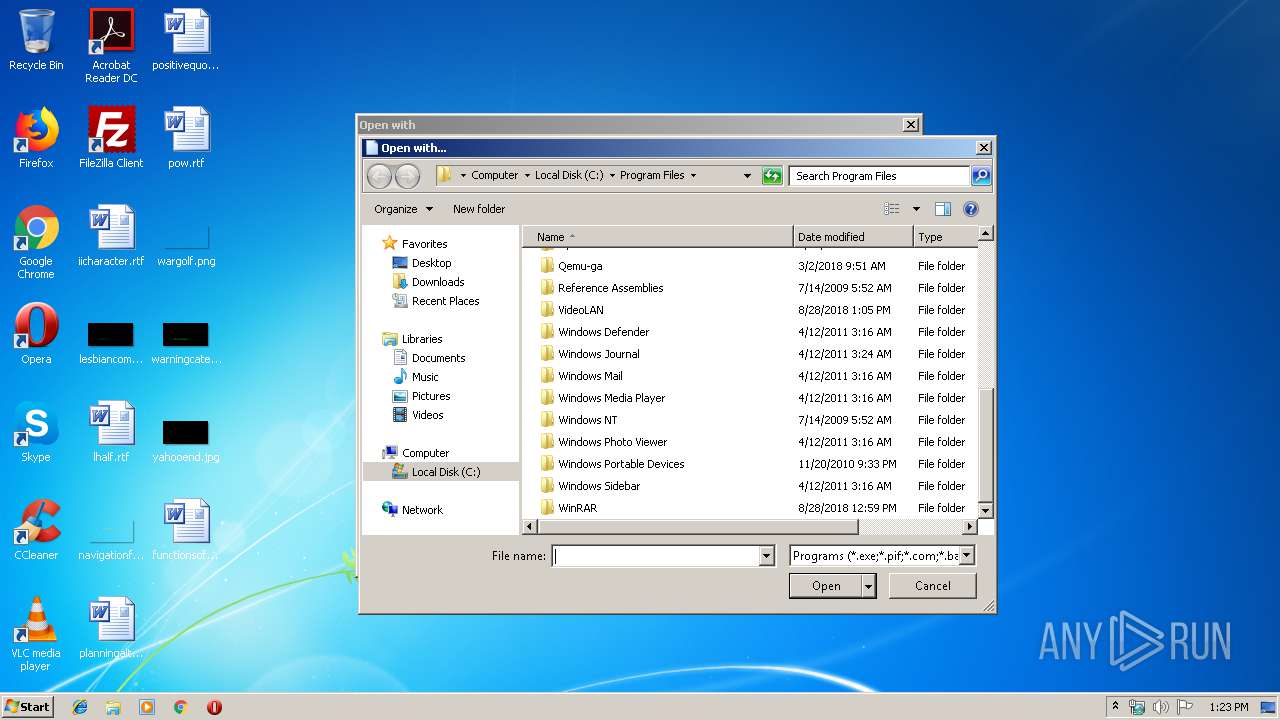
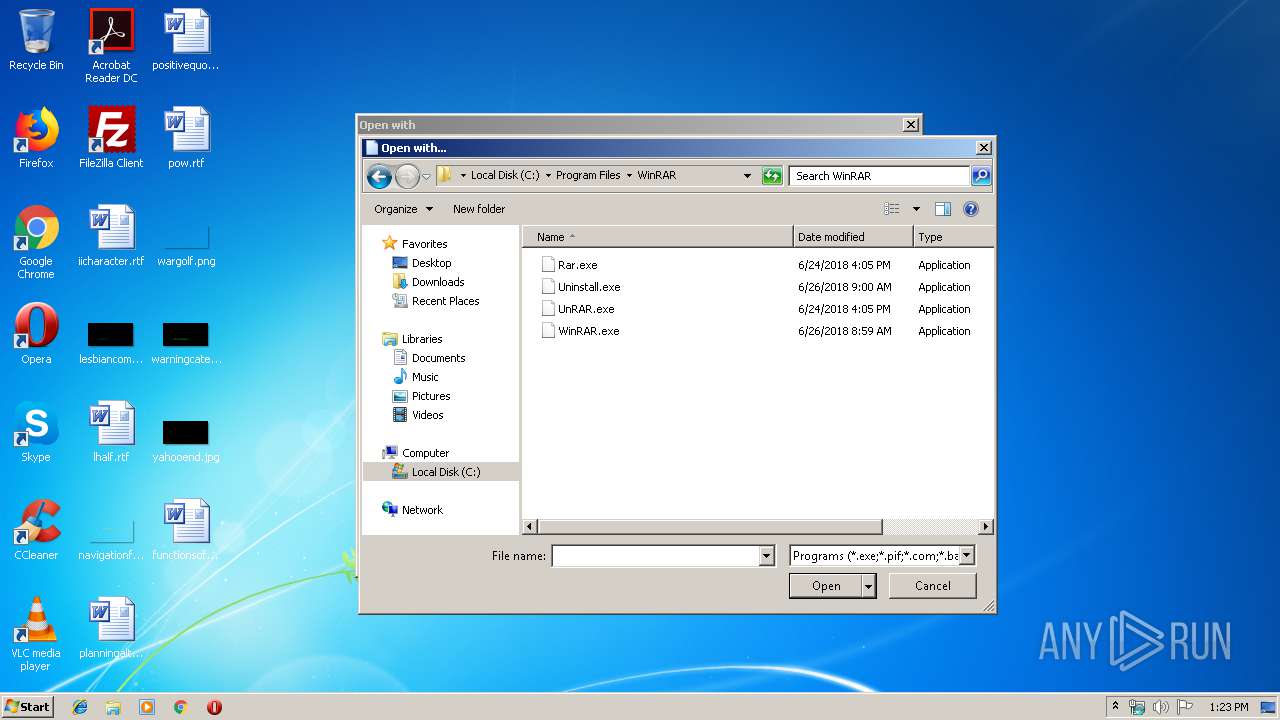
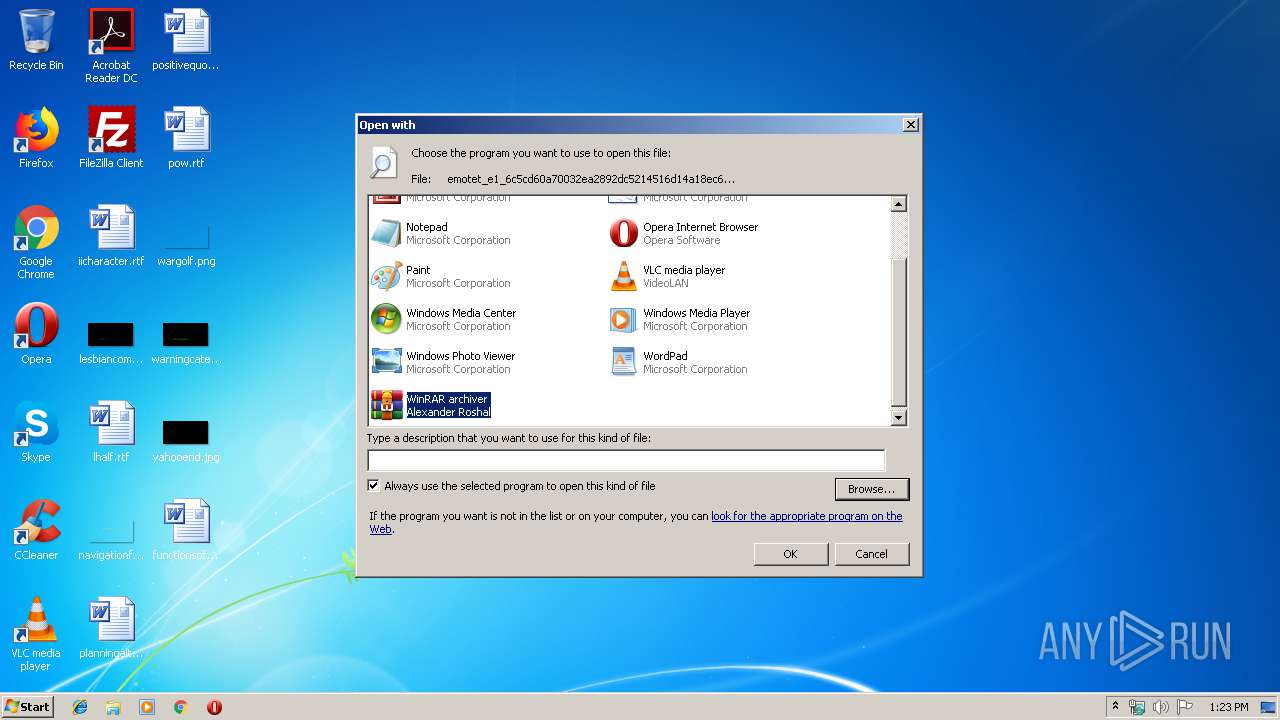
| 2940 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\emotet_e1_6c5cd60a70032ea2892dc5214516d14a18ec6e4d15f025b4c904acc8fffd3c2e_._zip | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3220 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa3848.14426\A_30095553_04292019.js" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3848 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\emotet_e1_6c5cd60a70032ea2892dc5214516d14a18ec6e4d15f025b4c904acc8fffd3c2e_._zip" | C:\Program Files\WinRAR\WinRAR.exe | — | rundll32.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 263
Read events
1 065
Write events
196
Delete events
2
Modification events
| (PID) Process: | (2940) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (2940) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2940) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2940) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Internet Explorer\iexplore.exe |
Value: Internet Explorer | |||
| (PID) Process: | (2940) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2940) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2940) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2940) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2940) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2940) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3848.14426\A_30095553_04292019.js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
5
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3220 | WScript.exe | GET | 404 | 104.24.123.71:80 | http://608design.com/mainto/6Cgy/ | US | xml | 345 b | malicious |
3220 | WScript.exe | GET | 404 | 202.92.6.35:80 | http://autmont.com/wp/rZzwq/ | VN | xml | 345 b | unknown |
3220 | WScript.exe | GET | 404 | 104.196.22.72:80 | http://asharqiya.com/ar/Ith/ | US | xml | 345 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3220 | WScript.exe | 139.159.158.121:443 | cssshk.com | — | CN | unknown |
3220 | WScript.exe | 52.220.199.21:443 | beutify.com | Amazon.com, Inc. | SG | unknown |
3220 | WScript.exe | 104.24.123.71:80 | 608design.com | Cloudflare Inc | US | shared |
3220 | WScript.exe | 202.92.6.35:80 | autmont.com | VNPT Corp | VN | unknown |
3220 | WScript.exe | 104.196.22.72:80 | asharqiya.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cssshk.com |
| malicious |
beutify.com |
| unknown |
608design.com |
| malicious |
asharqiya.com |
| suspicious |
autmont.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3220 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3220 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
3220 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |