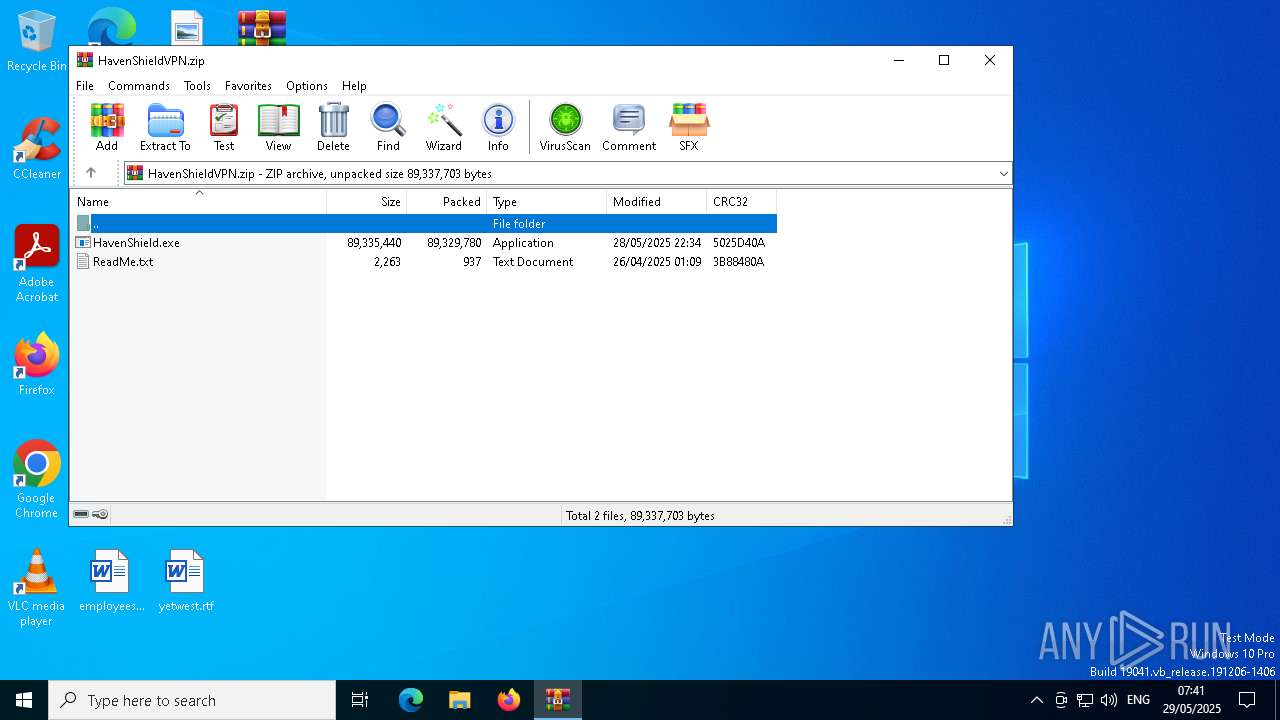
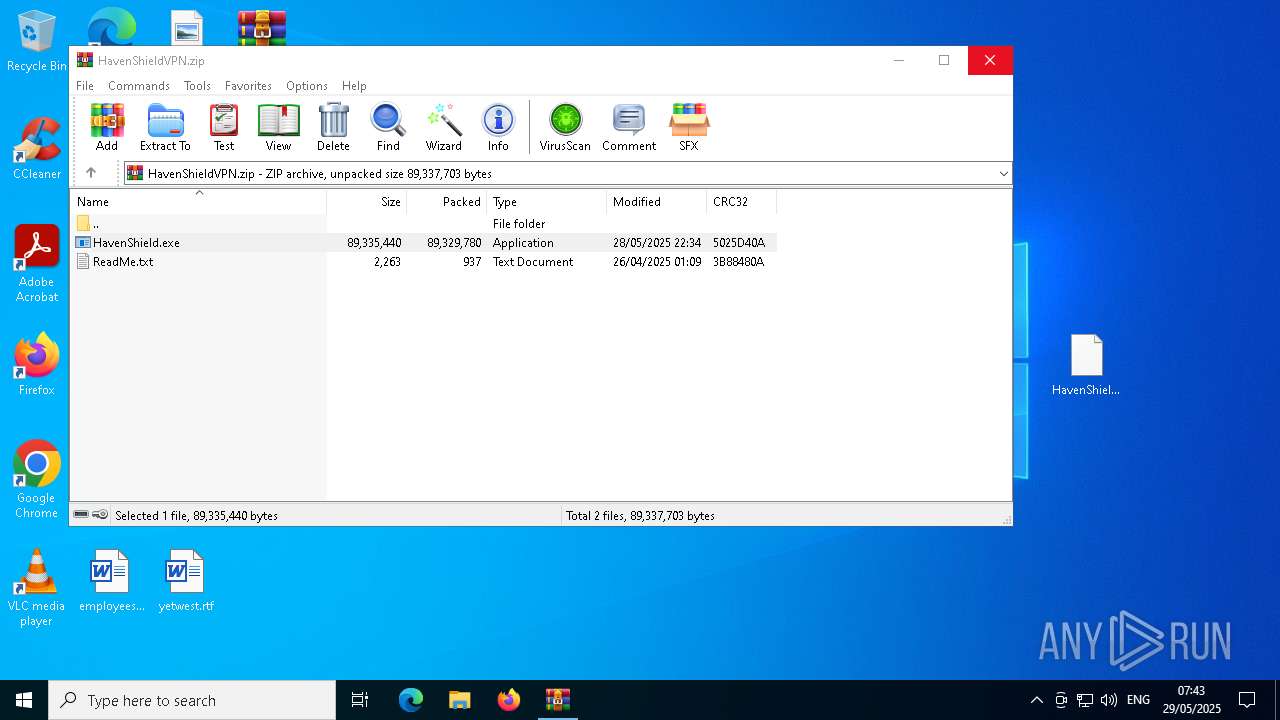
| File name: | HavenShieldVPN.zip |
| Full analysis: | https://app.any.run/tasks/0ad826d5-09cd-4c7b-b112-74ece06959b8 |
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2025, 06:41:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 5EE3EEAEA97469D6266577A8D4F7EAB9 |
| SHA1: | 898F1584BC62A01CBFAAD9C1EF6E701665F95B94 |
| SHA256: | 6C49A1098A62A06F4F9BBC63FA4D0CDCC0D3CA268D79E05C6047C61CDADFEF7A |
| SSDEEP: | 1572864:yPXBsE3YI3GvP3RdAkKLctXRa3Y9eelSL:y/BsSYI3GvvRdANLc9YWYL |
MALICIOUS
Executing a file with an untrusted certificate
- HavenShield.exe (PID: 1240)
Changes powershell execution policy (Unrestricted)
- HavenShieldVPN.exe (PID: 856)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- HavenShield.exe (PID: 1240)
The process creates files with name similar to system file names
- HavenShield.exe (PID: 1240)
Process drops legitimate windows executable
- HavenShield.exe (PID: 1240)
Drops 7-zip archiver for unpacking
- HavenShield.exe (PID: 1240)
Reads security settings of Internet Explorer
- HavenShield.exe (PID: 1240)
Executable content was dropped or overwritten
- HavenShield.exe (PID: 1240)
- HavenShieldVPN.exe (PID: 856)
There is functionality for taking screenshot (YARA)
- HavenShield.exe (PID: 1240)
- HavenShieldVPN.exe (PID: 2612)
Starts application with an unusual extension
- cmd.exe (PID: 968)
Starts CMD.EXE for commands execution
- HavenShieldVPN.exe (PID: 856)
Get information on the list of running processes
- HavenShieldVPN.exe (PID: 856)
