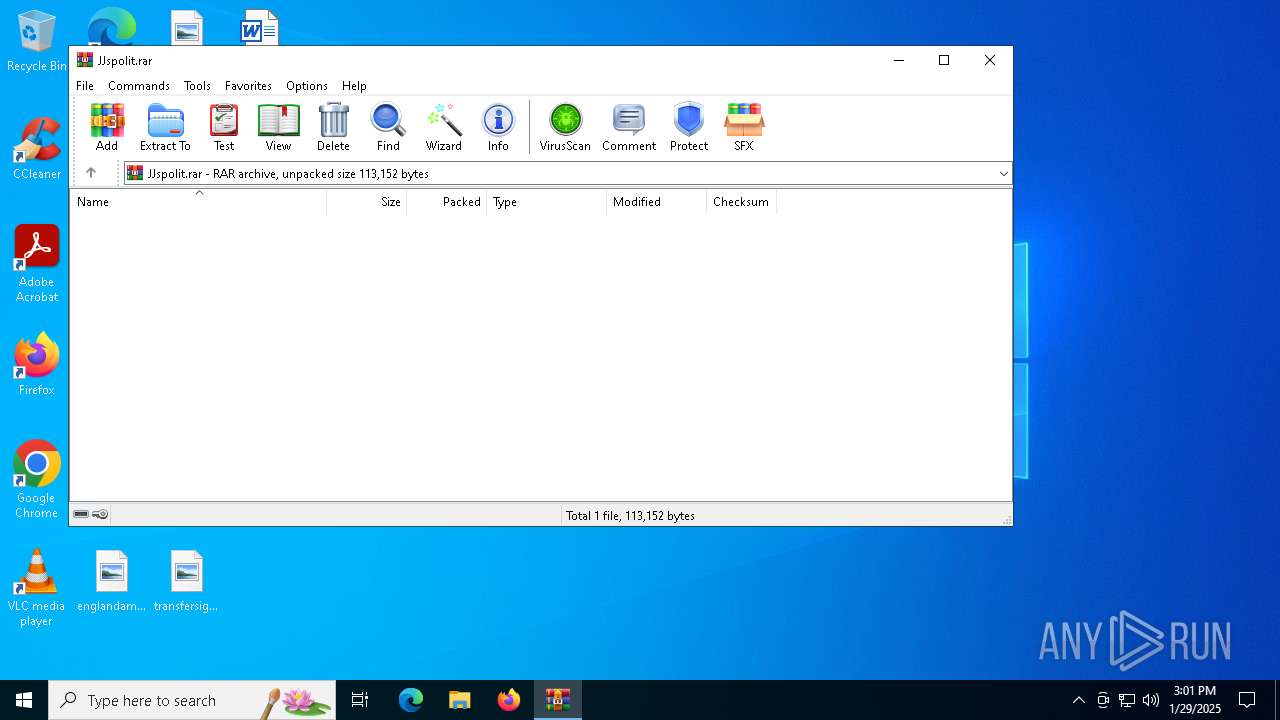
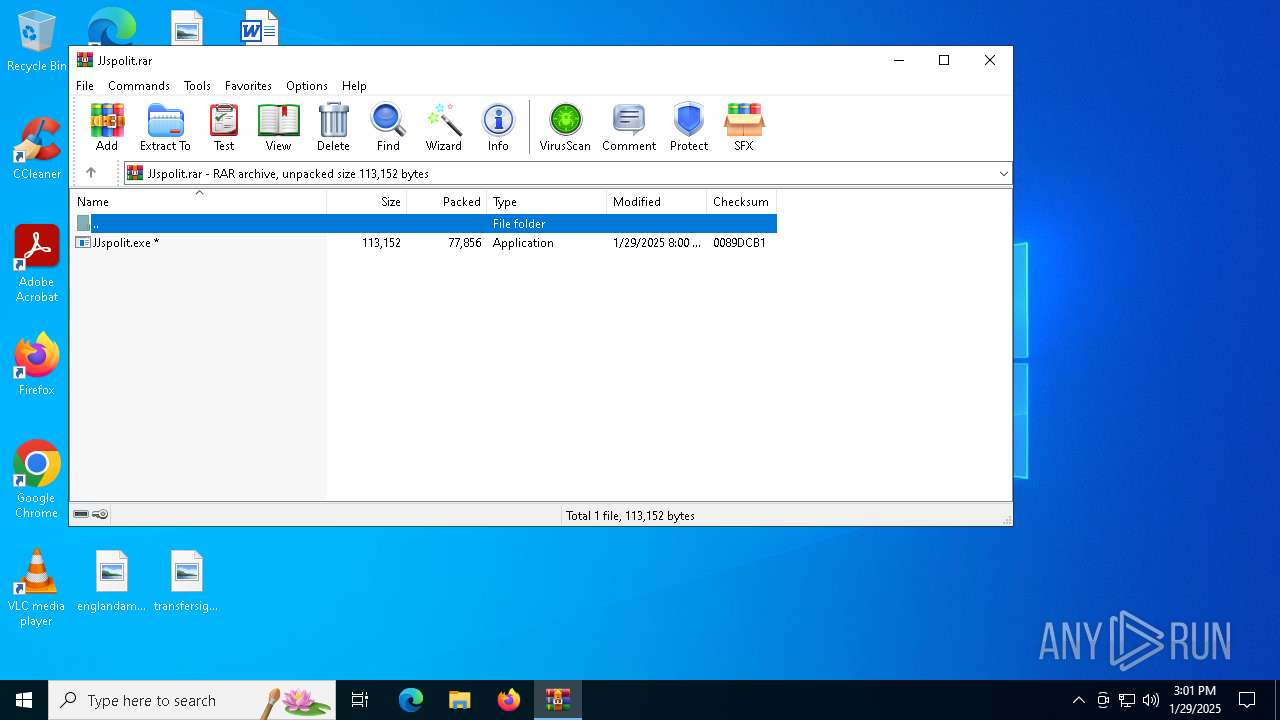
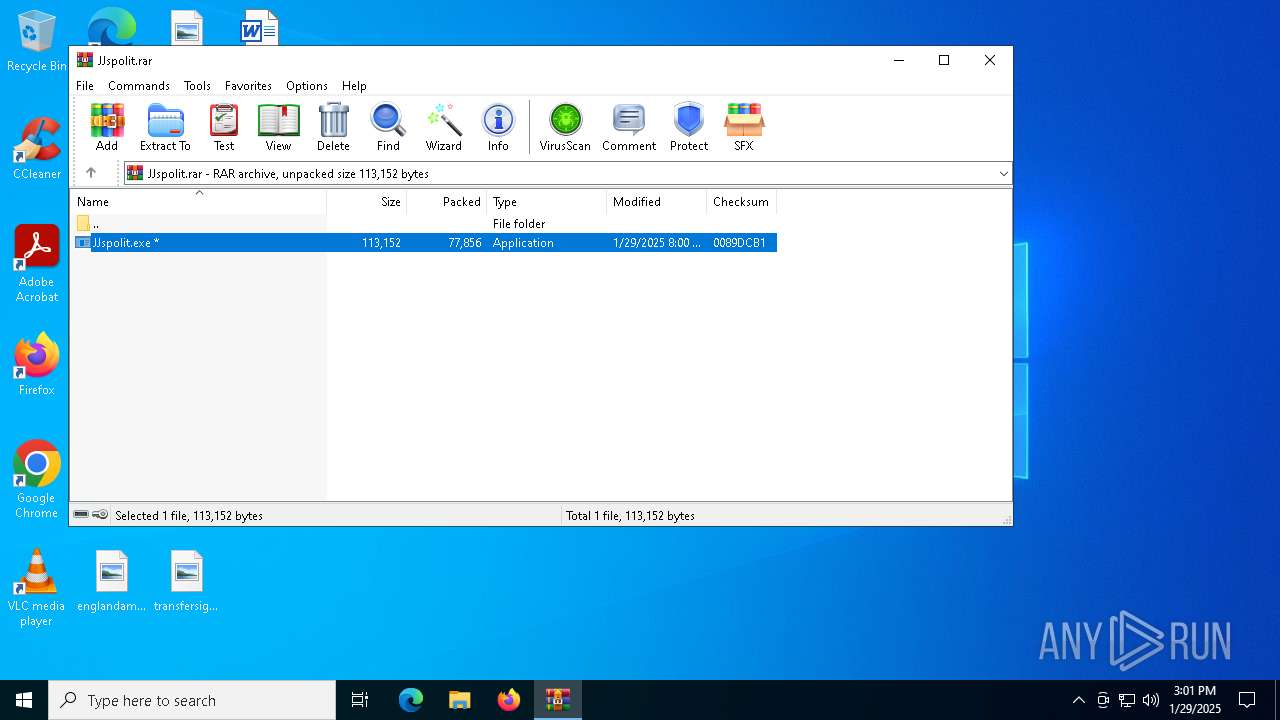
| File name: | JJspolit.rar |
| Full analysis: | https://app.any.run/tasks/710a0bf0-89f7-486a-8af5-46bbe85d75af |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2025, 15:00:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A6012BB08A7C25AD032FD31F815C7987 |
| SHA1: | 45CE05049E8740A21A28C89CF4918FAEFE1A1E6C |
| SHA256: | 6C50296F9DFD602721D55416F71A74BDC5F774E617DF5040829C18809E1031F7 |
| SSDEEP: | 1536:8Hl4m1LD6YPfTtE/dNf8czZ4VWyPNtlqF6O1JCvSuMpTSTZd:8DSkfTtELf1z4WyXls1kPMsZd |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes application which crashes
- JJspolit.exe (PID: 3988)
- JJspolit.exe (PID: 7120)
- JJspolit.exe (PID: 6764)
Checks for external IP
- JJspolit.exe (PID: 3988)
- svchost.exe (PID: 2192)
- JJspolit.exe (PID: 6764)
- JJspolit.exe (PID: 7120)
INFO
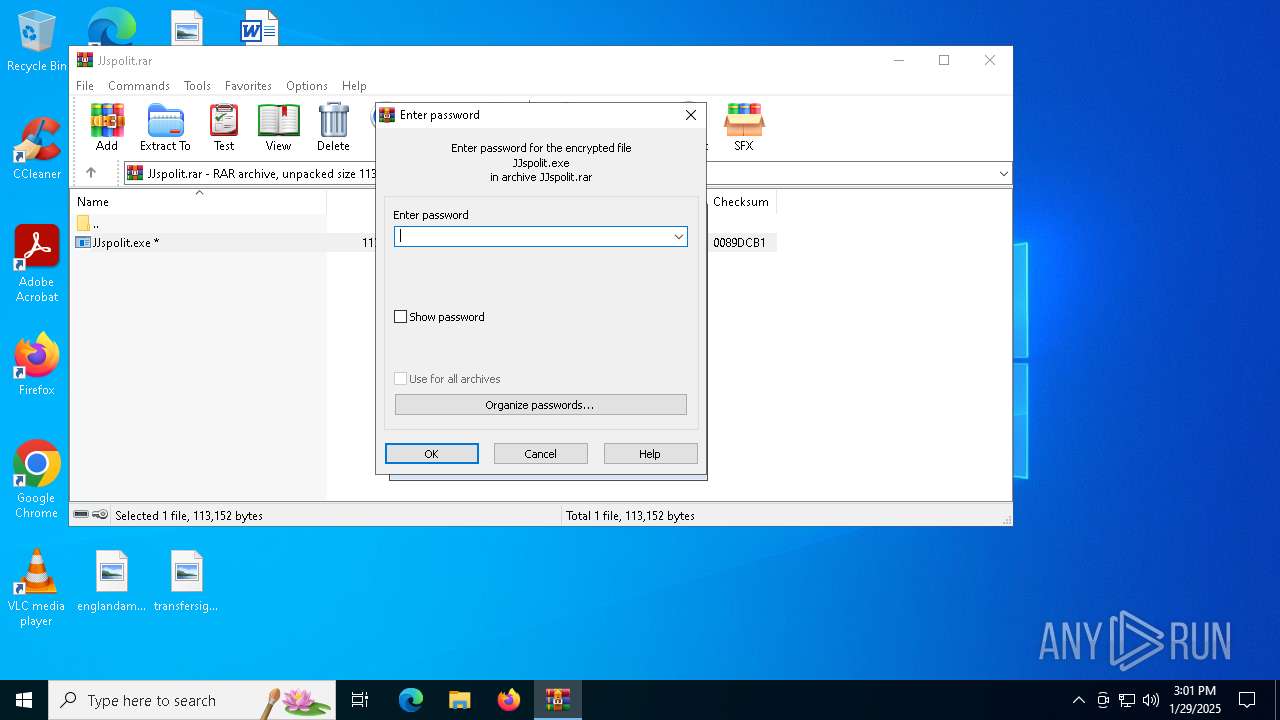
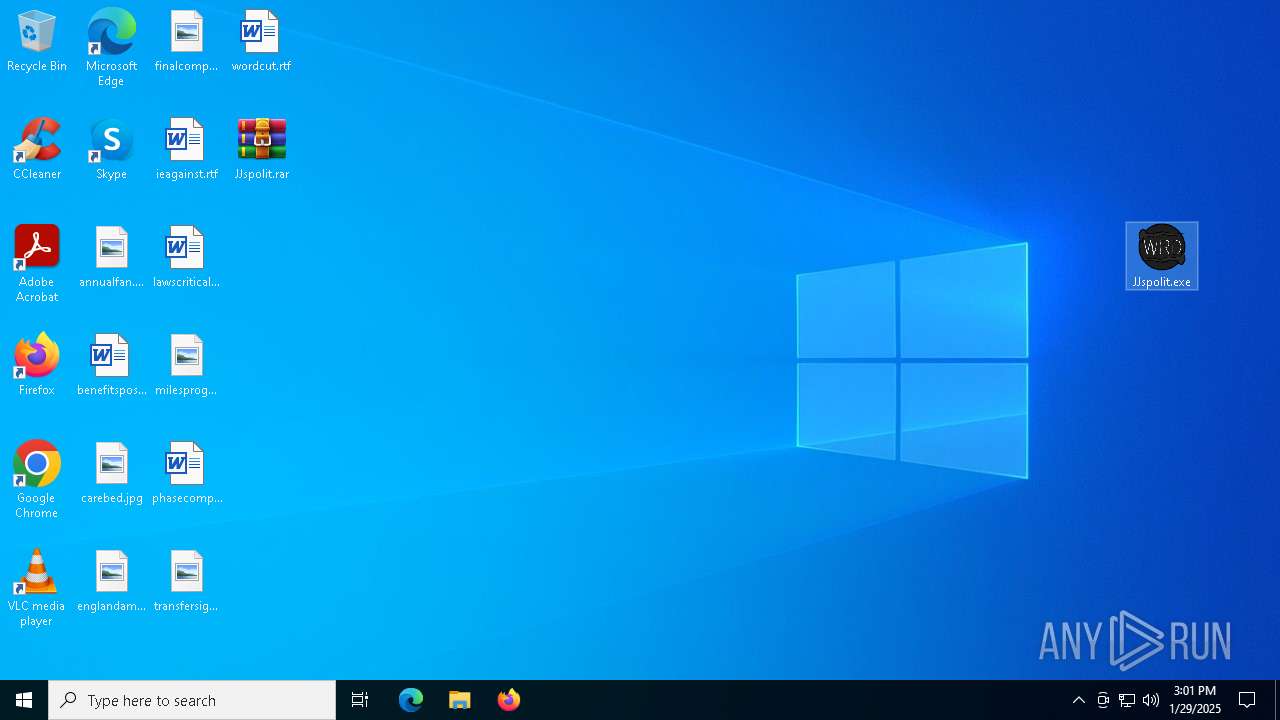
Manual execution by a user
- JJspolit.exe (PID: 3988)
- JJspolit.exe (PID: 6764)
- JJspolit.exe (PID: 6768)
- JJspolit.exe (PID: 5036)
- JJspolit.exe (PID: 7052)
- JJspolit.exe (PID: 6968)
- JJspolit.exe (PID: 6960)
- JJspolit.exe (PID: 7120)
- JJspolit.exe (PID: 6928)
- JJspolit.exe (PID: 2996)
- JJspolit.exe (PID: 644)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6316)
