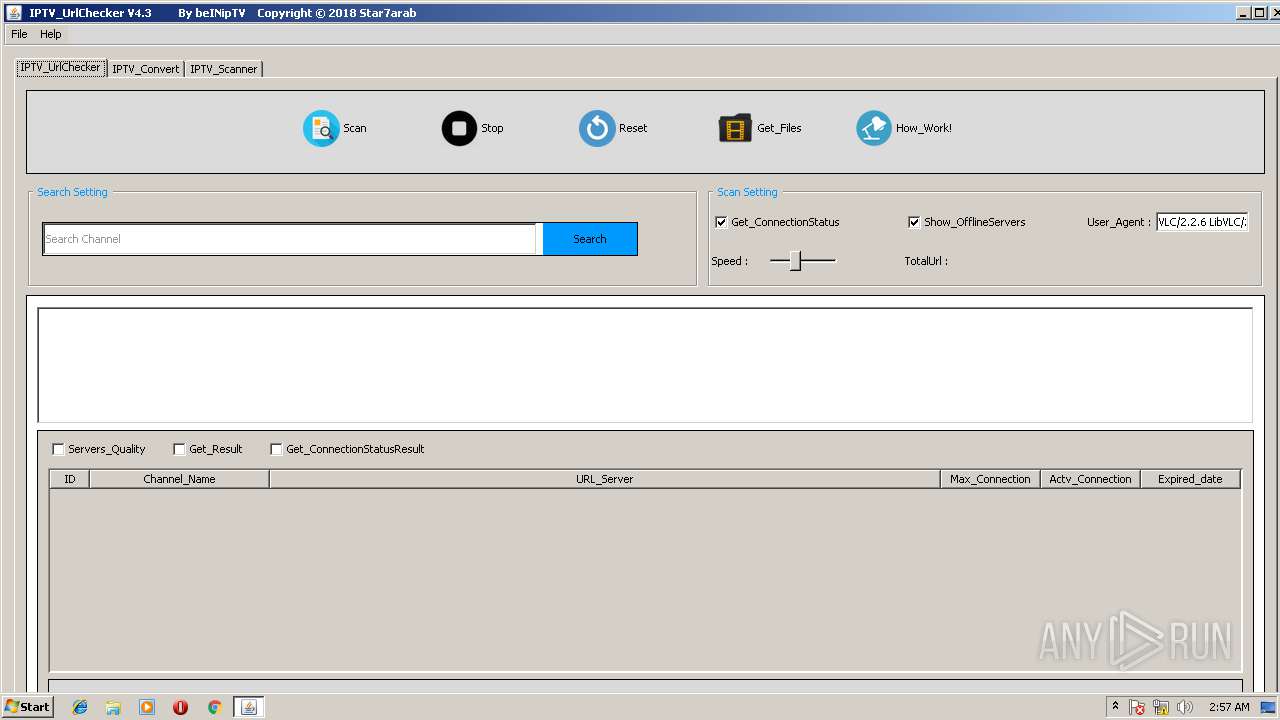
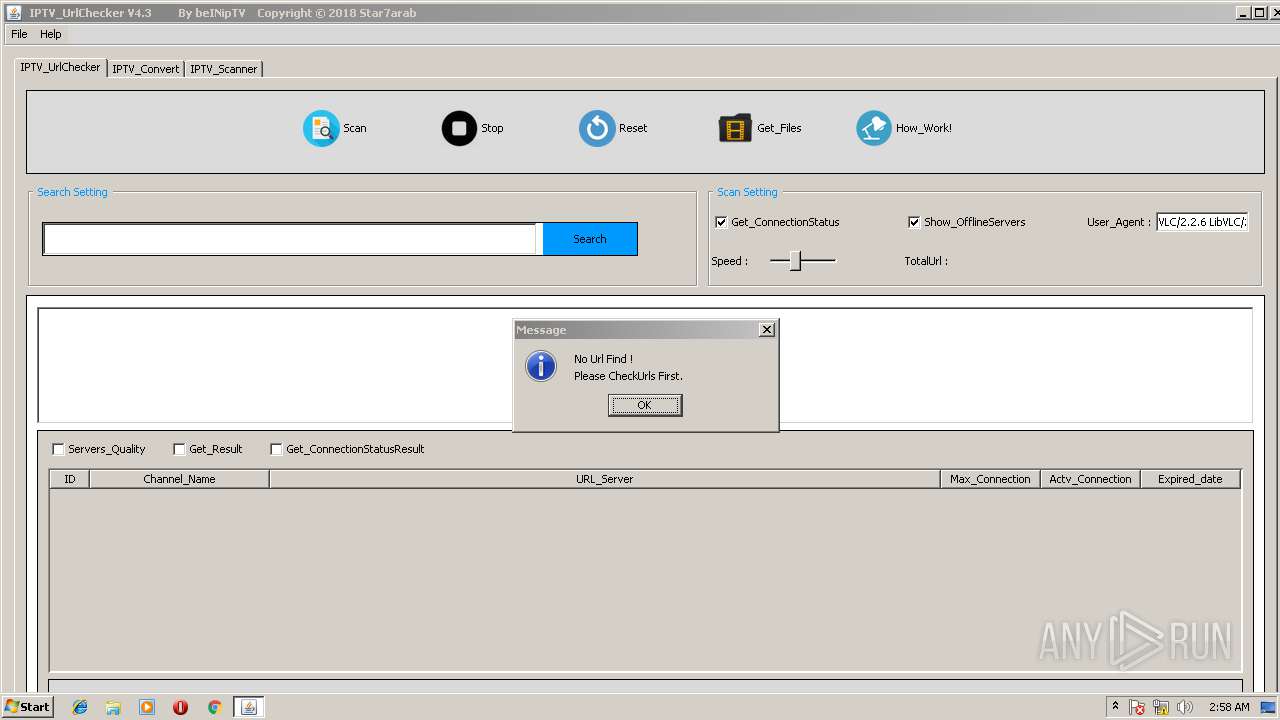
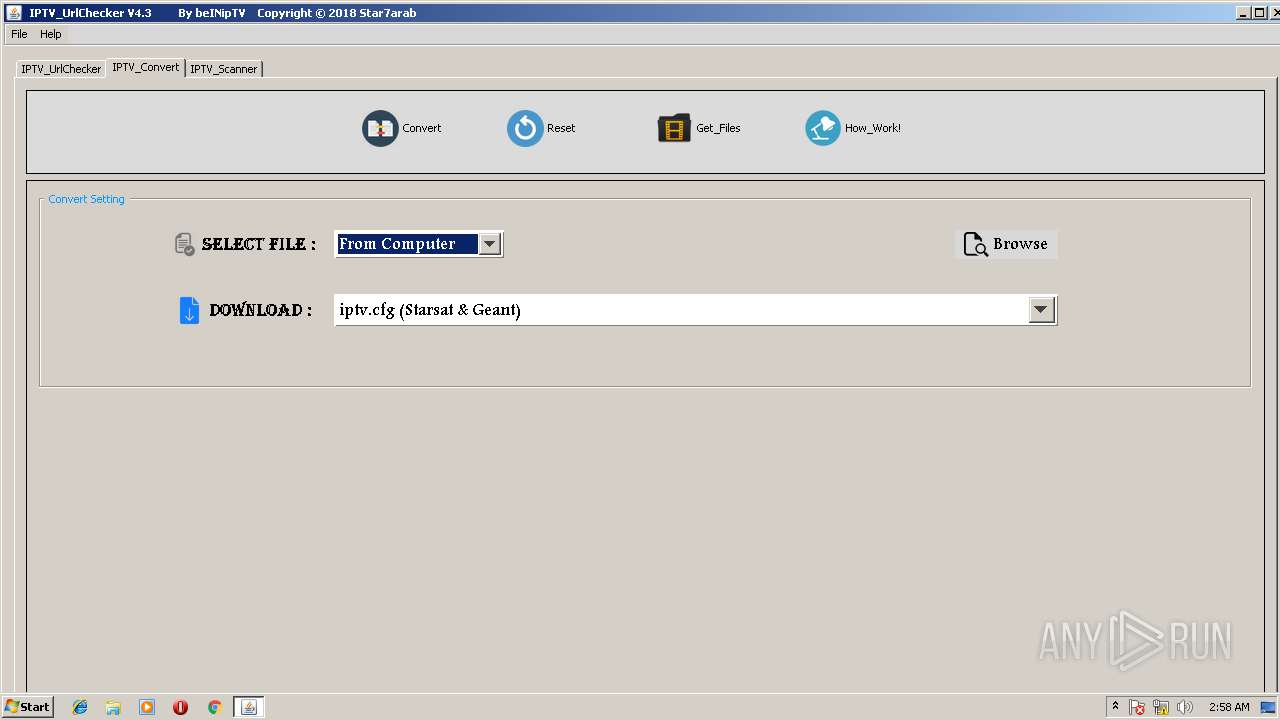
| File name: | IPTV_UrlChecker 4.3.exe |
| Full analysis: | https://app.any.run/tasks/1c772286-5fb2-4aa0-b909-f288dbf33c5d |
| Verdict: | Suspicious activity |
| Analysis date: | June 13, 2018, 01:57:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 186813F3AA3753D5CA3249974CFD9E7B |
| SHA1: | 000A0D5AF8F6CD40FC66CA4C915329B3DC5F1296 |
| SHA256: | 6C457A82FD4E2C3FC86256A34EBF4E39AA78BD15E5040EAD41CEA148F7F2120D |
| SSDEEP: | 12288:R2S/ifyCmMf/JATS4SJJrRjm5f1M+7ADNvnn0vZjQiFTf:RLhhM3JAubJJrRjmA6ADN/0B |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes JAVA applets
- IPTV_UrlChecker 4.3.exe (PID: 3500)
INFO
Dropped object may contain URL's
- IPTV_UrlChecker 4.3.exe (PID: 3500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (33) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (23.9) |
| .exe | | | Win64 Executable (generic) (21.2) |
| .scr | | | Windows screen saver (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:05:20 23:09:01+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 411172 |
| InitializedDataSize: | 449024 |
| UninitializedDataSize: | 18944 |
| EntryPoint: | 0x1240 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-May-2007 21:09:01 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 20-May-2007 21:09:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00064624 | 0x00064800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.32879 |
.data | 0x00066000 | 0x00001274 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.69523 |
.bss | 0x00068000 | 0x000049F0 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.edata | 0x0006D000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.10882 |