- cmd.exe (PID: 736)
Suspicious browser cookie database enumeration
- HavenShieldVPN.exe (PID: 856)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6576)
The process hides Powershell's copyright startup banner
- HavenShieldVPN.exe (PID: 856)
The process bypasses the loading of PowerShell profile settings
- HavenShieldVPN.exe (PID: 856)
Starts POWERSHELL.EXE for commands execution
- HavenShieldVPN.exe (PID: 856)
Application launched itself
- HavenShieldVPN.exe (PID: 856)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7868)
Checks for external IP
- svchost.exe (PID: 2196)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7152)
- HavenShield.exe (PID: 1240)
Checks supported languages
- HavenShield.exe (PID: 1240)
- HavenShieldVPN.exe (PID: 856)
- chcp.com (PID: 6992)
- msiexec.exe (PID: 5592)
- HavenShieldVPN.exe (PID: 2612)
- HavenShieldVPN.exe (PID: 5624)
Create files in a temporary directory
- HavenShield.exe (PID: 1240)
- HavenShieldVPN.exe (PID: 856)
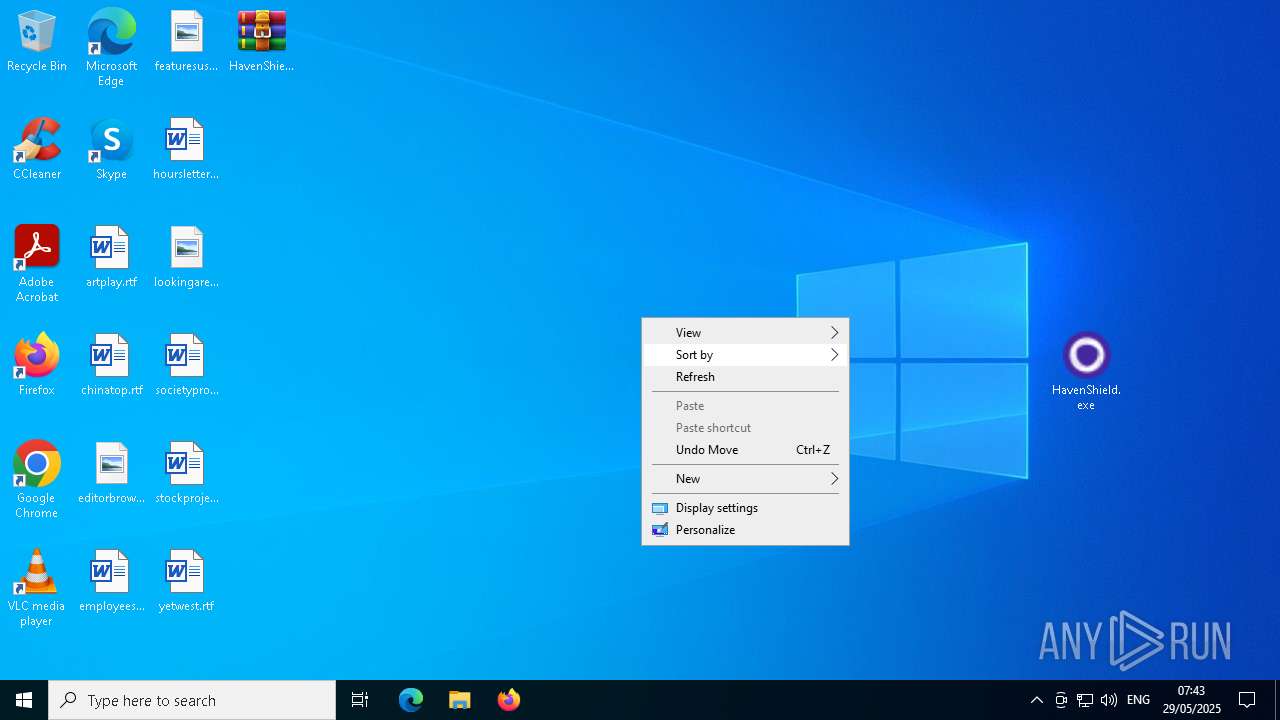
Manual execution by a user
- HavenShield.exe (PID: 1240)
Reads the computer name
- HavenShield.exe (PID: 1240)
- HavenShieldVPN.exe (PID: 856)
- msiexec.exe (PID: 5592)
- HavenShieldVPN.exe (PID: 2612)
- HavenShieldVPN.exe (PID: 5624)
Checks proxy server information
- slui.exe (PID: 2384)
- HavenShieldVPN.exe (PID: 856)
Reads product name
- HavenShieldVPN.exe (PID: 856)
Node.js compiler has been detected
- HavenShieldVPN.exe (PID: 856)
- HavenShieldVPN.exe (PID: 2612)
- HavenShieldVPN.exe (PID: 5624)
Reads the software policy settings
- slui.exe (PID: 2384)