Disables trace logs
- JJspolit.exe (PID: 3988)
- JJspolit.exe (PID: 6764)
- JJspolit.exe (PID: 7120)
Reads the computer name
- JJspolit.exe (PID: 3988)
- JJspolit.exe (PID: 6764)
- JJspolit.exe (PID: 6768)
- JJspolit.exe (PID: 5036)
- JJspolit.exe (PID: 7120)
- JJspolit.exe (PID: 7052)
- JJspolit.exe (PID: 6960)
- JJspolit.exe (PID: 644)
- JJspolit.exe (PID: 2996)
Checks supported languages
- JJspolit.exe (PID: 3988)
- JJspolit.exe (PID: 6764)
- JJspolit.exe (PID: 6768)
- JJspolit.exe (PID: 5036)
- JJspolit.exe (PID: 7052)
- JJspolit.exe (PID: 6968)
- JJspolit.exe (PID: 6960)
- JJspolit.exe (PID: 7120)
- JJspolit.exe (PID: 6928)
- JJspolit.exe (PID: 644)
- JJspolit.exe (PID: 2996)
Reads Environment values
- JJspolit.exe (PID: 3988)
- JJspolit.exe (PID: 6764)
- JJspolit.exe (PID: 7120)
Reads the machine GUID from the registry
- JJspolit.exe (PID: 3988)
- JJspolit.exe (PID: 6764)
- JJspolit.exe (PID: 6768)
- JJspolit.exe (PID: 6968)
- JJspolit.exe (PID: 7120)
- JJspolit.exe (PID: 6960)
- JJspolit.exe (PID: 6928)
- JJspolit.exe (PID: 644)
Checks proxy server information
- WerFault.exe (PID: 5256)
- JJspolit.exe (PID: 6764)
- JJspolit.exe (PID: 7120)
Creates files or folders in the user directory
- WerFault.exe (PID: 5256)
- WerFault.exe (PID: 7164)
Reads the software policy settings
- WerFault.exe (PID: 5256)
- WerFault.exe (PID: 7164)