.idata | 0x0006E000 | 0x00000FD0 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.07547 |
.rsrc | 0x0006F000 | 0x0008F000 | 0x0008F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.88571 |
.reloc | 0x000FE000 | 0x00002F9C | 0x00003000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.7099 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.12382 | 744 | UNKNOWN | English - United States | RT_ICON |
2 | 1.87204 | 2216 | UNKNOWN | English - United States | RT_ICON |
102 | 6.8912 | 578733 | UNKNOWN | English - United States | JAVA |
103 | 4.93722 | 383 | UNKNOWN | English - United States | JAVA |
104 | 7.65625 | 2885 | UNKNOWN | English - United States | JAVA |
A | 1.87486 | 22 | UNKNOWN | English - United States | RT_GROUP_ICON |
A2 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_Z10testStringP7JNIEnv_P8_jobjectP8_jstring@12 | 1 | 0x0001E430 |
_Z15jnm_exitWindowsP7JNIEnv_P8_jobjectl@12 | 2 | 0x0001EB72 |
_Z16jnm_getdriveinfoP7JNIEnv_P8_jobjectS2_@12 | 3 | 0x0001EF02 |
_Z16jnm_shellexecuteP7JNIEnv_P8_jobjectP8_jstringS4_S4_S4_l@28 | 4 | 0x0001EC12 |
_Z21jnm_getExecutableNameP7JNIEnv_P8_jobject@8 | 5 | 0x0001E6B2 |
_Z21jnm_getExecutablePathP7JNIEnv_P8_jobject@8 | 6 | 0x0001E5E2 |
_Z22jnm_deleteFileOnRebootP7JNIEnv_P8_jobjectP8_jstring@12 | 7 | 0x0001E786 |
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1396 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -classpath "C:\Users\admin\AppData\Local\Temp\temp0.jar;C:\Users\admin\AppData\Local\Temp\temp1.jar;" iptv.urlchecker.IPTVUrlChecker | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | IPTV_UrlChecker 4.3.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3500 | "C:\Users\admin\AppData\Local\Temp\IPTV_UrlChecker 4.3.exe" | C:\Users\admin\AppData\Local\Temp\IPTV_UrlChecker 4.3.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