Reads Environment values
- HavenShieldVPN.exe (PID: 856)
Changes the display of characters in the console
- cmd.exe (PID: 968)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 3124)
Reads CPU info
- HavenShieldVPN.exe (PID: 856)
Reads the machine GUID from the registry
- HavenShieldVPN.exe (PID: 856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:28 18:34:38 |
| ZipCRC: | 0x5025d40a |
| ZipCompressedSize: | 89329780 |
| ZipUncompressedSize: | 89335440 |
| ZipFileName: | HavenShield.exe |
Total processes
217
Monitored processes
69
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | C:\WINDOWS\system32\cmd.exe /d /s /c "tasklist" | C:\Windows\System32\cmd.exe | — | HavenShieldVPN.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | HavenShieldVPN.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 772 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | C:\Users\admin\AppData\Local\Temp\2xk2kex96Sy4Hz5LRLrA5qL6WQS\HavenShieldVPN.exe | C:\Users\admin\AppData\Local\Temp\2xk2kex96Sy4Hz5LRLrA5qL6WQS\HavenShieldVPN.exe | HavenShield.exe | ||||||||||||
User: admin Company: HavenShieldVPN Corporation. Integrity Level: MEDIUM Description: HavenShieldVPN Version: 0.0.0 Modules
| |||||||||||||||
| 896 | powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | HavenShieldVPN.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | C:\WINDOWS\system32\cmd.exe /d /s /c "chcp" | C:\Windows\System32\cmd.exe | — | HavenShieldVPN.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | "C:\Users\admin\Desktop\HavenShield.exe" | C:\Users\admin\Desktop\HavenShield.exe | explorer.exe | ||||||||||||
User: admin Company: HavenShieldVPN Corporation. Integrity Level: MEDIUM Description: HavenShieldVPN Services Version: 0.0.0 Modules
| |||||||||||||||
| 1472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | HavenShieldVPN.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
90 391
Read events
90 373
Write events
18
Delete events
0
Modification events
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\HavenShieldVPN.zip | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
22
Suspicious files
23
Text files
41
Unknown types
118
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
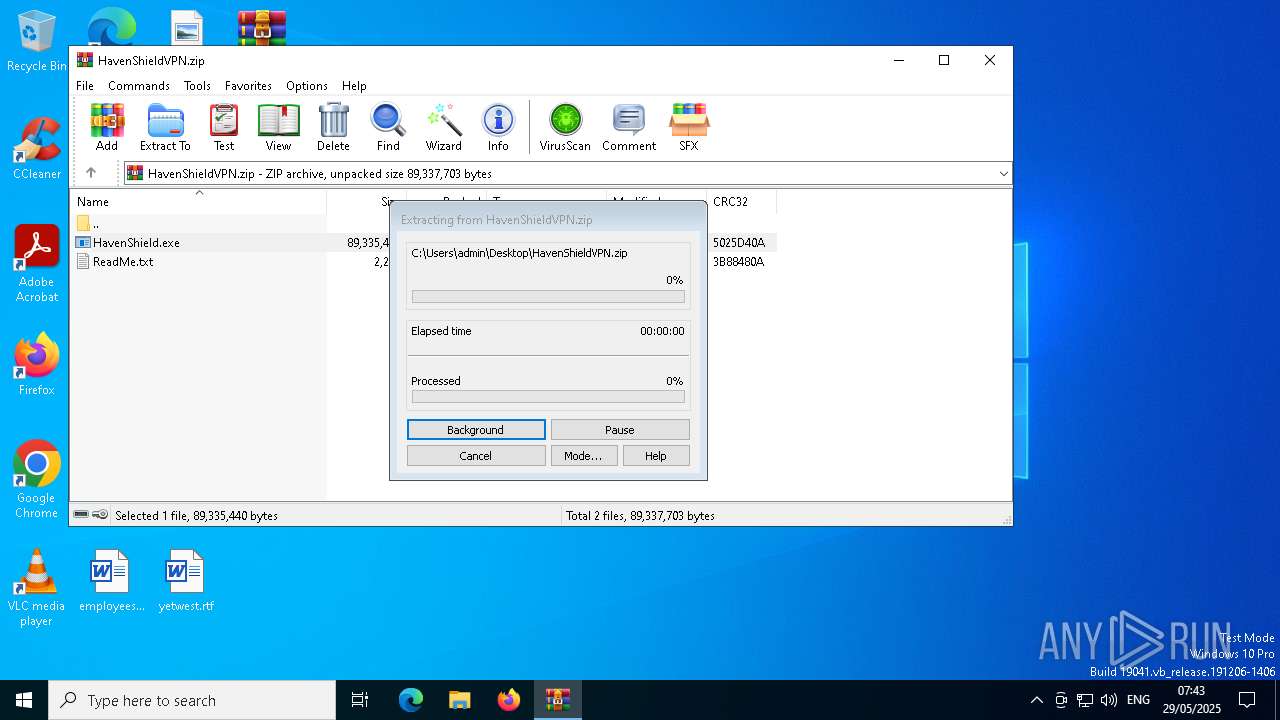
| 7152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7152.31397\HavenShield.exe | — | |
MD5:— | SHA256:— | |||
| 1240 | HavenShield.exe | C:\Users\admin\AppData\Local\Temp\nsb42EE.tmp\app-64.7z | — | |
MD5:— | SHA256:— | |||
| 1240 | HavenShield.exe | C:\Users\admin\AppData\Local\Temp\nsb42EE.tmp\7z-out\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 1240 | HavenShield.exe | C:\Users\admin\AppData\Local\Temp\nsb42EE.tmp\7z-out\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 1240 | HavenShield.exe | C:\Users\admin\AppData\Local\Temp\nsb42EE.tmp\7z-out\chrome_200_percent.pak | pgc | |
MD5:E9C1423FE5D139A4C88BA8B107573536 | SHA256:2408969599D3953AAE2FB36008E4D0711E30D0BC86FB4D03F8B0577D43C649FA | |||
| 1240 | HavenShield.exe | C:\Users\admin\AppData\Local\Temp\nsb42EE.tmp\nsis7z.dll | executable | |
MD5:80E44CE4895304C6A3A831310FBF8CD0 | SHA256:B393F05E8FF919EF071181050E1873C9A776E1A0AE8329AEFFF7007D0CADF592 | |||
| 1240 | HavenShield.exe | C:\Users\admin\AppData\Local\Temp\nsb42EE.tmp\7z-out\locales\cs.pak | pgc | |
MD5:582FDE87AAC61961E4F7955F16D31769 | SHA256:7D7B701CE510B2E4A18E957E500086DB590AAD8BF5ACD37F82263A676F0B556C | |||
| 1240 | HavenShield.exe | C:\Users\admin\AppData\Local\Temp\nsb42EE.tmp\7z-out\locales\bg.pak | pgc | |
MD5:E6608ECC589E87A6F78F9CE553EC2609 | SHA256:97EF7984074775282B68DCA5D5A469EFDB2B22474EE6669FDFB5197D3F1B3768 | |||
| 1240 | HavenShield.exe | C:\Users\admin\AppData\Local\Temp\nsb42EE.tmp\7z-out\locales\en-US.pak | mmw | |
MD5:5C52A86B21633B55B383C20F16859B2F | SHA256:41123D72BD8E289E85BD35227AABB4CC61FE1DE02B5CD7A7834E5EC200BC2078 | |||
| 1240 | HavenShield.exe | C:\Users\admin\AppData\Local\Temp\nsb42EE.tmp\7z-out\locales\de.pak | pgc | |
MD5:D1A513308F9DE55B6C7BBEEF7C4FE90B | SHA256:662496EFF49FEBBE49F0A03CF2C51ACAA743CB2237DE3C41014556E16F3D8E2B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
96
DNS requests
31
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 4.245.163.56:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
6668 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 4.245.163.56:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | compressed | 23.9 Kb | whitelisted |
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6668 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6668 | SIHClient.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6668 | SIHClient.exe | 23.32.238.112:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ipapi .co in DNS lookup) |