- WerFault.exe (PID: 836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 77856 |
| UncompressedSize: | 113152 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | JJspolit.exe |
Total processes
149
Monitored processes
16
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | "C:\Users\admin\Desktop\JJspolit.exe" | C:\Users\admin\Desktop\JJspolit.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 6.4.12.0 Modules
| |||||||||||||||
| 836 | C:\WINDOWS\system32\WerFault.exe -u -p 7120 -s 1796 | C:\Windows\System32\WerFault.exe | JJspolit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\Desktop\JJspolit.exe" | C:\Users\admin\Desktop\JJspolit.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 6.4.12.0 Modules
| |||||||||||||||
| 3988 | "C:\Users\admin\Desktop\JJspolit.exe" | C:\Users\admin\Desktop\JJspolit.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 2148734499 Version: 6.4.12.0 Modules
| |||||||||||||||
| 5036 | "C:\Users\admin\Desktop\JJspolit.exe" | C:\Users\admin\Desktop\JJspolit.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 6.4.12.0 Modules
| |||||||||||||||
| 5256 | C:\WINDOWS\system32\WerFault.exe -u -p 3988 -s 1776 | C:\Windows\System32\WerFault.exe | JJspolit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6316 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\JJspolit.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6764 | "C:\Users\admin\Desktop\JJspolit.exe" | C:\Users\admin\Desktop\JJspolit.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 2148734499 Version: 6.4.12.0 Modules
| |||||||||||||||
| 6768 | "C:\Users\admin\Desktop\JJspolit.exe" | C:\Users\admin\Desktop\JJspolit.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 6.4.12.0 Modules
| |||||||||||||||
Total events
14 448
Read events
14 414
Write events
34
Delete events
0
Modification events
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\JJspolit.rar | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
1
Suspicious files
10
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5256 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_JJspolit.exe_46d523d52922dfda817f7fa85c4b156db1f9c11_ea45177a_503e5e12-b7bd-41bf-bace-d7ca0163602b\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5256 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\JJspolit.exe.3988.dmp | — | |
MD5:— | SHA256:— | |||
| 7164 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_JJspolit.exe_46d523d52922dfda817f7fa85c4b156db1f9c11_ea45177a_21b02021-60fb-4006-8340-6c05d645eb7d\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7164 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\JJspolit.exe.6764.dmp | — | |
MD5:— | SHA256:— | |||
| 836 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_JJspolit.exe_46d523d52922dfda817f7fa85c4b156db1f9c11_ea45177a_b6b2f06c-aaf7-42bb-b4f7-fb67138beb74\Report.wer | — | |
MD5:— | SHA256:— | |||
| 836 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\JJspolit.exe.7120.dmp | — | |
MD5:— | SHA256:— | |||
| 5256 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC112.tmp.WERInternalMetadata.xml | binary | |
MD5:5224CFEE18E409CA34BBB6B50ACB2ABE | SHA256:9491EBB0688E7E8BD9F5448CB5BCA9C0F5E1F3387F0BFA6BCCF387266148924F | |||
| 6316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6316.18389\JJspolit.exe | executable | |
MD5:FF5AD3FD58805CCD7A30924FFCED15C6 | SHA256:5E5CCDF37AE8679D93E62E76678E8084B9BA9A7DF54A96218968955EE405A49A | |||
| 7164 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER1C43.tmp.xml | xml | |
MD5:573995E1CA57C87F333897317A0143CF | SHA256:CD33636D905BD7DEAA6B33256992B44910D8D0ECAD4E12B662CFFA3A2A23F4B2 | |||
| 5256 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:680B0331A3CC8FCCE16367586EC7A721 | SHA256:19F1B5D2C7F62663C14D97578411DC610E5F33E6CE4165977314442435F15305 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
40
DNS requests
23
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6092 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
3988 | JJspolit.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | US | text | 5 b | shared |
3984 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
3984 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
6652 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
5256 | WerFault.exe | GET | 200 | 95.101.78.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 312 b | whitelisted |
6092 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5256 | WerFault.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6092 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6092 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.227.221:443 | — | Ooredoo Q.S.C. | QA | unknown |
1612 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ip-api.com |
| shared |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3988 | JJspolit.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
3988 | JJspolit.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6764 | JJspolit.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
6764 | JJspolit.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
7120 | JJspolit.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
7120 | JJspolit.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
Process | Message |
|---|---|
JJspolit.exe | CLR: Managed code called FailFast without specifying a reason.
|
JJspolit.exe | CLR: Managed code called FailFast without specifying a reason.
|
JJspolit.exe | CLR: Managed code called FailFast without specifying a reason.
|