23
Read events
22
Write events
1
Delete events
0
Modification events
| (PID) Process: | (1396) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3500 | IPTV_UrlChecker 4.3.exe | C:\Users\admin\AppData\Local\Temp\temp0.jar | java | |
MD5:896696C80EC5FCB17247BFDF129236F6 | SHA256:7F5C7E978505EA32DFF534C1E16FB8EEA800250D8E2CDA9A897C06E8A249BE1B | |||
| 1396 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:77AB844276893EBA8E567DFB08028C5B | SHA256:F0A070C1E050C253205EF50A390DB743560A1D855DE7F076325B8CE996C51148 | |||
| 3500 | IPTV_UrlChecker 4.3.exe | C:\Users\admin\AppData\Local\Temp\temp1.jar | java | |
MD5:86CF28D78EA5FFD10BFC190A6CD70410 | SHA256:1895971812DD97715D0C27877291AA33FD24B49D60D751BB6E5720829B2CB76F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1396 | javaw.exe | GET | 301 | 67.199.248.10:80 | http://bit.ly/2HAsDSa | US | html | 114 b | shared |
1396 | javaw.exe | GET | — | 216.58.214.83:80 | http://www.algeria-iptv.tk/ | US | — | — | suspicious |
1396 | javaw.exe | GET | 200 | 109.236.88.2:80 | http://star7arab.com/user.asp?id=107524&f=CharFcontroler43.txt | NL | text | 2 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1396 | javaw.exe | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
1396 | javaw.exe | 216.58.214.83:80 | www.algeria-iptv.tk | Google Inc. | US | whitelisted |
1396 | javaw.exe | 109.236.88.2:80 | star7arab.com | WorldStream B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bit.ly |
| shared |
www.algeria-iptv.tk |
| suspicious |
star7arab.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1396 | javaw.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |